The $30 Malware Threat: How Ancient Visual Basic Powers Modern Cybercrime [2025]
Last week, during a routine security audit, a midsize tech company's IT team discovered a breach that left them scrambling. The culprit? A $30 piece of malware written in Visual Basic 6.0. Don't let its low price tag fool you—this tool is opening doors for cybercriminals worldwide, as detailed in a TechRadar report.
TL; DR
- Cheap Malware: A $30 Visual Basic tool is stealing credentials.
- Legacy Code: Visual Basic 6.0 helps it evade modern detection.
- Widespread Impact: Increasing corporate network breaches.
- Best Practices: Implementing layered security can mitigate risks.
- Bottom Line: Stay vigilant and update security measures.
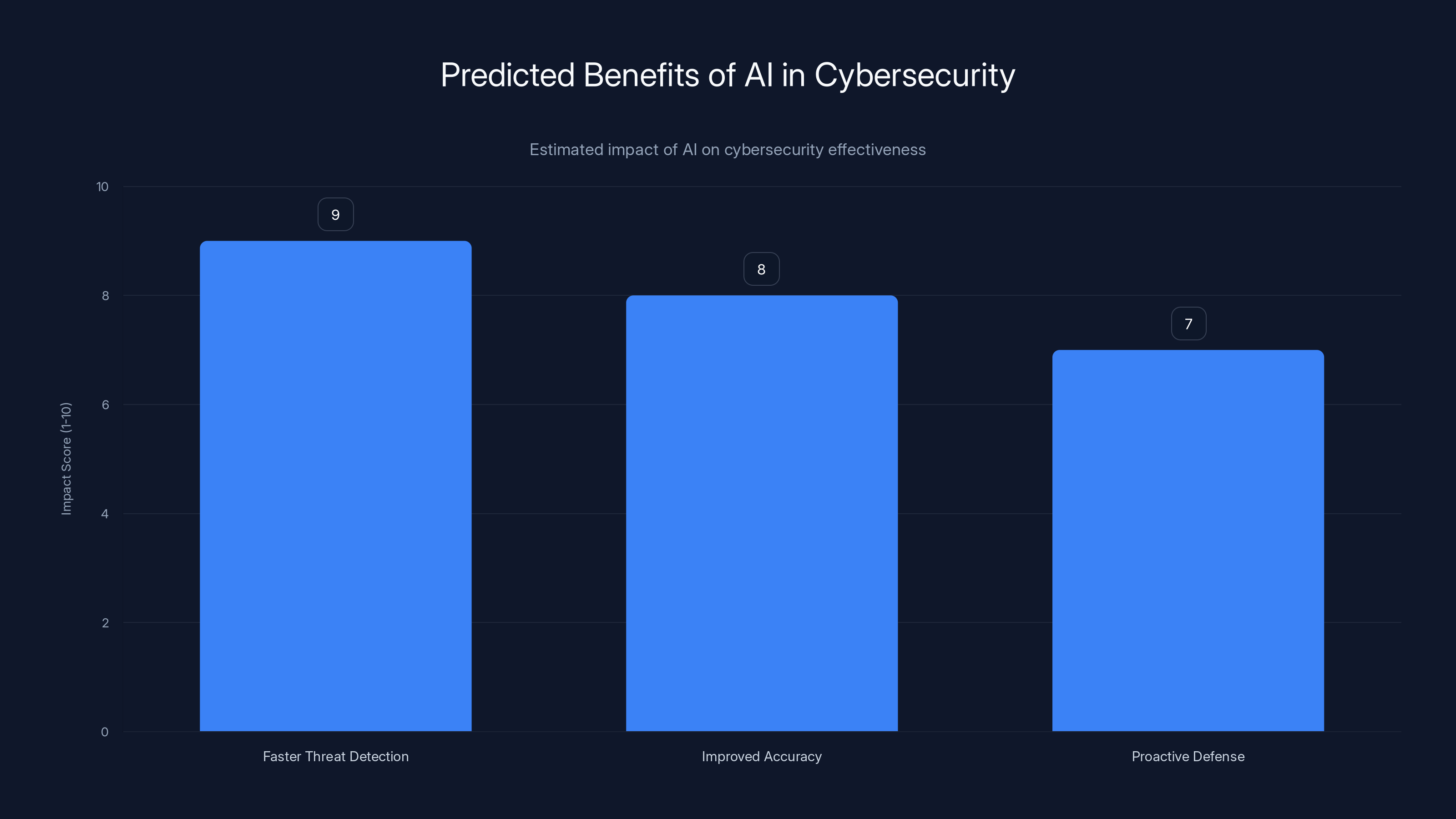
AI in cybersecurity is expected to significantly enhance threat detection speed, accuracy, and proactive defense capabilities. Estimated data.
Introduction
The increasing availability of cheap malware tools on the dark web has opened the floodgates for cybercrime, enabling even those with limited technical skills to execute sophisticated attacks. One such tool, known as Dark Cloud, has been making waves. Sold for just $30, this malware is written in the antiquated Visual Basic 6.0 programming language, yet it poses a significant threat to corporate networks globally, as highlighted by CyberPress.
