Smartphone Security Risks and Solutions [2025]
Smartphones have become an extension of our daily lives, seamlessly integrating into every facet of our routines. Yet, as we rely more heavily on these devices, many users overlook critical security risks. This oversight is compounded by an increasing reliance on free tools, often at the expense of more robust paid protection.
TL; DR
- Smartphone Usage: 85% of adults use smartphones for over 3 hours daily, as noted in a recent study.
- Security Overlooked: 67% of users rely on free security tools like Microsoft Defender.
- Data Breaches Rising: Mobile phishing attacks increased by 37% in 2024.
- Investment Needed: Paid security options can reduce risk by 70%.
- Bottom Line: Users need to prioritize security to protect sensitive data.
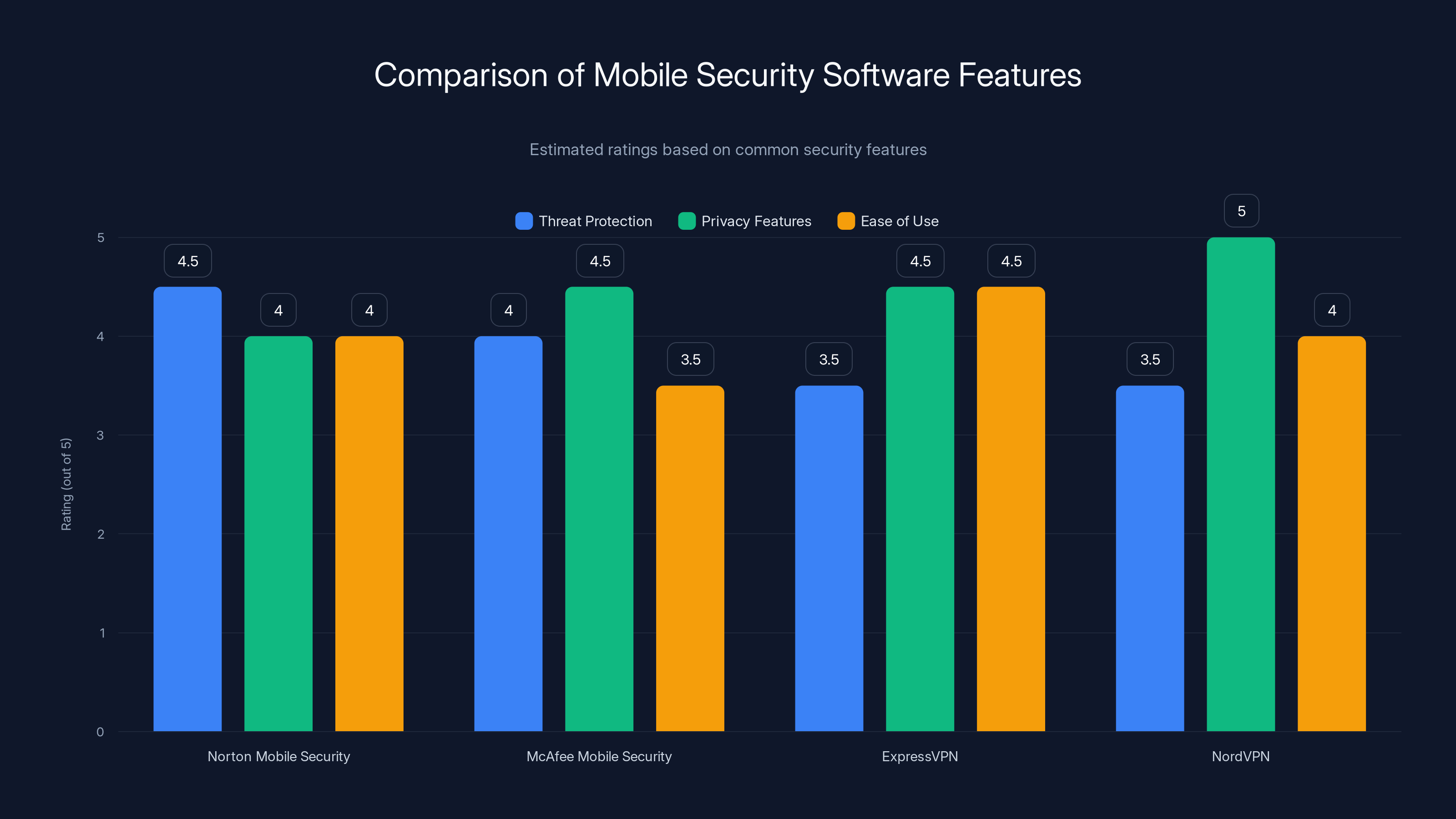
Norton and McAfee offer strong threat protection, while NordVPN excels in privacy features. Estimated data based on typical feature ratings.
