Stay Safe from iCloud Phishing Scams: What Every Apple User Needs to Know [2025]
Phishing scams have been around for decades, but their sophistication continues to evolve. Recently, Apple users have found themselves at the center of a new wave of phishing attacks, specifically targeting iCloud accounts. These scams often come in the form of fake emails warning users that their iCloud data will be deleted unless they take immediate action. The real danger begins when users follow the links in these emails, potentially compromising their data and security, as highlighted by The Guardian.
TL; DR
- Phishing Attacks Targeting iCloud: Fake emails claim iCloud data deletion.
- Immediate Action Required: Users urged to click on malicious links.
- Recognizing Phishing Signs: Poor grammar, suspicious URLs, and urgent language.
- Protection Measures: Enable two-factor authentication and verify email sources.
- Future Trends: Increased use of AI in phishing and cybersecurity solutions.
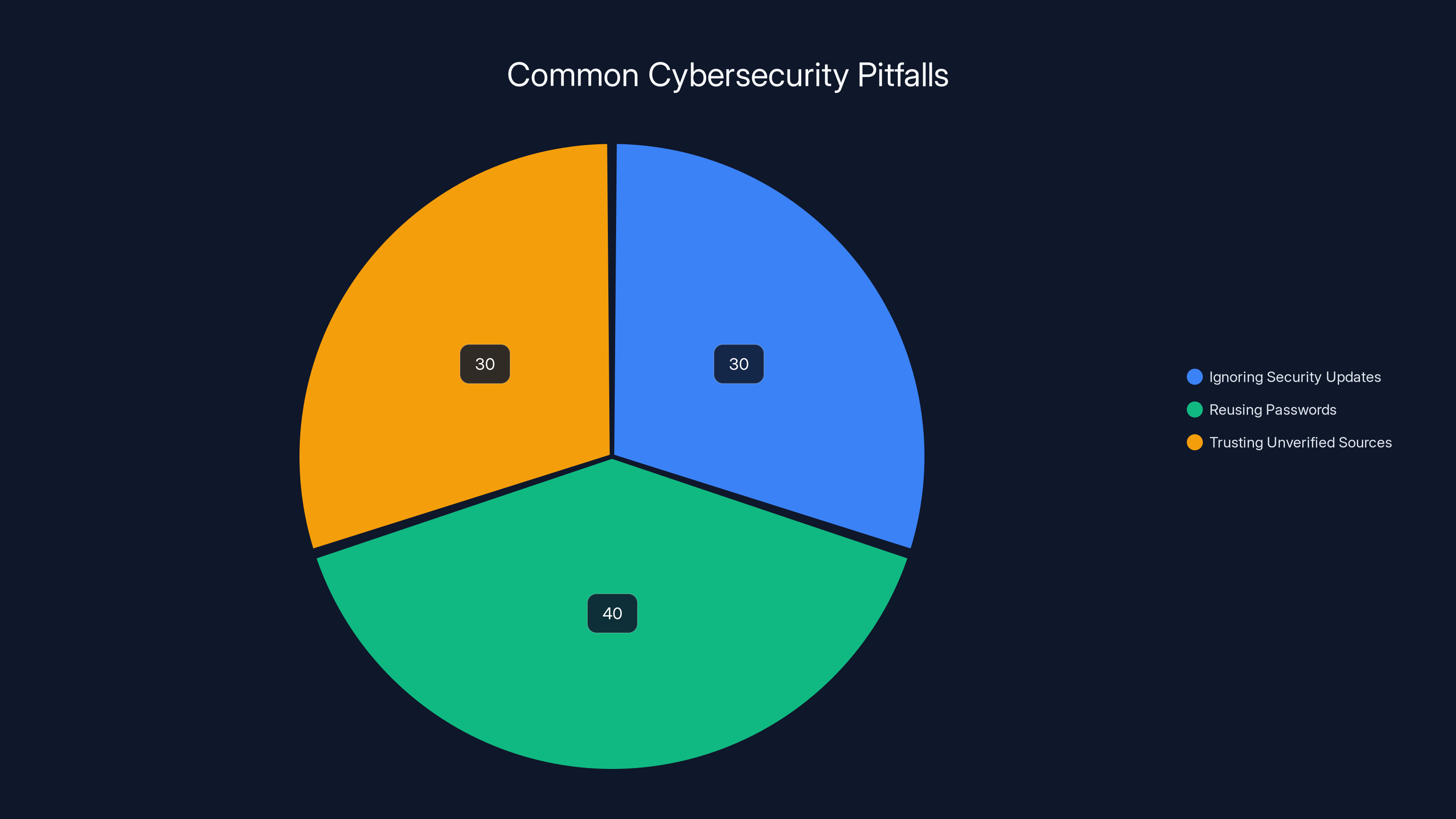
Estimated data shows that reusing passwords is the most common cybersecurity pitfall, followed by ignoring security updates and trusting unverified sources.
