British Businesses Struggling to Recover from Cyberattacks: Strategies for Resilience [2025]
Introduction
British businesses, from retail giants to small enterprises, are grappling with the aftermath of persistent cyberattacks. Despite adopting advanced cybersecurity measures, many are still vulnerable, with recovery proving elusive. This article explores why these challenges persist and offers actionable strategies to bolster resilience.

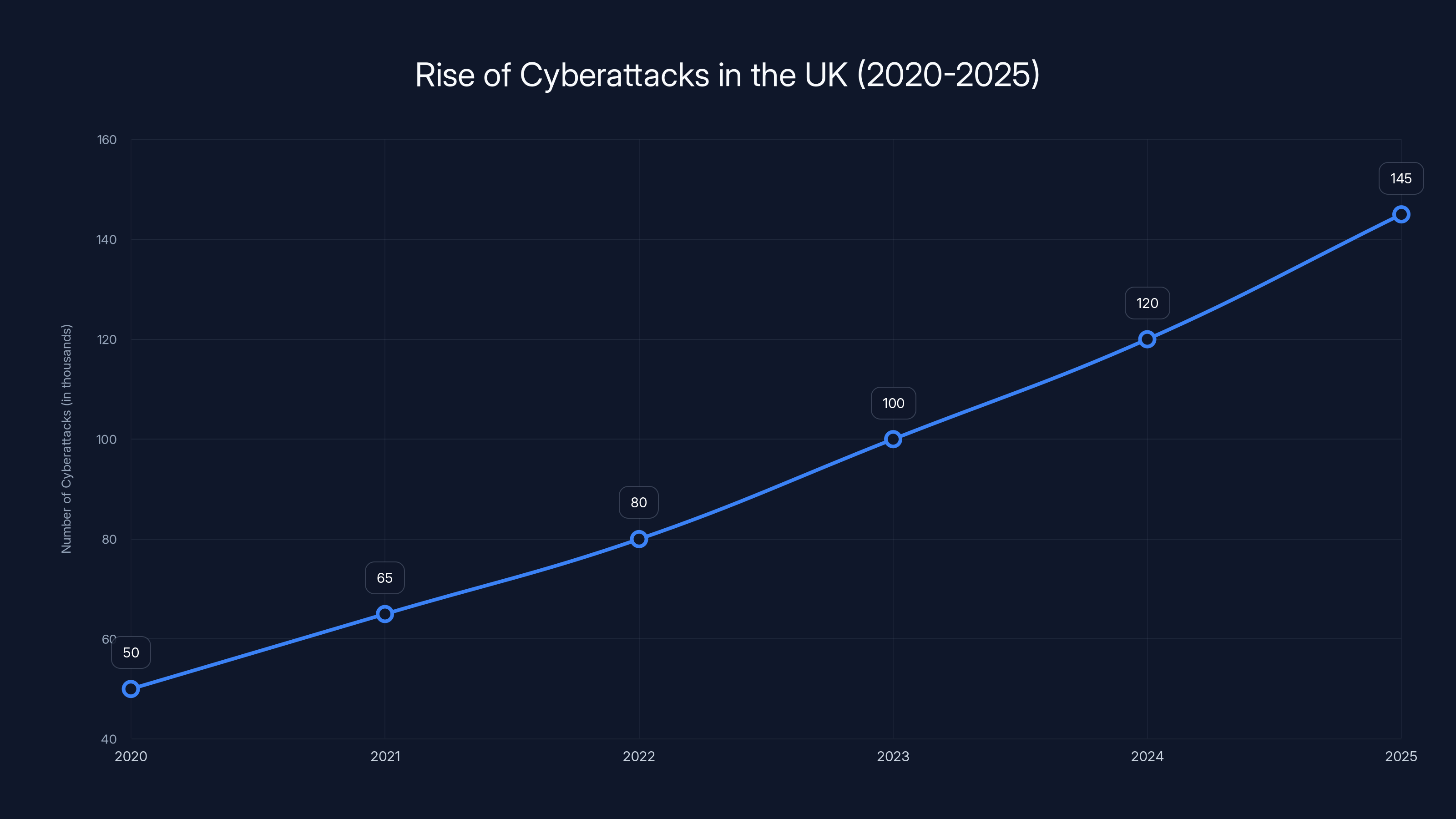
The chart illustrates a projected increase in cyberattacks in the UK, with numbers rising from 50,000 in 2020 to an estimated 145,000 by 2025. Estimated data.