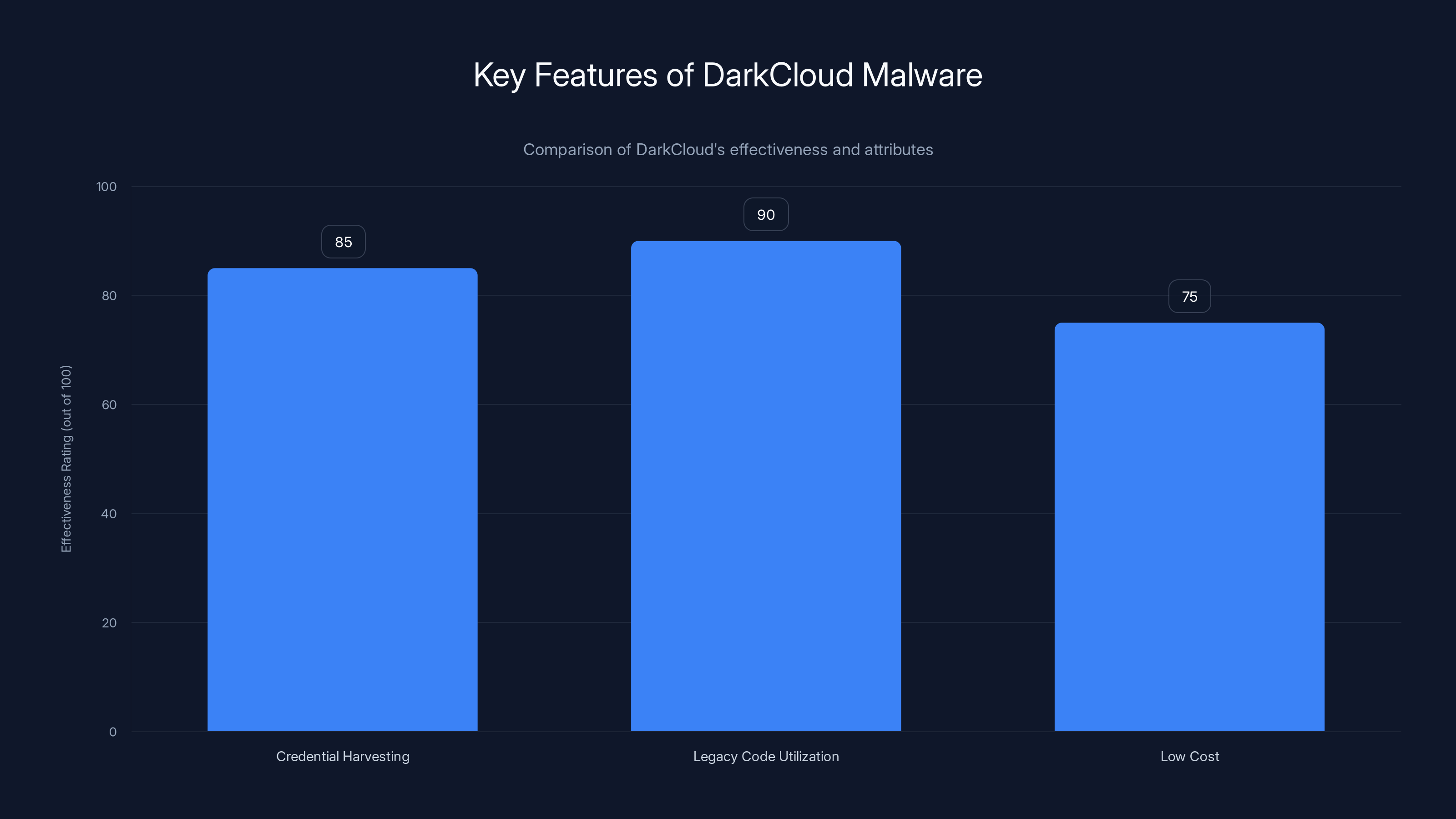
DarkCloud excels in evading detection due to its legacy code and is highly effective in credential harvesting, making it a potent tool despite its low cost. Estimated data.
A Deep Dive into Dark Cloud
What is Dark Cloud?
