Supreme Court Hacking Case: What the Tennessee Breach Reveals [2025]
January 2025 brought a sobering reality check for federal cybersecurity. A 24-year-old from Springfield, Tennessee, admitted to repeatedly breaking into the most powerful court system in America. Not once. Not a few times. Twenty-five different unauthorized accesses between August and October 2023.
Let that sink in. The institution that interprets the Constitution, that decides cases affecting hundreds of millions of Americans, had its secure filing system compromised by someone still young enough to not remember the original iPhone launch.
This isn't just another hacking story. It's a window into how government cybersecurity actually works (or doesn't work), why institutions struggle to protect themselves against determined attackers, and what patterns we're seeing across federal agencies.
In this article, I'm going to break down what happened, why it matters, and what it tells us about the state of government infrastructure security right now. Because if the Supreme Court can be breached, honestly, anywhere can.
TL; DR
- The breach: A 24-year-old from Tennessee gained unauthorized access to the Supreme Court's electronic filing system at least 25 times over three months in 2023
- What was accessed: Prosecutors haven't publicly disclosed what information was obtained, leaving critical questions unanswered
- The pattern: This is the latest in a series of breaches hitting federal court systems, including a 2023 Russian-attributed attack on federal court records
- The vulnerability: Federal agencies continue to struggle with basic cybersecurity hardening, legacy systems, and inadequate threat detection
- The implications: If courts aren't secure, what does that mean for judicial independence, case confidentiality, and public trust in the system?

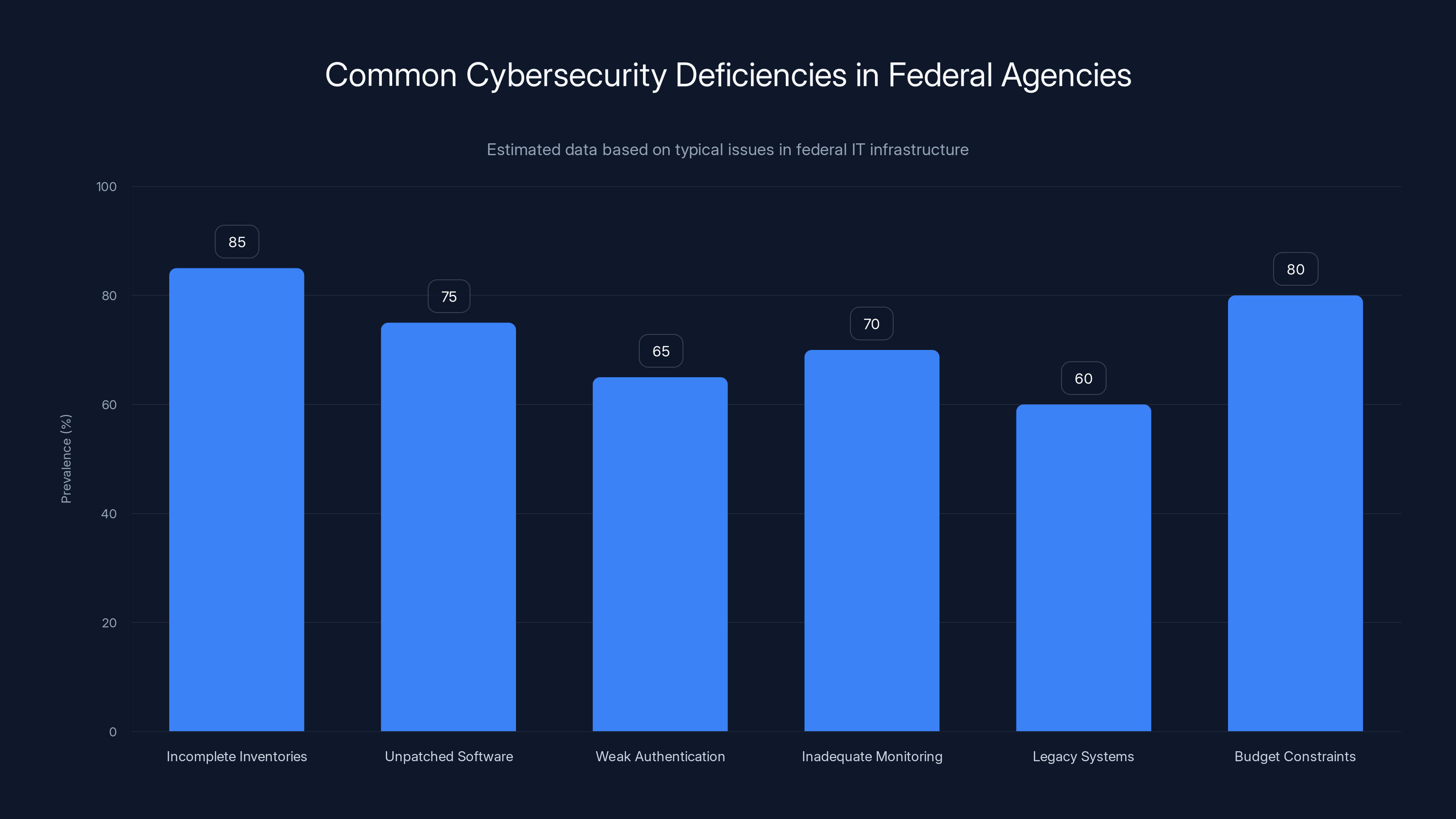
Estimated data shows that incomplete inventories and budget constraints are the most prevalent cybersecurity issues in federal agencies, affecting over 80% of them.
The Breach: What Actually Happened
Nicholas Moore, 24, accessed the Supreme Court's computer systems without authorization on 25 separate occasions between August and October 2023. According to court documents, he "intentionally accessed a computer without authorization" and "thereby obtained information from a protected computer."
That's the formal legal language. Here's what it actually means: someone found a way into a secure government system and came back dozens of times over three months. That's not a one-off lucky exploit. That's reconnaissance. That's repeated access. That's knowing you can get back in.
The fact that he was able to repeat this access 25 times without being detected raises massive red flags about the Supreme Court's monitoring infrastructure. Most mature security operations centers would flag unusual access patterns after the second or third anomaly. Twenty-five times suggests either the logging wasn't comprehensive, the alerting wasn't configured, or nobody was watching the alerts.
The details about exactly what Moore accessed remain classified or undisclosed. The government hasn't said whether he stole case files, looked at sealed documents, accessed attorney information, or something else entirely. This opacity itself is a problem. The public has a right to know what information potentially touched those compromised systems.
According to the charging documents, Moore's plea is scheduled for guilty on a charge of unauthorized computer access under the Computer Fraud and Abuse Act. The penalties for this crime can range from months to years in prison, depending on what exactly was accessed and the intent behind it.
Why This Matters: The Trust Problem
The Supreme Court isn't just another government agency. It's the final arbiter of constitutional disputes. People file cases worth millions of dollars. Attorneys submit confidential strategies. Judges' draft opinions sit in those systems before publication.
If the filing system is compromised, what happens to sealed documents? What about attorney-client privilege? What if an attorney's confidential brief ended up in the hands of opposing counsel through this breach?
