Asus Routers Hijacked to Power a Cybercrime Proxy Network: What We Know [2025]
Cybersecurity threats are evolving, and the latest wave of attacks has focused on consumer hardware, specifically Asus routers. These routers have been hijacked to power a dangerous cybercrime proxy network. This article dives deep into the mechanics of this threat, the implications for users, and what can be done to safeguard against such vulnerabilities.
TL; DR
- Kad Nap Malware: Over 14,000 Asus routers infected by Kad Nap, forming a botnet.
- Proxy Network: Used to facilitate illegal activities without users' consent.
- Security Flaws: Exploits vulnerabilities in outdated firmware and default settings.
- Mitigation Steps: Includes regular firmware updates and disabling remote management.
- Future Trends: Expect an increase in attacks targeting IoT and consumer devices.
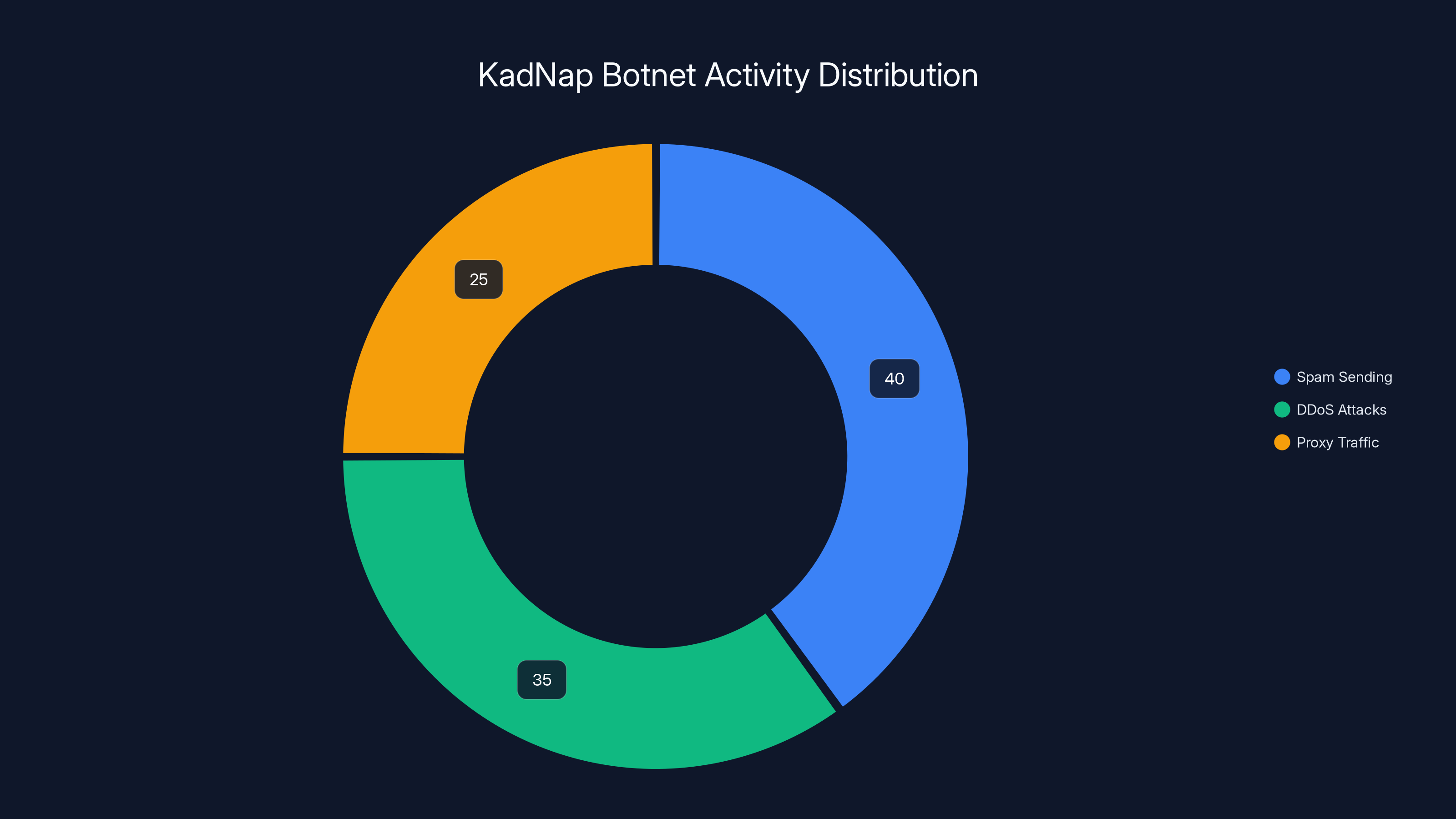
Estimated data shows that KadNap botnet primarily engages in spam sending (40%), followed by DDoS attacks (35%) and proxy traffic (25%).
