Industrializing Deception: How Cybercriminals Are Infiltrating Trusted Domains
Introduction
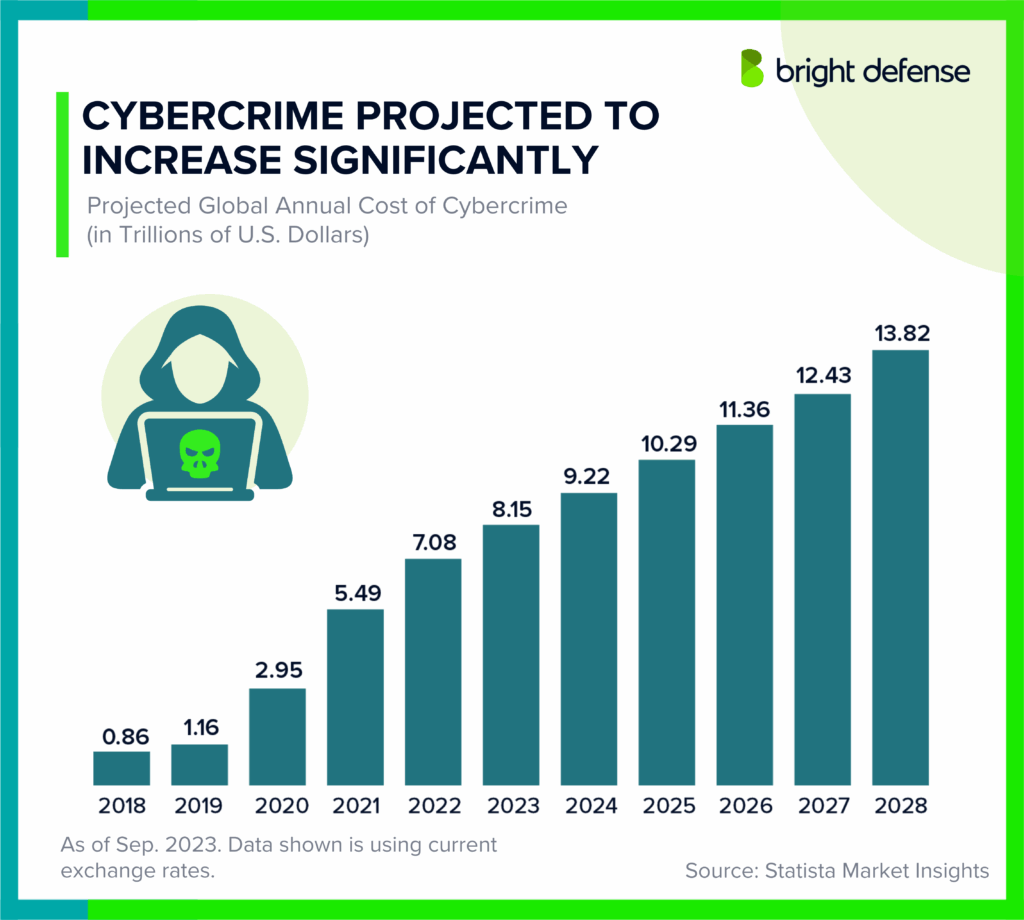
Last year, a major multinational corporation fell victim to a cyber attack that exploited a legacy software vulnerability, resulting in millions of dollars in losses. This incident is part of a broader trend where cybercriminals have industrialized deception, infiltrating trusted domains worldwide. Recent reports highlight how these syndicates are leveraging outdated software, crypto fraud, and fake e-commerce sites to exploit unsuspecting victims. This article delves into these cybercrime tactics, offering insights into how individuals and organizations can protect themselves.
