Anthropic's Security Flaws: A Deep Dive into MCP Vulnerabilities [2025]
Last month, security researchers from Oxford discovered a potentially catastrophic vulnerability at the core of Anthropic's Model Context Protocol (MCP). This isn't your run-of-the-mill coding mistake. It’s a systemic flaw that exposes over 150 million downloads and thousands of servers to remote code execution (RCE) attacks. Let’s unravel what this means for developers and businesses using Anthropic’s technologies.
TL; DR
- Critical Vulnerability: MCP’s flaw allows potential remote code execution (RCE), risking millions of downloads and servers.
- Systemic Issue: More than a bug, it’s a fundamental design flaw needing immediate attention.
- Real-World Impact: Many organizations face potential data breaches and operational disruptions.
- Mitigation Steps: Implementing security patches and following best practices can curb risks.
- Looking Ahead: Companies must prioritize security audits and robust testing to prevent similar threats.
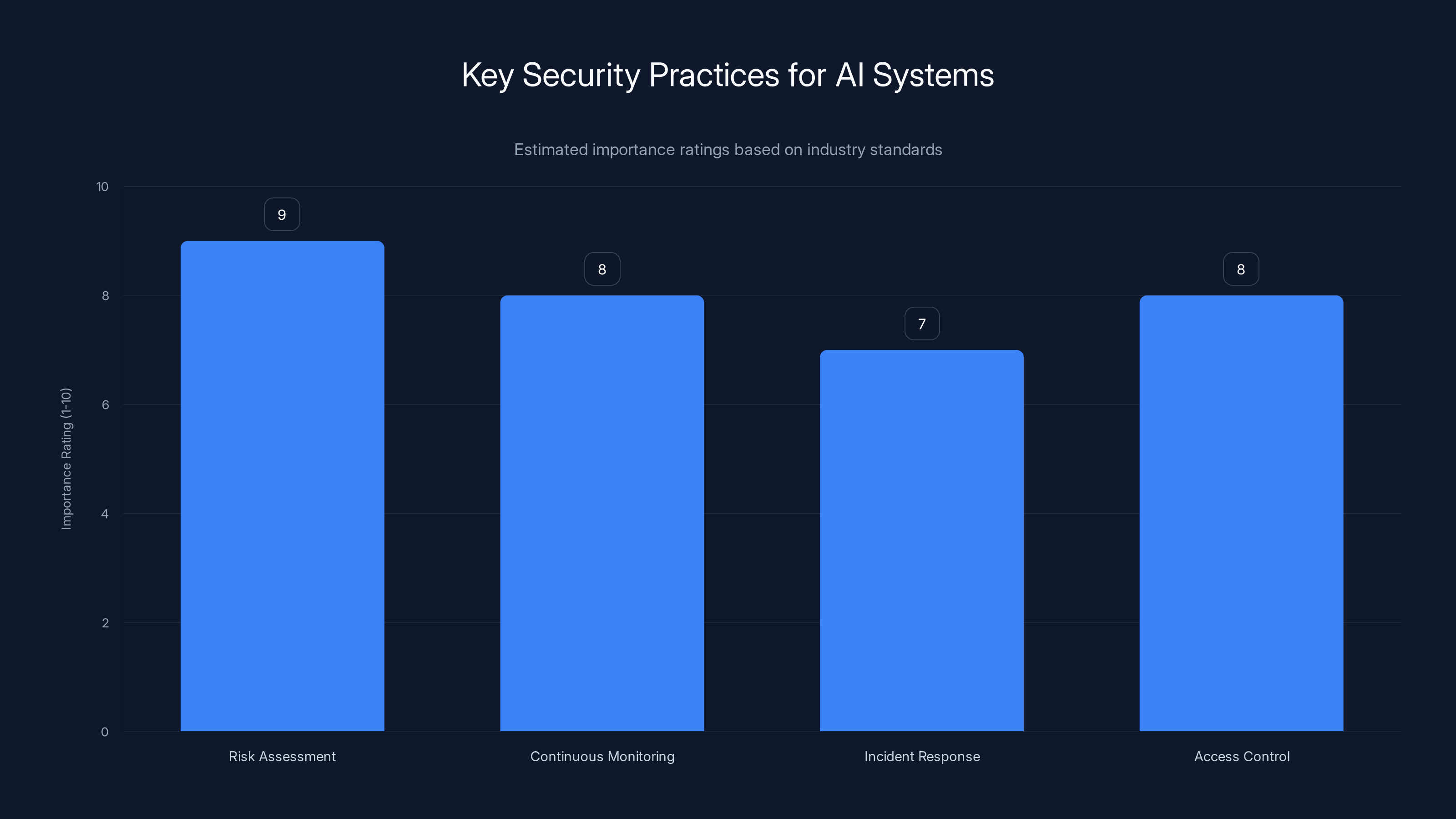
Risk assessment and continuous monitoring are crucial for AI security, with high importance ratings. (Estimated data)
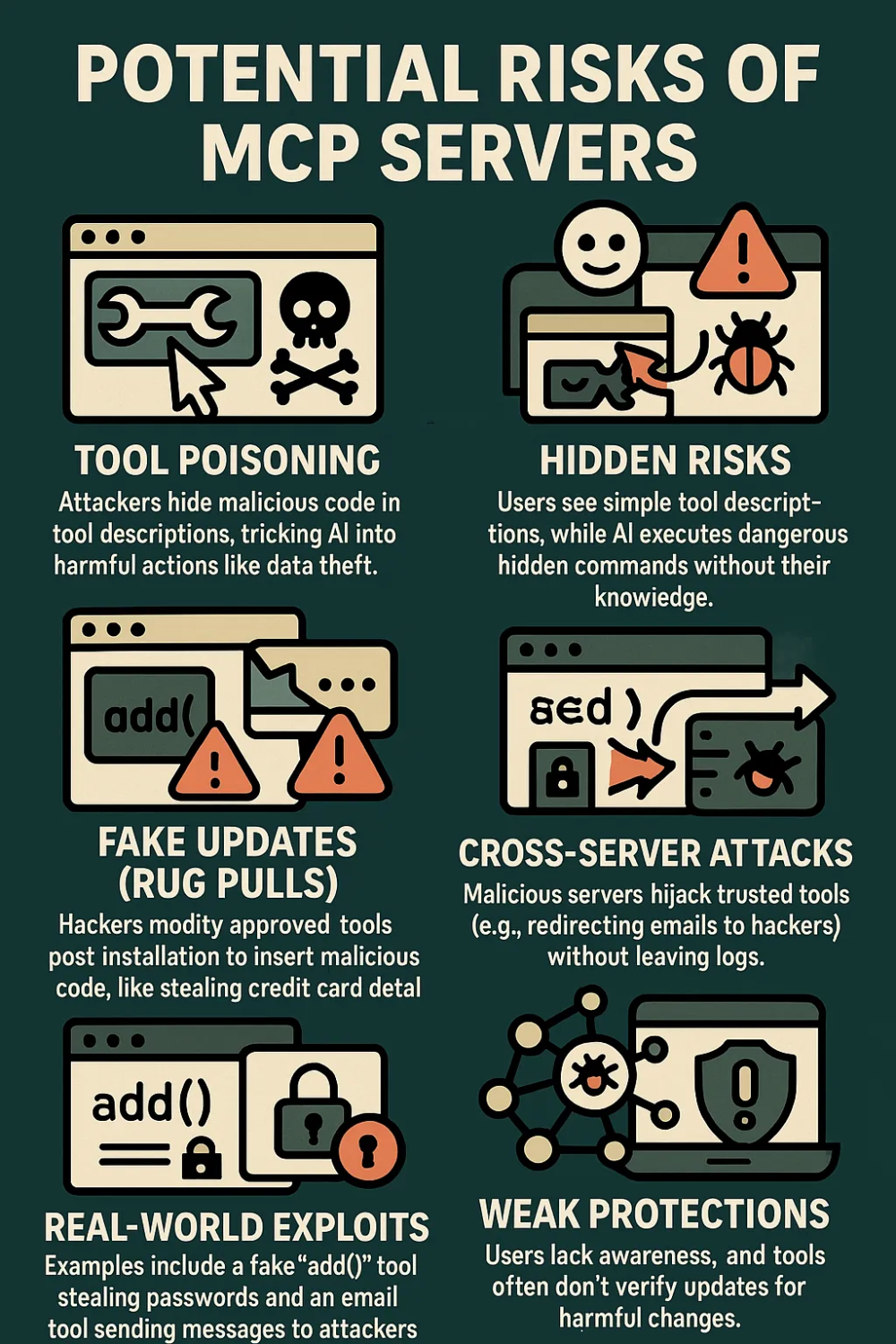
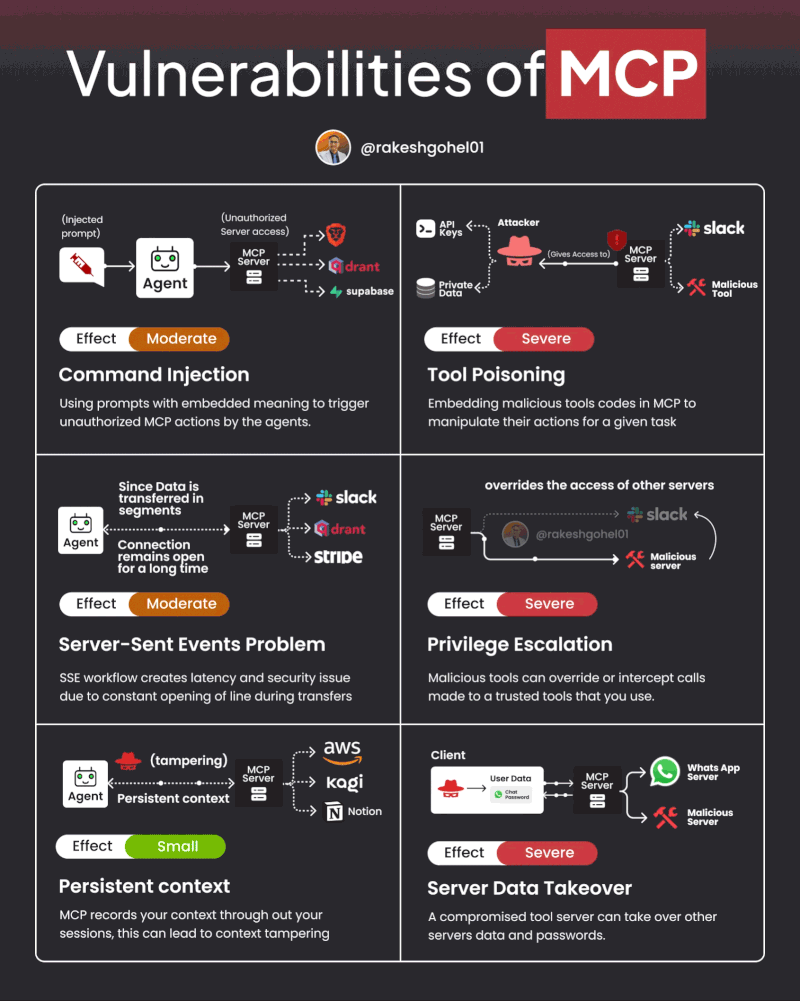