TL; DR
- Cyberattacks on the rise: British businesses face increasing threats, with 71% paying ransoms.
- Resilience is key: Recovery requires a robust, multi-layered cybersecurity strategy.
- Focus on training: Employee awareness is critical in preventing breaches.
- Invest in technology: Leverage AI and automation for proactive defense.
- Stay informed: Continuous monitoring and threat intelligence are essential.
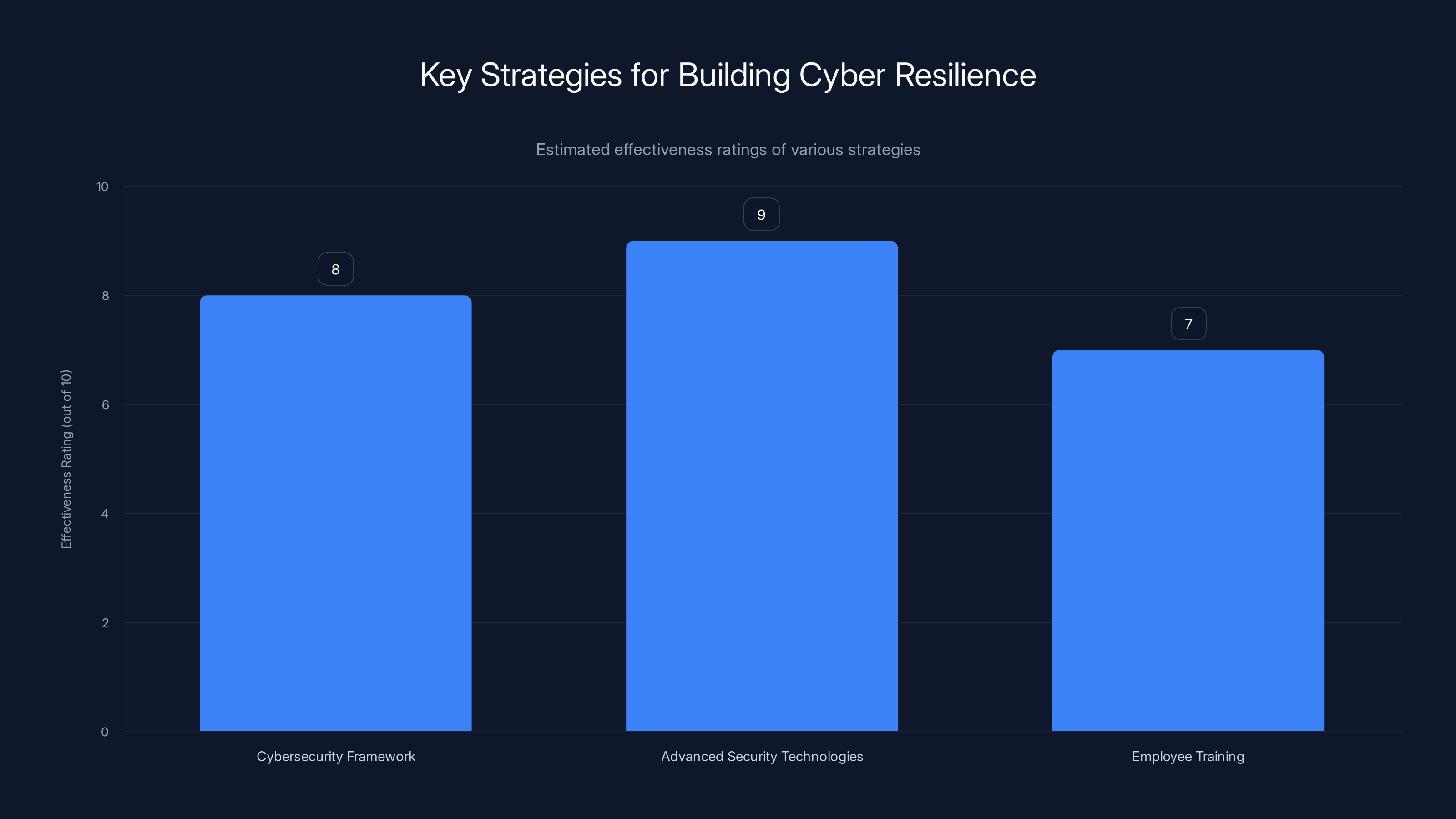
Investing in advanced security technologies is estimated to be the most effective strategy for building cyber resilience, followed closely by developing a comprehensive cybersecurity framework. Employee training is also crucial but slightly less effective on its own. Estimated data.
