The Fall of Leak Base: Inside the Seizure of a Major Data Leak Forum [2025]
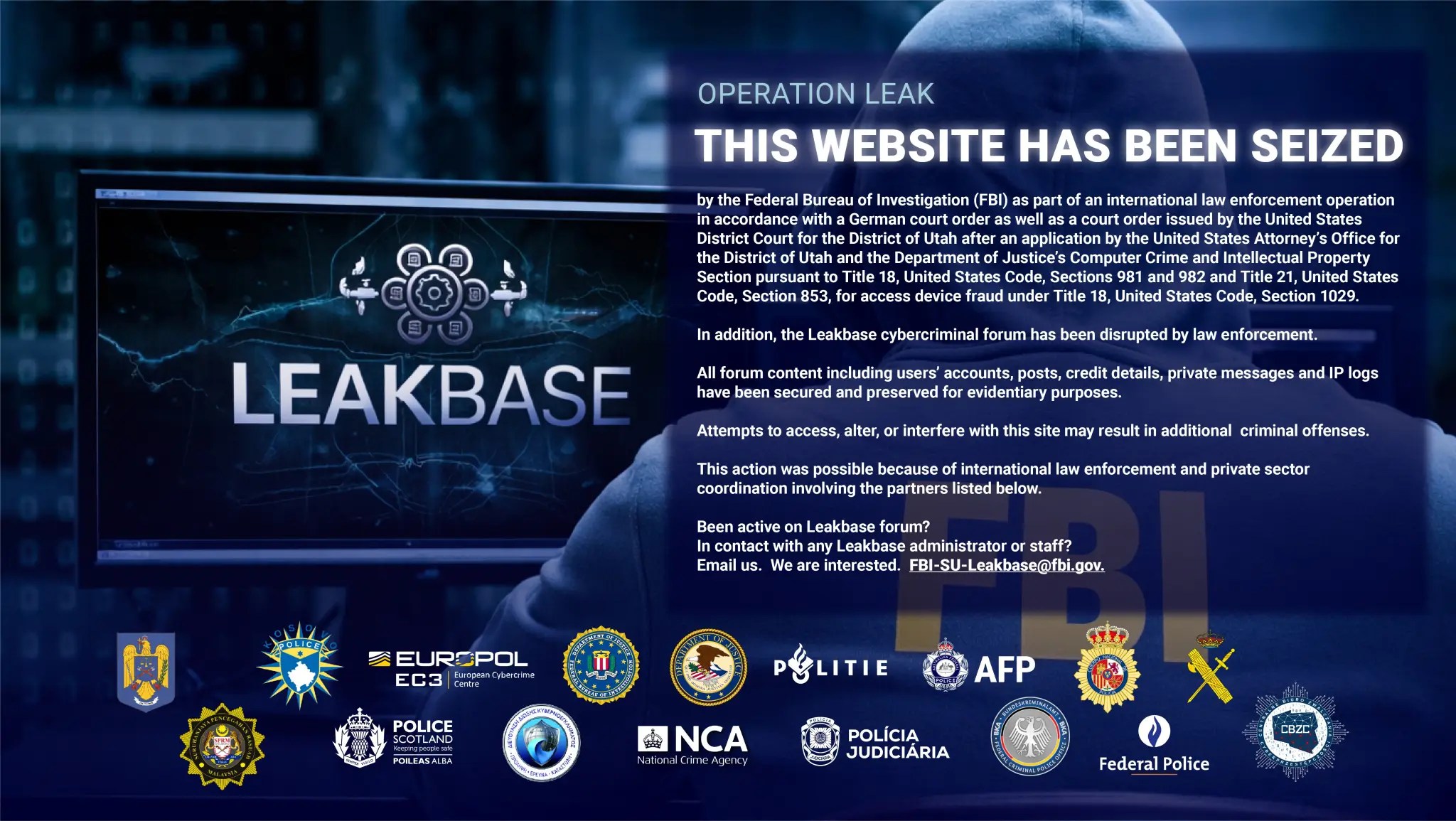
Last year, a significant event shook the cybercrime world—the takedown of Leak Base by the FBI and Europol. Leak Base was not just any data leak forum; it was a notorious platform that facilitated the trading of stolen data on a global scale. In this article, we'll dive deep into how Leak Base operated, the efforts behind its seizure, the implications for cybercrime, and what the future holds for data security.
