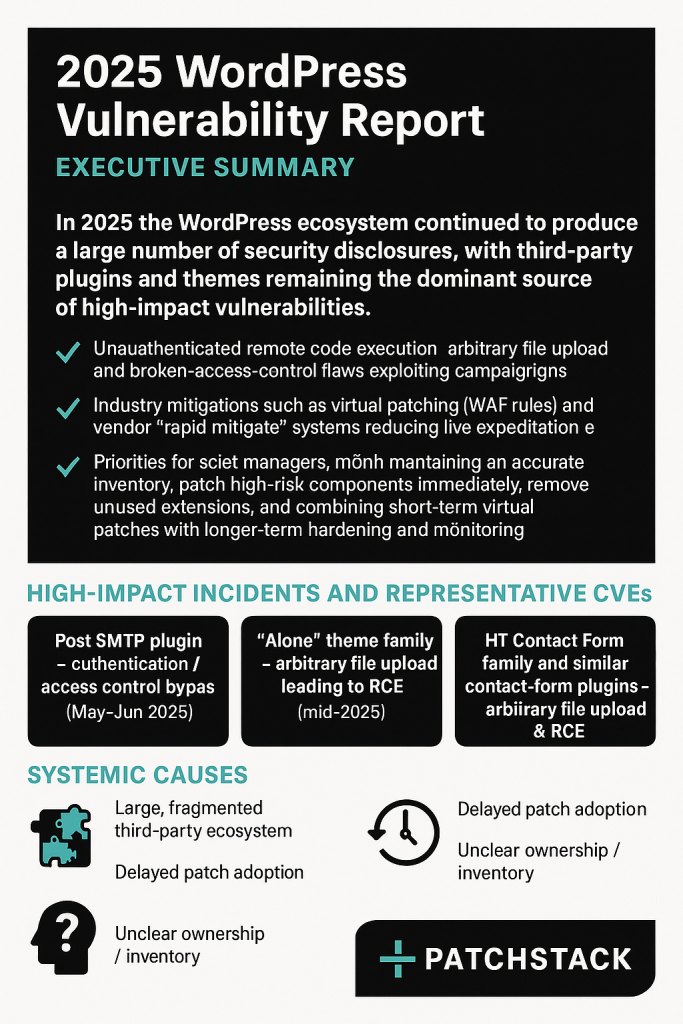
WordPress Plugin Security Flaws: Understanding Risks and Protecting Your Site [2025]
In a world where digital presence is paramount, WordPress stands as a giant, powering over 40% of the internet's websites. Its flexibility and ease of use make it a go-to choice for businesses, bloggers, and developers alike. However, with great power comes great responsibility. Recently, a security vulnerability in a widely-used plugin exposed around 500,000 WordPress sites to potential attacks. Let's dive into what happened, why it matters, and how you can protect your site from such threats.
TL; DR
- Recent Vulnerability: A flaw in a popular plugin exposed 500,000 WordPress sites.
- Immediate Action Needed: Update your plugins regularly to avoid vulnerabilities.
- Best Practices: Employ security plugins and regular backups.
- Long-term Solutions: Consider a WordPress security audit.
- Stay Updated: Subscribe to security blogs and forums.