Understanding the Phishing Threat
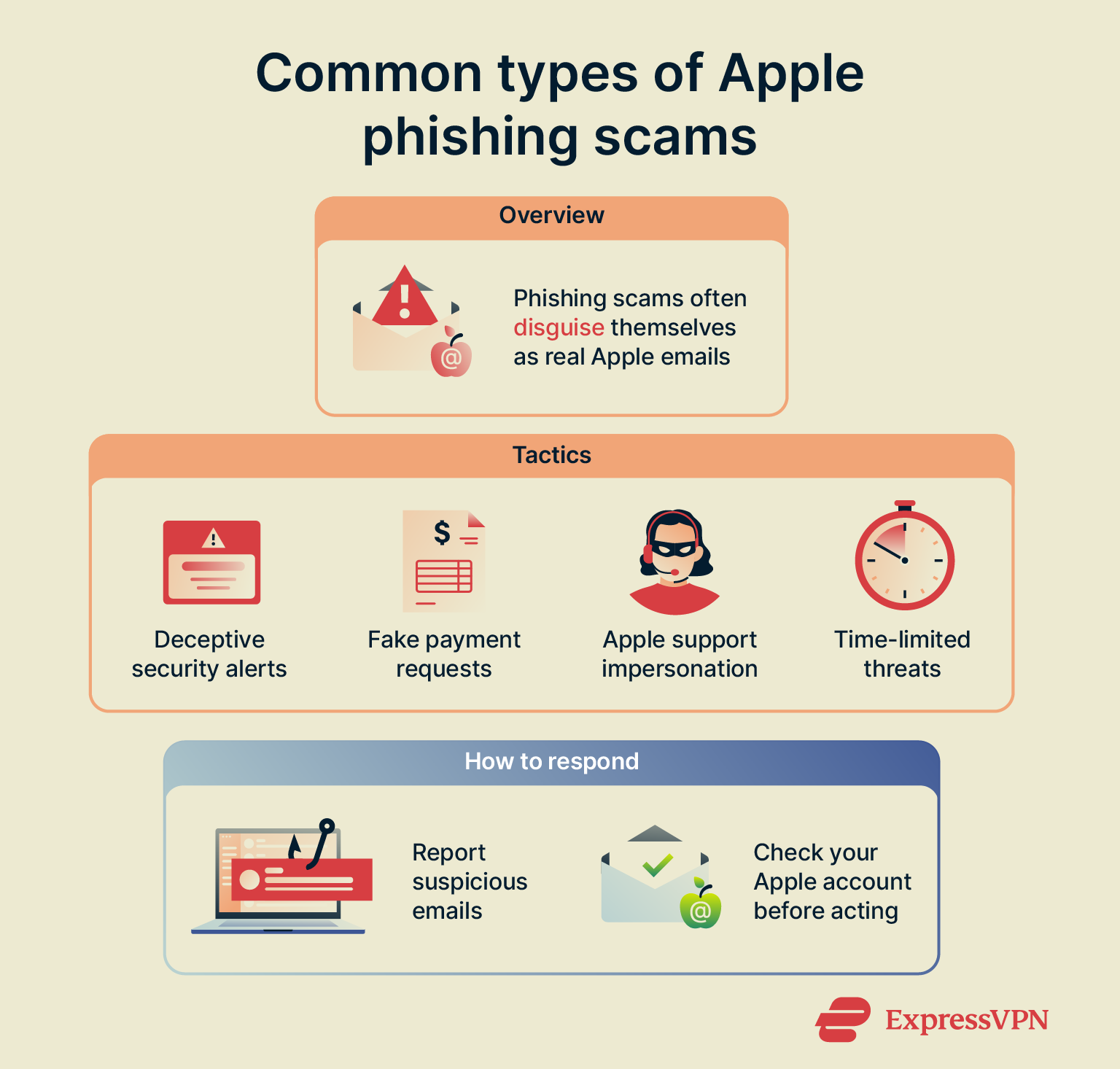
Phishing scams are designed to trick users into divulging personal information, such as passwords and credit card numbers. These scams often masquerade as legitimate communications from trusted organizations, like Apple. The recent iCloud phishing emails are part of this larger trend, exploiting the trust users have in Apple's brand, as noted by Consumer Affairs.
