Introduction: When Nation-State Hackers Come Calling
Last month, Singapore's government made a quiet but significant announcement that sent ripples through the cybersecurity community worldwide. A sophisticated Chinese cyber-espionage group had successfully infiltrated the networks of Singapore's four largest telecommunications companies, gaining what officials described as "limited access to critical systems" as reported by The Record. But here's what makes this story really interesting: they didn't steal customer data, didn't knock services offline, and didn't hold anyone for ransom. This wasn't a smash-and-grab heist. It was something far more deliberate and far more dangerous.
The group behind the attack, known as UNC3886, represents a new breed of cyber threat that keeps security teams up at night. Unlike the ransomware gangs making headlines, UNC3886 operates with patience. They're nation-state backed, likely working on behalf of the Chinese government, and their goals are intelligence gathering and strategic positioning as detailed by SecurityWeek. Think of them as digital burglars who want to slip into your house undetected, photograph your documents, and leave without you knowing they were ever there.
What happened in Singapore matters because it's not an isolated incident. It's part of a larger pattern of Chinese cyber operations targeting critical infrastructure across the Asia-Pacific region and beyond. The Singapore attack follows similar incursions at telecom companies in the United States and other countries as noted by Industrial Cyber. And the methods they're using—zero-day vulnerabilities, rootkits, advanced persistence techniques—represent a significant evolution in cyber-espionage tactics.
This article digs deep into what actually happened in Singapore, how these attacks work, why telecommunications companies are such attractive targets, and what the broader implications are for global cybersecurity. We'll examine the technical details of UNC3886's methods, compare this attack to similar incidents worldwide, and explore what organizations should be doing to defend themselves against state-sponsored threats.
Let's start by understanding exactly who got hit and why.
TL; DR
- The Attack: UNC3886, a China-backed hacking group, targeted Singapore's four largest telecom companies (Singtel, Star Hub, M1, and Simba Telecom) in a months-long campaign as reported by Creative Learning Guild.
- What They Got: Hackers gained "limited access to critical systems" but didn't disrupt services or steal customer data, according to Singapore's government as noted by Wiky.
- The Methods: Advanced tools including rootkits and zero-day exploits in routers and firewalls, targeting systems where traditional security tools can't detect malware as detailed by The Hacker News.
- The Pattern: Similar attacks are happening globally; this resembles Salt Typhoon attacks on U.S. telecoms, suggesting coordinated Chinese cyber-espionage operations as discussed by Industrial Cyber.
- Bottom Line: This is nation-state positioning for long-term intelligence gathering and potential future disruptive capabilities, not immediate criminal theft as analyzed by CSIS.
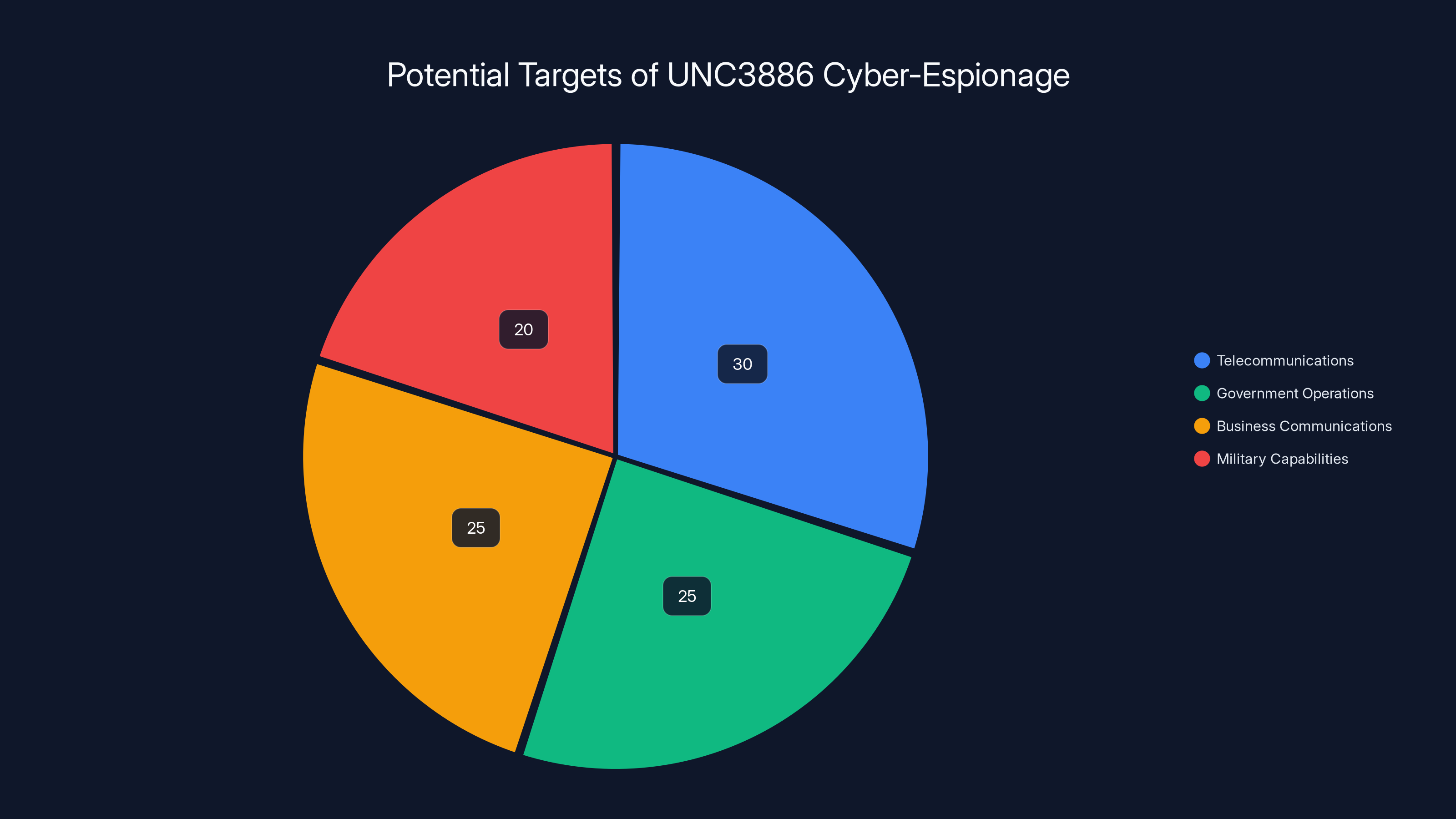
Estimated data shows telecommunications as the primary focus of UNC3886, followed by government and business communications.
The Four Targets: Understanding Singapore's Telecom Landscape
Singapore's telecommunications sector is one of Asia's most sophisticated and well-connected digital ecosystems. When the government announced the breach, they specifically named four companies: Singtel, Star Hub, M1, and Simba Telecom as reported by Industrial Cyber. These aren't random targets. These are the backbone of Singapore's digital infrastructure, responsible for voice communications, data transmission, and internet connectivity for millions of residents and businesses.
Singtel stands as the largest of the four, with the deepest roots in Singapore's telecom history. The company handles critical communications infrastructure, enterprise connectivity, and consumer services across Singapore and throughout the Asia-Pacific region. When hackers get inside Singtel's systems, they're not just accessing one company's data, they're potentially positioned to see information flowing across major regional networks.
Star Hub is the second-largest player, competing fiercely with Singtel across residential and business segments. M1 rounds out the major players, while Simba Telecom operates as a smaller but still significant player in the sector. Together, these four companies control the vast majority of telecommunications infrastructure in Singapore. That concentration makes them incredibly valuable targets for intelligence gathering as noted by Industrial Cyber.
Why focus on telecoms specifically? Because telecommunications companies sit at a unique intersection. They control the physical and digital infrastructure through which all other communications flow. Email servers, financial transactions, government communications, military coordination, business communications, personal data. It all passes through telecom networks. For a nation-state seeking intelligence, getting inside a telecom company's systems is like getting access to a massive surveillance relay that you can tap into for years without anyone knowing.
The attack lasted for months before detection and confirmation. That timeframe is significant. It suggests that UNC3886 had already bypassed initial defenses and established themselves deep enough in the networks to operate without raising alarms for an extended period as reported by The Record. The companies have since implemented detection mechanisms and remediation steps, but the fact that the breach went undetected for months points to the sophistication of the attack and the limitations of existing security measures.

