Unmasking Black Santa: The Malware Targeting HR Departments [2025]
Introduction
Last year, a new cybersecurity threat emerged, targeting one of the most unsuspecting sectors within companies: Human Resources (HR). This malware, known as Black Santa, has been wreaking havoc by exploiting the very tools meant to protect organizations—EDR systems. As an expert in cybersecurity, I’ve spent months studying this threat. Here’s everything you need to know about Black Santa, from how it operates to how you can safeguard your organization against it.

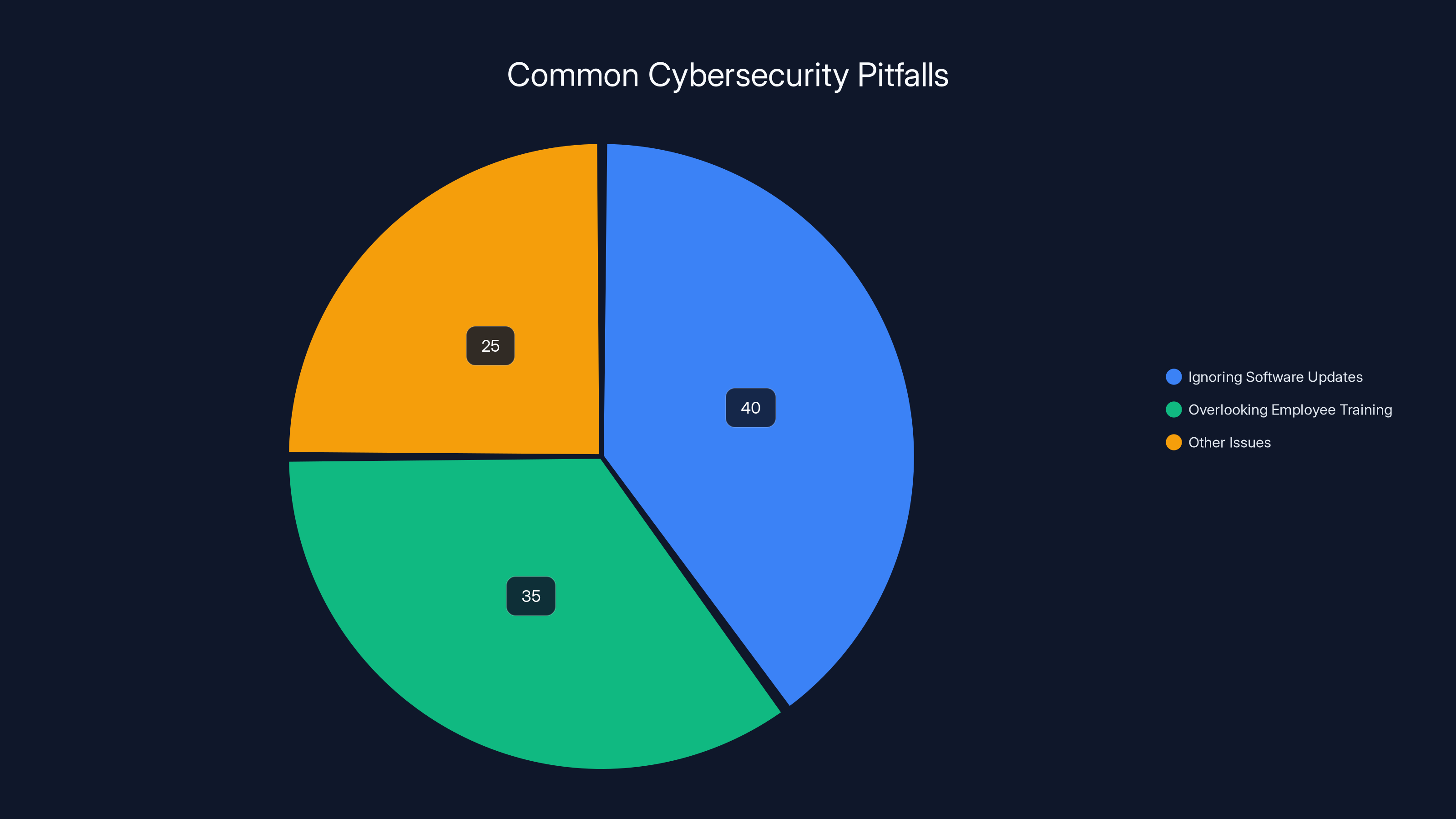
Ignoring software updates and overlooking employee training are major cybersecurity pitfalls, with estimated shares of 40% and 35% respectively. Estimated data.