Understanding the Vulnerability in Anthropic's MCP
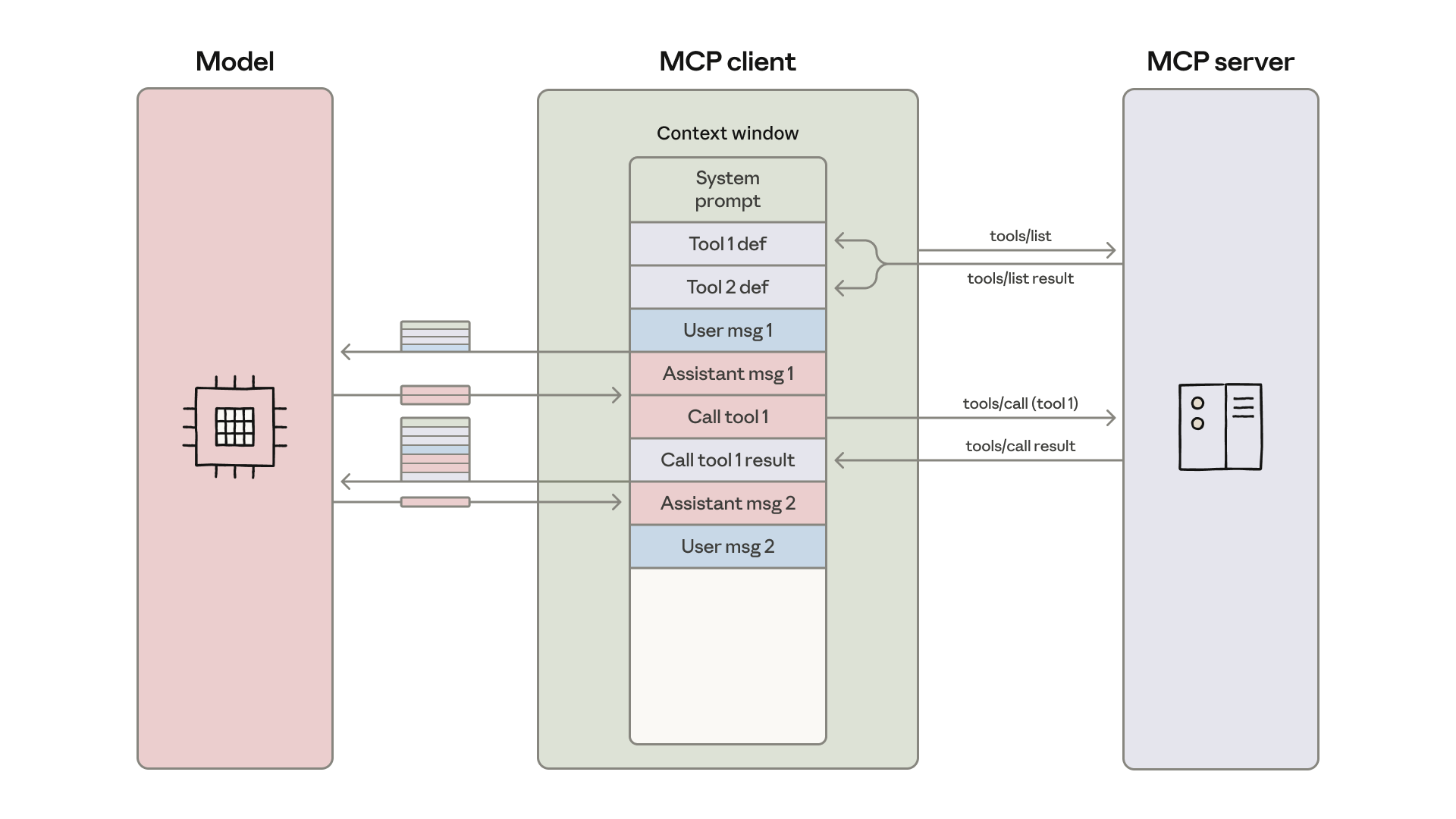
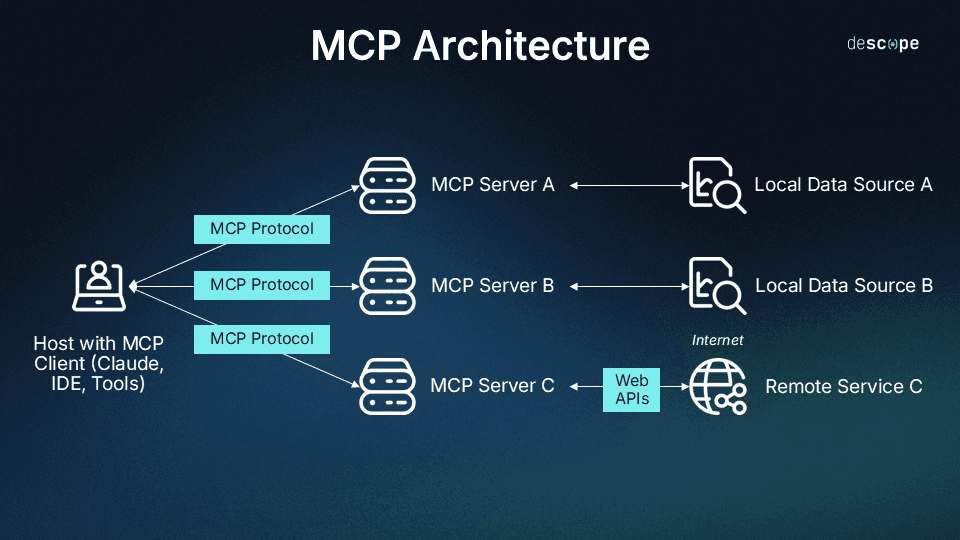
Anthropic's Model Context Protocol, or MCP, is a foundational component in their AI systems, designed to manage context in machine learning models. It facilitates the interaction between the model's layers, ensuring data flows seamlessly to produce accurate results.