The Rise of Kad Nap
The Kad Nap malware has emerged as a notable threat in the cybersecurity landscape. Discovered by Black Lotus researchers, Kad Nap has successfully infected over 14,000 Asus routers. These routers are then used as nodes in a botnet, which is a network of compromised devices controlled by attackers. This network facilitates malicious activities, including sending spam, launching Distributed Denial of Service (DDoS) attacks, and acting as a proxy for illicit internet traffic.
How Kad Nap Works
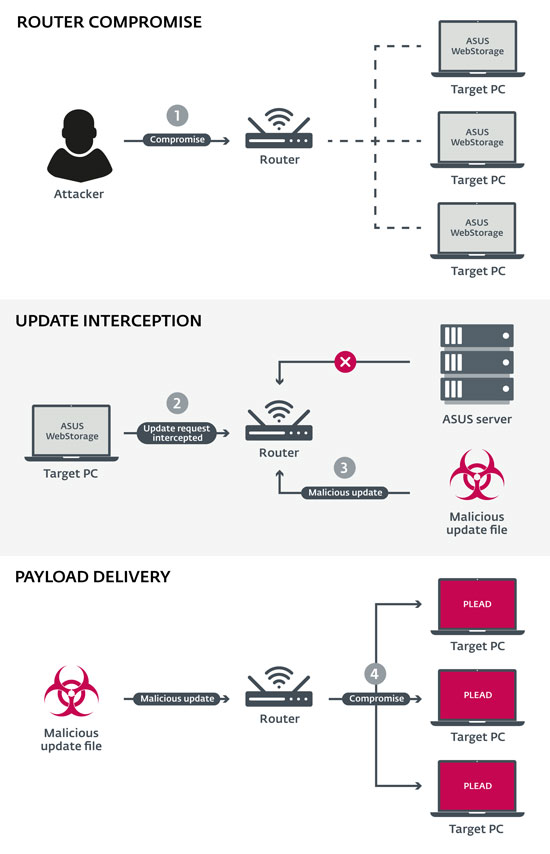
Kad Nap utilizes a custom implementation of the Kademlia DHT (Distributed Hash Table) protocol. This protocol is designed for decentralized and resilient peer-to-peer networks, making it difficult to dismantle the botnet. Here’s how it functions:
- Infection: The malware exploits known vulnerabilities in Asus routers, particularly those with outdated firmware or default configurations.
- Assimilation: Once a router is compromised, it becomes part of the Kad Nap network, communicating with other infected devices.
- Proxy Traffic: The compromised routers act as proxies, routing malicious traffic while masking the origin of the data.
Real-World Impact
The implications of Kad Nap are far-reaching. For users, this means their internet bandwidth is being used for criminal activities, potentially slowing down their network and increasing their data costs. Moreover, being part of a botnet can lead to legal issues if the router is linked to illegal activities.

