Ajax's Data Breach: Lessons and Strategies for Protecting Fan Information [2025]
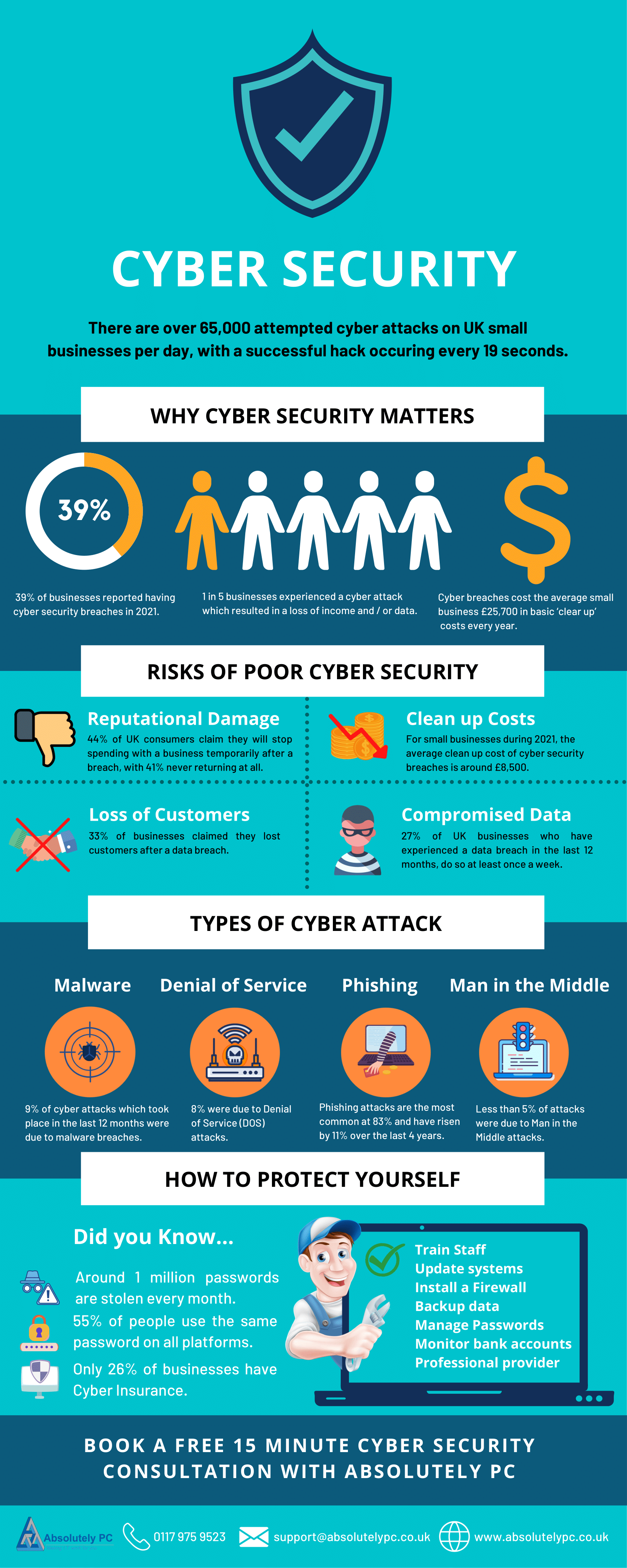
In a digital age where trust is as fragile as it is crucial, Ajax Amsterdam's recent data breach serves as a stark reminder of the vulnerabilities inherent in our interconnected world. The breach, affecting personal information of 300,000 fans, underscores a critical need for robust cybersecurity measures. Let's delve into what happened, why it matters, and how organizations can protect themselves from similar occurrences.
TL; DR
- Key Point 1: Ajax's data breach exposed sensitive information of 300,000 fans, highlighting major cybersecurity gaps.
- Key Point 2: The breach was enabled by a flaw in an app, allowing unauthorized access to personal data and system manipulations.
- Key Point 3: Proactive measures like regular security audits and intrusion detection systems are essential.
- Key Point 4: Organizations should adopt zero-trust architectures to minimize access vulnerabilities.
- Bottom Line: Strengthening cybersecurity protocols is imperative to protect sensitive user data and maintain trust.
