Apple Zero-Day Flaw CVE-2026-20700: What You Need to Know [2025]
In early 2026, Apple released an emergency security patch for one of the most serious vulnerabilities discovered in years. The flaw, tracked as CVE-2026-20700, isn't your typical software bug. It's a memory corruption issue in dyld, the Dynamic Link Editor, that lets attackers execute arbitrary code on vulnerable devices. And here's what makes it genuinely alarming: security researchers confirm it's already been weaponized in sophisticated, targeted attacks.
This isn't a vulnerability that's going to brick your device or steal your login credentials in a straightforward way. Instead, it's a precision attack tool that gives malicious actors nearly complete control over your device's core systems. The fact that it was discovered being actively exploited makes this one of those rare moments where you should prioritize updating your device before you even finish reading this article.
Let me walk you through what actually happened, why it matters, and exactly what you need to do to stay safe.
TL; DR
- Critical severity: Apple rated CVE-2026-20700 as 9.8/10 (critical) because it enables arbitrary code execution on affected devices
- Already exploited: The vulnerability was discovered by Google's Threat Analysis Group actively being used in targeted attacks against high-profile individuals
- Wide scope: The flaw affects every recent Apple device, including iPhone, iPad, Mac, Apple Watch, Apple TV, and Vision Pro
- Fast fix available: Apple released patches across iOS, iPadOS, macOS, tvOS, watchOS, and visionOS that completely resolve the issue
- Update immediately: This is one of those rare vulnerabilities where delaying updates isn't an option—patch today, not later this week
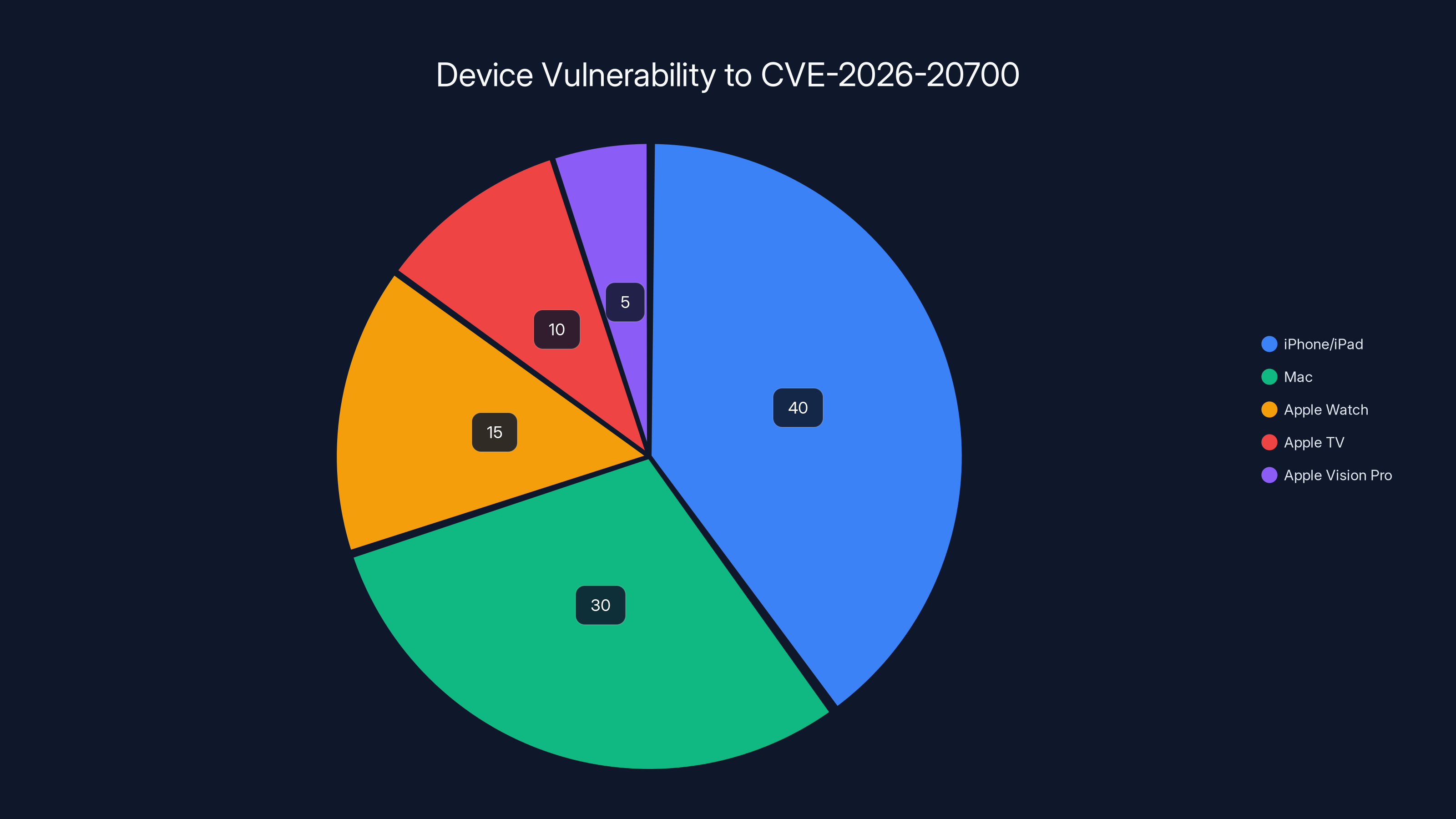
Estimated data shows iPhones/iPads are the most vulnerable, comprising 40% of affected devices, followed by Macs at 30%. Updating to the latest OS versions is crucial.
