Chrome Zero-Day CVE-2026-2441: Critical Security Update Guide [2025]
You've probably heard it before: "Just update your browser." Usually, it's a mild inconvenience, something you do when you restart your laptop. But sometimes—and we're talking right now—that update is the difference between normal browsing and having your computer compromised by attackers actively weaponizing a vulnerability.
That's where we are with CVE-2026-2441, a critical zero-day vulnerability in Google Chrome that's already being exploited in real attacks. This isn't theoretical. This isn't "could happen." This is happening. And if you haven't updated Chrome yet, you're potentially at risk.
Here's what you need to know, why it matters, and exactly what to do about it.
TL; DR
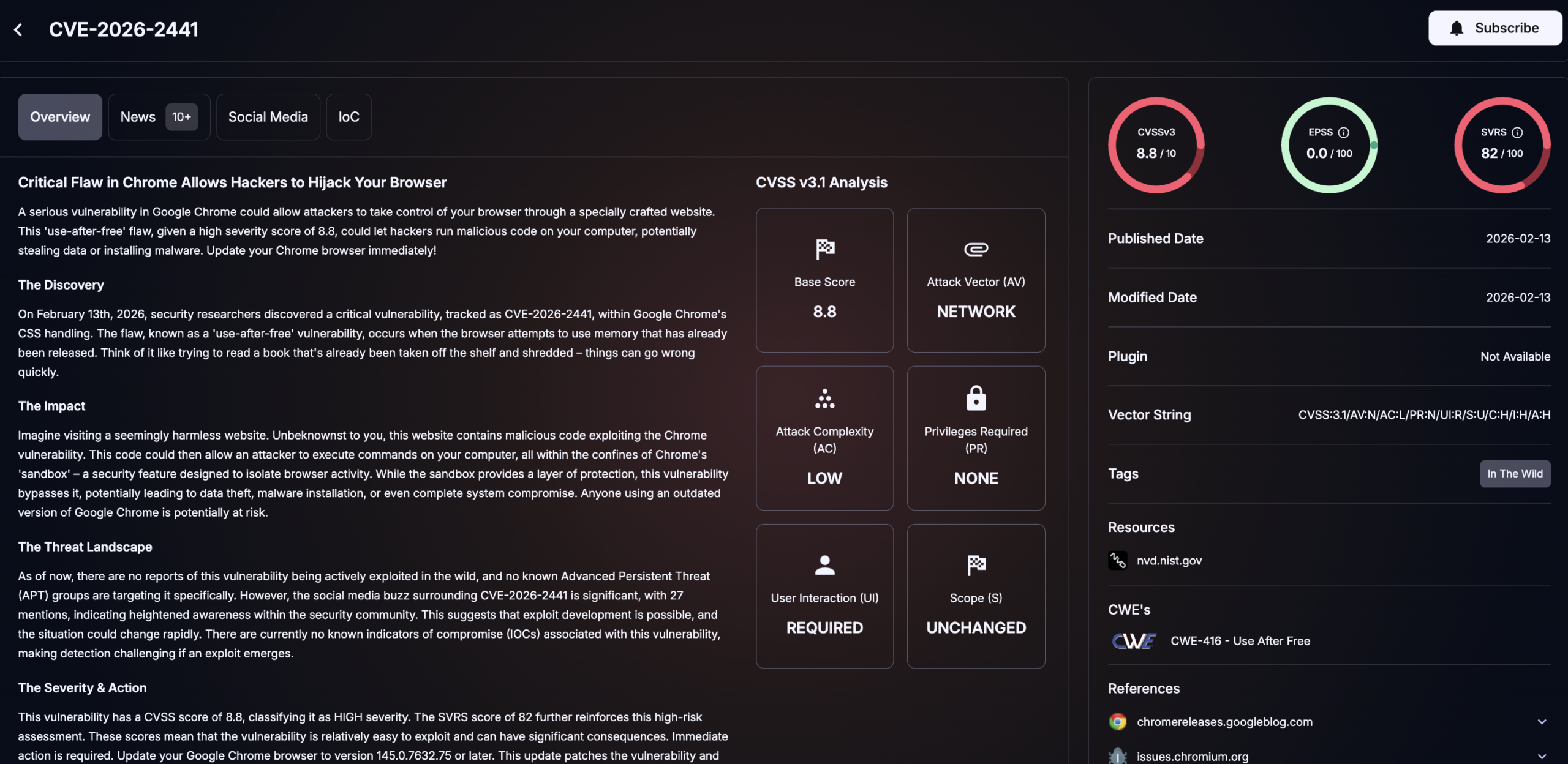
- Critical vulnerability confirmed: CVE-2026-2441 is a "use after free" bug in Chrome's CSS engine with a severity score of 8.3/10
- Active exploitation: Google confirmed this zero-day is being actively exploited in real-world attacks right now
- Update immediately: Windows/Mac users need Chrome 145.0.7632.75 or later; Linux users need 144.0.7559.75 or later
- How to check: Open Chrome menu (three dots) > Help > About Google Chrome to auto-update
- Bottom line: This is the first actively exploited Chrome vulnerability of 2025, and you should treat it with urgency
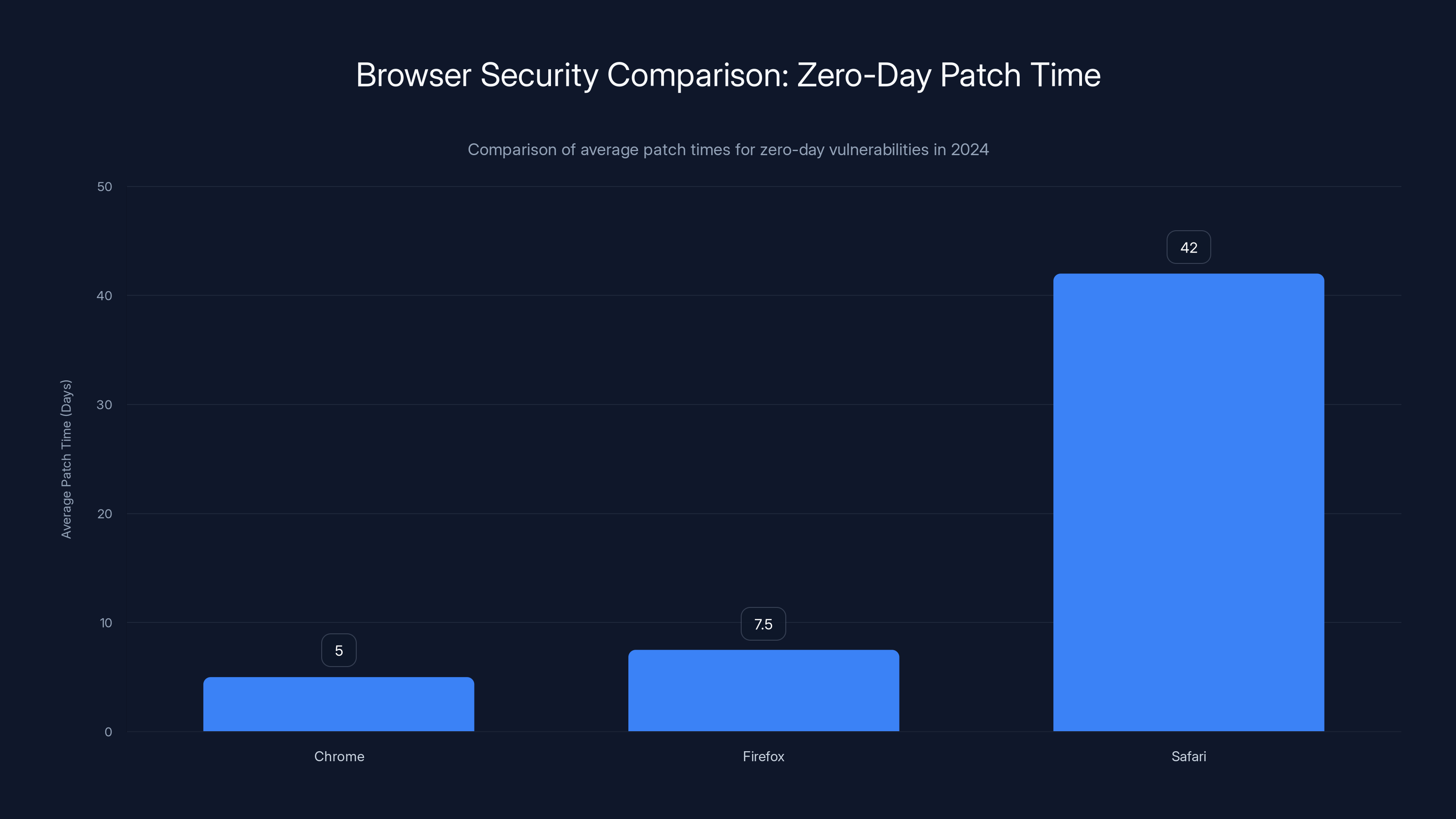
Chrome patches zero-day vulnerabilities faster (3-7 days) compared to Firefox (5-10 days) and Safari (up to 6 weeks). Estimated data based on 2024 trends.