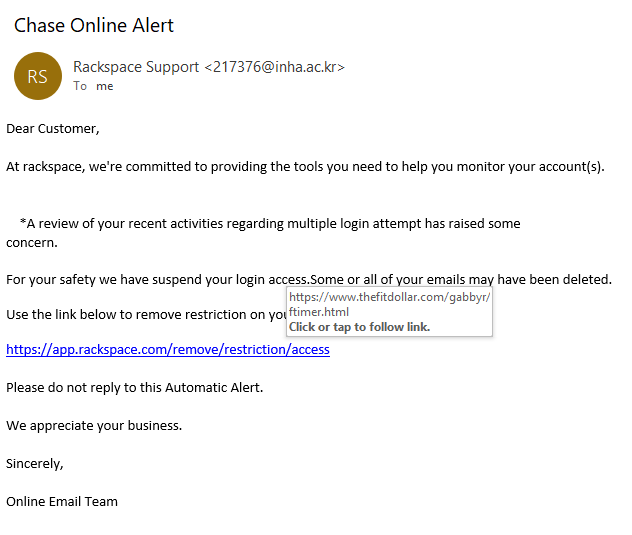
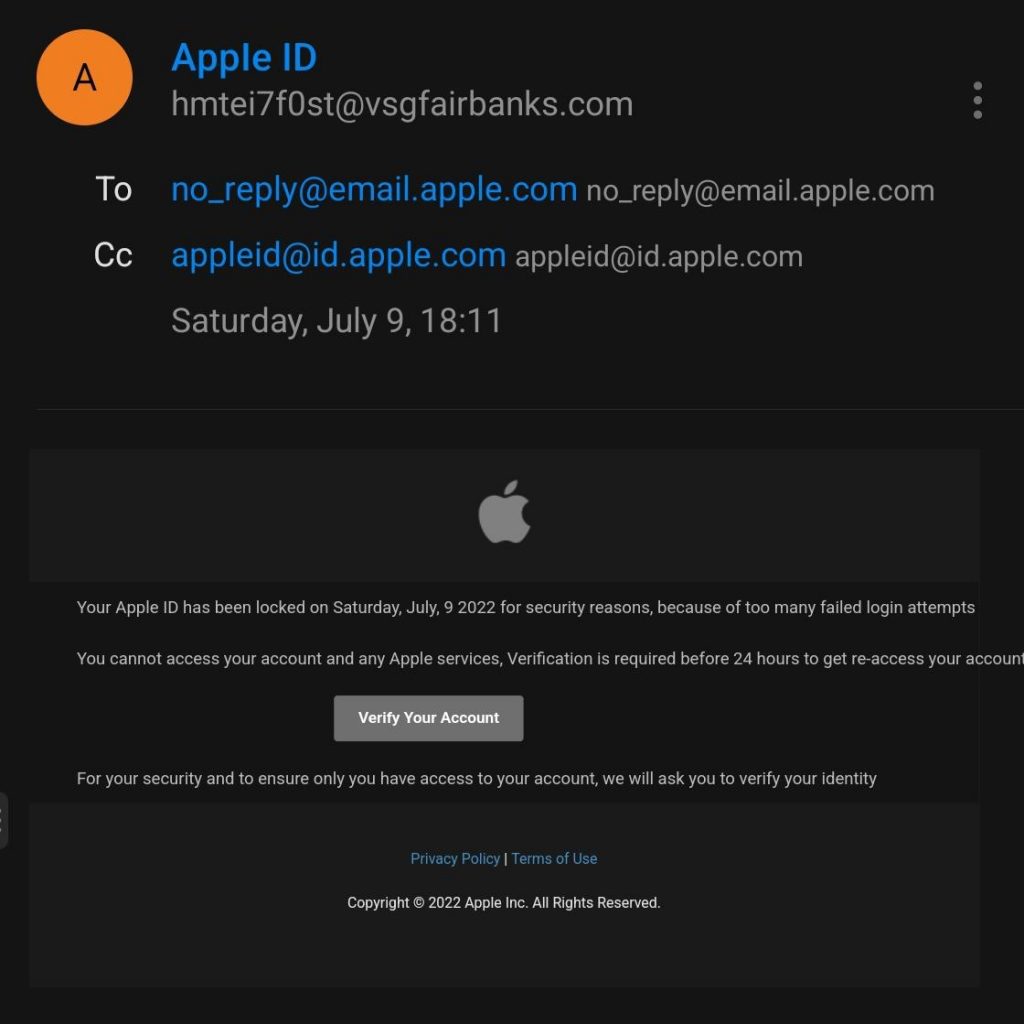
Anatomy of a Phishing Email
Phishing emails typically contain several telltale signs that can help you identify them:
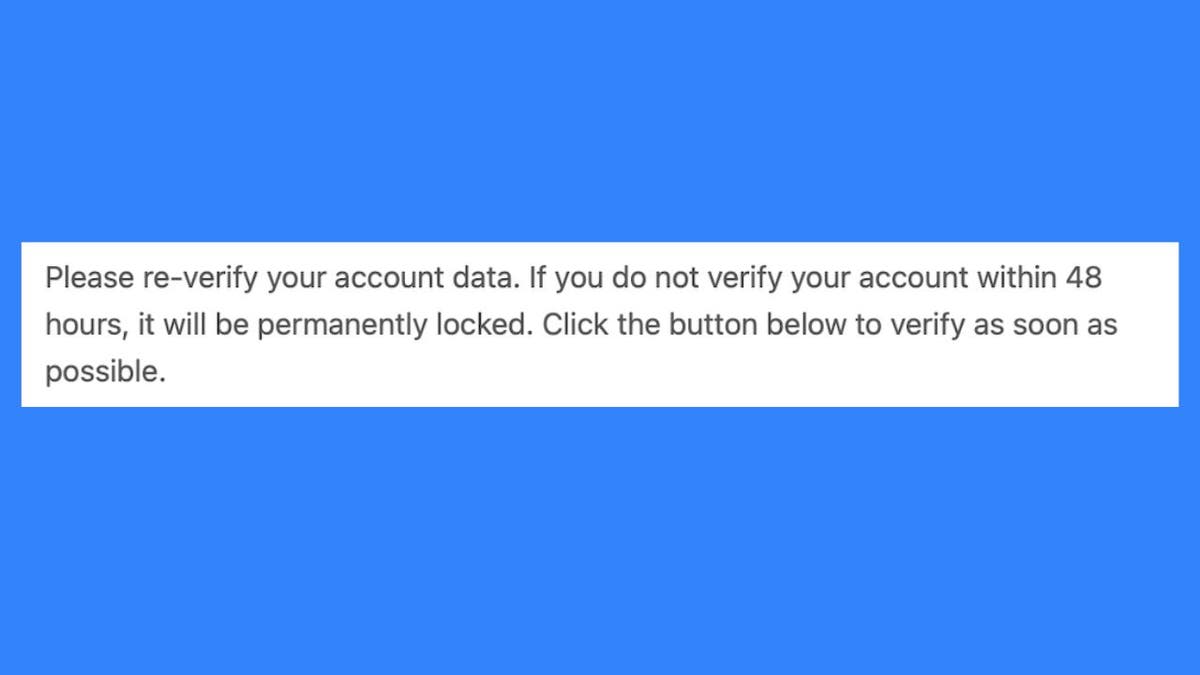
- Urgent Language: Emails often contain urgent messages about account security to panic users into action.
- Poor Grammar and Spelling: Many phishing emails are poorly written, with noticeable grammar and spelling errors, as discussed in Penn's Almanac.
- Suspicious URLs: Links in the email may look legitimate but often lead to malicious websites designed to harvest your credentials.