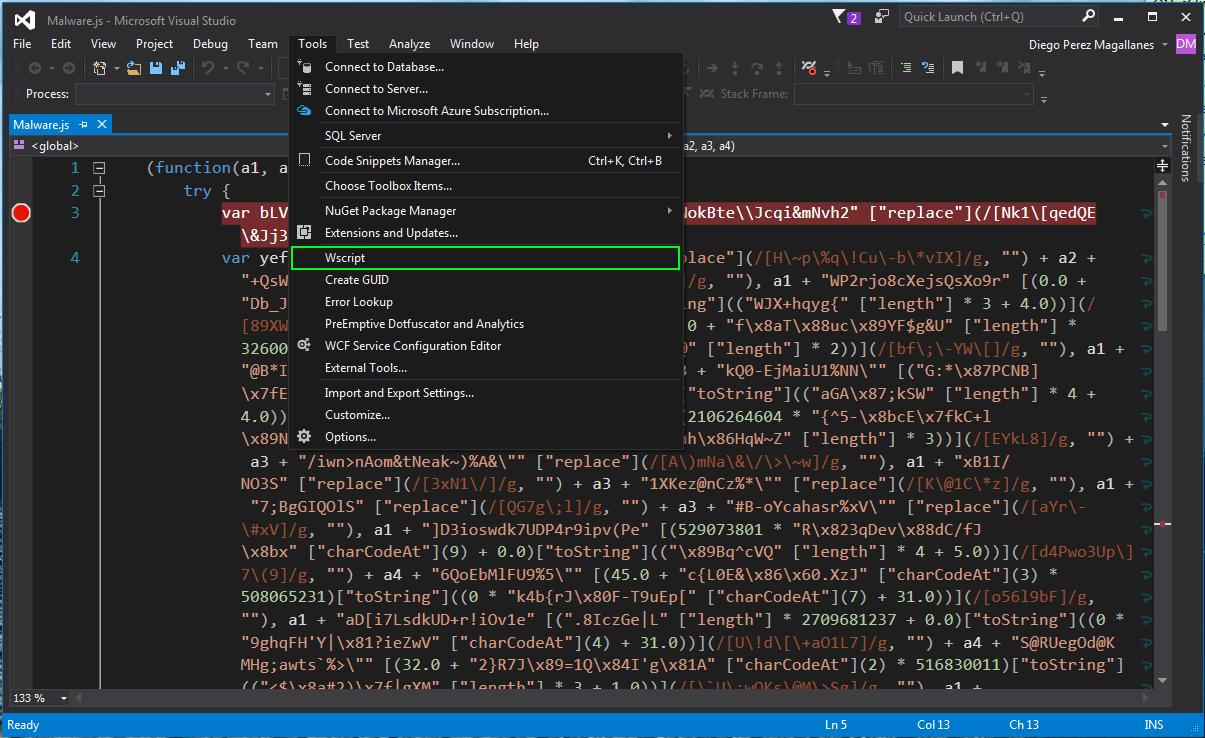
Dark Cloud is a credential-stealing malware that targets web browsers and enterprise software to harvest sensitive information, such as login credentials and financial data. Despite its low cost, this tool is surprisingly effective at bypassing some modern antivirus programs, largely due to its use of legacy code, as reported by TechRadar.
Why Visual Basic 6.0?
Visual Basic 6.0, a language that many consider obsolete, provides unique advantages to cybercriminals. Its simplicity and compatibility with older systems make it an attractive choice for malware developers looking to evade modern detection systems. This choice is akin to using a Trojan horse—an unexpected method that slips past vigilant security defenses, as noted by CyberPress.
The Mechanics of Credential Theft
Once installed, Dark Cloud operates by injecting itself into various processes and monitoring web browsers for login credentials. It also targets enterprise software, seeking out stored credentials and sensitive data. This information is then transmitted back to the attacker's server, where it can be used or sold on the dark web, according to CyberPress.
