Cyber Warfare: Preparing Your Enterprise for the Digital Frontlines [2025]
The landscape of conflict is shifting dramatically as geopolitical tensions spill over into the digital realm. Cyber warfare is no longer a distant threat; it's a present reality impacting industries worldwide. In particular, the ongoing tensions between the United States and Iran highlight the need for enterprises to bolster their defenses against sophisticated cyber threats. According to the Center for Strategic and International Studies, the conflict has significantly heightened cyber threats to U.S. energy infrastructure.
TL; DR
- Cyber warfare is impacting global industries, necessitating robust cybersecurity measures.
- Enterprises must adopt proactive defense strategies to mitigate the risks of cyberattacks.
- Implementing advanced threat detection and response mechanisms is crucial.
- Invest in cybersecurity training and awareness programs for all employees.
- Future-proof your cybersecurity infrastructure to adapt to evolving threats.
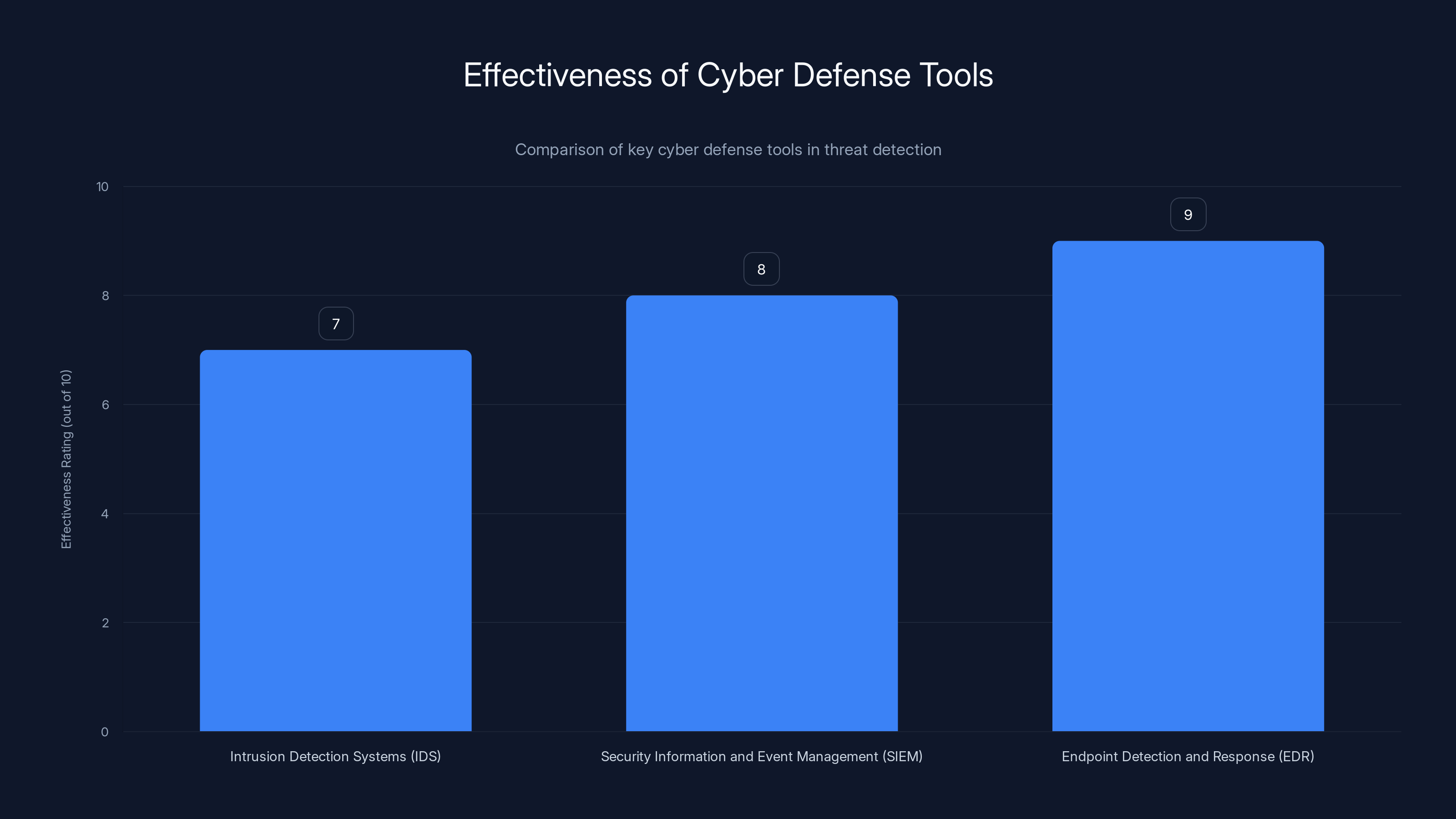
Endpoint Detection and Response (EDR) is rated highest in effectiveness for threat detection, reflecting its advanced capabilities in protecting endpoints from sophisticated attacks. Estimated data.