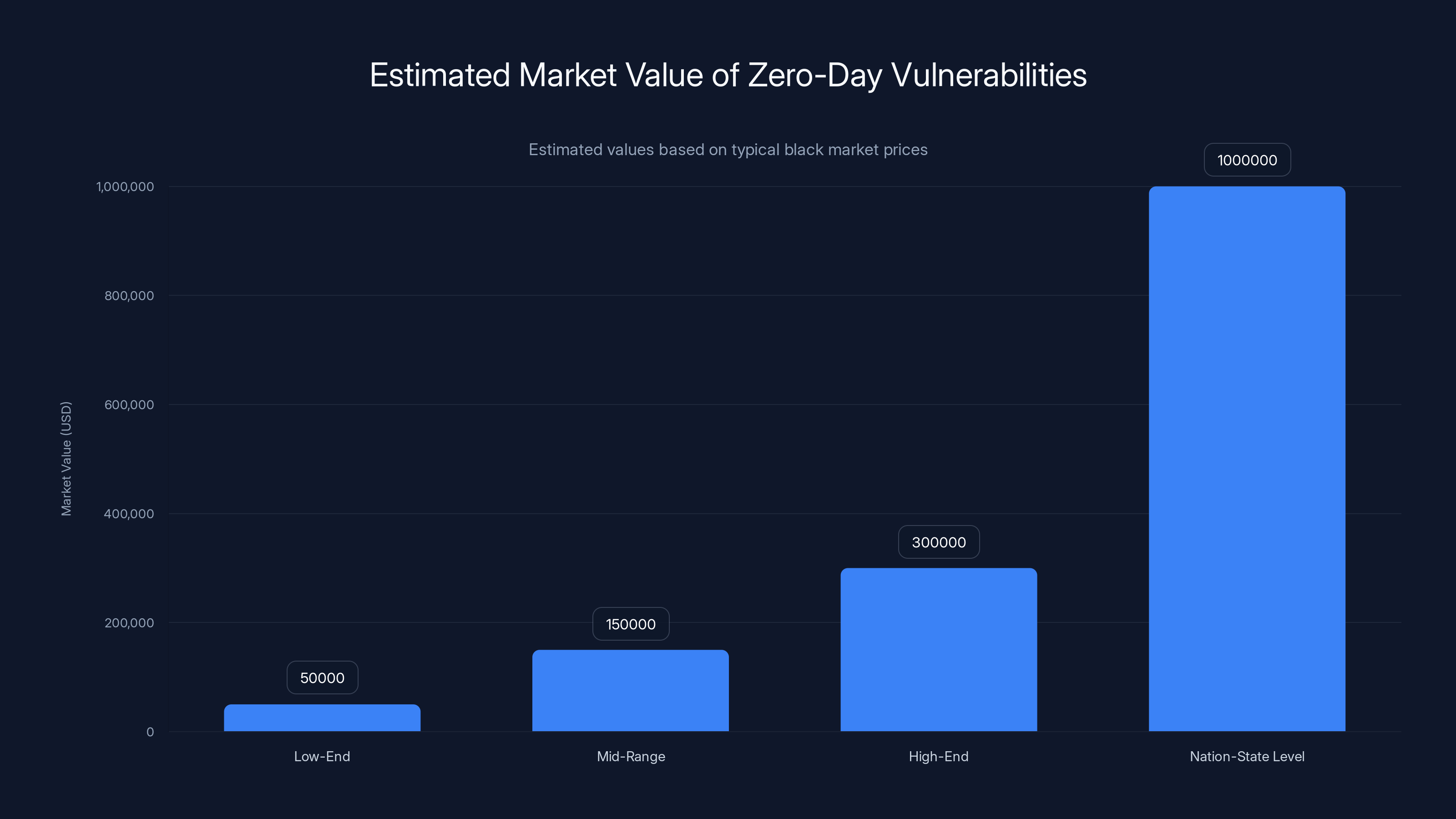
Zero-day vulnerabilities can range from
UNC3886: The Threat Actor Behind the Breach
UNC3886 isn't a new group. Mandiant, the cybersecurity division owned by Google, has been tracking this group for years. What makes UNC3886 distinct from other cyber-espionage groups is their focus on long-term infrastructure compromise and their willingness to target zero-day vulnerabilities that haven't been publicly disclosed as detailed by The Hacker News.
The designation "UNC3886" is cybersecurity shorthand for "Uncategorized Threat Group 3886," created by Mandiant analysts to track a specific collection of attack behaviors, infrastructure patterns, and targeting. Think of it as a fingerprint. When Mandiant sees certain techniques, specific infrastructure patterns, and particular target selections, they attribute them to UNC3886. The naming system helps analysts communicate about threat groups across the industry without making assumptions about who exactly is behind the attacks.
However, Singapore's government has been more direct. Officials publicly stated that UNC3886 is "likely working on behalf of China" as noted by Industrial Cyber. That's not speculation or inference. That's an official government assessment based on intelligence gathered from the attack investigation. The attribution carries weight because Singapore maintains sophisticated intelligence services and works closely with international partners like the United States and Australia on cyber matters.
What distinguishes UNC3886 from criminal hacking groups? Patience and resources. Criminal hackers usually want quick payoffs. They'll hit a target, extract data, and move on before getting caught. UNC3886 operates completely differently. They establish persistence mechanisms that allow them to stay inside a network for years if needed. They're not stealing customer credit card numbers for quick cash. They're positioning themselves to gather intelligence on strategic communications, understand network topology for potential future disruption, and maintain access to see what's happening across target networks.
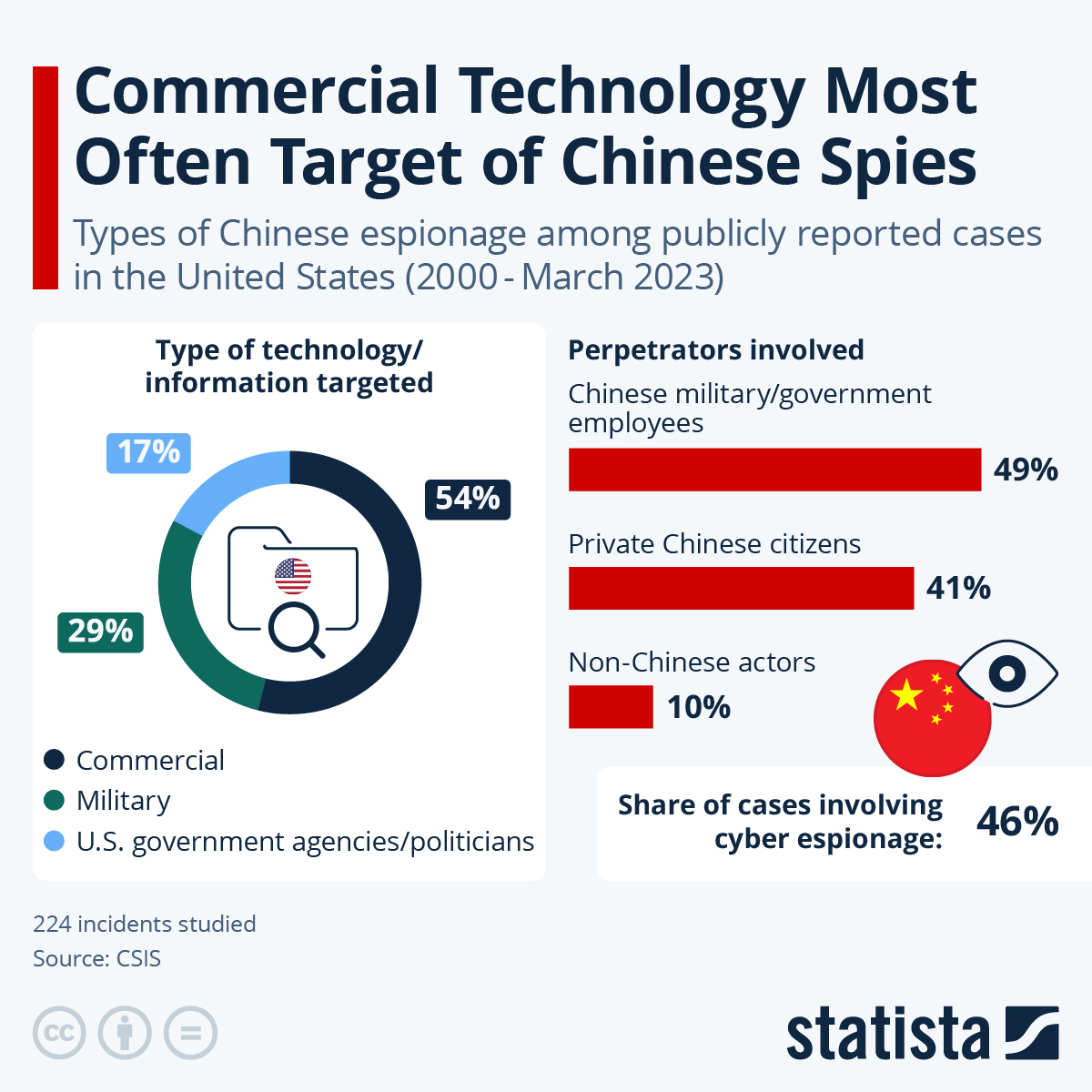
The group has a history of targeting the defense, technology, and telecommunications sectors across the United States and Asia-Pacific region. This isn't their first rodeo with critical infrastructure. They've previously hit technology companies, defense contractors, and telecommunications providers. Each attack builds their expertise and understanding of how these systems work, what security measures are in place, and how to avoid detection.