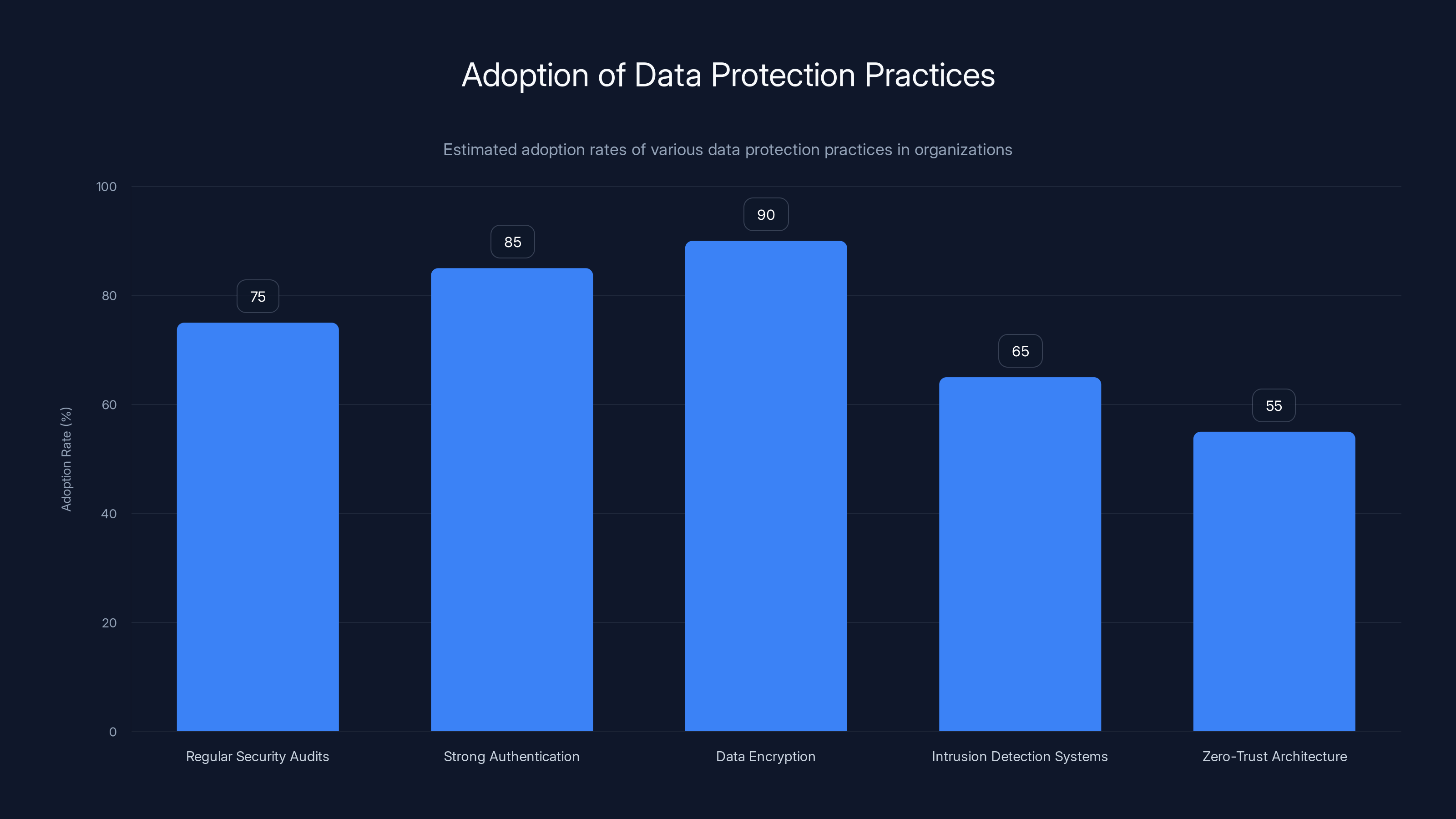
Data encryption and strong authentication mechanisms are the most widely adopted practices, with adoption rates of 90% and 85% respectively. Estimated data.
Understanding the Breach
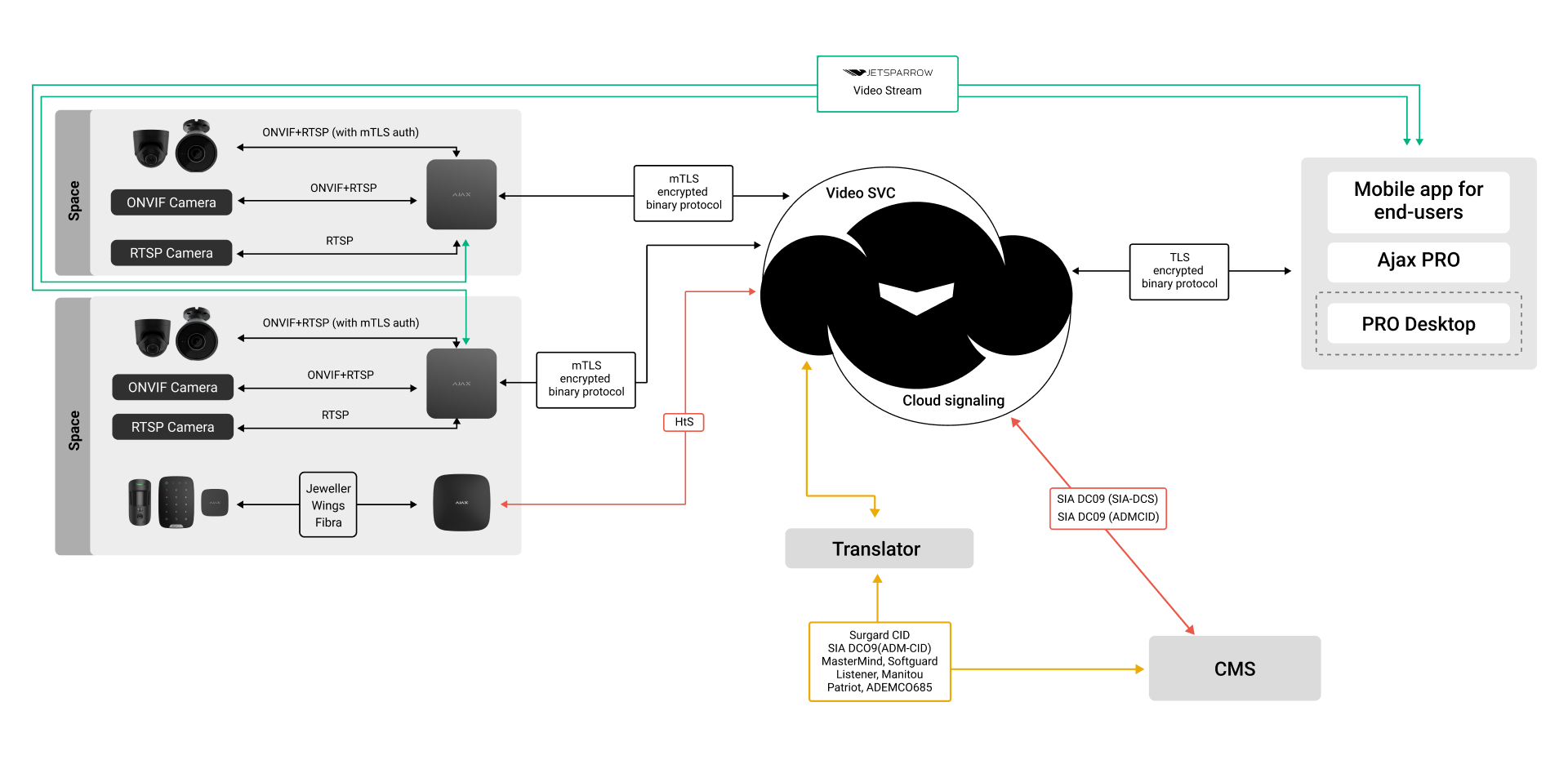
Ajax Amsterdam, a prestigious football club, revealed a significant data breach compromising the personal information of 300,000 fans. The breach was facilitated through a bug in their mobile application, which allowed unauthorized access to sensitive data, including email addresses and possibly more personal details.