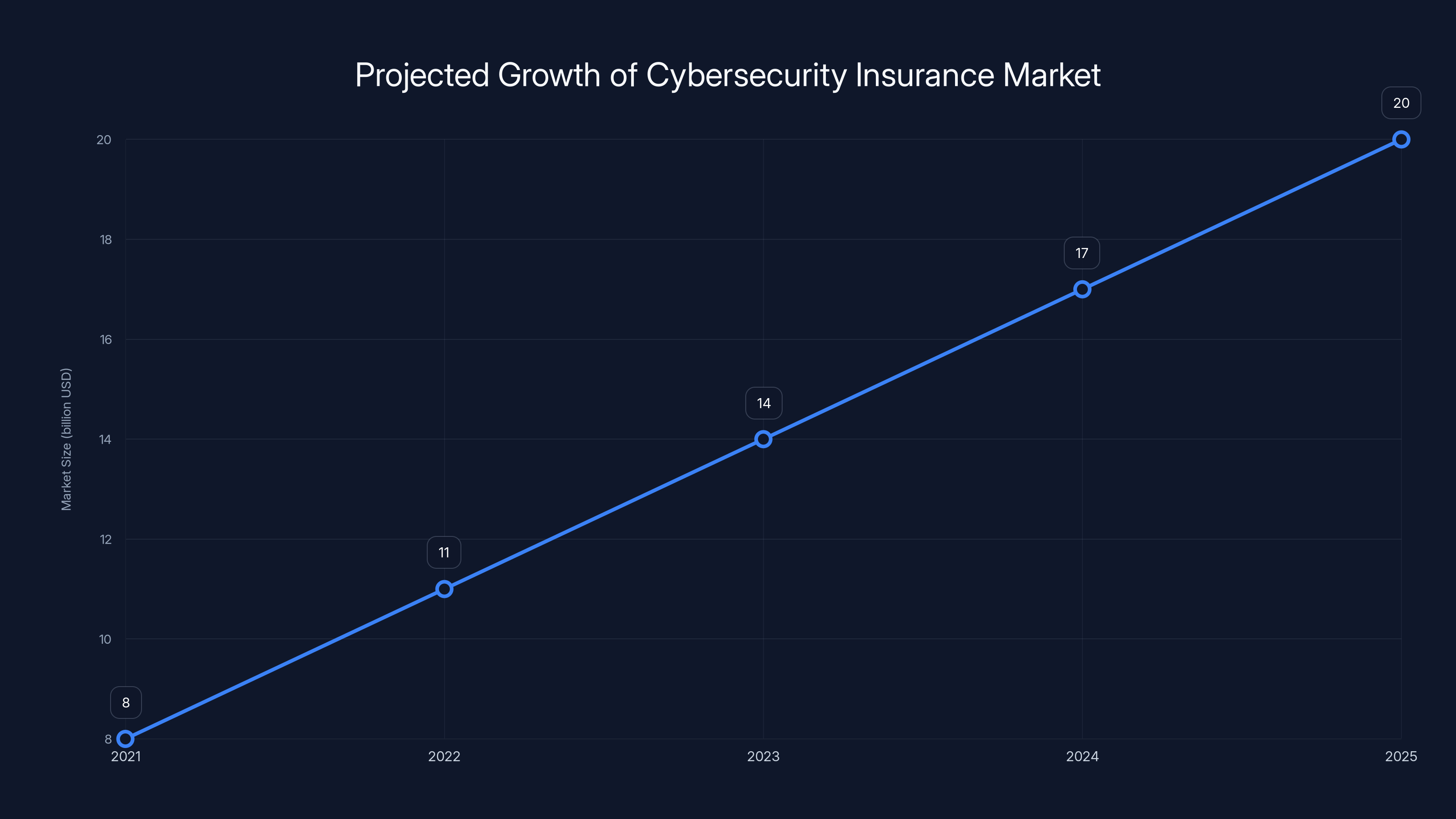
The global cybersecurity insurance market is projected to grow significantly, reaching $20 billion by 2025. Estimated data based on industry trends.
TL; DR
- Cybercrime Syndicates: Organized groups are exploiting vulnerabilities in outdated software globally, as highlighted in a recent executive order.
- Crypto Fraud: Sophisticated scams are tricking victims into paying fake fees, a trend noted in modern financial reviews.
- Fake E-commerce Sites: Over 800 fraudulent sites are offering too-good-to-be-true deals, as reported by TechRadar.
- Legacy Software Vulnerabilities: Exploits in outdated platforms like FCKeditor are rampant, as detailed in Duo's documentation.
- Prevention Strategies: Regular updates, multi-factor authentication, and user education are critical, as emphasized in a UNODC report.