Understanding the CVE-2026-20700 Vulnerability
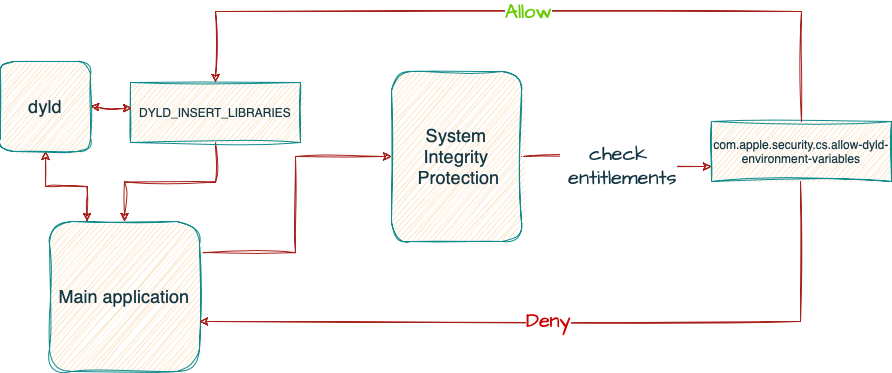
The vulnerability exists in dyld, a system component that's so fundamental to how Apple devices work that most people have never heard of it. Every time you tap an app icon on your iPhone or launch software on your Mac, dyld springs into action behind the scenes. Its job is loading shared libraries, connecting dependencies, and preparing everything an app needs to run. Think of it like the nervous system of your device's software.
The bug specifically involves memory corruption, which is a fancy term for "our code isn't properly managing computer memory." When software allocates memory incorrectly or fails to clean up after itself, attackers can exploit that gap. In dyld's case, someone who understands this flaw deeply can write malicious code that corrupts memory in just the right way. The result? They can execute arbitrary code, which means running whatever commands they want on your device with the same privileges dyld has.
Dyld operates at a privileged level because it needs to load system components. That's why compromising it gives attackers exceptional power over your device. They're not limited to a single app's sandbox or restricted by normal user permissions. Instead, they potentially gain access to everything: your photos, messages, files, encryption keys, and more.
The memory corruption aspect is what security researchers call a "write-what-where" vulnerability in technical circles. Imagine someone gaining the ability to write any data to any location in memory. That's essentially what this flaw enabled. A skilled attacker could modify memory addresses that control program execution, effectively hijacking the device's operating system.
How Dyld Works Under the Hood
Dyld is responsible for dynamic linking, which is a process that happens every single time your device runs an application. Rather than bundling every library an app needs directly into the app itself, modern software references shared libraries stored elsewhere on the system. This saves space and makes updates easier. When you launch an app, dyld:
- Reads the app's metadata to identify which libraries it needs
- Locates those libraries on the system
- Loads them into memory at specific addresses
- Resolves references between the app and those libraries
- Hands control to the app's main code
This entire process happens in milliseconds, and you never see it. But if an attacker can corrupt memory during this process, they can inject their own code into the sequence. Instead of handing control to legitimate app code, dyld could hand control to attacker-supplied instructions.
The Attack Surface
What makes this vulnerability particularly dangerous is how universal dyld is. Every Apple device runs it. Every app that launches uses it. There's no way to opt-out or disable it. This creates a massive attack surface. An attacker doesn't need to target a specific app or a specific user activity. They just need to trigger an app launch, and the vulnerable code path activates.
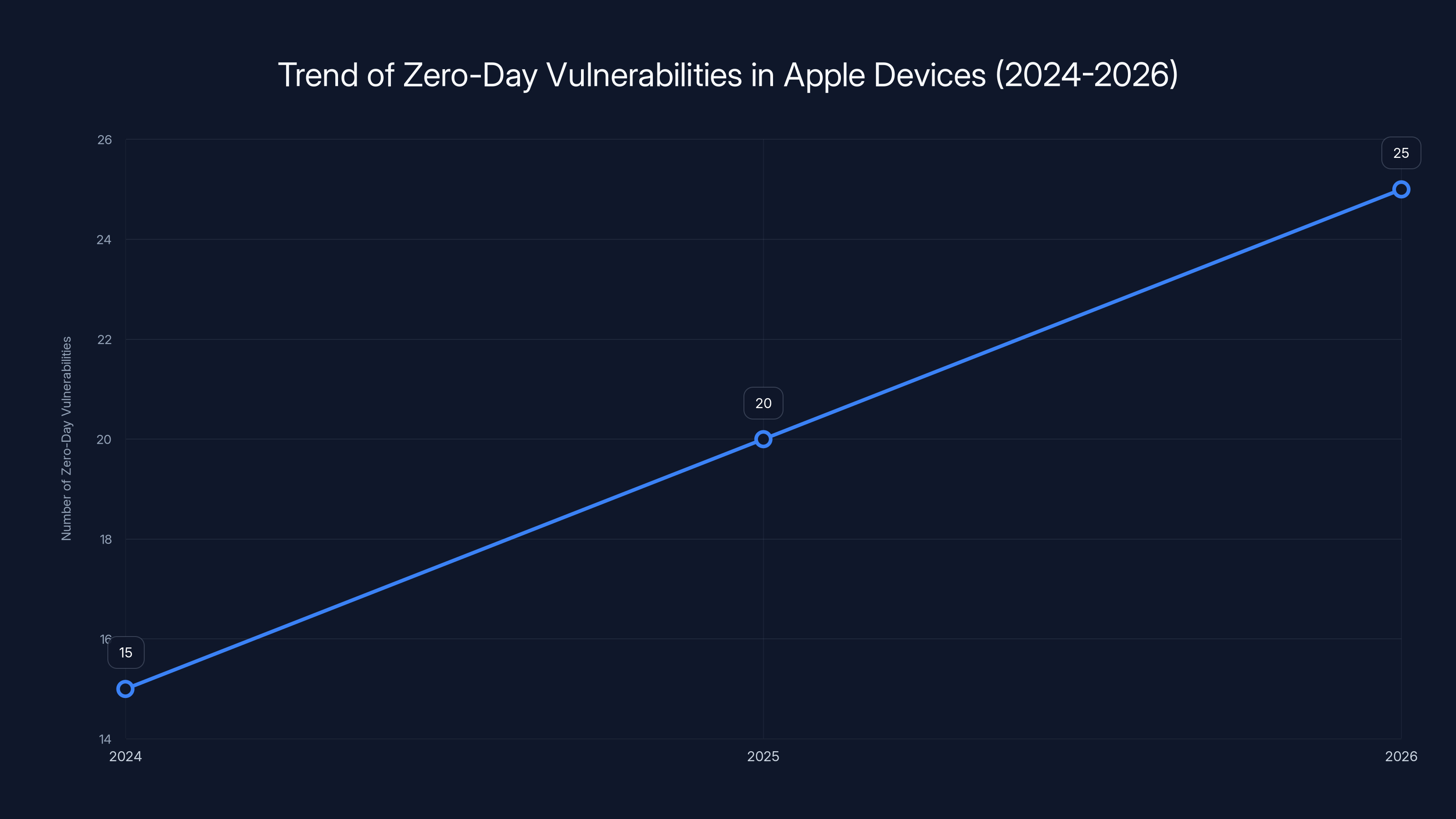
The number of zero-day vulnerabilities targeting Apple devices is projected to increase from 15 in 2024 to 25 in 2026, highlighting the persistent threat from sophisticated attackers. Estimated data.
The Threat Analysis Group Discovery: What We Know