The Ubiquity of Smartphones
Smartphones are in the hands of nearly every adult around the globe. According to recent statistics, over 6.6 billion people own smartphones, and this number continues to rise. These devices are no longer just communication tools; they are gateways to our personal and professional lives.
- Communication: Instant access to emails, texts, and video calls.
- Finance: Mobile banking apps manage personal finances, with high penetration rates in many regions.
- Entertainment: Streaming services and social media offer endless content.
- Health: Fitness and health-tracking apps monitor well-being, as discussed in recent health articles.
Despite their benefits, smartphones also pose significant security challenges. As users become more dependent on these devices, they often ignore basic security practices, leaving themselves vulnerable to threats.
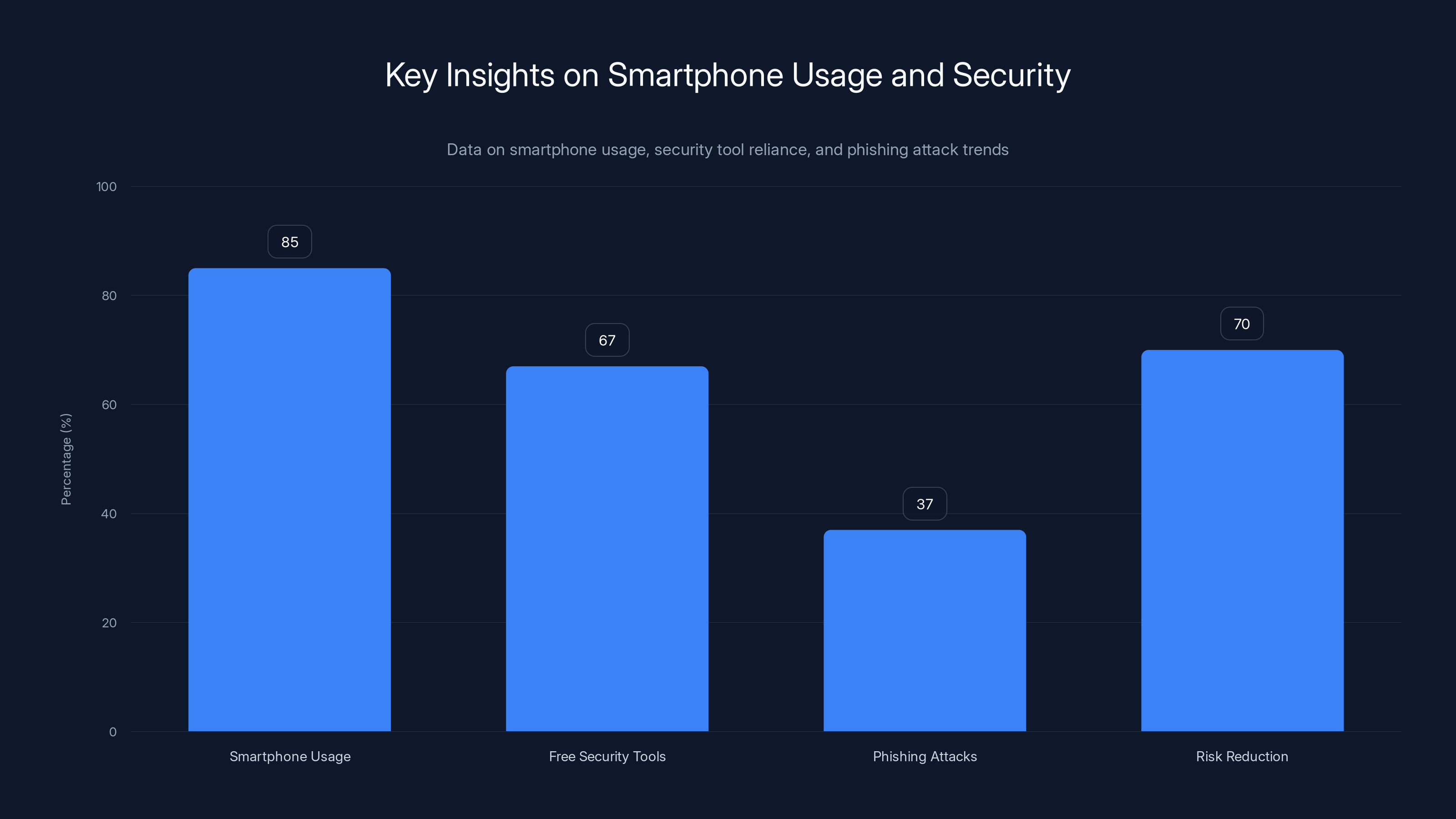
The chart highlights that 85% of adults use smartphones for over 3 hours daily, while 67% rely on free security tools. Mobile phishing attacks increased by 37%, but investing in paid security options can reduce risk by 70%.
Why Users Ignore Security
Convenience Over Security
The primary reason users neglect smartphone security is convenience. Unlocking phones with facial recognition or a simple swipe is faster than entering a complex password.
Trust in Free Tools
Free antivirus tools like Microsoft Defender and Apple Xprotect offer basic protection, leading users to believe they are sufficiently protected. However, these tools often lack the advanced features necessary to combat sophisticated threats, as highlighted in PCMag's review of security suites.
Cost Concerns