Key Features of Dark Cloud:
- Credential Harvesting: Targets browsers and enterprise software.
- Legacy Code Utilization: Evades modern detection tools.
- Low Cost: Affordable for even amateur cybercriminals.

The Rise of Low-Cost Cybercrime Tools
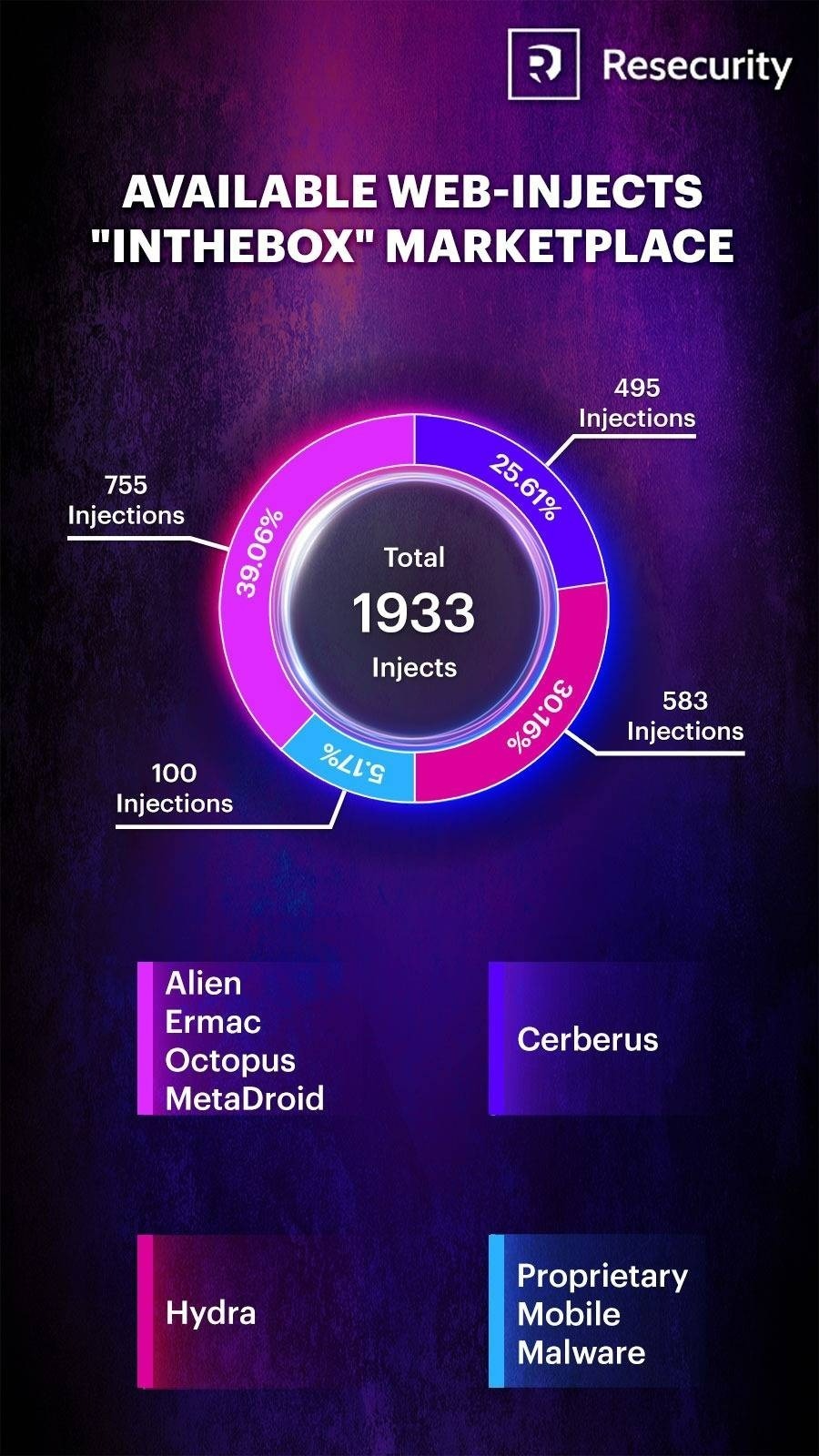
Accessibility on the Dark Web
The proliferation of online marketplaces on the dark web has made it easier than ever for individuals to purchase sophisticated malware tools like Dark Cloud. These platforms offer a range of products, from basic credential stealers to advanced ransomware kits, often complete with customer support and user manuals, as described by CyberPress.
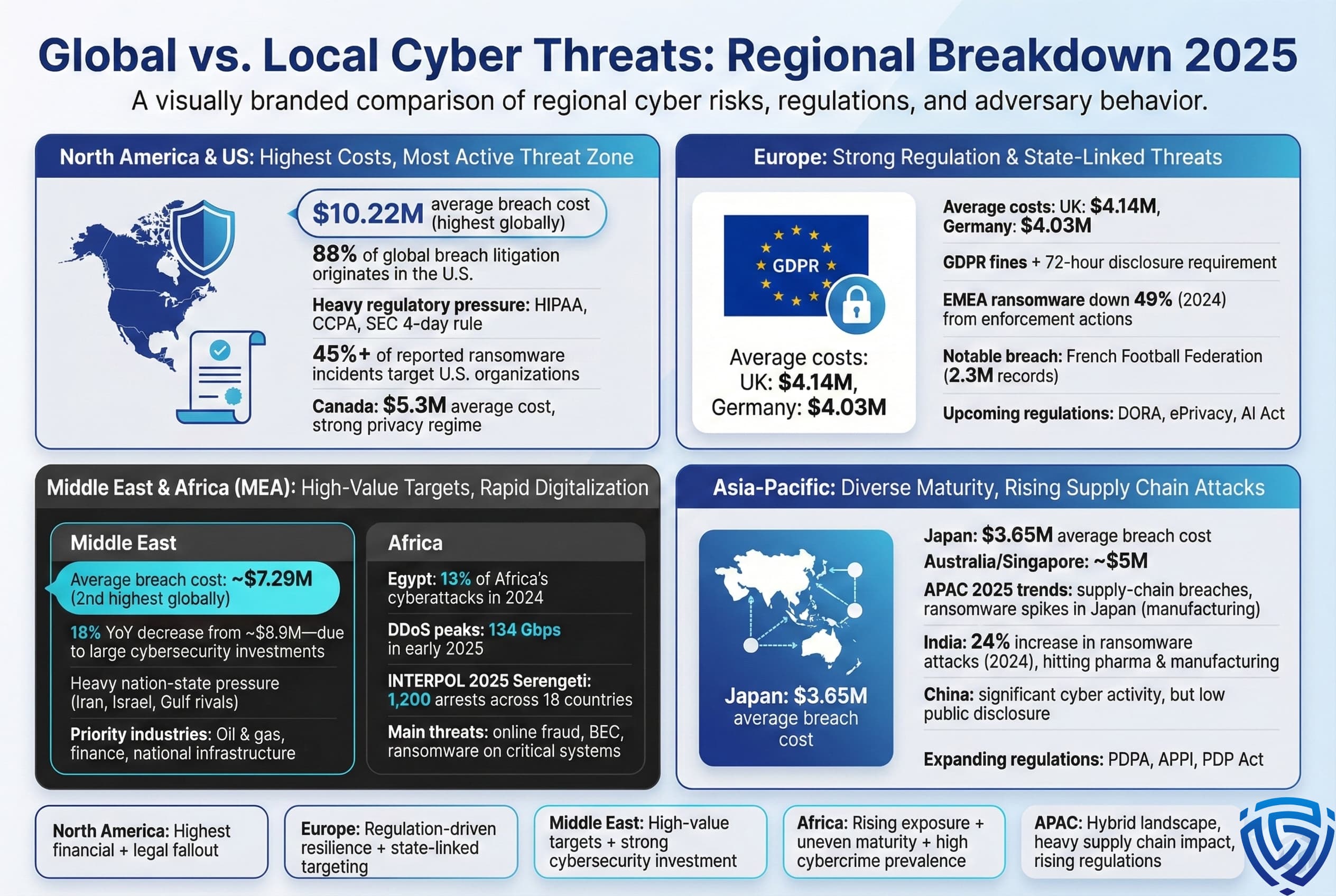
Impact on Corporate Networks
The accessibility of these tools has led to a surge in cyberattacks, particularly against small and medium-sized enterprises (SMEs) that may lack robust cybersecurity measures. Enterprises often become targets due to their valuable data and the potential for significant disruption, as noted by Cybersecurity Ventures.