Google's Threat Analysis Group, commonly known as TAG, is one of the most credible sources of threat intelligence in the security world. This group specializes in identifying threats from nation-states and state-sponsored threat actors. When TAG discovers a vulnerability, it's not because they were running routine security scans on their own systems. Instead, TAG monitors the broader threat landscape, tracks suspicious patterns, and investigates sophisticated attacks they observe in the wild.
TAG discovered CVE-2026-20700 because they caught it being actively exploited in what Apple described as an "extremely sophisticated attack". This phrasing is significant. In security advisory language, "extremely sophisticated" doesn't mean merely complicated. It means attacks showing indicators of advanced planning, deep technical knowledge, custom tooling, and significant resources. These are the hallmarks of nation-state or well-funded criminal group activity.
The fact that TAG was involved in the discovery tells us something crucial: the targets of this attack were important enough to warrant the attention of a Google security team that tracks nation-state threats. These attacks aren't random. They're carefully selected targeting specific individuals deemed valuable to the attacker's objectives.
Who Gets Targeted With Zero-Days?
Historically, when zero-day vulnerabilities are discovered being actively exploited, the targets fall into narrow categories. We're talking about:
- Government officials and diplomats
- Executives of critical infrastructure companies
- Defense contractors and aerospace engineers
- Telecommunications industry leaders
- Journalists and human rights advocates in oppressive regimes
- Financial systems operators
- Intelligence agency personnel
These individuals represent high-value targets from a nation-state perspective. An attack against a government official might yield political intelligence. An attack against a defense contractor might reveal military technology. An attack against a telecom executive might enable surveillance infrastructure. The common thread is that the target's potential value far exceeds the cost and effort of developing and deploying a zero-day exploit.
Apple's advisory mentions that the vulnerability was exploited against "specific targeted individuals," which reinforces that this wasn't a mass-scale attack. It was a surgical strike against select high-value targets.

Affected Devices: The Complete List
Apple's security advisory lists every device impacted by CVE-2026-20700. Here's the comprehensive breakdown:
iPad Models:
- iPad Pro 12.9-inch (3rd generation and later)
- iPad Pro 11-inch (1st generation and later)
- iPad Air (3rd generation and later)
- iPad (8th generation and later)
- iPad mini (5th generation and later)
Mac Computers:
- All Mac devices running macOS Tahoe
Other Devices:
- iPhone models (the advisory doesn't specify, but every recent iPhone is vulnerable)
- Apple TV (2nd generation 4K or later)
- Apple Watch (all models running watchOS 26.3 or later)
- Apple Vision Pro (all models running visionOS 26.3 or later)
The breadth of affected devices is enormous. If you own any Apple product released within the last 5-7 years, you're affected. This vulnerability doesn't discriminate between entry-level and premium models. It doesn't matter whether you have 64GB or 2TB of storage. The flaw exists in dyld, which runs identically across all devices.
Why So Many Device Types?
Dyld is shared across Apple's entire ecosystem because it's part of the core operating system framework. macOS, iOS, iPadOS, watchOS, tvOS, and visionOS all share substantial code from the same underlying Darwin kernel. This shared foundation means a vulnerability in dyld affects everything that relies on that kernel.