What Is CVE-2026-2441 and Why Should You Care?
Let's start with the basics, because understanding what you're dealing with makes you take it seriously.
CVE-2026-2441 is what security researchers call a "use after free" vulnerability. That's a fancy way of saying the browser is trying to use a piece of memory that's already been deleted or deallocated. In this case, it's specifically in Chrome's CSS (Cascading Style Sheets) engine, the part of the browser that handles how websites look and are formatted.
Here's the dangerous part: when this bug gets triggered by a specially crafted HTML page, it doesn't just crash your browser. It allows attackers to execute arbitrary code. That means they can run whatever programs they want on your machine. They're not limited to the browser sandbox anymore—they can potentially access your files, steal your passwords, install malware, or turn your computer into a bot for further attacks.
The severity rating of 8.3 out of 10 isn't arbitrary. The CVSS (Common Vulnerability Scoring System) takes into account several factors: what's required to exploit it (in this case, just viewing a malicious webpage), what an attacker can do once they've exploited it (execute code), and how widely it affects users (Chrome has 3.5 billion users globally). Put those together and you get a "high" severity rating that demands immediate attention.
What makes this specific vulnerability extra concerning is timing. Google released this patch in the first month of 2025, which means we're already seeing attackers experimenting with new attack vectors right out of the gate. The fact that Google explicitly stated this is being exploited "in the wild" means actual victims have already been hit—we just don't know the full scope yet.
The patch came surprisingly fast. Google usually takes a few days to patch critical vulnerabilities (remember Log 4j? That took weeks to fully remediate across the internet). This turnaround suggests Google's security team treated this with maximum urgency, which tells us they understood the real-world threat.
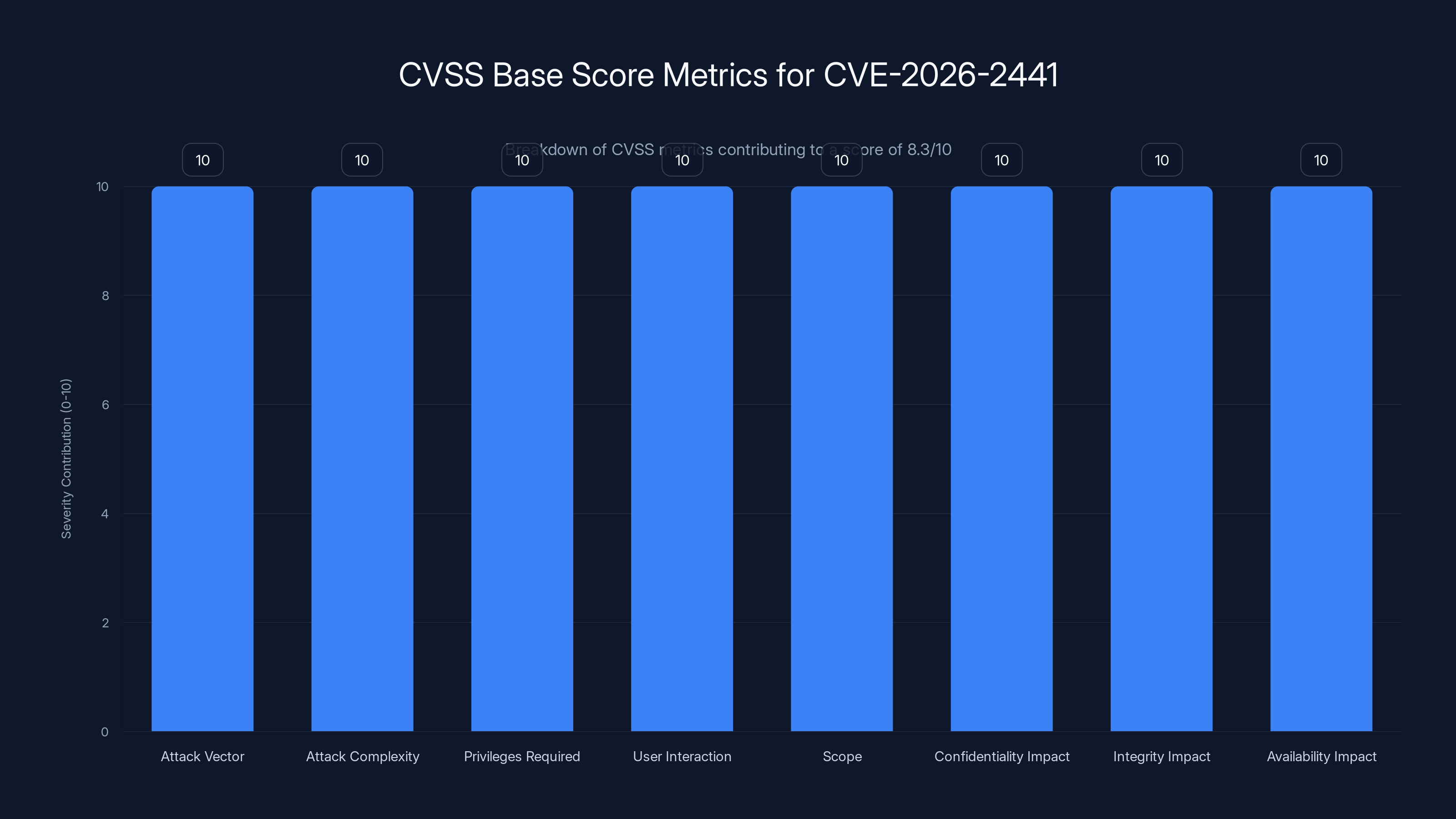
The CVSS base score metrics for CVE-2026-2441 show high severity in all categories, contributing to an overall score of 8.3/10, indicating a high level of urgency for addressing this vulnerability.