Notable Impacts:
- Increased Breaches: More frequent network compromises.
- Data Loss: Significant financial and reputational damage.
- Ransom Demands: Threats to leak stolen data if ransoms are unpaid.


Layered security, system updates, and AI integration are among the most effective strategies for robust cybersecurity defenses. Estimated data based on typical industry assessments.
Best Practices for Protecting Against Malware
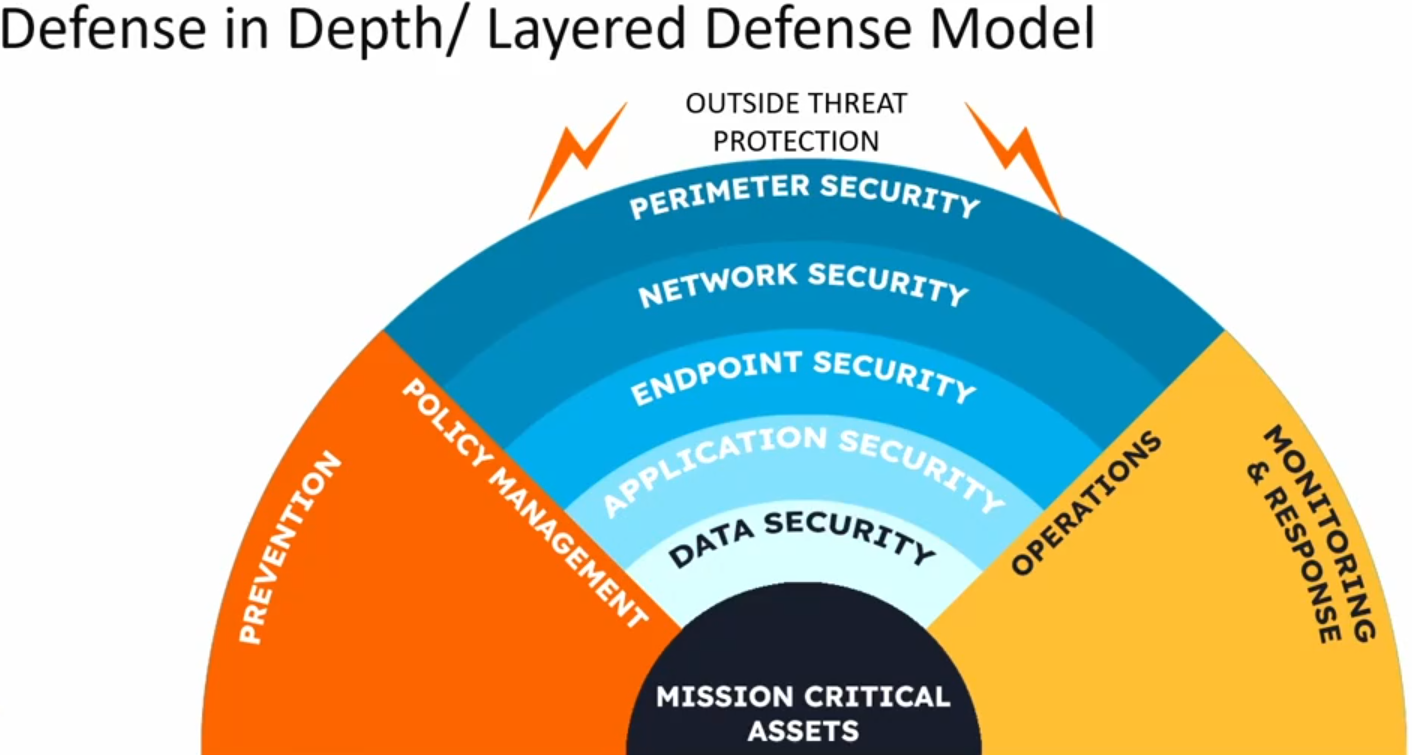
Implementing Layered Security
A layered security approach is essential in defending against malware threats. This involves deploying multiple security measures at various levels of your network infrastructure. According to IBM's insights, a multi-layered approach can significantly reduce the risk of breaches.
Key Components of Layered Security:
- Firewall Protection: Prevents unauthorized access.
- Intrusion Detection Systems (IDS): Monitors network traffic for suspicious activity.