However, Oxford researchers identified a flaw that could allow attackers to execute arbitrary code remotely by exploiting the protocol's handling of context data. This flaw isn't just a small oversight; it’s a systemic vulnerability that requires a complete architectural rethink.
What is Remote Code Execution (RCE)?
RCE is particularly dangerous because it can give attackers the keys to the kingdom. Once they gain access, they can manipulate data, install malware, or even control other connected systems.
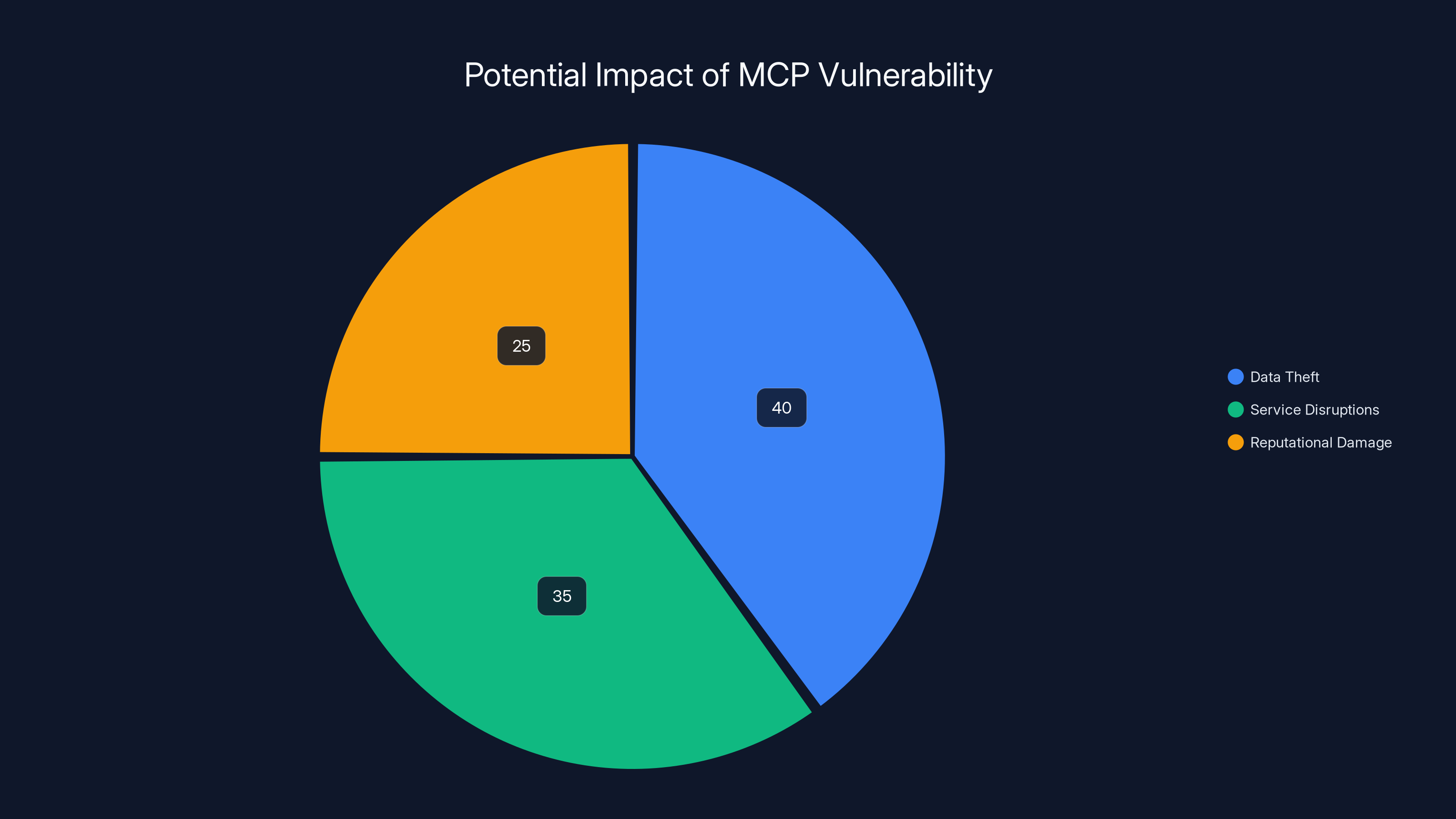
Estimated data shows that data theft accounts for 40% of potential impacts from MCP vulnerabilities, followed by service disruptions at 35% and reputational damage at 25%.
The Scope of the Problem
Anthropic’s MCP is widely adopted, with over 150 million downloads across various platforms. This widespread use means the potential impact of the vulnerability is massive. Thousands of servers running MCP could be compromised, leading to data theft, service disruptions, and reputational damage.