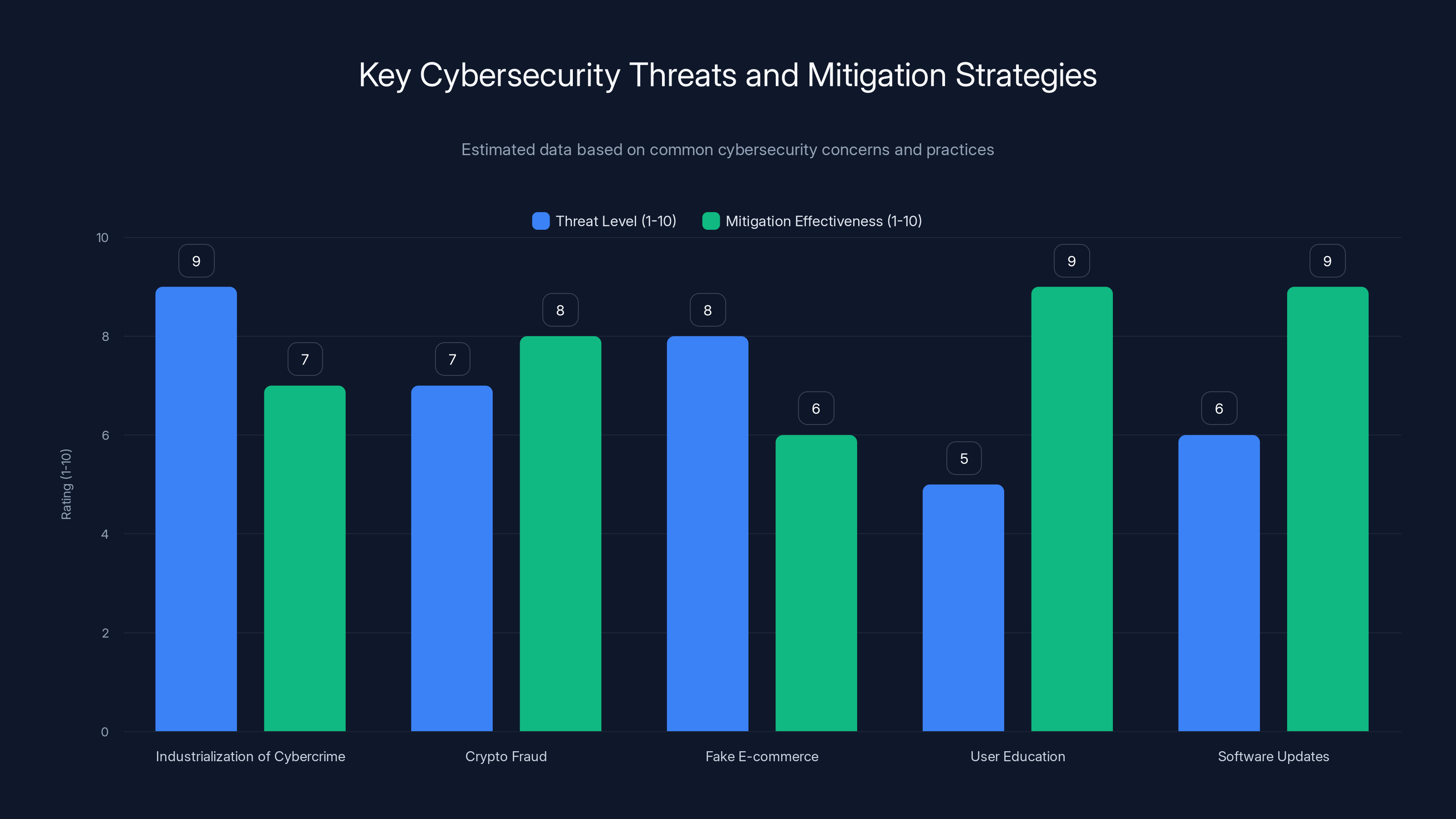
The industrialization of cybercrime poses the highest threat, but effective mitigation strategies like user education and software updates can significantly reduce risks. (Estimated data)
The Industrialization of Cybercrime
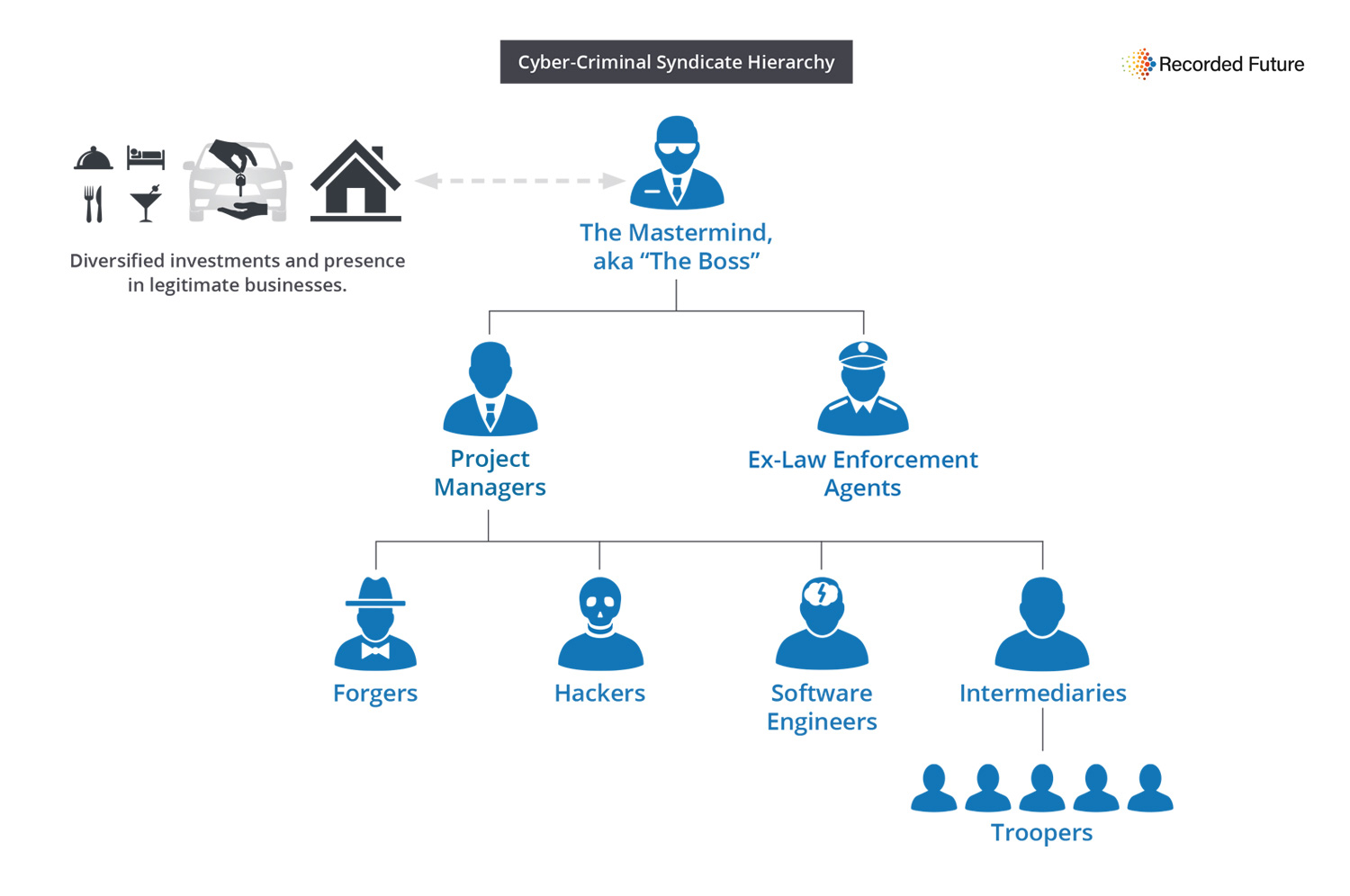
From Lone Hackers to Organized Syndicates
In the past, cybercrime was often the realm of lone hackers working in isolation. Today, it's a different story. Cybercriminals have organized into syndicates, operating much like traditional businesses. They employ specialists, from developers and marketers to customer