Zero-Days and Rootkits: The Technical Arsenal
The Singapore government's statement mentioned that UNC3886 used "advanced tools, like rootkits," to gain long-term persistence. For the non-technical reader, this requires some explanation, because the difference between ordinary malware and what UNC3886 was using is the difference between picking a lock and having a master key to every room in the building as noted by Industrial Cyber.
A zero-day vulnerability is a security flaw that nobody knew existed until it's exploited. The software vendor hasn't discovered it, security researchers haven't found it, and there's no patch. The "zero" refers to the number of days the vendor has known about the flaw before it's publicly exploited. Zero-days are incredibly rare and incredibly valuable. Some zero-days are sold on the black market for hundreds of thousands of dollars. Nation-states sometimes buy them, develop them, or steal them to maintain an asymmetric advantage against targets they're interested in.
UNC3886 is known for exploiting zero-day vulnerabilities specifically in routers, firewalls, and virtualized environments. Why these specific targets? Because they sit at the network perimeter and in critical infrastructure layers where traditional security tools have blind spots. Most malware detection systems work at the endpoint level, scanning the files and processes running on individual computers. But a router or firewall is a different beast. These devices are managing the flow of all traffic, operating at a network level where traditional security tools can't easily reach them.
A rootkit is malware that operates at the deepest levels of an operating system, essentially giving the attacker administrator-level access and the ability to hide their presence from normal detection methods. Imagine an intruder who not only picks your lock and enters your home, but also installs hidden cameras, bugs every room, and modifies your security system so it won't alert you when they're there. That's essentially what a rootkit does on a computer network. From that position of privilege, the attacker can:
- Monitor all network traffic passing through the compromised system
- Create backdoors for persistent access
- Harvest credentials from legitimate users
- Modify audit logs to hide their activities
- Intercept communications without users knowing
The combination of zero-day exploits and rootkit persistence is what transforms an ordinary breach into a nation-state level threat. A criminal hacker might use publicly known vulnerabilities and straightforward malware. UNC3886 is using the most advanced exploitation techniques available to establish deep access that's extremely difficult to detect and remove.
Singapore's government statement said the hackers "were able to gain limited access to critical systems but did not get far enough to have been able to disrupt services" as reported by The Record. That phrasing is interesting because it suggests the attackers might have had the capability to disrupt services if they wanted to, but they didn't. That's consistent with intelligence gathering missions where the objective is to remain undetected for as long as possible, not to cause immediate damage.

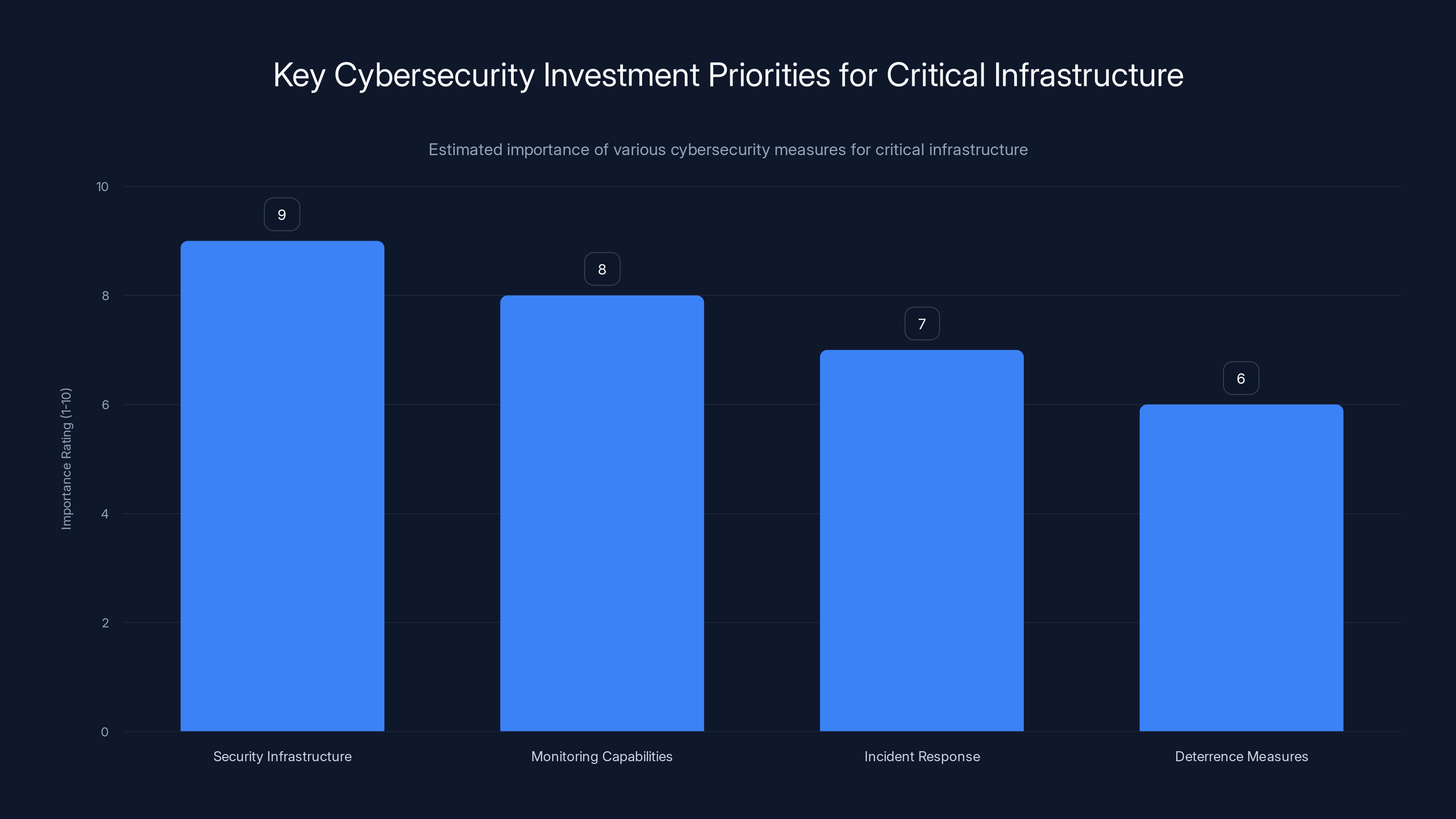
Investing in security infrastructure and monitoring capabilities is crucial for defending critical infrastructure against nation-state cyberattacks. Estimated data based on typical strategic priorities.
The Attack Timeline: Months of Undetected Presence
Singapore's government didn't release a detailed timeline of the attack, but piecing together the available information gives us a general picture of how events unfolded. The attack was months-long, meaning UNC3886 likely spent considerable time in reconnaissance and preparation before launching their initial intrusion attempts as reported by Creative Learning Guild.
The typical pattern for nation-state level attacks follows a predictable sequence. First comes reconnaissance, where the attackers research publicly available information about the target, scan for exposed systems, and identify potential entry points. For a major telecom company, this might involve scanning for outdated systems still exposed to the internet, researching the company's technology stack, identifying third-party vendors and partners, and looking for known vulnerabilities.
Second comes weaponization and initial access. This is where zero-day exploits come into play. Once UNC3886 identified a suitable vulnerability in the telecom companies' networks, they developed an exploit for it and launched their attack. The initial compromise might have been at a single point, like a firewall or router that was externally exposed. Once inside, the attacker establishes a foothold and begins expanding their access.
Third comes lateral movement and persistence. The attackers move from the initial compromised system to other systems within the network, establishing multiple backdoors and persistence mechanisms. This is where the rootkits come in. By installing these deep-level tools, the attackers ensure they can regain access even if individual compromises are discovered and cleaned up.
Fourth comes the intelligence gathering phase. Once established, the attackers can monitor network traffic, harvest credentials, collect sensitive documents, and understand the full architecture of the target networks. This phase might last for months or years, with the attackers remaining completely undetected.
The attack came to light only after detection and investigation. It's unclear whether the telecom companies discovered it themselves, whether government agencies identified it, or whether a combination of incident response activities brought it to light. The Singapore government's coordinating minister for national security, K. Shanmugam, made the announcement, suggesting that government agencies played a significant role in the discovery and investigation as noted by Industrial Cyber.