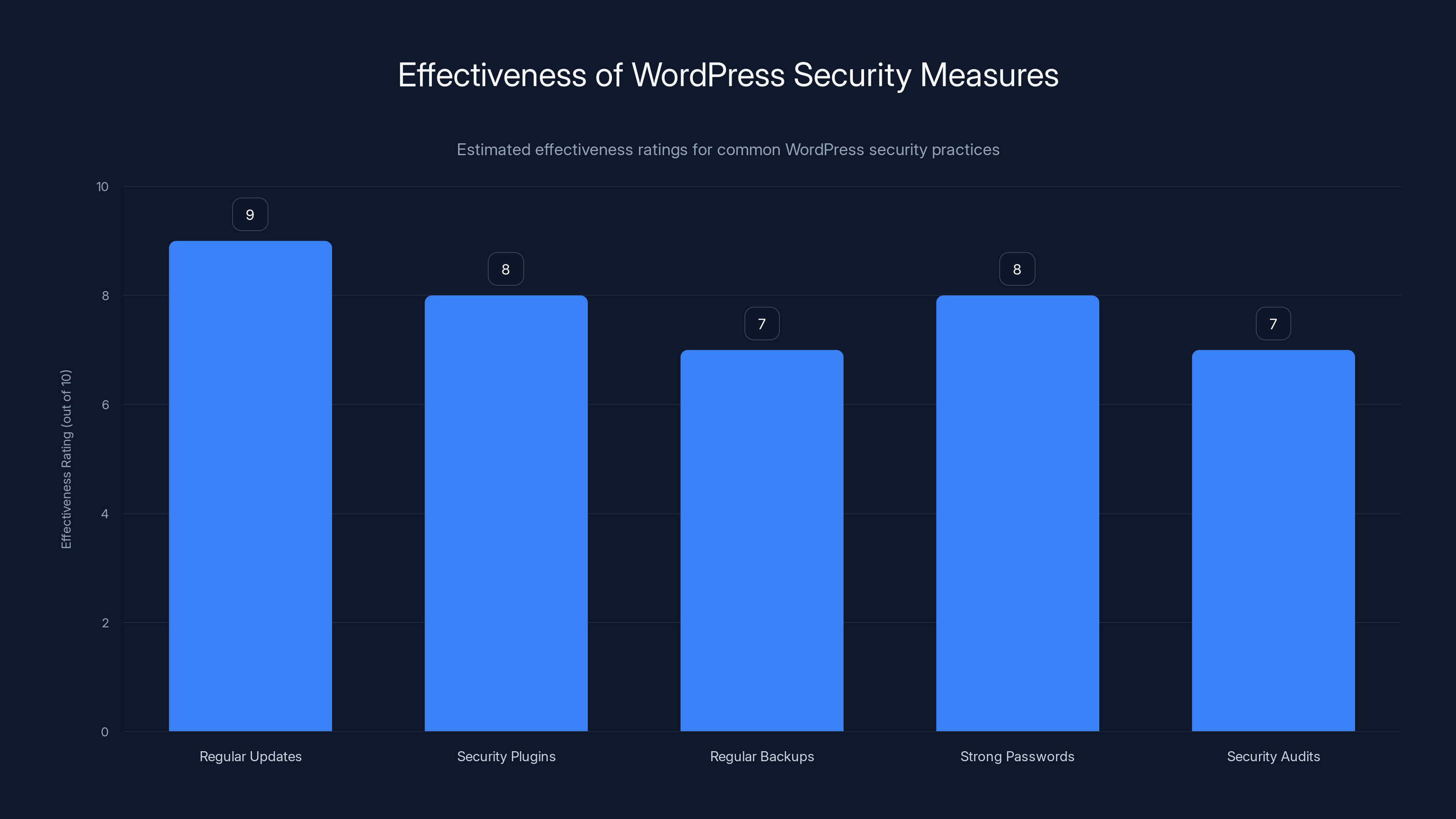
Regular updates are the most effective measure, scoring 9/10, closely followed by security plugins and strong passwords. Estimated data.
The Recent Security Flaw: A Closer Look
In early 2025, a security flaw was discovered in the Smart Slider 3 plugin, used by over 800,000 WordPress websites. This vulnerability allowed hackers to read arbitrary files on affected servers, potentially exposing sensitive data such as configuration files, user credentials, and more.
What Happened?
The flaw was an Arbitrary File Read vulnerability. This type of vulnerability allows attackers to access any file on the server that the web server process can read. In this case, the Smart Slider 3 plugin had a flaw in its code that did not properly sanitize input, allowing malicious actors to exploit it.
How Was It Discovered?
Security researchers often perform penetration testing and code audits on popular plugins to identify potential vulnerabilities. During one such audit, the flaw in Smart Slider 3 was discovered and promptly reported to its developers.

