The Greek Spyware Scandal: Lessons from the Convicted Spy Chief's Controversy [2025]
The world of cybersecurity is no stranger to scandals, but the recent controversy surrounding the use of Predator spyware in Greece has captivated global attention. The incident, often dubbed as the “Greek Watergate,” involved widespread phone hacking, allegedly orchestrated by government insiders with the help of a sophisticated spyware tool. This article delves into the technical and ethical dimensions of the scandal, exploring the implications for national security, privacy rights, and the future of cybersecurity.
TL; DR
- Spyware Usage in Greece: The Predator spyware was used to hack phones of government officials, opposition leaders, and journalists, as reported by BBC News.
- Legal Repercussions: Executives from Intellexa, the spyware maker, were convicted for illegal data acquisition, according to ICIJ.
- Government Involvement Allegations: Suspicions arose regarding the Greek government's role in the surveillance operations, highlighted by Politico.
- Impact on Privacy: The scandal underscores the vulnerabilities in digital communication systems, as discussed in SecurityWeek.
- Future of Cybersecurity: Calls for more robust legal frameworks and ethical standards in spyware development are emerging, as noted by Mashable.

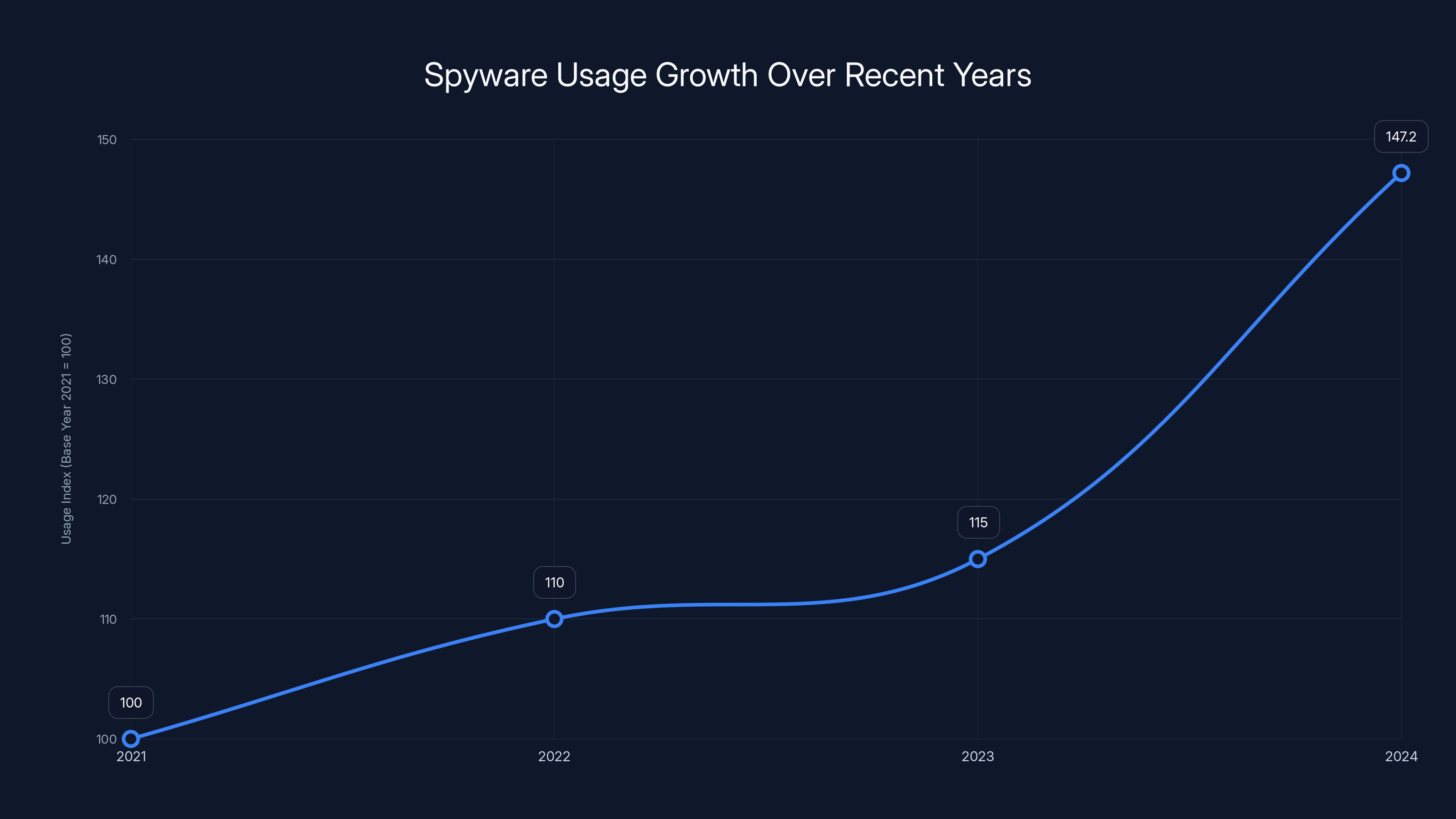
Spyware usage has shown a significant increase, with a 28% rise in 2024 compared to the previous year, highlighting the growing challenge of digital surveillance. Estimated data.