Understanding the Cyber Warfare Landscape
The digital battlefield is expanding. Cyber warfare involves the use of digital attacks to disrupt, destroy, or manipulate an adversary's information systems. These attacks can target critical infrastructure, financial systems, and private enterprises, causing widespread disruption. The Palo Alto Networks Unit 42 reports that Iranian cyberattacks have been increasingly targeting critical infrastructure in recent years.
Key Players and Motivations
The primary actors in cyber warfare include nation-states, hacktivists, organized cybercriminals, and insiders. Each has distinct motivations—ranging from political and economic gain to ideological beliefs. Nation-states often engage in cyber operations to weaken adversaries without engaging in physical conflict. Hacktivists might target organizations to promote social or political causes. Understanding these motivations helps in anticipating potential threats.
Common Tactics and Techniques
Cyber warfare tactics are constantly evolving. Some of the most common techniques include:
- DDoS Attacks: Overwhelming systems with traffic to render them unusable. CSO Online discusses how botnet-driven DDoS attacks have evolved.
- Phishing Campaigns: Trick users into revealing sensitive information.
- Malware Deployment: Infect systems to steal data or cause damage.
- Ransomware: Encrypt data and demand payment for decryption.
- Supply Chain Attacks: Compromise third-party vendors to access primary targets.