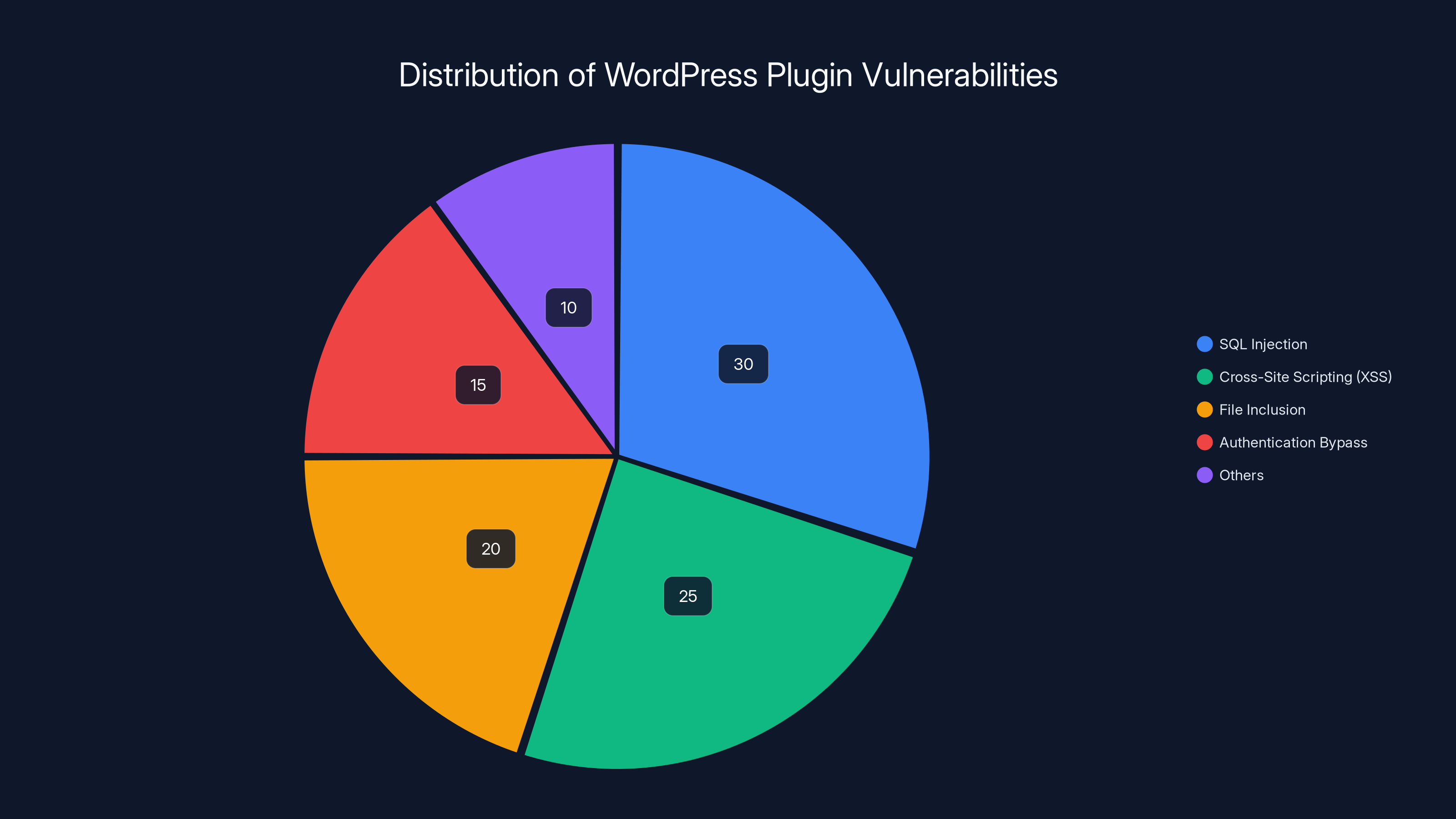
Estimated data shows SQL Injection and XSS as leading vulnerabilities in WordPress plugins, highlighting areas for security focus.