This goes beyond mere data theft. It strikes at the foundation of the judicial system. How can judges maintain impartiality if there's doubt about information security? How can attorneys trust the system with sensitive case strategy?
Think about a Supreme Court case involving national security, or one with massive corporate stakes. Attorneys pour months of work into petitions. If that intellectual property leaked to competitors, the damage would be catastrophic. If sealed documents became public, it could compromise ongoing investigations or harm privacy interests.
The Supreme Court, in particular, handles cases that shape American law for generations. A breach here isn't like compromising a Motor Vehicle Department database. The consequences ripple through the entire legal system.
The government has been surprisingly quiet about what was actually at risk. That silence breeds speculation and undermines public confidence. Transparency about the severity would be more constructive than the current vague official statements.
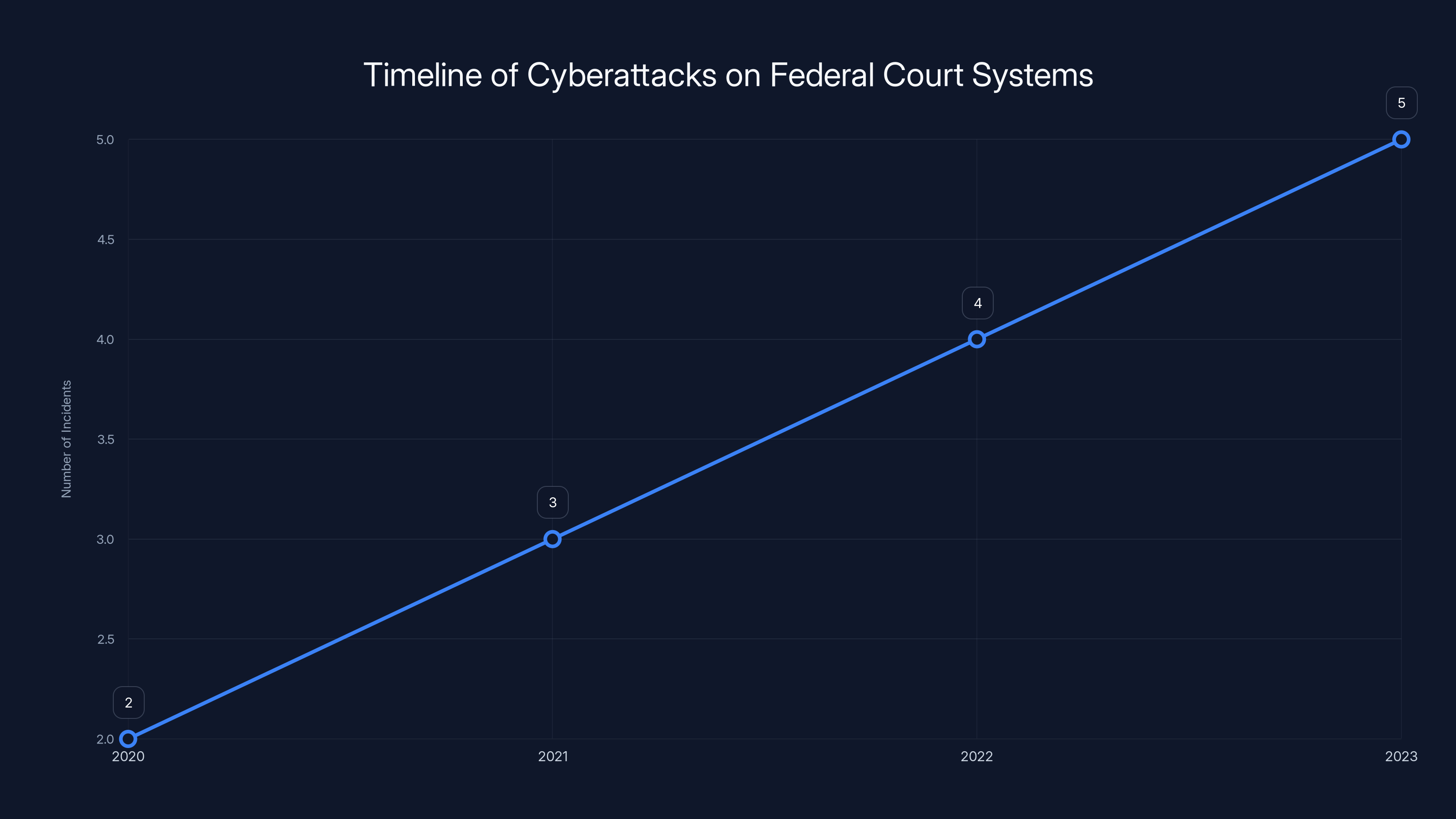
The number of cyberattacks on federal court systems has increased steadily from 2020 to 2023, highlighting growing vulnerabilities in legacy systems. (Estimated data)
The Pattern: Federal Court Systems Under Fire
This isn't an isolated incident. The Supreme Court breach is the latest in a series of cyberattacks hitting federal judicial infrastructure. Look at the timeline.
In August 2023, the Administrative Office of the U. S. Courts disclosed a cyberattack on its electronic court records system. Russian state-sponsored hackers were blamed. This is the organization that oversees the entire federal judiciary, managing case management systems used by district courts across all 94 federal judicial districts.
That attack was more serious in scope. It compromised systems used across the entire federal court system, not just the Supreme Court. The Administrative Office said it "strengthened its cybersecurity defenses" following the breach, which is bureaucratic-speak for "we found out we weren't as secure as we thought."
Before that, there were other incidents. Ransomware targeting state court systems. Data breaches at local courthouses. Each incident reveals the same pattern: legacy systems, insufficient monitoring, delayed detection.
Why does this keep happening? Federal agencies often run on technology from 15, 20, even 30 years ago. Judges and court staff aren't necessarily tech-savvy. Budget constraints limit cybersecurity investments. And ironically, the very security practices that protect sensitive cases sometimes work against comprehensive monitoring. Some systems are so air-gapped for security reasons that detecting intrusions becomes harder.
The pattern also shows that when breaches are discovered, the government is slow to communicate. Moore's unauthorized access happened in 2023. The charges weren't made public until 2026. During that gap, there was uncertainty about whether information security had been compromised and what information was at risk.
How Moore Got In: The Technical Reality
The court documents don't explain the specific vulnerability or attack vector Moore used. That's by design—publishing detailed information about how to breach government systems would be irresponsible. But we can infer some things.
Moore was 24. Probably smart about technology. Determined enough to research the target and attempt unauthorized access multiple times. He either found a vulnerability in the filing system itself, compromised credentials (perhaps through phishing or password reuse), or exploited some misconfiguration in the system architecture.
Given that he was able to gain access 25 times, it wasn't a complex, sophisticated attack that would be detected if you looked for it. Instead, it was probably something that exploited a known, unpatched vulnerability or relied on weak security practices that most organizations with basic security hygiene would have already eliminated.
This is the uncomfortable truth about government cybersecurity. You don't always need nation-state-level techniques to breach federal systems. Sometimes, competent attackers with basic technical knowledge can find ways through because the fundamentals weren't handled properly.