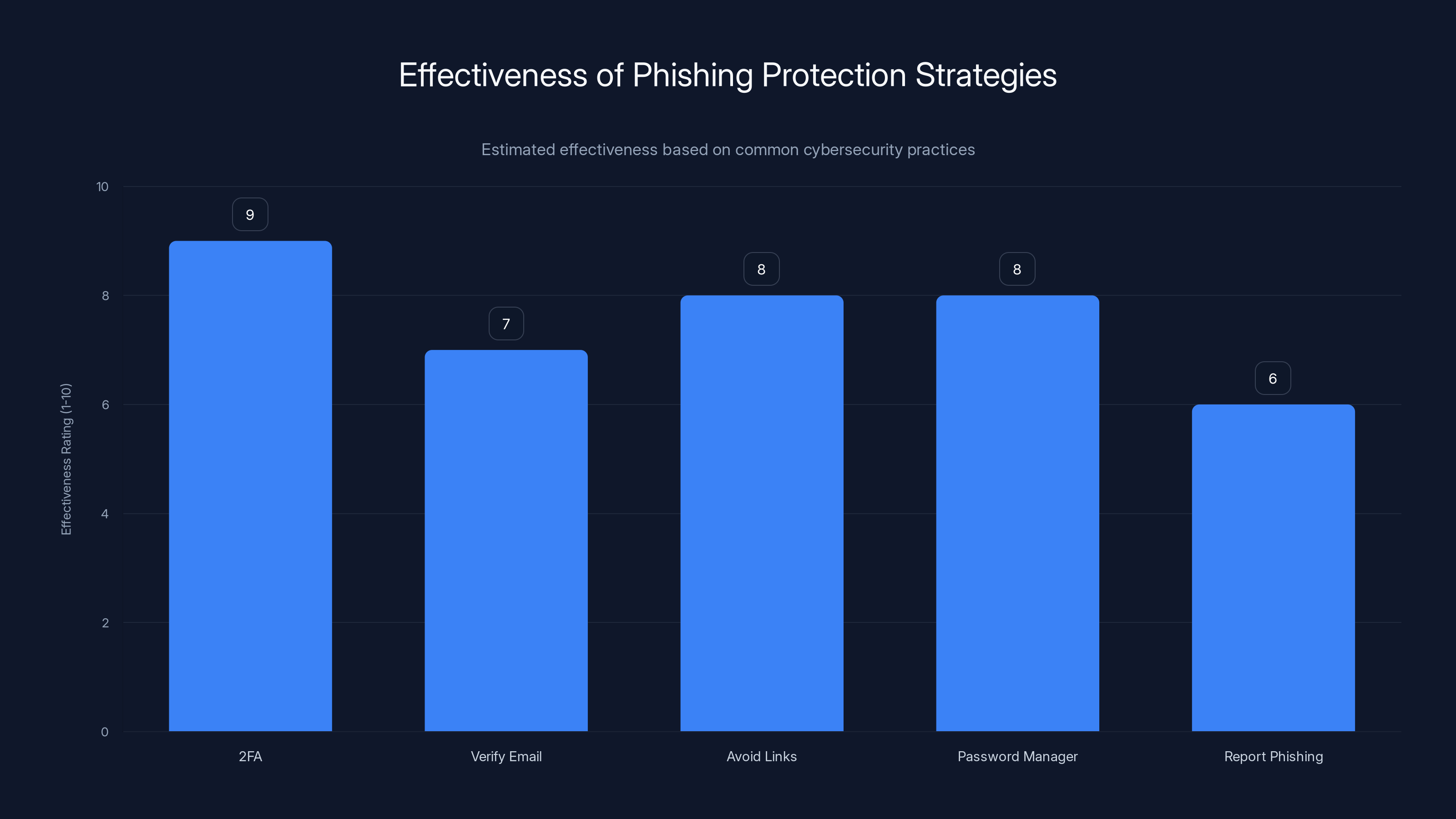
Two-factor authentication (2FA) is rated as the most effective strategy against phishing scams, followed closely by using a password manager and avoiding links in emails. (Estimated data)
How the Scam Works
The iCloud phishing emails typically warn users that their account is at risk of deletion due to insufficient storage or security issues. The email urges the user to click a link to upgrade their storage or secure their account. Once the user clicks the link, they are directed to a fake Apple login page, where their credentials are captured, as explained by Local 3 News.
Real-World Example
Consider this scenario: Jane receives an email appearing to be from Apple, warning her that her iCloud storage is full and her account will be deleted in 24 hours unless she upgrades her plan. Panicked, Jane clicks the link, enters her Apple ID and password on the fake login page, and unknowingly provides her credentials to the attackers.
Protecting Yourself from Phishing Scams
The best way to protect yourself from phishing scams is to be vigilant and proactive. Here are some practical steps you can take:
1. Enable Two-Factor Authentication (2FA)
Two-factor authentication adds an extra layer of security to your account. Even if your password is compromised, 2FA requires a second form of verification, typically a code sent to your phone, to access your account. This is recommended by The New York Times.