TL; DR
- Black Santa malware targets HR departments using phishing emails with malicious ISO files.
- Disables EDR tools, allowing deep system compromise.
- Sophisticated infection chain starts with fake resumes and Dropbox links.
- Cybersecurity best practices are essential to prevent breaches.
- Future trends suggest increased sophistication in malware attacks.
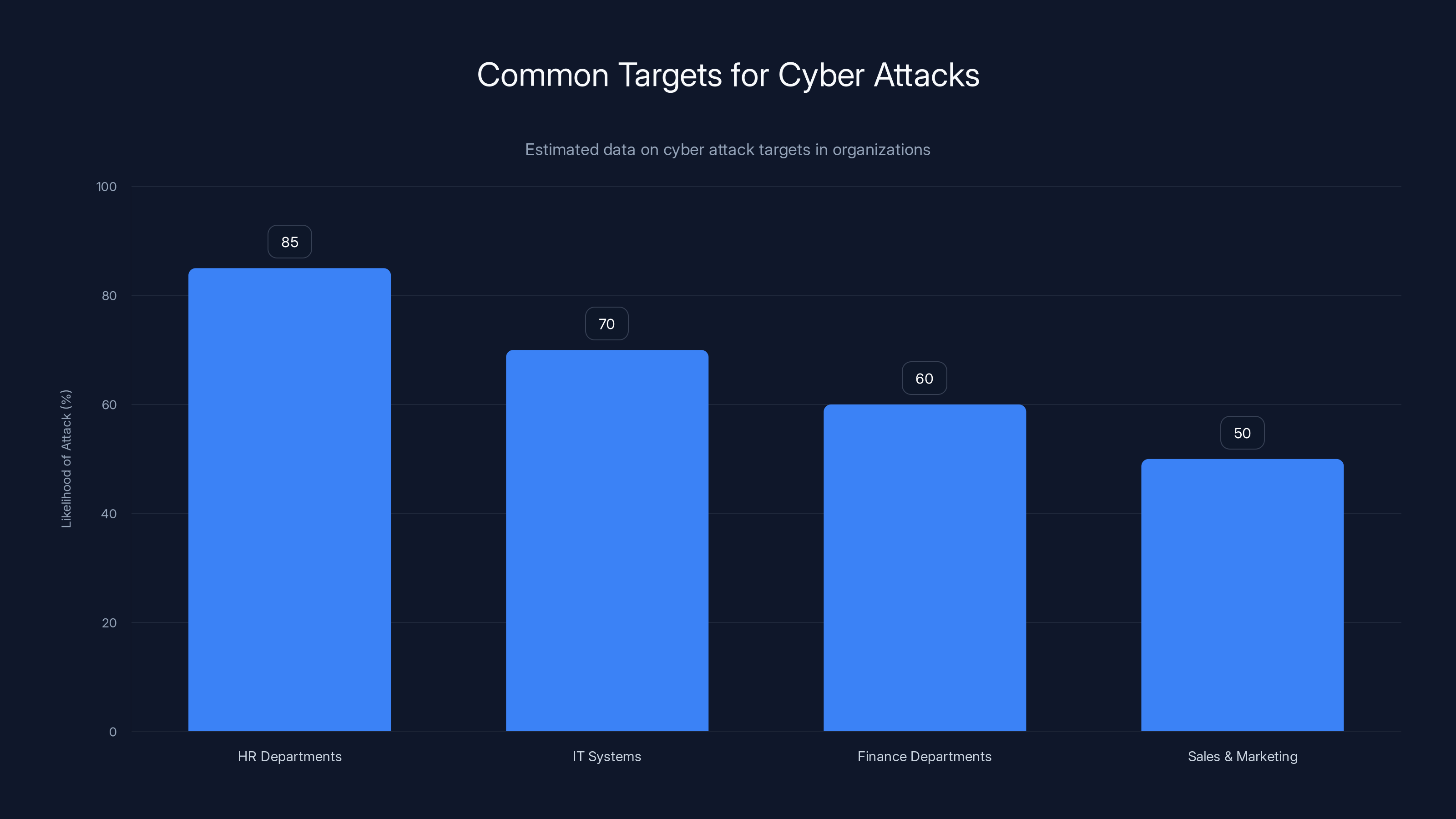
HR departments are increasingly targeted by cybercriminals due to the sensitive data they manage. Estimated data shows HR as a top target.