TL; DR
- Leak Base Takedown: A coordinated effort by the FBI and Europol dismantled Leak Base, arresting key members.
- Cybercrime Hub: Leak Base was a central hub for data trading, with over 142,000 users.
- Security Implications: The shutdown signals a strong stance against cybercrime, but challenges remain.
- Future Measures: Enhanced international cooperation is crucial for tackling cyber threats.
- Data Protection: Organizations must prioritize robust security practices to protect against leaks.
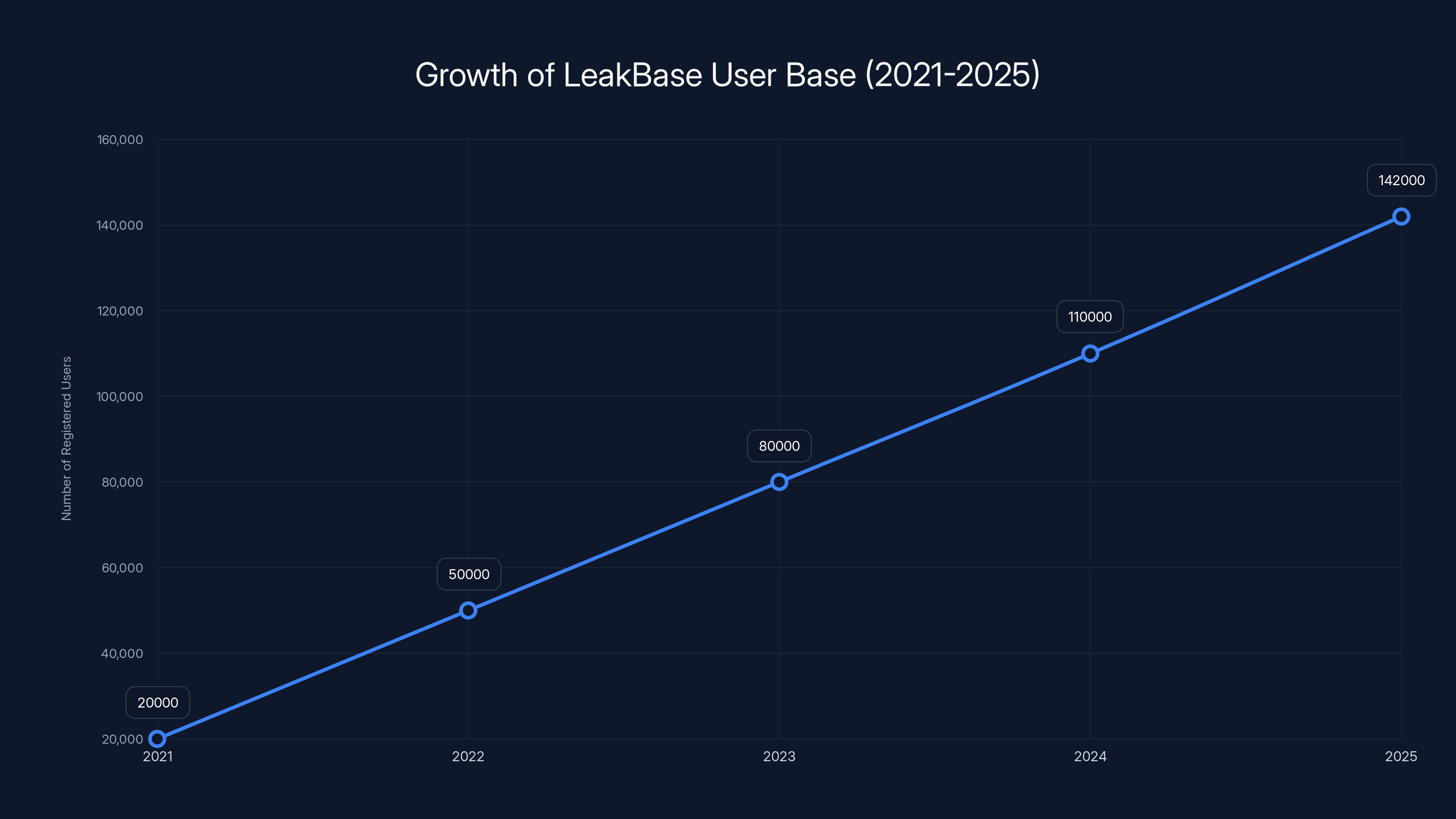
LeakBase experienced significant growth from 2021 to 2025, reaching over 142,000 users. Estimated data based on growth trends.
