Understanding the LLM Py Pl Package Compromise [2025]
In the world of software development, package management systems like Py Pl are crucial for the seamless integration of powerful libraries and tools. However, these systems are not immune to vulnerabilities. Recently, a popular Python package, Lite LLM, which offers a lightweight API layer for AI model integration, was compromised, exposing a critical security flaw that has left many developers and companies scrambling. This article delves into what happened, how it happened, and how you can protect your systems from similar threats.
TL; DR
- Key Point 1: A popular Python package, Lite LLM, was compromised, affecting thousands of users by deploying an infostealer malware.
- Key Point 2: The attack targeted cloud credentials, Kubernetes secrets, and cryptocurrency wallets.
- Key Point 3: Users are advised to rotate tokens and revert to secure versions of the package.
- Key Point 4: Understanding the attack vector is crucial for preventing future compromises.
- Bottom Line: Vigilance and best practices in package management are essential for maintaining security.
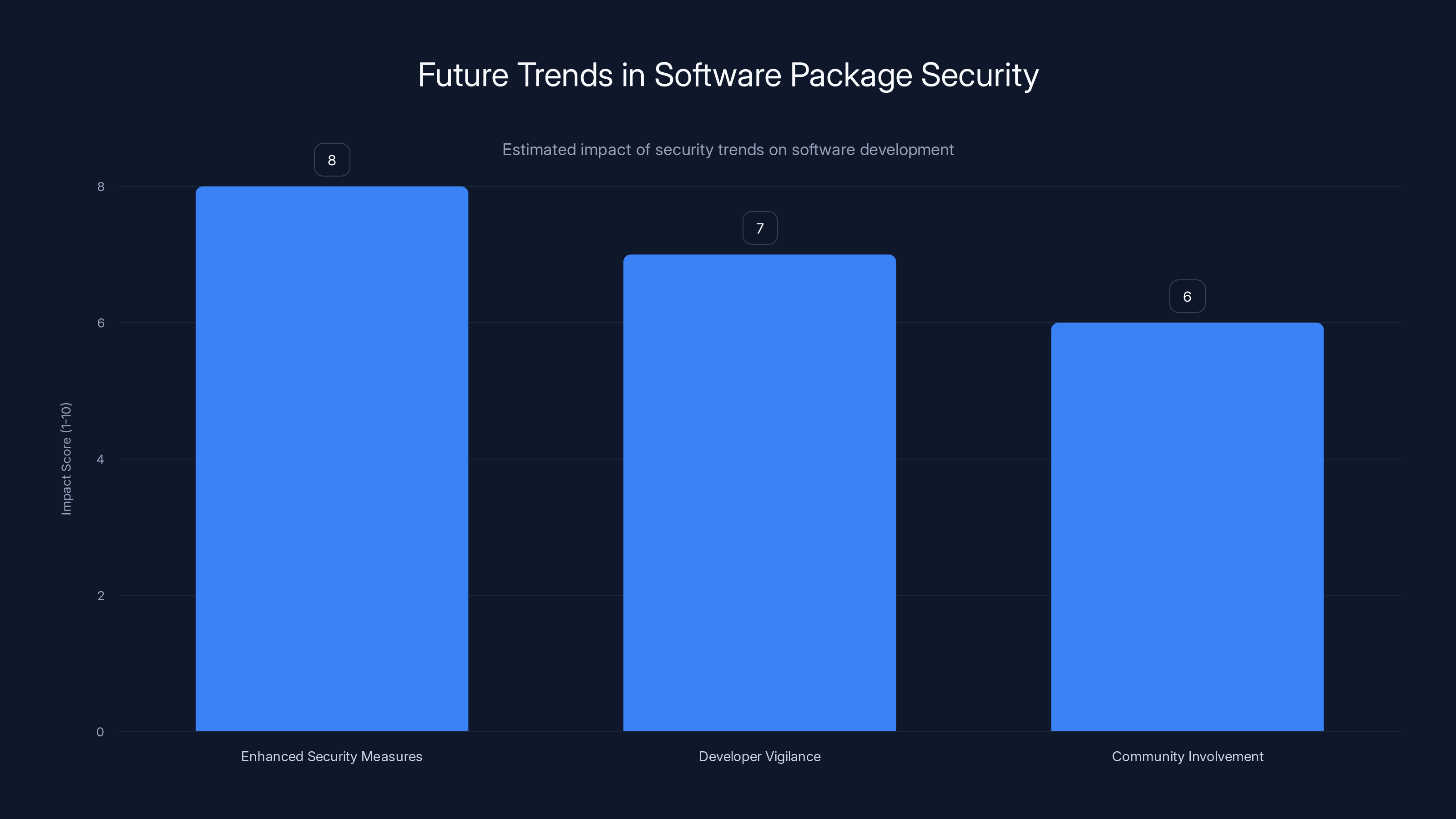
Estimated data suggests enhanced security measures will have the highest impact on software package security, followed by developer vigilance and community involvement.