The Rise of Black Santa
A New Threat in the Cyber Landscape
The emergence of Black Santa is a stark reminder of how cyber threats continue to evolve. HR departments, often less fortified than IT, have become attractive targets for hackers seeking to exploit vulnerabilities. According to Dark Reading, Black Santa has been particularly effective in bypassing traditional security measures.
Why HR?
HR departments are gold mines for cybercriminals. They handle sensitive personal data, including Social Security numbers, addresses, and bank details. By infiltrating HR systems, attackers gain access to a treasure trove of valuable information. As noted by JD Supra, HR departments are increasingly vulnerable due to the sensitive nature of the data they handle.
How Black Santa Operates
The Infection Chain
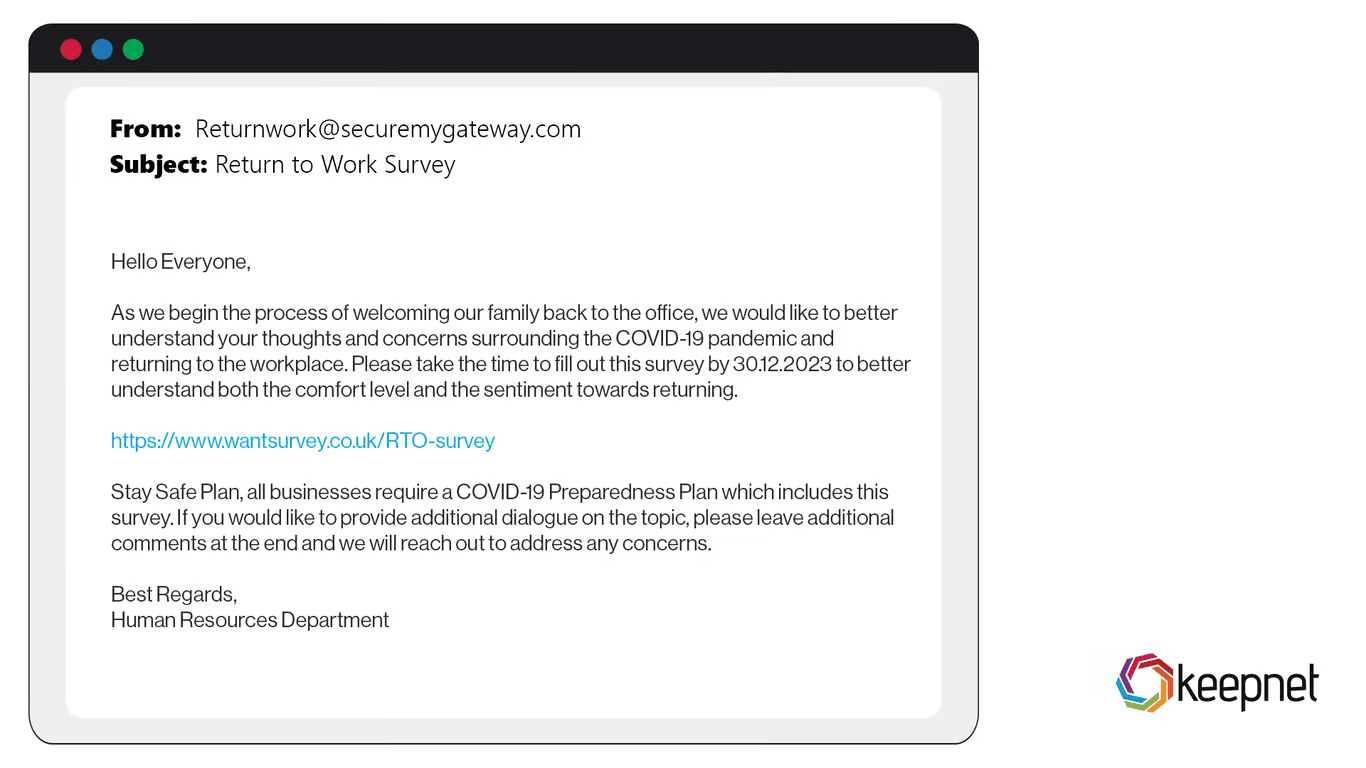
Black Santa employs a sophisticated infection chain that starts with a phishing email. These emails typically masquerade as job applications, containing a link to a Dropbox folder. Inside is a malicious ISO file, disguised as a resume. When opened, the ISO file executes a script that initiates the malware installation process. This method has been detailed in Help Net Security, highlighting the innovative techniques used by cybercriminals.