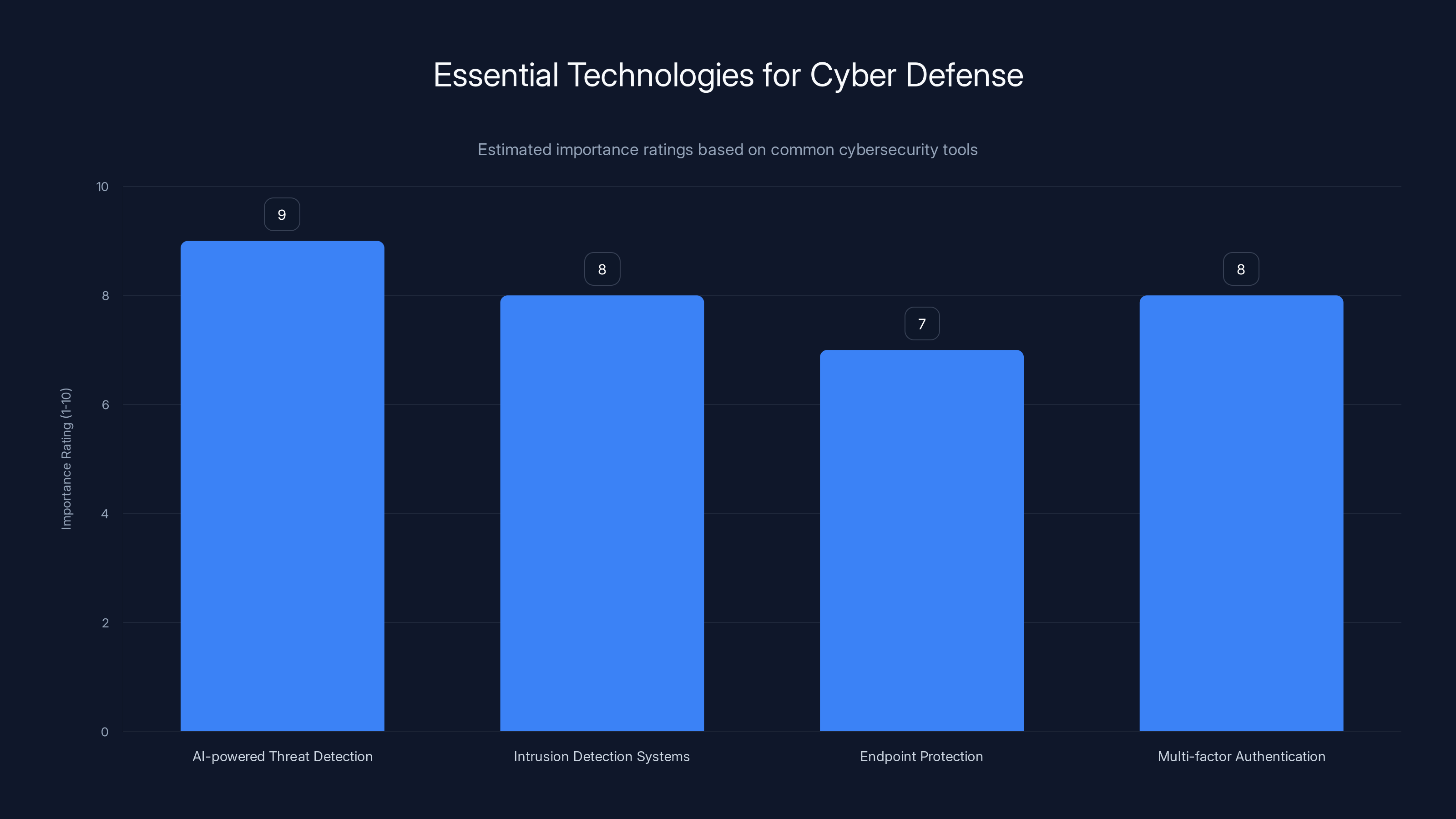
AI-powered threat detection is rated as the most important technology for defending against cyber threats, followed closely by multi-factor authentication and intrusion detection systems. (Estimated data)
Assessing Your Enterprise's Vulnerability
Before implementing robust defenses, enterprises must understand their existing vulnerabilities. Conducting a comprehensive risk assessment is the first step.
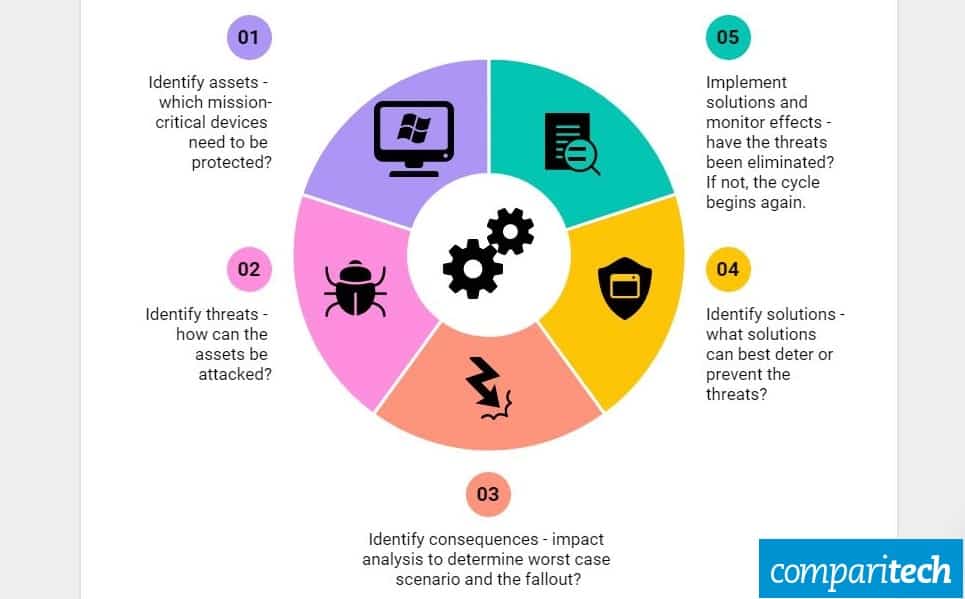
Performing a Cybersecurity Risk Assessment
A thorough risk assessment should include:
- Asset Identification: Catalog all digital assets and data.
- Threat Analysis: Evaluate potential threats based on industry and geopolitical factors.
- Vulnerability Scanning: Use tools to identify system weaknesses. The Wiz Academy provides insights on vulnerability prioritization.
- Impact Analysis: Determine the potential impact of various threat scenarios.
- Risk Mitigation Planning: Develop strategies to address identified vulnerabilities.
Prioritizing Critical Assets
Not all assets are equally valuable or vulnerable. Identify which systems and data are critical to your operations and prioritize their protection. Vocal Media highlights the growing importance of endpoint security in protecting critical assets.
QUICK TIP: Start by protecting your most sensitive data—such as customer information and financial records—to minimize the impact of a breach.