- Endpoint Security: Ensures devices connecting to the network are secure.
Regular Software Updates
Keeping software and systems updated is one of the simplest yet most effective defenses against malware. Regular updates patch known vulnerabilities that could be exploited by malware like Dark Cloud, as emphasized by PCMag.
Educating Employees
Human error remains a significant risk factor in cybersecurity. Regular training on recognizing phishing attempts and safe internet practices can drastically reduce the risk of malware infections.
Training Focus Areas:
- Phishing Awareness: Recognizing suspicious emails and links.
- Password Management: Using strong, unique passwords.
- Safe Browsing Practices: Avoiding untrustworthy websites and downloads.
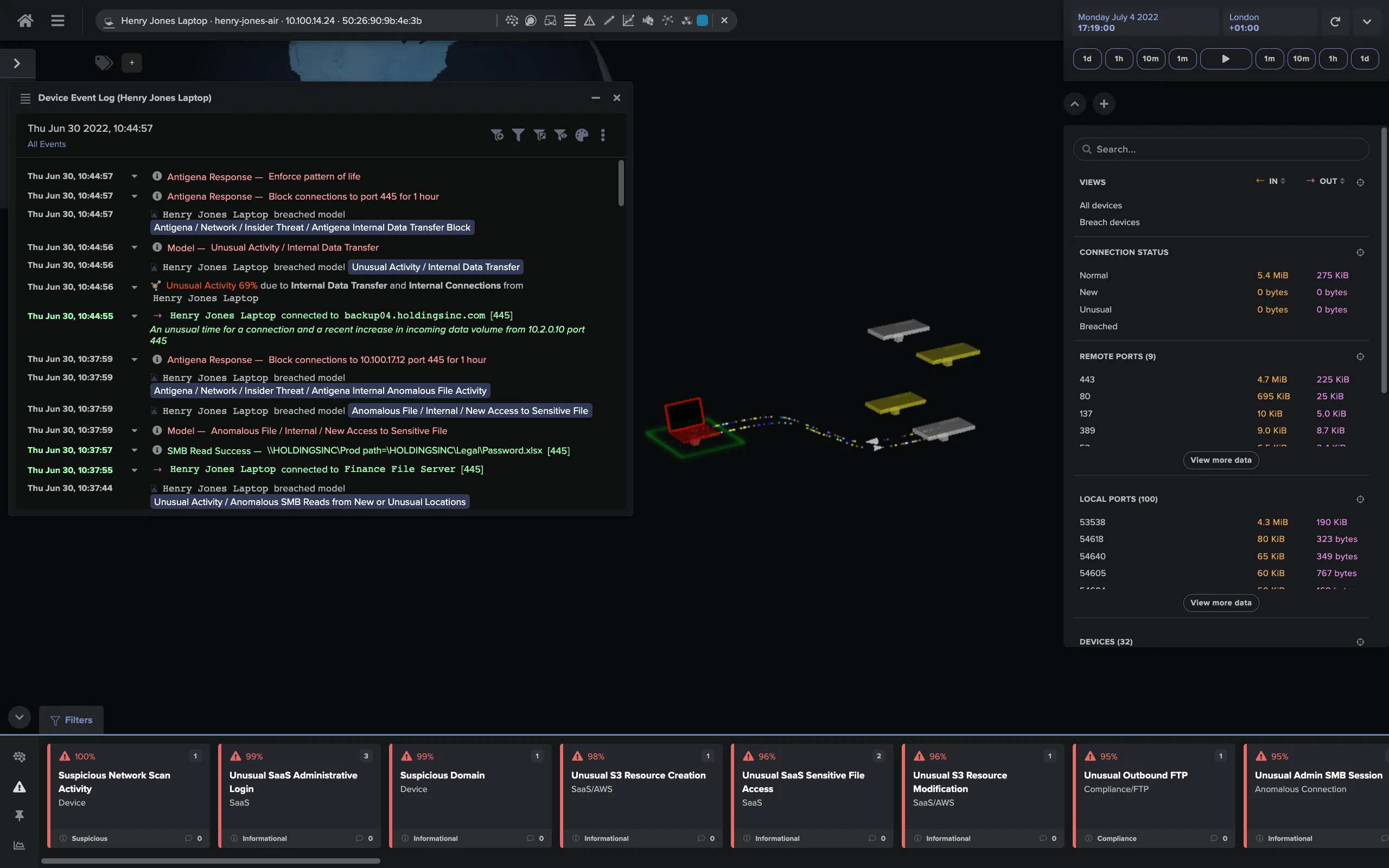
Utilizing Advanced Threat Detection
Modern threat detection tools that use machine learning and AI can help identify unusual network behavior indicative of a malware infection. These tools can often detect threats that traditional antivirus programs might miss, as highlighted by All About Cookies.
Examples of Advanced Threat Detection Tools:
- Crowd Strike: Offers endpoint protection with AI-powered threat detection.
- Palo Alto Networks: Provides advanced threat prevention capabilities.
- Darktrace: Uses AI to detect and respond to cyber threats in real-time.