service reps, to execute complex scams. These operations are sophisticated, targeting millions of victims across the globe, as noted in a Cloudflare report.
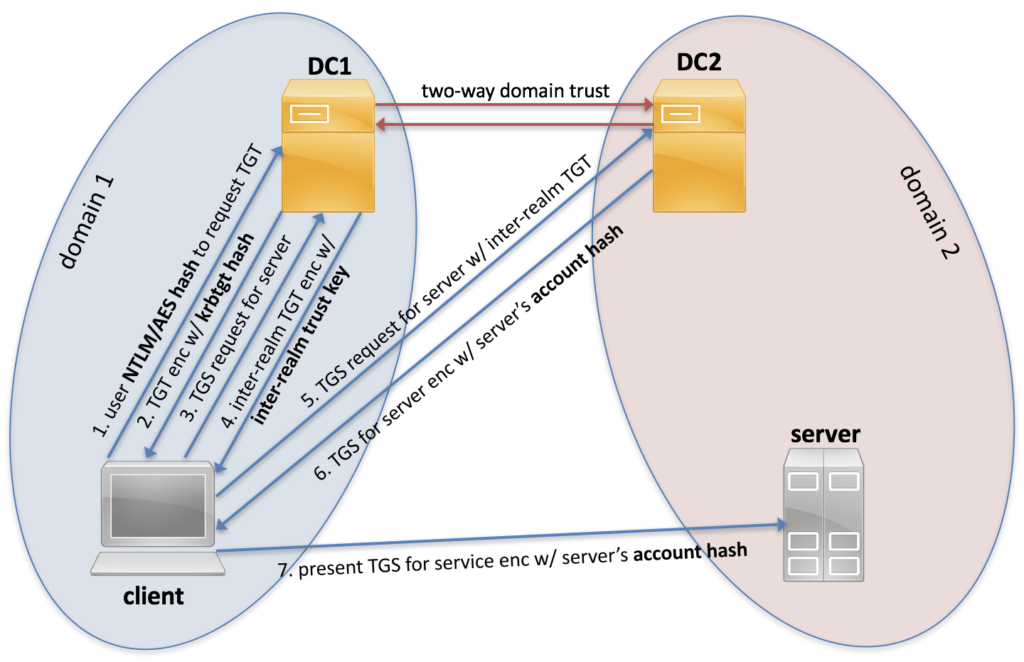
How Cybercriminals Exploit Trusted Domains
Trusted domains are those that users frequently visit and interact with, expecting a level of security and authenticity. Cybercriminals have learned to exploit these domains by infiltrating them with malware and fraudulent activities. They use techniques like phishing, domain spoofing, and injection attacks to gain access, as detailed in Frontiers in Computer Science.