The National Institutes of Standards and Technology, or NIST, publishes a cybersecurity framework that includes basic practices: maintain an inventory of systems, keep software updated, monitor for unauthorized access, enforce strong authentication. These aren't novel concepts. They're table stakes. Yet federal agencies struggle with implementation at scale.
Moore's case suggests the Supreme Court either didn't have these basics in place, or had them in place but wasn't monitoring effectively. Repeated unauthorized access that goes undetected for months indicates logging and alerting weren't configured properly.
It's worth noting that even sophisticated organizations struggle with this. But the Supreme Court isn't a startup balancing speed and security. It's a government institution with significant resources and stakes. The gap between what should be in place and what apparently was in place is alarming.

Detection and Response: The Painful Timeline
Here's a critical question nobody's answered publicly: how was Moore caught?
Was he detected through network monitoring? Did the Supreme Court eventually notice unusual access patterns? Did law enforcement investigation lead back to him? Did he leave digital footprints elsewhere that were traced back to the Supreme Court breach?
The charging documents don't say. But the timeline is telling. Accesses occurred August through October 2023. Charges weren't filed until much later. That gap suggests detection and investigation took considerable time.
In modern security operations, if you have proper monitoring, you should detect repeated unauthorized access within hours or days, not months. The fact that this went undetected for the duration of the breach window raises questions about whether monitoring was in place at all.
Once detected, response should have been swift: isolate affected systems, preserve forensic evidence, notify leadership, assess what was compromised, and bring in law enforcement if a crime had been committed. The wheels of federal justice move slowly, so delays in charging are somewhat expected. But the original detection delay is the real problem.
This has implications for all federal agencies. If detection takes months, how many other breaches are happening right now that nobody knows about yet? How many attackers are accessing federal systems repeatedly without triggering alerts?
The security community sometimes talks about the "dwell time," the average amount of time an attacker spends inside a system before being detected. For sophisticated nation-state actors targeting major corporations, dwell time averages months. For government agencies, it can be even longer.
The Supreme Court breach, with repeated access over three months, fits this pattern. If the institution can't detect someone accessing its systems 25 times in a quarter, the dwell time is measured in months at minimum.
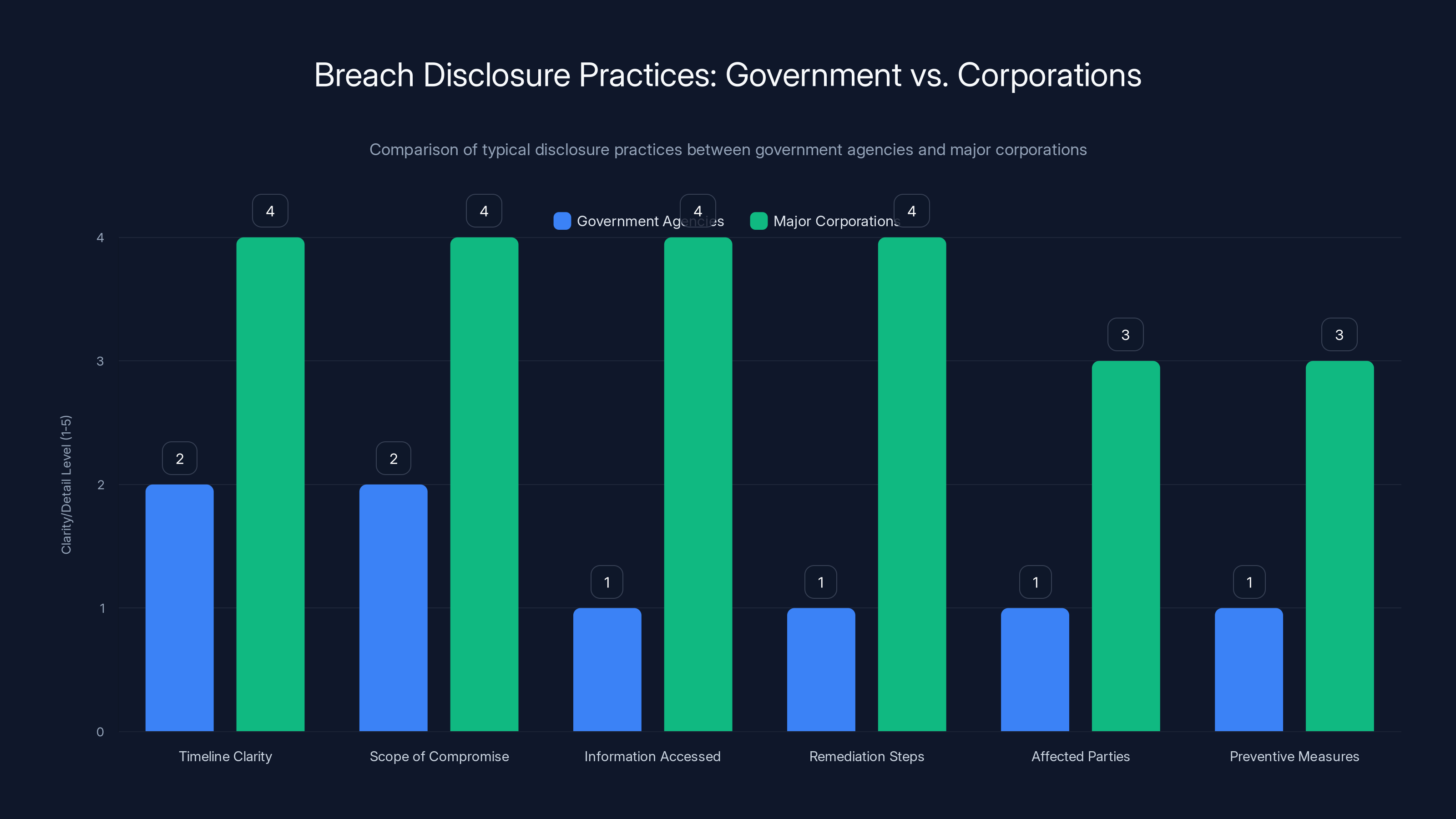
Major corporations typically provide more detailed breach disclosures than government agencies, due to stricter legal requirements. Estimated data.
Lessons from History: Previous Government Breaches
The Supreme Court breach isn't the first time a federal institution has been compromised. Learning from past incidents reveals patterns in how government handles cybersecurity failures.
The Office of Personnel Management breach in 2015 compromised background investigation files for 21.5 million people. The breach went undetected for months. When discovered, it was a massive scandal. The OPM director resigned. Congress held hearings. But systemic improvements took years to implement.
The Solar Winds breach in 2020 compromised federal agencies including Treasury, Justice, and State departments through a software supply chain attack. That was more sophisticated, harder to defend against without specific intelligence about the threat. But it also revealed that federal agencies weren't monitoring their enterprise software for anomalous behavior.
The Colonial Pipeline ransomware attack in 2021 shut down fuel distribution to the entire East Coast. It was a private company, but it demonstrated how critical infrastructure, whether government or private, was unprepared for sophisticated cyberattacks.