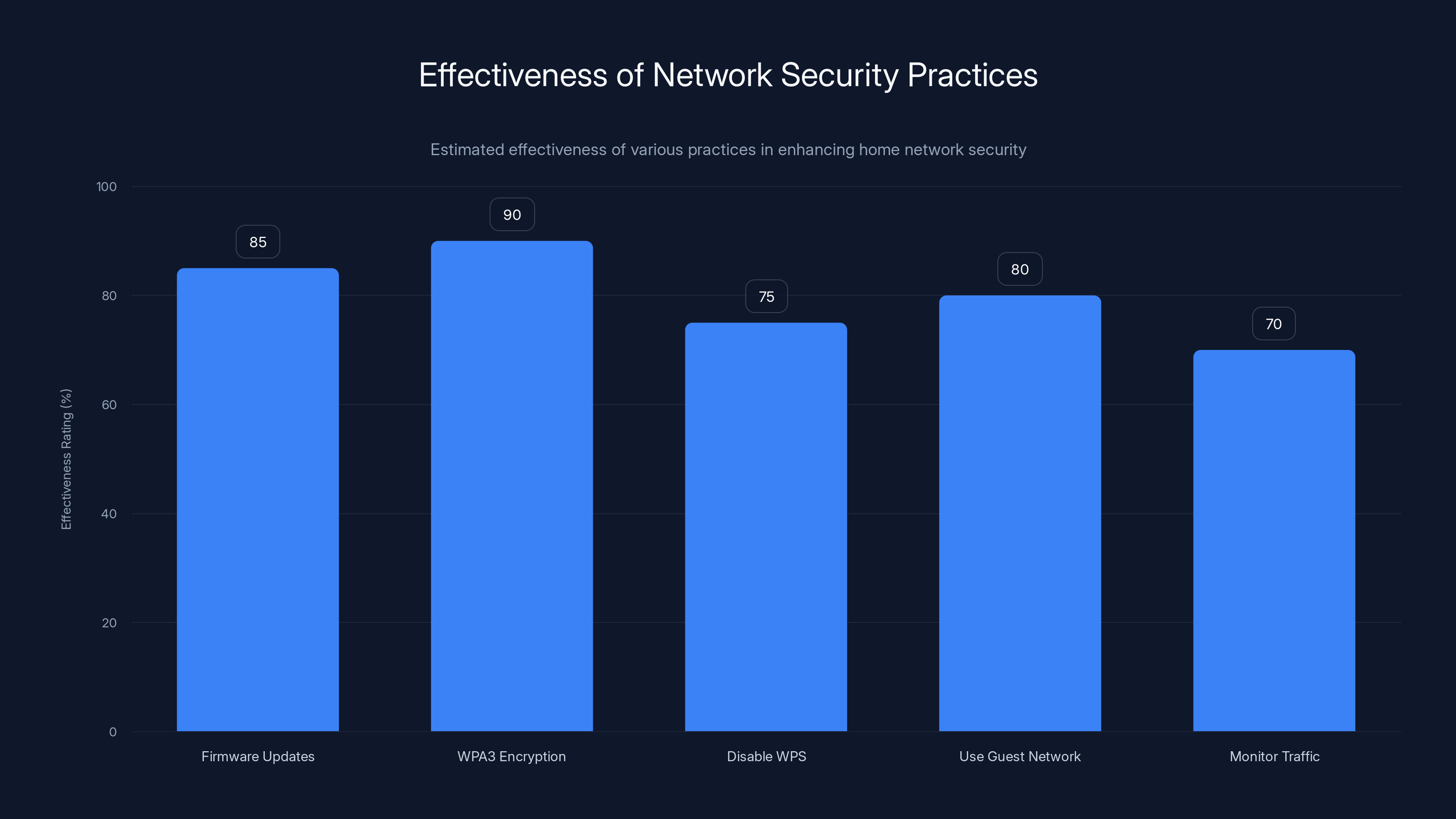
WPA3 Encryption is estimated to be the most effective practice, followed closely by regular firmware updates. Estimated data.
Understanding the Technical Details
To fully grasp the threat posed by Kad Nap, it’s essential to understand the technical vulnerabilities it exploits.
Firmware Vulnerabilities
Many Asus routers run on outdated firmware versions, leaving them open to exploits. Firmware is the software that controls the hardware of a device, and outdated versions often contain security flaws that have been patched in newer releases.
Common Vulnerabilities Include:
- Default Credentials: Many users do not change the default username and password, making it easy for attackers to gain access.
- Outdated Protocols: Older encryption protocols that are easier to break.
