US Agencies Alert: Iranian Hackers Targeting American Critical Infrastructure [2025]
The digital frontier is the new battleground, and the latest skirmish involves Iranian hackers allegedly targeting the United States' critical infrastructure. This isn't just a cyber threat; it's a national security alarm. Let's dive deep into what's happening, how it's affecting us, and what can be done to protect our vital systems.
TL; DR
- Iranian hackers are targeting US critical infrastructure, posing significant security threats. According to Politico, these attacks are part of a broader strategy to disrupt essential services.
- Attacks can lead to disruptive effects, impacting utilities, healthcare, and more. As noted by CSIS, the energy sector is particularly vulnerable.
- Cyber defenses must evolve to counter sophisticated threats from nation-state actors. The emerging cybersecurity threats highlight the need for advanced defense mechanisms.
- Implementing robust security protocols is essential for infrastructure protection. The CISA emphasizes the importance of endpoint security.
- Collaboration between public and private sectors is crucial for effective defense strategies. As discussed in Homeland Security Today, public-private partnerships are vital for national security.
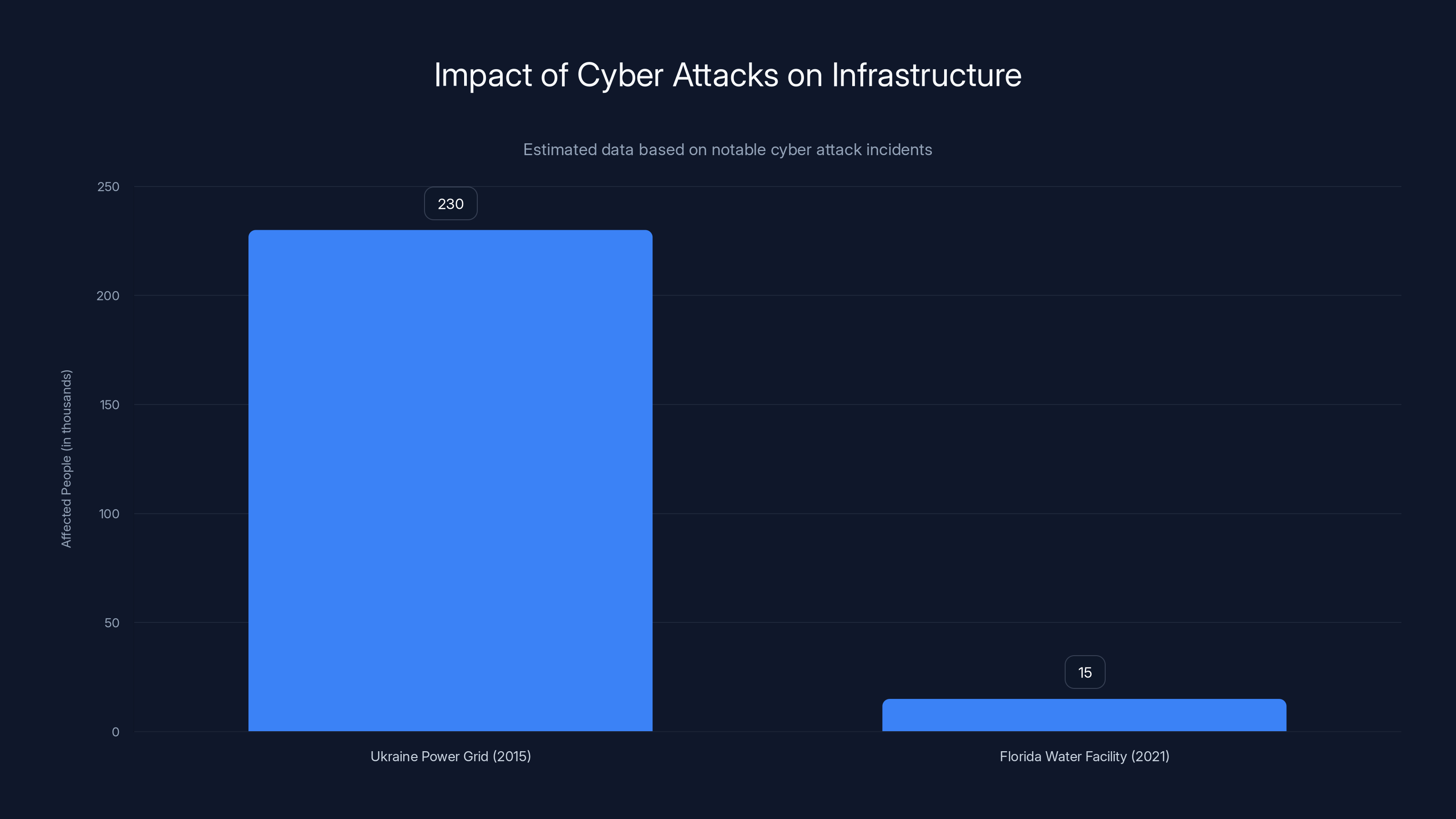
The 2015 Ukraine power grid attack affected 230,000 people, highlighting the severe impact of cyber threats on infrastructure. Estimated data for the Florida water facility incident shows potential impact.