Common Pitfalls and Solutions
Overreliance on Antivirus Software
While antivirus software is a crucial component of any cybersecurity strategy, relying solely on it can be a mistake. Malware like Dark Cloud can evade traditional antivirus detection, necessitating a more comprehensive security approach, as discussed in CyberPress.
Solution:
- Implement multi-layered security measures that include firewalls, IDS, and endpoint protection.
Neglecting Software and Firmware Updates
Failing to keep software and firmware updated leaves systems vulnerable to known exploits. Dark Cloud, for example, can exploit outdated software to gain access and install itself, as noted by CyberPress.
Solution:
- Establish a regular update schedule and automate updates where possible.
Lack of Incident Response Plan
Many organizations are ill-prepared to respond to a cybersecurity incident. Without a plan in place, response times can lag, and damage can escalate, as highlighted in CyberPress.
Solution:
- Develop and regularly update an incident response plan that includes specific roles and responsibilities.
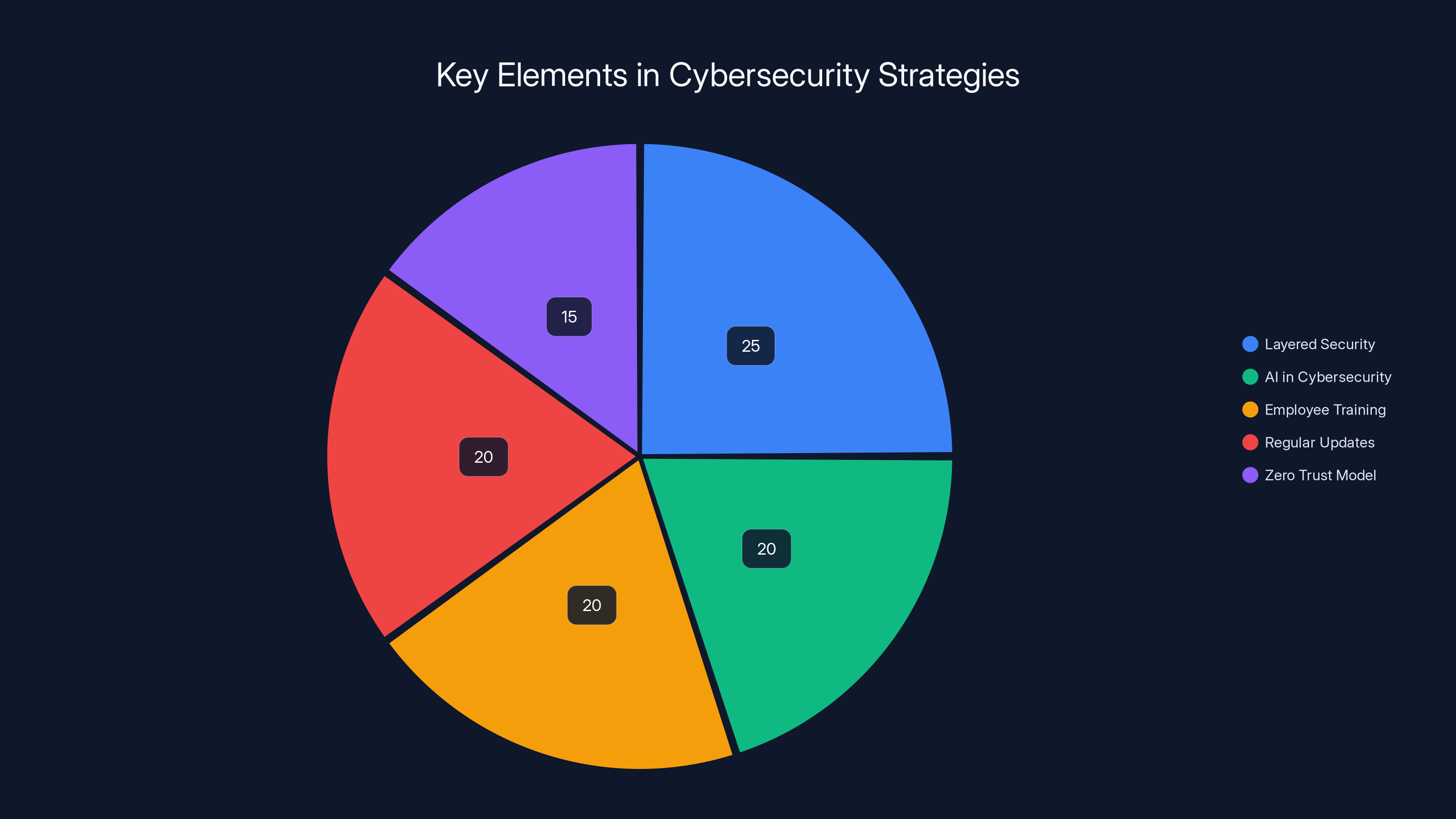
Layered security and AI play crucial roles in modern cybersecurity strategies, with employee training and regular updates also being vital components. (Estimated data)
Future Trends in Cybersecurity
Increased Use of AI and Machine Learning
As cyber threats evolve, so too must the tools we use to combat them. AI and machine learning are becoming increasingly integral to cybersecurity, offering the ability to analyze vast amounts of data and identify threats with greater speed and accuracy than ever before, as noted by IBM.