Understanding Arbitrary File Read Vulnerabilities
An Arbitrary File Read vulnerability is a significant security threat. It allows attackers to read any file on the server, provided they know its path and the server process has read permissions. This can include sensitive files like wp-config.php, which contains database credentials and other critical configuration details.
How Do These Vulnerabilities Occur?
Such vulnerabilities often arise due to improper input validation. When a plugin or theme does not adequately validate or sanitize input data, it opens the door for attackers to supply unexpected input, leading to unintended behavior.
Real-World Example
Imagine a website that allows users to upload files. If the upload script does not properly validate the file path or name, an attacker could potentially craft a request that tricks the server into reading files outside the intended directory.
Protecting Your WordPress Site
While vulnerabilities are a reality in the digital world, there are several steps you can take to protect your WordPress site.
1. Regular Updates
Keeping your WordPress core, themes, and plugins up to date is crucial. Developers frequently release updates to patch security vulnerabilities.
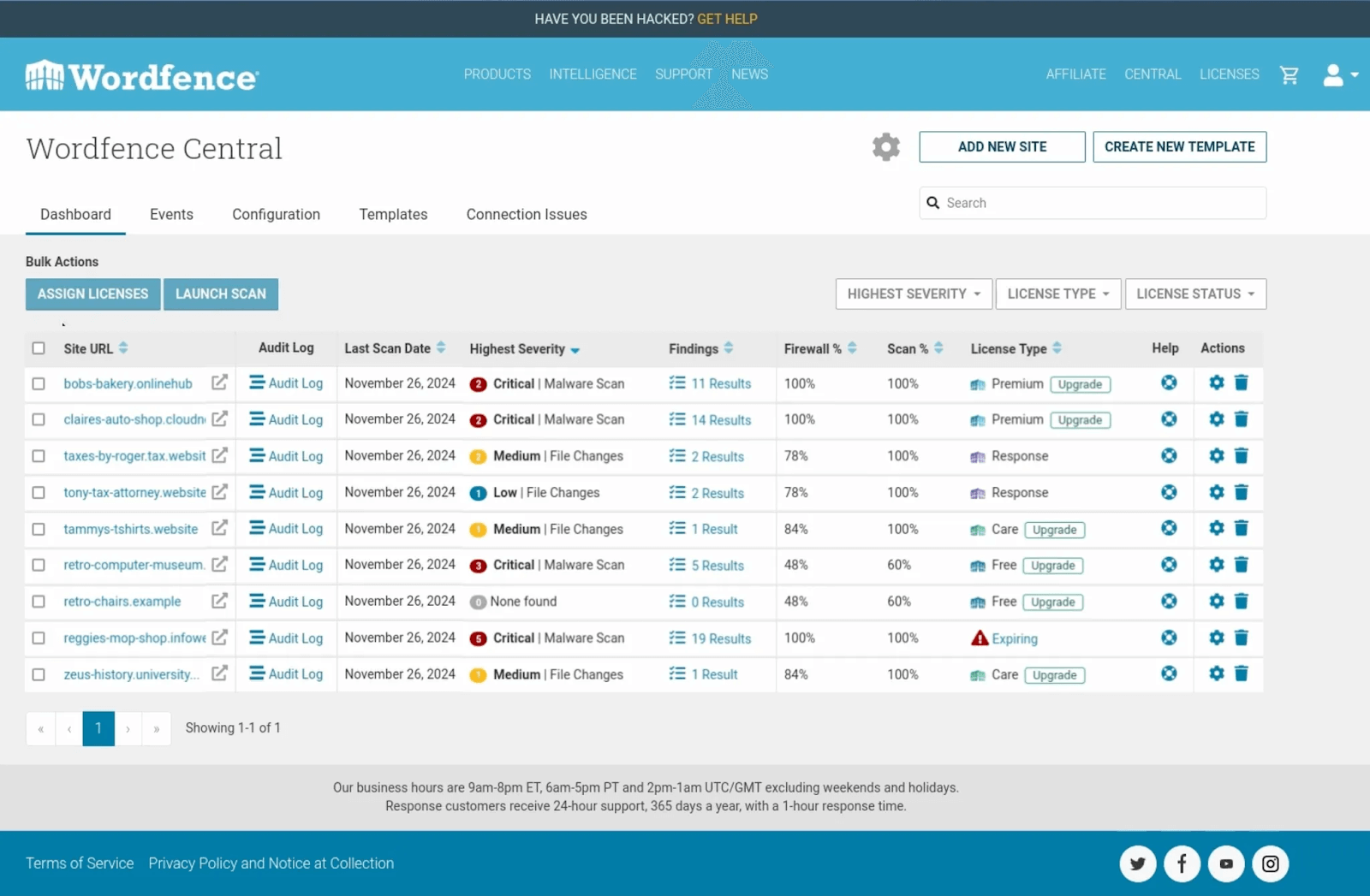
2. Employ Security Plugins
Security plugins provide an additional layer of protection. Popular options include Wordfence, Sucuri Security, and iThemes Security. These plugins offer features like firewall protection, malware scanning, and brute force attack prevention.