Understanding the Predator Spyware
Predator spyware, developed by Intellexa, is a tool designed to infiltrate smartphones by exploiting vulnerabilities within both iOS and Android operating systems. It operates by tricking users into clicking on malicious links, thereby gaining unauthorized access to sensitive information such as call logs, messages, emails, and even real-time location data, as detailed in PCMag.
How Predator Works
At its core, Predator functions through sophisticated phishing techniques. Once a target clicks on a deceptive link, the spyware installs itself on the device, operating stealthily in the background. Its capabilities include:
- Data Extraction: Seamlessly extracts call logs, texts, and emails.
- Location Tracking: Monitors the real-time location of the device.
- Microphone Activation: Turns on the device’s microphone to eavesdrop on conversations.
Technical Architecture
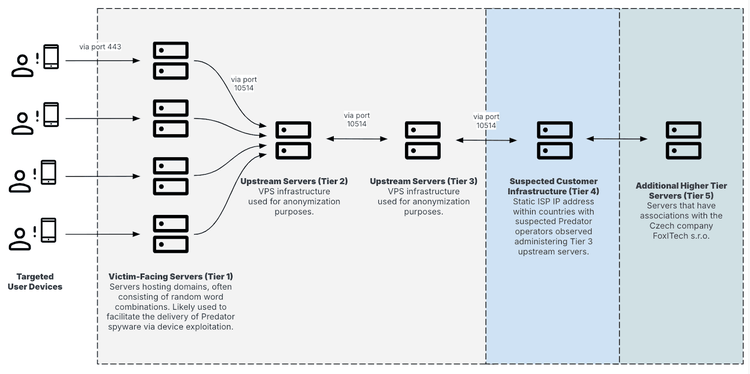
Predator relies on an intricate architecture involving several components:
- Command and Control Servers (C2): These servers issue commands to the infected devices and receive extracted data.
- Exploit Kits: Tailored scripts that exploit specific vulnerabilities in operating systems.
- Payload Delivery: Automated systems that ensure the spyware is delivered efficiently and discreetly.
Preventive Measures
To protect against such spyware, individuals and organizations are advised to:
- Verify Links: Avoid clicking on suspicious links from unknown sources.
- Update Software: Regularly update operating systems and applications to patch vulnerabilities, as recommended by VPNOverview.
- Use Security Apps: Employ reputable antivirus software that can detect and neutralize threats.
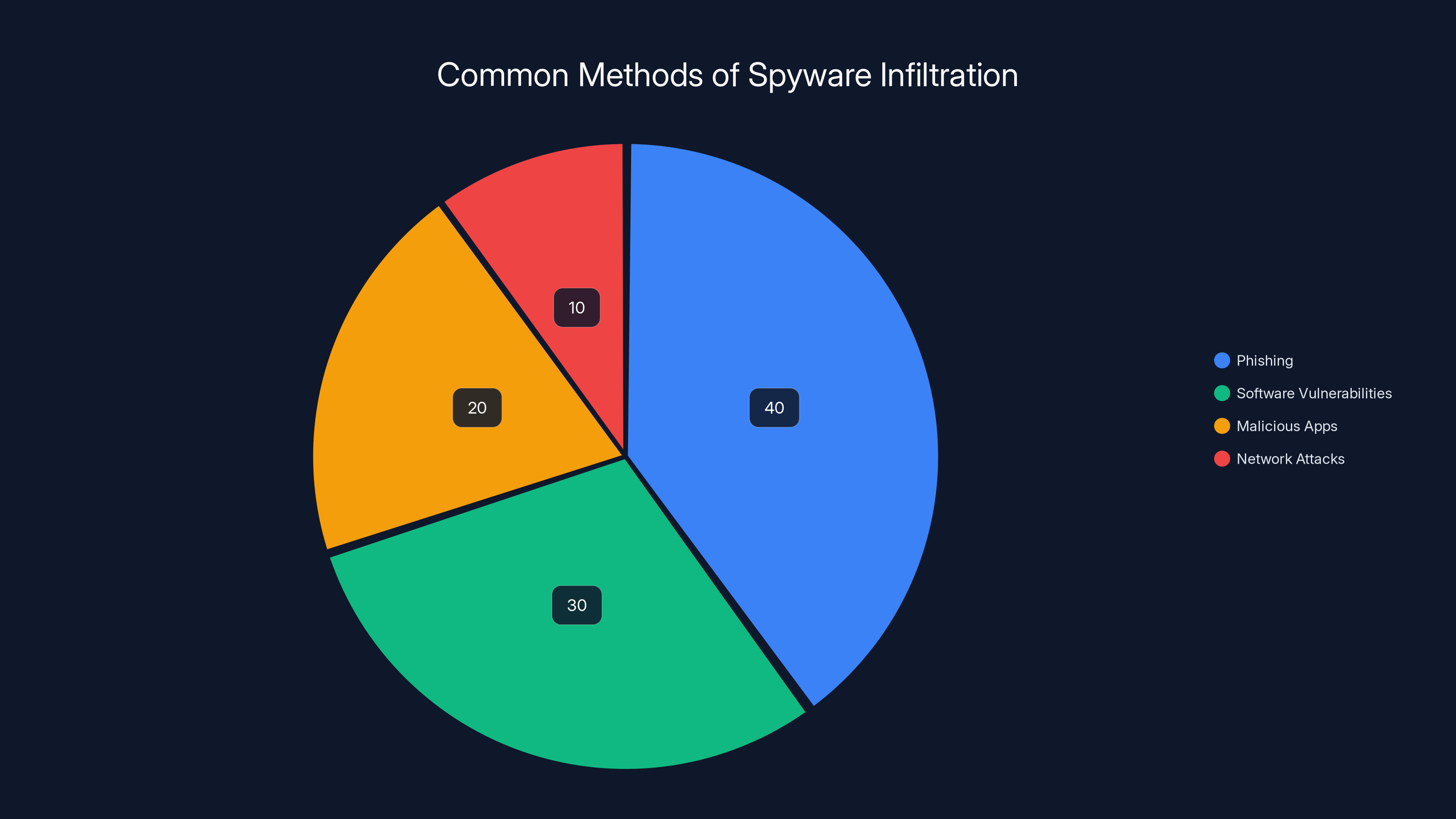
Phishing is estimated to be the most common method of spyware infiltration, accounting for 40% of cases. Estimated data.
The Greek Watergate: A Closer Examination