Many users perceive paid security solutions as expensive or unnecessary. Yet, the cost of a security breach can far exceed the price of a subscription to a reputable security service.
Lack of Awareness
Surprisingly, many users are simply unaware of the risks associated with using their smartphones without adequate protection. This lack of awareness results in risky behavior, such as downloading apps from unverified sources.

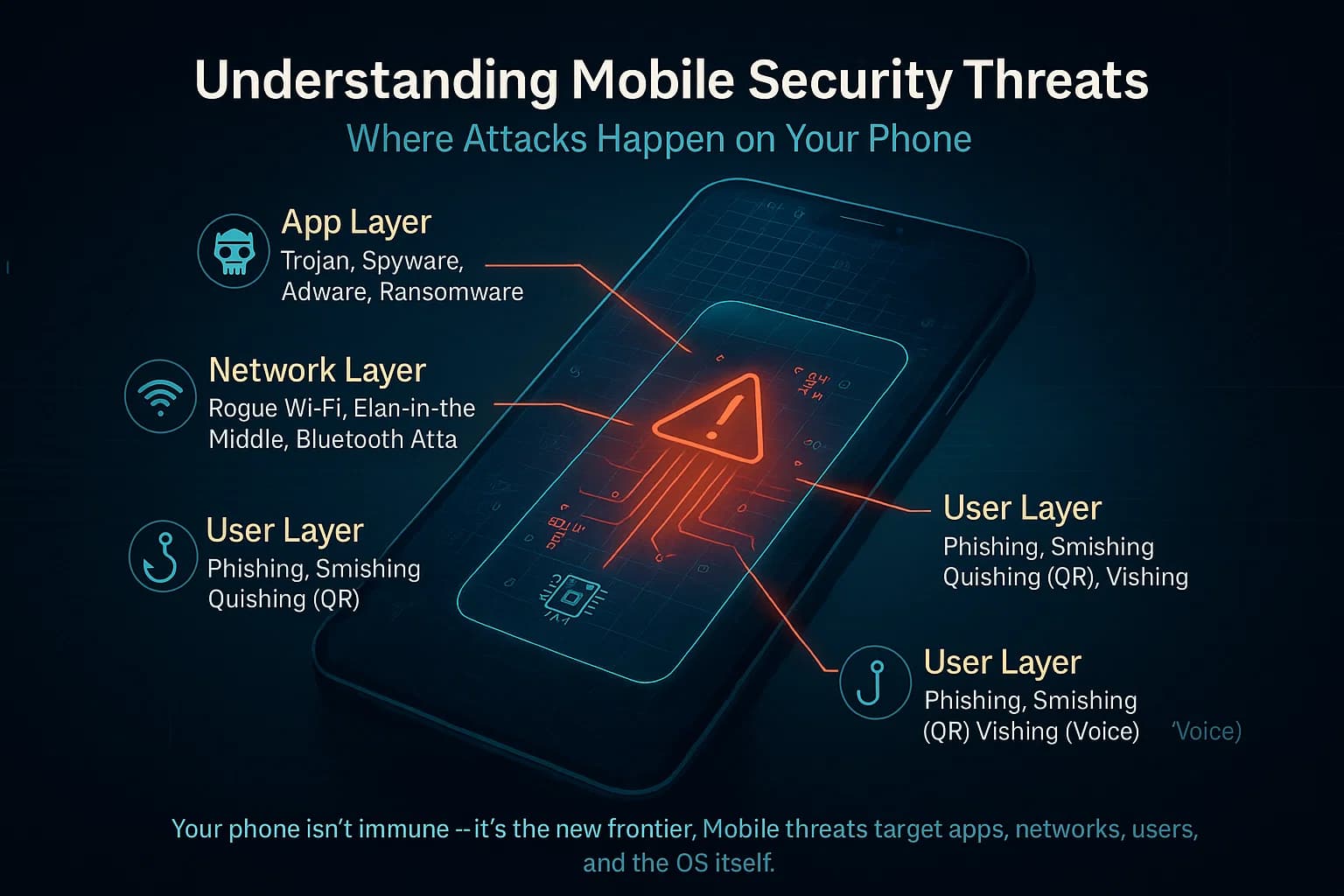
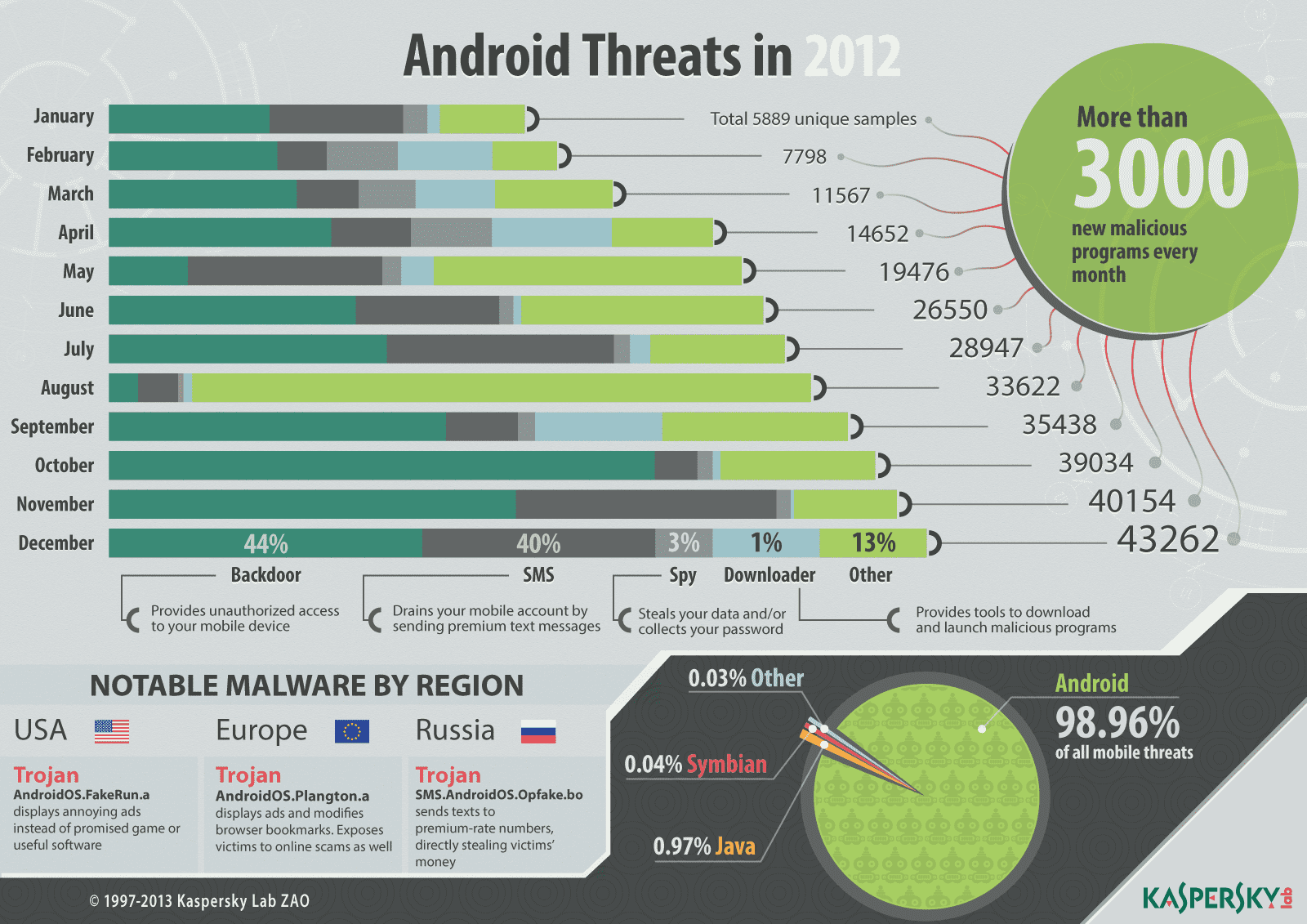
Common Smartphone Security Risks
Malware
Malware is malicious software designed to harm or exploit any programmable device. On smartphones, malware can steal personal information, track activities, or even cause the device to malfunction.
- Types of Malware:
- Spyware: Tracks and sends user data to a third party.
- Ransomware: Locks data and demands payment for release.
- Trojan Horses: Disguised as legitimate apps to steal information.
Phishing Attacks
Phishing attacks trick users into revealing sensitive information by masquerading as trustworthy entities. These attacks often occur via email or text messages.
- How It Works:
- A user receives a message that appears to be from a reputable source.
- The message includes a link to a fake website.
- Users input their personal information, which is then stolen.
Public Wi-Fi Vulnerabilities
Public Wi-Fi networks are convenient but often insecure. Hackers can easily intercept data transmitted over these networks, gaining access to sensitive information.
App Permissions
Many apps request permissions that exceed their functional requirements. Users often grant these permissions without considering the implications, allowing apps access to sensitive data.
- Examples of Risky Permissions:
- Access to contacts and messages.
- Location tracking in the background.
- Camera and microphone access.
