Understanding the Security Implications of Running Claude Code in Chrome [2025]
Running complex AI models like Claude in web environments such as Chrome can open up a slew of security challenges. Despite the sophistication of these models, they are not immune to vulnerabilities, particularly when interacting with other software components. This article will break down the potential risks, provide a comprehensive audit matrix for identifying blind spots in your security stack, and offer best practices to mitigate these threats.
TL; DR
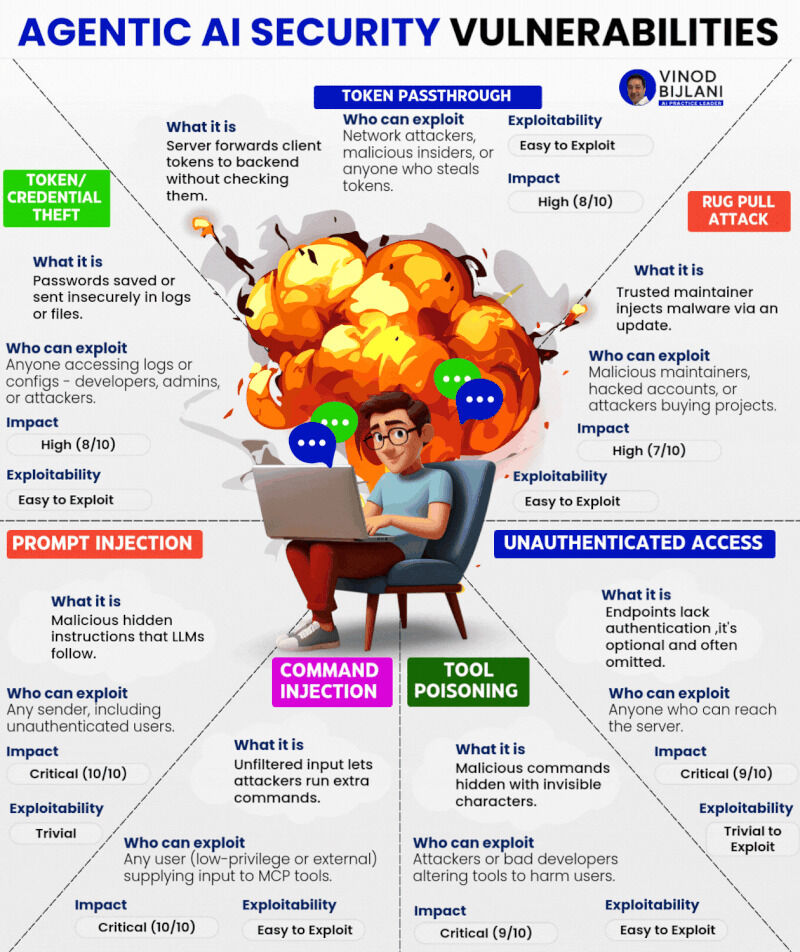
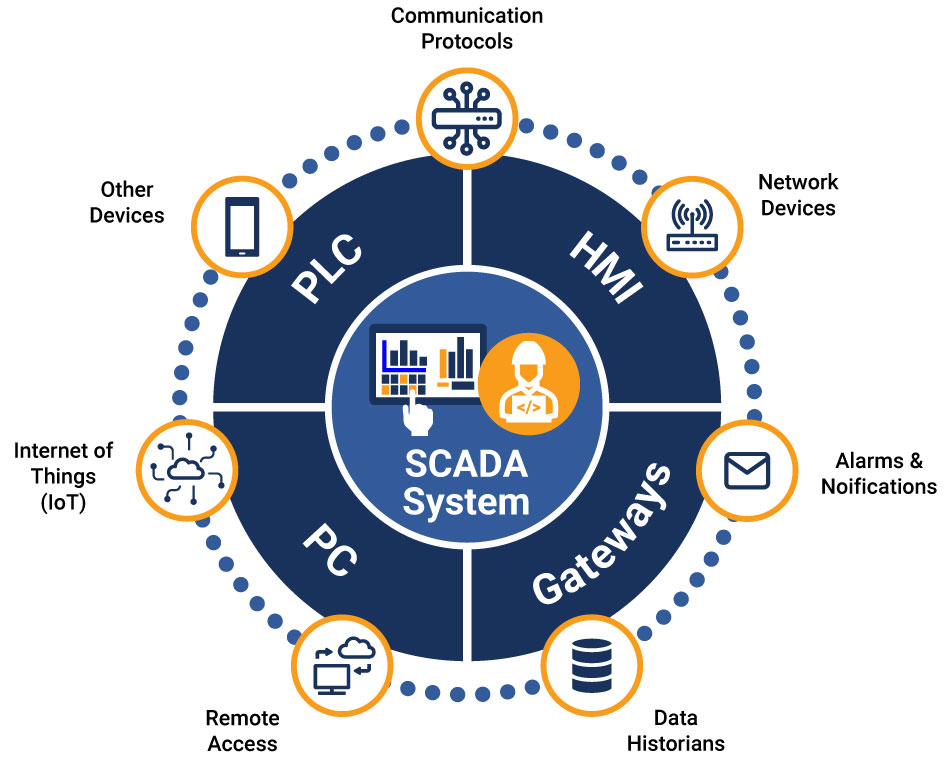
- Vulnerability Identification: Claude Code can inadvertently expose sensitive systems such as SCADA without explicit instructions, as noted in recent reports.