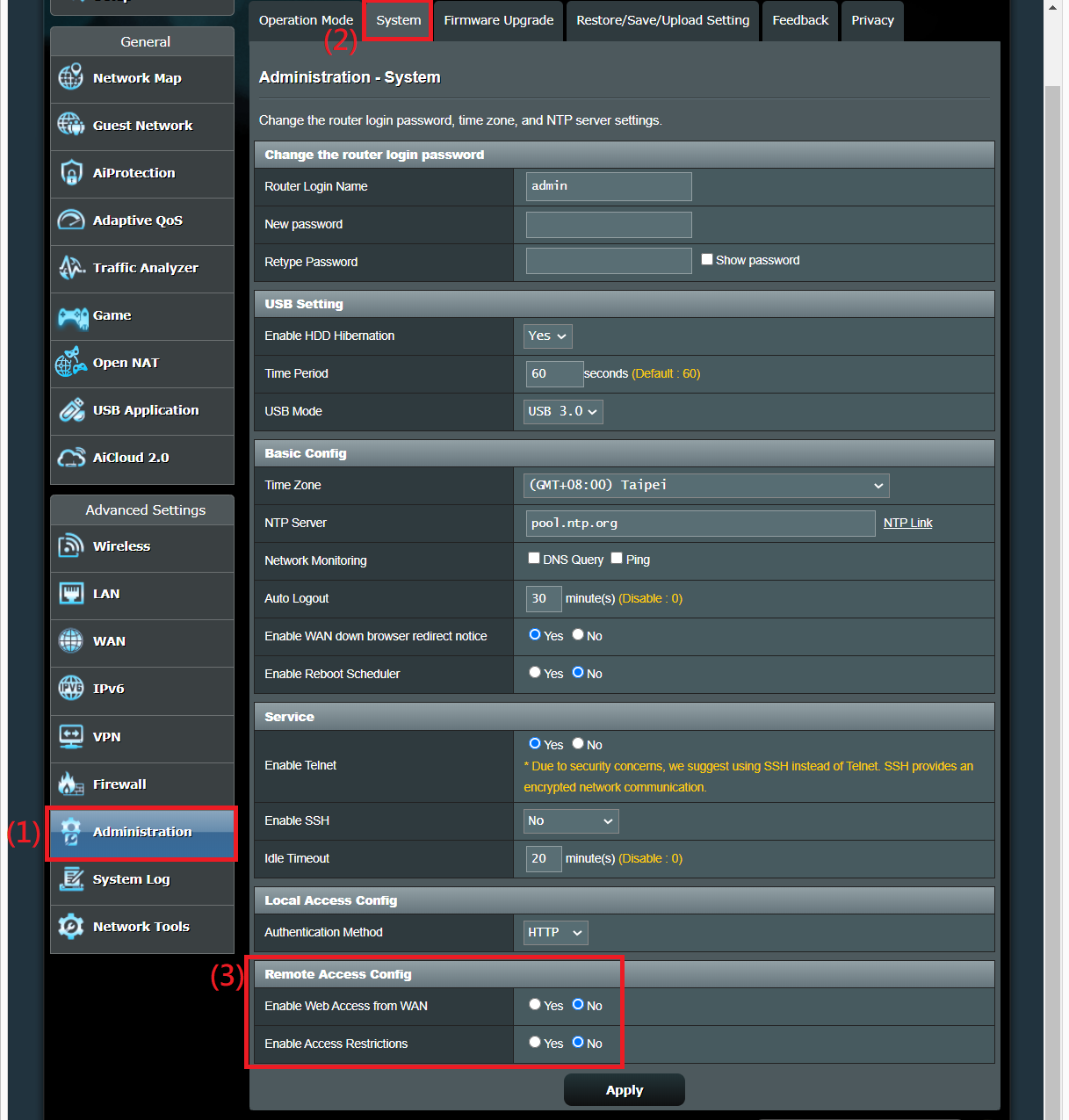
Exploiting Remote Management
Remote management features, if enabled, allow users to access their router’s interface from anywhere on the internet. However, this feature can be a significant security risk if not properly secured.