The "Limited Access" Claim: What It Really Means
Singapore's government emphasized that the attackers achieved only "limited access" and "did not disrupt services or access personal information." This statement requires careful parsing because it contains important nuances as reported by Wiky.
When a government officially states that an attacker had "limited access," it could mean several things. It could mean the attackers only compromised certain systems and didn't spread throughout the entire network. It could mean they accessed certain data but not everything. Or it could be a carefully worded statement designed to reassure the public while acknowledging the severity of what actually happened.
The fact that they gained access to "critical systems" at all is significant. Telecom companies typically segment their networks, placing customer data systems in different zones from operational systems, which are themselves separated from administrative systems. If the attackers gained access to critical systems, they might have compromised infrastructure that controls service delivery, manages network routing, or stores sensitive operational data.
The assurance that they "did not access personal information" is important for public reassurance, but it also suggests the investigators specifically looked for evidence of data theft and found none. That doesn't mean the attackers couldn't have accessed it. It means there's no evidence they did. The attack was more about positioning and intelligence gathering than about stealing customer databases.
The "did not disrupt services" claim is significant because it aligns with what we know about UNC3886's operational patterns. They're not interested in creating obvious damage. Disrupting telecom services across Singapore would trigger immediate incident response, law enforcement involvement, and international attention. Instead, they wanted to slip in unnoticed, establish long-term access, and use that access for intelligence purposes as reported by The Record.
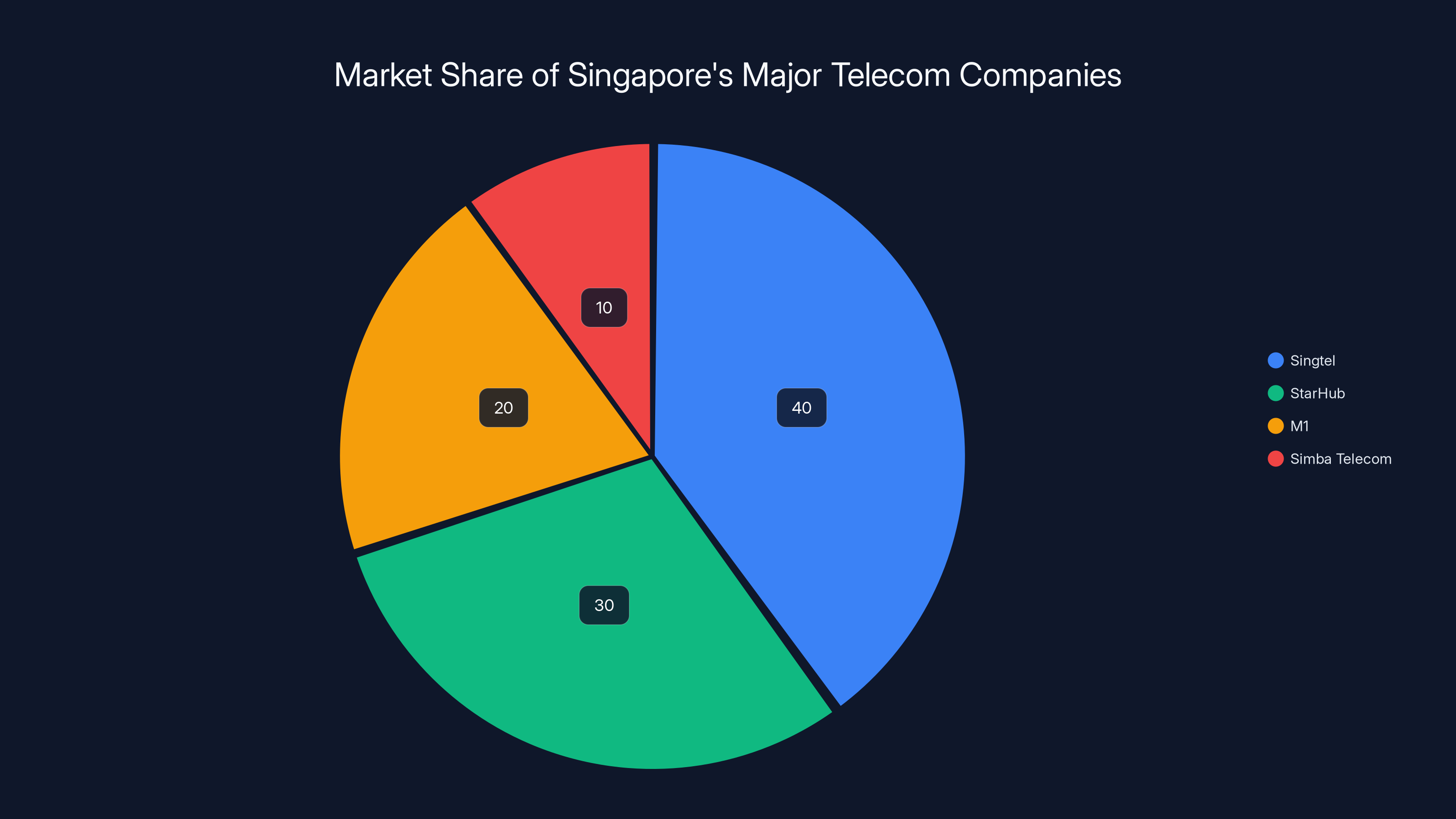
Singtel leads the telecom market in Singapore, followed by StarHub, M1, and Simba Telecom. Estimated data based on company influence and size.
Comparing Singapore to the Salt Typhoon Attacks
Singapore's government specifically referenced other cyberattacks on telecommunications companies around the world, noting that the Singapore attack "has not resulted in the same extent of damage as cyberattacks elsewhere." This is a reference to a different Chinese cyber-espionage operation known as Salt Typhoon as discussed by Industrial Cyber.
Salt Typhoon is a different but related threat actor that has been targeting telecommunications companies in the United States and other countries. Unlike UNC3886, which focuses on long-term intelligence gathering, Salt Typhoon's attacks have included more aggressive tactics like data exfiltration and attempts at service disruption. Salt Typhoon has targeted dozens of U.S. telecommunications companies, reportedly establishing access to multiple carriers simultaneously.
What's particularly alarming about Salt Typhoon is the scale and scope. Multiple investigations have suggested that Salt Typhoon potentially had access to lawful intercept capabilities within U.S. telecom networks. Lawful intercept systems are designed for law enforcement agencies to legally conduct wiretaps with proper warrants. If a foreign intelligence service gains access to these systems, they could potentially intercept communications on a massive scale without any legal authorization or detection.
The Salt Typhoon attacks also exposed the extent to which U.S. telecoms had been making security decisions based on cost rather than security principles. Some carriers had decommissioned older security monitoring systems without replacing them with equivalent protections. Others had poor network segmentation that allowed attackers who compromised one system to easily move laterally across the entire network.
The Singapore attack appears to be following a similar pattern, but as the government noted, hasn't reached the same level of disruption as Salt Typhoon. However, the Singapore government's public acknowledgment of the attack and the specific naming of UNC3886 suggests authorities are taking it very seriously and warning other organizations to be on alert as reported by The Record.
Both UNC3886 and Salt Typhoon are believed to be working on behalf of Chinese intelligence services. The parallel operations suggest a coordinated strategy by Chinese cyber-espionage units to map and penetrate telecommunications infrastructure globally. The objectives appear to include:
- Intelligence gathering on strategic communications
- Understanding network architecture for potential disruption capabilities
- Gaining access to lawful intercept and monitoring systems
- Establishing long-term persistence for potential future operations
- Collecting data on government and military communications