Building a Robust Cyber Defense Strategy
To effectively combat cyber threats, enterprises must adopt a multi-layered defense strategy. This includes implementing cutting-edge technologies and fostering a security-conscious culture.
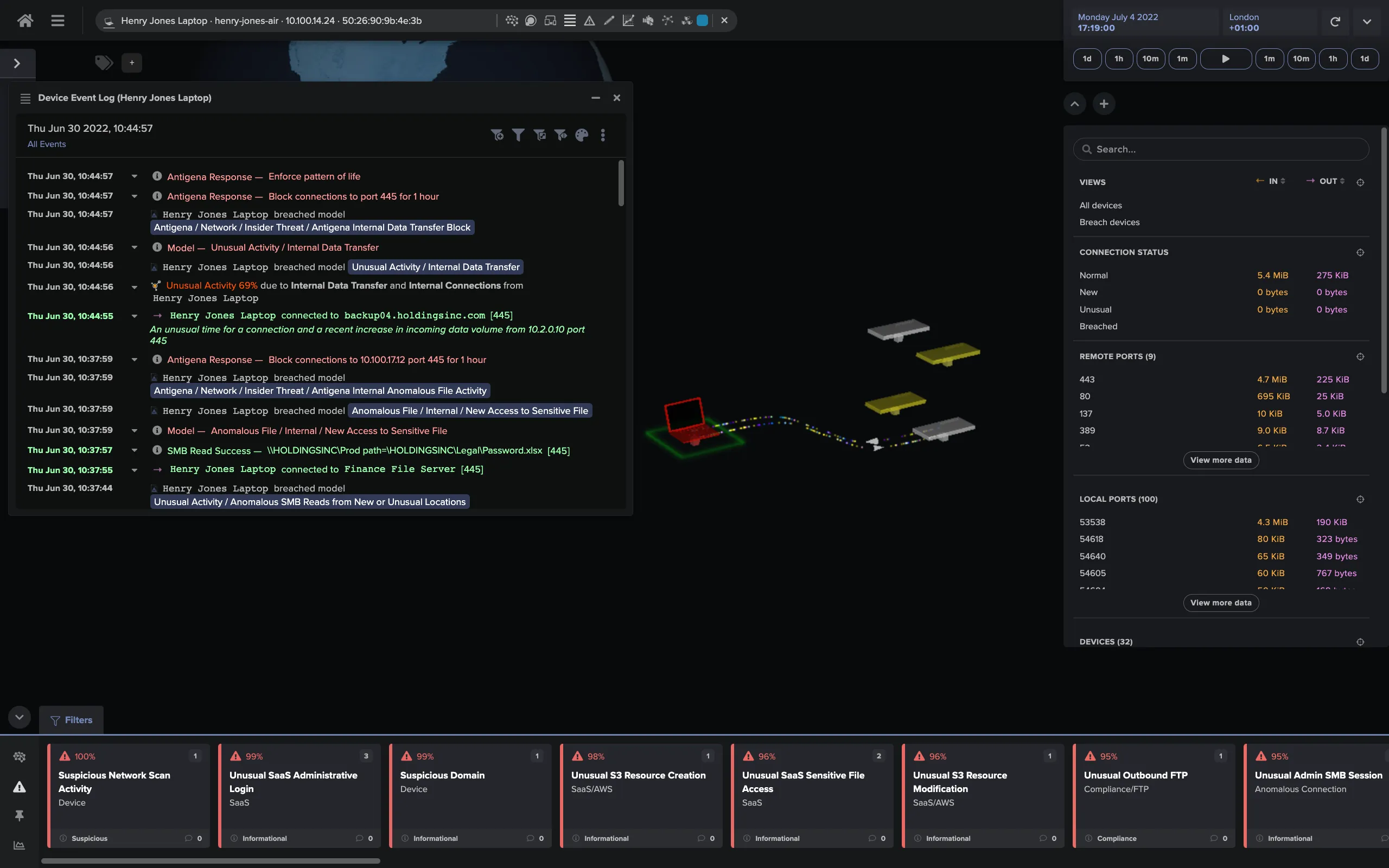
Advanced Threat Detection and Response
Investing in advanced threat detection tools is crucial. These tools use artificial intelligence to identify and respond to anomalies in real-time.
- Intrusion Detection Systems (IDS): Monitor network traffic for suspicious activity.
- Security Information and Event Management (SIEM): Aggregate and analyze security data.