Mitigation Strategies:
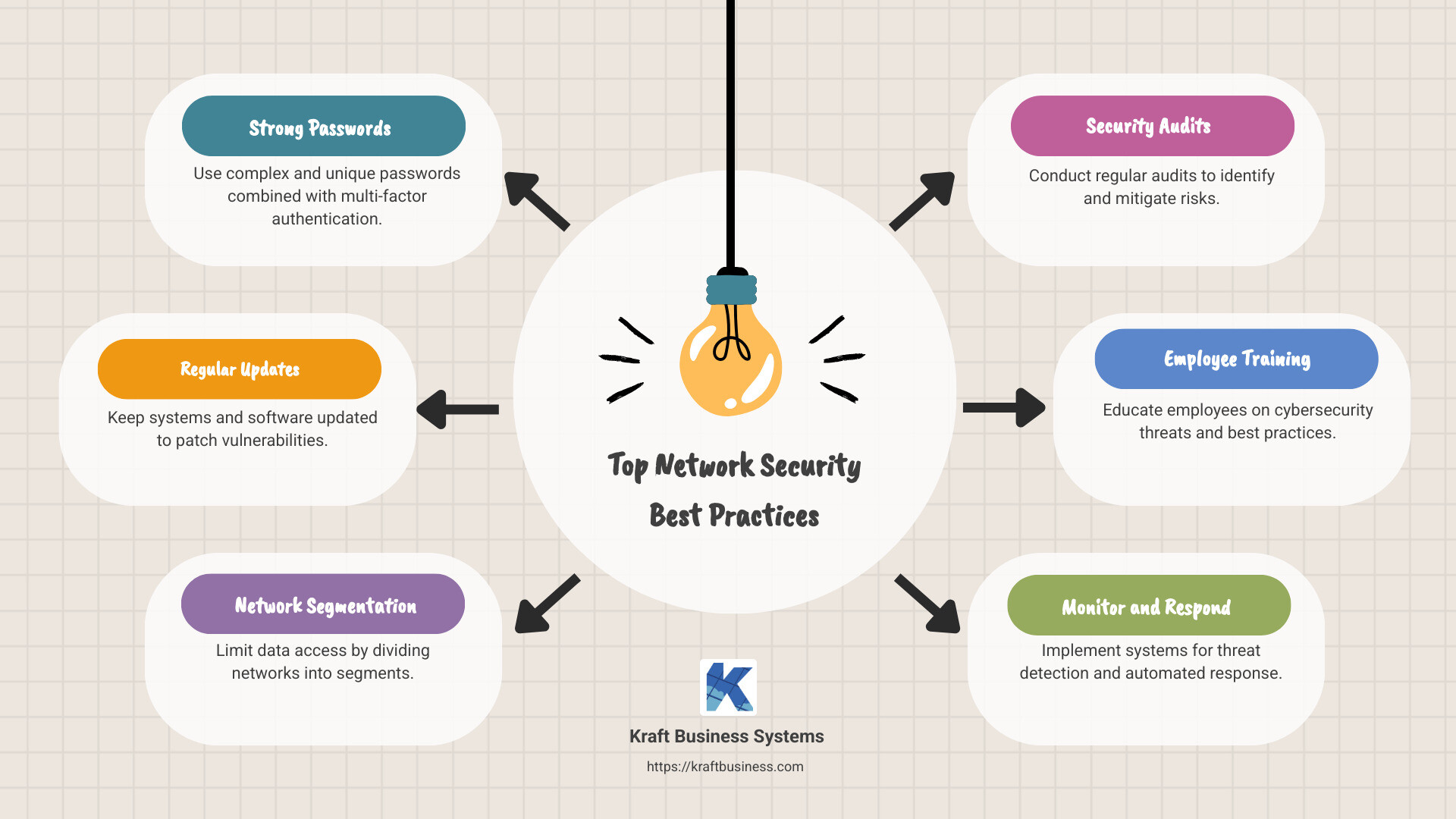
- Disable Remote Management: Unless absolutely necessary.