The Flaw in the System
The underlying issue stemmed from a vulnerability in the app's code, which permitted hackers to bypass authentication protocols. This breach of security not only exposed personal data but also allowed malicious actors to manipulate system functionalities, such as ticket transfers and stadium ban removals.
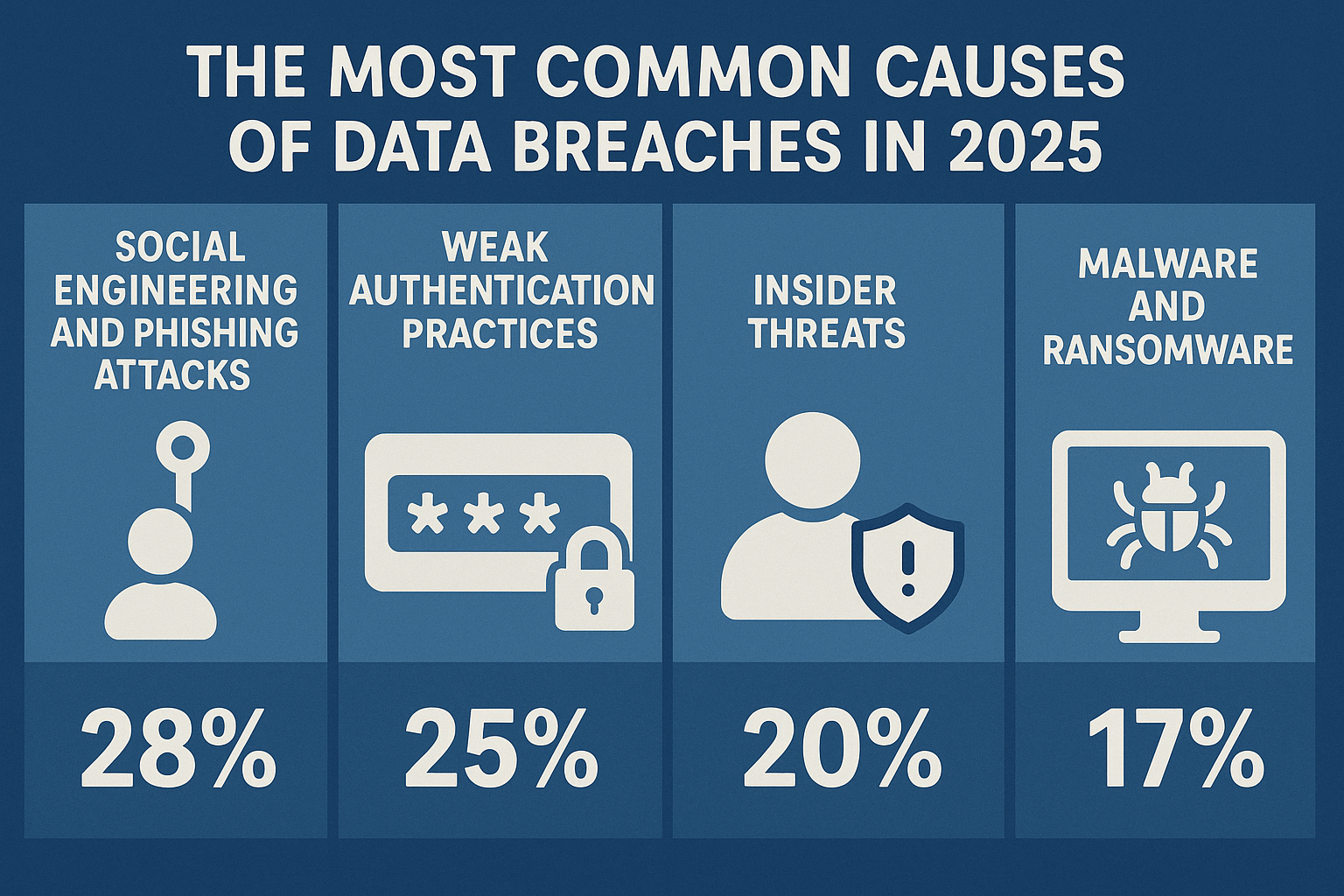
What Went Wrong:
- Authentication Bypass: Weak authentication measures enabled unauthorized access.