3. Regular Backups
Ensure you have regular backups of your website. In case of an attack, you can restore your site to a previous state. Use plugins like UpdraftPlus or BackupBuddy for automated backups.
4. Strong Passwords and User Permissions
Use strong, unique passwords for all user accounts. Limit user permissions to only what is necessary for each role.
5. Security Audits
Conduct regular security audits to identify and fix vulnerabilities. Automated tools like WPScan can help you find potential issues.
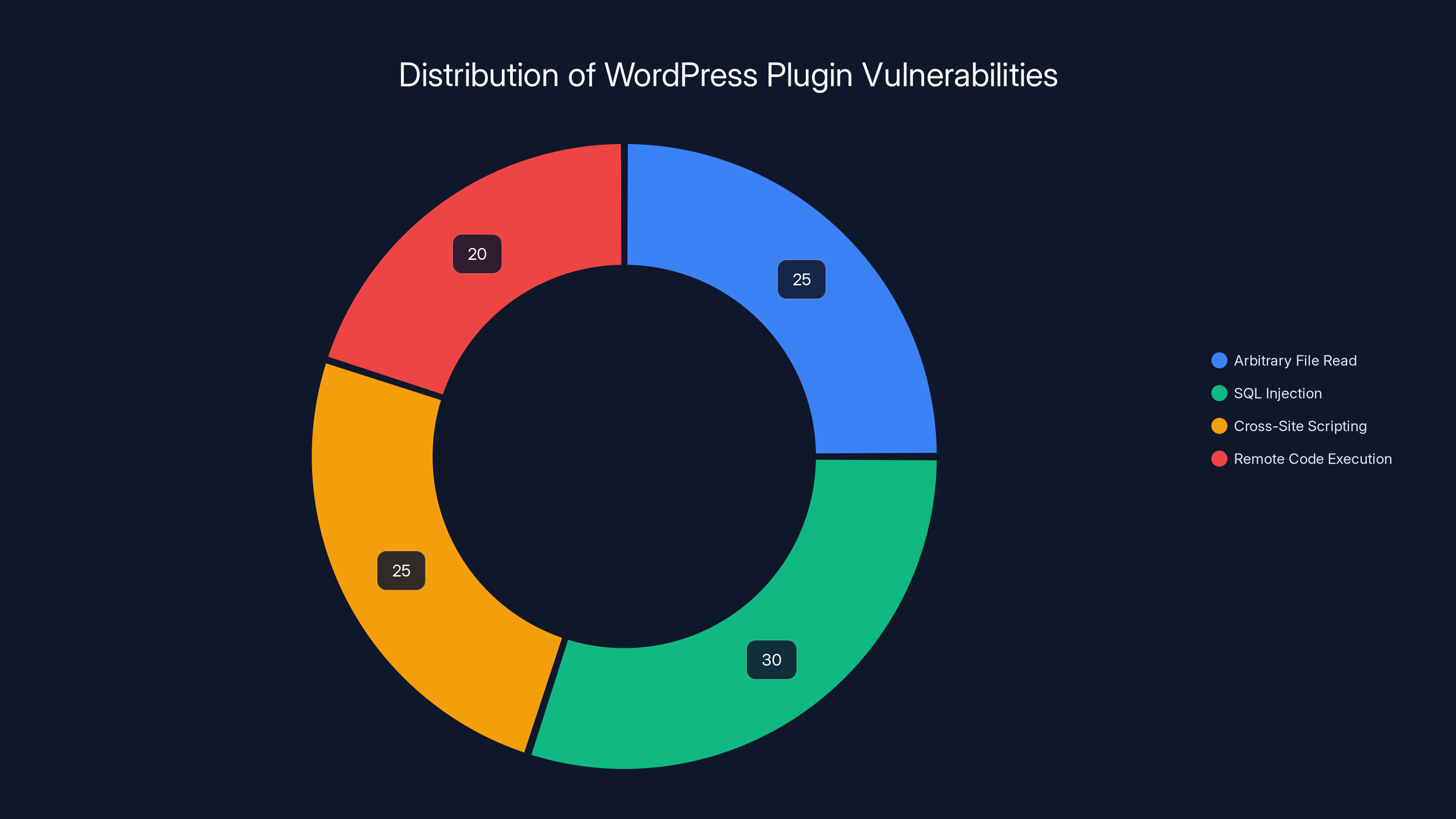
Arbitrary File Read vulnerabilities, like the one found in Smart Slider 3, account for an estimated 25% of common WordPress plugin vulnerabilities. Estimated data.
Common Pitfalls and How to Avoid Them
Ignoring Update Notifications
Many site owners ignore update notifications due to fear of breaking their site. However, outdated plugins are a common vector for attacks.
Using Nulled Plugins
Nulled plugins, or pirated versions, often contain malware or backdoors. Always download plugins from reputable sources.
Poor Hosting
Your hosting provider plays a critical role in your site's security. Choose a provider that offers robust security features, including DDoS protection and SSL certificates.
Future Trends in WordPress Security
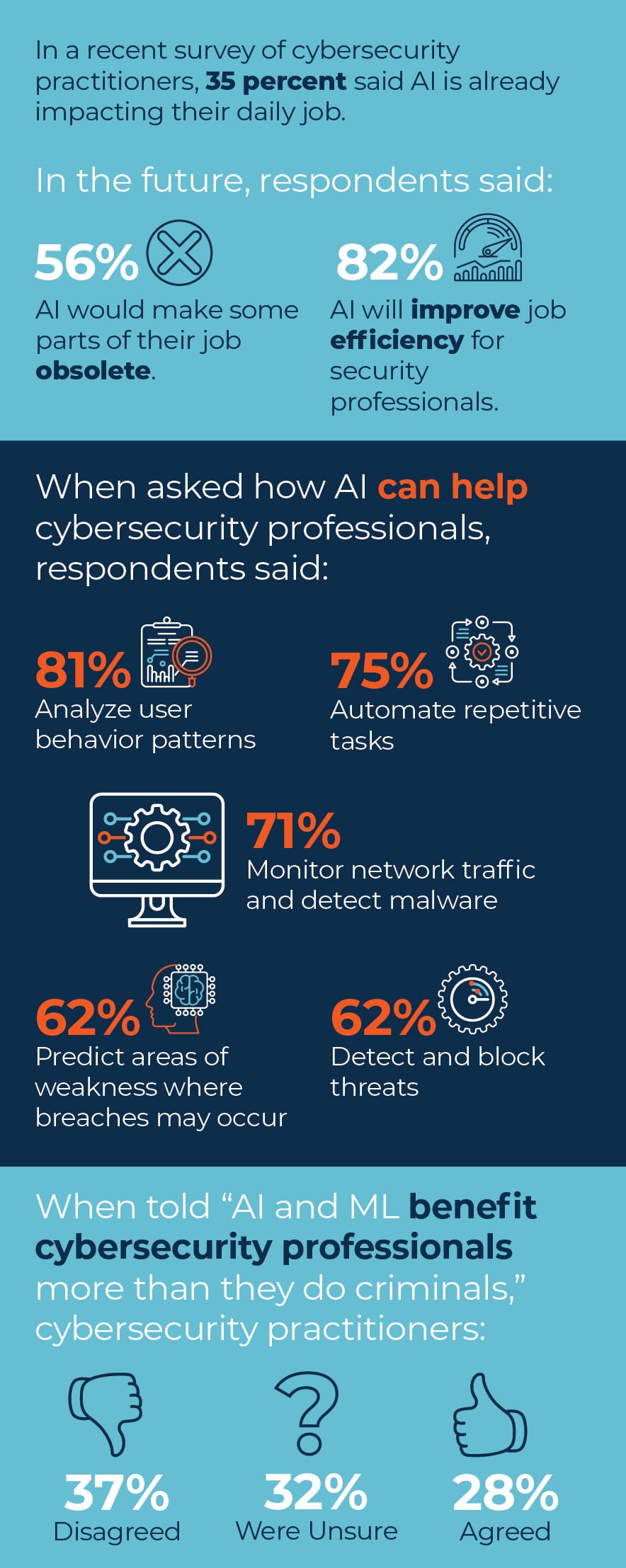
AI and Machine Learning
AI and machine learning are becoming integral to cybersecurity. Tools that leverage these technologies can detect and respond to threats in real-time, adapting to new attack vectors.