The Growing Threat of Cyberattacks
Cyberattacks have become a daily concern for businesses worldwide, but British companies are particularly vulnerable. Recent statistics reveal a shocking 71% of UK businesses have paid a ransom in the last year, highlighting the urgent need for improved security measures. According to Fortune Business Insights, the global cybersecurity market is expected to grow significantly, underscoring the importance of robust defenses.
Why Are Businesses Still Vulnerable?
Despite investing in sophisticated cybersecurity tools, businesses continue to fall prey to cyber threats. The reasons are multifaceted:
- Evolving Threat Landscape: Cybercriminals are constantly adapting, employing new tactics like ransomware-as-a-service (RaaS).
- Complex IT Environments: The shift to remote work has expanded attack surfaces, introducing vulnerabilities.
- Human Error: Phishing attacks exploit employee mistakes, emphasizing the need for better training.

Strategies for Building Cyber Resilience
Building resilience against cyberattacks involves more than just technology. Here’s a comprehensive approach:
1. Develop a Comprehensive Cybersecurity Framework
A strong cybersecurity framework is the backbone of any resilient organization. This involves:
- Risk Assessment: Identify and prioritize risks based on potential impact.
- Policy Development: Establish clear policies for data protection and incident response.
- Regular Audits: Conduct regular security audits to identify vulnerabilities.
2. Invest in Advanced Security Technologies
Technological solutions are critical to staying ahead of cyber threats. Consider:
- AI and Machine Learning: Use AI to detect anomalies and predict potential threats, as highlighted by Morphisec's adaptive AI defense.
- Endpoint Detection and Response (EDR): Monitor and respond to threats on endpoint devices, a strategy supported by The Hacker News.
- Network Segmentation: Limit the spread of threats within the network, as emphasized by Nile's zero trust fabric.
3. Employee Training and Awareness
Human error remains a significant vulnerability. Effective training programs should:
- Simulate Phishing Attacks: Regularly test employees with simulated phishing emails.
- Offer Continuous Education: Keep staff updated on the latest threats and security practices, as recommended by Cybersecurity Ventures.