The Rise of Lite LLM and Its Importance
Lite LLM is a vital tool for developers working with AI models. By providing a unified interface for calling multiple AI models, it simplifies the development process significantly. With over 40,000 stars on GitHub and more than 30,000 commits, its popularity is undeniable. However, this popularity also made it an attractive target for malicious actors.
What Happened?
The compromise occurred through malicious updates in versions 1.82.7 and 1.82.8, which deployed the Team PCP Cloud Stealer, an infostealer malware designed to harvest sensitive information such as cloud credentials and Kubernetes secrets.
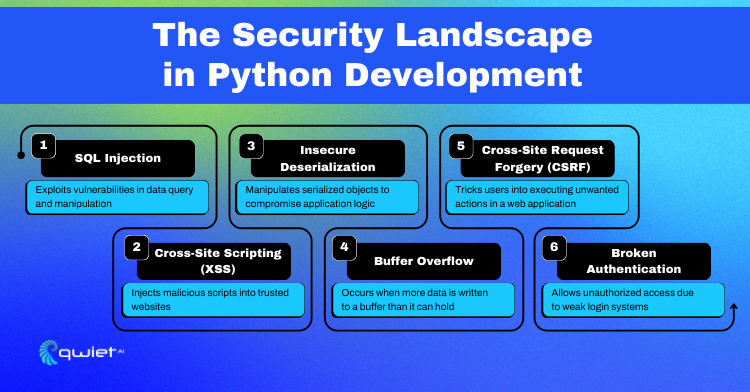
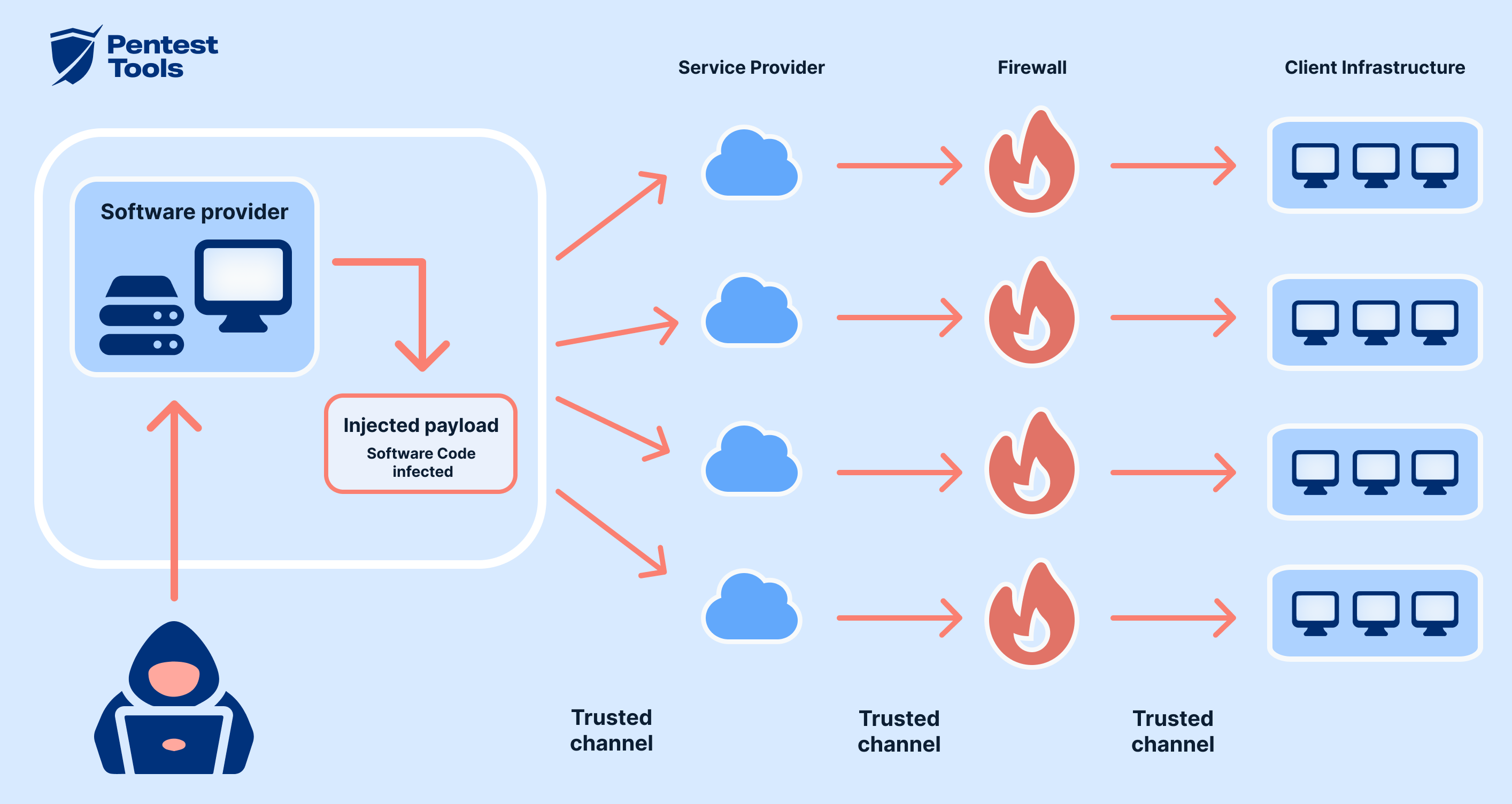
The Attack Vector
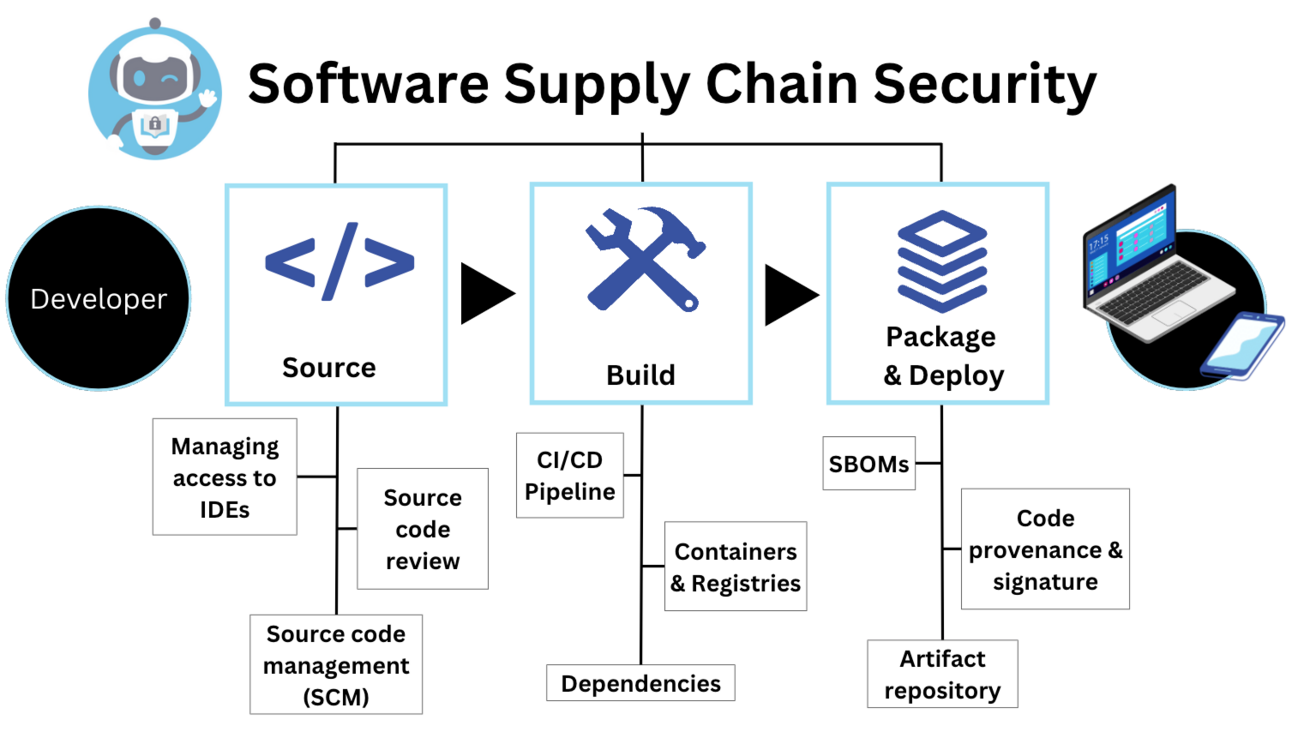