2. Verify the Sender's Email Address
Check the sender's email address carefully. Phishing emails often use addresses that look similar to legitimate ones but have slight variations.
3. Avoid Clicking Links in Emails
Instead of clicking links in emails, go directly to the official website by typing the URL into your browser. This ensures you are accessing the legitimate site, as advised by West Point AOG.
4. Use a Password Manager
Password managers can generate and store strong, unique passwords for each of your accounts, reducing the risk of using a compromised password across multiple sites.
5. Report Phishing Attempts
If you receive a suspicious email, report it to your email provider and the impersonated company. Apple has a dedicated page for reporting phishing attempts, as noted by NCOA.

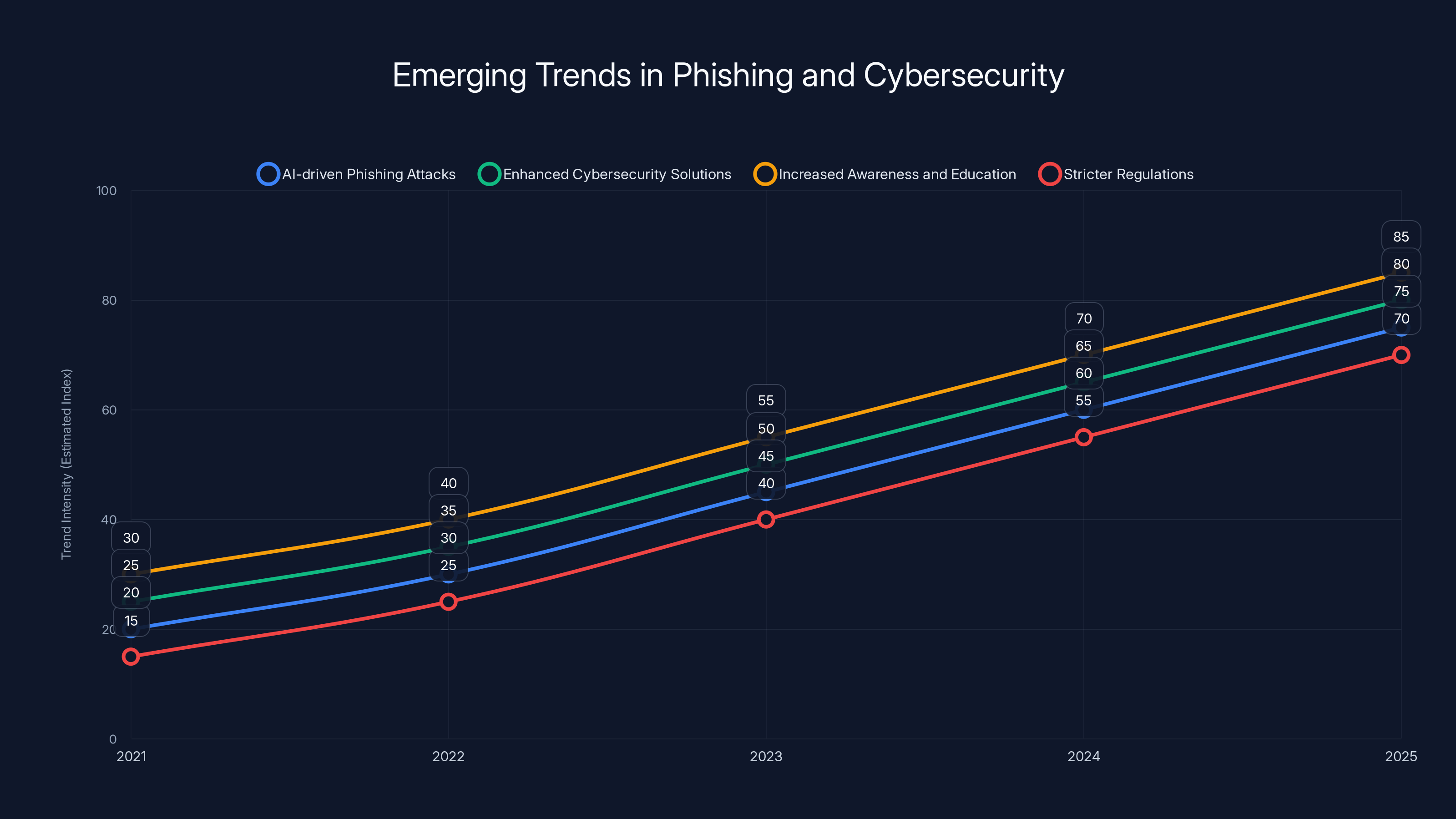
AI-driven phishing attacks and enhanced cybersecurity solutions are projected to grow significantly by 2025. Estimated data.
