The Rise and Fall of Tycoon 2FA: Lessons from a Global Phishing Takedown [2025]
In a bold and decisive strike against cybercrime, Microsoft and Europol recently orchestrated the takedown of Tycoon 2FA, a notorious phishing-as-a-service network capable of bypassing two-factor authentication (2FA) with alarming ease. This operation, involving multiple European law enforcement agencies, marks a significant victory in the ongoing battle against cyber threats that exploit vulnerabilities in authentication systems. Let's dive deep into how this operation unfolded, the technical intricacies of the Tycoon 2FA platform, and what it means for the future of cybersecurity.
TL; DR
- Phishing-as-a-service (Phaa S) networks like Tycoon 2FA streamline cybercrime operations.
- Bypassing 2FA was a critical feature that made Tycoon 2FA particularly dangerous.
- Global law enforcement collaboration was key to the successful takedown.
- Future cybersecurity trends will focus on enhancing multi-factor authentication.
- Organizations must remain vigilant against evolving phishing techniques.
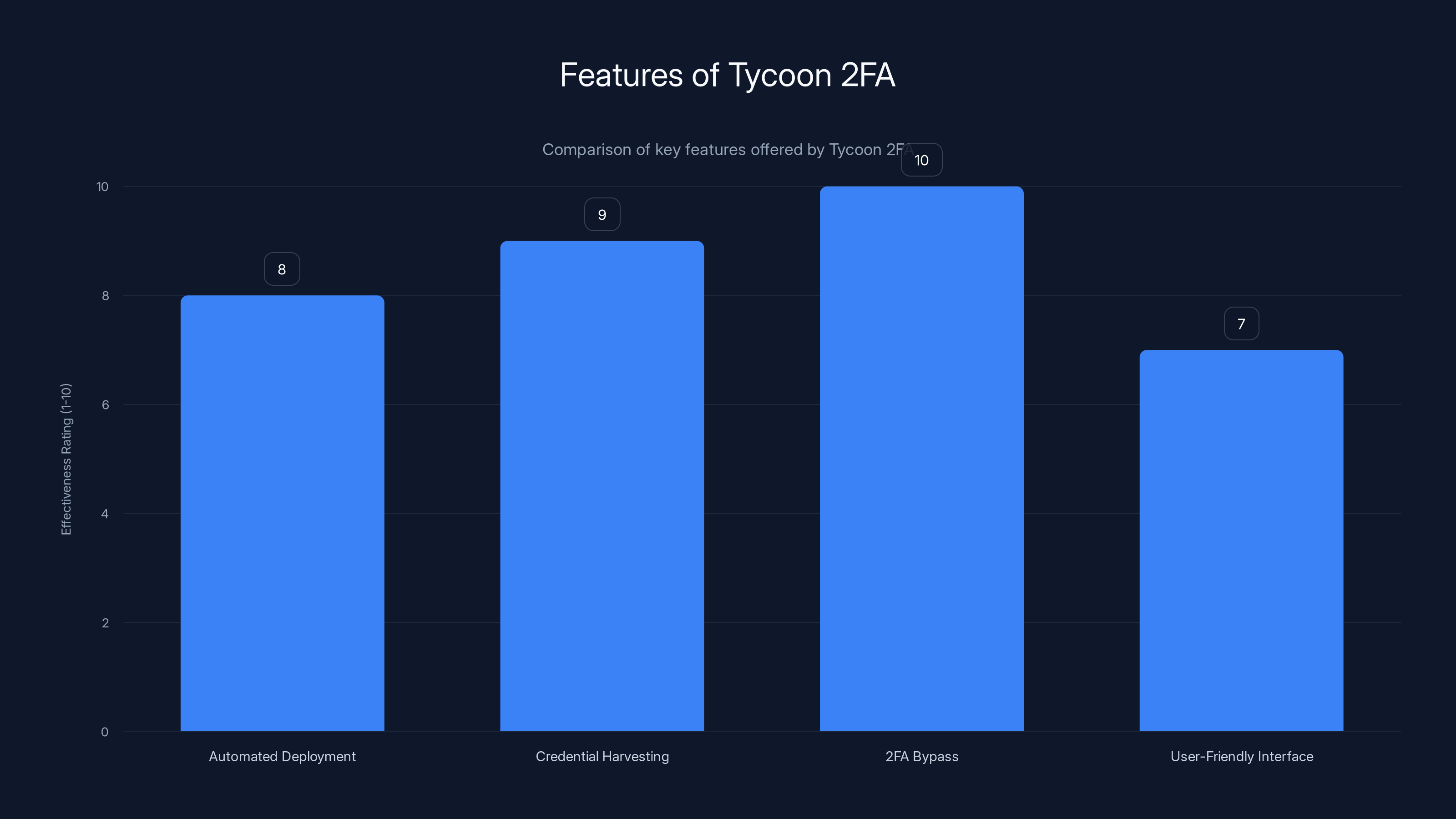
Tycoon 2FA excels in 2FA bypass techniques with a top rating of 10, highlighting its advanced capabilities in phishing attacks. (Estimated data)
Understanding Phishing-as-a-Service (Phaa S)
Phishing-as-a-Service platforms like Tycoon 2FA represent a new wave of cybercrime, where sophisticated phishing capabilities are sold to aspiring cybercriminals as an easy-to-use service. These platforms offer pre-configured kits and infrastructure, enabling even non-technical individuals to launch phishing campaigns.