A supply chain attack is a type of cyberattack where the attacker seeks to damage an organization by targeting less-secure elements in the supply chain. In this case, the attack vector was the Py Pl package distribution channel, a trusted source for obtaining Python libraries.
Key Features of the Attack:
- Malicious Code Injection: The attackers managed to inject malicious code into the Lite LLM package updates.
- Credential Harvesting: The malware was designed to steal cloud credentials and Kubernetes secrets, which could be used to access sensitive infrastructure.
- Widespread Impact: Given Lite LLM's widespread use, the attack had the potential to affect thousands of systems.
How Did It Happen?
The attackers likely gained access to the package maintainer's account or exploited a vulnerability in the package's distribution pipeline. This allowed them to push malicious updates that appeared legitimate to users.
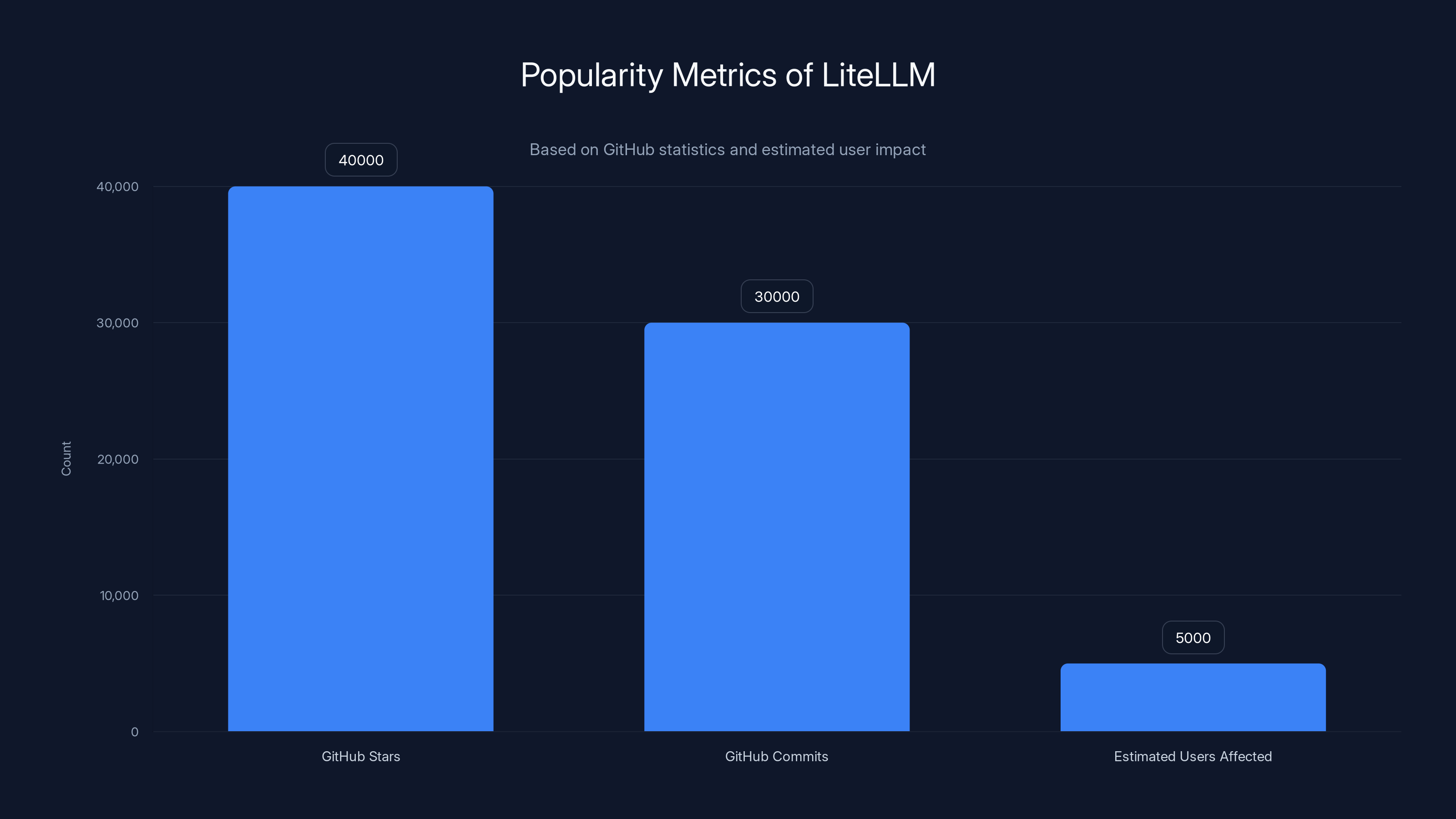
LiteLLM has gained significant popularity with over 40,000 stars and 30,000 commits on GitHub. The recent security breach potentially affected an estimated 5,000 users. (Estimated data for user impact)
Practical Implementation Guides
Securing Your Python Environments
Securing Python environments involves a combination of best practices and tools designed to protect against unauthorized access and malicious code execution.
- Regularly Audit Dependencies: Use tools like
pip-auditto identify known vulnerabilities in your dependencies.
bashpip install pip-audit pip-audit
-
Lock Package Versions: By locking package versions in your
requirements.txtorPipfile, you can prevent automatic updates to potentially compromised versions. -
Use Virtual Environments: Isolate Python environments to limit the impact of a compromised package.
-
Monitor Package Integrity: Use hash-based verification to ensure package integrity upon installation.
Responding to a Compromise
If you suspect a package compromise, take immediate action:
- Revert to a Safe Version: Downgrade to a version of the package prior to the compromise.
- Rotate Credentials: Immediately rotate any credentials that might have been exposed.
- Conduct a Security Review: Audit logs and systems to identify any unauthorized access or anomalies.
Common Pitfalls and Solutions
Ignoring Package Updates
Pitfall: Delaying package updates can lead to using outdated software with known vulnerabilities.