Understanding the Technical Details: Use After Free in CSS
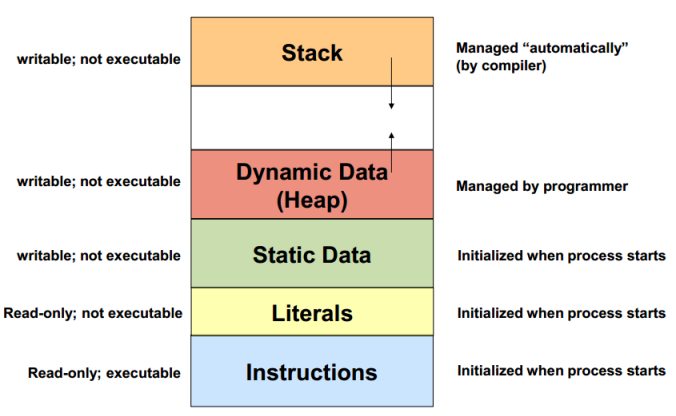
If you want to understand why this vulnerability is actually dangerous and not just a theoretical hole, you need to understand what "use after free" means at a technical level.
Memory management in complex programs like Chrome is essentially controlled chaos. The browser is constantly allocating memory (reserving space to store data), using that memory (reading and writing data to that space), and then deallocating memory (freeing up that space so it can be used for something else). This process happens millions of times per second when you're browsing.
The problem occurs when the developer's logic gets confused about whether a particular piece of memory is still valid. Imagine you rent an apartment, move out, and tell the landlord the unit is empty. But then you accidentally leave a copy of your key behind. Now the landlord rents that apartment to someone else. You still have a key, so you come back and try to use your apartment—except it's not your apartment anymore. The new tenant's stuff is everywhere. That's essentially what "use after free" does in memory.
In Chrome's CSS engine, this happens when the browser renders a webpage with certain CSS properties. The CSS engine allocates memory to store styling information. Then, under specific conditions, that memory gets freed. But sometimes the code tries to access that freed memory again—and that's where the danger lies.
Why CSS specifically? CSS is parsed and executed on every single webpage you visit. It's one of the most frequently executed parts of Chrome's rendering pipeline. That means the attack surface is enormous. An attacker doesn't need to trick you into downloading a file or clicking a link to a suspicious site. They just need to put malicious HTML and CSS on any website they control—or, more dangerously, inject it into a legitimate website via a compromise or ad network.
The sandbox escape is the critical escalation here. Chrome's sandbox is one of its best security features—it keeps websites isolated so even if one is compromised, it can't affect others or your system. But a "use after free" in core CSS rendering can potentially break through that sandbox, turning a browser-level bug into a system-level compromise.
How the Vulnerability Is Being Exploited in the Real World
Google hasn't released specifics about how this vulnerability is being exploited. That's deliberate. Their policy is to withhold technical details about actively exploited vulnerabilities until the majority of users have patched.
But we can make educated guesses based on how similar vulnerabilities have been used in the past.
Most likely scenario: attackers created a malicious webpage (or multiple webpages) designed to trigger the "use after free" bug through carefully crafted CSS. When someone visits that page in an unpatched Chrome browser, the vulnerability gets triggered, allowing code execution. From there, attackers could:
- Install a trojan or backdoor for persistent access
- Steal browser cookies (which means stealing login sessions for your email, banking, social media)
- Harvest cryptographic keys or stored passwords
- Deploy ransomware or cryptominers
- Use the compromised machine as a launching point for attacks on other systems
The attack doesn't require user interaction beyond just visiting the webpage. No clicking "download this file" or entering a password. Just viewing the page is enough.
Google mentioned this is the first actively exploited Chrome vulnerability of 2025, but they didn't specify the victims or attack method. That silence is notable because sometimes when major companies are targeted, Google keeps that quiet to avoid creating a roadmap for copycats.
What we do know from the past year: zero-day vulnerabilities in major browsers are increasingly being used by state-sponsored threat actors. In 2024, Google patched eight zero-days in Chrome, many attributed to advanced threat groups. This suggests that by 2025, sophisticated attackers have reliable supply chains for finding and exploiting these bugs.
The fact that this vulnerability appeared in January suggests we're entering a particularly active season for zero-day discoveries and exploitation. If the pattern from 2024 continues, we'll see more of these patches throughout the year.
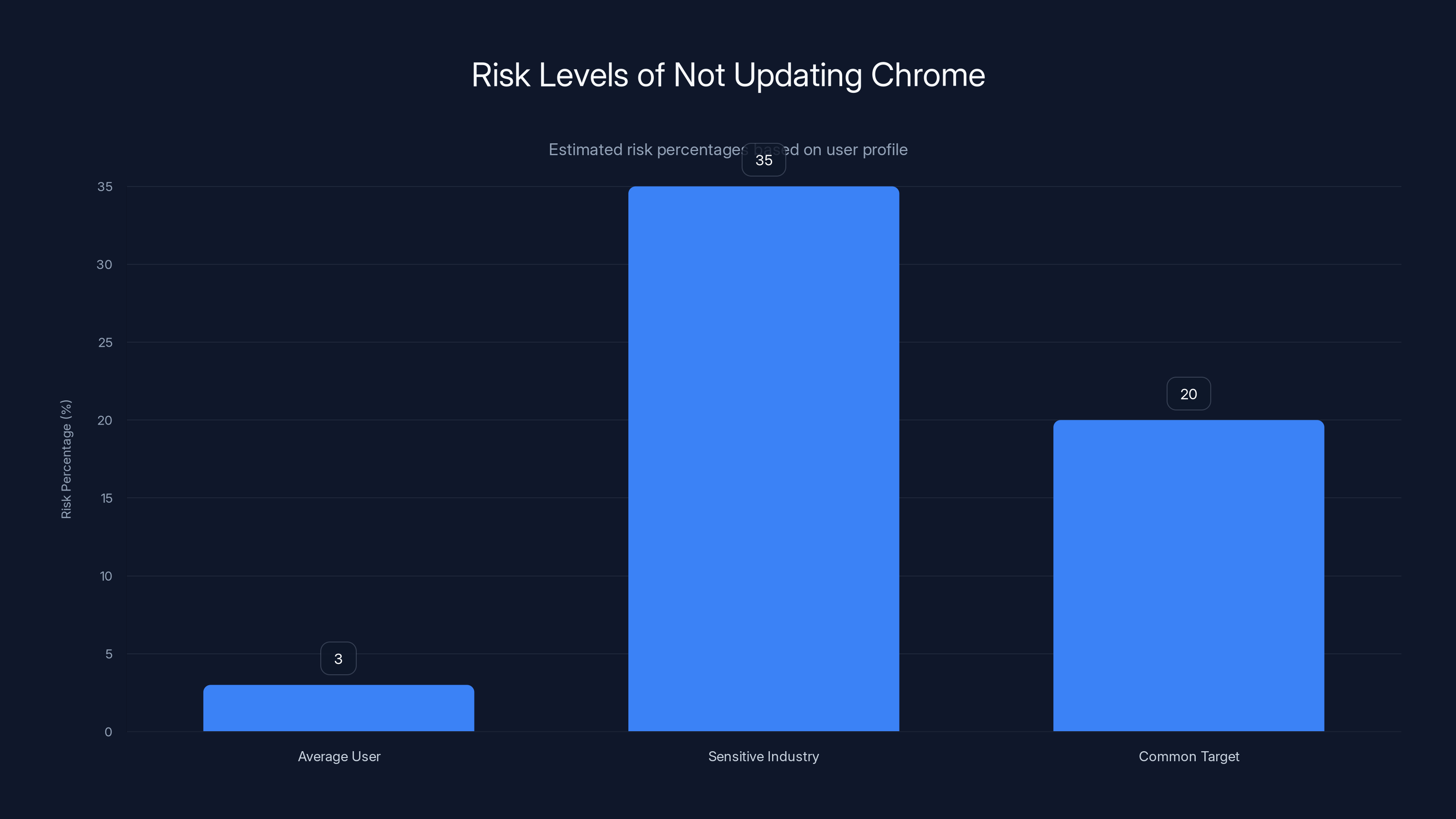
The risk of encountering a security threat varies by user profile, with sensitive industry workers facing the highest risk. Estimated data based on typical exposure.