- Create a Security-Conscious Culture: Encourage employees to report suspicious activities without fear.
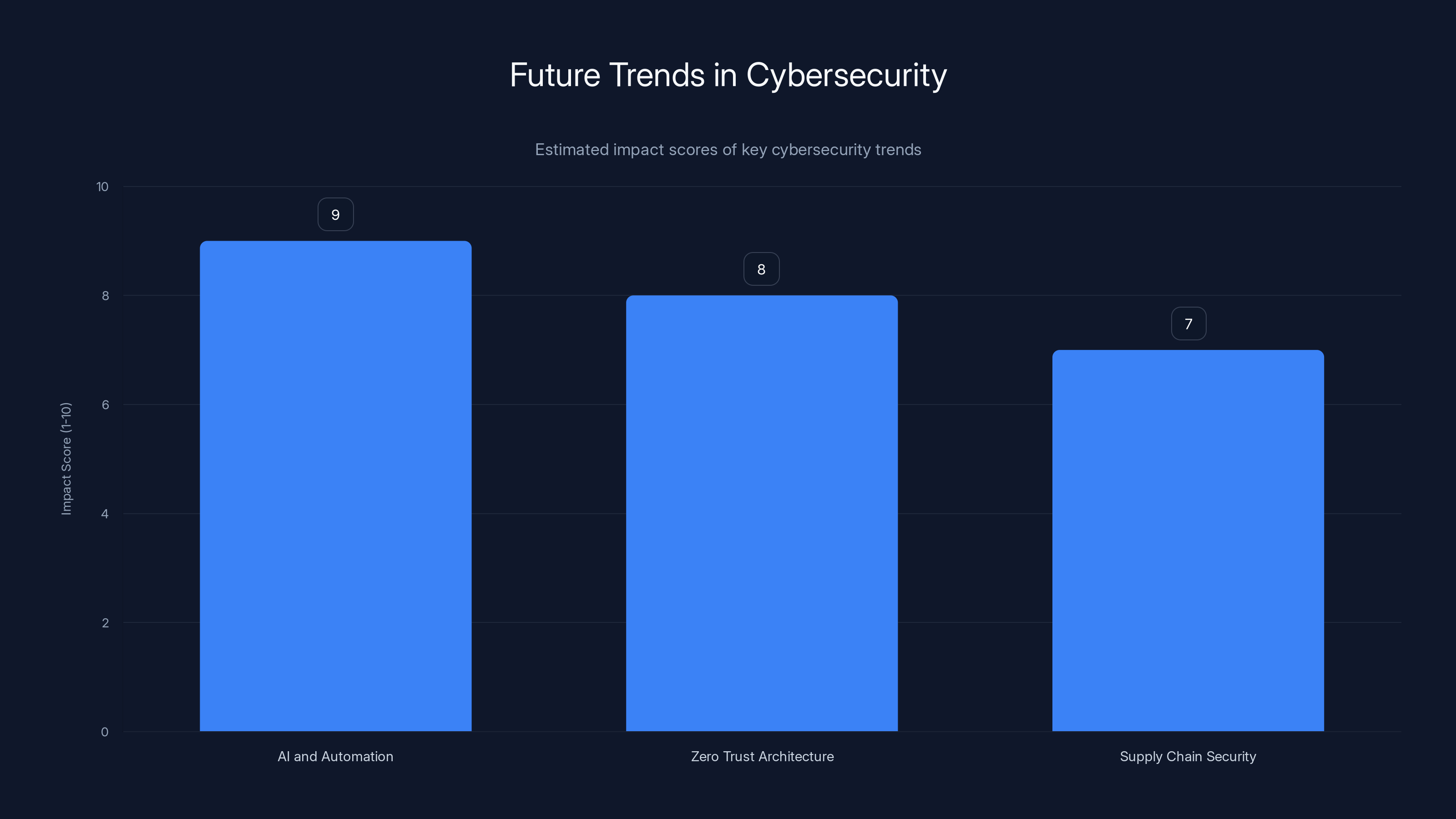
AI and Automation are expected to have the highest impact on future cybersecurity strategies, followed by Zero Trust Architecture and Supply Chain Security. (Estimated data)
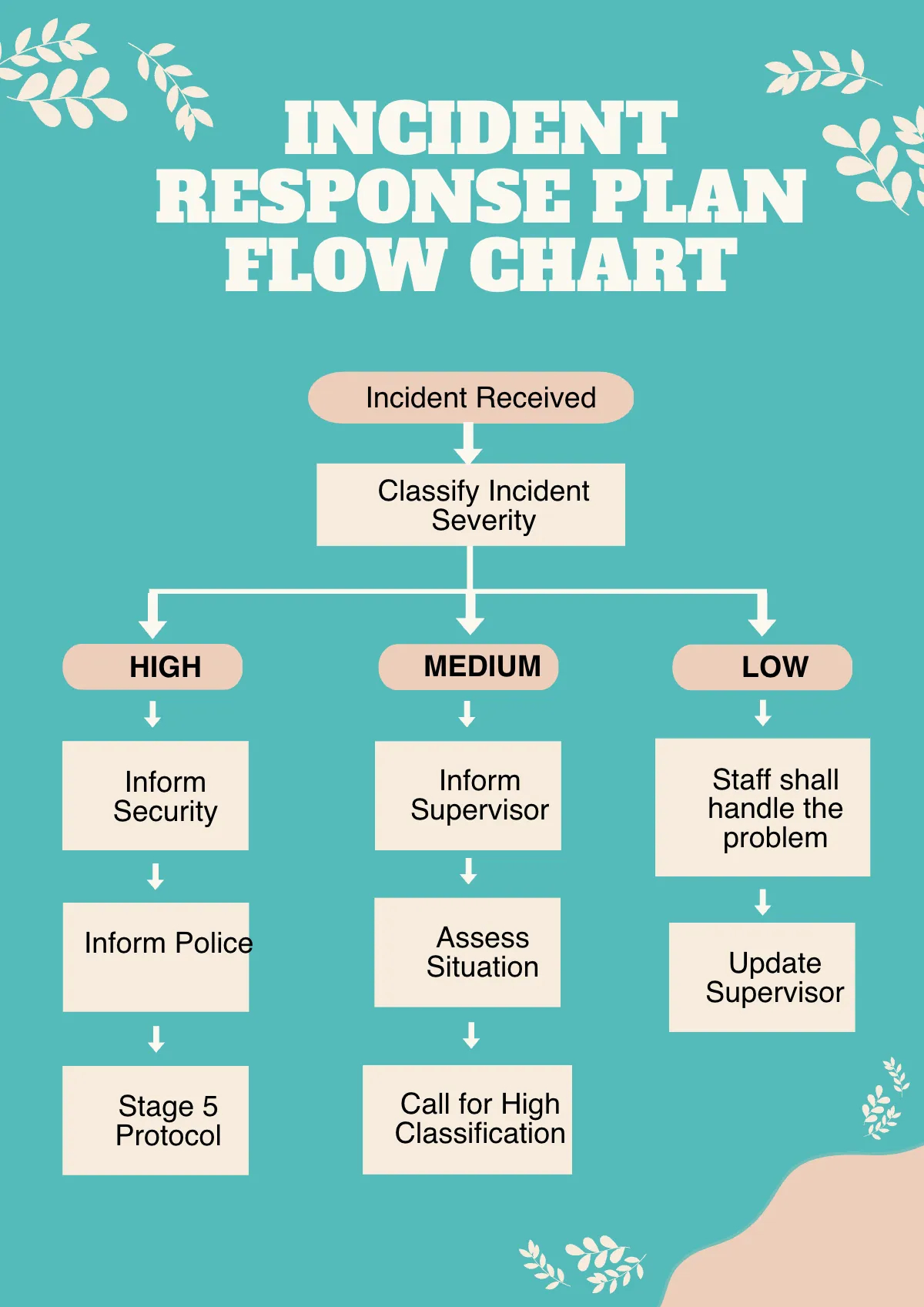
Implementing a Proactive Incident Response Plan
An effective incident response plan minimizes damage and accelerates recovery. Key steps include:
- Preparation: Define roles and responsibilities, and ensure everyone knows the plan.
- Detection and Analysis: Use tools to detect threats and assess their potential impact.
- Containment and Eradication: Quickly isolate affected systems and remove threats.
- Recovery and Post-Incident Review: Restore systems and evaluate the response to improve future readiness.
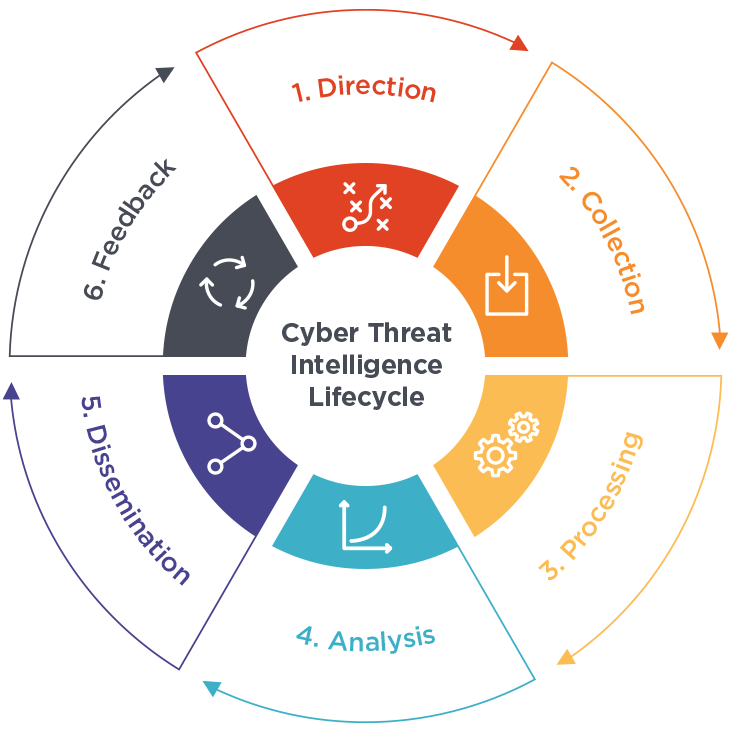
Leveraging Threat Intelligence
Keeping abreast of the latest threats is crucial for proactive defense. Threat intelligence involves:
- Monitoring Threat Feeds: Stay updated with real-time threat feeds from trusted sources.