Why Telecommunications Companies Are Prime Targets
Telecom companies occupy a uniquely important position in digital infrastructure, which makes them uniquely attractive to nation-state attackers. To understand why, you need to think about what passes through telecom networks and what access they provide.
Every phone call, text message, email, video conference, online banking transaction, government communication, and internet data flow passes through telecom infrastructure. For a nation-state seeking intelligence, gaining access to a major telecom's systems is like getting a tap on the most important phone line in a country. You can potentially intercept communications, understand who's communicating with whom, identify sensitive government operations, discover military intelligence, and gather information on businesses and individuals.
Telecom companies are also critical to national infrastructure. Disrupting telecom services would impact emergency services, government operations, financial systems, healthcare, and public communication. If you have access to telecom infrastructure, you have the potential to conduct devastating cyberattacks that could cripple an entire country's digital operations.
Another reason telecoms are attractive targets is that they often have less sophisticated security than technology companies. While Google, Microsoft, and other tech giants invest heavily in security research and have teams of top security engineers, many telecom companies have traditionally invested less in cyber defense. They've often prioritized operational efficiency and cost reduction over security, leaving legacy systems in place that become security liabilities.
Additionally, telecom companies have extensive partnerships and connections with other critical infrastructure. Power companies, water utilities, banking systems, and government agencies all rely on telecom infrastructure for their operations and communications. Compromising a telecom company provides potential access to all of these sectors indirectly.
The geopolitical dimension is also important. Taiwan, Japan, South Korea, Australia, and other U.S. allies in Asia-Pacific are all strategically important. Gaining intelligence on their communications and infrastructure could be valuable to China for strategic planning. Singapore specifically, despite its geographical distance from China, is a major financial hub and strategic chokepoint for sea traffic. Understanding its communications infrastructure is strategically relevant.

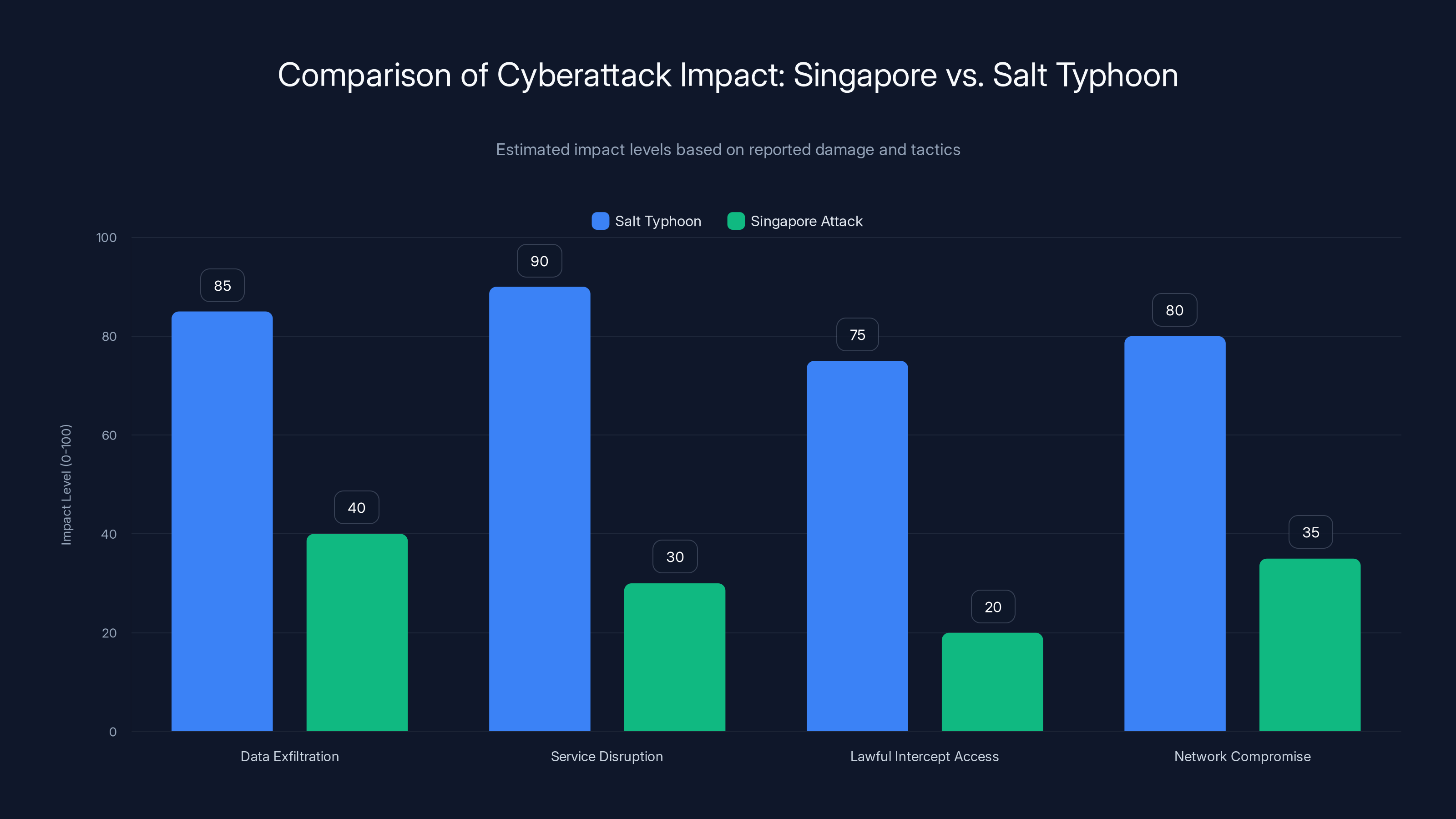
Salt Typhoon attacks have a significantly higher impact across various categories compared to the Singapore attack. Estimated data based on reported tactics and damage.
Nation-State Positioning for Future Conflict
One of the most important aspects of attacks like the Singapore incident is that they're not primarily about immediate theft or disruption. They're about positioning for potential future conflict. Chinese cyber operations, particularly those targeting telecom infrastructure, need to be understood in the context of what experts call "peacetime espionage and wartime attack preparation" as reported by The Record.
If tensions escalated between China and Taiwan, or China and Japan, or China and other regional powers, those nations would need to coordinate military responses with their allies. The U.S. military would need to coordinate with regional commands. Financial systems would need to operate to support military logistics. Communications infrastructure would be absolutely critical.
By establishing persistent access to telecom systems now, during peacetime, China is positioning itself to disrupt those communications in a future conflict scenario. They're not trying to cause disruption now because that would trigger too much international response. Instead, they're quietly establishing backdoors and understanding network architecture so that when a conflict does occur, they have the capability to degrade telecom services.
This is why the framing of the attack as "limited access" that "did not disrupt services" is so important. The attackers weren't interested in disruption. They were interested in establishing persistent, hidden access that they could potentially weaponize later. From a defense perspective, this is the most concerning type of threat because it's aimed at the long-term strategic military balance rather than immediate criminal gain.
This strategic framing also explains why governments are responding so seriously to these attacks. This isn't just about protecting customer data or ensuring services stay online. This is about maintaining strategic capabilities and the ability to coordinate responses to potential military threats.

Detection, Investigation, and Response
When Singapore's government announced the attack, they also revealed that the affected telecom companies had already begun remediation efforts. The companies issued a joint statement saying they "regularly face distributed denial-of-service and other malware attacks" and that they "adopt defence-in-depth mechanisms to protect our networks and conduct prompt remediation when any issues are detected" as reported by Wiky.
That statement is both reassuring and revealing. It's reassuring because it indicates the companies are taking security seriously and have incident response capabilities. It's revealing because it acknowledges that telecom companies face constant, ongoing cyber threats. DDoS attacks, malware attempts, and other probing activities are daily occurrences at major telecom companies.
The detection of the UNC3886 attack presumably happened through a combination of methods. It might have been detected through security monitoring that caught suspicious network activity. It might have been discovered through threat intelligence sharing with government agencies or international partners. It might have been found through a security audit or assessment. The specifics haven't been publicly disclosed.
Investigation likely involved forensic analysis of compromised systems, looking at audit logs to understand what the attackers accessed and when, tracing network connections to identify command and control infrastructure, and working with international partners to understand the full scope of the attack.
Response included removing the attackers' access, installing patches to close the zero-day vulnerabilities they exploited, hardening network security, and implementing additional monitoring to detect any remaining backdoors or persistence mechanisms.
One of the challenges with responding to nation-state level attacks is that attackers sometimes install multiple backdoors and persistence mechanisms. Even if you find and remove one entry point, the attackers might have another way back in. This is why responding to attacks like this often takes months or years of ongoing effort.