Solution: Implement a schedule for regular updates and automate dependency checks.
Over-reliance on Popular Packages
Pitfall: Assuming a package is safe because it is popular can lead to complacency.
Solution: Regularly review the code of critical dependencies and follow security advisories.

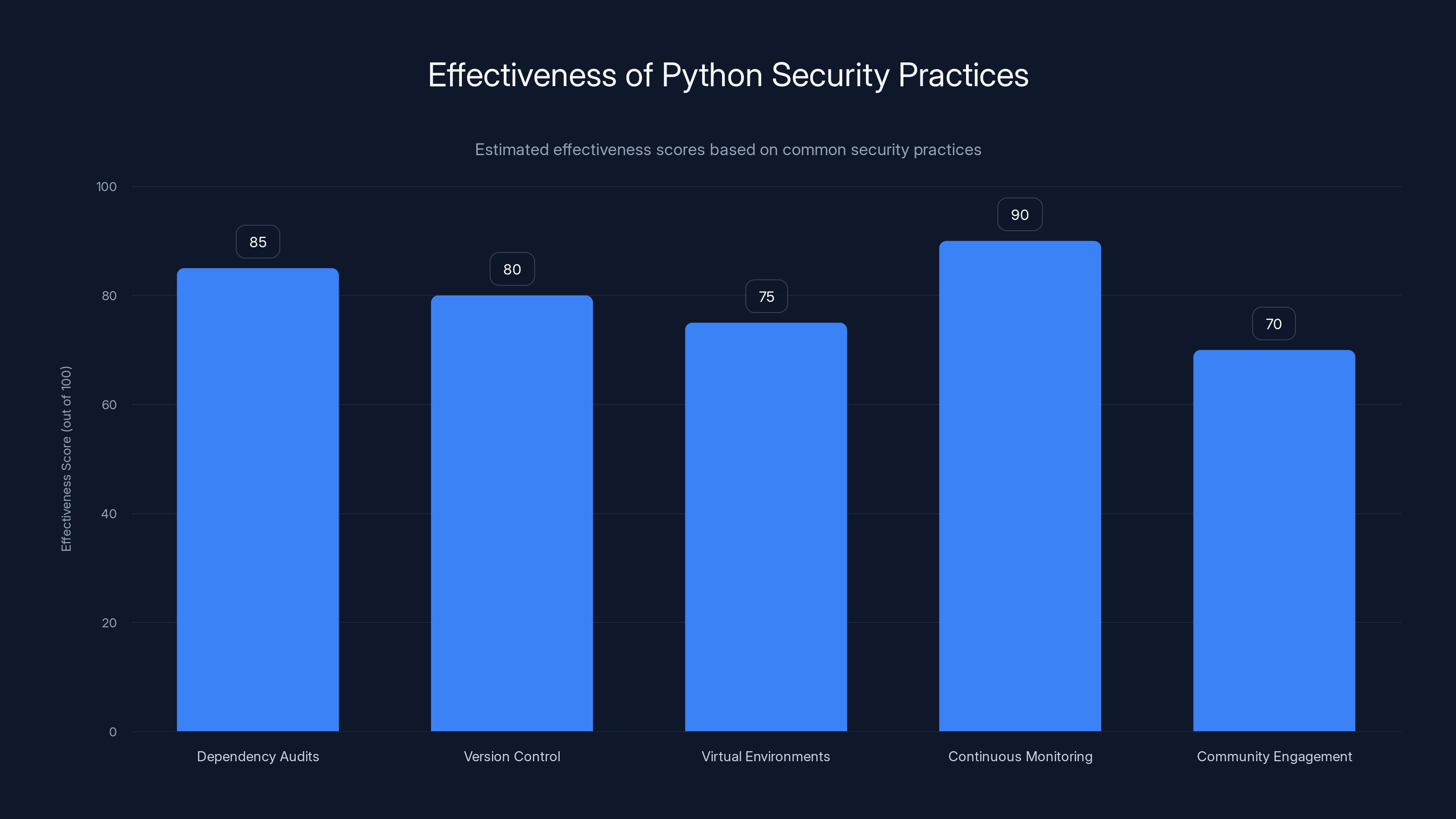
Continuous Monitoring scores highest in effectiveness for Python security practices, emphasizing the importance of real-time alerts. Estimated data.
