Understanding the Rise of SIM Farms: A Deep Dive into Global Network Exploitation [2025]
The digital landscape is ever-evolving, bringing with it innovations that redefine how we connect and communicate. However, alongside these advancements, new challenges arise. One such challenge is the proliferation of SIM farms—a clandestine operation that has increasingly threatened mobile networks globally.
TL; DR
- SIM farms exploit mobile networks to bypass verification systems, posing significant security threats.
- 94 deployments connected to 35 mobile carriers highlight the scale of this issue.
- Proxy Smart software is a key component enabling remote infrastructure access.
- Future trends suggest further sophistication in SIM farm technologies.
- Mitigation strategies include robust authentication and network monitoring.
The control server is the most critical component, requiring the highest focus, followed by SIM management software and network interface. (Estimated data)
What Are SIM Farms?
SIM farms are essentially operations that utilize multiple SIM cards in a coordinated manner to exploit mobile networks. These setups enable activities like bypassing phone-based verifications, bulk messaging, and other fraudulent actions. The SIM cards, often numbering in the thousands, are installed in a single location or distributed across several locations but controlled centrally.
How Do SIM Farms Operate?
The operation of a SIM farm involves the use of hardware and software to automate and manage the bulk processing of SIM cards. Typically, a SIM farm will deploy devices that can hold hundreds of SIM cards. These devices connect to a computer network, automating the process of sending and receiving SMS messages or making calls.
Key Components of a SIM Farm:
- SIM Box Devices: Physical hardware that houses multiple SIM cards.
- Automation Software: Manages the operation of these SIM cards.
- Network Infrastructure: Ensures connectivity and scalability.
Real-World Use Cases
One illustrative example of SIM farm usage is in bypassing two-factor authentication (2FA) systems. By using multiple SIM cards, fraudsters can intercept verification codes, allowing unauthorized access to user accounts.
Use Case: An attacker sets up a SIM farm to receive 2FA codes sent to compromised accounts, facilitating unauthorized transactions and account takeovers.

SIM farms contribute significantly to telecom fraud, accounting for an estimated
The Global Impact of SIM Farms
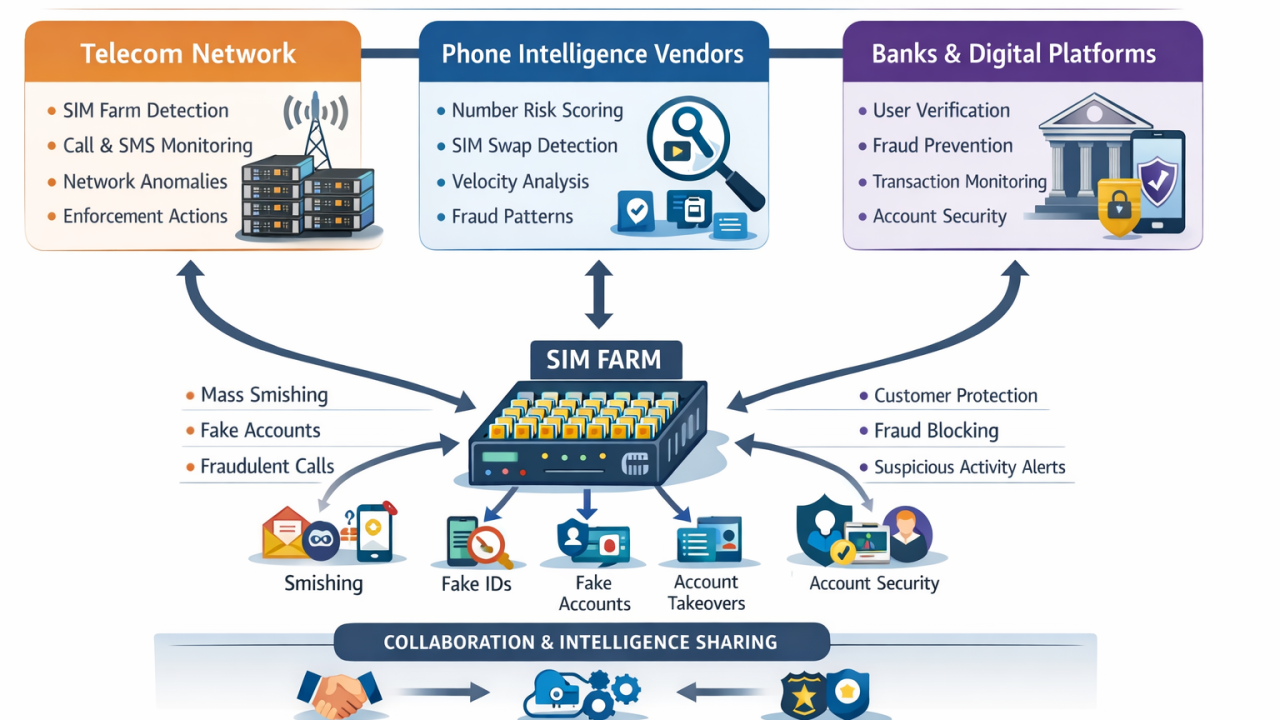
The discovery of 94 SIM farm deployments linked to 35 mobile carriers across major networks in the UK and US highlights the global scale of this issue. These farms, often connected through shared software like Proxy Smart, can undermine security across borders.