The Role of Outdated Software
Outdated software is a goldmine for cybercriminals. Vulnerabilities in legacy systems are frequently exploited because updates and patches are often neglected. One notable example is the legacy FCKeditor flaw, which has been used to hijack over 1,300 domains. This vulnerability allows attackers to upload malicious files, leading to unauthorized access and data breaches, as reported by Duo.
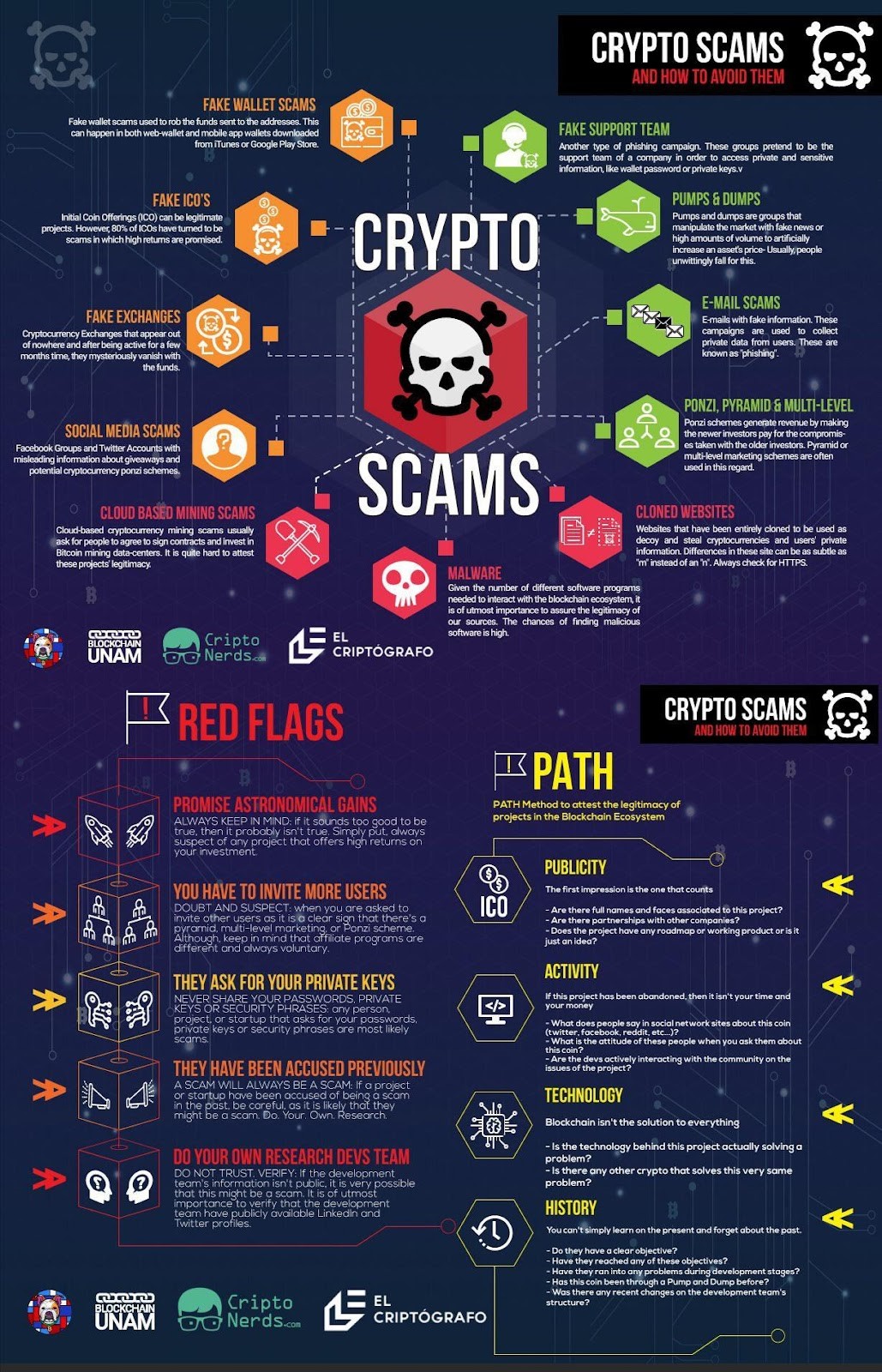
The Rise of Crypto Fraud
Understanding Crypto Fraud
Cryptocurrency has opened new avenues for cybercrime. Fraudsters use fake investment schemes and crypto exchanges to trick victims into transferring funds. The allure of quick riches makes these scams particularly effective, as highlighted in a modern financial review.