Disabling EDR Tools
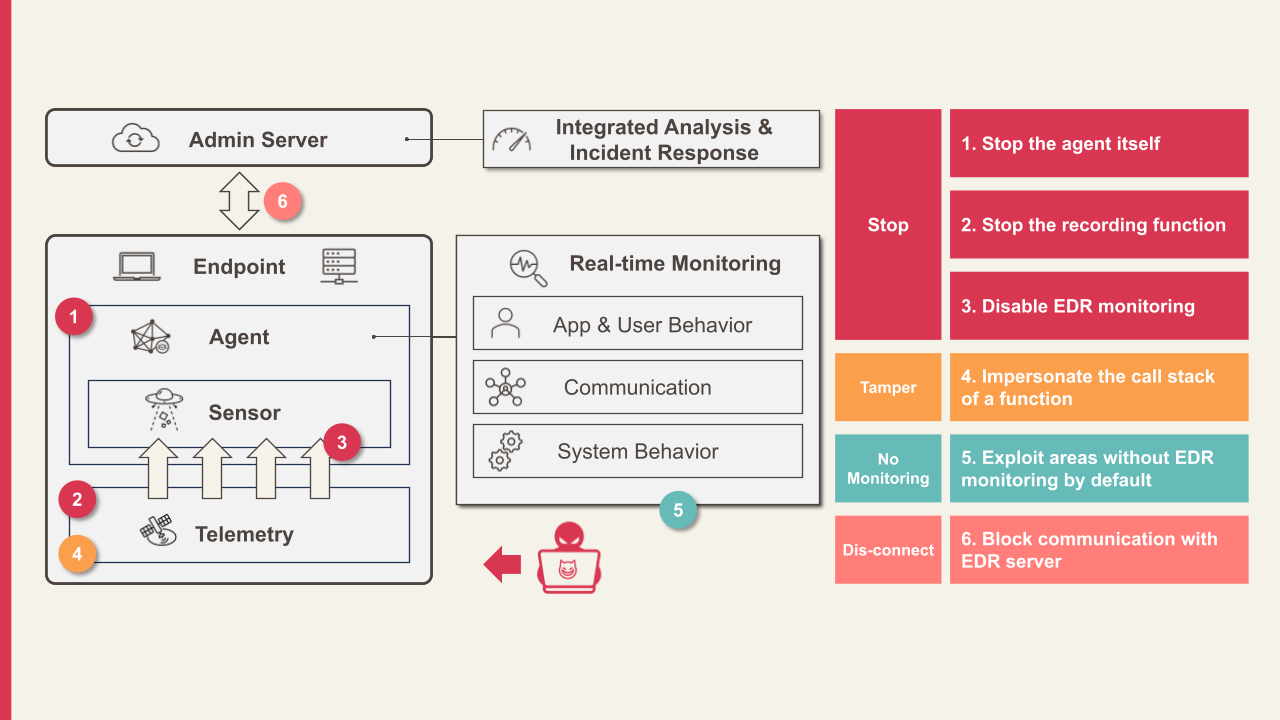
One of Black Santa's most dangerous features is its ability to disable Endpoint Detection and Response (EDR) tools. EDR systems are designed to detect and respond to suspicious activities. By incapacitating these tools, Black Santa can operate undetected, allowing hackers to navigate deeper into the network. SecurityWeek provides an in-depth analysis of how Black Santa achieves this.