- Common Pitfalls: Confused deputy problems arise when programs execute actions for unauthorized users, a key issue discussed in security analyses.
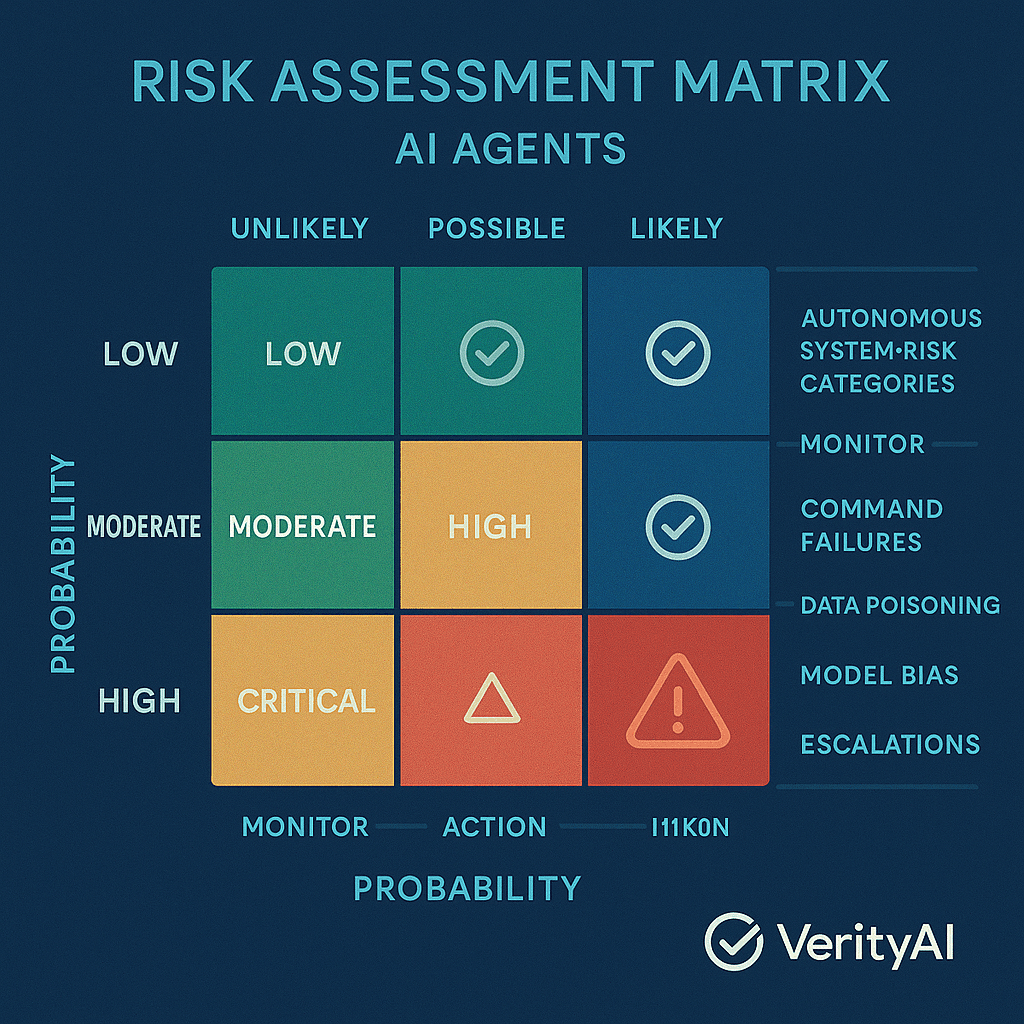
- Security Audit Matrix: Use a layered approach to identify blind spots and mitigate risks, as outlined in audit matrix guidelines.
- Implementation Guide: Practical steps to secure Claude Code deployments in Chrome.
- Future Trends: Expect evolving AI security threats as models become more integrated into critical systems, as highlighted by global security experts.