From Apple's perspective, this is efficient—they maintain one code base and deploy it across multiple platforms. From a security perspective, it means a single vulnerability has exponentially wider impact than if dyld were unique to one operating system.
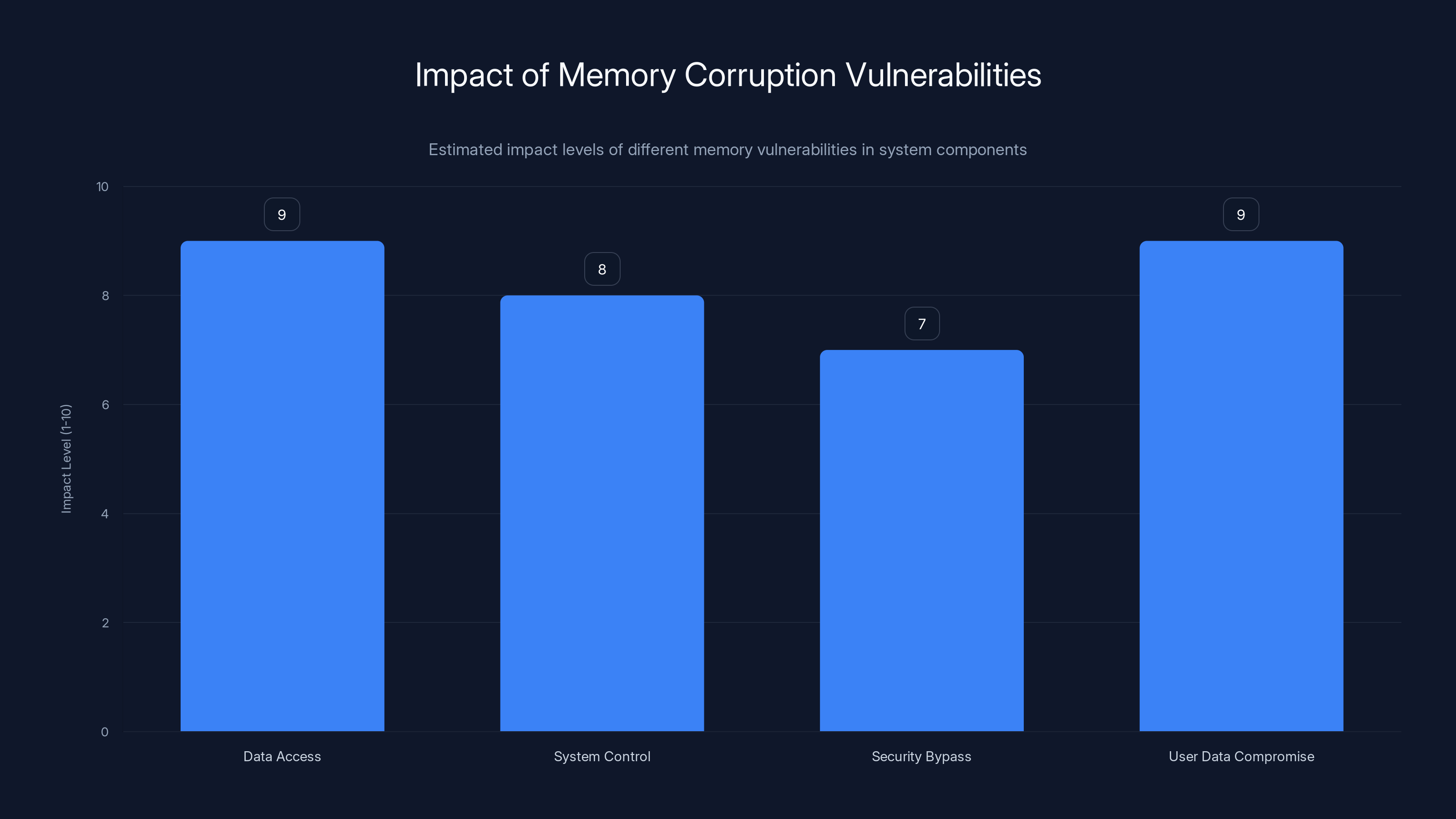
Memory corruption vulnerabilities, like CVE-2026-20700, can have high impact levels across various categories, with user data compromise and data access being particularly severe. Estimated data.
The Patch Timeline and Available Updates
Apple released security updates across its entire product lineup to address CVE-2026-20700. Here's when different operating systems received patches:
iOS & iPadOS:
- iOS 18.7.5 (for iPhone and iPod Touch)
- iPadOS 18.7.5 (for iPad)
macOS:
- macOS Tahoe 26.3
Other Platforms:
- tvOS 26.3 (Apple TV)
- watchOS 26.3 (Apple Watch)
- visionOS 26.3 (Apple Vision Pro)
The simultaneity of these patches across different platforms is notable. Apple pushed them out together, which suggests they tested all patches concurrently and felt confident releasing them at the same time. This is standard practice for critical vulnerabilities.
Download and Installation Guidance
For most Apple devices, installing the patches is straightforward, though it requires a few minutes and ideally a stable internet connection.