Common Pitfalls and How to Avoid Them
Even the most cautious users can fall victim to phishing scams. Here are some common pitfalls and strategies to avoid them:
Pitfall 1: Ignoring Security Updates
Failing to update your software and apps can leave your devices vulnerable to known exploits. Always keep your systems up to date.
Pitfall 2: Reusing Passwords
Using the same password across multiple sites increases the risk of a security breach. Unique passwords for each account are crucial, as emphasized by eSecurity Planet.
Pitfall 3: Trusting Unverified Sources
Avoid downloading apps or files from unverified sources, as they may contain malware.

Future Trends in Phishing and Cybersecurity
As technology evolves, so do the tactics of cybercriminals. Here are some emerging trends in phishing and cybersecurity:
AI-Driven Phishing Attacks
Cybercriminals are increasingly using artificial intelligence to create more convincing phishing emails that can bypass traditional security measures, as reported by Harvard Business Review.
Enhanced Cybersecurity Solutions
AI and machine learning are also being used to develop advanced cybersecurity solutions that can detect and prevent phishing attempts in real-time.
Increased Awareness and Education
Organizations are investing in cybersecurity education for employees, teaching them how to recognize and respond to phishing threats, as highlighted by Hacked.com.
Legislation and Regulation
Governments worldwide are implementing stricter regulations and penalties for cybercriminals to deter potential attacks.
Best Practices for Staying Safe Online
Staying safe online requires a combination of vigilance, education, and the right tools. Here are some best practices for protecting yourself:
- Regularly Update Software: Keep your operating system and apps updated to protect against vulnerabilities.
- Use Strong Passwords: Create complex passwords and change them regularly.
- Educate Yourself and Others: Stay informed about the latest threats and share information with friends and family.
- Back Up Your Data: Regularly back up your data to prevent loss in the event of an attack.

Conclusion
Phishing scams targeting Apple users are a growing concern, but with the right knowledge and precautions, you can protect yourself. Stay informed, remain vigilant, and adopt best practices to secure your digital life.
FAQ
What is phishing?
Phishing is a cybercrime where attackers impersonate legitimate organizations to steal personal information through fraudulent communications.
How can I recognize a phishing email?
Look for signs such as urgent language, poor grammar, and suspicious URLs. Always verify the sender's email address.
What should I do if I receive a phishing email?
Do not click on any links or provide personal information. Report the email to your email provider and the impersonated company.
How does two-factor authentication help protect my account?
Two-factor authentication adds an additional security layer by requiring a second form of verification, such as a code sent to your phone.
What trends are emerging in phishing and cybersecurity?
Trends include AI-driven phishing attacks, enhanced cybersecurity solutions, increased awareness and education, and stricter regulations.
Use Case: Simplify your cybersecurity management with AI-powered automation.
Try Runable For Free
Key Takeaways
- Phishing scams exploit trusted brands like Apple to steal user information.
- Recognizing phishing signs is crucial for online safety.
- Two-factor authentication significantly enhances account security.
- AI is both a tool for cybercriminals and a defense mechanism.
- User education and awareness are key to preventing phishing attacks.
Related Articles
- Secure Your Digital Life: Keeper Password Manager's Big Discounts [2026]
- 'Trusted Access for the Next Era of Cyber Defense': OpenAI's Cybersecurity Revolution [2025]
- How Hackers Hijack Your Inbox with Clever Tactics [2025]
- Understanding the Complexities of Prompt Injection Vulnerabilities in AI Systems [2025]
- WordPress Plugin Security Attacks: Safeguarding Your Site [2025]
- Inside the Kraken Extortion Attack: How Crypto Giants Defend Against Cyber Threats [2025]
![Stay Safe from iCloud Phishing Scams: What Every Apple User Needs to Know [2025]](https://tryrunable.com/blog/stay-safe-from-icloud-phishing-scams-what-every-apple-user-n/image-1-1776288829260.png)