CVE Severity Scoring Explained: What 8.3/10 Actually Means
When security teams say a vulnerability has an 8.3/10 severity score, they're using the CVSS (Common Vulnerability Scoring System) framework. Understanding this scoring helps you understand why you should treat this with urgency.
CVSS breaks down vulnerability severity into three metric groups:
Base Score Metrics determine the fundamental danger level:
- Attack Vector: How exploitable is it? (Network = most dangerous, Physical = least)
- Attack Complexity: How hard is it to exploit? (Low complexity = easier for attackers)
- Privileges Required: Do you need special access? (None = easier)
- User Interaction: Do users need to do something? (None = easier)
- Scope: Does it affect just the app, or the entire system?
- Confidentiality Impact: Can attackers read data they shouldn't? (High = very bad)
- Integrity Impact: Can attackers modify data? (High = very bad)
- Availability Impact: Can attackers crash systems? (High = very bad)
For CVE-2026-2441:
- Attack Vector: Network (you just need to visit a webpage)
- Attack Complexity: Low (no special tricks required)
- Privileges Required: None (anyone can trigger it)
- User Interaction: None (visiting the page is enough)
- Scope: Changed (breaks out of the browser sandbox to affect the system)
- Confidentiality: High (attackers can read anything your user can read)
- Integrity: High (attackers can modify anything your user can modify)
- Availability: High (attackers can crash or disable systems)
That combination adds up to 8.3, which places it in the "high" severity category. Anything 9.0 and above is "critical." While this isn't quite critical, it's serious enough that attackers are already weaponizing it.
For comparison:
- CVSS 7.0-8.9 = High (requires rapid patching)
- CVSS 9.0-10.0 = Critical (requires emergency patching)
An 8.3 sits right on that border. It's not a false alarm, and it's not a panic situation—it's a "fix this today" situation.
Step-by-Step: How to Update Chrome Immediately
Let's move from scary details to practical solutions. Updating Chrome is straightforward, but there are a few scenarios depending on your setup.
For Windows and Mac Users
You need Chrome version 145.0.7632.75 or later. Here's exactly how to check and update:
- Open Chrome and click the three horizontal lines (menu button) in the top-right corner
- Hover over "Help" and click "About Google Chrome"
- Chrome will automatically check for updates and download any available version
- Once the download completes, you'll see a "Relaunch Chrome" button with a yellow or red circle
- Click that button to restart Chrome with the updated version
- Verify the update worked: go back to Help > About Google Chrome and confirm the version is 145.0.7632.75 or higher
That's it. Chrome should have auto-updated already if you haven't disabled automatic updates, but it won't take effect until you restart the browser.
For Linux Users
Linux users need Chrome 144.0.7559.75 or later (note: this is a different version number than Windows/Mac due to different release cadences).
- Open Chrome and access the menu (three dots)
- Navigate to Help > About Google Chrome
- Chrome will check for updates
- If prompted, restart Chrome
- Verify you're on 144.0.7559.75 or higher
Linux users sometimes have to manually install updates depending on their distribution and installation method. If Chrome doesn't auto-update, you can also:
- Use your package manager to update Chromium (usually
sudo apt-get update && sudo apt-get install chromium) - Download the latest version directly from Google's download page
- Use Chrome's built-in update checker on your next restart
If You've Disabled Automatic Updates
If you're that person who disabled automatic updates because they annoyed you, here's the method:
- Open Chrome
- Click the menu button (three dots) in the top-right corner
- Click "Help"
- Click "About Google Chrome"
- Chrome will now check for updates even though you've disabled automatic updates
- It will download the new version in the background
- Look for the "Relaunch Chrome" button and click it
Note: This won't re-enable automatic updates permanently. It just forces a check this time. If you really want to stay current without constant updates, consider enabling Chrome's "Update on shutdown" option instead of completely disabling updates.
For Enterprise Users and IT Departments
If you manage Chrome deployments for a company:
- Update your Chrome Enterprise master policy immediately
- Push version 145.0.7632.75 (Windows/Mac) or 144.0.7559.75 (Linux) to all managed devices
- Use Google's Chromebook Management Console if you manage Chromebooks
- Monitor your organization's Chrome version distribution dashboard
- Send a company-wide notification urging employees to update
Big enterprises often have staged rollouts to avoid breaking things, but this is one where "break glass" procedures might be justified. The risk of a single compromised employee machine leading to full network breach often outweighs the risk of a hasty update.
Verifying the Update Actually Worked
After updating, verify it took effect:
- Click the three-dot menu in Chrome
- Go to "Help"> "About Google Chrome"
- Check the version number displays 145.0.7632.75 or higher (Windows/Mac) or 144.0.7559.75 or higher (Linux)
- If it shows a lower version, click "Relaunch Chrome" if available
- If that doesn't work, completely close Chrome (use Task Manager on Windows, Force Quit on Mac) and reopen it
Don't just assume the update worked because you saw a relaunch button. Actually verify the version number. There's a small chance something got corrupted, and you want to know.