Each of these breaches prompted reviews, reports, and recommendations. The Cybersecurity and Infrastructure Security Agency, or CISA, publishes incident reports and best practices. Federal agencies have access to these resources. Yet the pattern continues.
Why? Partly because cybersecurity is expensive and boring compared to mission-critical work. Partly because federal budgeting doesn't reward security investments with obvious immediate payoff. Partly because government moves slowly, and by the time you implement lessons from 2015, it's 2025 and the threat landscape has evolved.
The Legal Framework: Computer Fraud and Abuse Act
Moore was charged under the Computer Fraud and Abuse Act, or CFAA, one of the primary federal cybercrime statutes. Passed in 1986, it makes it illegal to access computers without authorization.
The law sounds straightforward. You can't hack computers. But in practice, the CFAA is famously broad and has been controversial in cybersecurity circles for decades.
The statute defines unauthorized access as accessing "a computer without authorization" or "in excess of authorized access." That second part is particularly problematic. If you have legitimate access to a computer for one purpose, but access files for a different purpose, does that violate the CFAA?
Courts have grappled with this question. Some interpretations are extremely broad. Others are more narrow. The circuit courts don't all agree.
In Moore's case, the application is straightforward. He accessed the Supreme Court system with no authorization at all. Not a question of exceeding authorized access. Just flat-out unauthorized intrusion.
The CFAA allows for both criminal and civil penalties. Prosecutors can pursue criminal charges, which can result in imprisonment and fines. The penalties depend on the circumstances and what information was accessed. If Moore accessed information containing medical records, financial information, or national defense information, penalties increase significantly.
The guilty plea means Moore is accepting responsibility. No trial, no jury. Sentencing will happen later, where the judge will consider the severity of the breach, Moore's age and background, his cooperation with authorities, and any victim impact statements from the Supreme Court.
Given Moore's age and the fact that his case is being handled seriously by federal prosecutors, he'll likely face real prison time. But the specifics depend on what a judge believes is appropriate punishment and deterrence.
What Information Was at Risk?
This is the biggest unanswered question. The government hasn't disclosed what Moore accessed during his 25 unauthorized sessions.
Possibilities range from publicly available information he could have accessed anyway, to highly sensitive documents that should never have been accessible through his method of entry.
Consider what actually sits in the Supreme Court's filing system:
Public case files and dockets are supposed to be publicly accessible. If Moore only accessed those, he technically got information that's already public, but he accessed it through unauthorized means. That's still illegal, but it's less damaging than if he accessed sealed documents or confidential information.
Sealed documents are another category. These are court filings restricted from public access to protect trade secrets, personal information, ongoing investigations, or privacy interests. If Moore accessed sealed documents, that's a serious violation.
Then there's attorney contact information, case strategy, judge communications, internal court memos, and administrative information. Depending on what Moore obtained, the impact ranges from a privacy violation to a threat to judicial independence.
The Supreme Court likely conducted a forensic investigation to determine what was accessed. That information was probably shared with Congress in classified briefings. But the public-facing disclosure has been minimal.
This opacity is a problem. The public has a right to know if their personal information was compromised. Attorneys whose cases were involved have a right to know if confidential information was breached. The courts themselves need to rebuild public trust by being transparent about what happened and what they're doing to prevent it.

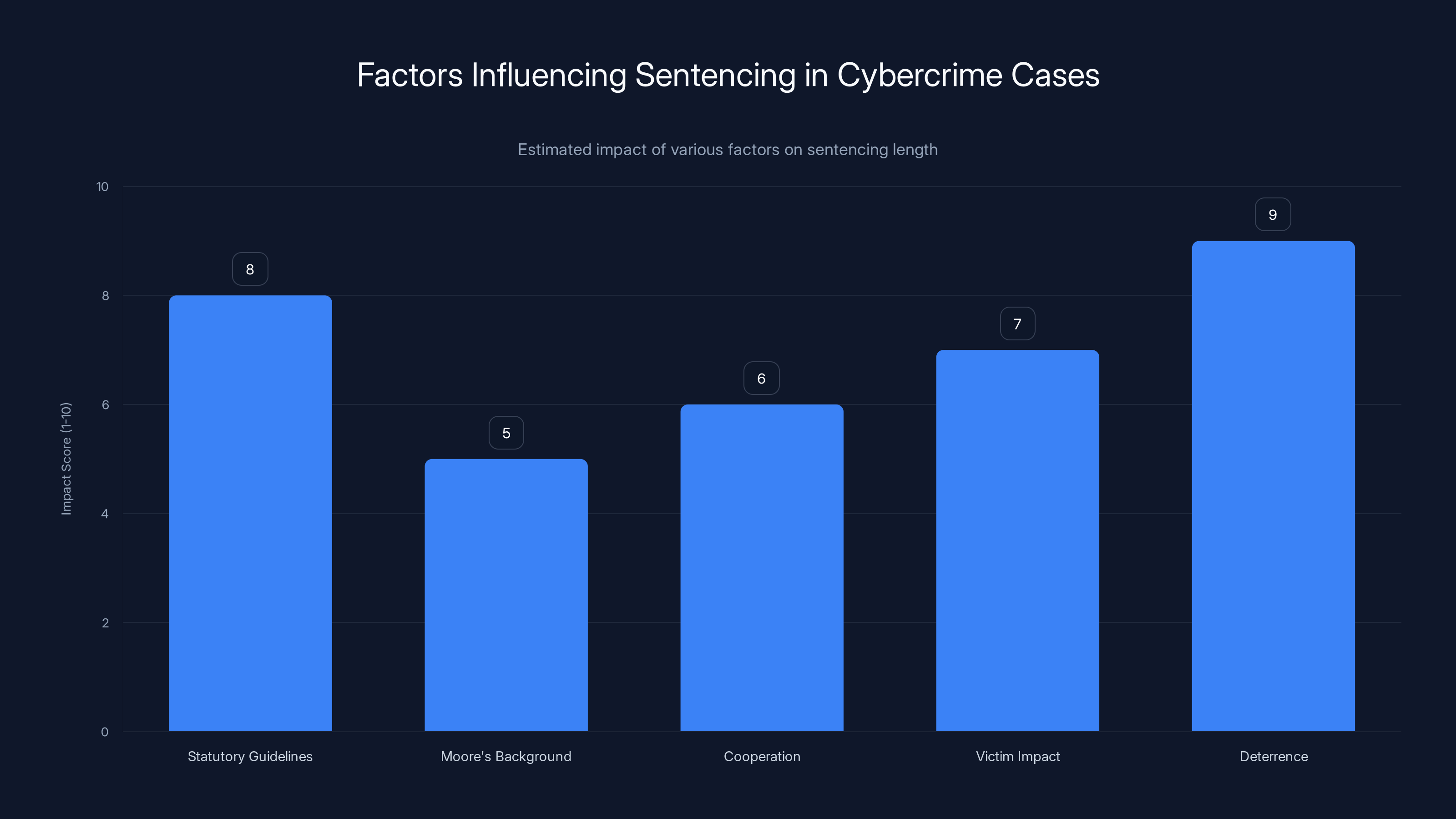
Estimated data: Deterrence and statutory guidelines have the highest impact on sentencing length in cybercrime cases, reflecting the seriousness of the offense and the need to prevent future crimes.
