Nord VPN's Salesforce Crisis: The Breach That Wasn't (Or Was It?)
Last week, the internet exploded with headlines about a massive Nord VPN data breach. Hackers claimed they'd compromised the VPN giant's development infrastructure through a Salesforce account. Nord VPN users started panicking. Twitter filled with worried posts. And then Nord VPN responded with a statement that basically said: "Don't worry, we've got this under control."
Except the story's more complicated than that.
This isn't your typical data breach narrative where a company gets hit, suffers damage, and slowly recovers. Instead, we're dealing with competing claims, vague statements, third-party complications, and a lot of questions that still don't have clear answers. Nord VPN denies the breach was serious. Hackers insist they accessed sensitive development tools. Security researchers are picking apart the details. And meanwhile, millions of people are wondering if their VPN provider's infrastructure is actually secure.
Let's walk through exactly what happened, why the claims matter, and what you should actually be concerned about.
TL; DR
- The Claim: Threat actors claimed they accessed Nord VPN development tools via a Salesforce instance
- Nord VPN's Response: The company denied a "data breach" occurred, saying the exposed account was a third-party trial with limited access
- The Problem: Nord VPN's statements have been vague, leading to confusion about what was actually compromised
- Security Implications: Even if access was limited, unauthorized access to development infrastructure raises red flags
- Bottom Line: This incident highlights why VPN security matters, but Nord VPN users don't need to panic—yet

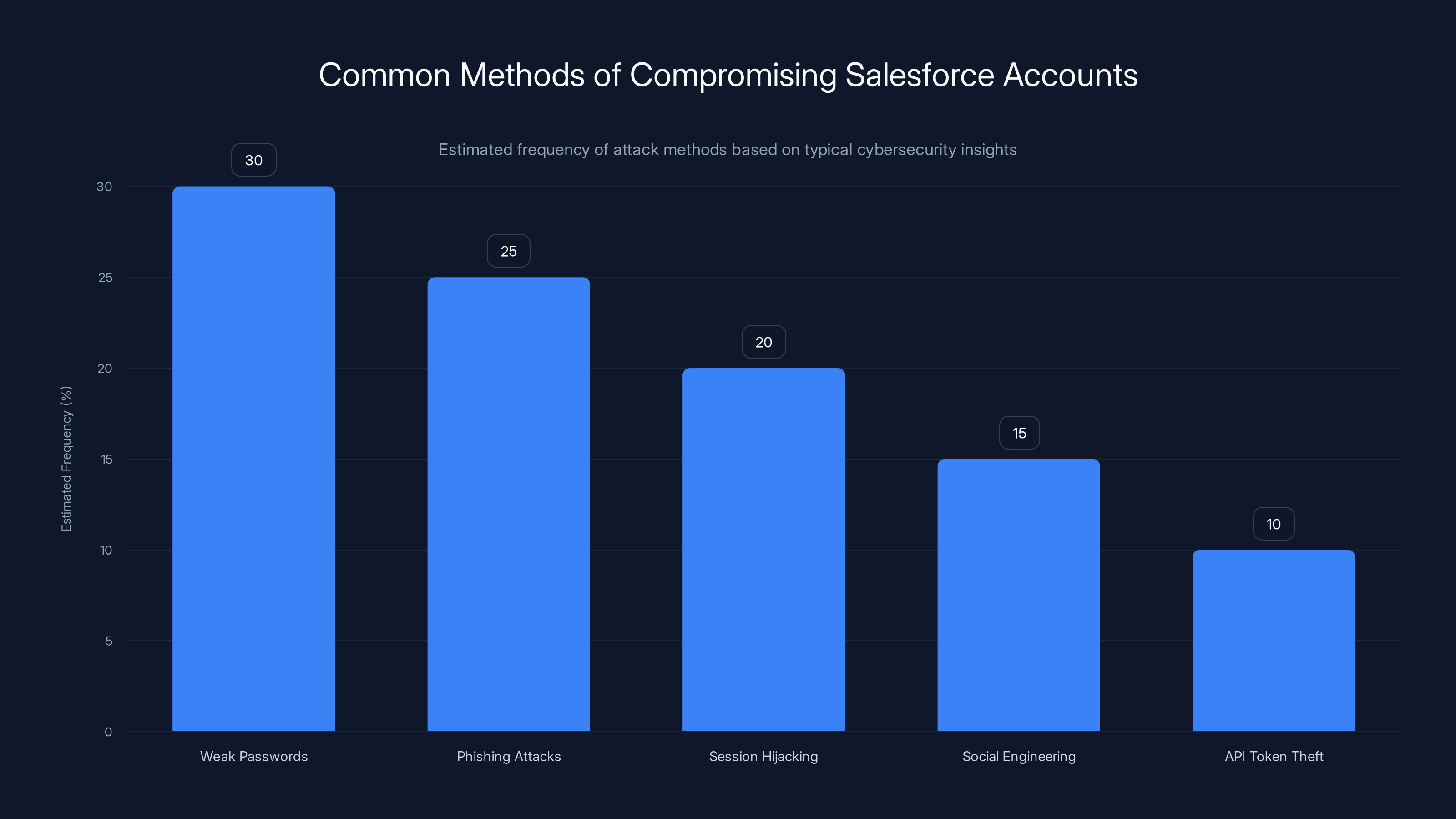
Weak passwords and phishing attacks are the most common methods used by threat actors to compromise Salesforce accounts. Estimated data based on typical cybersecurity trends.
Understanding the Initial Claim: What Hackers Said They Found
The whole thing started when threat actors posted on a dark web forum claiming they'd compromised Nord VPN's infrastructure. Their story was straightforward: they'd gotten into a Salesforce account, extracted credentials, and used those to access development tools. Simple as that.
On the surface, this sounds terrifying. Nord VPN is one of the world's largest VPN providers, trusted by millions of people to protect their internet traffic. If hackers could access the company's development infrastructure, they could theoretically modify software, steal code, or compromise the VPN application itself.
The implications would be massive. Development tools are where companies build, test, and deploy software. If hackers control those systems, they could inject malware into updates, backdoor the application, or gain access to source code worth millions. For a security company, this is basically the nightmare scenario.
But here's where the story gets messy. The threat actors posted screenshots and proof of access. They claimed they had credentials to multiple systems. They even provided technical details that sounded credible to people who know about this stuff.
Then Nord VPN responded. And the response created more questions than it answered.
Nord VPN's Official Response: The "No Data Breach" Claim
When Nord VPN issued its statement, the company was remarkably firm about one thing: there was no data breach. That word—"breach"—kept appearing in their denial. They said their infrastructure was secure. They said user data was safe. They said the situation was completely under control.
But they also said something else that caught security researchers' attention. They acknowledged that a third-party trial account for Salesforce had been compromised.
Let's break this down, because the language matters here.
A third-party trial account suggests this wasn't an account Nord VPN itself created or fully controlled. It was probably a Salesforce trial or demo account set up by a partner or vendor. These accounts often have limited functionality—they're meant to be temporary, time-boxed, and restricted in scope.
Nord VPN's statement essentially was: "Yes, hackers got into a Salesforce account. But it wasn't ours in the traditional sense, and even if they accessed it, the damage is minimal."
The problem? Nord VPN didn't explain what systems were actually accessible from that Salesforce account. They didn't detail what data was exposed. They didn't clarify whether the hackers could pivot to other systems. They basically said: "Trust us, it's fine" without providing the technical details that would let security researchers verify that claim.