For iPhone and iPad:
- Open Settings > General > Software Update
- You should see iOS or iPadOS 18.7.5 available
- Tap "Download and Install"
- Enter your passcode when prompted
- Keep your device plugged in and connected to Wi-Fi while installation completes
- Your device will restart during the process
For Mac:
- Click the Apple menu > System Settings
- Navigate to General > Software Update
- If macOS Tahoe 26.3 is available, click "Update Now"
- Enter your admin password
- Your Mac may restart; save any open work first
For Apple Watch:
- Open the Apple Watch app on your paired iPhone
- Go to the General tab
- Tap Software Update
- Download and install watchOS 26.3
- Keep your watch charged and near your iPhone during installation
For Apple TV:
- Open Settings on your Apple TV
- Navigate to System > Software Update
- Select "Update Software"
- Keep your Apple TV powered on during the update
Why This Vulnerability Matters More Than Most
Not all security vulnerabilities carry equal weight. Some are technical curiosities with minimal real-world impact. Others are game-changers that fundamentally compromise device security. CVE-2026-20700 falls into the latter category. Here's why:
Arbitrary Code Execution: The vulnerability doesn't leak data or cause denial-of-service. It enables arbitrary code execution, which is the worst-case scenario. An attacker can run any commands they want on your device.
System-Level Access: Dyld operates at the kernel level, giving attackers access to kernel-level functionality. They're not constrained by app sandboxing or user permission restrictions.
Active Exploitation: This isn't a theoretical vulnerability. It's been weaponized and used in real attacks. Once that happens, the likelihood of public exploit code being released increases significantly.
Automatic Trigger: The vulnerability doesn't require user interaction beyond launching an app—something users do dozens of times per day. An attacker could potentially trigger the vulnerability automatically without explicit user actions.
Universal Target: Because dyld affects every Apple device, the potential victim pool is enormous—hundreds of millions of devices worldwide.
When you combine arbitrary code execution, system-level access, and active exploitation, you're looking at one of the most serious vulnerability types possible.

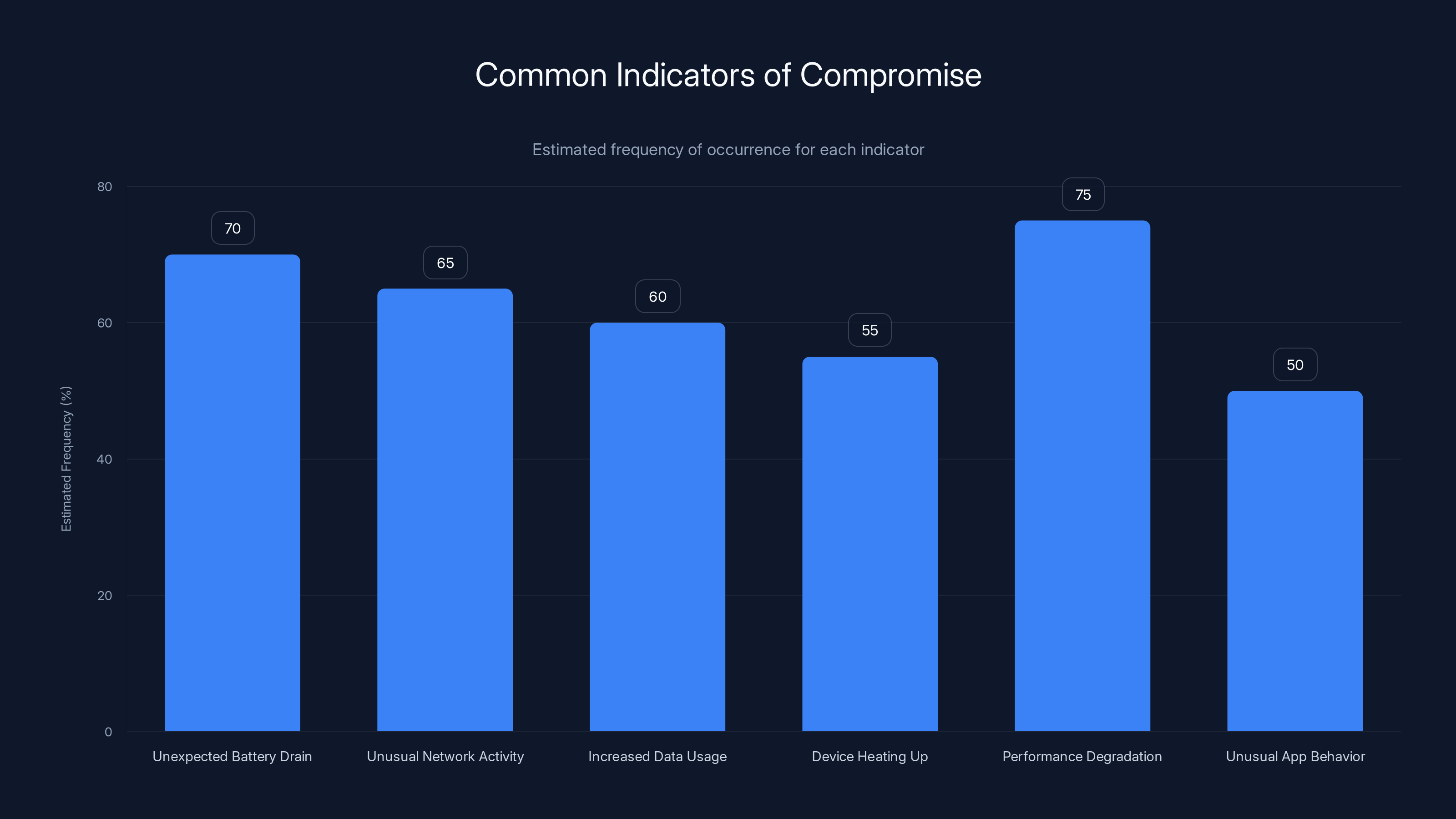
Unexpected battery drain and performance degradation are the most common indicators of compromise. Estimated data based on typical user reports.