- Endpoint Detection and Response (EDR): Protect endpoints from sophisticated attacks.
DID YOU KNOW: According to a report by Booz Allen Hamilton, AI-powered threat detection can reduce the time to identify breaches by up to 90%.
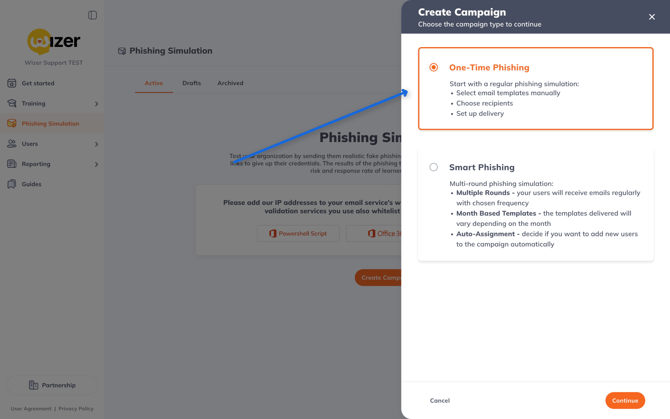
Cybersecurity Training and Awareness
Human error remains a leading cause of security breaches. Regular training can significantly reduce this risk.
- Phishing Simulations: Test employees with simulated phishing attacks.
- Security Workshops: Educate staff on best practices and emerging threats.
- Incident Response Drills: Prepare teams for actual cyber incidents.
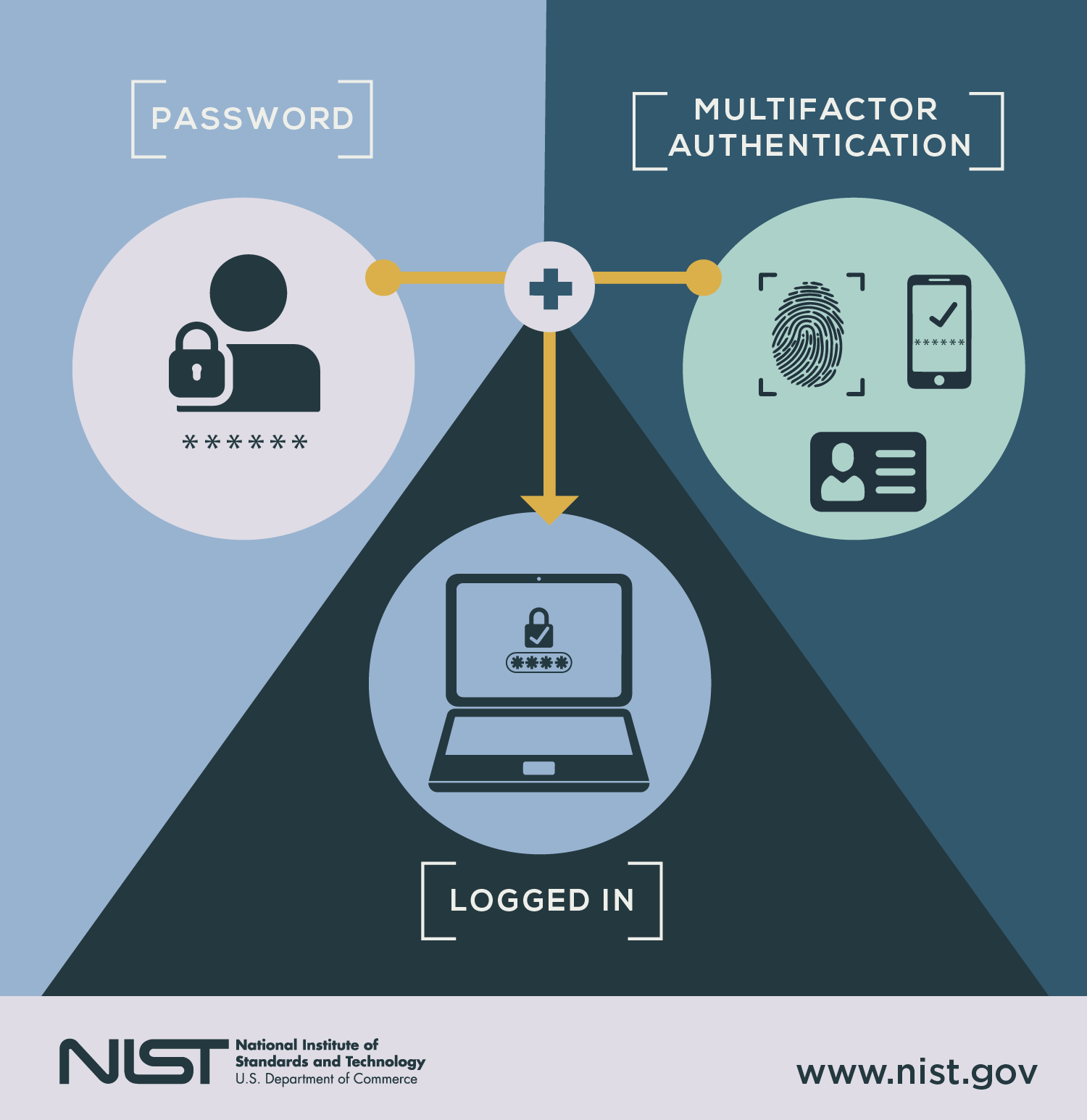
Multi-Factor Authentication (MFA)
Implementing MFA adds an additional layer of security by requiring multiple verification methods.