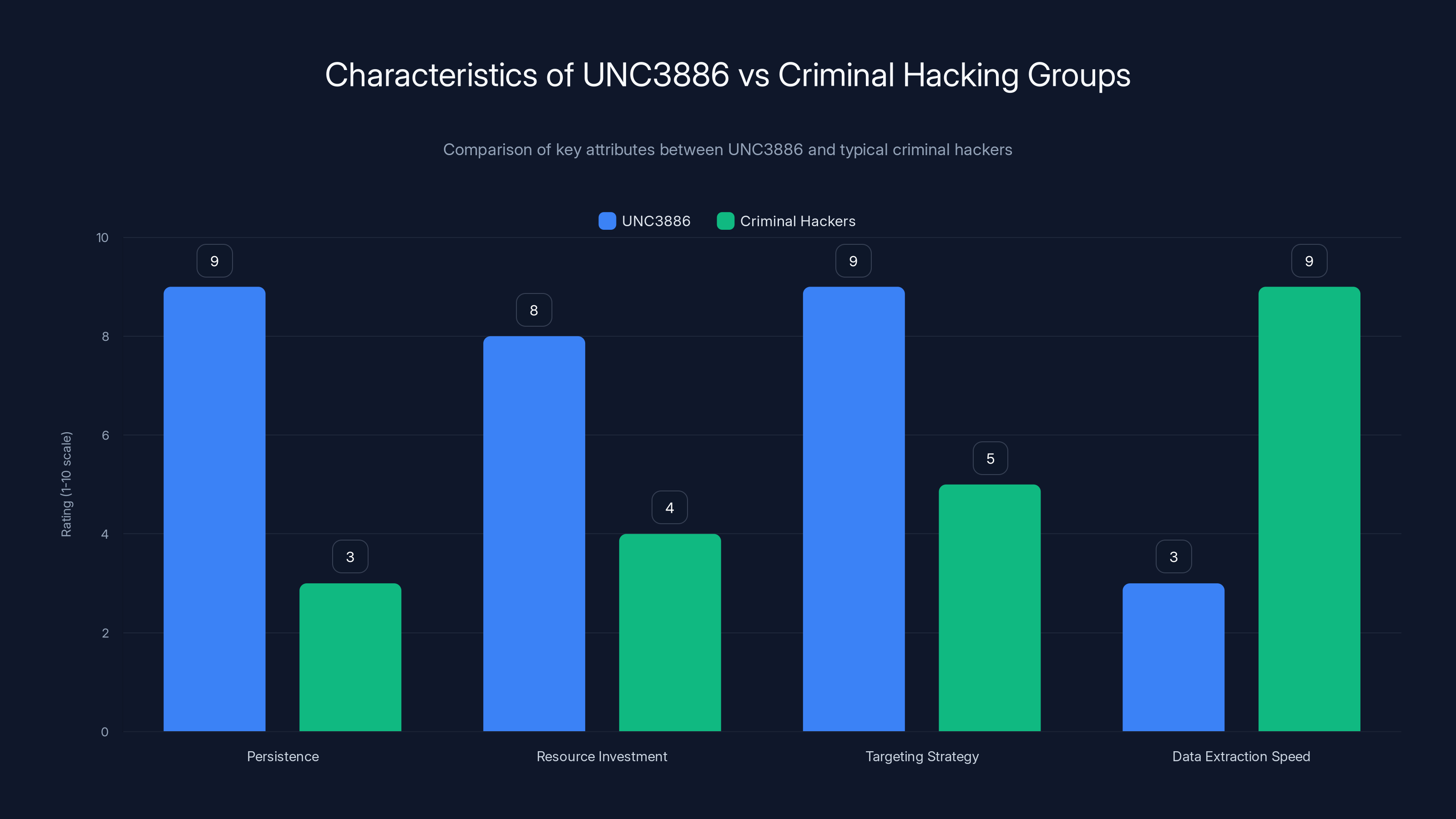
UNC3886 demonstrates high persistence and resource investment in their operations, contrasting with criminal hackers who prioritize quick data extraction. (Estimated data)
The Broader Pattern: China's Cyber Operations Strategy
The Singapore attack doesn't exist in isolation. It's part of a broader pattern of Chinese cyber operations targeting critical infrastructure in the Asia-Pacific region and beyond. Understanding this pattern helps contextualize why Singapore's government took the step of publicly acknowledging the attack and attributing it to China as reported by The Record.
China's cyber operations strategy appears to have several layers. At one level, there are the publicly known attacks and espionage operations that governments and security companies openly attribute to Chinese intelligence services. These are often the ones that become big news stories.
At another level, there are operations that are attributed only behind closed doors, in confidential government communications and security briefings. At a third level, there are operations that haven't been discovered yet.
The public naming of UNC3886 and its attribution to China suggests that Singapore's government believes the threat is significant enough that other organizations need to be aware and take defensive measures. This is a signal to other countries, other telecom companies, and other critical infrastructure operators that they should also be on alert for similar attacks.
China's overall cyber operations strategy appears to include:
- Intelligence gathering on communications infrastructure worldwide
- Understanding critical infrastructure so it can be disrupted if necessary
- Developing capabilities to conduct large-scale cyberattacks in a potential conflict scenario
- Testing new exploitation techniques and tools against real-world targets
- Maintaining long-term access to key infrastructure for strategic purposes
- Probing defenses to identify weaknesses
- Building maps of how different countries' critical infrastructure is connected
These operations aren't always coordinated in a central way. Different Chinese intelligence agencies might conduct overlapping or parallel operations. Some operations might be conducted by military units, others by civilian intelligence services, and others by government-affiliated private companies that serve as contractors.

Lessons for Defensive Operations
For organizations protecting critical infrastructure, the Singapore attack and similar incidents provide several important lessons about what effective defense looks like against nation-state level threats.
First, you cannot assume that good security practices will prevent a determined nation-state attacker from getting in. If an attacker has zero-day vulnerabilities and sufficient resources, they can likely breach even well-defended networks. The goal therefore isn't to prevent all breaches (which is impossible against nation-states), but to detect breaches quickly and limit the damage.
Second, network segmentation is critical. If an attacker compromises one system, network segmentation prevents them from automatically gaining access to every other system. By dividing the network into zones with different security levels and requiring additional authentication to move between zones, you limit the attacker's ability to spread laterally.
Third, monitoring and logging are essential. You need comprehensive visibility into what's happening on your networks. Who's accessing what systems? What data is being transferred? What commands are being executed? If you're not logging these activities, you won't be able to detect attackers. If you're not analyzing the logs, you won't catch suspicious activity.
Fourth, threat intelligence and information sharing are important. Knowing what tactics, techniques, and procedures (TTPs) nation-state groups are using helps organizations defend themselves more effectively. If you know UNC3886 typically exploits vulnerabilities in routers and firewalls, you can prioritize patching and monitoring those systems.
Fifth, incident response capabilities are critical. When you do detect an attack, you need the ability to respond quickly and effectively. That means having incident response plans, having trained personnel, having forensic tools available, and having working relationships with law enforcement and government agencies.
Sixth, supply chain security matters. UNC3886 might have entered telecom networks through compromised third-party vendors or partners. Vetting third-party security and monitoring their access is important. Seventh, assume breach. Plan for the scenario where attackers do get in. How will you detect them? How will you contain the damage? What's your communication plan? What's your recovery plan?