Understanding the Threat Landscape
Cyberwarfare has evolved into a complex arena where state-sponsored actors, like those from Iran, employ sophisticated techniques to disrupt and destabilize. The US, with its advanced but vulnerable infrastructure, is a prime target.
Why Critical Infrastructure?
Critical infrastructure refers to essential systems and assets, such as power grids, water supplies, transportation networks, and financial services. Disruption in these areas can have catastrophic effects on national security, public safety, and economic stability.
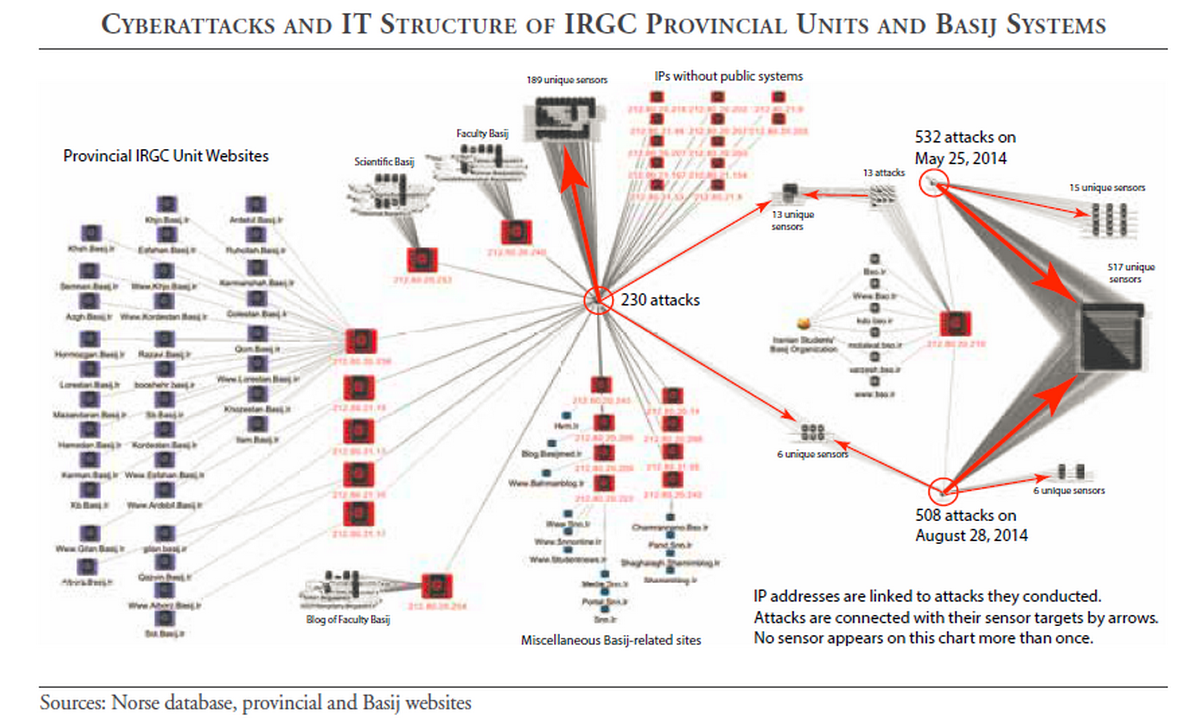
The Role of Iranian Hackers
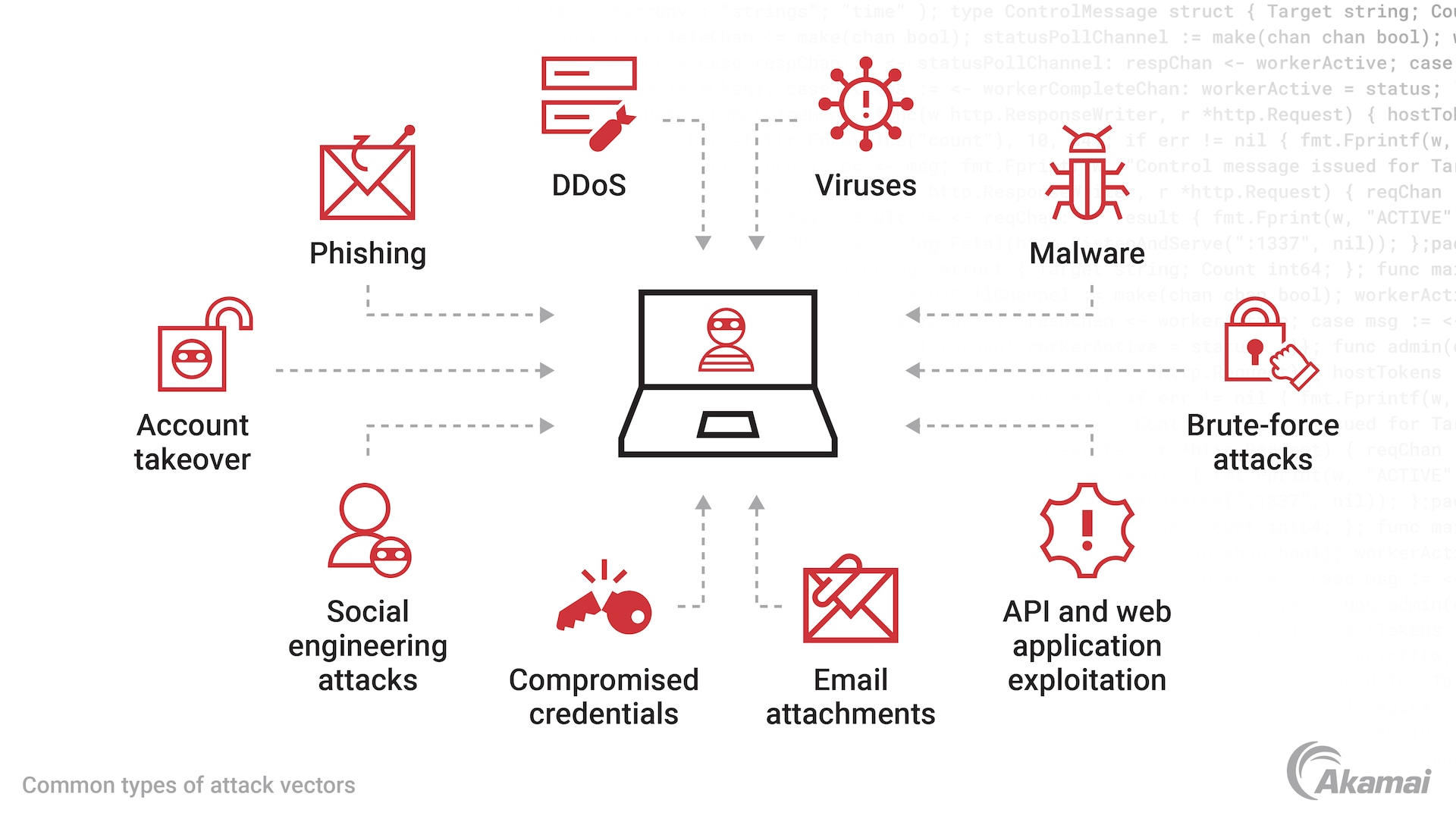
Iranian hackers have been implicated in various cyber attacks aimed at disrupting critical systems. Their motivations range from political retaliation to economic sabotage. According to a report by the Cybersecurity and Infrastructure Security Agency (CISA), these actors use a blend of social engineering, malware, and ransomware to infiltrate systems.
The Impact of Cyber Attacks on Infrastructure
Cyber attacks on critical infrastructure can lead to severe disruptions. Let's break down the potential impacts:
- Power Outages: Targeting energy grids can plunge entire regions into darkness. The CSIS analysis highlights the increased risk to energy infrastructure.
- Water Supply Contamination: Hacking water treatment facilities can lead to public health crises. Federal warnings have been issued regarding such threats.
- Healthcare Disruptions: Attacks on hospital systems can delay critical treatments. As reported by S&P Global, healthcare systems are increasingly targeted.
- Financial Chaos: Disruptions in financial systems can lead to economic instability. The Kennedys Law discusses potential economic impacts.