Blockchain for Security
Blockchain technology offers potential for enhancing security through its decentralized and immutable nature. While still in the early stages, it's an area to watch.

Recommendations for WordPress Users
- Stay Informed: Follow security blogs and forums to keep up with the latest vulnerabilities and fixes.
- Invest in Security: Consider premium security plugins and services for comprehensive protection.
- Educate Your Team: Ensure everyone involved with your site understands security best practices.

Implementing a Security Strategy
Step-by-Step Guide
- Assess Current Security: Conduct a thorough audit of your site's current security measures.
- Plan for Improvements: Identify areas for improvement and prioritize based on risk.
- Implement Changes: Deploy security plugins, update configurations, and fix any vulnerabilities.
- Monitor and Adjust: Regularly review security logs and make adjustments as needed.
Conclusion
WordPress security is an ongoing process that requires vigilance and proactive measures. By understanding the risks and implementing the strategies outlined in this article, you can significantly reduce the risk of your site falling victim to attacks.
FAQ
What is an Arbitrary File Read vulnerability?
An Arbitrary File Read vulnerability allows attackers to read files on a server without authorization, which can expose sensitive data.
How can I secure my WordPress site against plugin vulnerabilities?
Regularly update all plugins, use security plugins like Wordfence, and conduct frequent security audits to identify and fix vulnerabilities.