- Sharing Information: Collaborate with industry peers through information-sharing platforms, a strategy endorsed by Cybersecurity Insiders.
- Analyzing Trends: Identify patterns and predict future threats to stay one step ahead.
Future Trends in Cybersecurity
As cyber threats evolve, so must our defenses. Key trends to watch include:
1. Increased Use of AI and Automation
AI will play a pivotal role in cybersecurity, offering:
- Predictive Analytics: Anticipate threats before they occur.
- Automated Responses: Quickly neutralize threats without human intervention.
2. Zero Trust Architecture
Adopting a zero trust model ensures:
- Strict Access Controls: Verify every user and device, regardless of location.
- Micro-Segmentation: Further isolate network segments to limit threat movement.
3. Focus on Supply Chain Security
As supply chains become more integrated, they also become more vulnerable. Businesses must:
- Vet Third-Party Vendors: Ensure partners adhere to stringent security standards.
- Monitor for Supply Chain Attacks: Use specialized tools to detect anomalies in supply chain operations, as discussed by Industrial Cyber.

Common Pitfalls and How to Avoid Them
Despite best efforts, businesses often fall into common traps:
1. Overreliance on Technology
While technology is vital, overreliance can be detrimental. Balance tech with:
- Regular Human Oversight: Ensure human checks are in place to catch issues tech might miss.
- Diverse Security Measures: Combine technological solutions with procedural and policy-based approaches.
2. Neglecting Basic Cyber Hygiene
Simple practices can prevent many cyber incidents. Ensure:
- Regular Software Updates: Keep all systems and applications updated.
- Strong Password Policies: Implement multi-factor authentication (MFA) and enforce strong password policies.
3. Inadequate Backup Strategies
Data loss can cripple a business. Avoid this by:
- Regular Backups: Schedule frequent data backups and test recovery processes.
- Offsite and Cloud Solutions: Use cloud-based solutions for additional backup security.

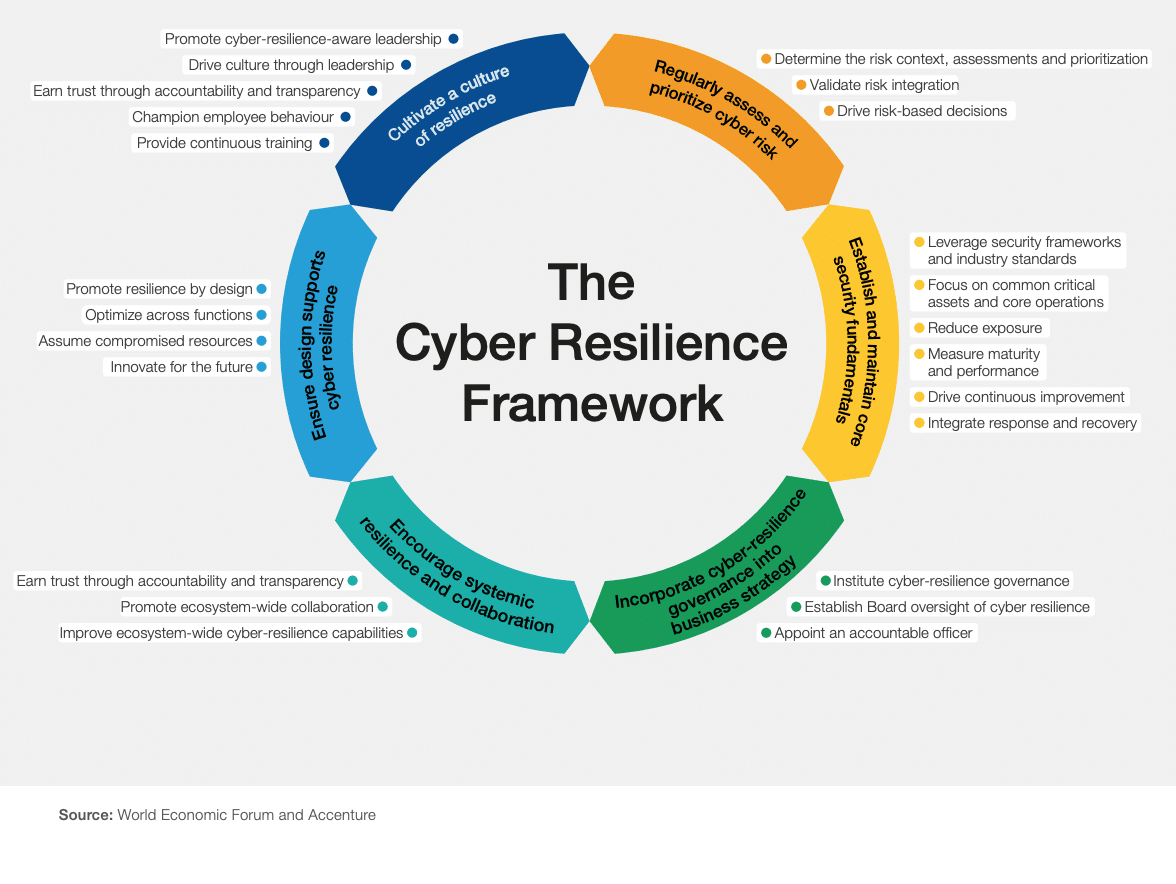
Building a Culture of Cyber Resilience
Resilience is as much about culture as it is about technology. Foster a security-first mindset by:
- Leadership Commitment: Ensure top management prioritizes and invests in cybersecurity.
- Employee Engagement: Involve staff at all levels in security initiatives.
- Continuous Improvement: Regularly review and update security practices based on new threats and technologies.
Conclusion
The cyber threat landscape is constantly evolving, and British businesses must adapt to survive. By implementing comprehensive security frameworks, investing in technology, and fostering a culture of resilience, organizations can effectively tackle the challenges of cyberattacks and protect their future.