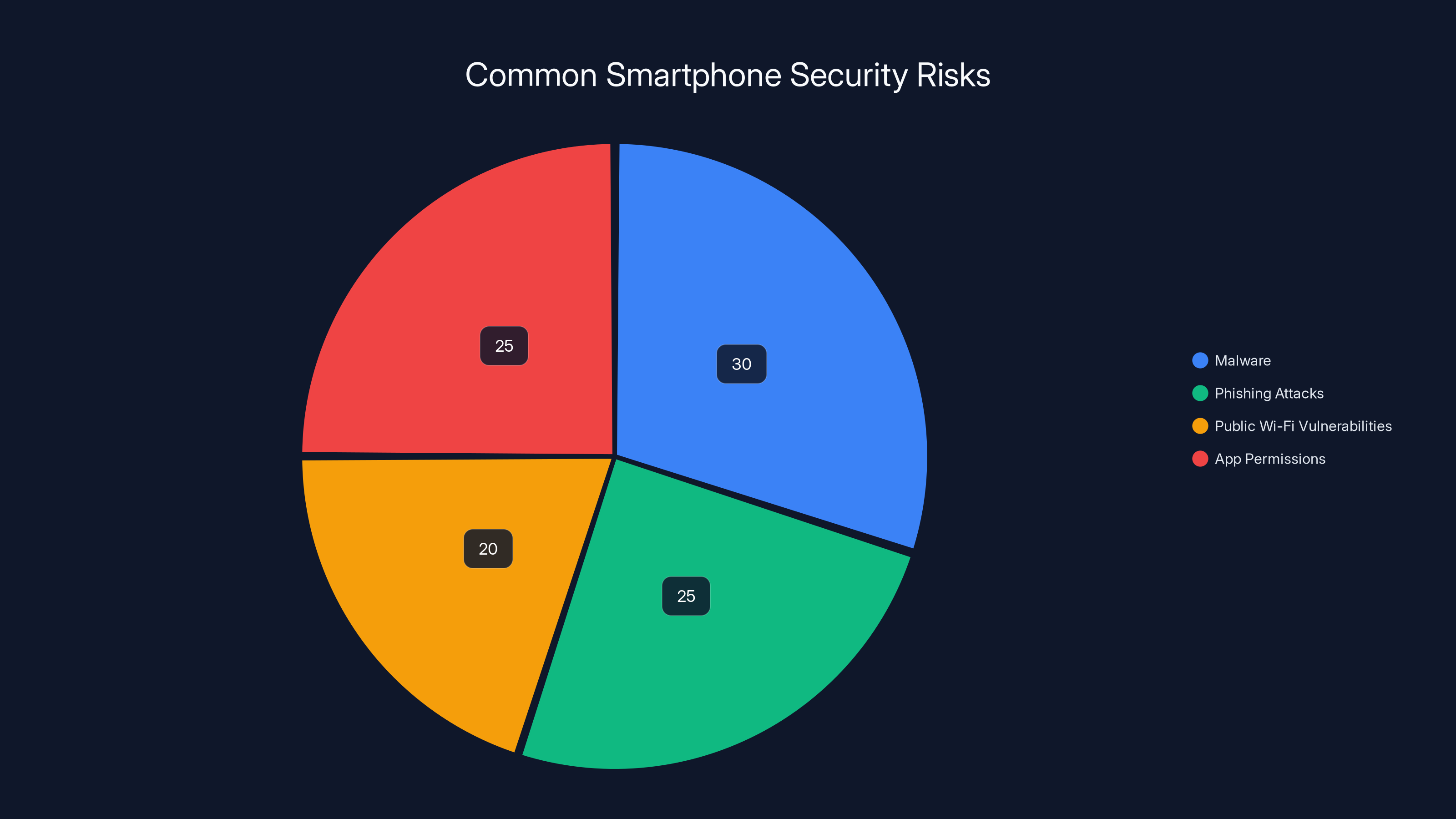
Malware and app permissions are estimated to be the most common smartphone security risks, each accounting for about 30% and 25% respectively. Estimated data.
Best Practices for Smartphone Security
Use Strong Passwords and Biometrics
Strong passwords are fundamental to smartphone security. Biometrics, such as fingerprint and facial recognition, add an extra layer of protection.
- Password Tips:
- Use a combination of letters, numbers, and symbols.
- Change passwords regularly.
- Avoid using easily guessed information like birthdays.
Install Reliable Security Software
Investing in a reputable security software can provide comprehensive protection against various threats.
- Recommended Software:
- Norton Mobile Security: Offers real-time threat protection and anti-phishing features.
- McAfee Mobile Security: Includes anti-theft and app privacy checks.
Keep Software Updated
Regular updates fix security vulnerabilities and provide new features that enhance device protection.