- Lack of Encryption: Insufficient data encryption allowed data to be accessed in plain text.
- Inadequate Monitoring: A lack of real-time monitoring delayed the detection of unauthorized access.
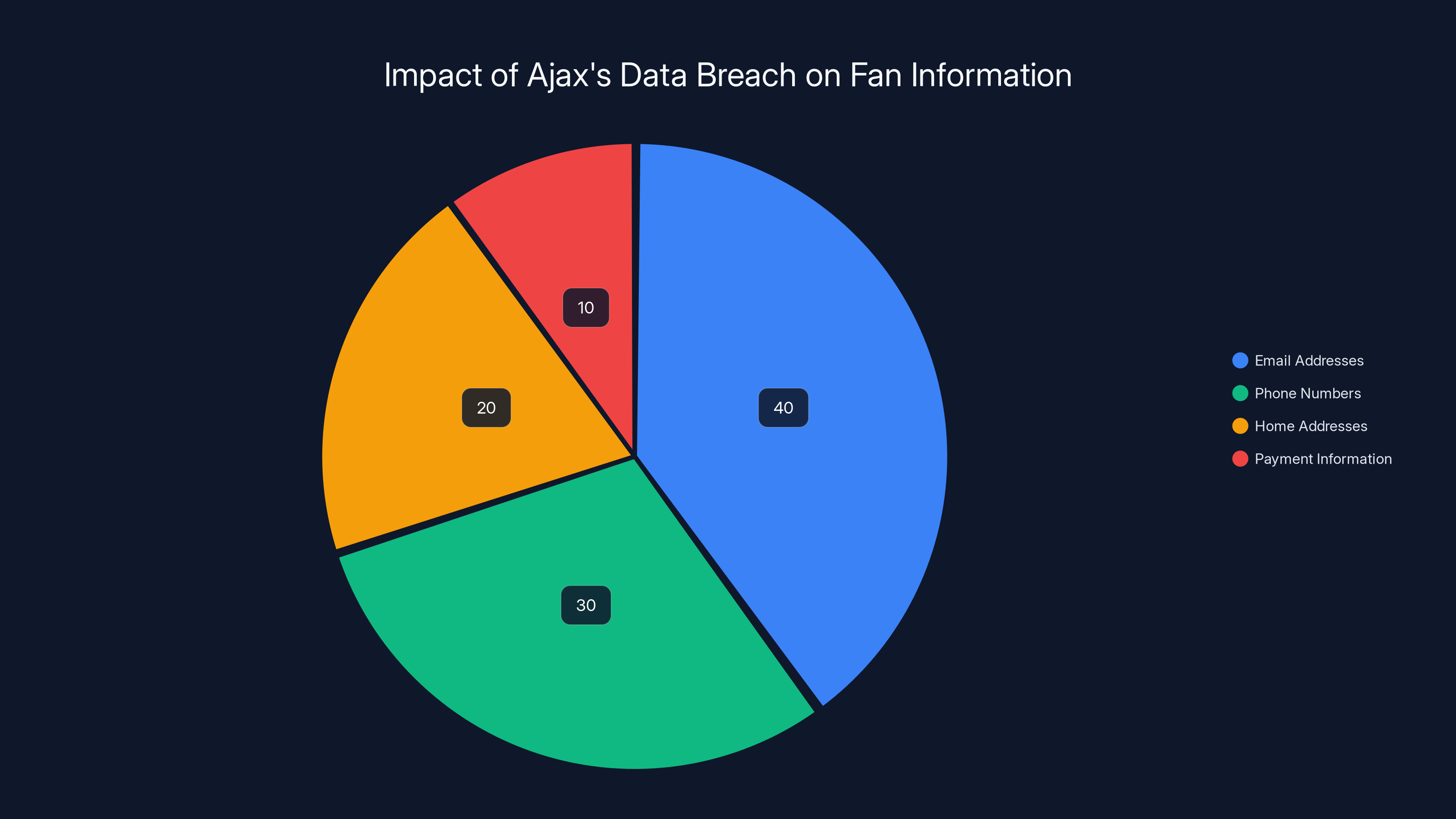
Estimated data shows email addresses were the most compromised, making up 40% of the breach, highlighting the need for secure communication channels.