- Benefits: Increases security without significantly hindering user experience.
- Implementation: Use SMS, authenticator apps, or biometric verification.

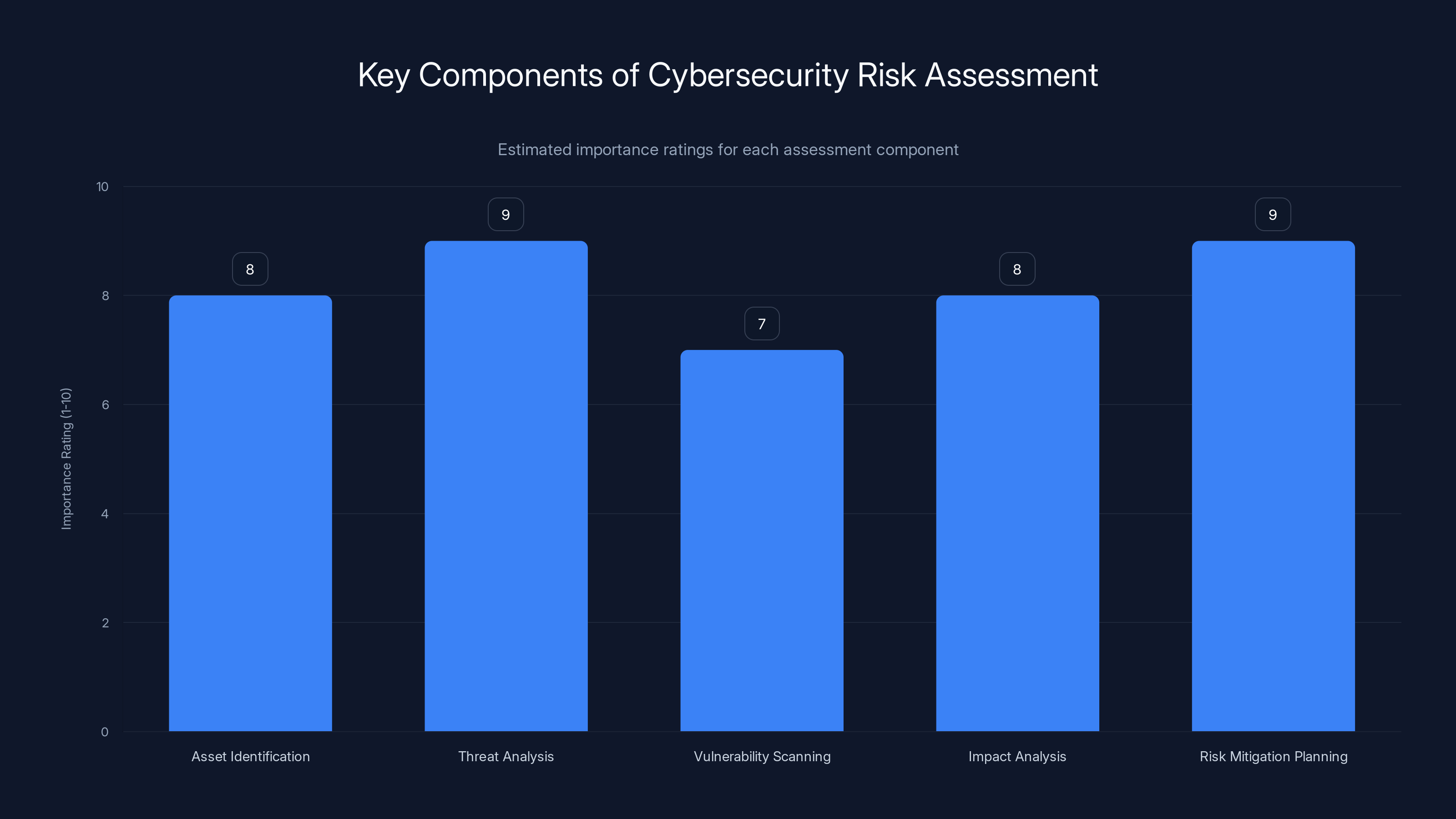
Asset identification and risk mitigation planning are crucial steps, both rated at 9, highlighting their importance in a cybersecurity risk assessment. Estimated data.