- Use Strong Passwords: Combine uppercase, lowercase, numbers, and symbols.

Building a Defense: Best Practices
Protecting against threats like Kad Nap requires both proactive measures and constant vigilance.
Firmware Updates
Regularly updating your router’s firmware is crucial. Manufacturers release updates to patch known vulnerabilities and enhance security features.
Steps to Update Firmware:
- Access the router’s web interface.
- Navigate to the firmware update section.
- Check for available updates and follow the installation instructions.
Network Security
Enhancing your home network security can deter attempts to compromise your router.
- Enable WPA3 Encryption: The latest and most secure Wi-Fi encryption standard.
- Disable WPS: Wi-Fi Protected Setup can be exploited in certain scenarios.
- Use a Guest Network: Isolates your main network from less secure devices.
Monitoring Network Traffic
Regularly monitoring network traffic can help identify unusual activity.
- Tools: Use network monitoring tools like Wireshark or PRTG.
- Indicators: Look for unusual spikes in traffic or unknown devices on your network.
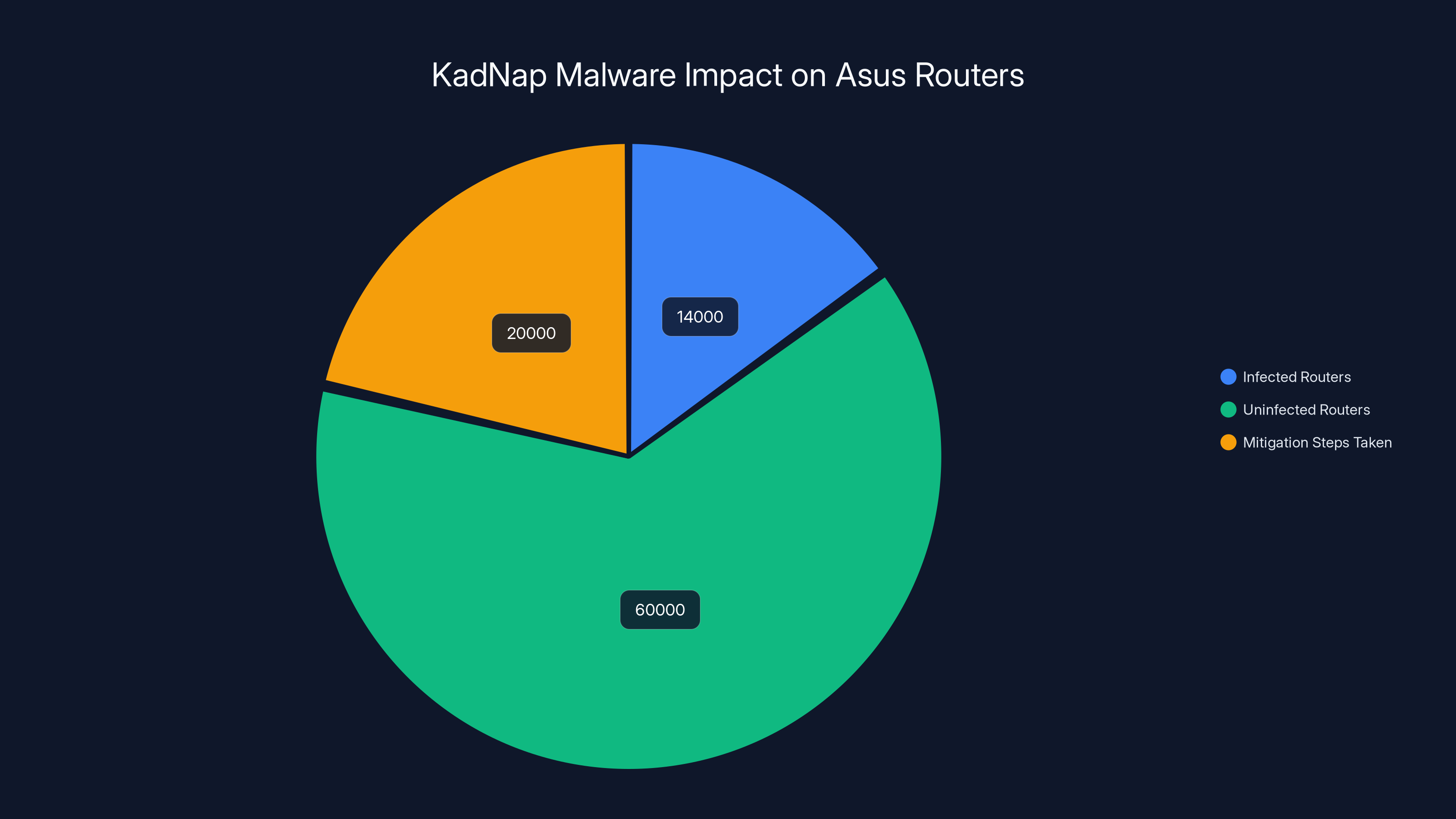
Estimated data shows 14,000 Asus routers infected by KadNap malware, with mitigation steps taken for 20,000 routers. Estimated data.