Real-World Example
Consider a healthcare company using MCP to manage patient data through AI-driven analyses. An attacker exploiting this vulnerability could access sensitive patient information, manipulate medical records, or disrupt healthcare services. The consequences are not just legal or financial—they can directly impact human lives.
Technical Details and Best Practices
How the Flaw Works
The vulnerability arises from how MCP manages context data across its layers. In technical terms, the protocol fails to sufficiently sanitize inputs, allowing attackers to inject malicious code. Here’s a simplified illustration:
- Input Handling: User data flows into MCP without proper validation.
- Context Management: The protocol processes this data, assuming it’s safe.
- Execution: Malicious code executes, granting attackers control.
Best Practices for Mitigation
- Input Validation: Always validate and sanitize all data inputs to prevent injection attacks.
- Regular Patching: Keep systems updated with the latest security patches from vendors.
- Access Controls: Limit user privileges to minimize potential damage from compromised accounts.
- Code Audits: Conduct regular code reviews and security audits to catch vulnerabilities early.
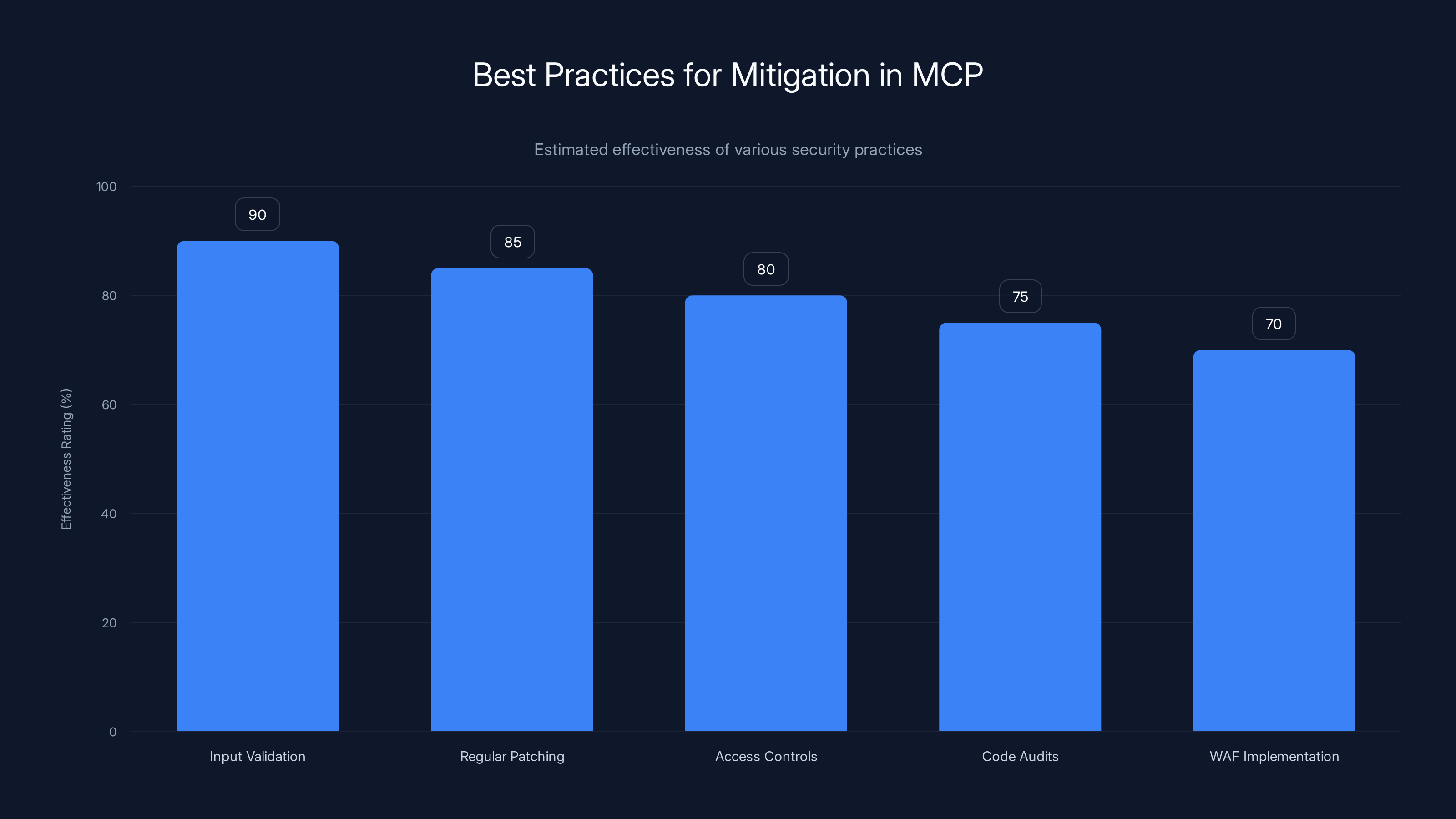
Input validation is the most effective practice for mitigating vulnerabilities in MCP, followed closely by regular patching. (Estimated data)
Common Pitfalls and Solutions
Underestimating Security Risks
One common mistake is underestimating the potential impact of security vulnerabilities. Businesses often assume they're too small to be targeted, but attackers look for any opportunity, regardless of company size.
Solution: Conduct regular risk assessments to understand and prioritize potential threats.
Delayed Patch Management
Delays in applying patches can leave systems vulnerable to exploitation. Attackers often exploit known vulnerabilities before patches are applied.
Solution: Establish a patch management policy that ensures timely updates across all systems.