What Made Tycoon 2FA Different?
Tycoon 2FA stood out due to its ability to bypass 2FA, a security measure that was once considered a robust defense against unauthorized access. By exploiting weaknesses in the 2FA process, Tycoon 2FA allowed attackers to hijack sessions and intercept authentication tokens, granting them access to sensitive accounts.
Features of Tycoon 2FA:
- Automated phishing kit deployment
- Real-time credential harvesting
- Advanced 2FA bypass techniques
- User-friendly interface for non-technical users
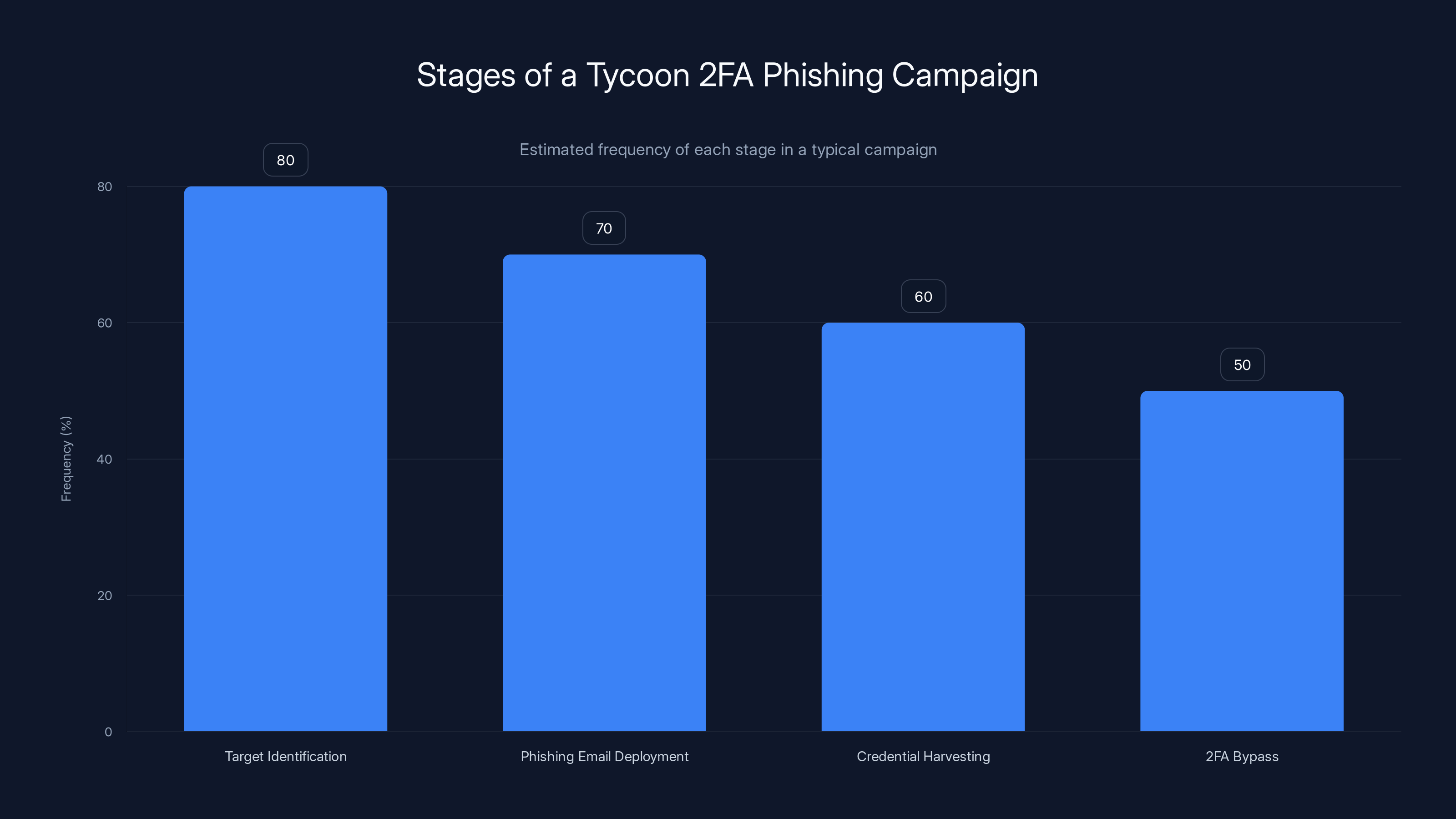
The chart estimates the frequency of each stage in a Tycoon 2FA phishing campaign, highlighting the systematic approach to bypassing 2FA. Estimated data.