The scandal unfolded when it was discovered that numerous high-profile individuals in Greece were targets of the Predator spyware. This included senior government ministers, opposition leaders, military officials, and journalists, raising questions about the sanctity of personal privacy and national security.
Key Players and Events
- Intellexa Executives: The company's founder and three other executives were convicted for illegally obtaining personal data, as reported by ICIJ.
- Government Resignations: The head of Greece’s national intelligence agency and a senior aide to Prime Minister Kyriakos Mitsotakis resigned amidst the scandal, according to BBC News.
- Judicial Inquiries: A series of legal investigations were launched to uncover the full extent of the espionage activities, as noted by Politico.
Allegations of Government Involvement
Despite the convictions, no government officials have been directly implicated. However, the widespread nature of the surveillance has led many to speculate about possible governmental complicity. Investigative journalists have suggested that the operations could not have been executed on such a scale without some level of state involvement, as discussed in SecurityWeek.
Legal and Ethical Implications
The case has reignited debates over the ethical use of surveillance tools and the legal frameworks governing their deployment. Key issues include:
- Accountability: Who should be held responsible when spyware is misused?
- Oversight: How can governments ensure that intelligence agencies comply with legal and ethical standards?
- Privacy Rights: What protections should be in place to safeguard citizens from unwarranted surveillance?

Spyware in the Modern Era: Challenges and Solutions
The Greek scandal is a microcosm of broader challenges faced in the digital age, where spyware is increasingly used for both legitimate and nefarious purposes.