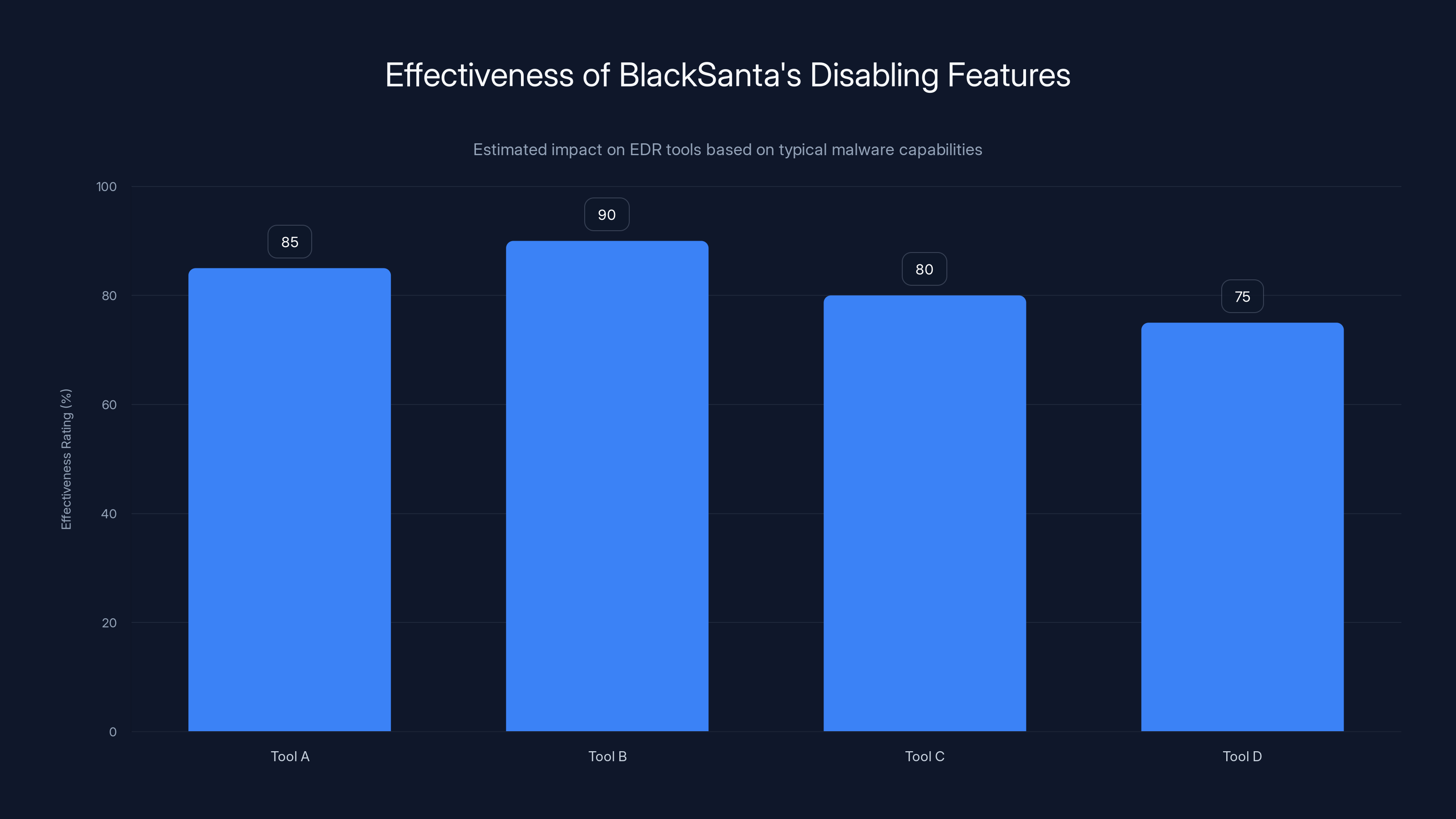
BlackSanta is estimated to disable EDR tools with an effectiveness ranging from 75% to 90%, making it a significant threat. Estimated data.
Technical Breakdown
Understanding EDR Disabling
Black Santa employs advanced techniques to disable EDR tools. It uses code injection and process hollowing to manipulate system processes. This allows the malware to run under the guise of legitimate applications, bypassing security measures. Security Brief discusses the technical intricacies of these methods.
plaintext// Example of process hollowing technique Create Process A(target Path, NULL, NULL, NULL, FALSE, CREATE_SUSPENDED, NULL, NULL, &si, &pi); Nt Unmap View Of Section(pi.h Process, target Base Address); Write Process Memory(pi.h Process, target Base Address, payload, payload Size, NULL); Resume Thread(pi.h Thread);
The Role of ISO Files
ISO files are typically used to distribute software. Black Santa exploits this by using ISO images to deliver its payload, knowing that many users recognize ISOs as legitimate files. This trick allows the malware to bypass some email filters that might block traditional executable files. Computing highlights the effectiveness of using ISO files in malware distribution.
