QR Code Phishing Tactics Surge: Navigating the 2026 Cybersecurity Landscape
The rise of QR code phishing, also known as quishing, is a stark reminder of how cyber threats continuously evolve. With a 146% increase in attacks during the first quarter of 2026, this tactic has caught the attention of cybersecurity experts worldwide. Microsoft reported detecting 8.3 billion phishing threats in Q1 alone, highlighting the sophistication and scale of these attacks.
TL; DR
- Phishing Surge: QR code phishing attacks rose by 146% in early 2026.
- Microsoft's Report: Detected 8.3 billion phishing threats in Q1 2026.
- Changing Tactics: Attackers are innovating to bypass traditional security measures.
- Best Practices: Implement multi-layered security strategies to mitigate risks.
- Future Outlook: Expect more sophisticated phishing tactics leveraging AI and machine learning.
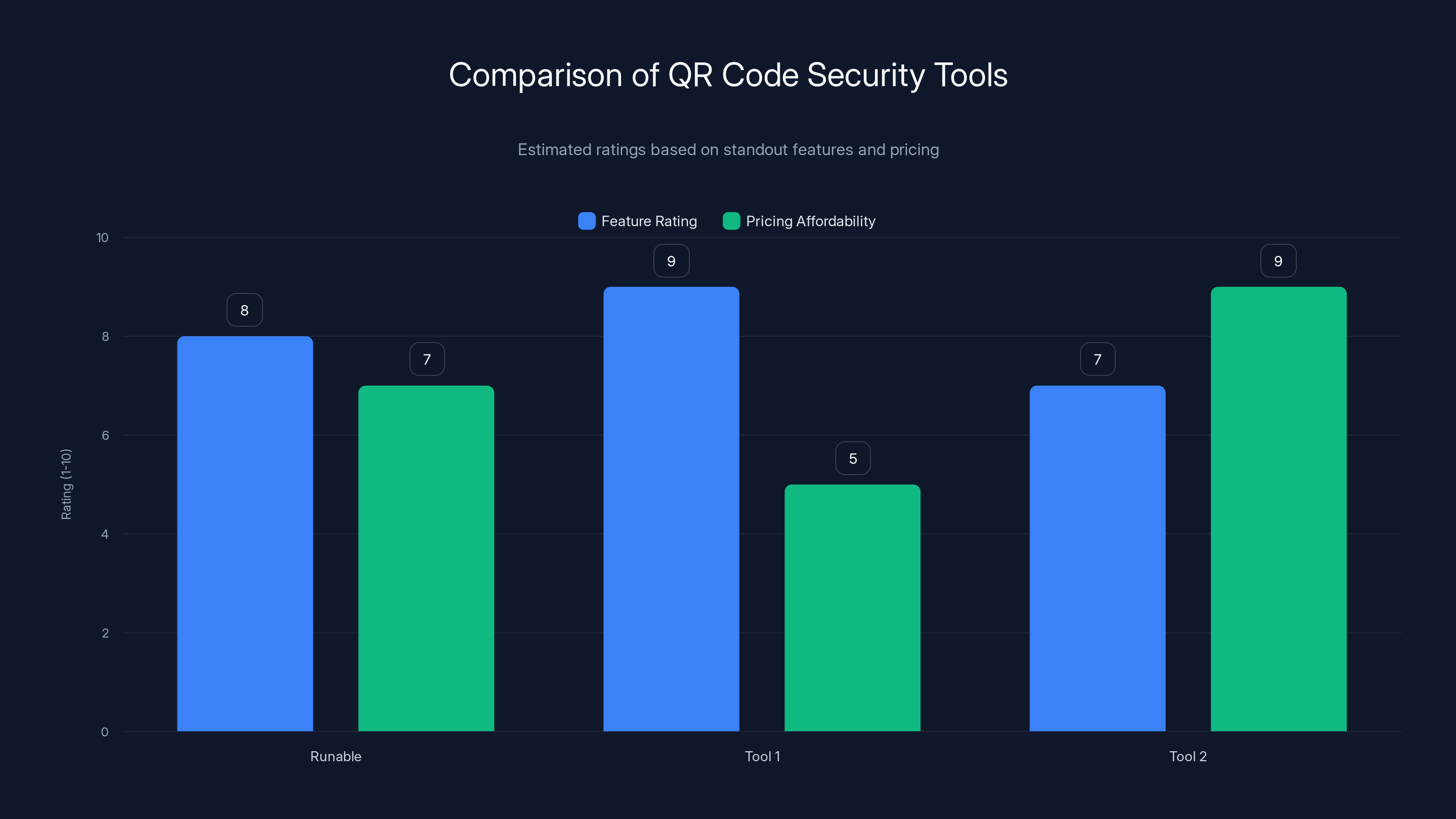
Tool 1 scores highest in feature rating due to real-time threat detection, while Tool 2 offers the best pricing affordability. (Estimated data)
Understanding QR Code Phishing
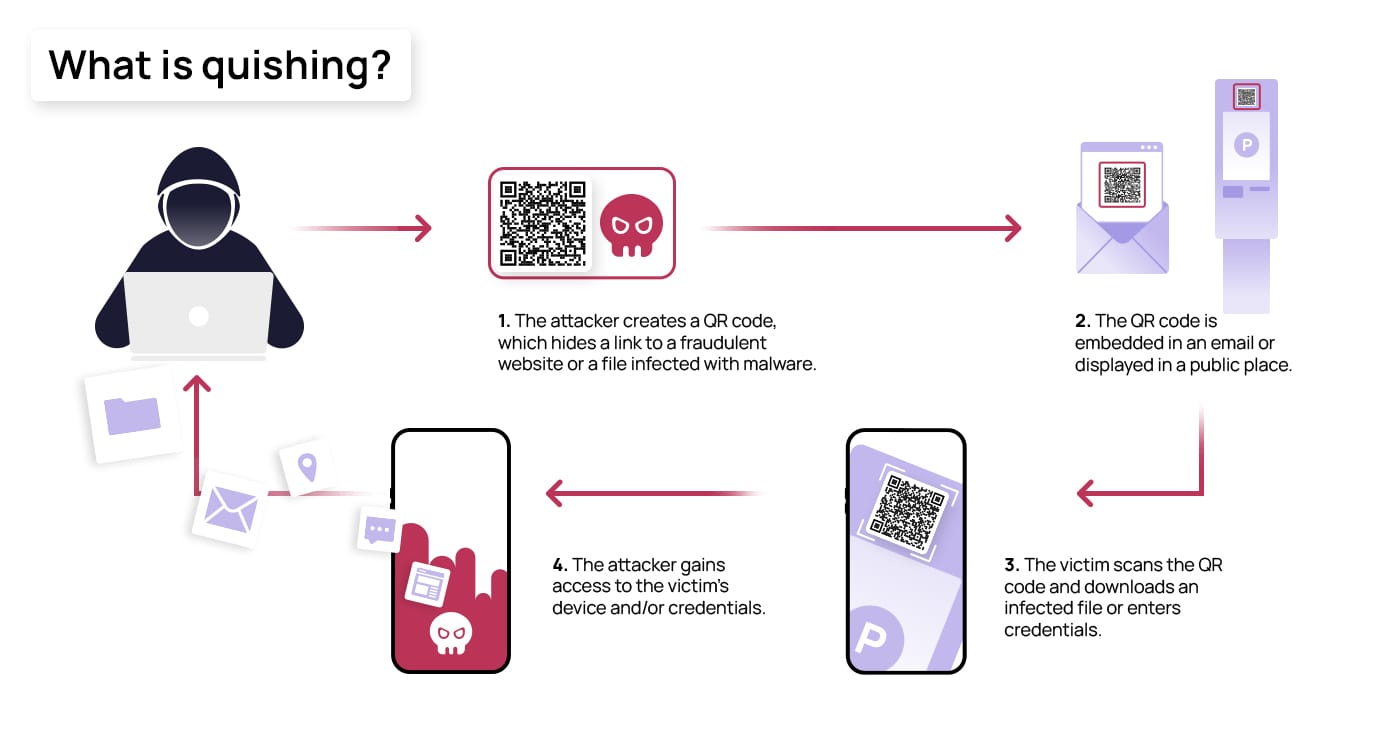
QR code phishing, or quishing, involves using QR codes to direct users to malicious websites that mimic legitimate ones. These codes can be easily distributed via email, social media, or printed materials. The unsuspecting user, upon scanning the code, is redirected to a page designed to steal sensitive information such as login credentials or financial data.