Future Trends and Recommendations
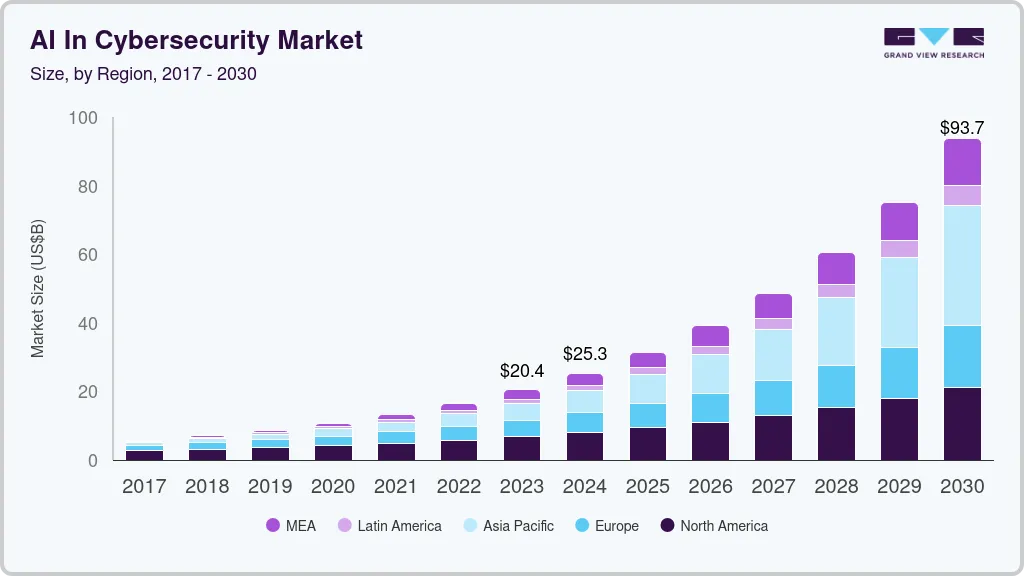
AI and Security
As AI continues to evolve, so will the methods attackers use to exploit vulnerabilities. MCP’s flaw highlights the need for a proactive approach to security in AI.
Recommendations:
- Invest in AI Security: Develop AI-specific security tools that can detect and mitigate threats in real-time.
- Collaborative Defense: Encourage collaboration between AI developers and security experts to build more resilient systems.
Regulatory Pressures
With the increasing integration of AI in critical sectors, regulatory bodies are likely to impose stricter security standards.
Recommendations:
- Compliance Training: Ensure all employees are trained on compliance requirements and security best practices.
- Regulatory Monitoring: Stay informed about changes in regulations to ensure ongoing compliance.
Conclusion
The discovery of this vulnerability in Anthropic’s MCP is a wake-up call for organizations relying on AI technologies. It underscores the importance of robust security practices and the need for continuous vigilance in protecting digital assets.
By understanding the risks, implementing best practices, and preparing for future trends, businesses can safeguard their systems and maintain trust with their customers.
Use Case: Automatically generate security audit reports to identify vulnerabilities like those in MCP.
Try Runable For FreeFAQ
What is Anthropic's Model Context Protocol?
Anthropic's Model Context Protocol (MCP) is a framework for managing context in AI models, ensuring data flows smoothly between different layers to produce accurate results.
How serious is the MCP vulnerability?
The MCP vulnerability is significant as it allows for remote code execution, potentially giving attackers full control over affected systems.
What steps can businesses take to mitigate this vulnerability?
Businesses should validate inputs, apply patches promptly, limit access controls, and conduct regular security audits to mitigate risks.
How does this vulnerability impact AI security trends?
This vulnerability highlights the need for AI-specific security measures and proactive collaboration between developers and security experts to build resilient systems.
Why is timely patch management crucial?
Timely patch management is essential to prevent attackers from exploiting known vulnerabilities before they are addressed.
Are there regulatory implications for AI security?
Yes, as AI becomes more integrated into critical sectors, regulatory bodies are likely to impose stricter security standards, requiring businesses to stay compliant.
Key Takeaways
- MCP vulnerability allows remote code execution, posing significant risks.
- Security best practices are crucial to mitigate potential threats.
- AI-specific security solutions are necessary for future resilience.
- Timely patch management can prevent exploitation of vulnerabilities.
- Regulatory pressures are increasing for AI security compliance.
Related Articles
- Understanding the Complexities of Prompt Injection Vulnerabilities in AI Systems [2025]
- Claude's Current Challenges: Understanding the Issues and Future Prospects [2025]
- WordPress Plugin Security Attacks: Safeguarding Your Site [2025]
- Cyber Warfare: Preparing Your Enterprise for the Digital Frontlines [2025]
- Stay Safe from iCloud Phishing Scams: What Every Apple User Needs to Know [2025]
- Can AI Judge Journalism? Exploring Risks and Innovations [2025]
![Anthropic's Security Flaws: A Deep Dive into MCP Vulnerabilities [2025]](https://tryrunable.com/blog/anthropic-s-security-flaws-a-deep-dive-into-mcp-vulnerabilit/image-1-1776342849531.jpg)