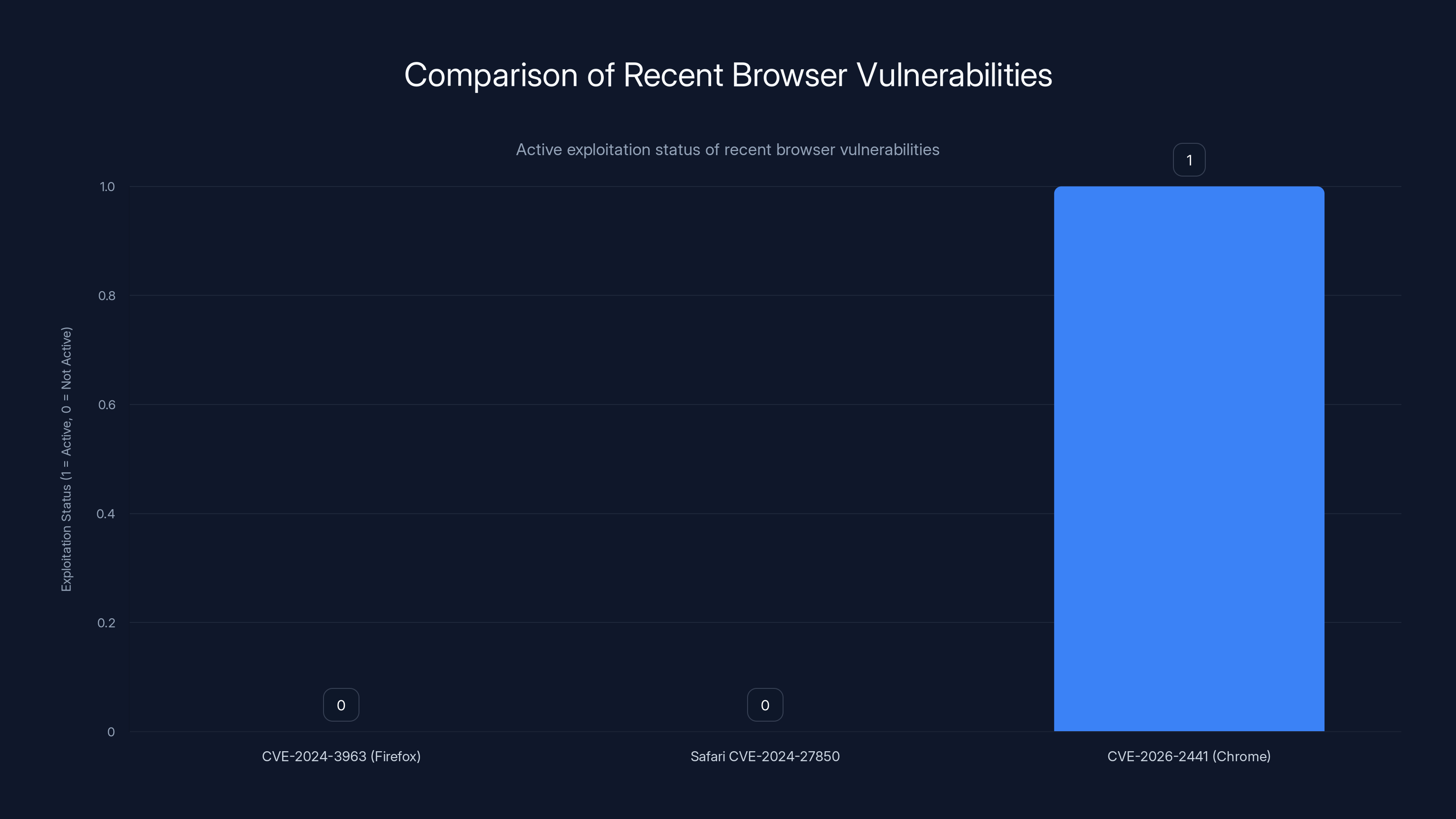
CVE-2026-2441 is actively exploited, unlike recent Firefox and Safari vulnerabilities, highlighting the urgency for immediate patching.
Why This Is Different From Other Chrome Vulnerabilities
Google patches Chrome regularly. The last Chrome update probably came a few weeks ago. So what makes CVE-2026-2441 different enough that we're writing about it as urgent news?
It's being actively exploited. That's the difference.
Most vulnerabilities that Google patches are discovered through responsible disclosure, bug bounty programs, or security research. Companies usually have a few weeks to patch before public disclosure. This gives organizations time to test updates and roll them out in an orderly way.
A zero-day, by definition, is unknown to the vendor when attackers find it. Google isn't aware of it until they either stumble across an attack, security researchers bring it to them, or threat intelligence firms identify it. For CVE-2026-2441, Google confirmed attackers are already using it. That means:
- Someone, somewhere has already been compromised by this attack
- Attackers have functional exploit code that works reliably
- There may be multiple groups independently using this vulnerability
- The attack is probably still active right now
Google's response was unusually swift. They patched it quickly and released security advisories immediately. That speed suggests their incident response team knew this was serious and pressing.
Comparison to other recent browser vulnerabilities:
- CVE-2024-3963 (Firefox): Disclosed, no active exploitation confirmed initially
- Safari CVE-2024-27850: Patched, but no real-world attacks documented at patch time
- CVE-2026-2441 (Chrome): Actively exploited before patch became available
The active exploitation angle is what separates "you should patch eventually" from "you should patch right now."
What Happens If You Don't Update? Real Risk Assessment
Let's be real for a moment. Not everyone updates Chrome immediately. Maybe you're thinking, "How likely is it that I'll actually encounter this attack?" That's a fair question.
The honest answer: It depends on who you are and what you do online.
If you're an average user doing normal browsing:
- Your risk is moderate but real
- Attackers could inject malicious code into any website through ad networks, compromises, or redirects
- The attack is passive—you don't need to do anything except visit a webpage
- Your odds of encountering it before patching are maybe 1-5%, but they're not zero
If you work in a sensitive industry:
- Finance, government, defense, law, journalism, healthcare, activism
- Your risk is significantly higher
- State-sponsored threat actors actively hunt for people in these fields
- They may specifically craft attacks targeting your organization
- Your odds are probably 20-50% if you're actively targeted
If you're a common target for cybercriminals:
- Running a business, managing significant assets, running cryptocurrency
- You're more likely to be specifically targeted
- Attackers might redirect you to malicious sites or inject ads on sites you visit
- Risk is elevated
The problem with zero-days being exploited in the wild is they don't announce themselves. You won't notice the attack happening. The computer won't behave differently. The page will load normally. The exploit code runs silently in the background.
The consequences are also delayed. A trojan installed today might not activate for weeks. A stolen credential might not be used until you're not paying attention. A backdoor might sit dormant until the attacker is ready to use it.
So "do I need to update" depends on your specific circumstances. But the general rule: if Google says update now and it's a zero-day being exploited, the safe play is to update now. The worst case of updating is a 30-second restart. The worst case of not updating is far worse.

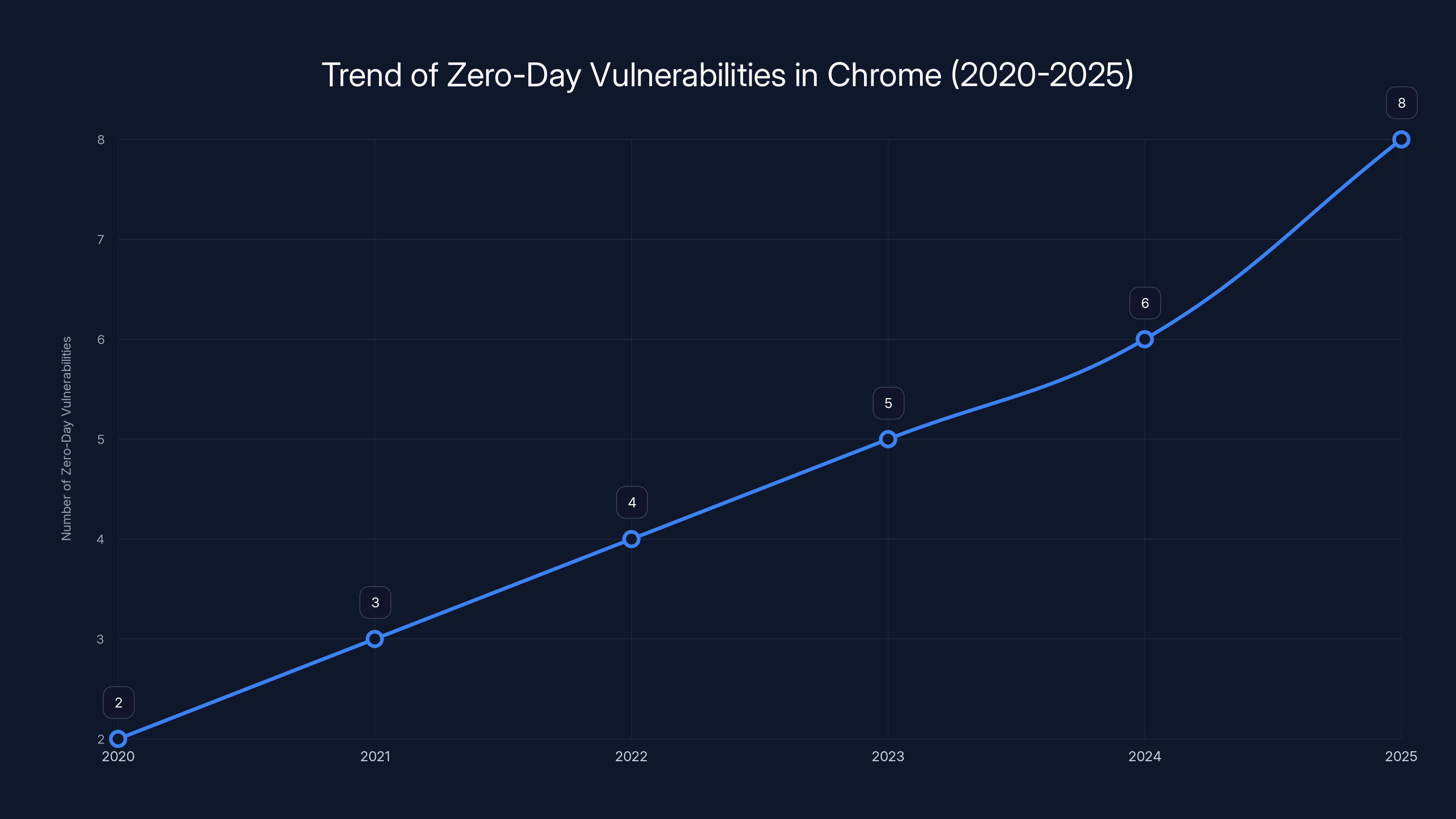
The number of zero-day vulnerabilities in Chrome has been steadily increasing, highlighting the growing importance of timely updates and security measures. Estimated data.