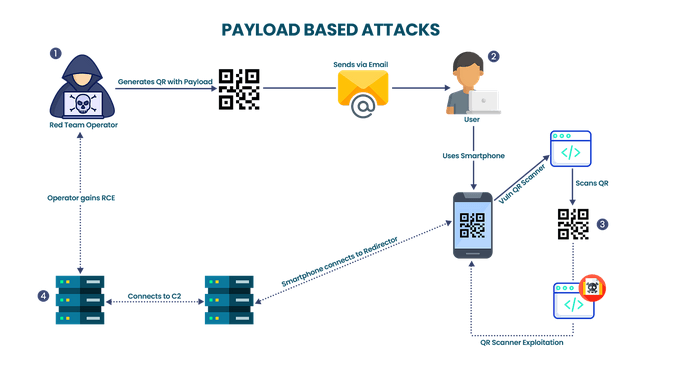
The Mechanics Behind QR Code Phishing
At its core, a QR code is a matrix barcode that stores information, typically a URL. Attackers generate QR codes that lead to phishing sites. When scanned, these codes can trigger automatic downloads or redirect users to a site that prompts for personal information.
Example Scenario: A user receives an email from what appears to be their bank. The email explains a security issue and asks the user to verify their identity by scanning the attached QR code. Upon scanning, the user lands on a website that looks identical to the bank’s login page. Entering credentials here sends them straight to the attacker.

QR code phishing attacks surged by 146% in Q1 2026 compared to Q4 2025, indicating a significant rise in cyber threats. Estimated data based on trends.