Protecting Your Organization
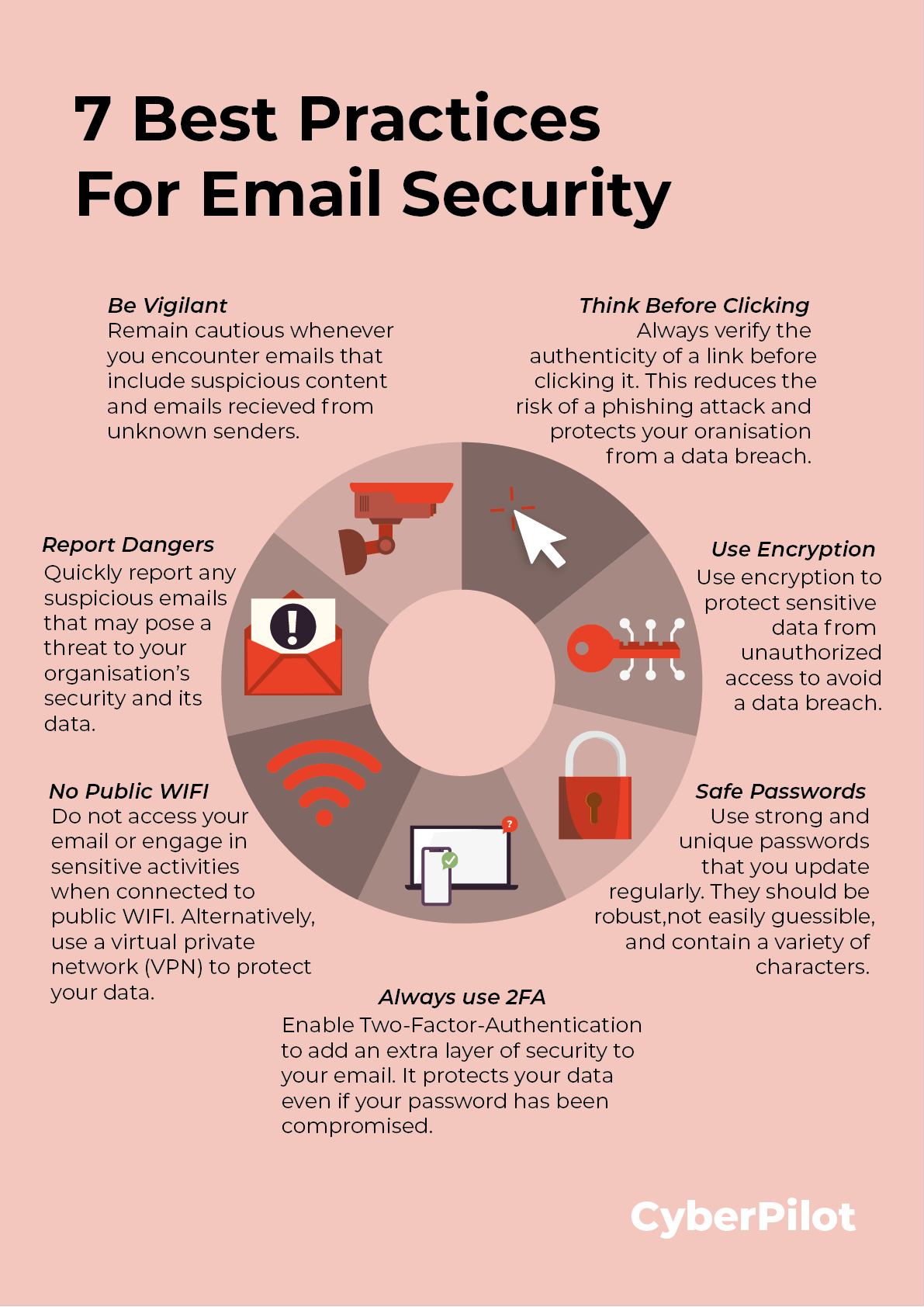
Implementing Stronger Email Security
Email security is the first line of defense against Black Santa. Organizations must employ spam filters and email authentication protocols like SPF, DKIM, and DMARC to identify and block phishing attempts. The National Cyber Security Alliance provides valuable tips for enhancing email security.