FAQ
What is cyber resilience?
Cyber resilience refers to an organization's ability to prepare for, respond to, and recover from cyberattacks. It involves a combination of strategies, technologies, and cultural practices aimed at minimizing the impact of cyber incidents.
How can businesses improve their cybersecurity posture?
Businesses can enhance their cybersecurity by adopting a multi-layered defense strategy, investing in advanced technologies like AI and machine learning, conducting regular security audits, and providing continuous employee training.
What role does employee training play in cybersecurity?
Employees are often the first line of defense against cyber threats. Effective training programs help employees recognize and respond to phishing attacks, understand the importance of strong passwords, and adopt security best practices.
Why are backups important in cybersecurity?
Regular backups ensure that critical data can be restored in the event of a cyberattack. This minimizes downtime and data loss, helping businesses recover more quickly.
What is the future of cybersecurity?
The future of cybersecurity will likely involve increased use of AI and automation, adoption of zero trust architectures, and a greater focus on supply chain security. These trends will help organizations better anticipate and respond to emerging threats.
How can businesses recover from a cyberattack?
Recovery involves a structured incident response plan that includes detection, containment, eradication, and recovery. Businesses should also conduct post-incident reviews to improve future resilience.
Key Takeaways
- Cyberattacks are increasing, with 71% of UK businesses paying ransoms.
- Resilience requires a holistic cybersecurity framework.
- Employee training is crucial to prevent phishing attacks.
- AI and automation are key trends for future cybersecurity.
- Zero trust architecture enhances network security.
Related Articles
- The Open Source Blind Spot in Our Supply Chains: A Comprehensive Guide [2025]
- The Rise of the Cyber Hacker: Does Clout Matter More Than Cash? [2025]
- Industrializing Deception: How Cybercriminals Are Infiltrating Trusted Domains [2025]
- Ajax's Data Breach: Lessons and Strategies for Protecting Fan Information [2025]
- Can Customer Success Managers Transition into Forward Deployed Engineers? [2025]
- Meta's Strategic Shift: Embracing AI Amidst Workforce Changes [2025]
![British Businesses Struggling to Recover from Cyberattacks: Strategies for Resilience [2025]](https://tryrunable.com/blog/british-businesses-struggling-to-recover-from-cyberattacks-s/image-1-1774526871608.jpg)