Why are nulled plugins dangerous?
Nulled plugins often contain hidden malware or backdoors, posing significant security risks to your site.
What should I do if my site gets hacked?
Immediately restore from a backup, change all passwords, and conduct a full security audit to identify and patch the vulnerability.
How often should I update my WordPress site?
Update WordPress core, themes, and plugins as soon as updates are available to minimize security risks.
Key Takeaways
- A recent plugin vulnerability affected 500,000 WordPress sites.
- Regular updates are crucial to maintaining website security.
- Security plugins offer essential protection against threats.
- Avoiding nulled plugins prevents potential malware infections.
- Future trends include AI and blockchain for enhanced security.
Related Articles
- The Human Cost of Cybersecurity and Solutions for 2025
- World Backup Day 2026: Save Big with Top NAS Deals and Best Practices
- World Backup Day 2026: Ultimate Guide to Ensuring Data Safety and Security
- European Commission Data Breach: What Happened and How to Respond [2025]
- Why October 1, 2026, Could Be the Day SSL/TLS Certificates 'Break the Internet' [2025]
- Why Millions of Business Laptops Lag Behind Updates: The Hidden Costs of Ignoring IT Maintenance [2025]
![WordPress Plugin Security Flaws: Understanding Risks and Protecting Your Site [2025]](https://tryrunable.com/blog/wordpress-plugin-security-flaws-understanding-risks-and-prot/image-1-1774892174722.jpg)