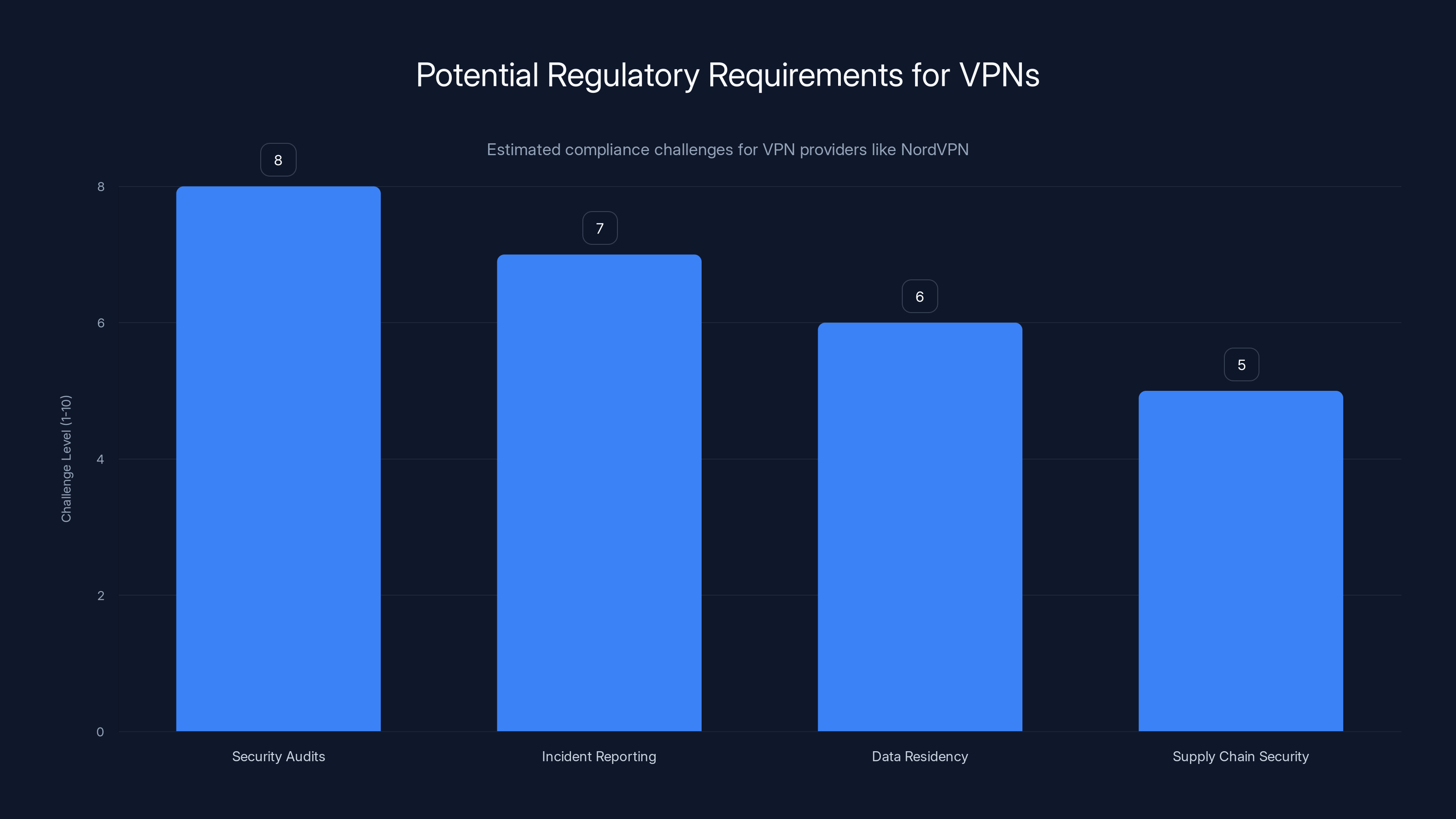
Estimated data shows security audits as the most challenging compliance requirement for VPN providers, followed by incident reporting and data residency rules.
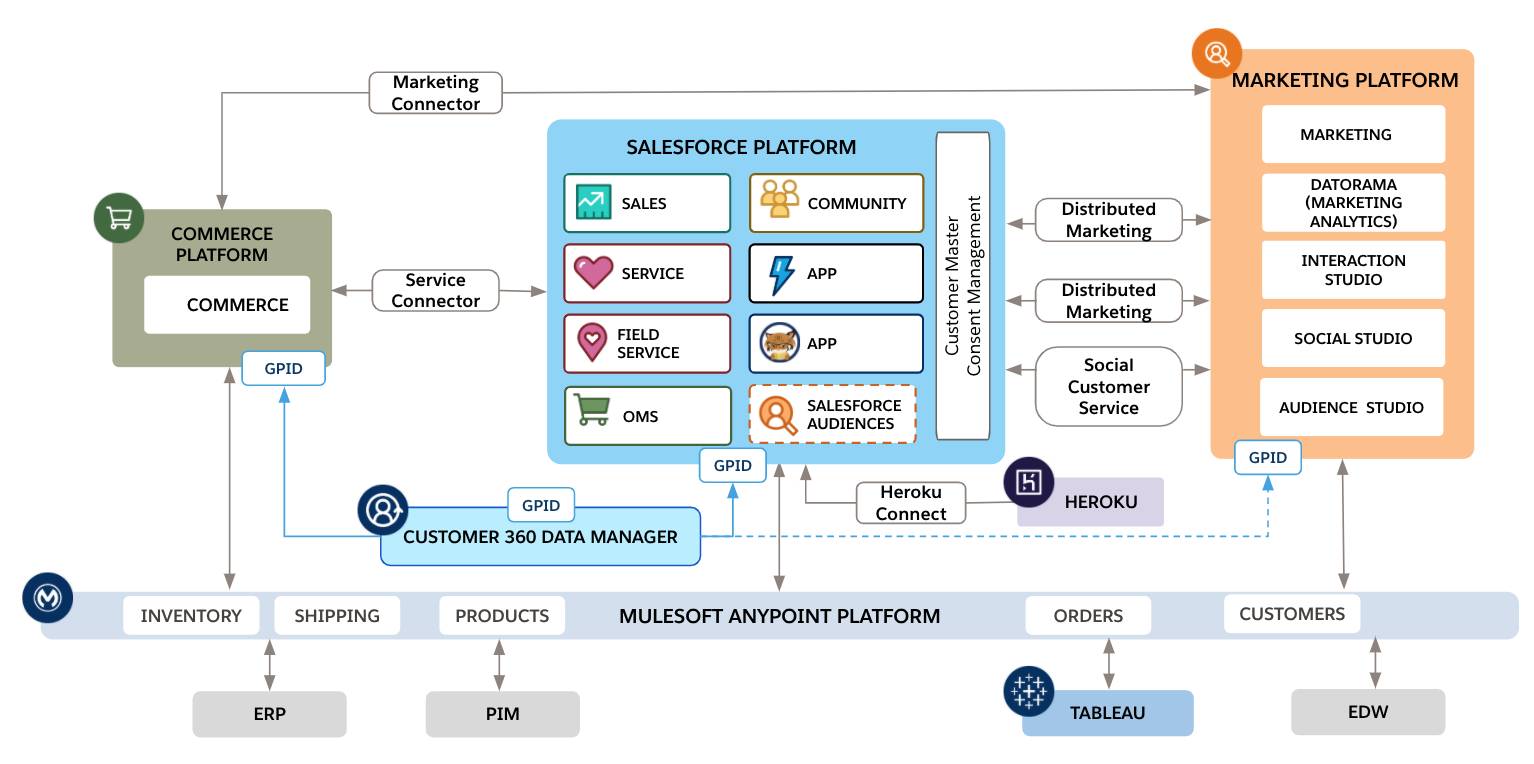
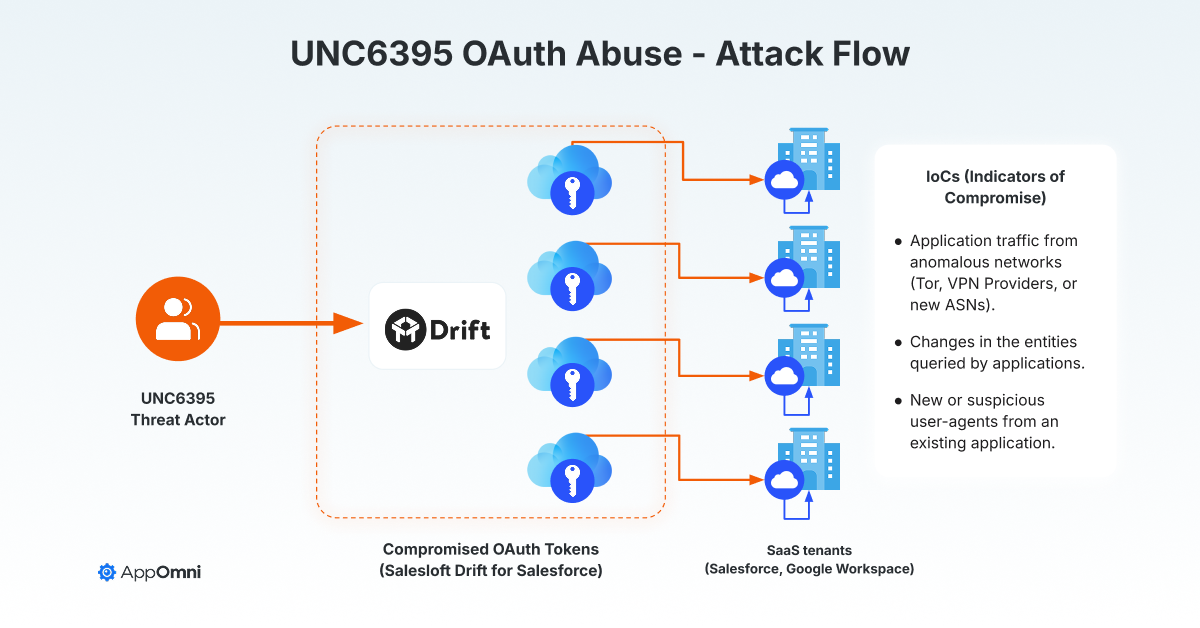
The Salesforce Angle: Why This Matters More Than You Think
Here's something important: Salesforce isn't just a fancy CRM. It's a massive platform that connects to other systems. Companies use Salesforce to manage customer data, partner information, integrations with development tools, API credentials, and more.
If you compromise a Salesforce account, you don't just access Salesforce. You potentially access everything connected to it.
For a tech company like Nord VPN, Salesforce probably connects to:
- Partner and integration management (OAuth tokens, API keys)
- Customer data (email addresses, support tickets, maybe payment information)
- Internal integrations (connections to development platforms, monitoring tools, cloud infrastructure)
- Credential storage (some companies store secrets in Salesforce)
- Admin access (if it's a highly privileged account)
Now, Nord VPN claims this was a "trial account" with "limited access." That could mean the access was restricted. Or it could mean Nord VPN is downplaying the scope of what was available.
The key question nobody's answered definitively: What was actually accessible through that Salesforce account?
Was it just basic contact information? Or was it connected to development systems, API repositories, or infrastructure management tools? If hackers could jump from Salesforce to Git Hub, AWS, or Nord VPN's internal development environment, then "limited access" becomes a misleading statement.
Development Infrastructure Compromise: The Real Risk
If hackers actually accessed Nord VPN's development infrastructure, that's a fundamentally different problem than accessing customer data.
Development infrastructure is the crown jewel of a software company. It's where code is written, compiled, tested, and deployed. If you compromise dev infrastructure, you can:
- Modify source code before it's released
- Inject backdoors into software builds
- Steal proprietary code worth millions