Real-World Implications
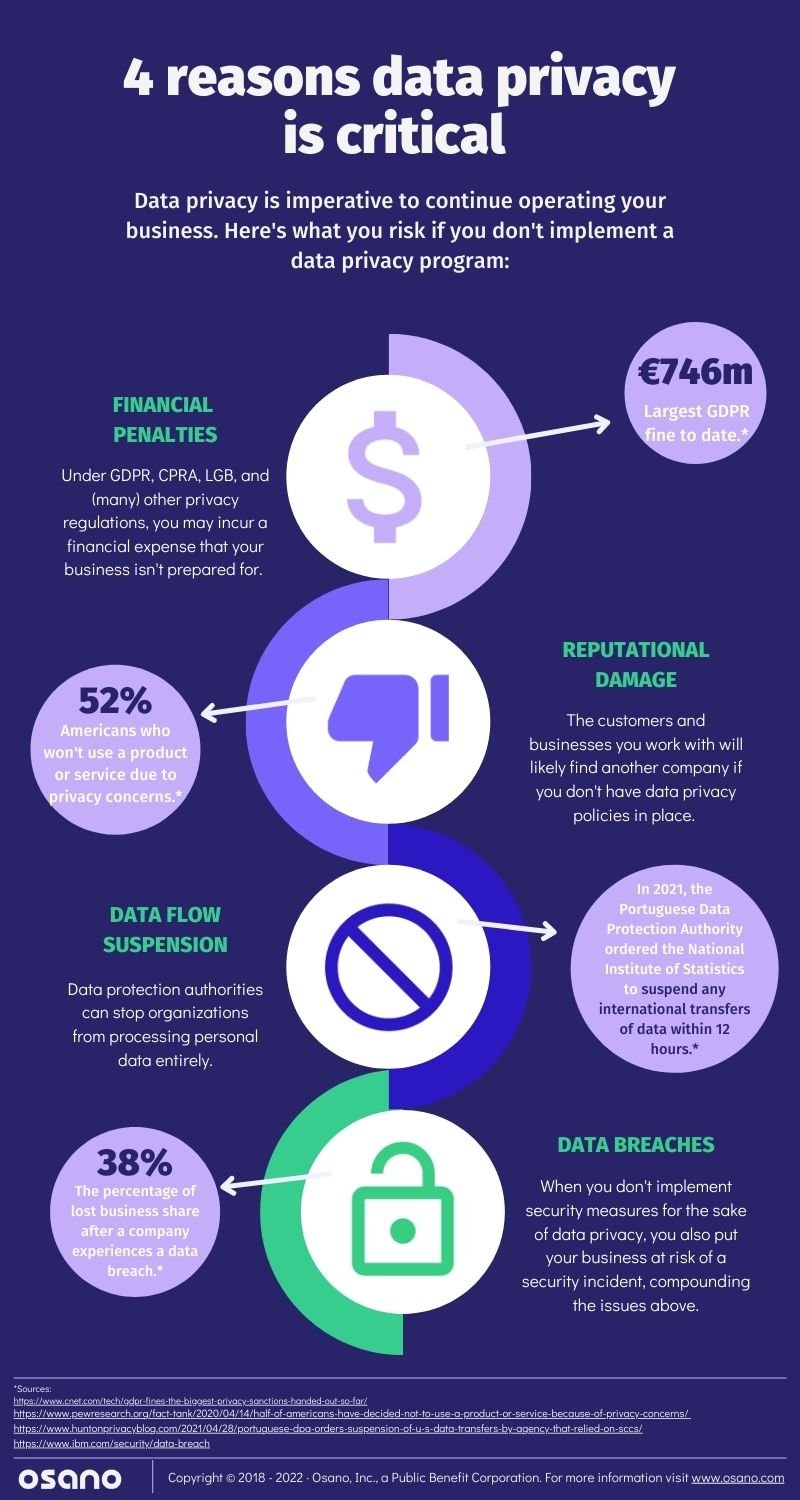
The breach has significant implications for both Ajax and its fans. For the fans, there's the immediate concern of identity theft and privacy invasion. For Ajax, the breach could mean not only financial penalties but also a loss of trust among its fanbase.
Impact on Fans
Fans affected by the breach face potential risks including:
- Identity Theft: Personal information could be used fraudulently.
- Phishing Attacks: Exposed email addresses may attract targeted phishing attempts.
- Loss of Trust: Fans may lose confidence in the club's ability to protect their data.
Impact on Ajax
The club is likely to face reputational damage, potential legal actions, and financial losses due to:
- GDPR Violations: Non-compliance with data protection regulations can lead to hefty fines.
- Reputational Damage: Damage to brand image may affect sponsorships and partnerships.
- Operational Disruptions: Addressing the breach diverts resources from regular operations.