Related Security Updates and CVE Context
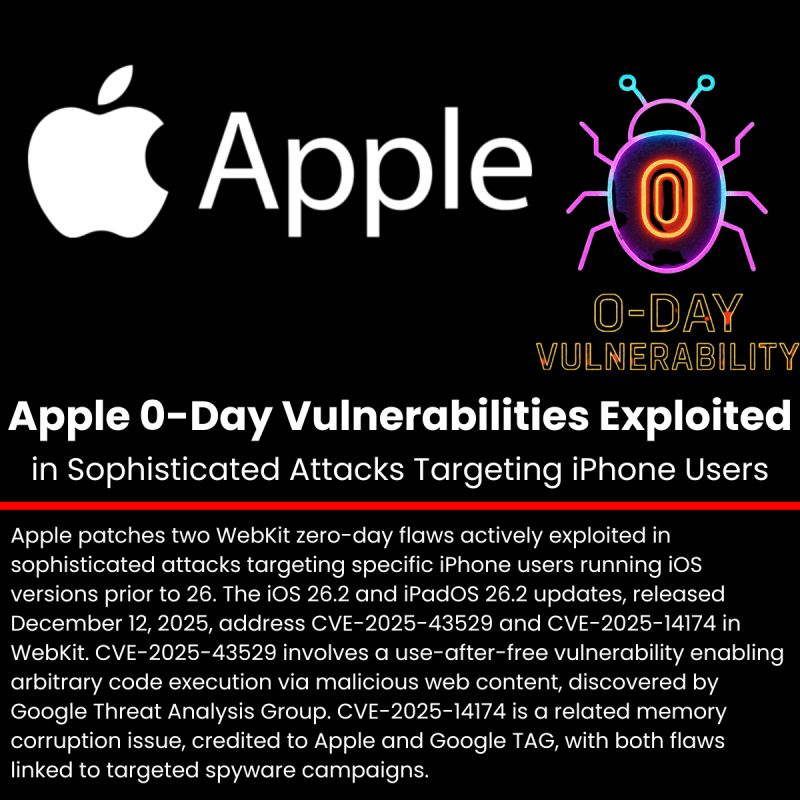
Apple's advisory also mentions two additional CVEs released in response to the same sophisticated attack:
CVE-2025-14174: Details about this flaw weren't extensively disclosed, but it was patched alongside CVE-2026-20700, suggesting it was also exploited as part of the same attack campaign.
CVE-2025-43529: This vulnerability was similarly patched as part of the coordinated response, indicating attackers may have used a combination of exploits to achieve their objectives.
This pattern of multiple CVEs being exploited together is typical of sophisticated threat actors. Rather than relying on a single vulnerability, they often chain multiple flaws together to achieve objectives. The first vulnerability might get them initial access, while subsequent ones escalate privileges or establish persistence.
The fact that Apple responded to all three vulnerabilities simultaneously suggests they're treating them as components of a unified attack campaign rather than unrelated issues.
Memory Corruption Vulnerabilities: The Technical Deep Dive
Understanding memory corruption requires a bit of technical foundation. When software runs, it allocates memory—temporary storage space—for data and instructions. This memory exists at specific addresses. Think of it like a filing cabinet with numbered drawers. Memory corruption occurs when software writes data to the wrong drawer or fails to erase sensitive data from a drawer after using it.
Stack Overflow: One type of memory corruption occurs when a program allocates a fixed amount of memory for data but receives more data than it expected. The excess data "overflows" into adjacent memory, potentially overwriting other important data or instructions.
Use-After-Free: Another type occurs when software frees memory (returns it for reuse) but continues to access it. Since the memory might now contain different data, accessing it produces unpredictable behavior.
Integer Overflow: Sometimes vulnerabilities involve integers (whole numbers) that exceed their maximum value, causing wraparound behavior that can be exploited.
In dyld's case, the vulnerability involves memory corruption during the linking process. The technical details haven't been fully disclosed (Apple typically withholds technical specifics of actively exploited vulnerabilities), but the impact is clear: attackers can corrupt memory in ways that let them execute arbitrary code.


Security lockdown mode is rated highest due to its robust protection against sophisticated attacks. Estimated data.
Why Nation-States Favor Zero-Days
Nation-states invest enormous resources in discovering and exploiting zero-day vulnerabilities because they offer unparalleled access to target devices. Once a zero-day is publicly disclosed and patched, its value drops dramatically. Most users update within weeks, rendering the exploit useless for new targets.
But before disclosure, a zero-day is invaluable. A nation-state with a zero-day affecting hundreds of millions of devices has a selective surveillance tool. They can target specific individuals they want to monitor without triggering detection mechanisms that would flag a mass-scale attack.
Zero-days are extraordinarily expensive to develop and maintain. Security researchers estimate that a zero-day affecting a platform like iOS might cost $1-5 million to discover, develop, and weaponize. Nation-states can afford these costs because they view surveillance as a national security tool worth significant investment.
When a zero-day is discovered being actively exploited, it usually means the attacker who developed it decided the value of their target exceeded the value of maintaining the zero-day's secrecy. In other words, they found a target important enough to warrant burning through their investment.