Economic and Security Implications
SIM farms impact both economic and security landscapes. Economically, they contribute to revenue loss for telecom companies due to fraudulent activities. From a security perspective, they pose a risk to user data integrity and privacy.
DID YOU KNOW: The telecommunications industry loses an estimated $25 billion annually to fraud, with SIM farms contributing significantly to this figure.
Technical Details and Best Practices
Understanding the technical aspects of SIM farms is crucial for developing effective countermeasures. Below, we delve into the technicalities and best practices for managing and mitigating these threats.
SIM Farm Architecture
A typical SIM farm architecture involves a centralized control system that manages SIM cards across multiple locations. This system relies on robust software capable of operating these cards efficiently and securely.
Components:
- Control Server: Manages operations and data flow.
- SIM Management Software: Automates tasks and optimizes performance.
- Network Interface: Facilitates communication across networks.
Implementation Guides
For network operators and security professionals, implementing robust security measures is crucial. Here are some implementation strategies:
- Enhanced Authentication Protocols: Utilize multi-factor authentication (MFA) beyond SMS-based systems.
- Network Monitoring Tools: Deploy advanced monitoring tools to detect unusual patterns indicative of SIM farm activity.
- Regular Audits: Conduct frequent audits of network traffic to identify potential vulnerabilities.
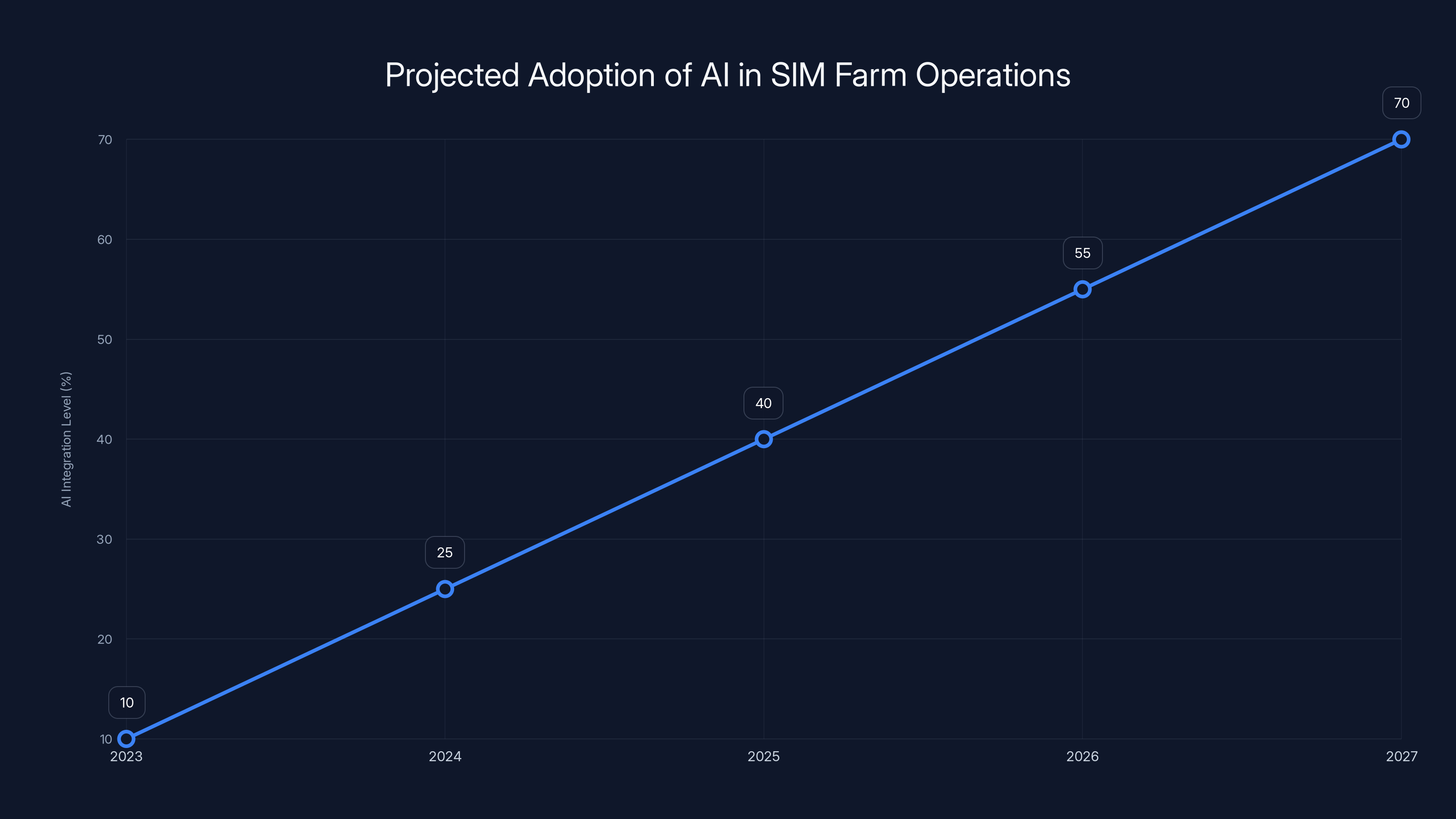
The integration of AI in SIM farm operations is projected to increase significantly, reaching 70% by 2027. Estimated data highlights the growing importance of AI in enhancing efficiency and stealth.