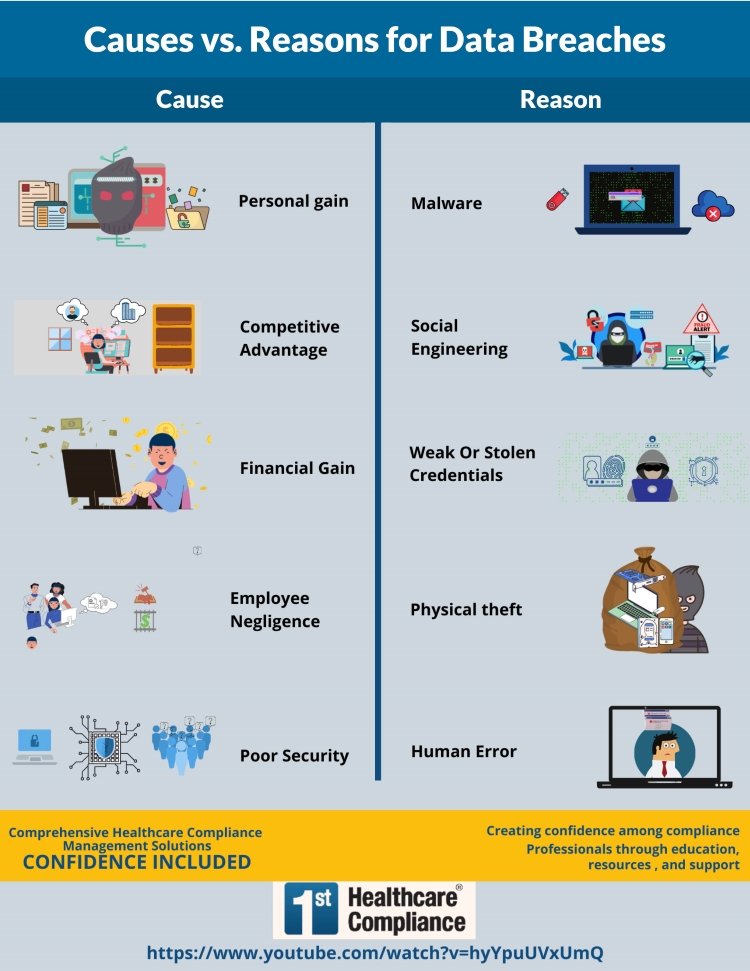
Best Practices for Data Protection
In light of the Ajax breach, organizations must reassess their cybersecurity strategies. Here are some best practices to consider:
1. Conduct Regular Security Audits
Frequent security audits help identify vulnerabilities before they can be exploited. These audits should cover:
- Code Reviews: Regular examination of application code for security flaws.
- Penetration Testing: Simulated cyberattacks to test defenses.
2. Implement Strong Authentication Mechanisms
Strengthening authentication protocols can prevent unauthorized access:
- Multi-Factor Authentication (MFA): Requiring additional verification steps.
- Biometric Authentication: Using fingerprints or facial recognition for access.
3. Encrypt Sensitive Data
Data encryption ensures that even if data is accessed, it remains unreadable without the proper decryption key.
4. Deploy Intrusion Detection Systems (IDS)
IDS can identify suspicious activity and alert administrators to potential security breaches in real-time.
5. Adopt a Zero-Trust Architecture
Zero-trust models assume that threats could be both external and internal, requiring verification at every access point within the network.
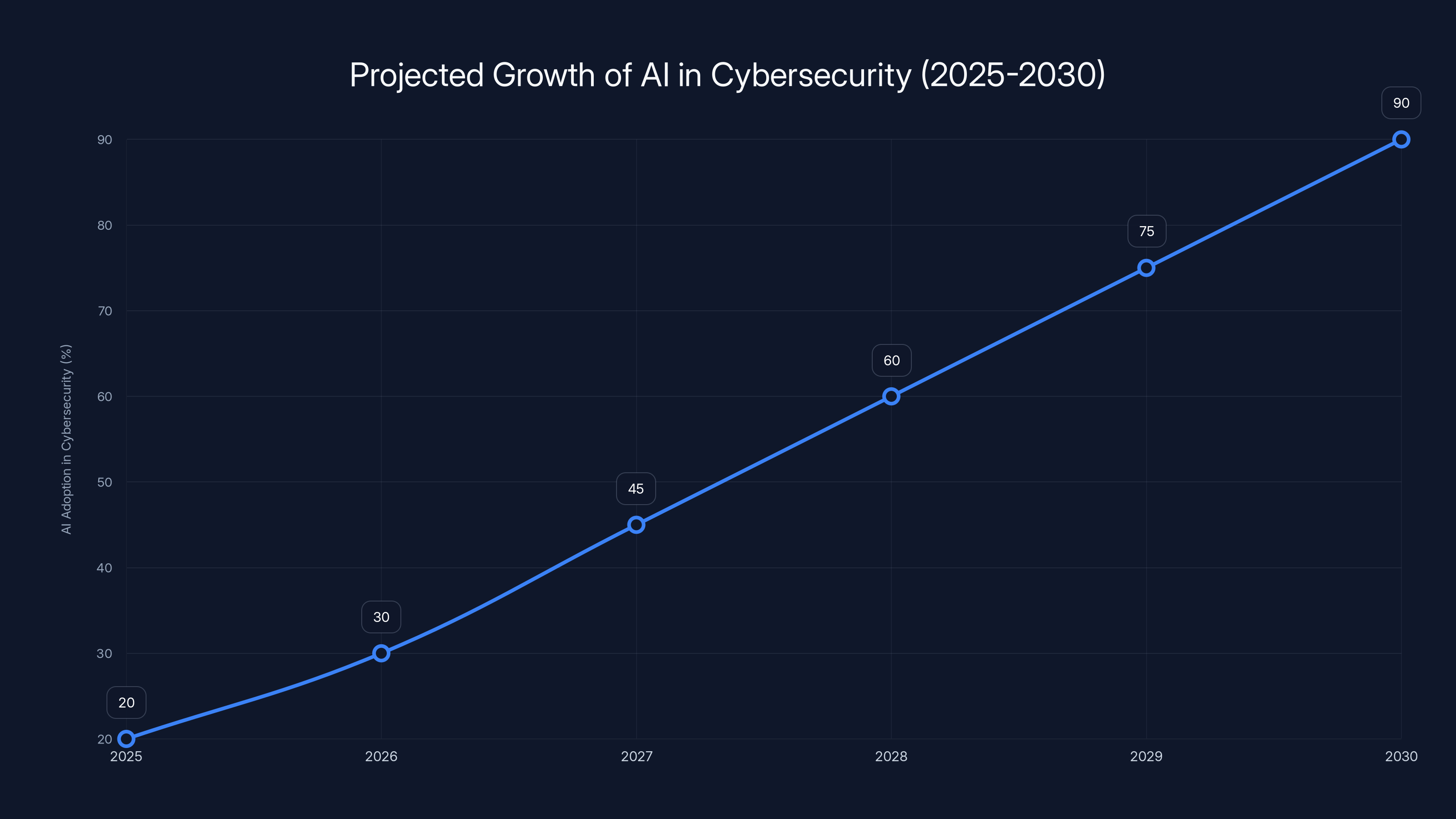
AI adoption in cybersecurity is projected to grow significantly, reaching 90% by 2030. Estimated data based on industry trends.
Common Pitfalls and Solutions
While the strategies above are essential, there are common pitfalls organizations should avoid:
Pitfall 1: Complacency
Assuming that existing measures are sufficient can lead to vulnerabilities. Regular updates and continuous improvement are crucial.
Solution:
- Continuous Learning: Stay informed about the latest cybersecurity threats and technologies.
Pitfall 2: Over-Reliance on Technology
While technology is key, it should not replace human oversight.
Solution:
- Human Oversight: Regularly train staff to recognize and respond to security threats.