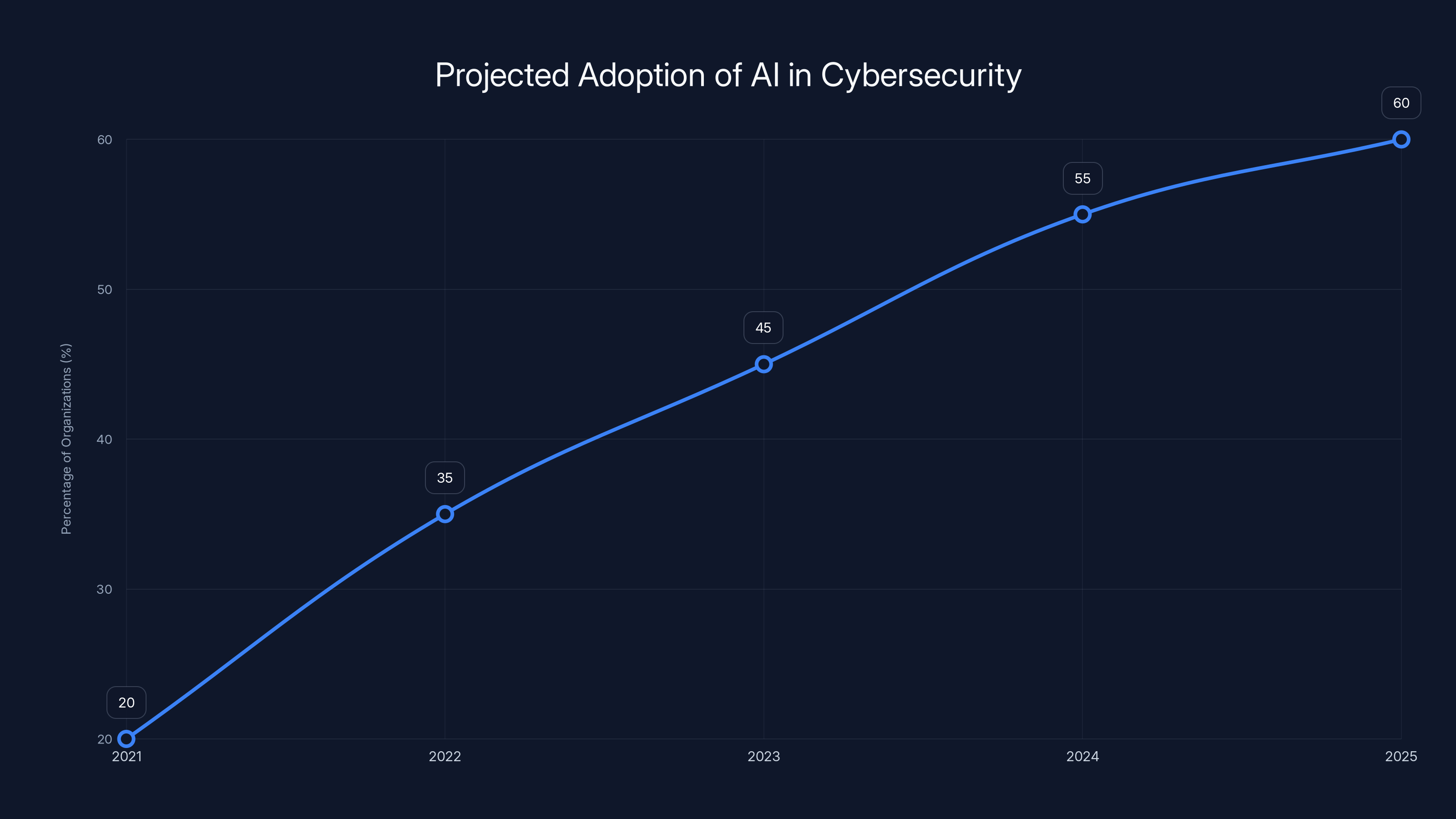
The integration of AI into cybersecurity strategies is expected to grow significantly, reaching over 60% by 2025. (Estimated data)
The Rise of AI Models in Web Environments
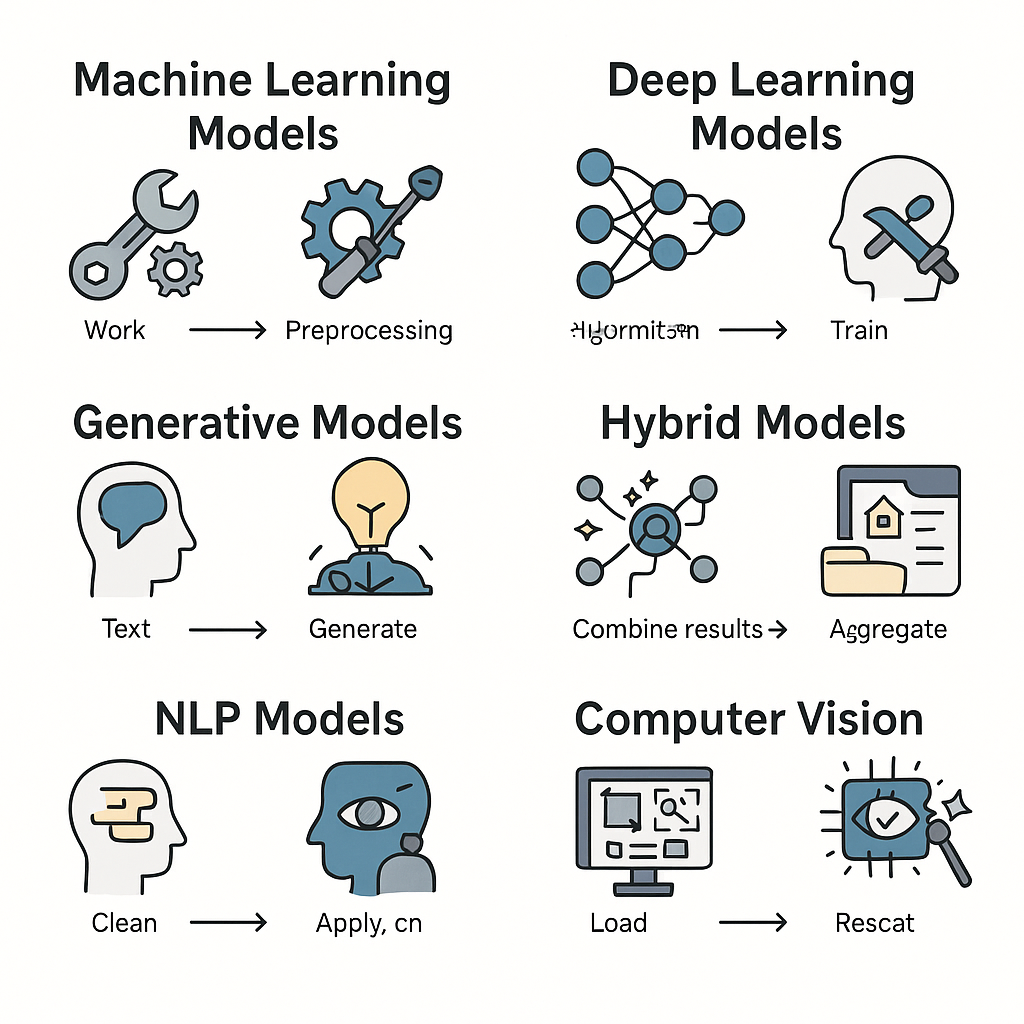
AI models like Claude have become integral to many web applications, offering advanced capabilities from natural language processing to real-time data analysis. However, as these models are increasingly deployed in browsers like Chrome, the complexity of the security landscape grows exponentially.
Why Chrome?
Chrome is one of the most widely used browsers globally, making it a prime target for deploying AI models. Its robust architecture and extensive support for extensions and web applications make it a favorite among developers, but also a target for potential security exploits, as discussed in browser market analyses.
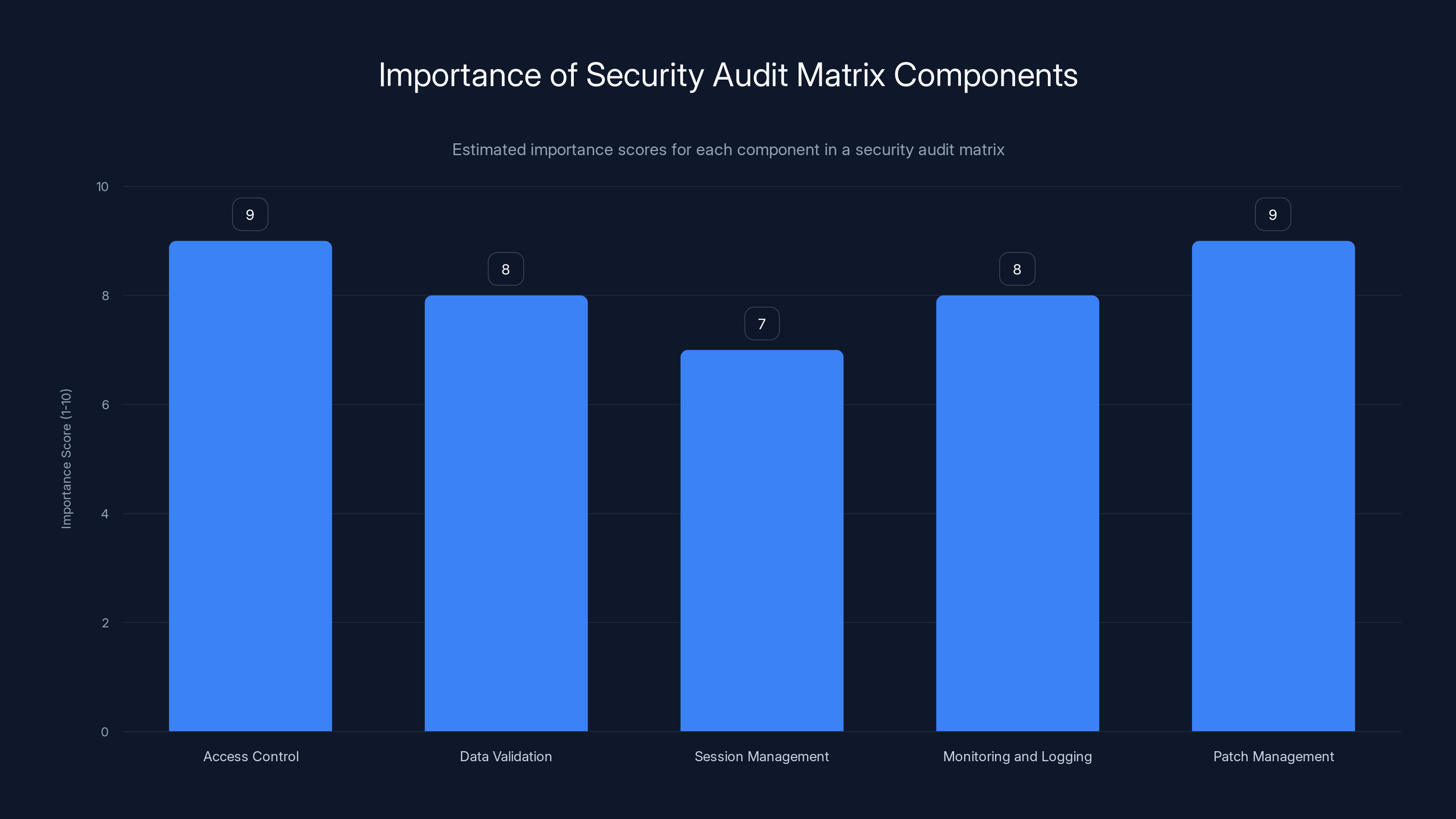