Enhancing EDR Capabilities
Since Black Santa targets EDR tools, enhancing these systems is crucial. Consider using behavior-based detection rather than solely relying on signature-based methods. This approach helps identify anomalies in system behavior that could indicate a malware presence. Insights from Market.us suggest that behavior-based detection is becoming increasingly important in modern cybersecurity strategies.
Regular System Audits and Training
Conduct regular system audits to identify vulnerabilities. Additionally, invest in continuous training for HR staff to recognize phishing attempts. Awareness is a crucial factor in preventing initial infection. The HIPAA Journal emphasizes the importance of regular audits and training in preventing data breaches.
Common Pitfalls and Solutions
Ignoring Software Updates
Many organizations fail to update their software regularly, inadvertently leaving vulnerabilities open for exploitation. Always ensure that all systems are up-to-date with the latest security patches. According to a recent study, a significant number of breaches occur due to unpatched vulnerabilities.
Overlooking Employee Training
Employees are often the weakest link in cybersecurity. Regular training sessions can dramatically reduce the risk of phishing attacks. Use real-world simulations to educate staff on identifying and reporting suspicious emails. JD Supra highlights the critical role of employee training in mitigating cybersecurity risks.

Future Trends in Cybersecurity
Increasing Malware Sophistication
As cybersecurity defenses improve, so too do the methods employed by cybercriminals. Expect to see increased use of AI and machine learning by hackers to automate and enhance their attacks. Dark Reading discusses how AI is being leveraged by cybercriminals to develop more sophisticated malware.
Collaboration Between Cybersecurity Firms
To combat evolving threats like Black Santa, increased collaboration between cybersecurity firms will be essential. Sharing threat intelligence can lead to faster identification and neutralization of new malware variants. Security Brief emphasizes the importance of collaboration in the cybersecurity industry.

Conclusion and Recommendations
The emergence of Black Santa serves as a wake-up call for organizations worldwide. By targeting HR departments, hackers have found a new weak link in the security chain. However, with comprehensive security measures, including robust email security, enhanced EDR capabilities, and continuous employee training, companies can significantly mitigate these risks.

FAQ
What is Black Santa malware?
Black Santa is a sophisticated malware designed to target HR departments by disabling EDR tools and allowing deeper system compromise.
How does Black Santa infect systems?
It uses phishing emails containing links to malicious ISO files disguised as resumes to initiate the infection.
What are the key defenses against Black Santa?
Implementing strong email security, enhancing EDR capabilities, and conducting regular employee training are crucial.
Why are HR departments targeted?
HR departments handle sensitive personal data, making them attractive targets for data theft.
What steps can organizations take to prevent infections?
Use email authentication protocols, conduct regular system audits, and ensure all software is up-to-date with security patches.
How can EDR tools be enhanced to detect Black Santa?
Incorporate behavior-based detection methods to identify anomalies in system behavior indicative of malware presence.

Key Takeaways
- BlackSanta targets HR departments through phishing emails.
- It disables EDR tools to allow deeper system compromise.
- ISO files are used to deliver the malware payload.
- Enhanced email security and EDR capabilities are essential defenses.
- Continuous employee training can reduce the risk of phishing attacks.
- Future malware will likely use AI and machine learning for more sophisticated attacks.
- Collaboration between cybersecurity firms is crucial for combating threats.
Related Articles
- Understanding the Threat: Russian Hackers Target Signal and WhatsApp Users [2025]
- The $30 Malware Threat: How Ancient Visual Basic Powers Modern Cybercrime [2025]
- Understanding ClickFix Attacks: How Hackers Target Windows Terminal for Malware [2025]
- Meta's New Scam Protection Features: Safeguarding Users in 2025
- The Evolution of Dark Web Monitoring: From Google's Exit to NordVPN’s Latest Innovations [2025]
- Ericsson Data Breach: Analysis and Strategies [2025]
![Unmasking BlackSanta: The Malware Targeting HR Departments [2025]](https://tryrunable.com/blog/unmasking-blacksanta-the-malware-targeting-hr-departments-20/image-1-1773232462766.jpg)