Pitfall 3: Ignoring Insider Threats
Internal threats can be as damaging as external ones.
Solution:
- Access Controls: Limit access to sensitive data based on roles and responsibilities.
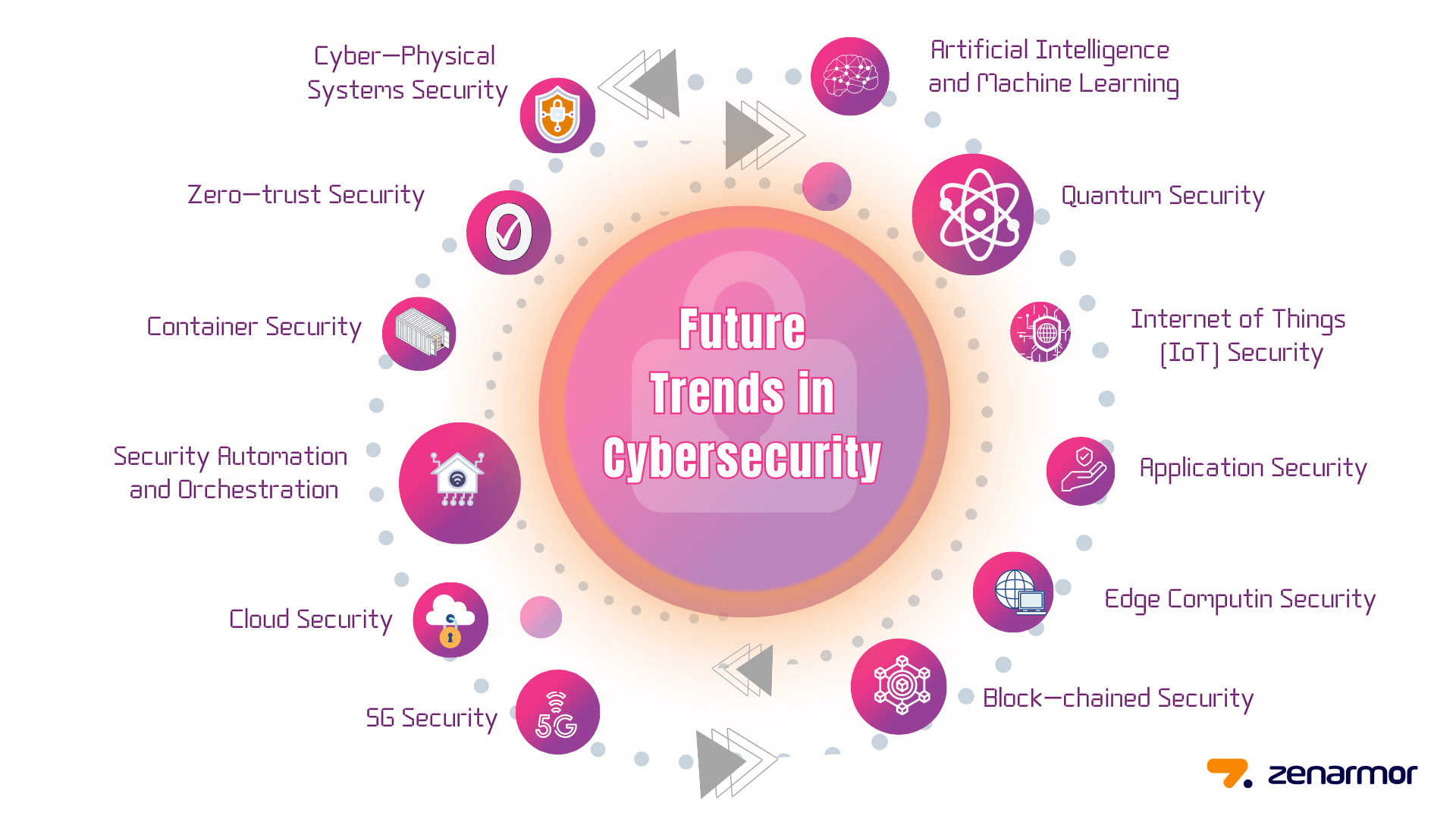
Future Trends in Cybersecurity
As threats evolve, so too must the strategies to combat them. Here are some trends to watch:
AI and Machine Learning in Cybersecurity
AI can automate threat detection and response, improving reaction times and reducing human error.
Blockchain for Data Integrity
Blockchain technology offers a decentralized approach to data integrity, making unauthorized alterations more difficult.
Enhanced Privacy Regulations
Expect tighter regulations globally, emphasizing user privacy and data protection.
Recommendations for Ajax and Similar Organizations
To prevent future breaches, organizations like Ajax should:
- Invest in Cybersecurity Training: Equip teams with the skills needed to protect sensitive data.
- Engage Ethical Hackers: Regularly employ ethical hackers to identify potential vulnerabilities.
- Enhance Incident Response Plans: Have a clear, actionable plan for responding to breaches.
Conclusion
The Ajax data breach is a cautionary tale about the importance of cybersecurity. By understanding the risks and implementing robust security measures, organizations can protect sensitive data and maintain trust. As technology evolves, so too must our approaches to security, ensuring safe digital environments for all users.
FAQ
What caused the Ajax data breach?
The breach was caused by a vulnerability in Ajax's mobile application, which allowed unauthorized access to sensitive fan data.
How can organizations prevent data breaches?
Organizations can prevent data breaches by implementing strong authentication measures, conducting regular security audits, and using encryption.
What are the risks of a data breach for fans?
Fans face potential identity theft, phishing attacks, and a loss of trust in the organization.
How does a zero-trust architecture help in cybersecurity?