Common Pitfalls and Solutions
While addressing SIM farm threats, organizations often encounter several challenges. Here are common pitfalls and their solutions:
Pitfall 1: Over-Reliance on SMS-Based Verification
Solution: Transition to app-based authentication methods that offer stronger security and better user experience.
Pitfall 2: Lack of Comprehensive Monitoring
Solution: Deploy comprehensive network monitoring systems that can identify and mitigate threats proactively.
Pitfall 3: Inadequate Employee Training
Solution: Regularly train staff on recognizing and responding to potential SIM farm activities.
Future Trends and Recommendations
As technology evolves, so too will the tactics employed by those operating SIM farms. Anticipating these changes is vital for staying ahead of the curve.
Emerging Technologies
The integration of AI and machine learning in SIM farm operations is likely to increase. These technologies can enhance the efficiency and stealth of SIM farm activities.
Recommendation: Stay informed about technological advancements and consider adopting AI-based security tools to counteract evolving threats.
Regulatory Measures
Governments and regulatory bodies are increasingly focusing on telecommunications security. New regulations could enforce stricter controls on SIM card issuance and management.
Recommendation: Collaborate with regulatory bodies to ensure compliance and contribute to shaping effective security policies.
Conclusion
SIM farms represent a significant threat to global telecommunications networks. By understanding their operations and impacts, stakeholders can better prepare and implement effective countermeasures. Continuous vigilance, technology adoption, and regulatory compliance are key to mitigating these threats.
Use Case: Automate your network security audits with AI to stay ahead of emerging threats.
Try Runable For FreeFAQ
What is a SIM farm?
A SIM farm is a setup that uses multiple SIM cards to exploit mobile networks for activities like bypassing verification systems and bulk messaging.
How do SIM farms impact mobile networks?
They pose security risks by enabling unauthorized access and contribute to financial losses for telecom companies due to fraud.
What are some mitigation strategies for SIM farms?
Strategies include enhanced authentication protocols, advanced network monitoring tools, and regular security audits.
What future trends are expected in SIM farm operations?
AI and machine learning are likely to enhance the efficiency of SIM farm operations, necessitating advanced security measures.
How can regulatory measures help combat SIM farm threats?
Stricter controls on SIM card issuance and management can help reduce vulnerabilities exploited by SIM farms.
Key Takeaways
- SIM farms exploit mobile networks, posing significant security threats.
- 94 deployments connected to 35 mobile carriers highlight the scale of this issue.
- ProxySmart software enables remote infrastructure access, complicating detection.
- Future trends suggest further sophistication in SIM farm technologies.
- Mitigation strategies include robust authentication and network monitoring.
- AI and machine learning will likely play a role in future SIM farm operations.
- Regulatory measures can enforce stricter controls to mitigate vulnerabilities.
Related Articles
- AI Agents: The Hidden Gatekeepers Giving Hackers Full System Access [2025]
- AI Models: The New Generation of Scammers [2025]
- Understanding New York's Ban on Insider Trading in Prediction Markets [2025]
- Ransomware and the Felony Murder Law: A New Legal Frontier [2025]
- Why B2B Stocks Are Plummeting in 2026: The Software's Inadequacy for the AI Era [2026]
- Why Alienware's $350 OLED Monitor is a Game Changer [2025]
![Understanding the Rise of SIM Farms: A Deep Dive into Global Network Exploitation [2025]](https://tryrunable.com/blog/understanding-the-rise-of-sim-farms-a-deep-dive-into-global-/image-1-1776893644115.jpg)