International Cooperation and Attribution
Singapore's public attribution of the attack to UNC3886 and to China is significant because attribution is both technically difficult and politically sensitive. For a government to publicly attribute an attack to another country, they need to be confident in their intelligence and be willing to accept the diplomatic consequences as noted by Industrial Cyber.
Attribution typically involves multiple intelligence streams. Technical attribution might include analyzing the tools and techniques used, identifying command and control infrastructure, and looking at operational patterns. But technical attribution alone is rarely sufficient for a government to make a public accusation. Usually, they combine technical evidence with human intelligence, signals intelligence, and information from international partners.
Singapore's position in international relations likely played a role in their willingness to make the attribution public. Singapore maintains good relationships with Western countries including the United States, Australia, and the United Kingdom. These countries have extensive intelligence capabilities and likely shared information with Singapore about UNC3886 and its likely connection to Chinese intelligence services.
The cooperation and intelligence sharing between countries on cyber threats is increasing. The Five Eyes alliance (United States, United Kingdom, Canada, Australia, and New Zealand) shares significant amounts of intelligence on cyber threats. Singapore, despite not being formally part of Five Eyes, works closely with these countries on security matters.
When Singapore's government made the public announcement, they were likely coordinating with international partners and following established patterns of attribution and disclosure. This kind of public acknowledgment serves multiple purposes: it warns other countries and organizations, it demonstrates to the domestic public that the government is addressing the threat, and it signals to the attacking country that their actions are known and are having diplomatic consequences.
The Role of Private Sector Visibility
While governments play an important role in attribution and response, much of the actual detection and investigation of cyberattacks happens in the private sector. The companies being attacked have the most detailed visibility into what happened. Security companies and researchers analyzing the attack have insights based on the tools and techniques used.
Mandiant, the Google-owned cybersecurity company that tracks UNC3886, plays an important role in documenting attack patterns and sharing that information with customers, law enforcement, and the public. When Mandiant publishes research about threat groups, that information becomes valuable to the broader security community.
Other security companies like CrowdStrike, Microsoft, Palo Alto Networks, and others also track nation-state cyber operations and publish research on their activities. This private sector research complements government intelligence and provides valuable information to organizations trying to defend themselves.
The Singapore telecom companies themselves likely worked with security consultants to investigate the breach, understand the scope of the attack, and develop remediation plans. While they didn't publicly disclose all the technical details, their joint statement acknowledged the attack and outlined their remediation approach as reported by Wiky.

Future Implications and Escalation Risks
The Singapore attack raises questions about future escalation of cyber operations against critical infrastructure. As countries develop more sophisticated cyber capabilities and establish persistent access to important networks, the risk of cyber conflict increases as reported by The Record.
In a potential military conflict, nations with persistent access to telecommunications infrastructure could use that access to devastating effect. Imagine a scenario where military operations are getting underway. One of the first steps might be cyberattacks targeting communications infrastructure to disrupt coordination and create chaos. If China already has backdoors installed in key telecom networks in Taiwan, Japan, or other countries, they could activate those backdoors to degrade critical communications when a conflict begins.
This creates a security dilemma for nations defending against such threats. To deter potential attacks, they need to make clear that attacking critical infrastructure will have severe consequences. But they also need to be careful not to escalate tensions or provoke the attacks they're trying to prevent.
For organizations operating critical infrastructure, the implications are clear: the threat from nation-state cyberattacks is not a hypothetical future concern, it's a present-day reality. Defensive investments in security infrastructure, monitoring capabilities, and incident response should be treated as essential strategic investments, not optional expenses.
The Singapore government's public response to the attack is also significant for what it signals to the international community. By publicly naming UNC3886 and attributing the attack to China, Singapore is signaling that such operations are unacceptable and that countries will use intelligence gathering and public attribution as responses. This creates a cost to China's cyber operations in the form of diplomatic friction and international attention.
However, this public response doesn't prevent future attacks. It might deter some low-level operations, but nation-state actors conducting espionage and strategic positioning operations are likely to continue regardless of public attribution. The risk of diplomatic fallout is generally seen as acceptable compared to the strategic value of the intelligence gathered and the capabilities developed.

What Telecom Companies Should Do Now
For telecommunications companies worldwide watching this incident unfold, the Singapore attack is a wake-up call about the evolving threat landscape. Nation-states are actively targeting telecom infrastructure, and traditional security approaches are insufficient.
Telecom companies should conduct comprehensive security audits of their networks, paying special attention to perimeter defenses like routers and firewalls where UNC3886 prefers to operate. They should inventory all systems and understand the full attack surface. They should implement network segmentation to limit lateral movement if attackers do gain entry. They should deploy advanced monitoring and detection systems that can identify unusual behavior even if malware is successfully installed.
They should establish relationships with government agencies and law enforcement so that if they detect attacks, they can rapidly escalate and receive support. They should participate in information sharing communities and threat intelligence exchanges so they know about threats targeting others in their sector.
They should also think carefully about their supply chain. Many telecom companies outsource operations to vendors and contractors. If those vendors are compromised, the telecom company is compromised. Vetting supply chain security and monitoring vendor access is critical.
Most importantly, they should treat cybersecurity as a strategic business priority, not just an IT expense. Board-level executives and C-suite leadership need to understand the cyber threat landscape and allocate resources accordingly. In the context of nation-state attacks, the costs of inadequate security can be measured in terms of national security implications, not just customer data protection.

The Geopolitical Dimension
To fully understand the Singapore attack, you need to see it in its geopolitical context. Singapore's strategic importance has grown significantly in recent years. It's a major financial center, a critical hub for regional trade and shipping, and home to significant technology infrastructure. China sees Singapore as an important player in regional geopolitics and wants to understand Singapore's capabilities and vulnerabilities as noted by Industrial Cyber.
Additionally, the attack reflects broader tensions in the Asia-Pacific region. As China becomes more assertive militarily, regional nations are strengthening their alliances with Western countries. The United States, Australia, Japan, and other countries are increasing military presence and coordination in the region. China's cyber operations are partly aimed at gathering intelligence on these partnerships and understanding the military capabilities of regional nations.
The timing of the public disclosure is also interesting. By announcing the attack publicly now, Singapore's government is signaling to other countries and to China that cyber operations against critical infrastructure are known about and will be responded to. This is part of a broader strategy of deterrence through transparency.
From China's perspective, conducting cyber espionage against regional critical infrastructure makes strategic sense. Even if the operations are discovered, the intelligence gathered and the capabilities developed have value. Plus, China likely has diplomatic confidence that these operations won't escalate into armed conflict or serious military response.

Conclusion: A New Normal in Cyber Warfare
The Singapore cyberattack against UNC3886 is neither unique nor particularly surprising to cybersecurity professionals who track nation-state operations. What makes it significant is the public acknowledgment, the specific attribution to a Chinese cyber-espionage group, and the clear demonstration that critical infrastructure worldwide is actively being targeted by sophisticated state-sponsored attackers as reported by The Record.
This attack reflects the emergence of a new phase in cyber conflict. We've moved past the era where cyberattacks were primarily conducted by criminals looking for financial gain or by hacktivists making political points. We're now firmly in an era where nation-states are conducting persistent, sophisticated cyberattacks against each other's critical infrastructure for strategic intelligence gathering and to position for potential future conflicts.
The methods used in the Singapore attack—zero-day exploits, rootkits, persistence mechanisms—represent the state of the art in offensive cyber capabilities. The targets chosen—telecommunications infrastructure—reflect the strategic value of communications networks to national security and military operations.
For organizations managing critical infrastructure, the implications are serious. You need to assume that sophisticated attackers are actively trying to compromise your systems. You need to implement defense-in-depth strategies that make it difficult for attackers to move laterally even if they do gain initial access. You need comprehensive monitoring to detect attackers quickly. And you need to be prepared for incident response when breaches do occur, because against nation-state level adversaries, prevention is impossible, but rapid detection and containment are achievable.
For countries and governments, the attack demonstrates the importance of cyber deterrence through transparency, investment in defensive capabilities, and international cooperation on threat intelligence. By publicly attributing the attack to China and demonstrating that their operations are being detected and investigated, Singapore and its international partners are sending a message that cyber operations have costs and consequences.
The Singapore attack also highlights the asymmetry in cyber conflict. A single small hacking group with nation-state backing can threaten the critical infrastructure of an entire country. A country needs far greater defensive resources to protect against these threats than an attacker needs to compromise infrastructure. This asymmetry is one of the defining characteristics of cyber warfare in the modern era.
Looking forward, we should expect to see more of these kinds of attacks, more public attribution, and more sophisticated defensive responses. Nations will continue to develop cyber capabilities, establish persistent access to critical infrastructure, and prepare for potential cyber conflict. Organizations managing critical infrastructure will need to continuously update their security practices to address evolving threats.
The good news is that many of the defensive measures that help protect against nation-state attacks are the same fundamentals that help protect against all cyberattacks: keep systems patched, segment networks, maintain comprehensive logging and monitoring, develop incident response capabilities, and treat cybersecurity as a strategic priority rather than a technical afterthought.
The Singapore attack is a reminder that in the interconnected digital world we inhabit, cybersecurity isn't optional. It's a fundamental requirement for national security, business continuity, and protection of critical services that billions of people depend on every day.