Understanding Leak Base
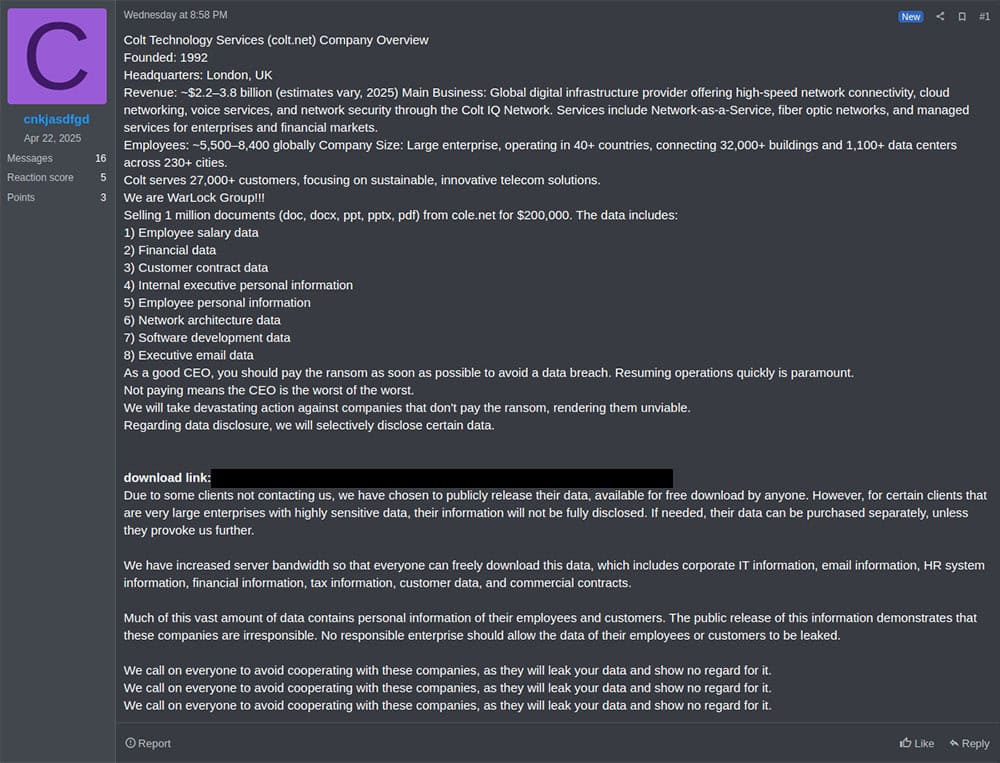
Leak Base emerged in 2021 as a haven for cybercriminals. It quickly gained notoriety for its vast repository of stolen data, including personal information, credit card details, and corporate secrets. By 2025, it had over 142,000 registered users, making it a significant player in the cybercrime ecosystem.
How Leak Base Operated
Leak Base functioned as a marketplace where users could buy and sell stolen data. Transactions were often conducted using cryptocurrencies to maintain anonymity. The forum was structured to facilitate easy access to data sets, with categories for different types of data, such as financial information, personal identification, and intellectual property.
Key Features and Tools
- Anonymous Transactions: Cryptocurrencies like Bitcoin were used to conceal identities.
- Robust Security: Leak Base employed encryption to protect its operations from law enforcement.
- Community Engagement: Users could share tips on exploiting data and avoiding detection.