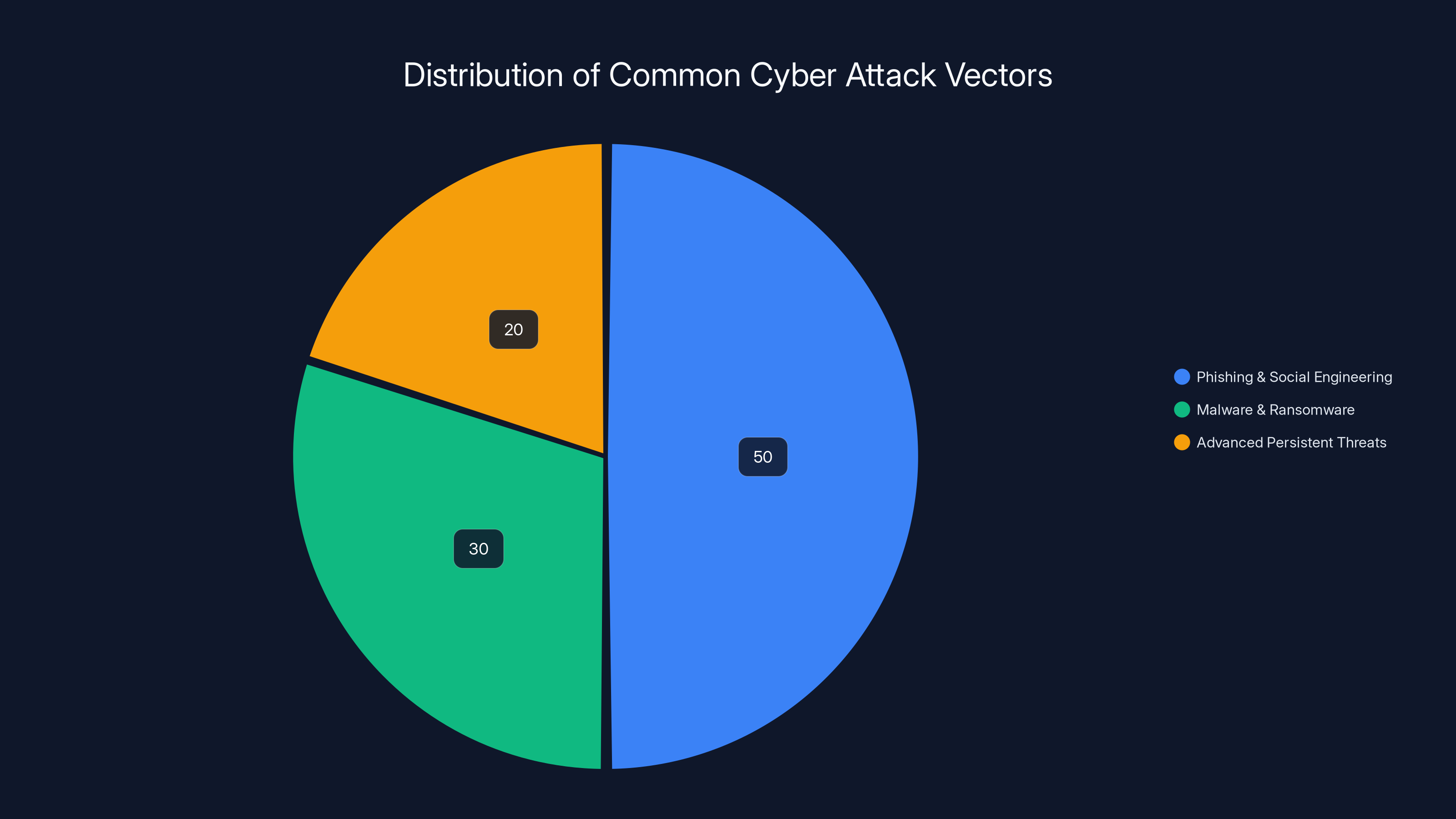
Phishing and social engineering are the most common attack vectors, estimated to account for 50% of attacks, followed by malware/ransomware at 30%, and APTs at 20%. Estimated data.
Real-World Examples
Consider the 2015 Ukraine power grid attack, where hackers caused a blackout affecting 230,000 people. This incident underscored the vulnerability of infrastructure systems to cyber threats.
Another case is the 2021 attack on a water treatment facility in Florida. Hackers attempted to increase lye levels in the water supply, which could have had disastrous health consequences if not detected in time.
Technical Details of Common Attack Vectors
1. Phishing and Social Engineering
These techniques exploit human psychology to gain unauthorized access. Attackers craft convincing emails or messages to trick employees into revealing sensitive information.