Zero-trust architecture requires verification at every access point, minimizing the risk of unauthorized access.
What role does AI play in cybersecurity?
AI can automate threat detection and response, improving efficiency and reducing human error in cybersecurity measures.
Why is human oversight important in cybersecurity?
Human oversight ensures that technology is used effectively and that staff can recognize and respond to threats not detectable by systems alone.
What future trends should organizations watch in cybersecurity?
Organizations should watch for advancements in AI, blockchain technology, and enhanced privacy regulations as key trends in cybersecurity.
How can Ajax regain trust after the breach?
Ajax can regain trust by transparently communicating their response, enhancing security measures, and demonstrating commitment to data protection.
Key Takeaways
- Proactive security measures are essential to prevent breaches.
- Zero-trust architectures minimize vulnerabilities.
- AI can automate threat detection and improve response times.
- Regular security audits are crucial for identifying weaknesses.
- Data encryption protects against unauthorized access.
- Human oversight remains important in cybersecurity.
Related Articles
- The Greek Spyware Scandal: Lessons from the Convicted Spy Chief's Controversy [2025]
- Databricks' Strategic Acquisition: A Deep Dive Into Lakewatch and AI Security [2025]
- Cyber-Resilience for the Modern Data Center: Strategies and Best Practices [2025]
- Understanding the LLM PyPl Package Compromise [2025]
- Understanding and Mitigating AI Vulnerabilities: The Guilt-Trip Phenomenon in OpenClaw Agents [2025]
- Navigating the Implications: Supreme Court Rules Cox Communications Not Liable for Pirated Music [2025]
![Ajax's Data Breach: Lessons and Strategies for Protecting Fan Information [2025]](https://tryrunable.com/blog/ajax-s-data-breach-lessons-and-strategies-for-protecting-fan/image-1-1774523085051.jpg)