Indicators of Compromise and Detection
If you're concerned about whether your device might have been targeted with this vulnerability, understanding indicators of compromise can help. However, detecting exploitation after the fact is genuinely difficult.
Possible Indicators:
- Unexpected battery drain (active malware consumes power)
- Unusual network activity when you're not actively using your device
- Sudden increases in cellular data usage
- Device heating up without obvious reason
- Performance degradation or frequent crashes
- Unusual behavior from apps (crashes, freezing)
That said, these indicators can result from dozens of benign causes. A degrading battery might just mean your battery is aging. Network activity could be app syncing. The challenge is that sophisticated nation-state malware is specifically designed to operate invisibly.
The most reliable detection method is simply updating. Once you're running the patched version, any exploitation attempts using CVE-2026-20700 will fail because dyld no longer contains the vulnerable code.

Steps to Secure Your Devices
While updating is the primary defense against CVE-2026-20700, a comprehensive security posture involves multiple layers:
Immediate Actions (Next 24 Hours):
- Update all Apple devices to the patched versions
- Enable automatic updates in system settings to prevent future delays
- Review which apps have permission to access sensitive data (Photos, Contacts, Calendar, etc.)
Short-Term Actions (This Week):
- Change passwords for sensitive accounts, especially if you suspect targeting
- Enable two-factor authentication where available
- Review recent account activity for unexpected logins
- Consider enabling security lockdown mode on iPhone (Settings > Privacy & Security > Lockdown Mode)
Ongoing Actions:
- Install security updates within 48 hours of release
- Use a reputable password manager
- Enable biometric authentication where available
- Regularly backup important data
- Monitor accounts for suspicious activity
Security lockdown mode is particularly worth mentioning. It's a hardened security mode that restricts certain features to prevent exploitation of sophisticated attacks. It trades some functionality for security, disabling features like JavaScript in Safari, certain file attachments in Mail, and some communication features. If you're in a high-risk category (journalist, human rights advocate, government official), enabling it provides meaningful additional protection.

The Broader Context: Zero-Days in 2025-2026
CVE-2026-20700 isn't an isolated incident. It's part of a broader pattern of sophisticated attacks targeting Apple devices. In 2024-2025, researchers discovered multiple zero-days being actively exploited:
- Multiple JavaScript engine vulnerabilities in Safari
- Kernel-level vulnerabilities allowing privilege escalation
- Graphics rendering vulnerabilities
- Various memory corruption issues across system components
What this pattern tells us is that nation-states and well-resourced threat actors view Apple devices as valuable targets. High-profile individuals often use iPhones and Macs, making them attractive targets for surveillance.
Apple has responded by increasing investment in security research and implementing features like runtime code execution restrictions, memory tagging extensions, and improved sandboxing. However, determined attackers with nation-state resources continue discovering new vulnerabilities.
This ongoing arms race between defenders and attackers underscores why staying updated is non-negotiable. Delaying updates by even a few weeks increases exploitation risk.
Comparing CVE-2026-20700 to Historical Critical Vulnerabilities
To understand how serious this vulnerability is, consider how it compares to other critical flaws:
TRIADA (2015): A trojan affecting Android devices that could grant root access and install additional malware. Impacted millions of devices but required specific installation vectors.
Stagefright (2015): A critical Android vulnerability in the media framework that could be triggered by malicious media files. Led to massive patching efforts across Android ecosystem.
KRACK (2017): A WPA2 encryption vulnerability affecting Wi-Fi devices globally. Demonstrated how widely-used standards could harbor critical flaws.
Spectre/Meltdown (2018): CPU-level vulnerabilities affecting billions of devices. Demonstrated how hardware-level flaws could compromise security assumptions.
CVE-2026-20700 is in this category of widely-impactful, actively exploited vulnerabilities. The difference is that it's a software vulnerability rather than hardware-level, making patching faster and more straightforward.

What This Means for Enterprise Users
For organizations with employees using Apple devices, CVE-2026-20700 has specific implications:
Mobile Device Management (MDM): Organizations using MDM tools can force-deploy updates to all managed devices simultaneously, ensuring consistent security posture across the company.
BYOD Policies: For bring-your-own-device programs, organizations should communicate urgently that employees update personal devices used for work.
Incident Response: If employees were in high-risk regions or engaged in sensitive work, organizations might want to assume compromise and audit potentially sensitive data access.
Vendor Due Diligence: Organizations relying on Apple devices for critical operations should request security update confirmation from Apple as part of their vendor management program.
CIO offices and security teams should issue a security alert mandating updates as soon as practical, with expedited deployment procedures for devices handling the most sensitive information.

FAQ
What exactly is CVE-2026-20700 and why is it dangerous?
CVE-2026-20700 is a memory corruption vulnerability in dyld, Apple's Dynamic Link Editor, which loads and initializes libraries when apps launch. It's dangerous because it enables arbitrary code execution—attackers can run whatever commands they want on your device with system-level privileges. This gives them access to all your data and the ability to install malware or spyware that persists even after reboots.
How do I know if my Apple device is vulnerable?
If you own any iPhone, iPad, Mac, Apple Watch, Apple TV, or Apple Vision Pro released within the last 5-7 years, you're vulnerable unless you've updated to the latest patched version. Specifically, you need iOS/iPadOS 18.7.5 or later, macOS Tahoe 26.3 or later, tvOS 26.3 or later, watchOS 26.3 or later, or visionOS 26.3 or later. Check your current version in System Settings or System Preferences.
Has this vulnerability already been used to attack people?