2. Malware and Ransomware
Malware can infiltrate systems through various means, such as infected emails or compromised websites. Ransomware encrypts data, holding it hostage until a ransom is paid.
3. Advanced Persistent Threats (APTs)
APTs involve prolonged campaigns where attackers establish a foothold within networks, monitoring and exfiltrating data over extended periods.
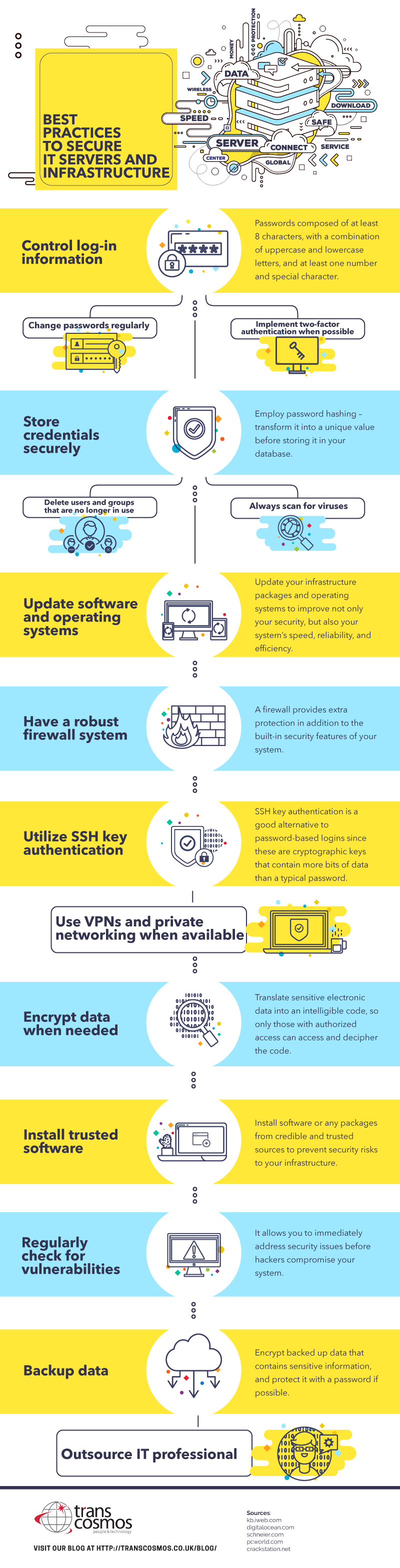
Best Practices for Infrastructure Protection
1. Implementing Multi-Layered Security
A multi-layered security approach, also known as defense-in-depth, involves using multiple security measures to protect information. This can include firewalls, intrusion detection systems, and endpoint protection.
2. Regular Security Audits and Penetration Testing
Conducting regular security audits helps identify vulnerabilities before attackers can exploit them. Penetration testing simulates attacks to test the effectiveness of security measures.
3. Employee Training and Awareness
Educating employees about cybersecurity threats is crucial. Training programs should focus on recognizing phishing attempts and following security protocols.
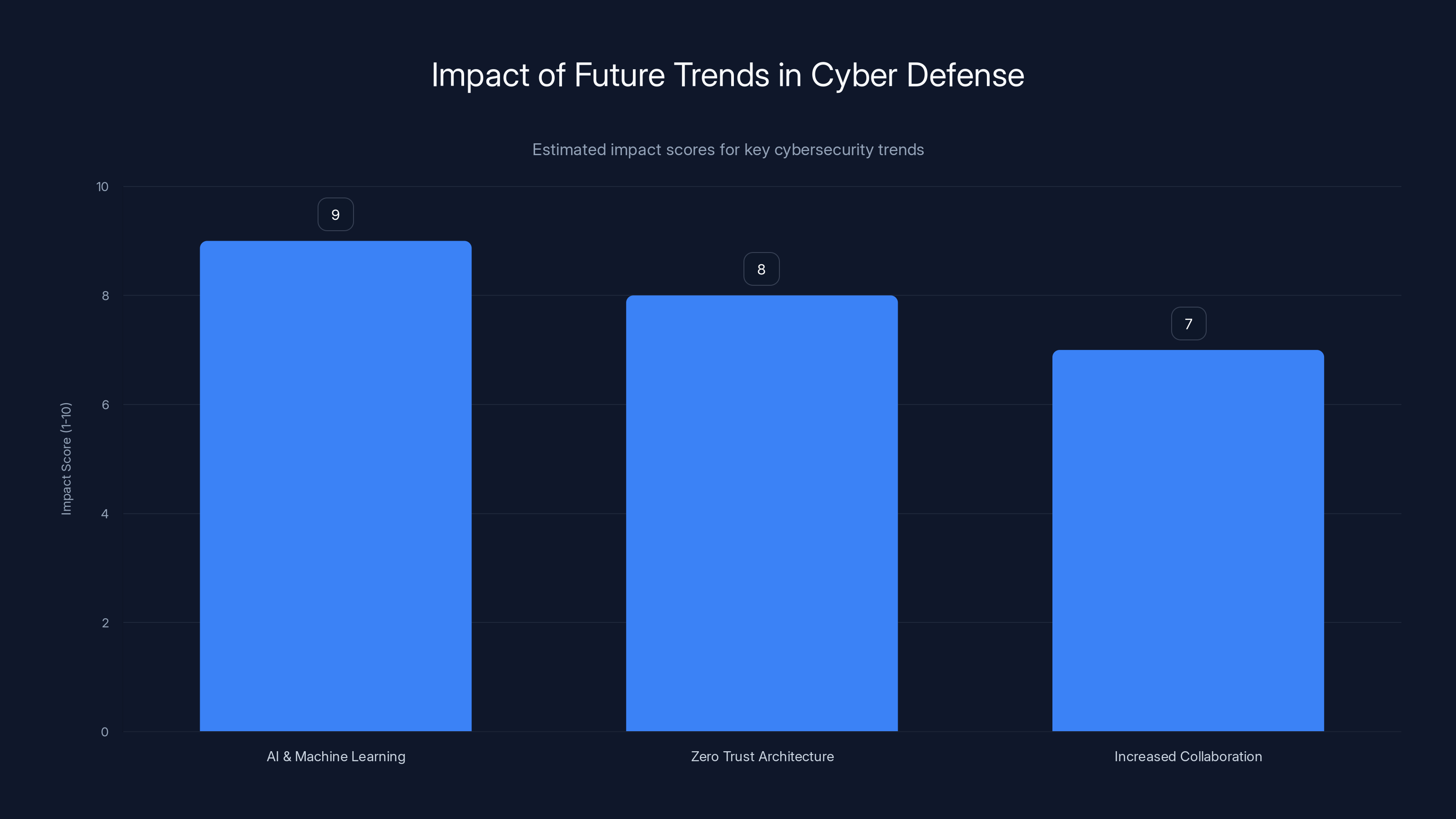