Real-World Use Case
Consider a scenario where a small business falls victim to a data breach. The stolen customer data could end up on Leak Base, where it is sold to the highest bidder, leading to identity theft and financial loss for affected individuals.

AI and blockchain are projected to have the highest impact on future data security, emphasizing the importance of technological advancement in cybersecurity. (Estimated data)
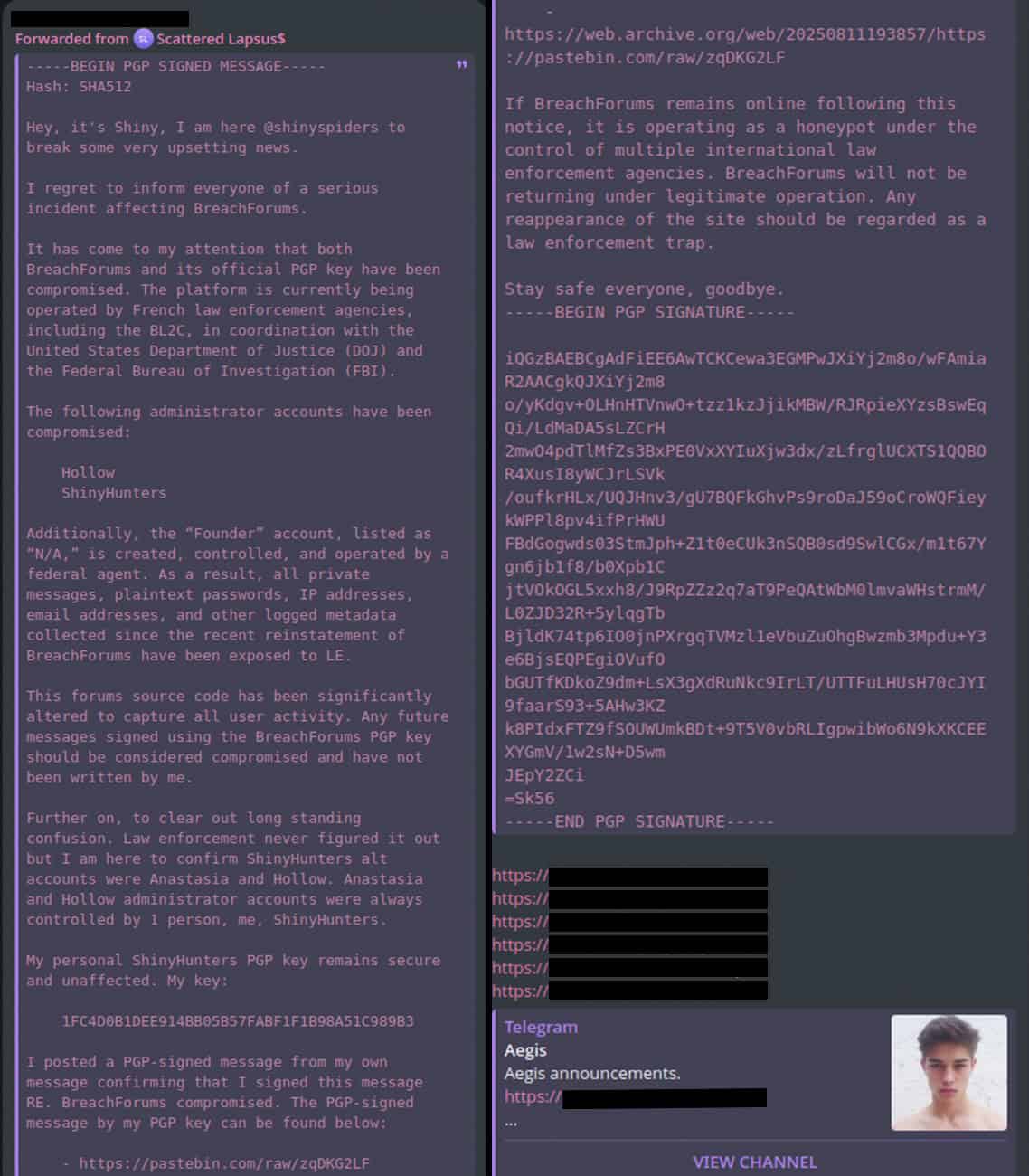
The Operation to Dismantle Leak Base
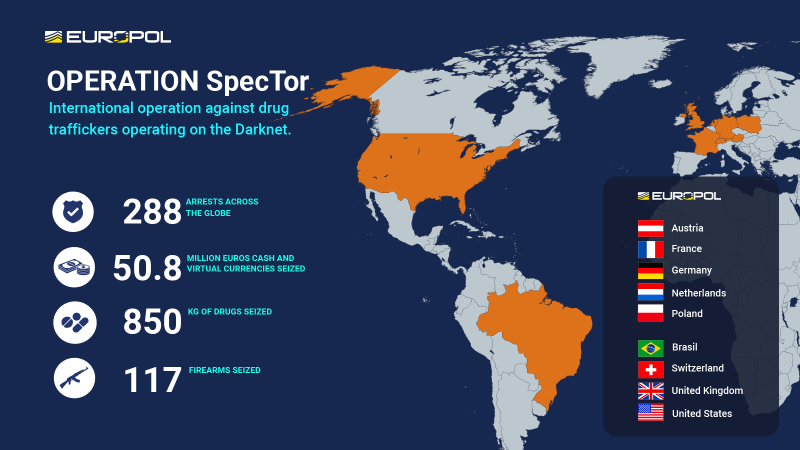
The takedown of Leak Base was a result of meticulous planning and international collaboration. The operation involved multiple law enforcement agencies, including the FBI, Europol, and local police forces.
Steps Involved
- Intelligence Gathering: Authorities monitored Leak Base activities to identify key players and gather evidence.
- Coordinated Raids: Simultaneous raids were conducted in multiple countries to apprehend suspects and seize assets.
- Domain Seizure: The Leak Base domain was taken offline, disrupting its operations.
Challenges Faced
- Anonymity of Users: The use of encryption and cryptocurrencies made it difficult to track participants.
- Legal Hurdles: Different jurisdictions have varying laws regarding cybercrime, complicating coordination.
- Rapid Technological Changes: Cybercriminals quickly adapt to new security measures.
Implications for Cybercrime
The shutdown of Leak Base sends a strong message to cybercriminals: law enforcement is determined to dismantle illegal operations. However, the fight against cybercrime is far from over.
Ongoing Threats
- Emergence of New Platforms: As one forum is shut down, others will inevitably arise to fill the void.