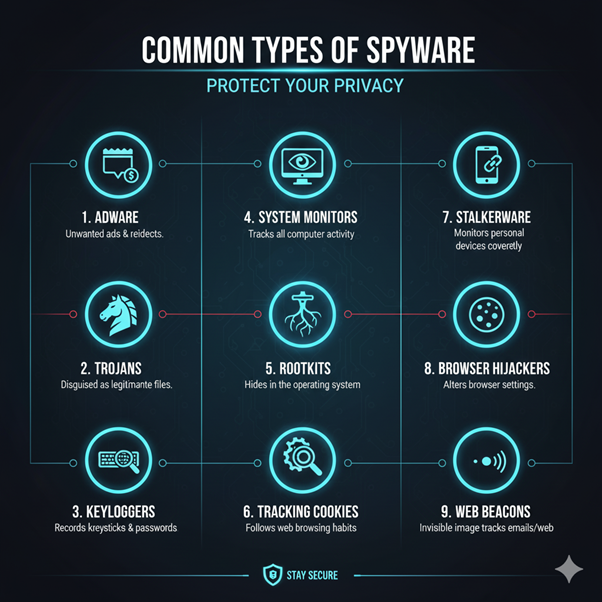
Common Uses of Spyware
- Law Enforcement: Used to track criminal activities and gather intelligence.
- Corporate Espionage: Employed by businesses to gain a competitive edge by spying on rivals.
- Personal Surveillance: Sometimes used in domestic disputes to monitor partners or family members.
Risks and Pitfalls
- Loss of Privacy: Unchecked use of spyware can lead to significant violations of personal privacy.
- Data Breaches: Compromised devices can result in massive data leaks.
- Legal Consequences: Organizations using spyware unlawfully may face severe legal repercussions.
Best Practices for Spyware Mitigation
Organizations can take several steps to protect themselves from spyware threats:
- Implement Strong IT Policies: Develop and enforce robust cybersecurity policies.
- Employee Training: Educate employees on recognizing and avoiding phishing attempts.
- Regular Audits: Conduct frequent security audits to identify and address vulnerabilities.
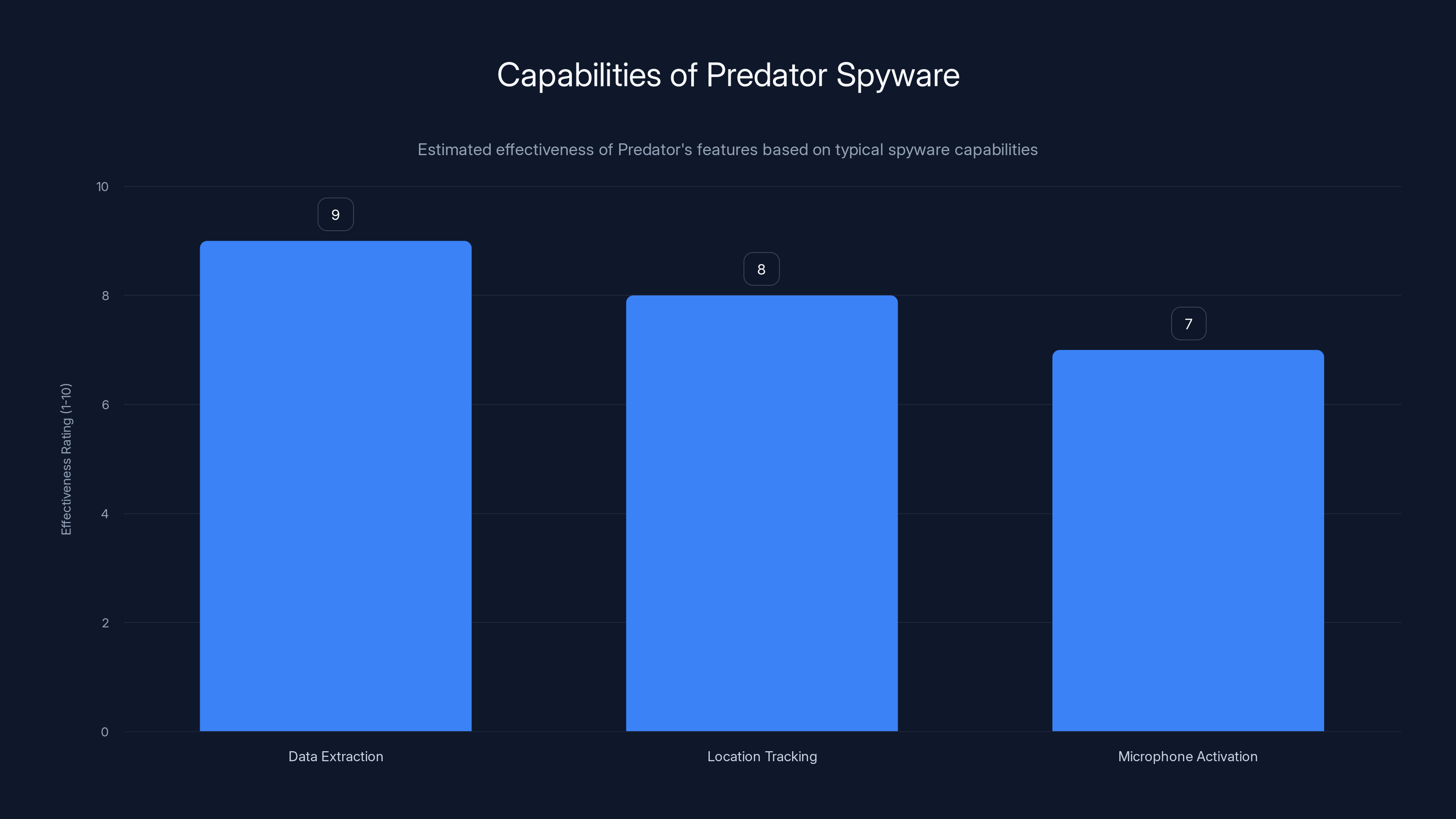
Predator spyware is highly effective in extracting data, tracking location, and activating microphones, with ratings of 9, 8, and 7 respectively. Estimated data.