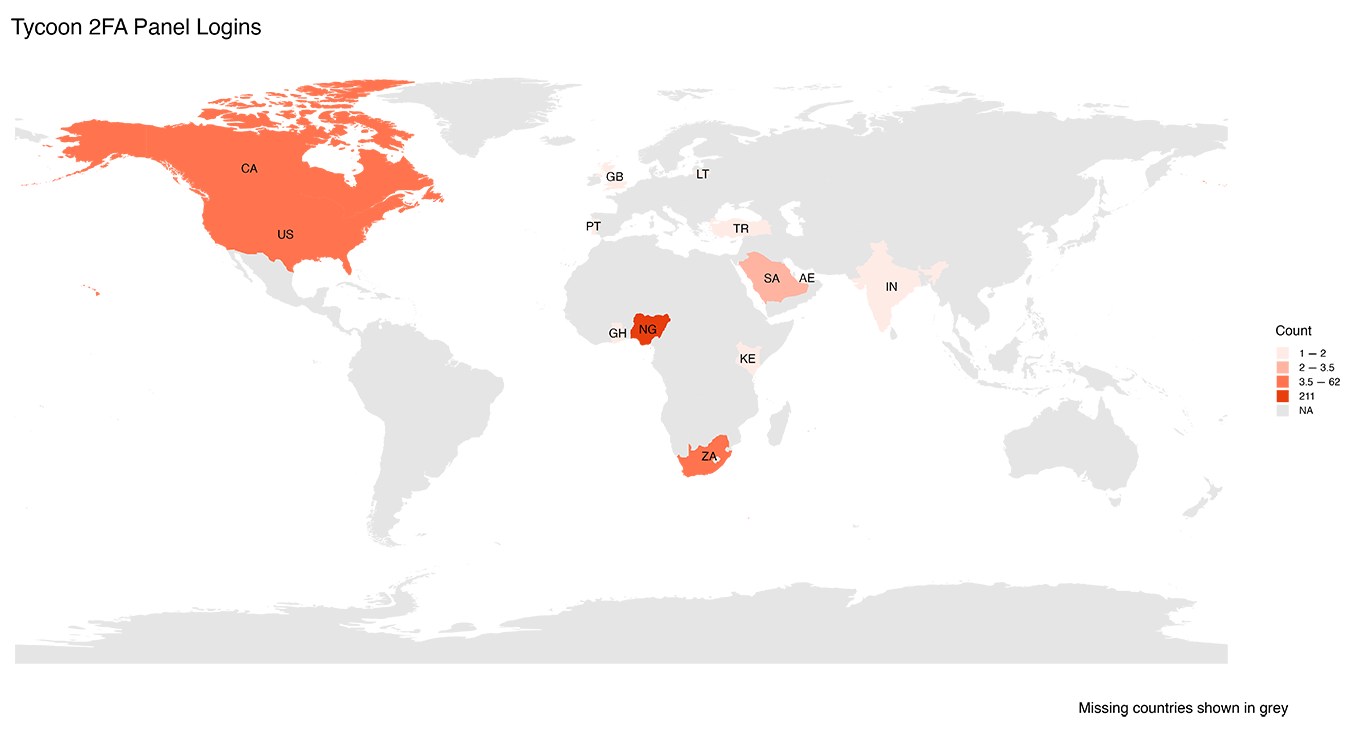
The Global Takedown Operation
The takedown of Tycoon 2FA was no small feat. Coordinated by Europol, the operation saw the collaboration of law enforcement agencies from Latvia, Lithuania, Portugal, Poland, Spain, and the United Kingdom. This multinational effort led to the dismantling of Tycoon 2FA's core infrastructure and the seizure of several domains used to conduct phishing operations.