Common Crypto Scams:
- Fake Exchanges: These sites mimic legitimate crypto platforms, luring users to deposit funds that are never returned.
- Ponzi Schemes: Promise high returns for early investors, funded by new investors until the scheme collapses.
- Rug Pulls: Developers create a new token, inflate its value, then disappear with investors' money.
The Impact of Fake Fees
A prevalent tactic in crypto fraud is the imposition of fake fees. Victims are led to believe they must pay fees to unlock their crypto funds, but these payments go directly to the scammers, as noted by the National Council on Aging.
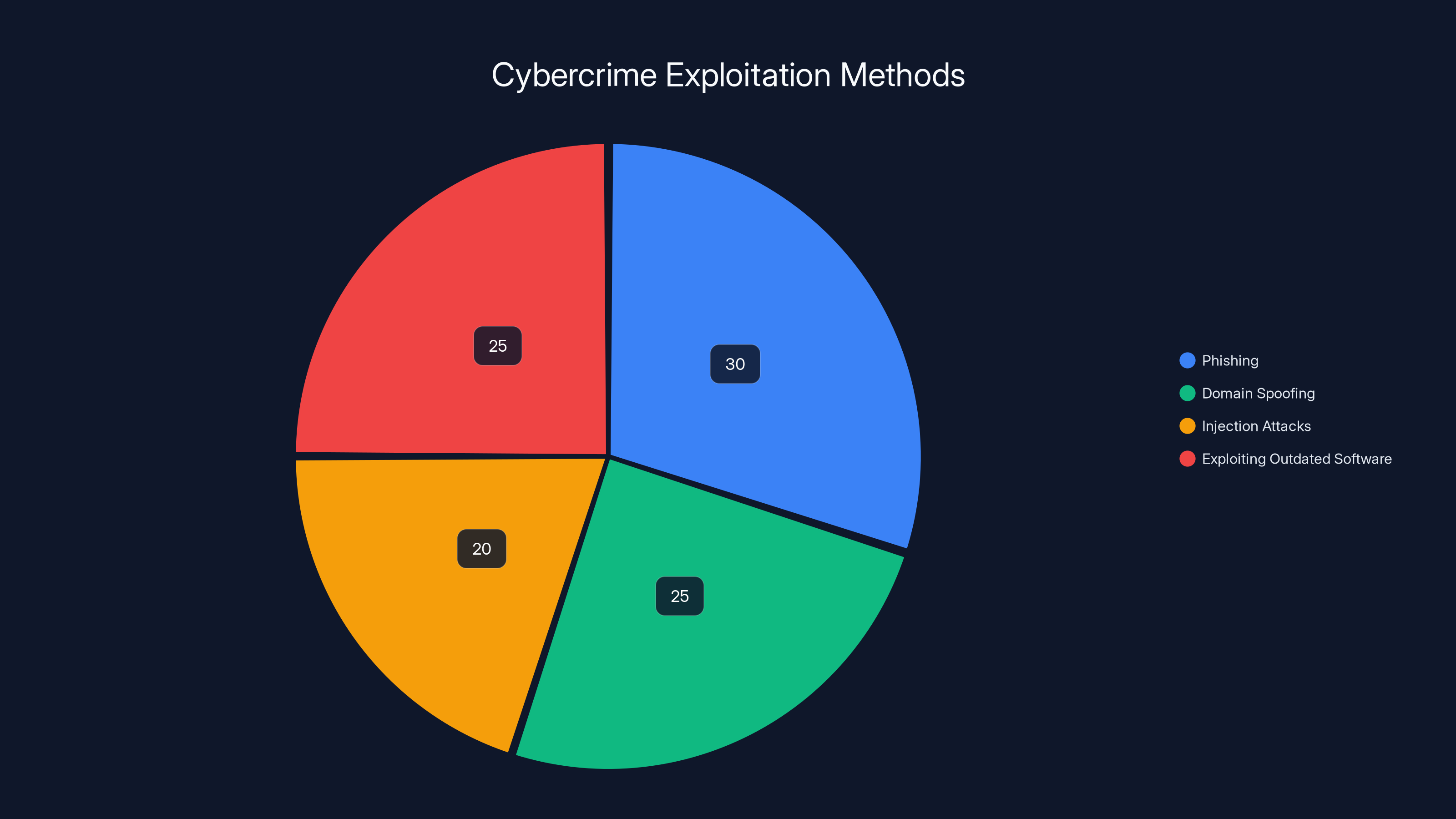
Cybercriminals utilize various methods to exploit trusted domains. Phishing and exploiting outdated software are among the most common tactics. (Estimated data)
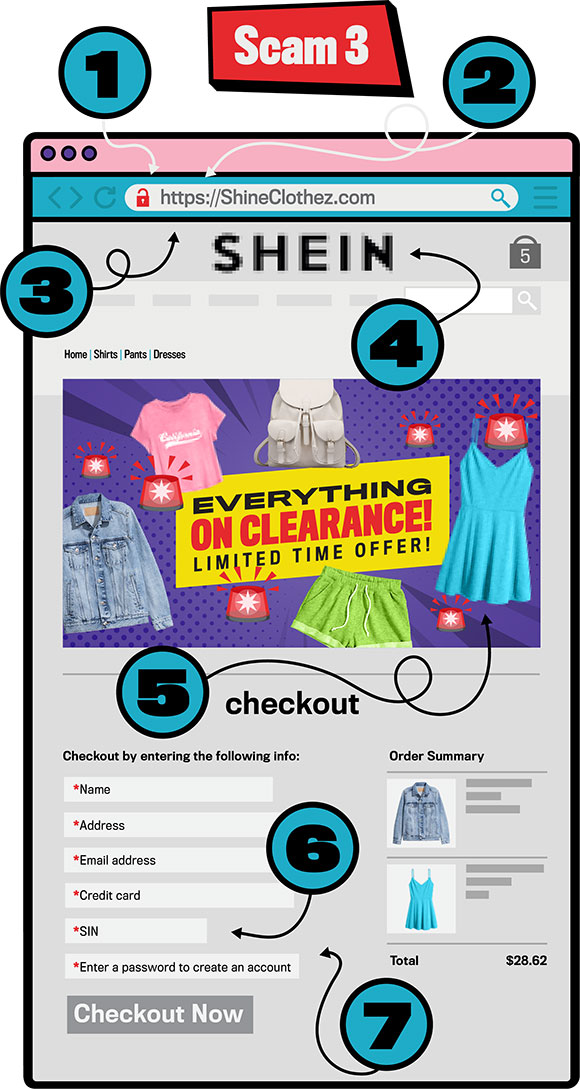
Fake E-commerce Sites: A Growing Threat
Anatomy of a Fraudulent E-commerce Site
Fake e-commerce sites have proliferated, with cybercriminals setting up over 800 such sites. These sites often offer products at unbeatable prices, enticing users to make purchases. The items never arrive, and the user's payment information is often used for further fraud, as reported by TechRadar.
Red Flags:
- Too-Good-to-Be-True Deals: Extremely low prices on high-demand products.
- Lack of Contact Information: No physical address or customer service number.
- Poor Website Design: Low-quality images and text laden with grammatical errors.
Case Study: The Chinese-Speaking Syndicate
One notable operation involves a Chinese-speaking syndicate running these fraudulent sites. They exploit language barriers and cultural differences to target Western consumers, often using SEO techniques to appear legitimate, as detailed in The Guardian.
Best Practices for Protecting Against Cybercrime
Regular Software Updates
Keeping software up to date is one of the simplest yet most effective ways to protect against cybercrime. Software developers regularly release patches to fix vulnerabilities. Ignoring these updates leaves systems open to attack, as emphasized in Apple's latest guidelines.
Implementing Multi-Factor Authentication (MFA)
MFA adds an extra layer of security by requiring two or more verification steps to access an account. Even if a hacker obtains your password, MFA can prevent unauthorized access, as recommended by Duo's security documentation.
Educating Users
User education is a critical component of cybersecurity. Training programs can teach employees and individuals to recognize phishing attempts, avoid suspicious links, and practice safe browsing habits, as outlined in a UNODC report.