AI and Machine Learning are projected to have the highest impact on future cyber defense strategies, followed by Zero Trust Architecture and Increased Collaboration. Estimated data.
Common Pitfalls and Solutions
Pitfall: Over-Reliance on Technology
While technology is essential for defense, relying solely on it can be a weakness. Human oversight and intervention are critical components of a robust security strategy.
Solution: Human-Centric Security
Incorporate human elements into cybersecurity strategies. This includes training, awareness programs, and fostering a culture of security within organizations.

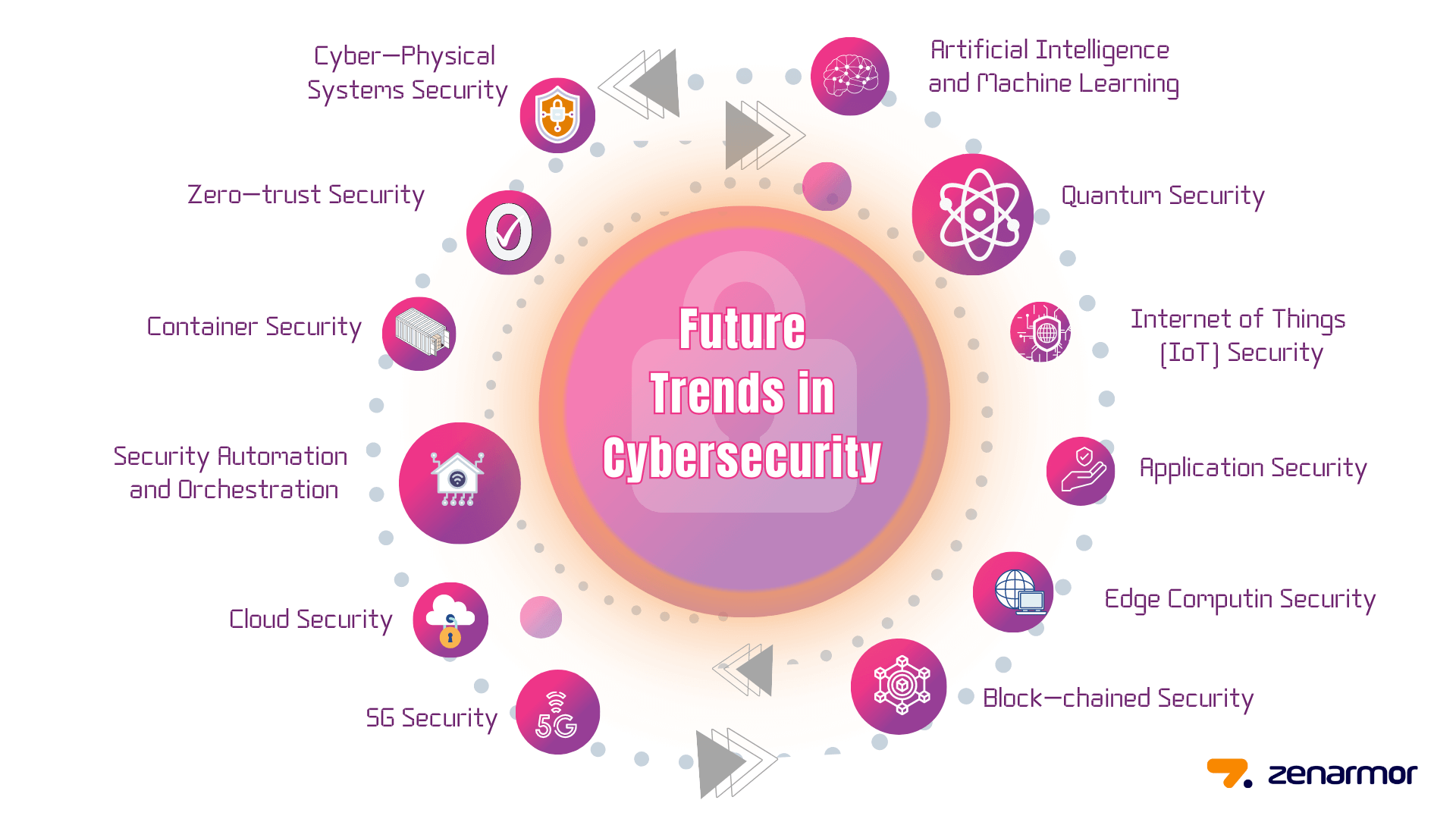
Future Trends in Cyber Defense
1. AI and Machine Learning
AI and machine learning are transforming cybersecurity by automating threat detection and response. These technologies can analyze vast amounts of data to identify patterns and anomalies.
2. Zero Trust Architecture
Zero Trust is a security model that requires verification for every user and device, regardless of whether they are within the organization's network. It assumes that threats can originate from anywhere.
3. Increased Collaboration
Collaboration between government agencies, private sectors, and international partners is vital for sharing information and developing unified defense strategies. As highlighted by ExecutiveBiz, collaboration is key to addressing quantum risks.
Recommendations for Organizations
1. Develop an Incident Response Plan
An incident response plan outlines procedures for detecting, responding to, and recovering from cyber attacks. It should be regularly tested and updated.
2. Invest in Cyber Insurance
Cyber insurance can mitigate financial losses associated with cyber incidents. Policies should be tailored to address specific organizational risks. According to Insurance Business Magazine, fraud has overtaken ransomware in cyber risk rankings.
3. Engage with Threat Intelligence
Threat intelligence involves gathering and analyzing information about potential threats. This proactive approach helps organizations anticipate and mitigate risks.
Conclusion
The threat of Iranian hackers targeting US critical infrastructure is a stark reminder of the vulnerabilities in our digital world. By understanding these threats and implementing robust security measures, organizations can safeguard against disruptions that could have far-reaching consequences.
Use Case: Automate your security analytics with AI to detect threats faster.