- Create trojanized versions of applications
- Access internal credentials and API keys
- Monitor all developer activity and communications
For a VPN company, this is catastrophic. Users rely on Nord VPN to encrypt and protect their traffic. If the VPN application itself is compromised at the source, every user becomes vulnerable.
Nord VPN claims they found no evidence of code tampering. Fine. But how did they determine this? Did they audit every build since the compromise? Did they check git logs? Did they verify the integrity of released versions?
The company hasn't provided those details, which leaves security researchers and users in an uncomfortable position: we have to take their word for it.
Timeline Confusion: When Did This Actually Happen?
One of the strangest aspects of this incident is how unclear the timeline is.
The hackers claim they compromised the Salesforce account at a specific date. Nord VPN says they detected and remediated the issue. But when exactly? How long had the account been compromised? Did hackers maintain persistence? Did they create backup access routes?
Nord VPN's statement didn't include dates. It didn't explain how long the unauthorized access lasted. It didn't clarify whether they're still monitoring the account or systems for further compromise.
This matters because threat actors often maintain "backdoor" access for months or years before being discovered. They might compromise an account, leave quiet for a while, then access it again when attention dies down.
Without a clear timeline, we can't assess the severity. Did hackers have access for three hours or three months? That's a massive difference in potential impact.
From a cybersecurity perspective, the lack of timeline transparency is almost as concerning as the breach itself. It suggests either:
- Nord VPN discovered this recently and is still investigating
- Nord VPN doesn't have good visibility into when the compromise occurred
- Nord VPN knows the timeline but doesn't want to disclose it
None of those options is reassuring.
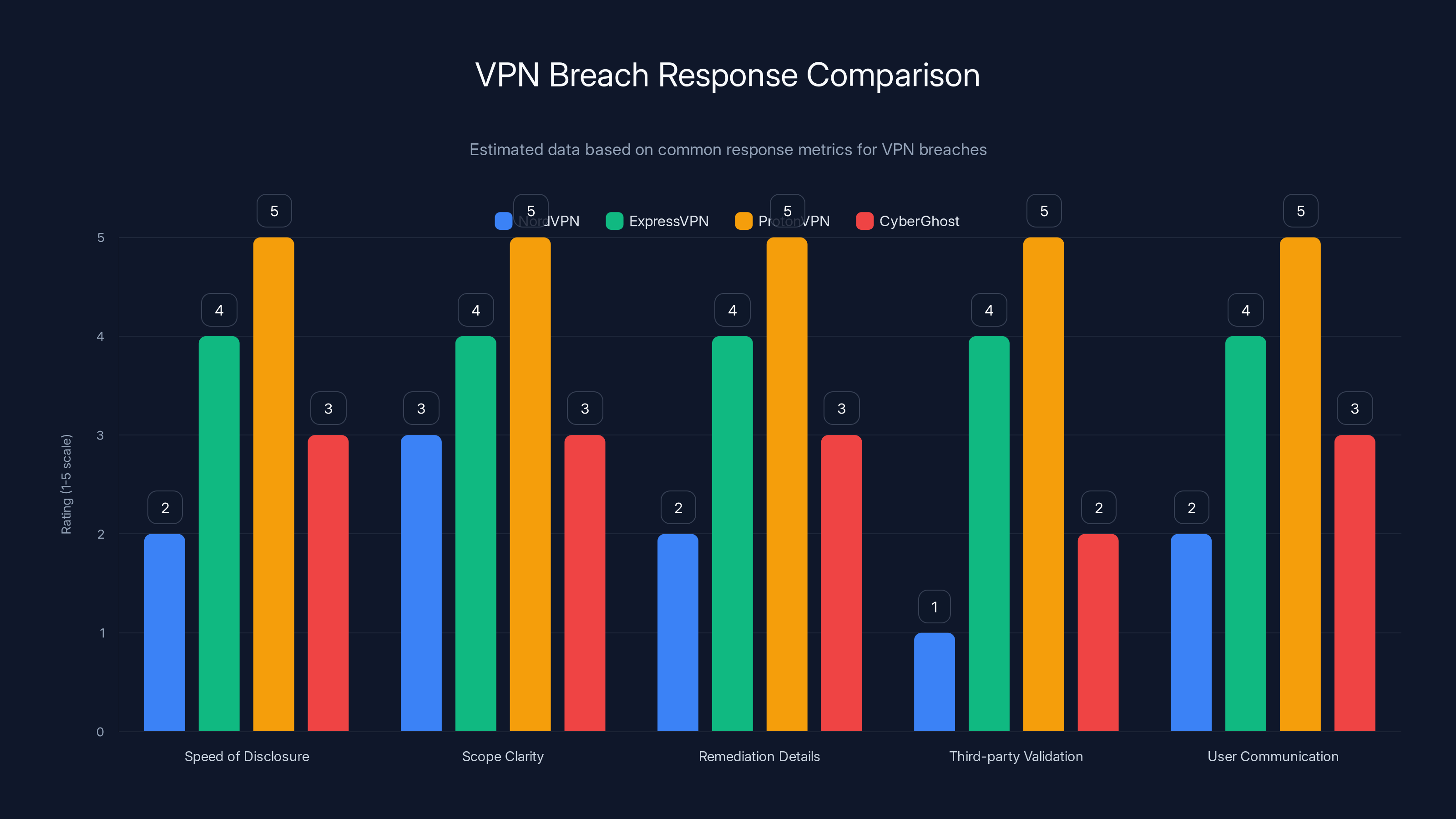
Estimated data shows ProtonVPN leading in breach response metrics, while NordVPN lags behind, especially in third-party validation and user communication.