Securing Remote Work Environments
The rise of remote work has introduced new security challenges. Enterprises must adapt their strategies to protect remote workers and networks.
Virtual Private Networks (VPNs)
VPNs encrypt internet traffic, safeguarding data transmitted over unsecured networks. Ensure remote workers use VPNs to access company resources.
QUICK TIP: Regularly update VPN software to patch vulnerabilities and enhance security.
Cloud Security Measures
As businesses migrate to the cloud, securing these environments is paramount.
- Data Encryption: Encrypt data both at rest and in transit.
- Access Controls: Implement strict access controls to limit data exposure.
- Regular Audits: Conduct regular security audits to identify potential vulnerabilities. Cyble emphasizes the importance of regular audits in maintaining cloud security.

Future-Proofing Your Cybersecurity Infrastructure
As cyber threats evolve, so too must your defenses. Future-proofing your cybersecurity infrastructure ensures you're prepared for emerging challenges.
Embracing Artificial Intelligence
AI is revolutionizing cybersecurity, providing powerful tools for threat detection and response.
- Behavioral Analytics: Use AI to identify abnormal user behavior that may indicate a breach.
- Automated Incident Response: Deploy AI-driven solutions to automate responses to common threats.
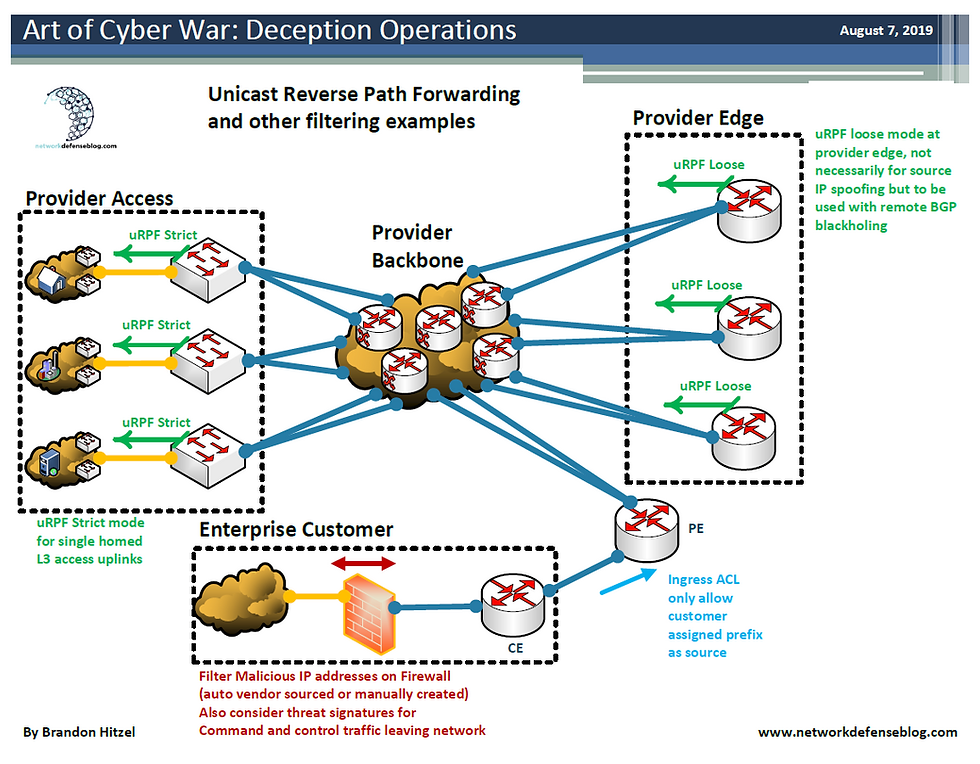
Zero Trust Architecture
Zero Trust is a security model that requires verification for every user and device accessing the network.