- Increased Sophistication: Cybercriminals are continually developing more sophisticated methods to evade detection.
- Global Reach: The international nature of cybercrime requires enhanced cooperation among countries.
Future Predictions
- Improved Collaboration: Expect more joint operations between countries to tackle cyber threats.
- Advanced Technologies: Law enforcement will leverage AI and machine learning to predict and prevent cyber attacks.


Encryption and Intrusion Detection Systems (IDS) are among the most effective measures for protecting against data leaks. Estimated data.
Protecting Against Data Leaks
Organizations must take proactive measures to safeguard their data. Here are some best practices:
Implement Robust Security Protocols
- Encryption: Use strong encryption methods to protect sensitive data.
- Access Controls: Limit access to data based on roles and responsibilities.
- Regular Audits: Conduct frequent security audits to identify vulnerabilities.
Educate Employees
- Training Programs: Regularly train employees on data security best practices.
- Phishing Simulations: Conduct simulations to raise awareness about phishing attacks.
Utilize Advanced Tools
- Intrusion Detection Systems (IDS): Implement IDS to monitor and alert on suspicious activity.
- Data Loss Prevention (DLP) Solutions: Use DLP solutions to prevent unauthorized data transfers.
Common Pitfalls and Solutions
Organizations often encounter challenges when implementing data security measures. Here are some common pitfalls and how to overcome them:
Pitfall: Insufficient Budget
Many organizations underestimate the budget required for effective data security.
Solution: Prioritize security spending based on risk assessment and allocate resources accordingly.