Future Trends in Cybersecurity
The Greek spyware scandal has underscored the need for advancements in cybersecurity strategies. Here are some emerging trends:
AI and Machine Learning
Artificial intelligence and machine learning are increasingly being used to detect and neutralize spyware threats. These technologies can:
- Identify Anomalies: Detect unusual patterns that may indicate a security breach.
- Automate Responses: Quickly respond to threats without human intervention.
Blockchain Technology
Blockchain's decentralized nature offers promising potential for enhancing security measures. It can be used to:
- Secure Data Transmission: Ensure data integrity and authenticity.
- Enhance Privacy: Enable anonymous transactions and communications.

Conclusion
The Greek spyware scandal serves as a stark reminder of the complexities surrounding digital surveillance. As technology evolves, so too must our approaches to safeguarding privacy and security. By adopting a proactive stance and leveraging cutting-edge technologies, individuals and organizations can better protect themselves against future threats.
FAQ
What is Predator spyware?
Predator is a type of spyware developed by Intellexa, capable of infiltrating smartphones to extract sensitive information by exploiting system vulnerabilities.
How does Predator spyware infiltrate devices?
It uses phishing techniques to trick users into clicking malicious links, which then install the spyware onto their devices.
What was the Greek Watergate scandal?
A mass-wiretapping campaign in Greece where Predator spyware was used to hack the phones of government officials, journalists, and others.
How can individuals protect themselves from spyware?
By verifying links before clicking, regularly updating software, and using reputable security apps.
What are the ethical concerns surrounding spyware use?
Key concerns include privacy violations, lack of accountability, and potential misuse by governments and organizations.
How are AI and machine learning being used in cybersecurity?
They are employed to detect anomalies, automate threat responses, and enhance overall security measures.
Use Case: Automating your weekly reports with AI to enhance security insights.
Try Runable For FreeKey Takeaways
- The Predator spyware scandal highlights vulnerabilities in digital communications.
- Legal frameworks need strengthening to regulate the use of surveillance tools.
- AI and blockchain technology offer promising solutions for enhancing cybersecurity.
- Ethical considerations are paramount in the deployment of surveillance technologies.
- Organizations must implement robust IT policies to mitigate spyware risks.
- Regular software updates are crucial for protecting against spyware threats.
- Public awareness and education are key to preventing phishing attacks.
- Governments must balance national security needs with citizens' privacy rights.
Related Articles
- The Future of Online Privacy: Age Checks and VPN Regulations [2025]
- Databricks' Strategic Acquisition: A Deep Dive Into Lakewatch and AI Security [2025]
- Understanding the LLM PyPl Package Compromise [2025]
- Understanding and Mitigating AI Vulnerabilities: The Guilt-Trip Phenomenon in OpenClaw Agents [2025]
- The Rise of the Cyber Hacker: Does Clout Matter More Than Cash? [2025]
- Cyber-Resilience for the Modern Data Center: Strategies and Best Practices [2025]
![The Greek Spyware Scandal: Lessons from the Convicted Spy Chief's Controversy [2025]](https://tryrunable.com/blog/the-greek-spyware-scandal-lessons-from-the-convicted-spy-chi/image-1-1774474510762.jpg)