System Architecture: Why Courts Are Vulnerable
To understand why the Supreme Court's filing system was vulnerable, you need to understand how court systems are built.
Many federal courts run on systems built decades ago. The Public Access to Court Electronic Records, or PACER, system is the federal case management and public access system. PACER was first introduced in the 1980s. Parts of it have been updated, but the underlying architecture is ancient by technology standards.
Legacy systems have known disadvantages for security. They often lack modern authentication mechanisms like multi-factor authentication. They have limited logging capabilities, so unauthorized access can't be detected retroactively. They're hard to patch because patches might break other critical functions they depend on.
Federal courts also operate with constraints that make security harder. Cases with sealed documents require air-gapped systems or at least segregated networks so that highly sensitive information isn't on the same network as public-facing systems. This architectural separation actually makes monitoring harder because you need separate logging and alerting for different network segments.
Then there's the human factor. Judges and court staff aren't necessarily technologically sophisticated. Security policies that make sense to security professionals might be confusing or inconvenient to people who just want to do their job. When security gets in the way, people find workarounds. Those workarounds become vulnerabilities.
The Supreme Court likely has significant resources to invest in security. But even with resources, upgrading legacy systems used across the entire federal judiciary is a massive undertaking. You can't just shut everything down and replace it. Cases are active. Decisions need to be published. The system has to be available.
Moore's ability to access the system 25 times without detection suggests that either the monitoring wasn't in place, wasn't comprehensive, or the alerts weren't being watched. All three are solvable problems, but they require investment and operational discipline.
Incident Disclosure: What Went Right and Wrong
How the Supreme Court (or federal prosecutors on its behalf) handled the public disclosure of this breach reveals both good and bad practices.
Good: The case was eventually disclosed. Government agencies sometimes try to quietly handle security incidents without public announcement. Here, the charges and guilty plea became public record, so journalists could report on them.
Bad: The disclosure was vague. No timeline of when the breach was discovered. No details about what information was accessed. No explanation of remediation efforts. This creates a vacuum of information that speculation rushes to fill.
Bad: The delay between the unauthorized access (August-October 2023) and charges becoming public was long enough that nobody knew this had happened for months. Organizations dealing with the Supreme Court had no opportunity to assess their own risk or take protective measures.
Good practice in breach disclosure includes clear timeline, scope of compromise, what information was accessed, affected individuals or organizations, steps being taken to prevent recurrence, and how to get more information. The Supreme Court's disclosure checked few of these boxes.
For comparison, when major corporations suffer breaches, they usually publish detailed disclosure statements. Not because they want to, but because state and federal law requires it. Government agencies have fewer such requirements, which is why disclosure tends to be minimal.
The security research community often criticizes government transparency on breaches. The argument is that the public deserves to know when government systems they depend on have been compromised. The government's argument is that detailed disclosure could reveal vulnerabilities that are still being fixed, or could provide a roadmap for other attackers.
There's tension between these positions, but most cybersecurity professionals lean toward transparency. Even vague disclosure ("our system was breached, we're investigating, affected parties will be notified") is better than no disclosure.

The Broader Security Problem: Federal IT Infrastructure
The Supreme Court breach is a symptom of a larger problem in federal IT infrastructure. Across federal agencies, cybersecurity remains an ongoing challenge despite years of investments and initiatives.
The Office of Management and Budget publishes annual cybersecurity reports on federal agencies. These reports consistently show that many agencies fail basic security controls. Out of 24 major federal agencies, most have been categorized as having significant cybersecurity deficiencies.
Problems include:
Incomplete inventories: Many agencies don't have complete visibility into what systems they operate. You can't secure systems you don't know you have.
Unpatched software: Known vulnerabilities go unfixed for months or years. Every day a patch sits uninstalled is a day an attacker could exploit it.
Weak authentication: Passwords without multi-factor authentication are still common. Passwords are cracked or phished. Multi-factor authentication significantly increases attack difficulty.
Inadequate monitoring: Even agencies with monitoring infrastructure often don't have staff to watch the alerts. Alerts fire, nobody reviews them, intrusions go undetected.
Legacy systems: Older systems lack security features, patch availability, and support. But they're critical to operations so they can't be shut down.
Budget and resource constraints: Cybersecurity requires ongoing investment. It's not a one-time purchase and done. Training, tools, staff, upgrades, and incident response all cost money. Federal budgeting doesn't always reflect the true cost of security.
The Supreme Court breach reflects these systemic problems. A determined attacker (even a young, skilled amateur) was able to access a federal system repeatedly. Detection took months. Disclosure took even longer.
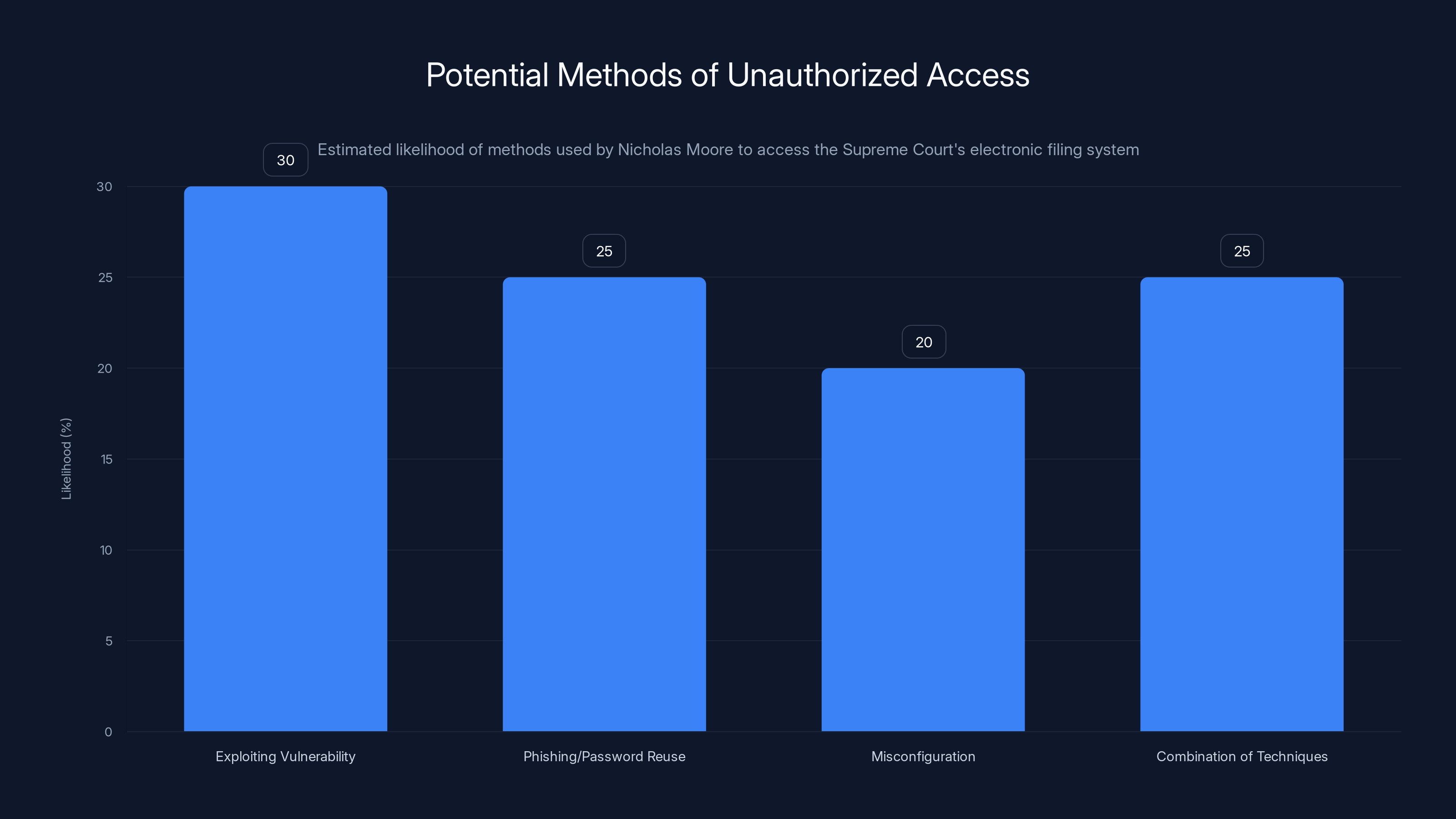
Estimated data suggests multiple methods could have been used by Nicholas Moore, with exploiting vulnerabilities and a combination of techniques being the most likely.