What Nord VPN Says About Their Security Practices
In response to the incident, Nord VPN emphasized their existing security measures. The company highlighted their zero-knowledge architecture, their no-logs policy, and their track record.
Here's what's important to understand: those things are good. They genuinely do make Nord VPN more secure than many competitors.
But they don't prevent infrastructure compromise.
Zero-knowledge means Nord VPN's infrastructure is designed so that even the company can't see user traffic. If your connection goes through Nord VPN's servers and the data is encrypted end-to-end, then even a Salesforce compromise shouldn't expose your actual internet traffic.
The no-logs policy means Nord VPN doesn't store records of what users do online. So even if hackers accessed the company's servers, they wouldn't find logs of user activity.
But there are still risks:
- If hackers modified the VPN application itself, they could insert code that leaks data
- If they accessed customer databases, they might get email addresses, support tickets, or subscription information
- If they stole source code, they could identify vulnerabilities to exploit later
- If they accessed API infrastructure, they could mess with service availability or inject malicious redirects
Nord VPN's existing security architecture helps mitigate some of these risks, but it doesn't eliminate them entirely.

Third-Party Risk: The Salesforce Connection Problem
This incident highlights a massive security blind spot for many companies: third-party risk.
Nord VPN didn't control Salesforce. Salesforce is managed by a different company. Nord VPN can set up security policies, configure accounts, and restrict permissions, but ultimately they depend on Salesforce's security.
If Salesforce gets compromised, or if Nord VPN misconfigures a Salesforce account, that's a problem. And apparently, that's exactly what happened.
This is the pattern we see over and over: Company A uses Service B. Service B gets compromised. Company A's data is exposed. Then Company A says "It wasn't our fault, it was a third-party" while users lose trust anyway.
For Nord VPN, the exposure was limited (allegedly). But the principle is the same. You can have the best security practices in the world, but if a third-party vendor gets compromised, you're vulnerable.
That's why major companies now have "third-party risk management" programs. They audit vendors, require security certifications, impose strict access controls, and monitor for suspicious activity.
Did Nord VPN have those controls in place for this Salesforce account? They haven't said.
If they didn't, that's a process failure. If they did, then the hackers were sophisticated enough to bypass them. Neither scenario is great.
What Users Should Actually Worry About
Let's cut through the noise and talk about what matters for Nord VPN users.
Your VPN passwords are probably safe. Nord VPN uses industry-standard password hashing. Even if hackers accessed a password database, they'd need significant computing power to crack it.
Your browsing history is probably safe. The whole point of a VPN is that even Nord VPN doesn't see what you're doing. If the infrastructure wasn't modified, your traffic is still encrypted.
But here's what you should monitor:
Email phishing attacks: If hackers got your email address from customer data, expect phishing attempts. Be suspicious of emails claiming to be from Nord VPN asking you to "verify your account" or "confirm your subscription."
Suspicious activity on your account: Check your Nord VPN account settings occasionally. If you see logins from locations you don't recognize, change your password immediately.
Future security updates: Monitor whether Nord VPN releases security updates or patches in the coming months. These might indicate they found vulnerabilities during investigation.
VPN service reliability: If the service becomes unreliable, experiences frequent disconnections, or starts performing oddly, that could indicate active compromise or remediation efforts.
The truth is, unless Nord VPN confirms that source code was actually modified, the impact to users is limited. VPN companies are attractive targets, and breaches at the infrastructure level happen more often than public companies admit. What matters is how they respond and whether they're transparent about it.

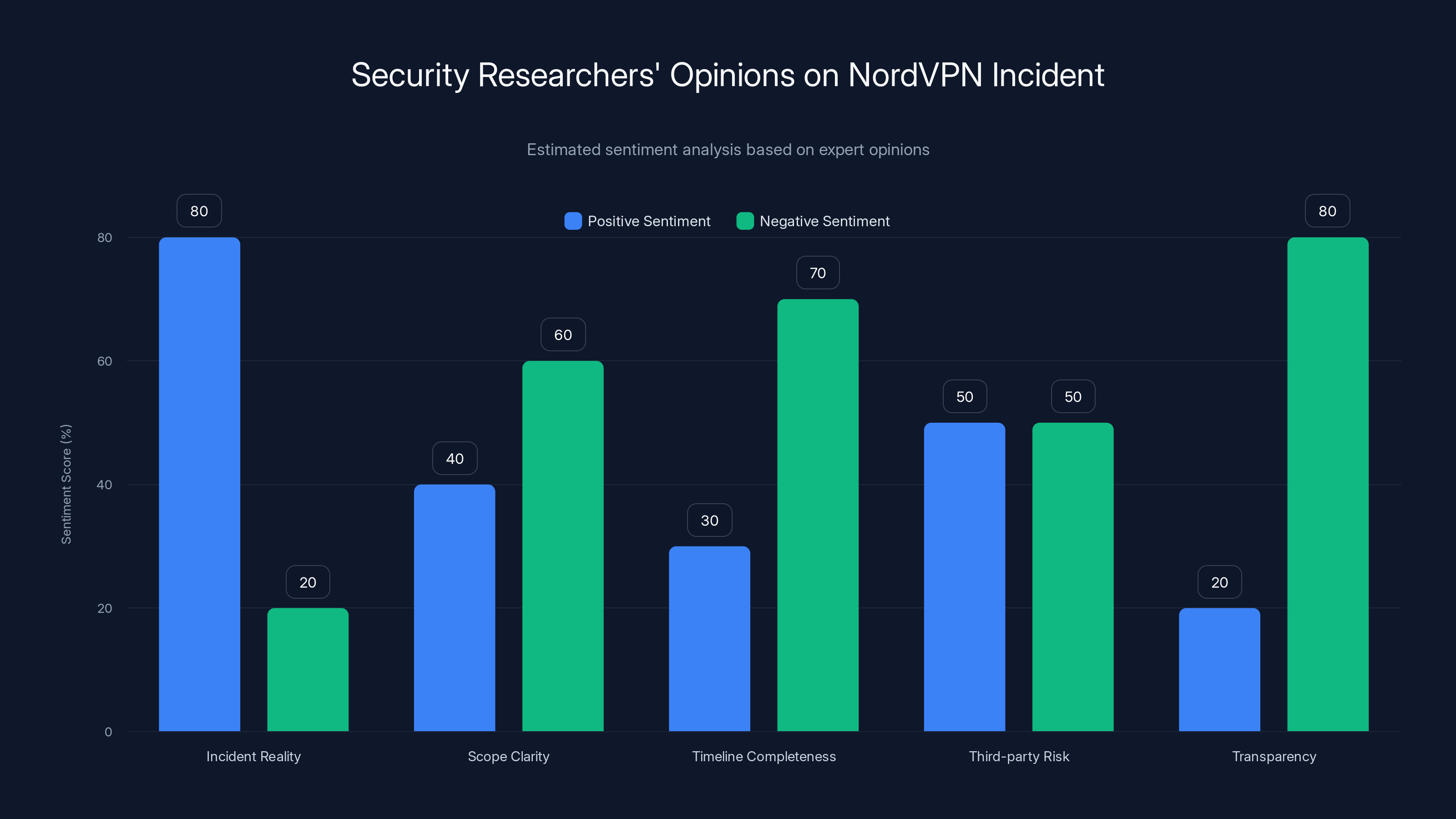
Estimated data shows researchers generally agree on the incident's reality but criticize the lack of transparency and unclear scope.