Pitfall: Overlooking Insider Threats
Insider threats are a significant risk factor that is often overlooked.
Solution: Implement monitoring systems to detect unusual employee behavior and restrict access to sensitive data.

The Role of Governments and Organizations
Governments and organizations must collaborate to enhance cybersecurity measures. Here's how they can contribute:
Government Initiatives
- Legislation: Enact laws that promote data protection and penalize cybercriminals.
- Public Awareness Campaigns: Educate the public about the importance of cybersecurity.
Organizational Responsibilities
- Adopt Best Practices: Implement industry-standard security practices.
- Collaboration: Share threat intelligence with other organizations to enhance collective security.

Future Trends in Data Security
As technology evolves, so do the threats and solutions in data security. Here are some trends to watch:
Artificial Intelligence and Machine Learning
AI and machine learning will play a crucial role in detecting and mitigating cyber threats in real-time.
- Predictive Analytics: Use AI to predict potential security breaches before they occur.
- Automated Response: Implement automated systems that respond to threats without human intervention.
Blockchain Technology
Blockchain offers a decentralized approach to data security, providing transparency and immutability.
- Secure Transactions: Use blockchain to secure financial transactions and protect against fraud.
- Identity Verification: Implement blockchain-based identity verification to enhance authentication processes.
Case Study: A Successful Defense Against a Data Leak
Scenario: A multinational corporation faced a potential data leak due to a phishing attack.
Steps Taken
- Immediate Response: The security team quickly identified the breach and isolated affected systems.
- Forensic Analysis: Conducted a forensic analysis to determine the extent of the breach.
- Public Disclosure: Communicated transparently with stakeholders about the incident.
- Security Enhancements: Implemented additional security measures to prevent future breaches.
Results
The corporation successfully mitigated the impact of the data leak and restored stakeholder trust through transparency and swift action.

Conclusion
The takedown of Leak Base is a significant victory in the fight against cybercrime. However, it also highlights the ongoing challenges and the need for continuous vigilance. By adopting robust security practices and fostering international cooperation, we can build a more secure digital landscape.

FAQ
What is Leak Base?
Leak Base was a notorious data leak forum where users traded stolen data. It was shut down by the FBI and Europol.
How did Leak Base operate?
Leak Base operated as a marketplace for stolen data, utilizing cryptocurrencies for anonymous transactions.
What are the implications of Leak Base's shutdown?
The shutdown demonstrates law enforcement's commitment to combating cybercrime but also highlights the need for ongoing vigilance.
How can organizations protect against data leaks?
Organizations should implement robust security protocols, educate employees, and utilize advanced security tools.
What role do governments play in data security?
Governments can enact legislation, raise public awareness, and collaborate with organizations to enhance cybersecurity measures.
What are future trends in data security?
Future trends include the use of AI and machine learning for threat detection and the implementation of blockchain technology for secure transactions.
Key Takeaways
- The coordinated effort by the FBI and Europol led to the successful dismantling of the LeakBase forum.
- LeakBase served as a major hub for illegal data trading, highlighting the global scale of cybercrime.
- Enhanced international cooperation is crucial for addressing the complex challenges of cyber threats.
- Organizations must prioritize robust security practices to protect against data leaks.
- The use of advanced technologies like AI and blockchain will play a key role in future cybersecurity measures.
Related Articles
- The Rise and Fall of Tycoon 2FA: Lessons from a Global Phishing Takedown [2025]
- Massive Data Breach on French Medical Platform: Lessons and Future Implications [2025]
- Understanding X Money: The Future of Payments with William Shatner and Elon Musk [2025]
- LexisNexis Data Breach: What You Need to Know [2025]
- Understanding Computer Vulnerabilities to TEMPEST Attacks [2025]
- The Rise of Government Hacking Tools in Cybercrime: A Deep Dive [2025]
![The Fall of LeakBase: Inside the Seizure of a Major Data Leak Forum [2025]](https://tryrunable.com/blog/the-fall-of-leakbase-inside-the-seizure-of-a-major-data-leak/image-1-1772708668406.jpg)