Why QR Code Phishing is Effective
Psychological Manipulation
QR codes are convenient and often seen as harmless. This perception makes them an ideal tool for attackers. Users are conditioned to trust these codes, especially when presented in a professional context.
Technical Simplicity
Creating a QR code is simple and requires minimal technical skill. This lowers the barrier for attackers, allowing a wider range of cybercriminals to deploy these attacks.
Bypassing Traditional Security
Traditional security measures, such as email filters and malware detection, often overlook QR codes. These codes can effectively bypass these defenses, reaching the end-user without raising red flags.
Real-World Use Cases and Examples
Case Study: Retail Sector
In a notable incident, a major retail chain discovered that hackers had replaced legitimate QR codes on promotional materials with malicious ones. Customers scanning these codes were redirected to a fake website that harvested personal and payment information.
Phishing in Public Spaces
Public places like cafes and airports often display QR codes for convenience. Attackers exploit these spaces by placing their own codes over legitimate ones, targeting users who unsuspectingly scan them.
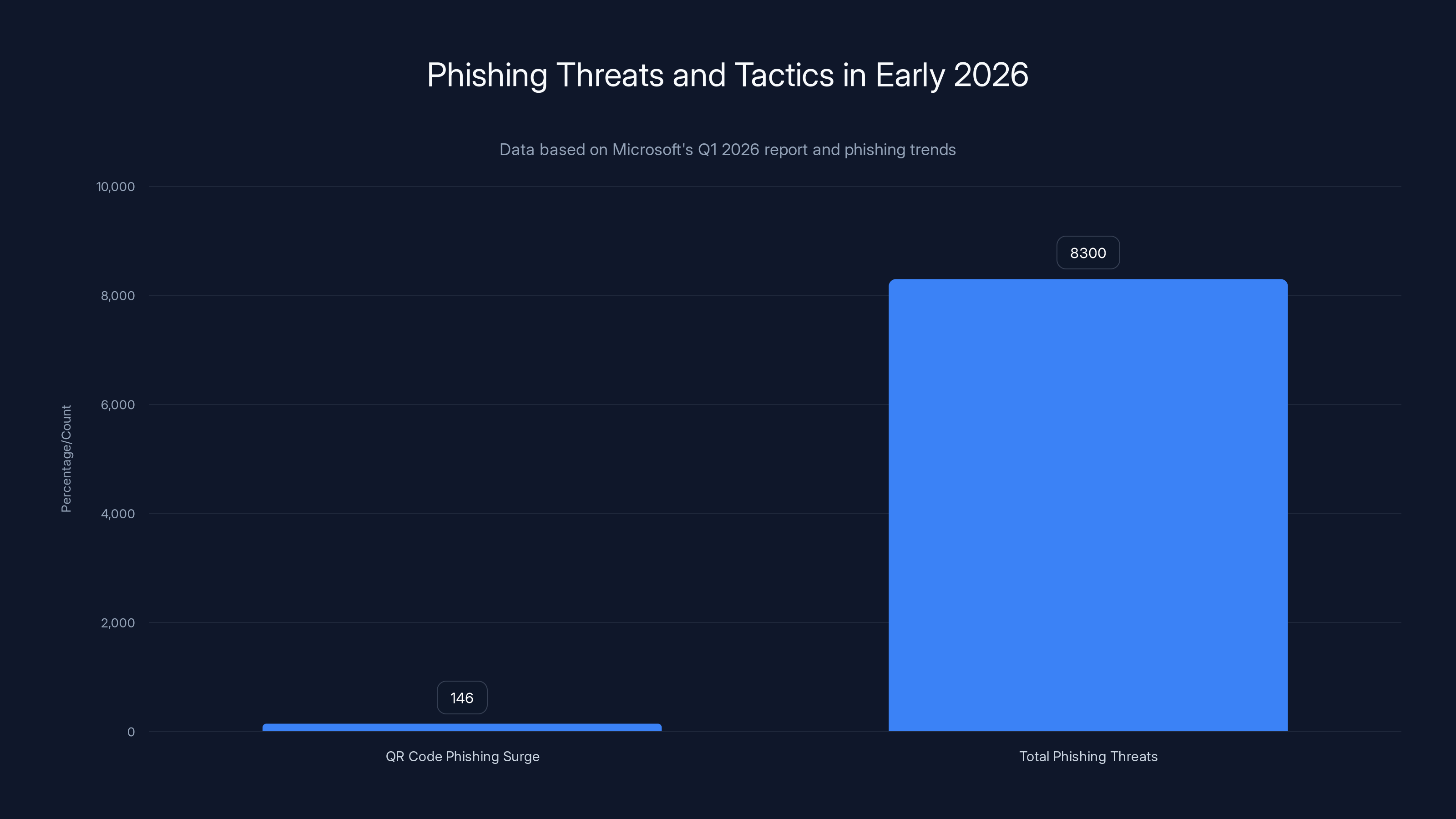
In early 2026, QR code phishing attacks surged by 146%, with a total of 8.3 billion phishing threats detected, highlighting the need for advanced security measures.
Technical Details and Best Practices
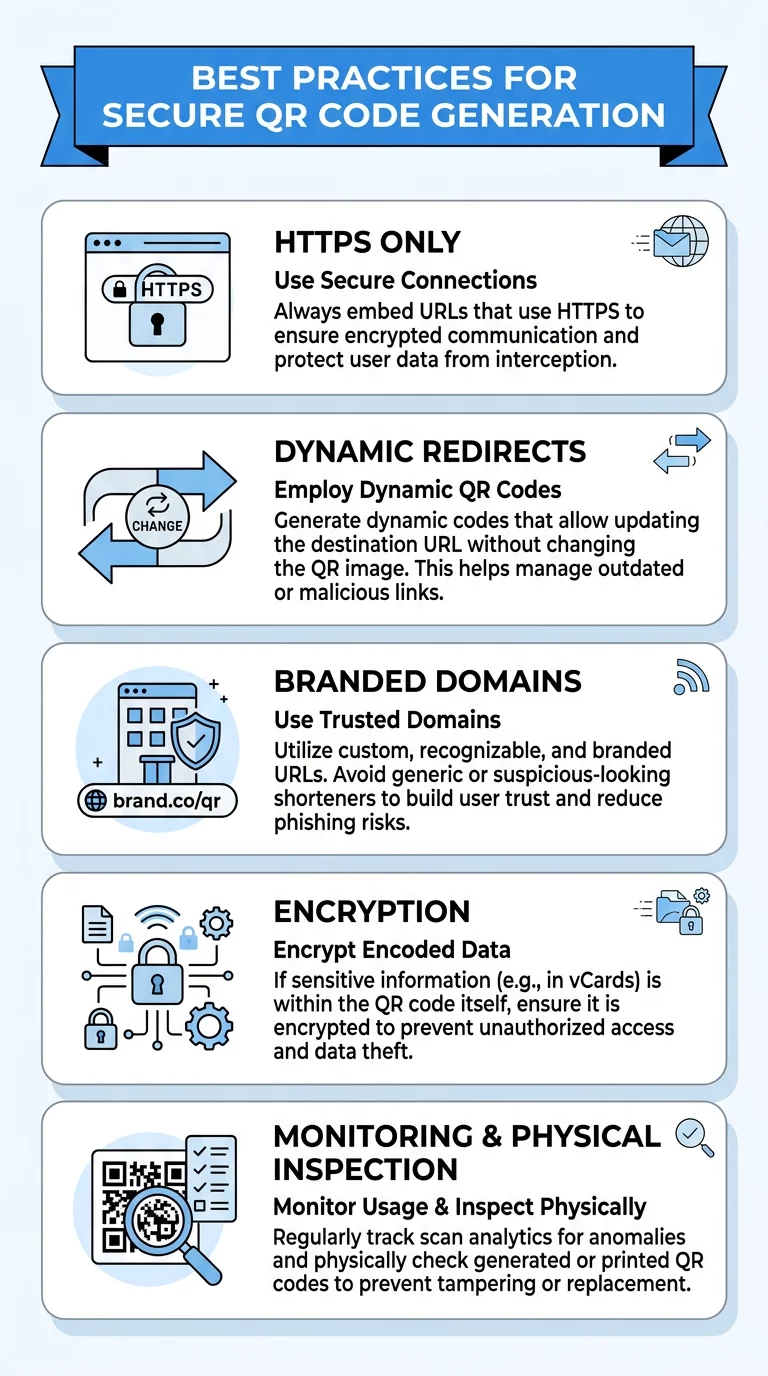
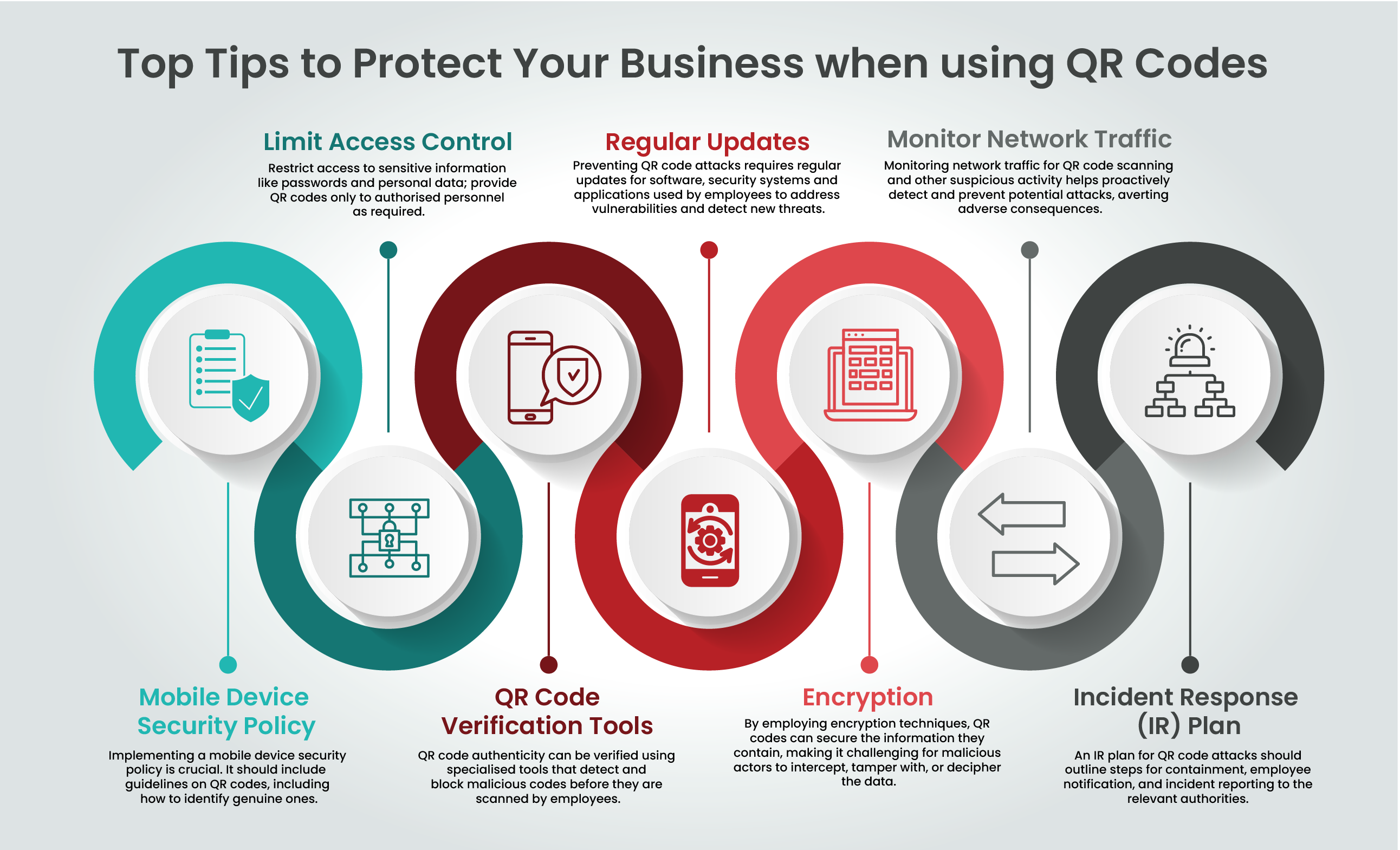
QR Code Security Best Practices
- Educate Users: Train employees and customers about the risks associated with scanning unknown QR codes.