The Transparency Gap: Why Nord VPN's Response Falls Short
Here's my honest assessment: Nord VPN's response to this incident was defensible but inadequate.
The company confirmed unauthorized access occurred. They said they addressed it. They claimed no customer data was compromised. They emphasized their security architecture.
But they didn't provide:
- Specific dates of the compromise and remediation
- Detailed access scope (what systems were reachable from that Salesforce account)
- Technical indicators of compromise (were there backdoors? modified files? suspicious login attempts?)
- Third-party verification (did an independent security firm audit the incident?)
- Forensic timeline (what happened minute-by-minute during the breach?)
- Communication plan (will they keep users updated? how will they prove no code was modified?)
For a company built on trust and security, this lack of transparency is damaging. Users want to know they're protected. Security researchers want to verify claims. The industry wants clear standards for incident response.
Nord VPN provided none of that.
Now, I understand why. Detailed incident response reports can expose vulnerabilities. Timeline specifics might invite copycat attacks. Technical details could reveal security practices.
But that creates a trust vacuum. Users have to decide: Do I believe Nord VPN's "trust us, it's fine" statement? Or do I switch to a different provider?
For many users, the answer is uncomfortable.
Comparing This to Other VPN Breaches: Is This Unique?
Nord VPN isn't the only VPN company that's dealt with security incidents. Let's look at how this compares.
Express VPN suffered a serious infrastructure compromise in 2020 when a server was accessed and a private TLS key was stolen. The company disclosed it, explained what happened, and implemented fixes. Transparency helped rebuild trust.
Proton VPN has generally maintained a strong security reputation, though like all VPNs, they've had to address various claims and concerns over the years.
Cyber Ghost and other smaller players have experienced security incidents, usually with limited impact.
What separates the well-handled breaches from the problematic ones?
- Speed of disclosure: How quickly did the company inform users?
- Scope clarity: Did they explain exactly what was compromised?
- Remediation details: What specific steps did they take to fix it?
- Third-party validation: Did they have independent security firms audit their response?
- User communication: Did they keep users updated throughout the process?
On most of these metrics, Nord VPN's response has been weak.
That said, some context matters. Nord VPN is owned by Nord Security, a privately held company, not a public corporation. Public companies face SEC disclosure requirements and shareholder scrutiny that drive transparency. Private companies have more flexibility (which sometimes means less transparency).
It's not an excuse, but it's context.
What This Means for VPN Security Going Forward
This incident illustrates a broader problem in cybersecurity: infrastructure compromise is becoming more common, but company responses haven't evolved.
When a hacker compromises development infrastructure, it's not just about what they accessed today. It's about what they can do tomorrow. They might maintain persistence for months, monitoring development, waiting for the right moment to inject code.
For VPN companies, this is especially critical. Users need absolute confidence that the software isn't compromised. One backdoor in the VPN application affects millions of people.
That's why the industry needs:
Reproducible builds: Code is compiled in a reproducible way so anyone can verify the binary matches the source code. This prevents backdoors in compiled software.
Source code transparency: Major VPN providers should open-source critical security components. Mullvad has done this. It makes it harder to hide backdoors.
Regular audits: Independent security firms should audit development infrastructure and processes. Not just after an incident, but regularly.
Public disclosure policies: Clear standards for when and how to disclose security incidents. No more vague "we handled it" statements.
User verification tools: VPN apps should have ways for security researchers to verify that the code running on your device matches the official build.
Nord VPN has made some progress on these fronts (they've open-sourced some components, they publish transparency reports), but they need to go further.
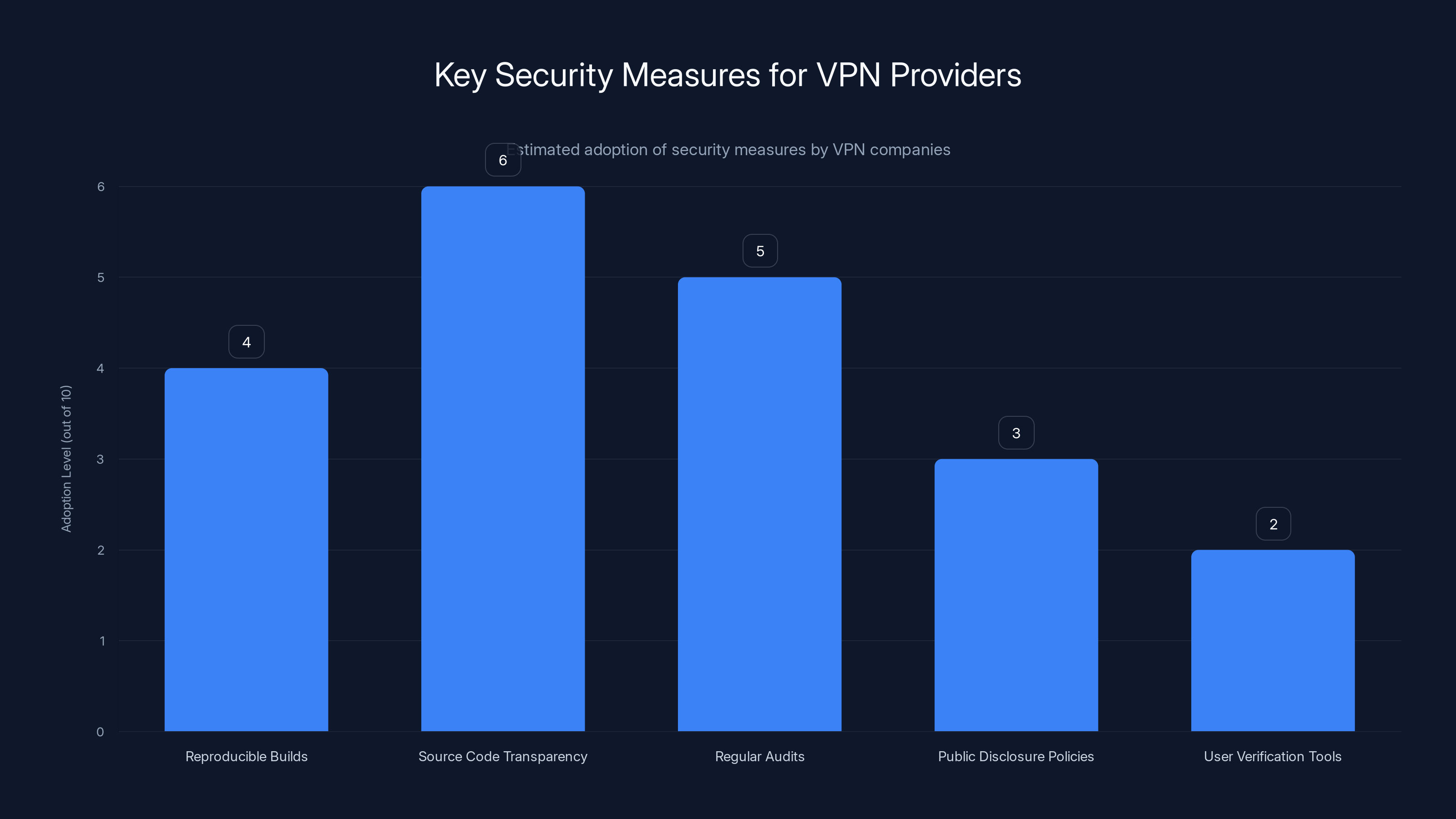
Estimated data shows varying adoption levels of key security measures among VPN providers, with source code transparency being relatively more adopted. Estimated data.