FAQ
What is UNC3886 and why does it matter?
UNC3886 is a cyber-espionage group tracked by Mandiant (Google's cybersecurity division) that is likely working on behalf of Chinese intelligence services. The group specializes in exploiting zero-day vulnerabilities in routers, firewalls, and virtualized environments to gain long-term persistent access to target networks without being detected. UNC3886 matters because they represent the kind of sophisticated, nation-state level threat that can compromise critical infrastructure and maintain hidden access for intelligence gathering purposes as noted by Industrial Cyber.
How did UNC3886 gain access to Singapore's telecom networks?
Based on the information disclosed by Singapore's government, UNC3886 likely used zero-day vulnerabilities in routers or firewalls exposed to the internet. These vulnerabilities were previously unknown to the software vendors and had no available patches. Once the initial breach was achieved, the group installed rootkits and other persistence mechanisms to maintain long-term hidden access to the networks, allowing them to gather intelligence for months without being detected as reported by Wiky.
Why would China conduct cyberattacks on Singapore's telecom companies?
China has strategic interests in Singapore as a major regional financial hub, critical shipping chokepoint, and important partner of Western countries including the United States. By gaining access to Singapore's telecommunications infrastructure, Chinese intelligence services can gather intelligence on Singapore's military capabilities, government operations, business communications, and connections with other countries. Additionally, establishing persistent access now positions China to disrupt these communications during any future military conflict as reported by The Record.
What does "limited access" mean in the context of this attack?
When Singapore's government stated that the attackers achieved only "limited access," this likely means they compromised certain systems but did not achieve complete network control or access to every system. It could also mean they accessed particular types of data or particular network segments but not others. The term is somewhat ambiguous and designed to reassure the public while acknowledging that a serious compromise did occur at the level of critical systems as reported by Wiky.
How does the Singapore attack compare to Salt Typhoon attacks on U.S. telecoms?
Both UNC3886 and Salt Typhoon are believed to be Chinese cyber-espionage groups targeting telecommunications infrastructure globally. However, Salt Typhoon's attacks have been larger in scale, affecting dozens of U.S. carriers, and have included more aggressive data exfiltration and service disruption attempts. Salt Typhoon reportedly gained access to lawful intercept capabilities in some cases, potentially allowing large-scale communications interception. The Singapore attack appears to follow a similar pattern but hasn't reached the same magnitude of disruption as discussed by Industrial Cyber.
What should other telecom companies do to protect themselves?
Telecom companies worldwide should conduct comprehensive security audits focusing on perimeter defenses like routers and firewalls, implement network segmentation to prevent lateral movement, deploy advanced monitoring and detection systems, establish relationships with government agencies for threat reporting, participate in threat intelligence sharing communities, audit their supply chain to ensure vendors aren't compromised, and treat cybersecurity as a strategic priority requiring board-level attention and adequate resource allocation as reported by The Record.
Can similar attacks happen in other countries' critical infrastructure?
Yes, absolutely. The fact that UNC3886 has targeted telecommunications infrastructure in Singapore and elsewhere, and that similar groups like Salt Typhoon have targeted U.S. telecoms, demonstrates that this threat is global. Any country with telecommunications infrastructure can be targeted. Any critical infrastructure sector could be vulnerable to similar attacks if they don't implement robust security measures and maintain vigilant monitoring for suspicious activity as detailed by The Hacker News.
How did Singapore's government detect the attack if it was months-long?
The exact detection mechanism hasn't been publicly disclosed, but it likely involved a combination of security monitoring systems, forensic investigations, information shared by international intelligence partners, and threat intelligence about known UNC3886 activities. The detection probably came from suspicious network activity, unexpected systems behavior, or findings from a security assessment or incident response investigation as reported by The Record.
What role does attribution play in responding to cyberattacks?
Public attribution of cyberattacks to nation-states serves several purposes. It warns other organizations and countries to implement defensive measures against the same threat. It demonstrates to the domestic public that the government understands what happened and is responding. It signals to the attacking country that their operations are known and monitored. It can have diplomatic consequences and create costs associated with cyber operations. However, attribution alone doesn't prevent future attacks, especially from nation-states, because the strategic value of intelligence gathering typically outweighs the diplomatic costs as noted by Industrial Cyber.
What is a zero-day vulnerability and why is it valuable to attackers?
A zero-day vulnerability is a security flaw that hasn't been publicly disclosed and hasn't been patched by the software vendor. It's "zero-day" because the vendor has zero days of advance notice before the flaw is exploited. Zero-days are valuable to attackers because they represent flaws that defensive systems don't know how to protect against. Nation-states sometimes purchase zero-days on the black market or develop them internally to gain advantages against specific targets as detailed by The Hacker News.

Related Insights and Future Reading
The Singapore telecom attack illustrates how nation-state cyber operations are evolving and becoming more sophisticated. Similar attacks are occurring against critical infrastructure worldwide, targeting telecommunications, energy, water, and financial systems. Understanding these threats and implementing appropriate defensive measures is becoming increasingly important for organizations in every sector as reported by The Record.
The public acknowledgment of the attack and the attribution to China signal that governments are taking nation-state cyber threats seriously and are willing to publicly call out attacks rather than handling them quietly. This transparency approach may help deter future operations, though evidence suggests nation-states continue attacking regardless of public attribution because the strategic value of intelligence gathering remains high.
For security professionals and organizations managing critical infrastructure, the Singapore attack demonstrates the importance of staying current on threat intelligence, maintaining robust security fundamentals, assuming breach scenarios in planning, and building incident response capabilities that can activate quickly when attacks are detected.
The long-term strategic implications of these kinds of attacks extend beyond immediate cybersecurity concerns into broader questions about military deterrence, strategic stability, and the risks of cyber conflict escalation. As nations develop more sophisticated cyber capabilities and establish more persistent access to critical infrastructure, the risk that a future military conflict could be preceded or accompanied by devastating cyberattacks increases significantly.
Key Takeaways
- UNC3886, a Chinese cyber-espionage group, gained 'limited access' to critical systems at Singapore's four largest telecom companies (Singtel, StarHub, M1, and Simba Telecom) through months-long attack campaign using zero-day vulnerabilities and rootkits as reported by The Record.
- Nation-state attackers prioritize establishing long-term hidden persistence for intelligence gathering over immediate disruption or data theft, making detection and containment more difficult than criminal cyberattacks as noted by Industrial Cyber.
- Telecommunications infrastructure is strategically valuable to nation-states because it provides access to government, military, financial, and business communications, making these companies prime targets for espionage and potential wartime disruption as detailed by The Hacker News.
- The attack follows a broader pattern of Chinese cyber operations globally, including the larger Salt Typhoon campaign targeting U.S. telecom companies, suggesting coordinated strategy to map and penetrate critical infrastructure worldwide as discussed by Industrial Cyber.
- Organizations defending against nation-state threats should focus on fundamental security practices: network segmentation, comprehensive monitoring and logging, rapid incident response capabilities, and treating cybersecurity as strategic priority requiring board-level commitment and resources as reported by The Record.
Related Articles
- Polish Power Grid Breach: How Russian Hackers Exploited Default Credentials [2025]
- Privacy-Focused Home Office: 33 Essential Gadgets & Gear [2025]
- Mustang Panda's CoolClient Backdoor Evolution: What Security Teams Need to Know [2025]
- NymVPN v2026.1 Update: AmneziaWG & Censorship Resistance Guide [2025]
- Supreme Court Hacking Case: What the Tennessee Breach Reveals [2025]
![China-Backed Hackers Target Singapore Telecoms: What You Need to Know [2025]](https://tryrunable.com/blog/china-backed-hackers-target-singapore-telecoms-what-you-need/image-1-1770741455237.jpg)