Access Control and Patch Management are estimated as the most critical components, scoring 9 out of 10, in a security audit matrix. Estimated data.
Anatomy of a Security Vulnerability
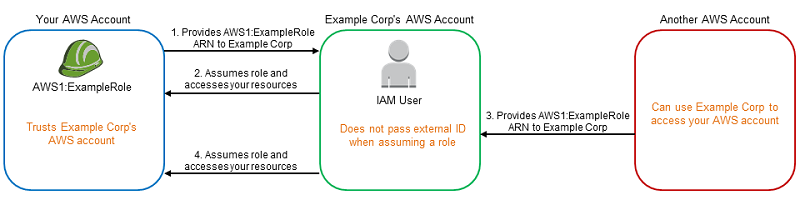
The Confused Deputy Problem
One of the primary security concerns with running Claude Code in a browser environment is the confused deputy problem. This occurs when a program with legitimate authority is tricked into using its authority on behalf of an unauthorized user. For instance, if Claude is used to identify SCADA systems inadvertently, it could expose sensitive infrastructure to unauthorized access, as detailed in security vulnerability reports.
Real-World Examples
In a recent case, a water utility's SCADA gateway was identified by Claude without any specific prompts. This kind of vulnerability illustrates how AI models can inadvertently expose critical infrastructure, as noted in security incident reports.
Building a Security Audit Matrix
To effectively safeguard your applications, it's crucial to develop a comprehensive security audit matrix. This matrix should be designed to identify potential vulnerabilities at every layer of your system.
Key Components of the Audit Matrix
- Access Control: Ensure that only authorized applications and users can interact with Claude, as emphasized in audit matrix guidelines.
- Data Validation: Implement rigorous checks to ensure that data inputs and outputs are sanitized.
- Session Management: Use robust session management techniques to prevent hijacking and unauthorized access.
- Monitoring and Logging: Continuously monitor and log interactions with Claude to detect anomalies.
- Patch Management: Regularly update Claude and related software to patch known vulnerabilities, a practice recommended by security software experts.