The Hacker Perspective: Why Salesforce Was the Target
Let's think about this from the attacker's viewpoint. Why would they target Salesforce?
Salesforce is a high-value target because it's a central hub. For a tech company, Salesforce connects to:
- Customer relationship management (names, emails, deal information)
- Partner management (third-party integrations, credentials)
- Finance systems (through integrations)
- Development tool integrations (Git Hub, Jenkins, Jira)
- API management (OAuth tokens, API keys)
If you're trying to get into a company's infrastructure, Salesforce is a great entry point. One compromised credential can lead to access across multiple systems.
For the attackers, the goal was probably:
- Access Salesforce
- Extract credentials or API tokens
- Use those to access development systems
- Either steal code or inject backdoors
- Maintain persistence for long-term access
The fact that they targeted Salesforce specifically (not email, not a web server, not an API) suggests they were sophisticated. They knew Salesforce would be connected to other systems.
This tells us something important: the attackers weren't script kiddies running automated scans. They researched Nord VPN's infrastructure and made a calculated decision about where to strike.
That makes the incident more serious than a random breach.

How Salesforce Accounts Get Compromised
This is worth examining because it reveals systemic security issues.
Salesforce accounts are typically compromised through:
Weak credentials: Simple passwords that are easy to guess or crack. Most users avoid weak passwords, but "trial" accounts might have generic credentials.
Credential reuse: Using the same password across multiple sites. If a password is leaked from one service, attackers try it on Salesforce.
Phishing: Attackers send emails impersonating Salesforce, asking users to "verify" or "re-authenticate." Users click the link and provide credentials to a fake site.
Social engineering: Attackers call IT support, claiming to be employees, and trick support staff into resetting passwords or creating new accounts.
Session hijacking: Stealing active session tokens so the attacker can access the account without needing the password.
API token theft: Stealing API tokens that are stored insecurely (sometimes in code, config files, or logs).
Nord VPN hasn't revealed which method was used. That's another transparency gap.
If it was weak credentials, it suggests poor password management practices. If it was phishing, it suggests security awareness training gaps. If it was API token theft, it suggests poor secret management.
Each scenario tells a different story about where Nord VPN's security needs improvement.
The Regulatory Angle: Should Nord VPN Face Consequences?
Depending on jurisdiction, Nord VPN might face regulatory scrutiny for this incident.
In Europe, the GDPR requires companies to notify affected individuals of data breaches within 72 hours. Did Nord VPN do this? We don't know, because they haven't disclosed user impact.
In the US, state laws vary, but many require notification if personal data is accessed. Nord VPN claims no personal data was compromised, so notification might not be required. But that claim is unverified.
For cybersecurity regulations specifically, Nord VPN operates in a somewhat gray area. They're not a financial institution (subject to NIST standards) or a healthcare provider (subject to HIPAA). They're a software/service company, which means regulatory requirements are less defined.
That could change. Governments are increasingly regulating critical infrastructure, and VPNs are becoming recognized as important security tools. We might see:
- Mandatory security audits before operating
- Incident reporting requirements to government agencies
- Data residency rules (which Nord VPN might already comply with)
- Supply chain security standards (like NIST SP 800-171)
If Nord VPN wants to operate in Europe and the US long-term, they need to exceed minimum regulatory requirements, not just meet them.
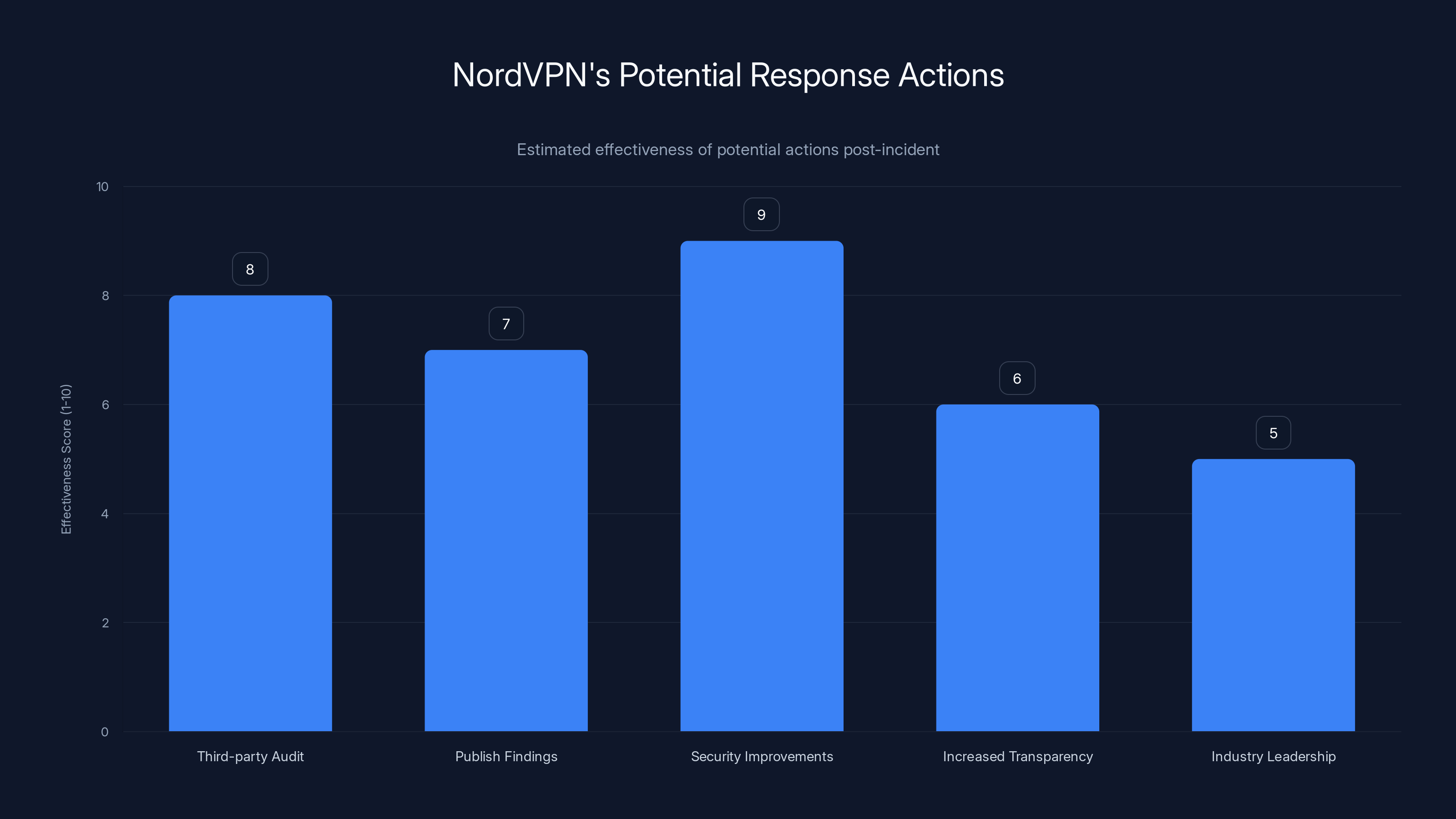
Estimated effectiveness scores suggest that implementing systemic security improvements could be the most impactful action for NordVPN to regain trust.