Common Pitfalls and Solutions
Overreliance on Antivirus Software
While antivirus software is essential, it should not be the only line of defense. Cyber threats are evolving, and additional layers of security are necessary, as noted in Fortune Business Insights.
Solution: Combine antivirus software with firewalls, intrusion detection systems, and regular security audits.
Neglecting Mobile Security
As more people use mobile devices for online transactions, neglecting mobile security is a significant oversight, as highlighted in Cloudflare's report.
Solution: Install mobile security apps, keep your operating system updated, and avoid downloading apps from untrusted sources.
Future Trends in Cybercrime
AI and Machine Learning
Cybercriminals are increasingly using AI and machine learning to automate attacks. These technologies can analyze vast amounts of data to identify vulnerabilities faster than humans, as discussed in Frontiers in Computer Science.
Impact: Expect more sophisticated phishing attacks and social engineering tactics as AI continues to evolve.
Blockchain and Decentralized Security
While blockchain technology underpins many cryptocurrencies, it also offers potential for cybersecurity. Decentralized security systems can distribute data across multiple nodes, making it harder for cybercriminals to compromise, as noted in Cloudflare's report.
Recommendations for Organizations
Establishing a Cybersecurity Framework
Organizations should adopt a comprehensive cybersecurity framework, adhering to standards such as ISO/IEC 27001. This framework should include risk assessment, incident response, and continuous monitoring, as recommended by Fortune Business Insights.
Investing in Cybersecurity Insurance
Cybersecurity insurance can mitigate the financial impact of a cyber attack, covering costs associated with data breaches and system downtime, as projected by Fortune Business Insights.
Conclusion
Cybercriminals are industrializing deception at an unprecedented scale, exploiting vulnerabilities in trusted domains to perpetrate sophisticated scams. By understanding these tactics and implementing robust security measures, individuals and organizations can protect themselves from becoming victims. Staying informed and vigilant is crucial in navigating the evolving landscape of cybercrime.
FAQ
What is the biggest threat from cybercriminals today?
The biggest threat is the industrialization of cybercrime, where organized groups exploit outdated software and trusted platforms to execute sophisticated attacks, as noted in Cloudflare's report.
How can individuals protect themselves from crypto fraud?
Individuals can protect themselves by only using reputable exchanges, enabling security features, and conducting thorough research before investing in any crypto asset, as recommended by modern financial reviews.
Why are fake e-commerce sites so effective?
These sites are effective because they exploit consumer trust and the desire for bargains, often using SEO to appear legitimate and offering enticing deals that lure unsuspecting shoppers, as reported by TechRadar.
What role does user education play in cybersecurity?
User education is vital in cybersecurity, as informed users are less likely to fall for phishing scams and other social engineering tactics, as outlined in a UNODC report.
How can businesses mitigate the risk of cyber attacks?
Businesses can mitigate risk by updating software regularly, implementing multi-factor authentication, conducting security audits, and training employees on cybersecurity best practices, as recommended by Fortune Business Insights.
What future trends should we expect in cybercrime?
Expect increased use of AI and machine learning by cybercriminals to automate attacks, as well as the potential rise of blockchain-based security solutions, as discussed in Frontiers in Computer Science.
Is cybersecurity insurance worth the investment?
Yes, cybersecurity insurance can help organizations recover financially from a cyber attack, covering costs related to data breaches and system recovery, as projected by Fortune Business Insights.
Why is it important to keep software updated?
Keeping software updated is crucial because updates often include patches for security vulnerabilities that could otherwise be exploited by cybercriminals, as emphasized in Apple's latest guidelines.
Key Takeaways
- Cybercriminals are industrializing deception on a global scale.
- Outdated software poses significant cybersecurity risks.
- Fake e-commerce sites exploit consumer trust with fraudulent deals.
- AI and blockchain are emerging trends in cybercrime and cybersecurity.
- User education and regular software updates are crucial for protection.
Related Articles
- The Open Source Blind Spot in Our Supply Chains: A Comprehensive Guide [2025]
- Ajax's Data Breach: Lessons and Strategies for Protecting Fan Information [2025]
- The Greek Spyware Scandal: Lessons from the Convicted Spy Chief's Controversy [2025]
- Understanding the LLM PyPl Package Compromise [2025]
- The Rise of the Cyber Hacker: Does Clout Matter More Than Cash? [2025]
- Cyber-Resilience for the Modern Data Center: Strategies and Best Practices [2025]
![Industrializing Deception: How Cybercriminals Are Infiltrating Trusted Domains [2025]](https://tryrunable.com/blog/industrializing-deception-how-cybercriminals-are-infiltratin/image-1-1774525020497.jpg)