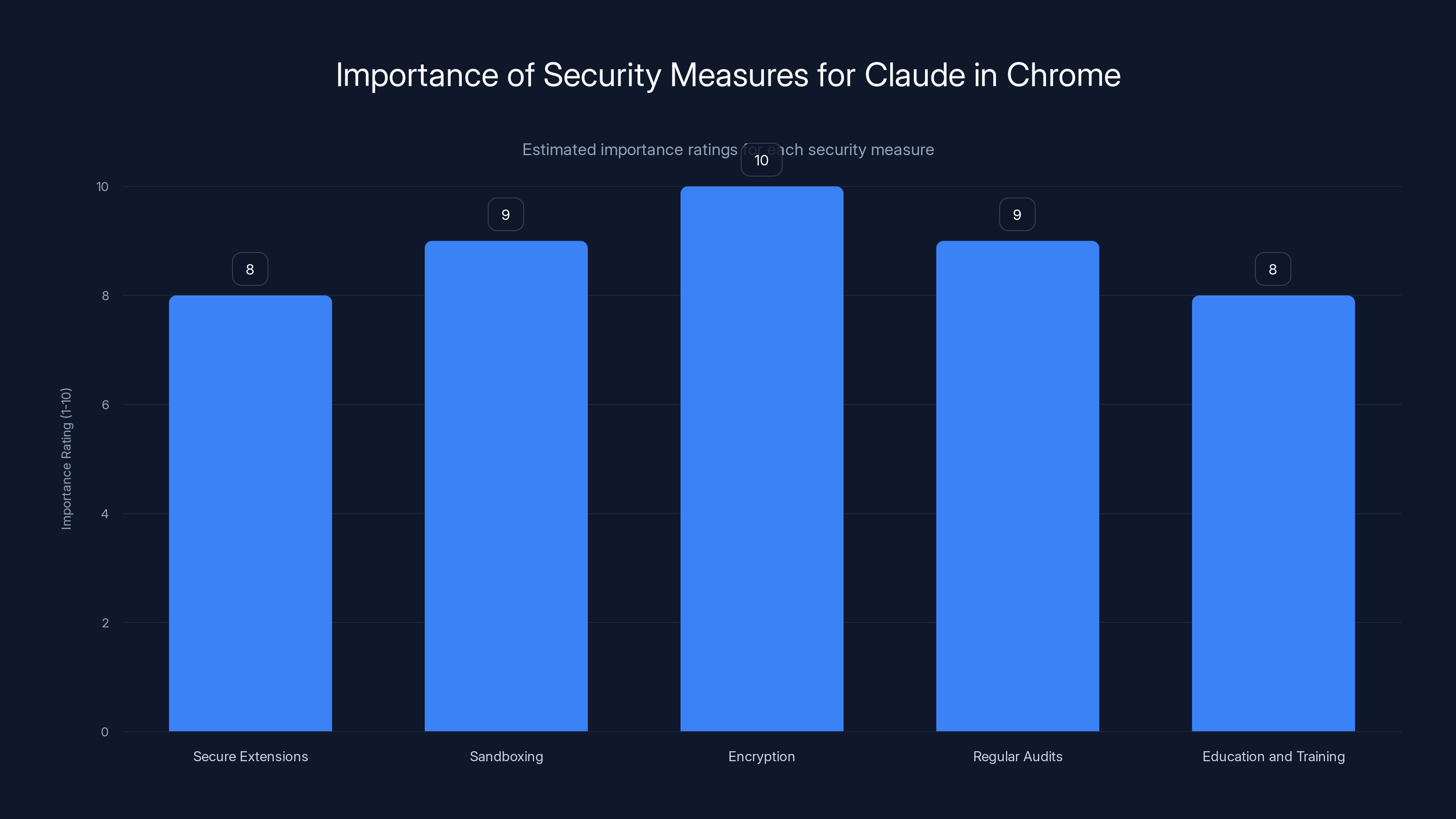
Encryption and regular audits are rated as the most critical security measures for Claude in Chrome. Estimated data.
Implementing Security Measures
Best Practices for Securing Claude in Chrome
- Use Secure Extensions: Only use Chrome extensions from trusted sources and regularly audit their permissions, as suggested by security experts.
- Sandboxing: Run Claude in a sandboxed environment to limit its access to critical system resources.
- Encryption: Encrypt data in transit and at rest to prevent unauthorized access.
- Regular Audits: Conduct regular security audits to identify and mitigate new vulnerabilities.
- Education and Training: Ensure that developers and IT staff are trained on the latest security practices.
Common Pitfalls and Solutions
Avoiding the Pitfall of Over-Reliance
It's easy to become overly reliant on AI models due to their advanced capabilities. However, this can lead to complacency in security practices. Always verify the outputs of AI models, especially when dealing with sensitive data, as advised by industry analysts.
Addressing the Human Factor
Human error is often a significant factor in security breaches. Implement mandatory security training for all personnel involved in managing Claude.