- Use Secure QR Code Generators: Ensure QR codes are generated using secure, reputable platforms that offer tracking and analytics.
- Implement URL Filtering: Use security software that can detect and block access to malicious URLs.
- Regular Audits: Conduct regular audits of all QR codes used in your organization to ensure they haven’t been tampered with.
Technical Implementation Guide
- Secure Mobile Devices: Equip mobile devices with security applications that scan QR codes for malicious content before opening associated links.
- Two-Factor Authentication (2FA): Require 2FA for access to sensitive systems, which can prevent unauthorized access even if credentials are compromised.
- Monitoring and Response: Set up systems to monitor and respond to phishing incidents swiftly, minimizing damage.
Common Pitfalls and Solutions
Pitfall 1: Overlooking Physical Security
Solution: Regularly inspect physical spaces for unauthorized QR codes and equip employees with the knowledge to identify suspicious codes.
Pitfall 2: Neglecting User Education
Solution: Implement comprehensive training programs that emphasize the importance of verifying the source of QR codes.

Future Trends and Recommendations
AI and Machine Learning in Phishing
Attackers are increasingly using AI to automate and enhance their phishing campaigns. AI can create more convincing fake websites and identify potential targets based on behavior patterns.
Recommendations for Organizations
- Invest in AI-Driven Security Solutions: Leverage AI to identify and thwart phishing attacks in real-time.
- Stay Informed: Keep abreast of the latest phishing tactics and update security protocols accordingly.
- Collaborate with Industry Peers: Share information on phishing threats and best practices with other organizations to enhance collective security.

Conclusion
The surge in QR code phishing attacks underscores the need for vigilance and proactive security measures. By understanding the tactics used by attackers and implementing comprehensive security strategies, organizations can better protect themselves and their users from these evolving threats.
FAQ
What is QR code phishing?
QR code phishing involves using QR codes to direct users to malicious websites designed to steal personal information.
How does QR code phishing work?
Attackers create QR codes that link to phishing sites, tricking users into providing sensitive data.
What are the benefits of QR code phishing for attackers?
It’s easy to deploy, bypasses traditional security measures, and exploits the trust users place in QR codes.
How can organizations protect against QR code phishing?
Implement security best practices such as user education, secure QR code generation, and the use of security software.
What future trends should we expect in phishing tactics?
Expect more sophisticated attacks leveraging AI and machine learning to automate and enhance phishing campaigns.
Why are QR codes considered a security risk?
Their ubiquity and perception as harmless make them attractive vectors for phishing attacks.
The Best Tools for QR Code Security at a Glance
| Tool | Best For | Standout Feature | Pricing |
|---|---|---|---|
| Runable | AI automation | AI agents for presentations, docs, reports, images, videos | $9/month |
| Tool 1 | QR code security | Real-time threat detection | Subscription-based |
| Tool 2 | Mobile security | Comprehensive device protection | Free tier available |
Quick Navigation:
- Runable for AI-powered presentations, documents, reports, images, videos
- Tool 1 for QR code security
- Tool 2 for mobile security
Key Takeaways
- Phishing attacks via QR codes rose by 146% in 2026.
- Microsoft detected 8.3 billion phishing threats in Q1 2026.
- Attackers use QR codes to bypass traditional security measures.
- Implement multi-layered security strategies to mitigate risks.
- Expect more sophisticated phishing tactics leveraging AI.
Related Articles
- How AI Tools Have Made Vulnerability Exploitation Faster and Easier [2025]
- Why Encryption Breaking is 20x Cheaper and What CEOs Need to Do [2025]
- How Hackers Exploit Trusted Email Platforms and What You Can Do [2025]
- GPT-5.5 vs Mythos: Unveiling the Real Cybersecurity Contenders [2025]
- Microsoft's Xbox Mode Revolutionizes Windows 11 PCs [2025]
- Mastering Quick Resume Settings on Xbox: Optimal Gaming Experience in 2025