What Independent Security Researchers Are Saying
When Nord VPN announced the incident, security researchers immediately started analyzing the claims and counter-claims.
The consensus among major security firms and independent researchers:
-
The incident is real: Hackers definitely accessed something. Nord VPN confirmed it, and the technical details provided by the attackers seemed credible.
-
The scope is unclear: Whether it was truly "limited" is debatable. Without forensic reports, it's impossible to verify.
-
The timeline is incomplete: We don't know when the access occurred or how long it lasted. This is critical information.
-
Third-party risk was the weakness: Using a third-party trial account without adequate isolation was a security misconfiguration.
-
Transparency is inadequate: Nord VPN's response lacks the detail needed to assess actual impact.
Some researchers have been more critical, pointing out that this is the second time Nord VPN has suffered a significant infrastructure incident in recent years. That pattern suggests systemic issues, not a one-off mistake.
Others have been more charitable, noting that all major companies face compromise attempts, and Nord VPN's zero-knowledge architecture at least limits user impact.
The safest conclusion: this incident reveals security practices that need improvement, but it doesn't necessarily mean Nord VPN is unsafe as a VPN provider right now.
Recommendations: What Nord VPN Should Do Now
If I were advising Nord VPN (which I'm not), here's what I'd recommend:
Conduct a third-party forensic audit: Hire a respected security firm like Mandiant or Darktrace to investigate the incident independently. Publish the full report (redacted where necessary for security).
Verify code integrity: Use reproducible builds or other methods to prove that no source code was modified. Publish a public statement confirming this.
Implement Salesforce security improvements:
- Require MFA on all Salesforce accounts
- Implement IP whitelisting
- Use dedicated service accounts with minimal permissions
- Monitor Salesforce activity with SIEM tools
- Regular access reviews
Improve incident response transparency: Publish a detailed post-mortem explaining what happened, how it was discovered, what was done to remediate, and what changes were made to prevent recurrence.
Conduct infrastructure audit: Review all third-party integrations for similar vulnerabilities. Check for weak credentials, overpermissioned accounts, and poor isolation.
Enhanced user communication: Even if no user data was compromised, users deserve clear information. Send emails explaining the incident, the investigation, and what users can do to protect themselves.
Public commitment to security: Increase bug bounty rewards, publish security research, open-source more code components, and seek regular third-party audits.
These steps would rebuild trust and demonstrate that Nord VPN takes security seriously.

What Users Should Do Right Now
If you're a Nord VPN user, here are practical steps:
Change your Nord VPN password: Not because it was definitely compromised, but as a precaution. Use a strong, unique password.
Enable two-factor authentication: Most VPN providers support 2FA. Turn it on. This prevents account takeover even if your password is compromised.
Monitor for phishing: Watch your email for suspicious messages claiming to be from Nord VPN. Don't click links in unsolicited emails.
Check account activity: Log into your Nord VPN account and check for suspicious logins or devices. If you see something odd, change your password immediately.
Keep the app updated: Make sure you're running the latest version of the Nord VPN app. Updates might include security fixes related to this incident.
Consider alternatives: If you're uncomfortable with Nord VPN, other options exist. Mullvad, Proton VPN, and Express VPN are reputable alternatives with different security models.
Don't rely on VPN alone: VPNs encrypt your connection, but they're not a complete security solution. Use strong passwords, enable 2FA on important accounts, keep software updated, and practice safe browsing habits.
The VPN industry is competitive. If users lose confidence in Nord VPN, they'll switch. That's the market incentive for the company to get this right.
The Bigger Picture: Infrastructure Security in 2025
This incident is part of a larger trend: attackers are increasingly targeting company infrastructure rather than user data directly.
Why? Because infrastructure is valuable in ways that user data isn't.
If you compromise customer databases, you get names and emails. That's worth something on the dark web, but it's limited value.
If you compromise infrastructure, you get:
- Source code (potentially worth millions)
- Development credentials (access to production systems)
- Customer secrets (API keys, private information)
- Supply chain access (ability to compromise downstream users)
- Long-term persistence (maintaining access for months or years)
For major vendors, infrastructure compromise is the attack of choice. We've seen it with:
- Solar Winds (2020): Supply chain compromise affecting 18,000+ organizations
- Codecov (2021): CI/CD platform compromise affecting thousands of companies
- Circle CI (2023): Similar CI/CD compromise
- 3CX (2023): Software update poisoned with malware
Nord VPN's Salesforce compromise fits this pattern. The attackers wanted access to development infrastructure, not customer email addresses.
As companies and governments recognize this threat, we'll likely see:
- Stricter supply chain security requirements
- Increased investment in infrastructure hardening
- More frequent security audits and certifications
- Better isolation of development environments
- Enhanced monitoring and detection capabilities
Companies that don't upgrade their infrastructure security practices will become increasingly attractive targets.

FAQs About This Incident
People have lots of questions about what happened. Let me address the most common ones.
What exactly did hackers access in Nord VPN's Salesforce account?
Nord VPN hasn't disclosed this clearly. They claimed it was a "third-party trial account" with limited access, but they haven't specified what systems or data were reachable from that account. This is one of the biggest transparency gaps. A comprehensive answer would detail which systems were connected to Salesforce, what data was stored there, and what the hackers actually accessed.
Does this mean my VPN traffic was compromised?
Most likely no, but it's not guaranteed. Nord VPN's zero-knowledge architecture means the company doesn't see or store user traffic. If hackers didn't modify the VPN application itself, your traffic should still be encrypted. However, if source code was modified and a malicious version was released, that would be a different story. Nord VPN claims no code was modified, but this claim hasn't been independently verified, which is why trust is an issue.
Should I switch to a different VPN provider?
Not necessarily, but it depends on your risk tolerance. Nord VPN is still a functional, reputable VPN provider. This incident doesn't prove that you're currently unsafe using their service. However, if transparency and incident response are important to you, other providers with stronger track records might be preferable. Mullvad is open-source and very transparent. Proton VPN is Switzerland-based and has good privacy practices. The choice depends on your priorities.
Is my password at risk?
Your Nord VPN password is probably safe. Nord VPN uses industry-standard password hashing, meaning even if the password database was accessed, passwords are stored in a form that's difficult to crack. However, if you reuse your password across multiple sites, you should change it everywhere as a precaution. If you used a unique password for Nord VPN, the risk is lower.
What should I do if I'm worried about this?
Start with basics: change your Nord VPN password if you haven't already, enable two-factor authentication if available, and monitor your account for suspicious activity. Check your email for phishing attempts. Keep the Nord VPN app updated. Beyond that, if the incident really concerns you, consider switching to a provider with a stronger transparency record. But understand that no VPN provider is immune to attacks, and the question is really about how they respond, not whether they get attacked.
Will Nord VPN face legal consequences for this?
That depends on whether they violated regulations. If they delayed notifying affected users beyond the 72-hour GDPR requirement, they could face fines. If they failed to implement required security controls, they could face liability. However, Nord VPN claims minimal user impact, which might limit regulatory exposure. The bigger consequence might be loss of user trust, which affects their business.
How does this compare to other VPN breaches?
Nord VPN has had security incidents before (most notably in 2019 when a server was compromised). This Salesforce incident is similar in pattern: infrastructure access, questions about scope, delayed disclosure. The difference this time is that user impact seems genuinely limited. However, the pattern of incidents is concerning and suggests systemic security practices that need improvement beyond just VPN software itself.