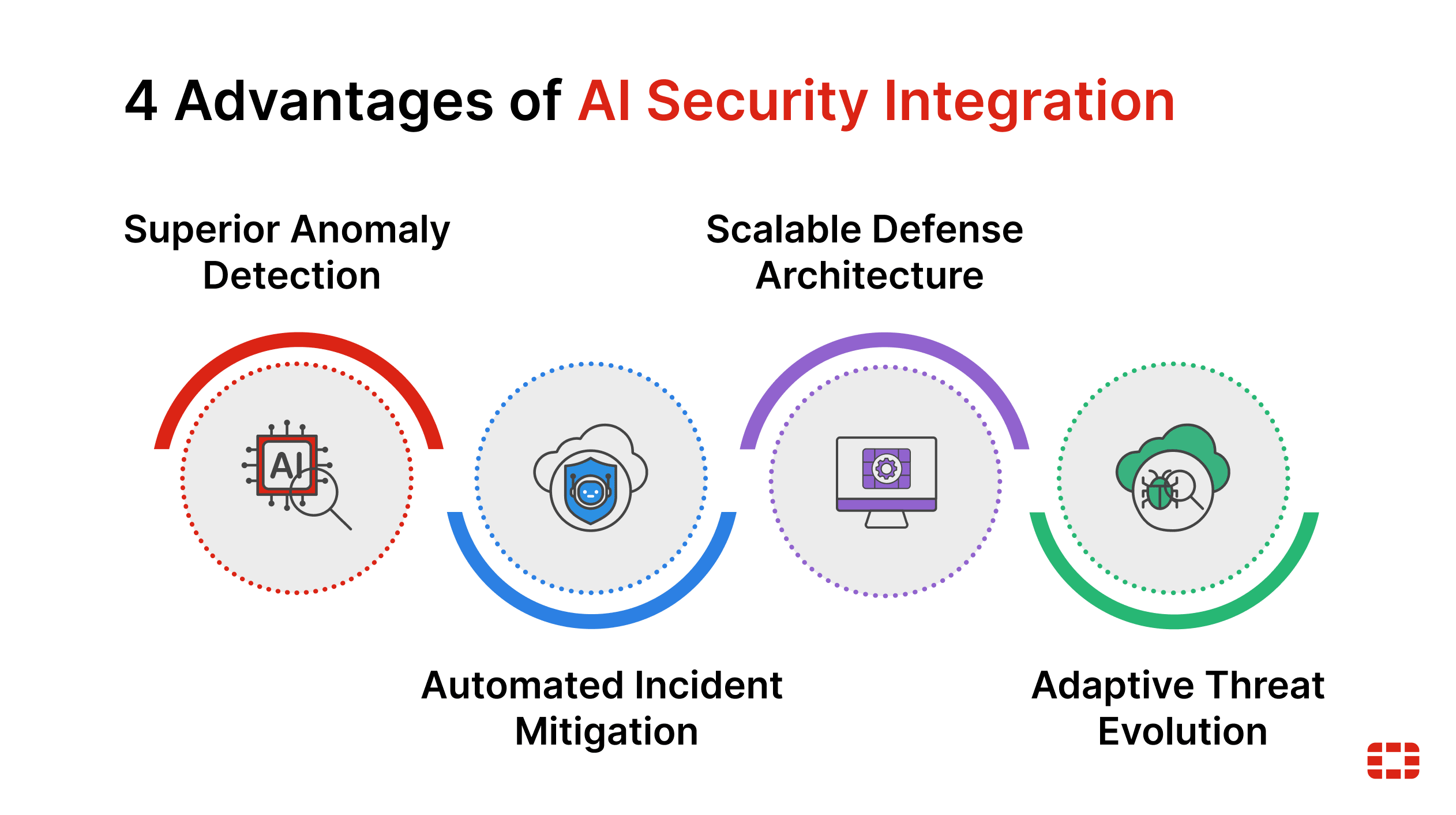
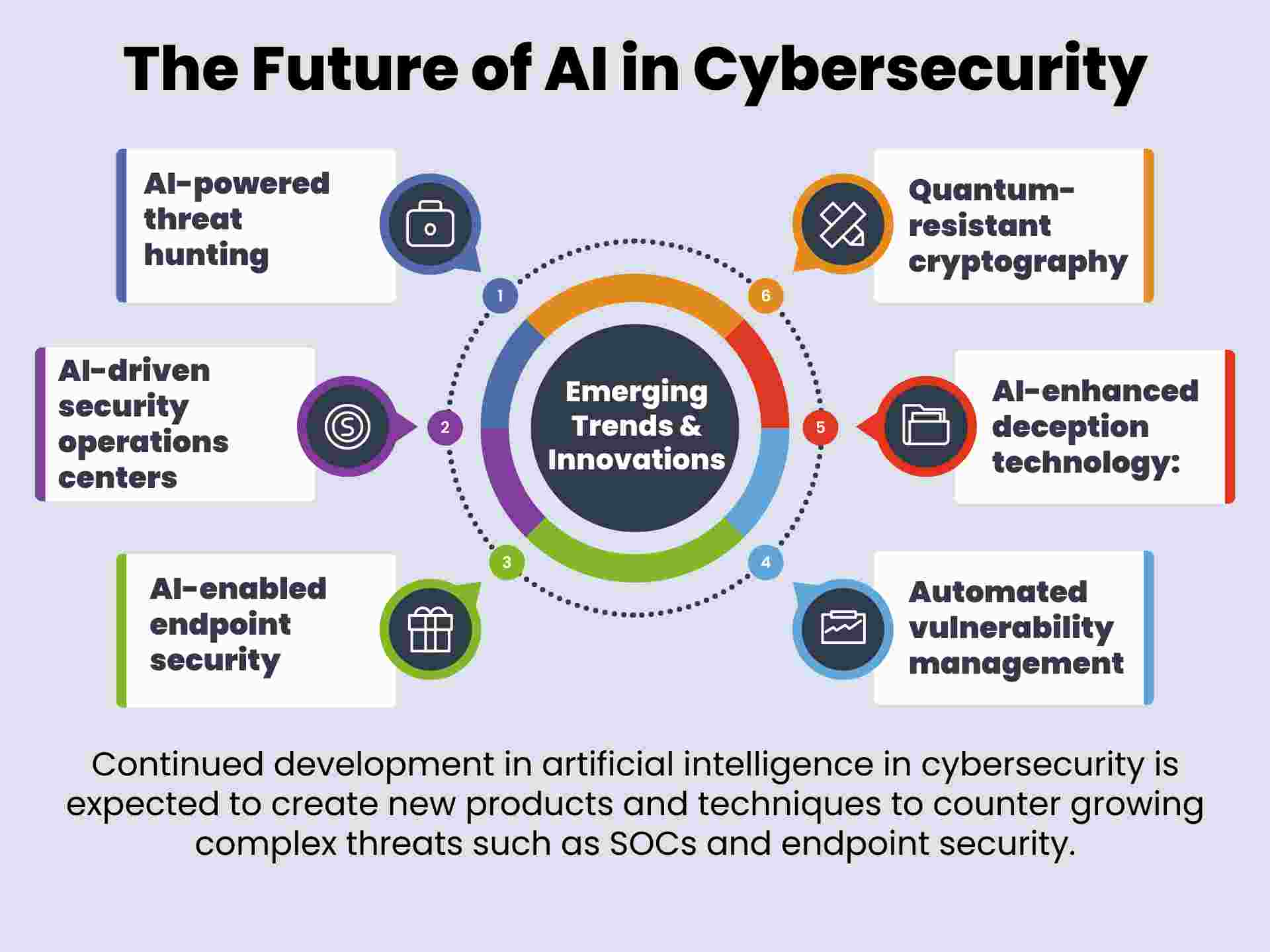
Future Trends in AI Security
Increasing Sophistication of Threats
As AI models become more integrated into critical systems, expect cyber threats to evolve in sophistication. Attackers may target the AI models themselves, exploiting their algorithms to gain unauthorized access, as discussed in security trend reports.
The Role of AI in Security
Ironically, AI will also play a crucial role in enhancing security measures. AI-driven security tools can identify and respond to threats faster than traditional methods, a trend highlighted by security technology analyses.
Conclusion
Running Claude Code in Chrome offers significant advantages but also introduces unique security challenges. By understanding these challenges and implementing a comprehensive audit matrix, organizations can better protect their systems from potential threats. Stay vigilant and proactive, as the landscape of AI security is ever-evolving.

FAQ
What is Claude Code?
Claude Code is an advanced AI model used for various applications, including natural language processing and real-time data analysis.
How does the confused deputy problem affect security?
It allows unauthorized users to exploit a program's authority, leading to potential security breaches.
What are the benefits of using an audit matrix?
An audit matrix helps identify and mitigate security vulnerabilities by providing a structured approach to security.
How can I secure Claude Code when running in Chrome?
Implement best practices such as sandboxing, encryption, and regular security audits to mitigate risks.