The Broader Context: Zero-Days and Browser Security in 2025
CVE-2026-2441 isn't an isolated incident. It's part of a broader trend.
Google patched eight zero-days in 2024. That's notable because:
- In 2010, Google might patch one or two zero-days per year
- The increase reflects more sophisticated attackers
- It also reflects better detection capabilities
- Or maybe both
Many of the 2024 zero-days were linked to state-sponsored groups. That means sophisticated nation-state actors are actively hunting for browser vulnerabilities and using them to compromise specific targets.
Browser security has become a geopolitical issue. A zero-day in Chrome, Firefox, or Safari can be used for:
- Surveillance of journalists in certain countries
- Cyber espionage against companies
- Preparation for major cyberattacks
- Stealing intellectual property
- Corporate espionage
The fact that we're seeing these exploited zero-days in the first month of 2025 suggests:
- Threat actors are well-funded and organized
- They're continuously hunting for new vulnerabilities
- Once found, they weaponize them quickly
- They're confident these attacks will work before patches deploy at scale
For users, this means:
- Browser security is now a personal security issue, not just a convenience
- Patching delays increase your risk significantly
- Staying current is a basic security hygiene requirement
- Using an outdated browser is roughly equivalent to not using a seatbelt
Chrome's security advantage comes partly from its update frequency. Chrome pushes major updates every 4 weeks, and security patches as needed. Firefox updates monthly. Safari updates with i OS/mac OS updates. The more frequently your browser updates, the less time attackers have to exploit known vulnerabilities.

Chrome vs. Other Browsers: Security Comparison
You might be wondering: is Chrome uniquely vulnerable, or do Firefox and Safari have similar issues?
All major browsers have zero-days. The difference is volume and response time.
Chrome:
- 8 zero-days patched in 2024
- Average time to patch from discovery: 3-7 days
- Large security team (100+ researchers)
- Rapid release cycle (4-week major versions)
- Also the most targeted browser due to market share
Firefox:
- Patches zero-days as discovered
- Average time to patch: 5-10 days
- Smaller team than Chrome
- Monthly release cycle
- Less frequently targeted because smaller market share
Safari:
- Tied to i OS/mac OS releases
- Average time to patch: can be up to 6 weeks for major OSes
- Tied to Apple's release schedule
- Smaller team
- Often targeted heavily because of valuable Apple ecosystem users
Chromium-based browsers (Edge, Brave, etc.):
- Get Chrome's security updates automatically
- Edge adds its own security features on top
- Generally benefit from Chrome's rapid patching
The landscape is: every browser gets zero-days. Chrome patches faster but gets targeted more. Safari patches slower but has advantages from Apple's ecosystem controls. Firefox is a middle ground.
No browser is "safe." The question is: which one patches fastest and how often do you stay updated? For CVE-2026-2441, the answer is clear: Chrome has the patch, it's available, apply it now.

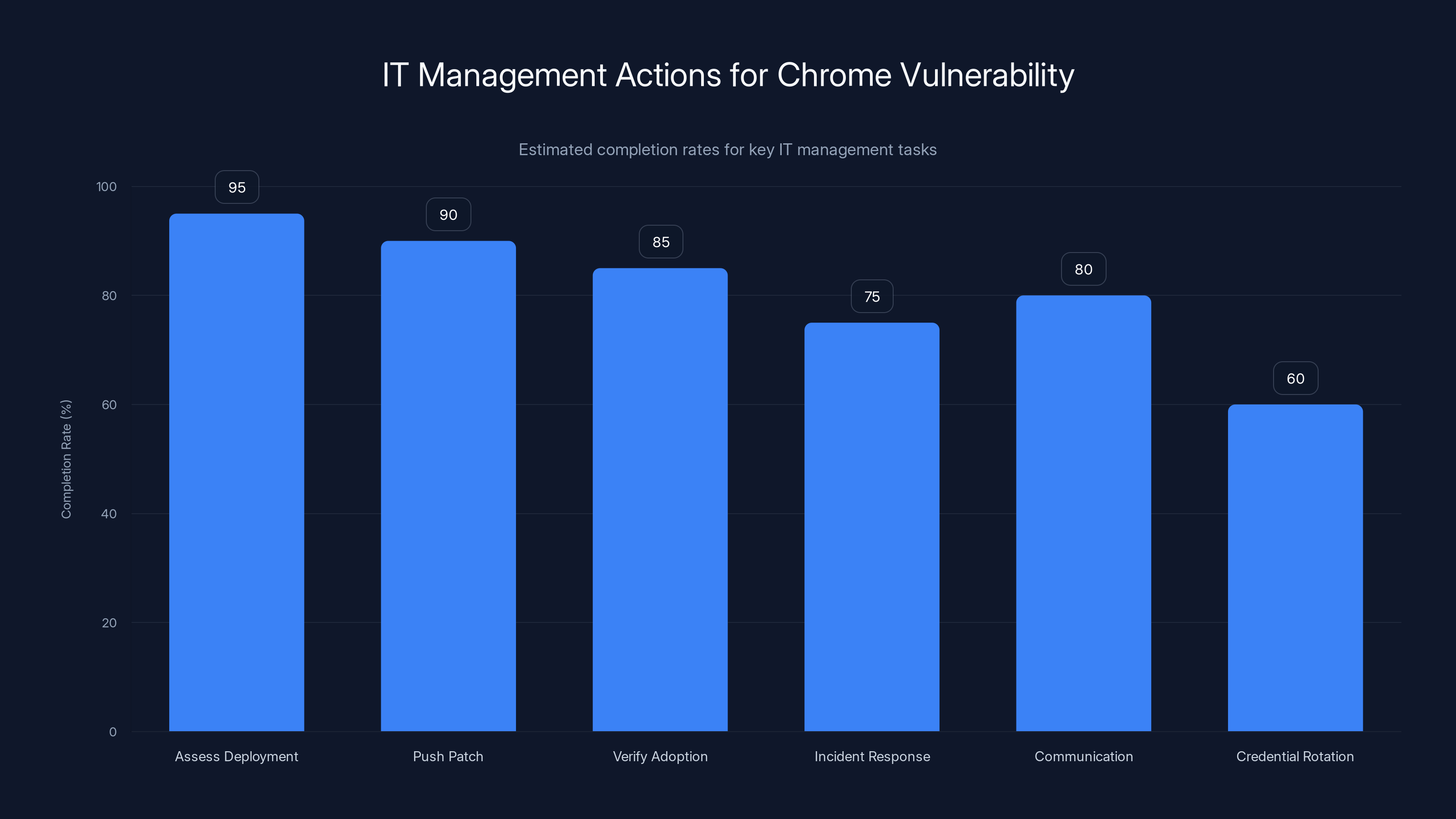
Estimated data shows that tasks like assessing deployment and pushing patches are completed more quickly compared to tasks like credential rotation. Estimated data.