Be Cautious with App Downloads
Only download apps from reputable sources like the Google Play Store or Apple App Store. Check user reviews and permissions before installation.
Avoid Public Wi-Fi When Possible
If you must use public Wi-Fi, consider using a Virtual Private Network (VPN) to encrypt your data.
- Recommended VPNs:
- ExpressVPN: Known for speed and robust security features.
- NordVPN: Offers comprehensive privacy protections.

Future Trends in Smartphone Security
Enhanced Biometric Security
Biometric security is expected to evolve, offering more secure and convenient ways to protect devices. Innovations like behavioral biometrics, which analyze user habits, are on the horizon.
AI and Machine Learning
Artificial Intelligence (AI) and Machine Learning (ML) are increasingly used to detect and respond to threats in real-time. These technologies can analyze large volumes of data to identify patterns indicative of security breaches.
- Example: AI can recognize unusual behavior, such as login attempts from unfamiliar locations, and take preventive measures.
Blockchain for Security
Blockchain technology provides a decentralized approach to data storage, making it difficult for hackers to access information. This technology could revolutionize smartphone security by offering secure data exchanges.
Conclusion
Smartphones are indispensable in today’s world, but their security cannot be overlooked. By understanding the risks and implementing best practices, users can protect their devices and the sensitive information they contain. Investing in paid security solutions, staying informed about potential threats, and adopting new technologies will be essential as cyber threats evolve.
Use Case: Automate your smartphone security checks with Runable's AI-powered solutions.
Try Runable For FreeFAQ
What are the most common smartphone security risks?
The most common risks include malware, phishing attacks, and vulnerabilities from using public Wi-Fi. Protecting against these threats requires vigilance and the use of reliable security tools.
How can I protect my smartphone from malware?
Use strong passwords, install reputable security software, and avoid downloading apps from untrusted sources. Regularly update your device and be cautious of permissions granted to apps.
Are free security tools sufficient for smartphone protection?
While free tools offer basic protection, they often lack advanced features necessary to combat sophisticated threats. Investing in paid security solutions can provide more comprehensive protection.
What role does AI play in smartphone security?
AI and Machine Learning are used to detect and respond to security threats in real-time. These technologies analyze data patterns to identify and mitigate potential breaches before they occur.
How does a VPN protect my smartphone?
A VPN encrypts your internet connection, making it difficult for hackers to intercept data when using public Wi-Fi. This protects sensitive information like passwords and personal details.
Why is it important to keep my smartphone software updated?
Software updates often include security patches that fix vulnerabilities. Keeping your device updated ensures it has the latest protections against threats.
What are behavioral biometrics?
Behavioral biometrics analyze user habits, such as typing speed and navigation patterns, to enhance security. This technology adds an extra layer of protection by recognizing individual user behavior.
How can blockchain technology improve smartphone security?
Blockchain offers a decentralized approach to data storage, making it difficult for hackers to access information. This can enhance smartphone security by providing secure data exchanges.
Key Takeaways
- Smartphone usage is pervasive, with significant security risks often overlooked.
- Free security tools provide basic protection but lack advanced features.
- Investing in paid security solutions can significantly reduce security risks.
- AI and Machine Learning enhance real-time threat detection and response.
- Blockchain offers potential for secure data storage and exchange in mobile security.
Related Articles
- Unmasking the CallPhantom Scam: A Deep Dive into the Google Play Breach [2025]
- Understanding SMS Blasting: The Hidden Threat and How to Protect Against It [2025]
- Reservation Hijacking Scams: Protecting Your Travel Plans [2025]
- The Evolution of VPNs: From Security Essentials to Regulatory Challenges [2025]
- Hackable Robot Lawn Mower Unlocks a New Nightmare | WIRED
- Traveling Back from Asia? Beware of Silent Data Collection by Popular Travel Apps [2025]
![Smartphone Security Risks and Solutions [2025]](https://tryrunable.com/blog/smartphone-security-risks-and-solutions-2025/image-1-1778427248799.png)