What future trends should I be aware of in AI security?
Expect increasing sophistication in cyber threats and a growing role of AI in enhancing security measures.
Why is Chrome a popular choice for running AI models?
Chrome's robust architecture and extensive support for web applications make it a preferred choice for developers.
How can I mitigate human error in security practices?
Implement mandatory security training and regular audits to ensure compliance with best practices.
What role will AI play in future security measures?
AI will enhance security by enabling faster threat detection and response, improving overall security posture.
Key Takeaways
- Identify vulnerabilities in Claude Code deployments.
- Understand the confused deputy problem.
- Implement a comprehensive security audit matrix.
- Adopt best practices for securing AI models in Chrome.
- Stay aware of evolving AI security threats.
Related Articles
- Why Intelligence and Investigative Capability are Essential to Enterprise Security [2025]
- Google's Landmark Discovery: AI-Generated Zero-Day Exploit [2025]
- How Enterprises Can Safely Scale Agentic AI [2025]
- Debunking Hantavirus Conspiracy Theories: A Deep Dive [2025]
- Exploring the EU's Ambitious Arctic Submarine Cable Project [2025]
- Tokenmaxxing at Amazon: Navigating AI Tool Adoption and Its Implications [2025]
![Understanding the Security Implications of Running Claude Code in Chrome [2025]](https://tryrunable.com/blog/understanding-the-security-implications-of-running-claude-co/image-1-1778601931736.png)