Prevention Beyond Patching: Additional Security Measures
Patching is the most important step, but it's not the only defense.
1. Keep Your Operating System Updated
Why? Because a successful Chrome exploit might need OS-level vulnerabilities to escalate from the browser sandbox to full system access. A fully patched OS makes that escalation harder.
- Windows: Enable automatic updates
- Mac: Install security updates from Software Update
- Linux: Run
sudo apt-get update && sudo apt-get upgraderegularly (or equivalent for your distro)
2. Use Security Extensions (Selectively)
Browser security extensions can catch some attacks, but they also add attack surface. Good options:
- u Block Origin: Ad blocker that also blocks malicious scripts
- HTTPS Everywhere: Forces HTTPS on websites that support it
- No Script: Blocks Java Script by default (very strict, not for everyone)
Avoid installing too many extensions. Each one is additional code running in your browser, each one has access to what you see.
3. Enable Chrome's Advanced Protection
If you're a high-value target:
- Go to Chrome settings
- Search for "Advanced Protection"
- Enable it
This enables strict phishing and malware protections, requires a security key for account recovery, and limits third-party app access. It's slower but safer for people actively targeted.
4. Disable Java Script on Untrusted Sites
For paranoid users (which, given active zero-days, isn't paranoid anymore):
- Install No Script or u Matrix
- These block Java Script by default
- Whitelist only sites you trust
- This breaks some websites but nearly eliminates browser-based attacks
Note: This is extreme and impractical for daily use. But for accessing sensitive things (banking, email accounts from untrusted networks), it's reasonable.
5. Use a Virtual Machine for Untrusted Browsing
For high-risk scenarios:
- Run Chrome inside a virtual machine with a snapshot
- If your VM gets compromised, just revert to the snapshot
- This prevents attacks from spreading to your main system
Tools: Virtual Box (free), Hyper-V (Windows Pro/Enterprise), UTM (Mac).
6. Separate Browser Profiles for Sensitive Activities
Create a separate Chrome profile for:
- Banking and financial services
- Email accounts
- Cryptocurrency wallets
- Work accounts
Use your main profile for general browsing. If the main profile gets compromised, your financial accounts are in a separate profile with different cookies, saved passwords, and extensions.

Timeline: How Zero-Day Vulnerabilities Typically Unfold
Understanding the typical progression of a zero-day helps you understand why Google's urgency matters.
Phase 1: Discovery (Unknown duration)
- Attackers or researchers find the vulnerability
- They begin developing exploit code
- No one (including Google) knows about it yet
- This is the zero-day phase
Phase 2: Early Exploitation (Days to weeks)
- Attackers deploy the exploit against targets
- Google either discovers the attack or researchers report it
- For CVE-2026-2441, Google confirmed it's in this phase
Phase 3: Patch Development (Hours to days)
- Google's security team develops and tests a fix
- For this vulnerability: patch deployed within days
Phase 4: Release (Hours)
- Google releases the patch to all users
- Users need to install it
- Attackers adapt and look for ways around the patch
Phase 5: Widespread Adoption (Days to weeks)
- Most users get the patch
- Exploit becomes less reliable as fewer unpatched systems exist
- Attackers move on to finding new vulnerabilities
We're currently in Phase 4 (patch released, awaiting widespread adoption). The vulnerability goes from "actively exploitable on billions of devices" to "only exploitable on millions of devices" as adoption increases.
Your responsibility: move yourself out of the "exploitable" category by updating.

What Google Gets Right (and Wrong) About Security Communication
Google's security advisory for CVE-2026-2441 was careful. They confirmed:
- The vulnerability exists
- It's being actively exploited
- Here's the patch
- Update now
They withheld:
- The specific websites hosting the exploits
- The attack methodology in detail
- The victims affected
- The threat actors responsible
This approach is smart for security. Releasing full technical details would give attackers a roadmap for developing new attacks against the patched vulnerability. But it's frustrating for transparency.
What would help users more:
- Estimated attack scale (how many users affected?)
- Confirmation whether it's criminal, state-sponsored, or opportunistic
- Specific threat intelligence (if safe to share)
- Timeline for when the majority will be patched
But even without that, Google's core message is clear: patch now. And that's the right message.
Preparing Your Organization (For IT Managers)
If you manage IT for a company, here's how to handle this:
Immediate Actions (Today)
-
Assess your Chrome deployment:
- How many devices are running Chrome?
- What versions are deployed?
- Use your mobile device management (MDM) or IT management tools to check
-
Push the patch:
- If you manage Chrome Enterprise: update your policy to enforce version 145.0.7632.75 or later
- If you manage Chromebooks: push update to all devices immediately
- If users manage their own devices: send urgent notification to update
-
Verify adoption:
- Monitor your device management dashboard
- Track what percentage of devices have updated
- Aim for 90%+ adoption within 24 hours
Short-term (This Week)
-
Incident response assessment:
- Ask security team: have you detected any compromises related to this vulnerability?
- Check logs for unusual activity from the patch date backward
- Monitor endpoint detection and response (EDR) tools for alerts
-
Communication:
- Send email to all staff explaining the vulnerability and importance of updating
- Provide clear instructions for manual update if not managed
- Set expectations: "All company devices should be updated within 24 hours"
-
Credential rotation (optional but recommended):
- For high-risk employees: consider rotating passwords for critical accounts
- For everyone else: just ensure they're not reusing passwords
- This assumes attackers may have had access to browser cookies
Medium-term (This Month)
-
Incident investigation:
- If you detected potential compromises, begin investigation
- Engage incident response team or external forensics
- Check for signs of persistent access (backdoors, beacons)
-
Security posture improvements:
- Review your Chrome update policy: can it be faster?
- Consider moving to managed Chrome deployments if not already
- Implement browser-level protections (extensions, sandboxing)
-
Threat hunting:
- Search your logs for indicators of compromise related to CVE-2026-2441
- Check for suspicious processes spawned from Chrome
- Review network traffic for command and control connections
Common Questions About This Vulnerability
Q: Will Chrome automatically update for me? Yes, unless you've disabled automatic updates. Chrome checks for updates every few hours and applies them on restart. However, you need to actually restart Chrome for the update to take effect. Just because Chrome downloaded it doesn't mean it's installed.
Q: What if I use Chromium instead of Chrome? Chromium (the open-source base) is maintained by Google and gets the same patches. Derivative browsers like Edge, Brave, and Opera get patches automatically. Only old Chromium builds that aren't receiving updates would be vulnerable.
Q: Is my Chromebook affected? Yes, Chromebooks run Chrome OS which includes Chrome. Updates push to Chromebooks automatically, but check your version to be sure. Go to Settings > About > Google Chrome OS to check.