How the Operation Unfolded
- Intelligence Gathering: Law enforcement agencies gathered intelligence on Tycoon 2FA's operations, identifying key players and infrastructure.
- Cross-Border Collaboration: Agencies worked together to share information and coordinate actions.
- Raid and Seizure: Physical raids were conducted to seize servers and data, disrupting the network's operations.
- Arrests and Legal Proceedings: Key individuals behind Tycoon 2FA were arrested, and legal actions were initiated.
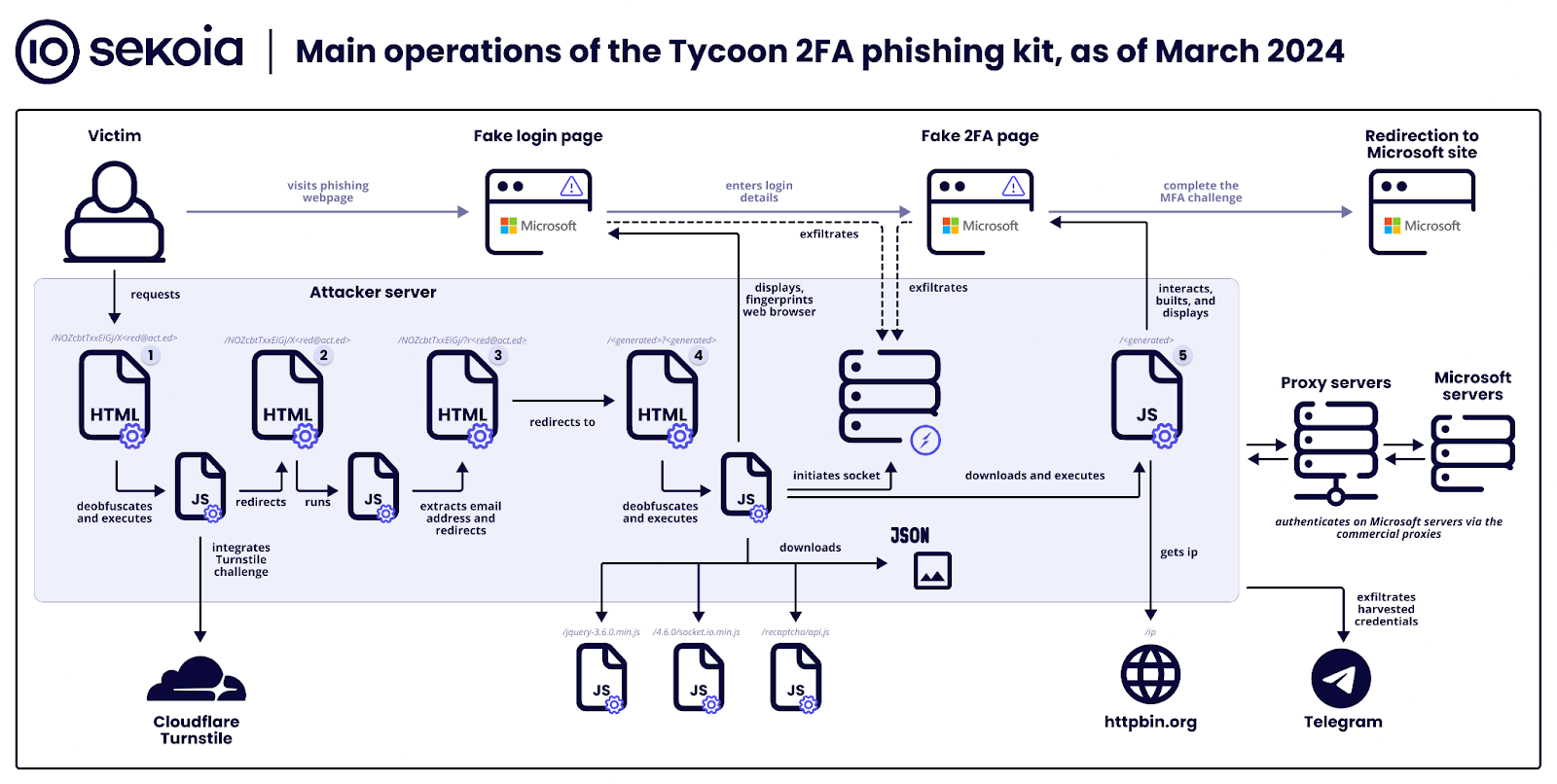
Technical Details of Tycoon 2FA
To understand the impact of Tycoon 2FA, it's crucial to delve into its technical architecture and how it bypassed 2FA mechanisms.