Implications for Judicial Independence
The Supreme Court breach raises philosophical questions about judicial independence and public trust in the institution.
Judicial independence is the principle that courts operate free from political influence or interference. Judges should be able to make decisions based on law and facts, not fear or favor.
Cybersecurity is relevant to judicial independence because if court systems are vulnerable to compromise, then the integrity of judicial decisions is at risk. What if an attorney with access to opposing counsel's brief strategy had gained unfair advantage? What if a judge's draft opinion had been leaked before publication?
The public also needs to trust that the judicial system is secure. If citizens believe court systems are vulnerable to hackers, they lose confidence in the institution. That erosion of trust weakens the courts' authority.
The Supreme Court's role as final arbiter of constitutional disputes makes this even more critical. Decisions from the Court shape American law for generations. If there's doubt about the security of those decisions, it undermines the legitimacy of the decisions themselves.
Republicans and Democrats might disagree on particular Supreme Court decisions, but both sides should agree that the Court's systems need to be secure and trustworthy. A breach that potentially compromised the integrity of decisions would be a crisis for the institution.

What the Supreme Court Needs to Do
Responding to the Moore breach requires both immediate and long-term actions.
Immediate actions:
- Complete forensic analysis of what was accessed and notify affected parties
- Audit all user accounts and access permissions to eliminate unnecessary access
- Implement multi-factor authentication across all systems, if not already done
- Review logs from the breach period and any surrounding time to identify other anomalies
- Conduct a tabletop exercise simulating breach detection and response to find gaps in current processes
- Engage the FBI and CISA to conduct independent security assessments
Medium-term actions:
- Implement comprehensive logging and monitoring with dedicated staff to review alerts
- Upgrade authentication and access control systems to modern standards
- Conduct a network architecture review to identify air-gapping opportunities for high-sensitivity data
- Develop and test an incident response plan specifically for unauthorized access scenarios
- Establish regular security testing and penetration testing by external experts
- Implement a security awareness training program for all staff
Long-term actions:
- Plan and execute a modernization of legacy systems with security built in from the start
- Establish a Chief Information Security Officer position with adequate authority and resources
- Work with CISA and other federal agencies to share threat intelligence and best practices
- Publish annual security reports showing metrics on vulnerability patching, monitoring coverage, and incident response
- Develop recruiting and retention strategies for cybersecurity talent (federal salaries are often lower than private sector)
The Supreme Court likely has plans for many of these already. But the level of public transparency will determine whether public trust is restored.
Federal Agency Response: CISA and the NSA
The Cybersecurity and Infrastructure Security Agency, part of the Department of Homeland Security, is the federal government's cybersecurity coordinator. CISA works with agencies to improve security and responds to major incidents.
The National Security Agency, particularly its Cybersecurity Collaboration Center, also advises federal agencies on security practices.
Both organizations publish advisories about threats and vulnerabilities. CISA publishes alerts about active cyberattacks targeting federal agencies. The NSA publishes security requirements for federal systems.
In response to the Supreme Court breach and the earlier attack on the Administrative Office of the U. S. Courts, these agencies likely increased focus on court system security. CISA may have issued new directives about authentication, monitoring, and vulnerability management specifically for judicial systems.
But the gap between publishing advisories and getting all federal agencies to implement the recommendations remains large. Many agencies lack the expertise, budget, or political will to implement security recommendations quickly.
The Supreme Court breach might be the catalyst for more aggressive federal action to improve court system security. A breach of the nation's highest court is high-visibility enough that Congress might allocate specific funding for upgrades.

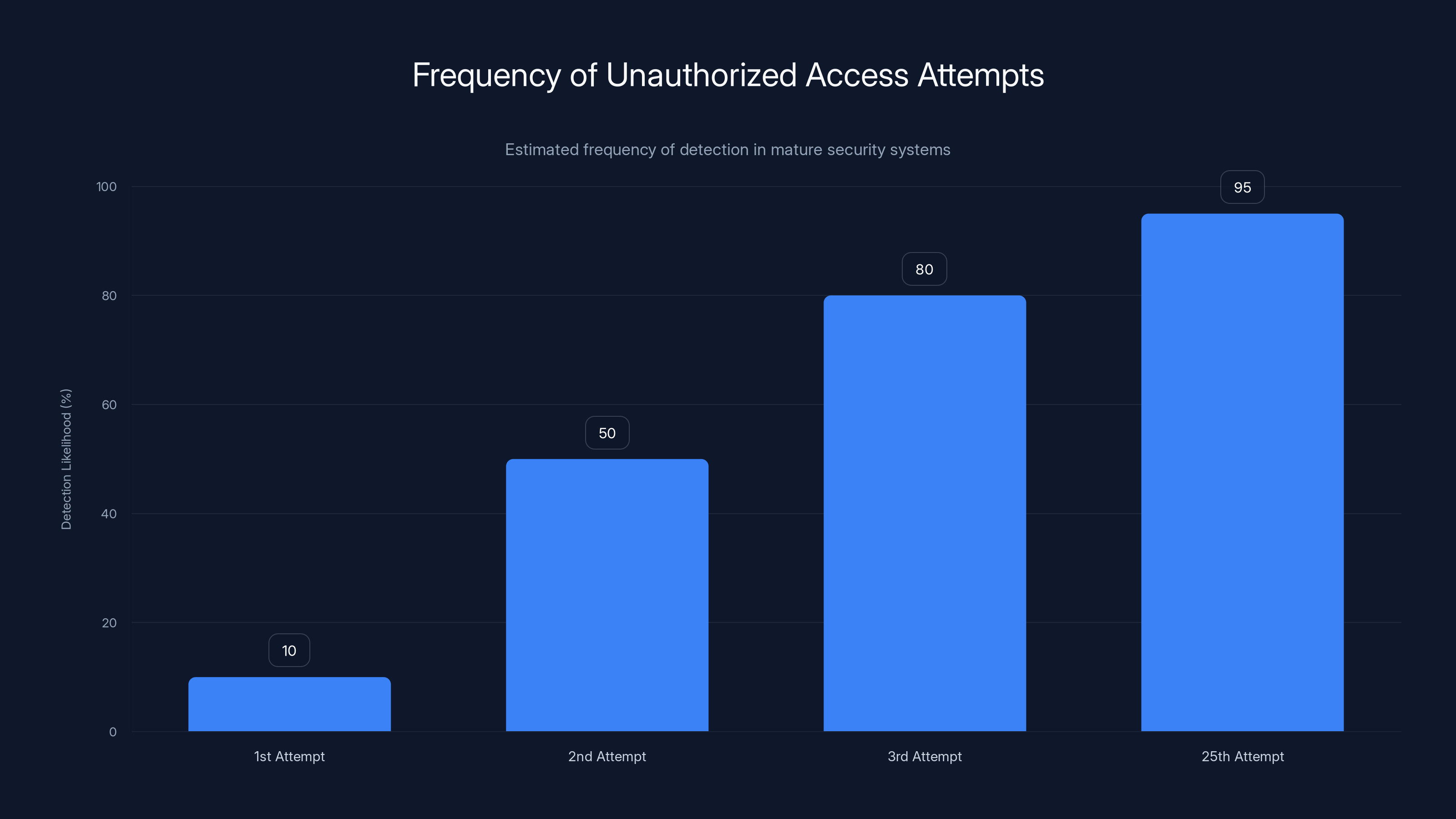
Estimated data shows that mature security systems would likely detect unauthorized access by the 3rd attempt, highlighting a significant gap in the Supreme Court's monitoring capabilities.