Q: Can a web page infect my computer without me clicking anything? Yes, that's what makes this vulnerability serious. Just visiting the page is enough. You don't need to click a link, download a file, or enter a password. Passive exploitation is the most dangerous kind.
Q: Will my antivirus protect me? Some will, some won't. If the exploit is brand-new and not in antivirus signatures, protection probably won't help. Antivirus is last-line defense, not primary defense. Patching is the primary defense.
Q: How do I know if I've been compromised? You probably don't. That's the problem. A targeted attack doesn't leave obvious signs. Your machine will work normally. Malware runs silently in the background. The best indication would be:
- Unexpected account lockouts (password reset by attacker)
- Unusual account activity (logins from strange locations)
- Missing files or money (in extreme cases)
- IT team alerting you to unusual network traffic from your device

Expert Recommendations and Best Practices
Based on how security researchers and incident responders handle these situations:
-
Update now, investigate later. Patching is the immediate priority. You can look for compromises after you've closed the hole.
-
**Don't wait for "testing." Zero-days being actively exploited don't wait for testing in a lab. Deploy immediately and monitor carefully.
-
Monitor for behavioral changes. After updating, watch for:
- Unusual CPU usage
- Unexpected network connections
- Slow system performance
- Strange processes in Task Manager/Activity Monitor
-
Assume breach for high-value targets. If you're specifically targeted (work in security, defense, government, journalism), assume attackers may have already compromised your system. Update to stop new attacks, but investigate thoroughly.
-
Use defense in depth. Don't rely on patching alone. Combine with:
- Security extensions
- Behavioral monitoring
- Network segmentation
- Account security (strong passwords, 2FA, security keys)
-
Stay informed. Follow security feeds for subsequent patches. If there's a bypass for this patch, you want to know immediately.

What Happens Next: Looking Forward
After you patch, what should you expect?
Short-term (Next few days):
- Security researchers will start analyzing the vulnerability publicly
- Technical details may emerge about how it works
- Follow-up patches may come if the initial patch has issues
- Attackers will try to find workarounds
Medium-term (Next few weeks):
- Google will publish a security advisory with details
- Academic papers may analyze the vulnerability class
- Security vendors will update their tools
- Attackers move on to new vulnerabilities
Long-term (This year):
- This will be one of many zero-days Google patches in 2025
- The same vulnerability class will likely appear in other browsers
- Security tool vendors will improve detection
- Users who update quickly will forget about it
The reality: CVE-2026-2441 is urgent now, but it'll become history within weeks. The important thing is you take action today so you're part of the "history" and not part of the "still vulnerable" group.

Final Takeaway: Why This Matters Beyond Chrome
CVE-2026-2441 isn't just about a browser bug. It's about the broader reality of software security in 2025.
Zero-days are not anomalies. They're part of the landscape. Well-funded, sophisticated threat actors continuously hunt for them. The moment they find one that works, they weaponize it. The window between first exploitation and widespread patching is usually days.
Your responsibility as a user is simple: stay updated. Not eventually, not when you feel like it, now.
Chrome makes this easy. Updates happen in the background. You just need to restart the browser. 30 seconds of inconvenience versus potentially hours of incident response if you get compromised.
The math is obvious.
Update your browser. Verify it worked. Go back to your day. That's it. You've just protected yourself against one of the most active threats in modern computing.
And if you're running an organization? Make sure your infrastructure, devices, and users all get updated today. Zero-days at scale can become major incidents. But they're only incidents if you let them spread.

FAQ
What exactly does CVE-2026-2441 allow an attacker to do?
CVE-2026-2441 is a "use after free" vulnerability in Chrome's CSS rendering engine that allows attackers to execute arbitrary code. In practical terms, this means an attacker can run malicious programs on your computer with the same permissions your user account has, potentially stealing files, passwords, personal data, or installing persistent malware through a specially crafted webpage you visit.
How do I know if my version of Chrome is vulnerable?
Open Chrome and go to the three-dot menu in the top-right corner, then select Help > About Google Chrome. The page will show your current Chrome version. If you see a version lower than 145.0.7632.75 (Windows/Mac) or 144.0.7559.75 (Linux), you're vulnerable and need to update immediately. If you see a version number equal to or higher than these, you're protected.
Can this vulnerability be exploited on mobile Chrome or Android?
This specific vulnerability affects Chrome on Windows, mac OS, and Linux as detailed in Google's security advisory. Mobile platforms like Android have their own version of Chrome that follows different update schedules. If you use Chrome on an Android phone, make sure your version is also updated through the Google Play Store to ensure protection against similar vulnerabilities.
What should I do if I visited an unknown website or clicked a suspicious link before updating Chrome?
Immediately update Chrome to the patched version, then consider changing your passwords for sensitive accounts like email, banking, and social media. Monitor your accounts for unusual activity, enable two-factor authentication if not already enabled, and consider running a malware scan with your antivirus software. For very sensitive accounts, monitor login activity and watch for accounts being accessed from unfamiliar locations.
Is it safe to delay updating until the next scheduled update?
No. This is an actively exploited zero-day, meaning attackers are currently weaponizing it against real targets. Delaying the update increases your risk substantially. The patch is stable and tested by millions of users worldwide. The risk of delaying vastly outweighs the minimal risk of any compatibility issues from the update.
How does Google find and patch zero-day vulnerabilities so quickly?
Google runs a threat analysis group that monitors for signs of exploitation through various channels including incident response investigations, security researcher reports, and internal telemetry. Once a zero-day is identified, Google's large security team can often develop and test a patch within days. Google also has a responsible disclosure policy where independent security researchers report vulnerabilities to them before public disclosure.
Will the patch break any of my Chrome extensions or websites I use?
No. Security patches like this only fix underlying code issues and don't alter the extensions API or web platform APIs. All your extensions should continue working exactly as before. If you notice an extension suddenly not working after updating, the issue is likely unrelated to this specific security patch.

Key Takeaways
CVE-2026-2441 is the first actively exploited Chrome zero-day of 2025, representing a critical vulnerability that requires immediate patching. This "use after free" bug in Chrome's CSS engine allows attackers to execute arbitrary code through specially crafted webpages, potentially leading to complete system compromise. Update Chrome to version 145.0.7632.75 or later (Windows/Mac) or 144.0.7559.75 (Linux) immediately by accessing the Help menu and selecting About Google Chrome. While patching is paramount, implementing additional security measures like keeping your operating system updated, using security extensions, and creating separate browser profiles for sensitive activities can provide layered protection. For organizations managing multiple devices, immediate deployment of the patch across all systems should be prioritized, with verification that at least 90% of devices have updated within 24 hours. The broader context shows that zero-day vulnerabilities are increasingly common, particularly those exploited by state-sponsored threat actors, making browser security a critical component of personal and organizational cybersecurity in 2025.

Related Articles
- Surfshark VPN Deal: Save 86% on Premium Plan Plus 3 Extra Months [2025]
- Fake Chrome AI Extensions: How 300K+ Users Got Compromised [2025]
- Surfshark VPN 87% Off: Complete Deal Analysis & VPN Buyer's Guide [2025]
- Apple Zero-Day Flaw CVE-2026-20700: What You Need to Know [2025]
- ExpressVPN 81% Off Deal: Complete 2025 Guide [Updated]
- Microsoft Zero-Day Exploits: Critical Windows & Office Vulnerabilities [2025]
![Chrome Zero-Day CVE-2026-2441: Critical Security Update Guide [2025]](https://tryrunable.com/blog/chrome-zero-day-cve-2026-2441-critical-security-update-guide/image-1-1771259929385.jpg)