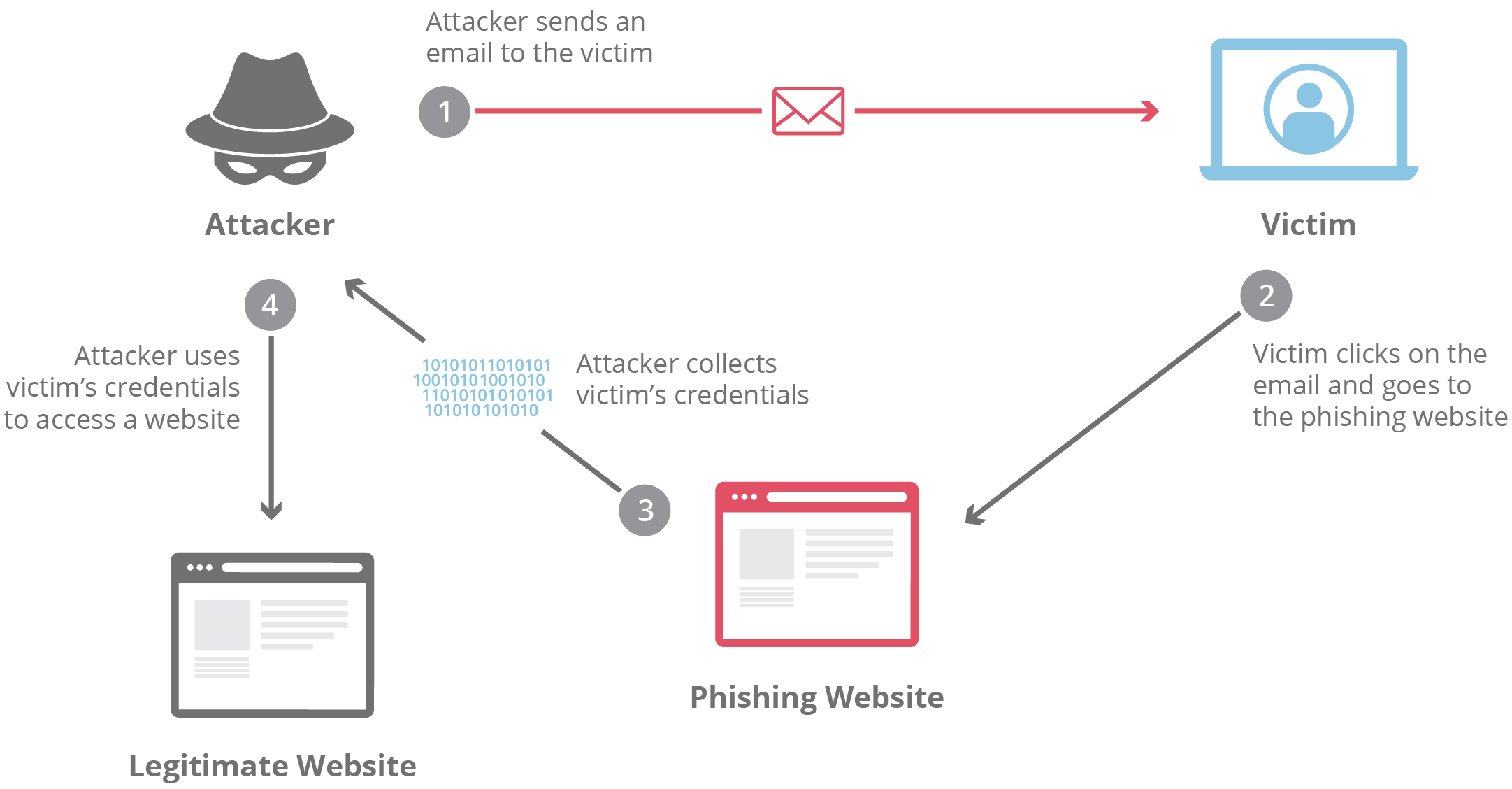
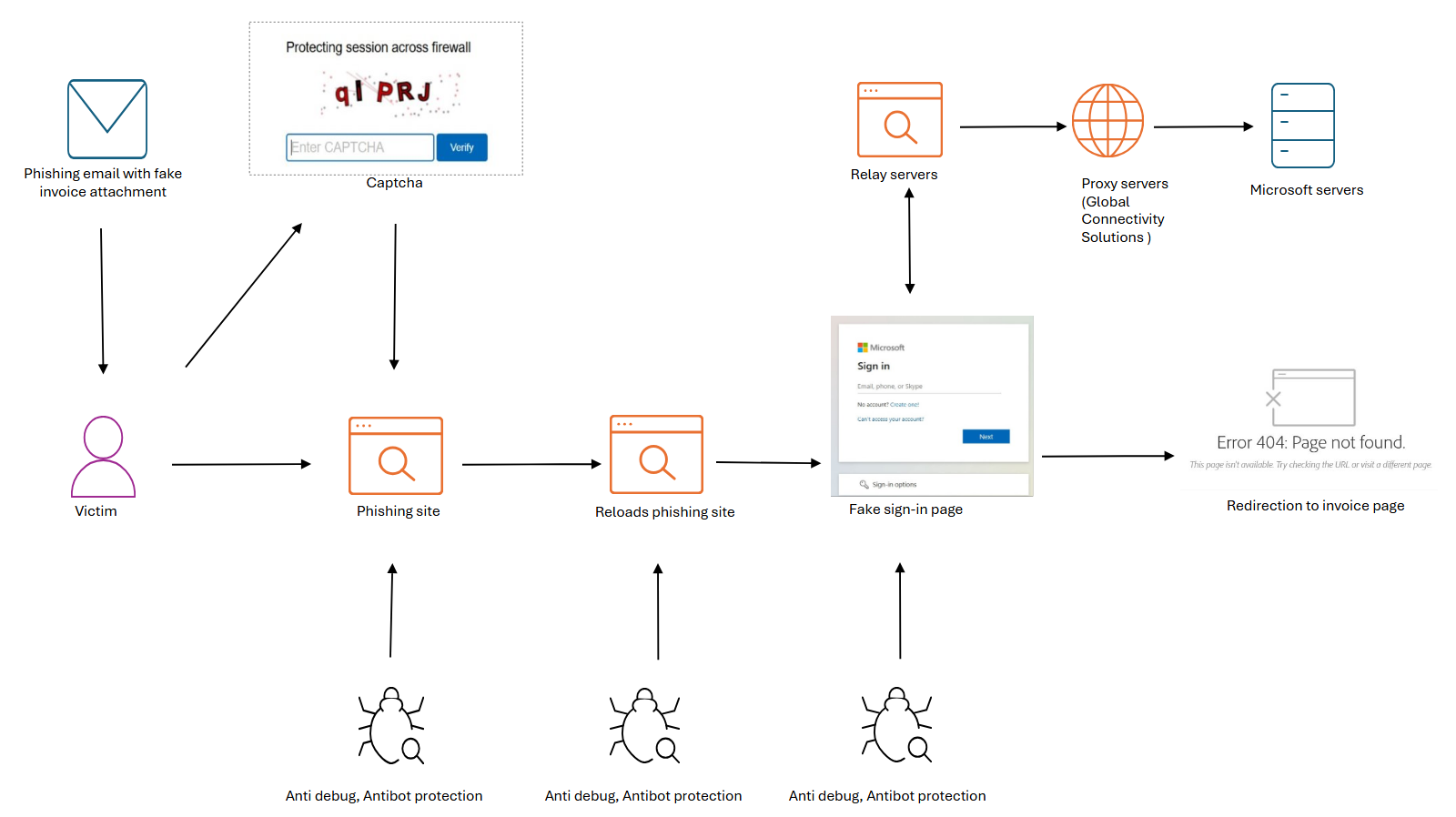
Anatomy of a Phishing Campaign
A typical Tycoon 2FA phishing campaign involved several stages:
- Target Identification: Attackers identified potential victims, often through email lists or social engineering.
- Phishing Email Deployment: Using Tycoon 2FA's tools, attackers sent phishing emails that mimicked legitimate services.
- Credential Harvesting: Victims were lured into providing their credentials on fake login pages.
- 2FA Bypass: Once credentials were obtained, Tycoon 2FA used session hijacking techniques to bypass 2FA.
Bypassing 2FA: The Technical Exploit
2FA is typically bypassed through session hijacking, where attackers intercept authentication tokens exchanged between the user and service. Tycoon 2FA's platform automated this process, making it accessible to less sophisticated attackers.
- Session Hijacking: Intercepting session tokens to gain access without needing the second factor.
- Real-Time Phishing: Phishing pages dynamically updated to capture 2FA codes in real-time.