Lessons for Private Sector Security
While the Supreme Court is a government institution, the breach has lessons for private sector organizations handling sensitive information.
Legacy systems are a liability: The older your infrastructure, the harder it is to secure. If you're running 20-year-old systems managing critical data, you're taking on significant risk. Modernization is expensive, but the cost of a breach is higher.
Detection requires investment: You can't detect intrusions if you're not monitoring. Logging and alerting infrastructure costs money and requires people to actually watch the alerts. Budget for both.
Repeated access indicates process failure: If an attacker can access your system 25 times before you notice, your monitoring and alerting is inadequate. The Supreme Court's experience suggests even sophisticated institutions can have blind spots.
Transparency builds trust: Organizations that are transparent about breaches, what information was compromised, and what they're doing to prevent recurrence recover public trust faster than those that are secretive.
Insider threat is real: Not all breaches are external. Sometimes employees or contractors exceed their authorized access. Implementing the principle of least privilege (giving people only the access they need) reduces this risk.
Many of these lessons are well-known in security circles. The Supreme Court breach is a reminder that even sophisticated institutions struggle with consistent implementation.
The Criminal Case: What's Next
Moore's guilty plea means he's accepting criminal responsibility. The next step is sentencing.
At sentencing, the judge will consider several factors:
Statutory sentencing guidelines: The Computer Fraud and Abuse Act allows for imprisonment for a term of years. The specific sentence range depends on what information was accessed and what harm resulted.
Moore's background: His age, education, employment history, and any prior criminal record will be considered. A 24-year-old first-time offender might receive leniency compared to someone with a history of crimes.
His cooperation: If Moore cooperated with investigators and prosecutors, that can result in a reduced sentence. Cooperation might include disclosing his methods, explaining how he gained access, and helping prosecutors understand what information was compromised.
Victim impact: The Supreme Court and any affected parties might file victim impact statements explaining how the breach harmed them.
Deterrence: Judges often consider whether a sentence will deter the defendant and others from similar crimes. A harsh sentence sends a message that cybercrimes against federal institutions won't be tolerated.
Sentencing in major federal cybercrime cases typically results in prison time, often measured in years rather than months. Moore's age and first-time offender status might mitigate that somewhat, but accessing the Supreme Court's systems isn't a minor crime.

Broader Context: Youth and Cybercrime
Moore's age (24) raises questions about why young, intelligent people turn to cybercrime.
The cybersecurity field actually needs talented young people. The industry has a major shortage of skilled professionals. If Moore's skills are real, he could have had legitimate career opportunities in cybersecurity, penetration testing, or security research.
Some young hackers start with curiosity. They want to learn how systems work, and accessing unauthorized systems becomes a way to scratch that itch. Some move into legitimate security careers. Others get caught and face criminal consequences.
The case of Moore is a cautionary tale. Accessing government systems is a federal crime with serious consequences. Even if done out of curiosity rather than malice, the legal penalties are severe.
There's also a broader question about security culture in the hacking and security community. Some hackers view unauthorized access as acceptable if no information is stolen or modified. Law enforcement and prosecutors don't share that view. Under the CFAA, accessing a computer without authorization is illegal regardless of what you do once you're inside.
For young people interested in cybersecurity, legitimate paths exist: bug bounty programs, authorized penetration testing jobs, academic programs in cybersecurity, and certifications like CISSP or CEH that lead to security careers.
Moore's breach raises the question of whether he was aware of these legitimate alternatives, or if he felt excluded from the mainstream security community for some reason. Those details might emerge during sentencing, when biographical information is typically disclosed.
International Implications: Court Systems Worldwide
The Supreme Court breach isn't unique to the United States. Court systems worldwide face similar cybersecurity challenges.
Courts in the United Kingdom, Canada, and Australia have also experienced cyberattacks. Some have resulted in system outages that delayed trials. Some have compromised case files.
The pattern is similar globally: courts operate with limited IT resources, often use legacy systems, and struggle to prioritize security against operational demands.
This creates an international concern. If attackers discover methods to compromise one country's court system, those methods might work against another country's similar systems. Information about vulnerabilities spreads through underground forums and among professional hackers.
There's also concern about state-sponsored actors targeting courts in adversary nations. The 2023 Russian attack on the Administrative Office of the U. S. Courts was attributed to Russian intelligence. Other nations might engage in similar targeting to gather intelligence or disrupt judicial processes.
International cooperation on court security would strengthen all systems. Sharing best practices, threat intelligence, and lessons learned would help courts worldwide improve. But that cooperation doesn't exist to the degree it does in other critical infrastructure sectors.

The Future: Strengthening Institutional Security
The Supreme Court breach reveals vulnerabilities that extend beyond that single institution. The entire federal court system, and many private organizations, face similar risks.
Addressing these risks requires sustained commitment, adequate funding, skilled personnel, and modern infrastructure. It's not glamorous work. Security doesn't win cases or move the nation forward. But without security, the other work falls apart.
The next few years will reveal whether this breach catalyzes meaningful change or becomes just another incident that's investigated and then forgotten until the next breach happens.