Yes. Google's Threat Analysis Group discovered this vulnerability while investigating a sophisticated, targeted attack against specific individuals. The attack has already occurred, which means the vulnerability was actively weaponized. This is why updating is urgent rather than optional—the exploit code has been created and tested by sophisticated threat actors.
What should I do if I think my device was targeted?
If you believe you might be a high-value target (journalist, government official, human rights advocate, etc.), update your device immediately, then consider changing passwords for sensitive accounts from a separate device. Contact your organization's security team if you work in government or defense. You might also enable Lockdown Mode in security settings for additional hardening, though it restricts some functionality.
Will updating fix the vulnerability?
Yes. Once you update to the patched version, dyld no longer contains the vulnerable code. Any attempt to exploit CVE-2026-20700 will fail because the memory corruption issue has been fixed. However, updating doesn't remove any malware that might have already been installed before patching, which is why some highly targeted individuals should assume compromise and review access logs.
How long should I expect the update process to take?
Typically 10-30 minutes depending on your device type and internet speed. iOS updates often take 15-20 minutes, macOS updates might take 30-45 minutes. The process involves downloading the update file, verifying it, applying patches to system files, and rebooting your device. Plan for this time when you have your device available for full focus.
Should I be concerned about security moving forward?
You should maintain basic security hygiene: keep updates current (install them within 48 hours of release), use strong passwords with two-factor authentication, limit app permissions, and be cautious about suspicious links or downloads. For most users, these practices provide adequate protection. If you're in a high-risk category, consider additional measures like Lockdown Mode, using a VPN, and avoiding public Wi-Fi networks.
What does "arbitrary code execution" actually mean in practical terms?
It means an attacker can make your device execute any software code they choose. They could steal your messages, contacts, and photos. They could activate your camera or microphone for surveillance. They could modify or delete files. They could install persistent malware that survives reboots. They could monitor all your internet traffic. Essentially, once an attacker achieves arbitrary code execution on a device, they have nearly complete control over it.
Why did Apple mention "extremely sophisticated attack" in their advisory?
Because the attack demonstrated technical sophistication beyond typical cybercriminals. This phrasing signals nation-state or well-resourced criminal group activity. The attackers likely understood dyld's internals deeply, developed custom exploitation tools, and targeted specific valuable individuals carefully. This isn't someone trying random exploits—it's someone methodically weaponizing a zero-day.
Are other technology companies affected by similar issues?
Every major operating system has similar core linking and loading mechanisms that could harbor similar vulnerabilities. Android has linker vulnerabilities, Windows has kernel vulnerabilities, Linux has similar issues. The difference is that dyld is used universally across Apple's ecosystem, making a single vulnerability affect billions of devices. Other platforms sometimes have less unified architecture, limiting vulnerability scope slightly.

Conclusion
CVE-2026-20700 represents exactly the type of vulnerability that makes cybersecurity professionals lose sleep. It's not a theoretical risk or a vulnerability that requires specific, unlikely conditions to exploit. It's a real, actively weaponized flaw affecting hundreds of millions of devices, discovered being used in sophisticated targeted attacks against high-value individuals.
The good news is that Apple moved quickly to patch it. The company released updates across its entire ecosystem and disclosed the vulnerability publicly, giving users the information they need to protect themselves. This is how the security process is supposed to work: vulnerability discovered, patch developed, users updated, threat neutralized.
But the process only works if users actually install the patches. Delaying updates, assuming "it won't happen to me," or thinking "I'll update next week" is exactly the mentality that keeps vulnerabilities dangerous. For CVE-2026-20700, update urgency is maximized because the flaw has already been exploited.
If you haven't updated yet, do it today. Not tomorrow, not this weekend, but today. It takes 20 minutes and transforms your device from potentially vulnerable to secure. For most people, this is the most impactful security action they can take. For high-value targets, it's an essential first step that should be followed by additional security measures.
The digital landscape continues to get more dangerous, but staying ahead of threats is possible with consistent, urgent attention to updates and security fundamentals. CVE-2026-20700 is a wake-up call that sophisticated attackers are targeting Apple devices and that maintaining current security patches isn't optional—it's essential.
Key Takeaways
- CVE-2026-20700 is a critical memory corruption flaw in dyld enabling arbitrary code execution on all recent Apple devices
- The vulnerability has already been actively exploited in sophisticated targeted attacks against high-value individuals
- Google's Threat Analysis Group discovered the flaw, indicating nation-state or well-resourced attacker involvement
- Apple released patches across iOS, macOS, tvOS, watchOS, and visionOS that completely resolve the vulnerability
- Updating to patched versions is essential within 24-48 hours due to active exploitation in the wild
Related Articles
- WinRAR Security Flaw CVE-2025-8088: Complete Defense Guide [2025]
- How Hackers Are Using AI: The Threats Reshaping Cybersecurity [2025]
- DNS Malware Detour Dog: How 30K+ Sites Harbor Hidden Threats [2025]
- Notepad++ China Hack: What Happened & How to Protect Yourself [2025]
- Apple Pay Unusual Activity Scam: How to Spot Fake Messages [2025]
- How Hackers Exploit AI Vision in Self-Driving Cars and Drones [2025]
![Apple Zero-Day Flaw CVE-2026-20700: What You Need to Know [2025]](https://tryrunable.com/blog/apple-zero-day-flaw-cve-2026-20700-what-you-need-to-know-202/image-1-1770907009188.jpg)