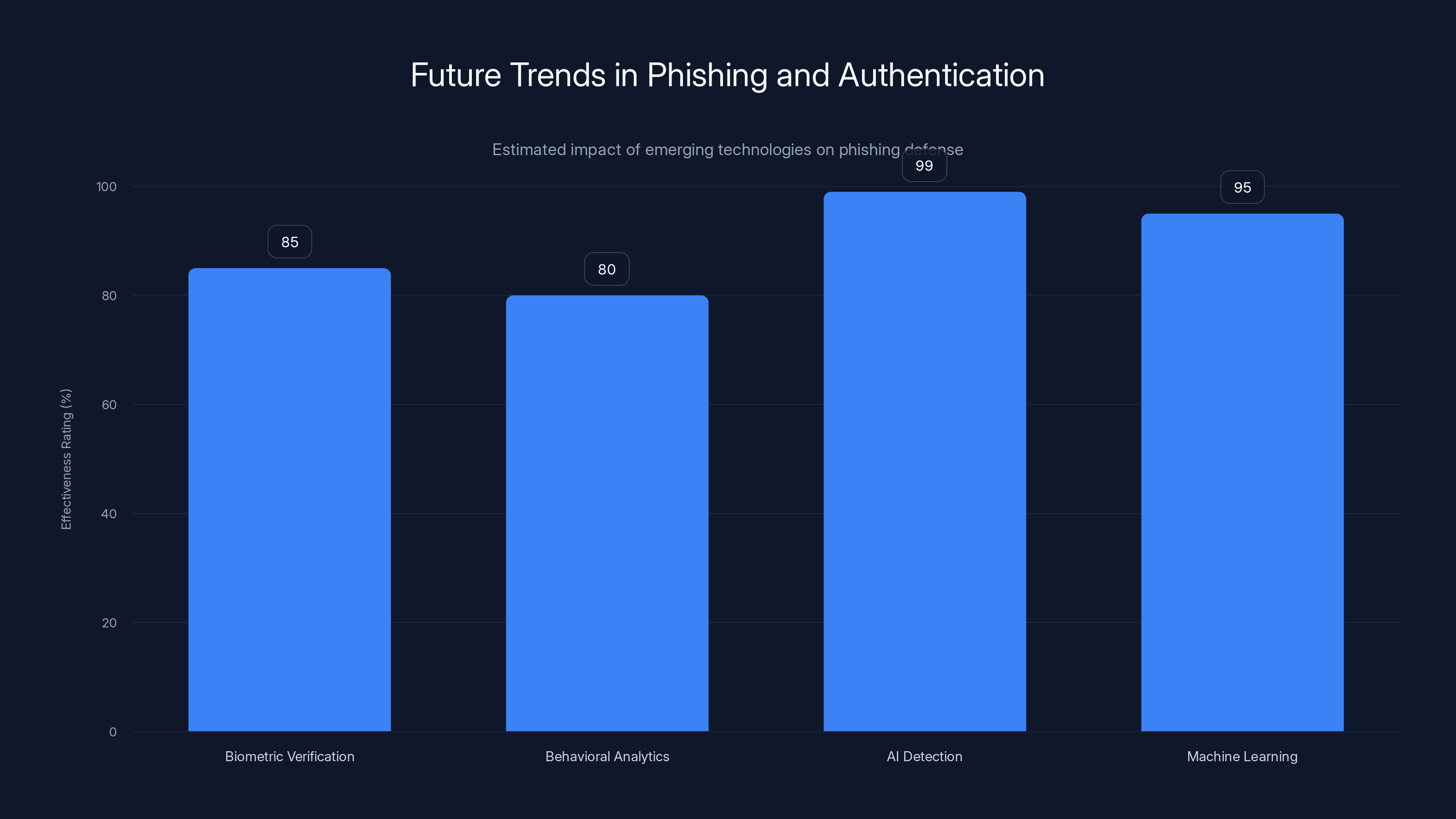
AI-driven solutions show the highest potential effectiveness in detecting phishing attempts, with an accuracy of up to 99%. Estimated data based on emerging trends.
Best Practices to Mitigate Phishing Attacks
Organizations must adopt a proactive approach to combat phishing threats. Here are some best practices:
- User Education: Conduct regular training sessions to educate employees about phishing tactics.
- Email Filtering: Implement advanced email filters to block phishing emails before they reach users.
- Multi-Factor Authentication: Use MFA solutions that combine something you know, have, and are.
- Security Audits: Perform regular security audits to identify and address vulnerabilities.

Common Pitfalls and Solutions
Despite best efforts, many organizations fall victim to phishing attacks due to common pitfalls:
- Over-reliance on 2FA: Assuming 2FA alone is sufficient protection.
- Lack of Incident Response Plan: Being unprepared to respond to phishing incidents.