Predicted Benefits of AI in Cybersecurity:
- Faster Threat Detection: Identify and respond to threats in real-time.
- Improved Accuracy: Reduce false positives and focus on genuine threats.
- Proactive Defense: Predict and mitigate potential threats before they occur.
The Rise of Cyber Insurance
As the financial impact of cyberattacks grows, more organizations are turning to cyber insurance as a safeguard. This trend is expected to continue, with policies becoming more comprehensive and tailored to specific industry needs, as reported by Cybersecurity Ventures.
Key Considerations for Cyber Insurance:
- Coverage Limits: Understanding what is covered and any exclusions.
- Policy Inclusions: Ensuring coverage for ransomware, data breaches, and business interruption.
- Cost: Balancing premium costs with potential financial benefits.
The Importance of Zero Trust Models
The Zero Trust security model, which operates under the assumption that threats could be both external and internal, is gaining traction. By never trusting and always verifying, organizations can better protect sensitive data and systems, as emphasized by CyberPress.
Zero Trust Principles:
- Least Privilege Access: Restrict user access rights to the bare minimum.
- Microsegmentation: Divide the network into smaller segments to limit lateral movement.
- Continuous Monitoring: Constantly monitor and verify user identity and device health.
Conclusion
In an era where $30 can purchase a potent malware tool capable of breaching corporate networks, the importance of robust cybersecurity measures cannot be overstated. The use of legacy technologies like Visual Basic 6.0 highlights the need for vigilance and adaptability in the face of evolving threats, as discussed in TechRadar.
By implementing layered security, keeping systems updated, educating employees, and leveraging advanced threat detection technologies, organizations can better protect themselves from the growing threat of low-cost cybercrime tools. As we look to the future, the integration of AI, the adoption of Zero Trust models, and the strategic use of cyber insurance will be crucial in maintaining robust cybersecurity defenses.

FAQ
What is Visual Basic 6.0?
Visual Basic 6.0 is a programming language developed by Microsoft in the late 1990s. Despite its age, it remains in use for certain legacy systems and applications, which is why it still features in some malware development, as explained by CyberPress.
How does Dark Cloud malware operate?
Dark Cloud operates by injecting itself into processes to monitor web browsers and enterprise software for credentials. It then transmits this data back to the attacker's server, as detailed in CyberPress.
What are the risks of using outdated software?
Outdated software can have unpatched vulnerabilities that are easy targets for malware like Dark Cloud. Regular updates are crucial to protect against such exploits, as noted by CyberPress.
How can companies protect against malware threats?
Companies can protect against malware threats by implementing layered security measures, educating employees about cybersecurity, and keeping their software updated, as recommended by IBM.
What role does AI play in cybersecurity?
AI plays a significant role in modern cybersecurity by offering faster threat detection, improved accuracy, and proactive threat mitigation, as highlighted by IBM.
Why is cyber insurance becoming more popular?
As the financial impact of cyberattacks increases, more organizations are turning to cyber insurance to help mitigate financial losses associated with data breaches and other cyber incidents, as reported by Cybersecurity Ventures.
What is a Zero Trust security model?
A Zero Trust security model assumes that threats can come from both inside and outside the network. It emphasizes never trusting and always verifying users and devices, as explained by CyberPress.
What is the importance of a layered security approach?
Layered security provides multiple defensive measures to protect against cyber threats, ensuring that if one layer fails, others remain in place to mitigate the risk, as noted by IBM.
How can employee training help in cybersecurity?
Training helps employees recognize threats like phishing attempts, use strong passwords, and practice safe browsing, which can significantly reduce the risk of malware infections, as highlighted by CyberPress.
What is the future of cybersecurity?
The future of cybersecurity will likely see increased reliance on AI and machine learning, more comprehensive cyber insurance policies, and the widespread adoption of Zero Trust security models, as predicted by IBM.
Key Takeaways
- Cheap malware tools like DarkCloud are increasing corporate network breaches, as noted by CyberPress.
- Visual Basic 6.0 helps malware evade modern detection systems, as highlighted by TechRadar.
- Layered security and regular updates are essential for protection, as recommended by IBM.
- AI and machine learning are pivotal in modern threat detection, as noted by IBM.
- Zero Trust models are gaining traction for robust network security, as explained by CyberPress.
- Cyber insurance is becoming a crucial safeguard against financial losses, as reported by Cybersecurity Ventures.
Related Articles
- Understanding Phishing Campaigns: How Fake Email Chains Exploit Urgency [2025]
- Trump's Cyber Strategy: A New Era for U.S. Cyber Power [2025]
- Understanding ClickFix Attacks: How Hackers Target Windows Terminal for Malware [2025]
- Inside the FBI's Cybersecurity Breach: Unraveling the Hijacking of Wiretaps and Search Warrants [2025]
- TriZetto Data Breach: Lessons and Future Implications for Healthcare Security [2025]
- OpenAI's Acquisition of Promptfoo: Securing AI Agents for the Future [2025]
![The $30 Malware Threat: How Ancient Visual Basic Powers Modern Cybercrime [2025]](https://tryrunable.com/blog/the-30-malware-threat-how-ancient-visual-basic-powers-modern/image-1-1773095736572.jpg)