Try Runable For Free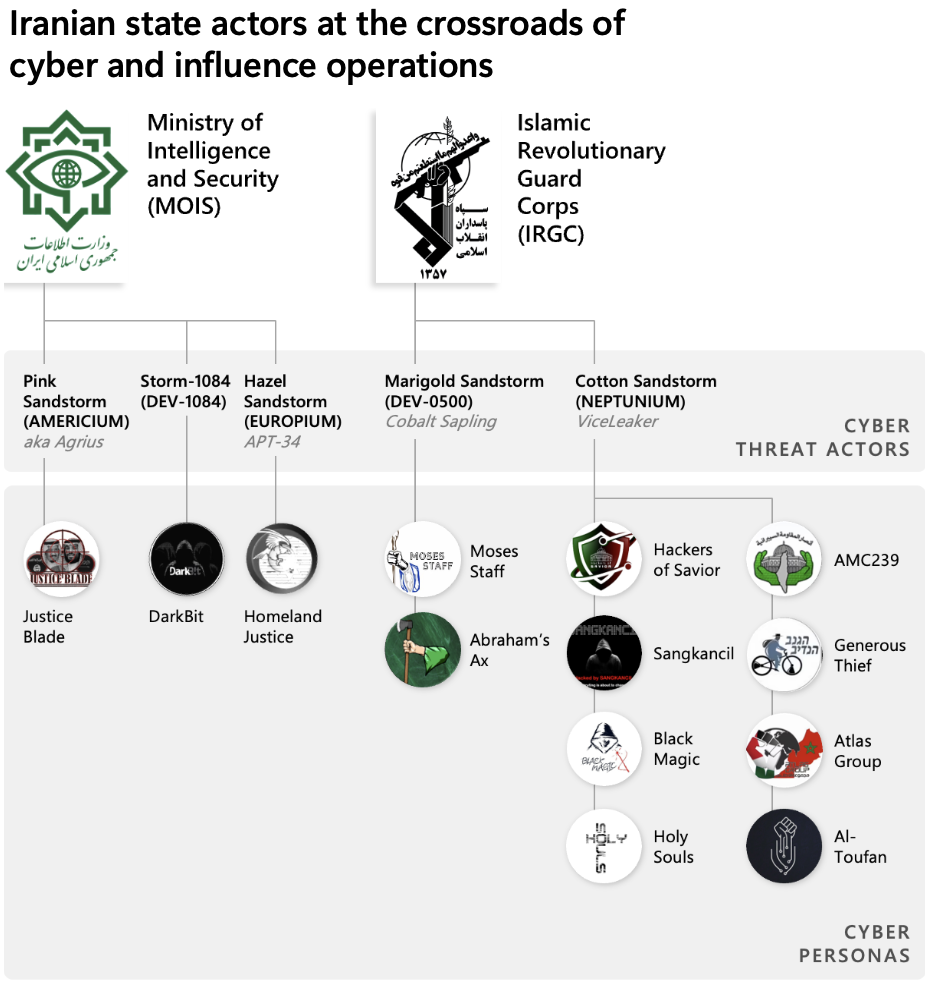
FAQ
What is critical infrastructure?
Critical infrastructure includes systems and assets essential to the nation's security, economy, and public health. Examples include power grids, water supplies, and communication networks.
How do Iranian hackers target US infrastructure?
Iranian hackers use techniques such as phishing, malware, and advanced persistent threats to infiltrate and disrupt critical systems.
What are the consequences of a cyber attack on infrastructure?
Consequences can include power outages, water contamination, healthcare disruptions, and financial instability, all of which can have wide-reaching effects on society.
How can organizations protect against these threats?
Organizations should implement multi-layered security, conduct regular audits, train employees, and develop incident response plans to protect against cyber threats.
Why is collaboration important in cybersecurity?
Collaboration allows for information sharing and coordinated responses, which are crucial for effectively defending against sophisticated cyber threats.
Key Takeaways
- Iranian hackers are actively targeting US critical infrastructure.
- Cyber attacks can cause significant disruptions and pose national security risks.
- Multi-layered security and employee training are vital for protection.
- AI and machine learning are shaping the future of cybersecurity.
- Collaboration between sectors enhances defense capabilities.
Related Articles
- Cybercriminals Target Vulnerable Sectors as Crypto Fraud Escalates [2025]
- Stay Safe from Deepfakes: Expert Steps to Verify Before You Act [2025]
- Inside the Shadowy World of Modern Scam Factories: Lessons from a Bombed Casino Near the Cambodia–Thailand Border [2025]
- Understanding Anthropic's Mythos AI Model: A New Era in Cybersecurity [2025]
- 5 Key Insights from Samsara's Reacceleration to $1.9 Billion in ARR [2025]
- Project Glasswing: AI Cybersecurity's New Vanguard [2025]
![US Agencies Alert: Iranian Hackers Targeting American Critical Infrastructure [2025]](https://tryrunable.com/blog/us-agencies-alert-iranian-hackers-targeting-american-critica/image-1-1775658917928.jpg)