The Supreme Court's response will signal how seriously federal institutions take cybersecurity. If funding is allocated, systems are modernized, and transparency is improved, it suggests real change. If the incident fades from headlines and basic security practices remain unchanged, the pattern will continue.
For other institutions managing sensitive information, the lesson is clear: security vulnerabilities aren't theoretical risks. They're real, they're exploitable, and they require serious ongoing attention.
FAQ
What exactly is the Supreme Court's electronic filing system?
The Supreme Court's electronic filing system is a computer network that allows attorneys to submit cases, briefs, and other legal documents electronically rather than by paper mail. It also houses case files, dockets, and other court records. While parts of this system are public-facing (allowing public access to published decisions), other parts contain sealed documents and confidential information restricted from public access.
How did Nicholas Moore gain access to the filing system?
The exact method of access hasn't been publicly disclosed by prosecutors or the court. It could have involved exploiting a vulnerability in the system itself, compromising credentials through phishing or password reuse, exploiting a misconfiguration, or using a combination of techniques. The key point is that he was able to repeat the access 25 times, suggesting it wasn't a one-time lucky exploit but rather knowledge of a persistent weakness.
What information might have been compromised in the breach?
The government has not publicly disclosed what specific information Moore accessed during his 25 unauthorized sessions. Possibilities range from publicly available case information (which would be less damaging since it's already public, though the unauthorized access method is still illegal) to sealed documents, attorney information, judge communications, or other sensitive materials. The lack of public disclosure leaves significant uncertainty about the breach's scope.
Why did it take so long for Moore to be charged after the breach occurred?
Moore's unauthorized access occurred between August and October 2023, but charges weren't made public until January 2026. This delay likely reflects the time needed for detection, forensic investigation, gathering evidence, and coordinating with law enforcement. It also shows that detection didn't happen immediately during the breach period, raising questions about the court's monitoring infrastructure.
What are the potential consequences for Nicholas Moore?
Under the Computer Fraud and Abuse Act, penalties for unauthorized computer access can range from months to several years in prison, depending on what information was accessed and what harm resulted. Given that Moore accessed the Supreme Court's systems (critical infrastructure) multiple times, sentencing will likely result in significant prison time. His age, cooperativeness with prosecutors, and lack of prior criminal history might mitigate the sentence somewhat, but federal judges typically impose meaningful prison sentences for such cases.
What should organizations do to prevent similar breaches?
Organizations can reduce breach risk through: implementing multi-factor authentication, maintaining comprehensive logging and monitoring of system access, keeping software patched and updated, conducting regular security assessments and penetration testing, limiting user access to only what's necessary for their role, training staff on security best practices, developing and testing incident response plans, and investing in cybersecurity expertise and infrastructure. The principle of assuming breaches will happen and preparing for detection and response is critical.
How does this breach affect public trust in the Supreme Court?
Cyber breaches of government institutions undermine public confidence in their integrity and security. For the Supreme Court specifically, a breach raises questions about whether confidential case information, attorney strategy, or judicial communications might have been compromised. This matters because the public needs to trust that the Court's decisions are made independently and confidentially. Transparent disclosure of what happened and what's being done to prevent recurrence is essential for rebuilding trust.
Are court systems nationwide at risk for similar breaches?
Yes. Many federal courts use similar legacy systems and face comparable security challenges. The fact that the Administrative Office of the U. S. Courts (which oversees federal judicial systems nationwide) was also attacked in 2023 suggests systemic vulnerabilities across the federal judiciary. Even state and local court systems face similar risks, with limited IT budgets and aging infrastructure making them attractive targets for attackers.

Conclusion
The Supreme Court hacking case involving Nicholas Moore is more than just a cybercrime story. It's a window into how even the most prestigious American institutions struggle with cybersecurity fundamentals.
A 24-year-old gained unauthorized access to the nation's highest court's filing system on at least 25 separate occasions. Detection took months. The public disclosure was minimal and vague. The information compromised remains unknown. These aren't just operational failures; they're indicators of a deeper problem in how federal institutions approach security.
The breach reflects larger patterns visible across government IT infrastructure. Legacy systems that lack modern security features. Insufficient monitoring and alerting. Budget constraints that prioritize operations over security. Slow coordination between agencies and with law enforcement. And ultimately, the difficulty of maintaining robust security across complex, mission-critical systems while also ensuring those systems remain operational.
But this case also illustrates that breaches of critical institutions aren't inevitable. They result from specific failures that are correctable. Multi-factor authentication would make repeated unauthorized access harder. Comprehensive logging and monitoring would detect intrusions much faster. Regular security assessments would identify vulnerabilities before attackers find them.
The Supreme Court has the resources to implement these measures. Whether it does so, and whether those investments are sustained over time through budget cycles and administrative changes, will determine whether Moore's case becomes a catalyst for genuine security improvements or just another incident that fades from headlines.
For other organizations managing sensitive information, the lesson is straightforward: cybersecurity isn't a one-time project or budget line item. It's an ongoing commitment to protecting assets, detecting compromise, and responding effectively. The Supreme Court's experience demonstrates that even institutions with significant resources and stakes can fall short of that commitment. But it also demonstrates that recognizing and addressing security gaps is possible, if taken seriously.
The coming months will reveal whether the Supreme Court views this breach as a wake-up call or a manageable incident. The answer will have implications for public trust, judicial independence, and the broader federal government's approach to cybersecurity. Because if the Supreme Court can be breached, and if the public learns that lesson through vague official statements and incomplete disclosure, confidence in the institution itself is damaged.
The path forward requires more transparency, more investment, and more sustained attention to security fundamentals. The Moore case has created an opportunity for that change. Whether that opportunity is seized depends on leadership across the judicial branch, federal agencies, and Congress.
Key Takeaways
- A 24-year-old from Tennessee gained unauthorized access to the Supreme Court's electronic filing system at least 25 times between August-October 2023, highlighting critical detection failures
- The government has not disclosed what information was compromised during the breach, leaving uncertainty about the scope and severity of the incident
- Federal court systems and government agencies broadly struggle with legacy infrastructure, inadequate monitoring, and insufficient cybersecurity investment despite known best practices
- Detection and disclosure delays (3+ months between breach and charges) indicate systemic problems in how federal institutions monitor and respond to intrusions
- The breach raises serious concerns about judicial independence, confidentiality of case information, and public trust in the Supreme Court system if vulnerabilities aren't addressed
Related Articles
- Google Veo 3.1: AI Video Generation with Vertical 4K Upscaling [2025]
- Microsoft Deployment Toolkit Deprecated: What It Means for Your Infrastructure [2025]
- Are You Dead Yet: China's Viral App Redefining Digital Safety [2025]
- PC Sales Downturn 2026: Why Memory Prices Are Skyrocketing [2025]
- Elgato Stream Deck Plus: Ultimate Control Hub for Streamers & Creators [2025]
- Meta's VR Studio Shutdowns: What Happened to Reality Labs [2025]
![Supreme Court Hacking Case: What the Tennessee Breach Reveals [2025]](https://tryrunable.com/blog/supreme-court-hacking-case-what-the-tennessee-breach-reveals/image-1-1768333229012.jpg)