The Evolving Threat Landscape
As cybercriminals continue to innovate, the threat landscape evolves. The focus on IoT (Internet of Things) and consumer devices like routers is expected to intensify.
Future Trends
- Increased IoT Attacks: As more devices connect to the internet, they become targets for cyber attacks.
- Sophisticated Malware: Malware is becoming more advanced, using AI to adapt and evade detection.
Recommendations for Users
Staying ahead of these threats requires adopting a security-first mindset.
- Educate Yourself: Stay informed about the latest threats and security practices.
- Invest in Security Solutions: Consider advanced security solutions that include intrusion detection and prevention.

Conclusion
The hijacking of Asus routers by the Kad Nap malware highlights the vulnerabilities in consumer hardware and the need for robust security practices. By understanding the threats and implementing the recommended measures, users can better protect themselves from becoming unwitting participants in cybercrime.
FAQ
What is Kad Nap malware?
Kad Nap is a malware strain that targets Asus routers, integrating them into a botnet used for malicious proxy traffic.
How does Kad Nap affect Asus routers?
It exploits vulnerabilities in the routers to take control and use them to route illicit internet traffic without the owner's knowledge.
How can I protect my Asus router from Kad Nap?
Regularly update your router's firmware, disable remote management, and ensure strong, unique passwords for your network.
Are there any legal risks associated with my router being part of a botnet?
Yes, if your router is used for illegal activities, you could be implicated, even if unknowingly.
What future trends should I be aware of regarding router security?
Expect an increase in attacks targeting IoT devices and more sophisticated malware using AI to evade detection.
Why are Asus routers specifically targeted by Kad Nap?
While not specifically targeted, Asus routers may be more susceptible due to their prevalence and potential security vulnerabilities.
What tools can help me monitor network traffic for signs of malware?
Tools like Wireshark and PRTG can help monitor network traffic for unusual activity, indicating potential malware presence.
Key Takeaways
- KadNap malware has infected over 14,000 Asus routers.
- Compromised routers form a botnet for malicious proxy traffic.
- Firmware vulnerabilities are a key entry point for attacks.
- Disabling remote management can mitigate risks.
- Expect more attacks on IoT and consumer devices in the future.
- Regular firmware updates are crucial for router security.
- Advanced security solutions can help detect and prevent intrusions.
- Monitoring network traffic can reveal signs of compromise.
Related Articles
- Securing 6G Networks: Global Efforts and Future Trends [2025]
- The $30 Malware Threat: How Ancient Visual Basic Powers Modern Cybercrime [2025]
- WhatsApp Introduces Parent-Linked Accounts for Pre-Teens: A Comprehensive Guide [2025]
- How Meta is Fighting Back Against Scammers with Advanced Technology [2025]
- Unmasking BlackSanta: The Malware Targeting HR Departments [2025]
- Meta's New Scam Protection Features: Safeguarding Users in 2025
![Asus Routers Hijacked to Power a Cybercrime Proxy Network: What We Know [2025]](https://tryrunable.com/blog/asus-routers-hijacked-to-power-a-cybercrime-proxy-network-wh/image-1-1773245137334.jpg)