Future Trends and Recommendations
Enhanced Package Security
As the ecosystem evolves, expect stronger security measures from package managers. Features like mandatory 2-factor authentication for maintainers and automated security checks for new versions will become standard.
Increased Developer Vigilance
Developers must remain vigilant, incorporating security into the software development lifecycle (SDLC). This includes security training, code reviews, and automated security testing.
Community Involvement
Open source communities play a critical role in identifying and patching vulnerabilities. Active participation and contribution to security discussions can help mitigate risks.
Conclusion
The compromise of the Lite LLM package serves as a stark reminder of the vulnerabilities inherent in software supply chains. By understanding the risks and implementing best practices, developers can better protect their projects and data from malicious threats.
FAQ
What is a supply chain attack?
A supply chain attack targets less-secure elements in a supply chain to compromise a larger organization or system. It's a growing threat in software development, affecting package managers like Py Pl.
How can I protect my Python projects from similar attacks?
Implement best practices such as regular dependency audits, version locking, and using virtual environments to isolate projects. Additionally, stay informed about security advisories related to your dependencies.
What immediate steps should I take if I suspect a package compromise?
Revert to a safe version, rotate exposed credentials, and conduct a thorough security review of your systems.
Why are popular packages targeted more frequently?
Their widespread use makes them attractive targets for attackers looking to maximize impact and reach.
How does package version locking help in security?
By locking package versions, you prevent automatic updates to potentially compromised versions, maintaining control over which versions you use.
What role does the community play in open-source security?
The open-source community helps identify vulnerabilities, contributes patches, and shares knowledge to improve the overall security of projects.
Key Takeaways
- Supply Chain Vulnerabilities: Understanding the risk is crucial for prevention.
- Best Practices: Regular audits and version control are essential.
- Immediate Response: Quick action can mitigate the impact of a compromise.
- Community Involvement: Contribute to discussions and solutions.
- Monitoring and Alerts: Use tools to monitor dependencies for vulnerabilities.
- Credential Management: Regularly rotate and secure credentials.
The Best Practices for Python Security at a Glance
| Practice | Description | Tools |
|---|---|---|
| Dependency Audits | Regularly check for vulnerabilities | pip-audit, safety |
| Version Control | Lock package versions to known safe states | pipenv, poetry |
| Virtual Environments | Isolate environments to prevent cross-contamination | virtualenv, venv |
| Continuous Monitoring | Use tools for real-time vulnerability alerts | snyk, dependabot |
| Community Engagement | Participate in open-source security discussions | GitHub, forums |
Quick Navigation:
By staying informed and proactive, developers can safeguard their projects against threats like the recent Lite LLM compromise. Emphasizing security at every stage of development is crucial in today's digital landscape.

Related Articles
- The Rise of the Cyber Hacker: Does Clout Matter More Than Cash? [2025]
- Cyber-Resilience for the Modern Data Center: Strategies and Best Practices [2025]
- Databricks' Strategic Acquisition: A Deep Dive Into Lakewatch and AI Security [2025]
- Inside the World of Cyber Espionage: How Iranian Hackers Exploit Telegram for Global Data Breaches [2025]
- Exposing the Visibility Gap: Unleashing the Full Potential of Agentic SOC [2025]
- How Biometric Authentication Can Tackle Bot Problems on Social Platforms [2025]
![Understanding the LLM PyPl Package Compromise [2025]](https://tryrunable.com/blog/understanding-the-llm-pypl-package-compromise-2025/image-1-1774465628938.jpg)