- Principles: Trust nothing, verify everything.
- Implementation: Segment networks, enforce least privilege access, and continuously monitor activity.
Common Pitfalls and Solutions
Even the best-prepared enterprises can fall victim to cyberattacks. Avoid these common pitfalls:
Overreliance on Technology
While technology is crucial, don't overlook the human element. Establish a culture of security awareness and responsibility.
Inadequate Incident Response Plans
Having a response plan is essential, but it must be regularly tested and updated.
- Solution: Conduct regular drills and update plans based on lessons learned.
Ignoring Third-Party Risks
Supply chain attacks are on the rise. Vet and monitor third-party vendors to ensure they adhere to your security standards. The UK NCSC has reported on the exploitation of routers for DNS hijacking, highlighting the importance of monitoring third-party risks.
QUICK TIP: Include security clauses in vendor contracts to ensure compliance and accountability.
Future Trends and Recommendations
Cyber warfare tactics will continue to evolve. Staying ahead of trends is key to maintaining robust defenses.
Quantum Computing
Quantum computing poses both opportunities and threats to cybersecurity.
- Opportunities: Potential for advanced encryption methods.
- Threats: Ability to break current encryption standards.
Collaborative Defense
As cyber threats become more sophisticated, collaboration between enterprises, governments, and cybersecurity firms is crucial.
- Information Sharing: Participate in threat intelligence sharing networks.
- Public-Private Partnerships: Engage in initiatives to strengthen national cybersecurity. The ODNI report underscores the importance of such collaborations in addressing escalating cyber risks.
Conclusion
The digital frontlines are expanding, and enterprises must be prepared to defend against an array of cyber threats. By understanding the landscape, assessing vulnerabilities, and implementing robust defenses, organizations can protect themselves against the growing tide of cyber warfare.
Use Case: Automate your cybersecurity reports with AI-driven insights for comprehensive threat analysis.
Try Runable For Free
FAQ
What is cyber warfare?
Cyber warfare involves the use of digital attacks to compromise, disrupt, or destroy information systems of adversaries, often targeting critical infrastructure and enterprises.
How can enterprises prepare for cyber warfare?
Enterprises should conduct risk assessments, implement advanced threat detection tools, foster a security-conscious culture, and ensure robust incident response plans.
What technologies are essential for defending against cyber threats?
Key technologies include AI-powered threat detection, intrusion detection systems, endpoint protection, and multi-factor authentication.
How does Zero Trust architecture enhance security?
Zero Trust architecture requires verification for every network access request, reducing the risk of unauthorized access and lateral movement within the network.
Why is cybersecurity training important?
Training reduces the likelihood of human error, which is a common cause of security breaches, and ensures employees are aware of best practices and emerging threats.
How can enterprises protect remote workers?
Enterprises should use VPNs, enforce strict access controls, and ensure all remote workers use up-to-date security software.
What role does AI play in cybersecurity?
AI enhances threat detection and response by identifying anomalies, automating common responses, and analyzing vast amounts of security data in real-time.
What future trends should enterprises watch in cybersecurity?
Key trends include the rise of quantum computing, increased collaboration for defense, and the growing importance of AI in threat detection.

Key Takeaways
- Cyber warfare is a growing threat requiring robust defenses.
- Enterprises must prioritize critical asset protection and risk assessments.
- Advanced threat detection tools and AI are crucial for defense.
- Regular cybersecurity training reduces human error risks.
- Future-proofing involves adopting Zero Trust and AI technologies.
Related Articles
- Understanding the Complexities of Prompt Injection Vulnerabilities in AI Systems [2025]
- Stay Safe from iCloud Phishing Scams: What Every Apple User Needs to Know [2025]
- Inside the Kraken Extortion Attack: How Crypto Giants Defend Against Cyber Threats [2025]
- Breaking Down the Live Nation/Ticketmaster Monopoly: Impacts and Future Directions [2025]
- Navigating the Road Ahead: Ford's Tech Transition After Doug Field's Departure [2025]
- Maine's Data Center Ban: Implications and Future Directions [2025]
![Cyber Warfare: Preparing Your Enterprise for the Digital Frontlines [2025]](https://tryrunable.com/blog/cyber-warfare-preparing-your-enterprise-for-the-digital-fron/image-1-1776335667661.jpg)