Should I trust Nord VPN's claim that no data was compromised?
With caution. Nord VPN has incentive to downplay the incident. However, their technical architecture (zero-knowledge) does genuinely limit user data exposure compared to traditional VPNs. The issue is that we can't independently verify their claims. An independent third-party audit would be more convincing than Nord VPN's own statement. Until that happens, skepticism is reasonable.
What does this mean for VPN security in general?
It shows that VPN providers are high-value targets for sophisticated attackers, and even major providers can be compromised at the infrastructure level. This doesn't mean VPNs are useless, but it does mean you should choose providers that are transparent about security, invest in infrastructure hardening, and have good track records of incident response. VPNs encrypt your traffic, which is valuable, but they're not a complete security solution.
Is using a VPN still worth it after this incident?
Yes. VPNs provide real security benefits by encrypting your traffic and hiding your IP address from websites you visit. This incident doesn't change that value. What it does suggest is that you should be selective about which VPN provider you use. Choose one with a good security track record, transparent practices, and strong infrastructure. Nord VPN is still a reasonable choice, but so are alternatives with stronger transparency records.
Conclusion: Learning From the Incident
Here's what we know for certain: hackers accessed a Nord VPN Salesforce account. Nord VPN responded by securing the account and investigating. The company claims no significant data was compromised and no user data was exposed.
Here's what we don't know: exactly what systems were accessible from that Salesforce account, how long hackers had access, whether they modified any code, and what Nord VPN's forensic investigation actually found.
That knowledge gap is the real issue.
In cybersecurity, you can't just tell people "trust us, it's fine." You have to show them. You have to provide evidence. You have to submit to independent verification. You have to be transparent about vulnerabilities so the industry can learn and improve.
Nord VPN didn't do that. And that's what erodes trust.
Now, I don't think this incident means Nord VPN is unsafe or that you should panic if you're a user. Infrastructure compromises happen to every major tech company. What separates good companies from bad ones is how they respond.
The best outcome would be if this incident prompted Nord VPN to:
- Conduct a serious third-party audit
- Publish detailed findings
- Implement systemic security improvements
- Become more transparent in the future
- Lead the industry in security practices
The worst outcome would be if they do the bare minimum and hope everyone forgets about it by next month.
Based on Nord VPN's response so far, it looks like they're somewhere in the middle. They've acknowledged the issue, they've claimed to fix it, but they haven't demonstrated the kind of transparency that would truly rebuild confidence.
For users, the lesson is simple: don't blindly trust any company's security claims. Verify, question, and keep options open. For Nord VPN, the lesson is equally clear: transparency builds trust, and secrecy destroys it. The company that leads the industry in honest, detailed incident reporting will win the most loyal users.
This incident is a test of whether Nord VPN understands that.

FAQ
What is a zero-knowledge VPN architecture?
Zero-knowledge means the VPN provider is designed so that even the company itself cannot see, access, or store information about what users do online. Your internet traffic is encrypted from the moment it leaves your device until it reaches the final destination. The VPN servers route your traffic but don't decrypt it. This design means that even if Nord VPN's infrastructure is compromised, hackers can't access your browsing data because the company never possessed it in the first place.
How do threat actors typically compromise Salesforce accounts?
Threat actors use several methods including weak or reused passwords, phishing attacks that trick employees into providing credentials, session hijacking to steal active session tokens, social engineering to manipulate IT support staff, and API token theft from insecurely stored secrets. In Nord VPN's case, the exact method hasn't been disclosed, which itself raises questions about investigation transparency and root cause analysis that could prevent future incidents.
What are the implications if Nord VPN's source code was modified?
If hackers had access to development systems and modified Nord VPN source code before it was compiled into the application, they could inject malware, backdoors, or data-stealing code that would run on millions of user devices. This is far more serious than accessing customer data because it would put every user's device and data at risk. Nord VPN claims they found no evidence of code modification, but independent verification through reproducible builds or third-party audits would be more convincing.
Why is third-party risk management important for VPN companies?
VPN companies depend on numerous third-party services like Salesforce, cloud providers, payment processors, and communication platforms. If any third-party is compromised or misconfigured, it can expose the VPN company and its users. Proper third-party risk management includes security assessments before engagement, strict access controls, ongoing monitoring, and incident response plans. This incident shows that even well-known companies sometimes fail at basic third-party security hygiene.
How should users verify that their VPN provider is actually secure?
Look for providers that open-source their code (so anyone can audit it), publish regular third-party security audits, maintain transparent privacy policies and incident disclosure procedures, offer reproducible builds, maintain active bug bounty programs, and have clear communication about security practices. Mullvad excels in transparency. Proton VPN provides regular audit reports. Trust should be based on verifiable practices, not marketing claims.
What's the difference between a data breach and an infrastructure compromise?
A data breach typically means customer data (names, emails, passwords, payment information) was accessed or stolen. An infrastructure compromise means hackers gained access to internal systems like development tools, production servers, or administrative systems. Infrastructure compromises can be more serious because they enable attackers to modify software, steal intellectual property, and maintain long-term access. This Nord VPN incident was primarily an infrastructure compromise at the Salesforce level, not a direct customer data breach, though customer data might have been accessible depending on what Salesforce was connected to.
Why is transparency important in security incident response?
When companies suffer security incidents, transparency helps stakeholders understand the scope, impact, and remediation efforts. It builds trust by demonstrating that the company takes security seriously and has nothing to hide. It allows security researchers to identify systemic issues and recommend improvements. It helps other companies avoid similar mistakes. And it gives users information they need to make informed decisions about whether to continue using the service. Nord VPN's vague response undermines trust more than an honest explanation would, even if the honest explanation were less flattering.
What regulatory requirements apply to VPN companies?
VPN companies fall under different regulations depending on jurisdiction. In Europe, the GDPR requires notification of data breaches within 72 hours and implementation of security by design. The upcoming NIS2 Directive will impose stricter security requirements for critical infrastructure. In the US, state laws vary, but many require notification if personal information is accessed. Companies operating internationally need to comply with the strictest jurisdiction they operate in, which typically means GDPR compliance for any European customers.
Should users switch from Nord VPN due to this incident?
Not necessarily, unless transparency and security practices are your top priorities. Nord VPN is still a functional VPN provider, and this incident doesn't prove users are currently unsafe. However, if you're concerned about how the company handles security incidents, you might consider alternatives. Mullvad is more transparent and open-source. Express VPN publishes regular audit reports. Proton VPN emphasizes privacy. Each has different strengths depending on what matters most to you.
Key Takeaways
- NordVPN acknowledged unauthorized access to a Salesforce trial account, but claims it was a limited, third-party incident with minimal user impact
- The company's vague response lacks specific details about what systems were accessible, how long access lasted, and what forensic investigation found
- Even if customer data wasn't compromised, infrastructure access to development tools poses serious risk if source code was modified
- This incident highlights systemic third-party risk management gaps common across tech companies using integrated SaaS platforms
- Transparency and independent verification are more important than company reassurance when assessing security incident severity and provider trustworthiness
Related Articles
- Post-Quantum Cryptography: Securing TLS for the Quantum Era [2025]
- ESA Cyberattack: What You Need to Know About the 200GB Breach [2025]
- Federal Cybersecurity Crisis: Why Government Digital Defense Is Collapsing [2025]
- GPS Jamming: The Vulnerability Threatening Modern Infrastructure [2025]
- Holiday Email Scams 2025: How to Spot and Stop Them [Updated]
- WebRAT Malware on GitHub: The Hidden Threat in Fake PoC Exploits [2025]
![NordVPN Salesforce Breach Claim: What Really Happened [2025]](https://tryrunable.com/blog/nordvpn-salesforce-breach-claim-what-really-happened-2025/image-1-1767625614954.jpg)