- Ignoring Security Updates: Failing to apply critical security patches promptly.
Solutions:
- Implement layered security measures that go beyond 2FA.
- Develop and regularly update a comprehensive incident response plan.
- Prioritize security updates to minimize exposure to vulnerabilities.
Future Trends in Phishing and Authentication
As cyber threats evolve, so too must our defenses. Here are some trends to watch:
Enhanced Multi-Factor Authentication
Future MFA solutions will likely incorporate more sophisticated mechanisms such as biometric verification and behavioral analytics to thwart phishing attacks.
AI and Machine Learning
AI will play a crucial role in detecting and mitigating phishing attempts. Machine learning algorithms can identify patterns and anomalies indicative of phishing.
Recommendations for Organizations
To stay ahead of phishing threats, organizations should:
- Invest in Advanced Threat Detection: Leverage AI and ML tools to enhance threat detection capabilities.
- Strengthen Authentication Protocols: Adopt MFA solutions with multiple layers of verification.
- Promote a Security-First Culture: Encourage employees to prioritize security in their daily activities.
- Collaborate with Industry Peers: Share insights and strategies to combat phishing threats collectively.
Case Study: Successful Phishing Mitigation
Consider the case of a mid-sized tech firm that successfully fended off a sophisticated phishing attack by implementing advanced threat detection tools and conducting regular employee training. By fostering a culture of security awareness, the firm was able to identify and neutralize phishing attempts before any damage was done.

Conclusion
The takedown of Tycoon 2FA is a testament to the power of global collaboration in the fight against cybercrime. As phishing tactics continue to evolve, organizations must remain vigilant and proactive in their defense strategies. By adopting advanced security measures and fostering a culture of security awareness, businesses can protect themselves from the ever-present threat of phishing attacks.
Use Case: Automate your security incident response with AI-driven tools for rapid threat detection.
Try Runable For Free
FAQ
What is phishing-as-a-service (Phaa S)?
Phishing-as-a-service (Phaa S) refers to platforms that sell phishing capabilities as a service, enabling users to launch phishing attacks without technical expertise.
How did Tycoon 2FA bypass 2FA?
Tycoon 2FA bypassed 2FA using session hijacking techniques, intercepting authentication tokens to gain unauthorized access.
What are the benefits of multi-factor authentication?
Multi-factor authentication enhances security by requiring multiple forms of verification, reducing the risk of unauthorized access.
How can organizations protect against phishing attacks?
Organizations can protect against phishing by implementing user education programs, advanced email filtering, and multi-factor authentication.
What role does AI play in phishing prevention?
AI enhances phishing prevention by detecting patterns and anomalies indicative of phishing attempts, improving threat detection accuracy.
How did global collaboration contribute to the takedown of Tycoon 2FA?
Global collaboration allowed law enforcement agencies to share intelligence and coordinate actions, leading to the successful dismantling of Tycoon 2FA.
What are the future trends in authentication technologies?
Future trends in authentication include enhanced MFA solutions with biometric and behavioral analytics, and increased use of AI for threat detection.
Why is it important to have an incident response plan?
An incident response plan is crucial for quickly addressing security incidents, minimizing damage, and restoring normal operations.
How can organizations foster a security-first culture?
Organizations can foster a security-first culture by promoting security awareness, providing regular training, and encouraging proactive security practices.

Key Takeaways
- Phishing-as-a-service platforms simplify cybercrime with user-friendly interfaces.
- Tycoon 2FA's ability to bypass 2FA posed significant security risks.
- Global collaboration is essential in dismantling sophisticated cybercrime networks.
- Future authentication trends include biometric and behavioral analytics enhancements.
- AI plays a pivotal role in detecting and mitigating phishing threats.
Related Articles
- Unmasking the Latest Phishing Threat: Fake Google Security Pages [2025]
- LexisNexis Data Breach: What You Need to Know [2025]
- Hackers Are Turning to Easy, Fast AI Solutions to Roll Out Attacks: How to Keep Your Business Safe [2025]
- Massive Data Breach on French Medical Platform: Lessons and Future Implications [2025]
- The Rise of Government Hacking Tools in Cybercrime: A Deep Dive [2025]
- The Silent Threat: How Hackers Exploit .arpa Domains for Phishing Schemes [2025]
![The Rise and Fall of Tycoon 2FA: Lessons from a Global Phishing Takedown [2025]](https://tryrunable.com/blog/the-rise-and-fall-of-tycoon-2fa-lessons-from-a-global-phishi/image-1-1772706873987.jpg)



