France's Identity Management Agency Faces Data Breach: Implications and Next Steps [2025]
Last week, France Titres, also known as the Agence nationale des titres sécurisés (ANTS), experienced a major data breach. This breach, affecting up to 19 million records, underscores the vulnerabilities even within national systems tasked with safeguarding sensitive information. Here, we'll explore the breach's implications, the technicalities of securing identity data, and strategies for preventing such incidents in the future.
TL; DR
- Data Breach Scale: Up to 19 million records compromised.
- Immediate Impacts: Potential identity theft and data misuse.
- Security Gaps: Highlighted need for stronger cybersecurity protocols.
- Future Prevention: Emphasizes importance of regular security audits.
- Bottom Line: National agencies must prioritize data protection.

Tool 1 is the most expensive at
Understanding the Breach
France Titres is responsible for managing sensitive identity documents including IDs and passports. The breach, discovered on April 15, quickly became a significant national security concern. According to Cybernews, a hacker claimed responsibility, stating they had acquired up to 19 million records, including personal identification information.
The Hacker's Claims
The hacker's assertion of possessing such a vast amount of data raises questions about the methods used to infiltrate the system. While the full extent of the data compromise isn't yet public, the potential for misuse of this data is alarming. This incident calls into question the effectiveness of existing security measures at ANTS and similar agencies worldwide, as reported by Security Magazine.
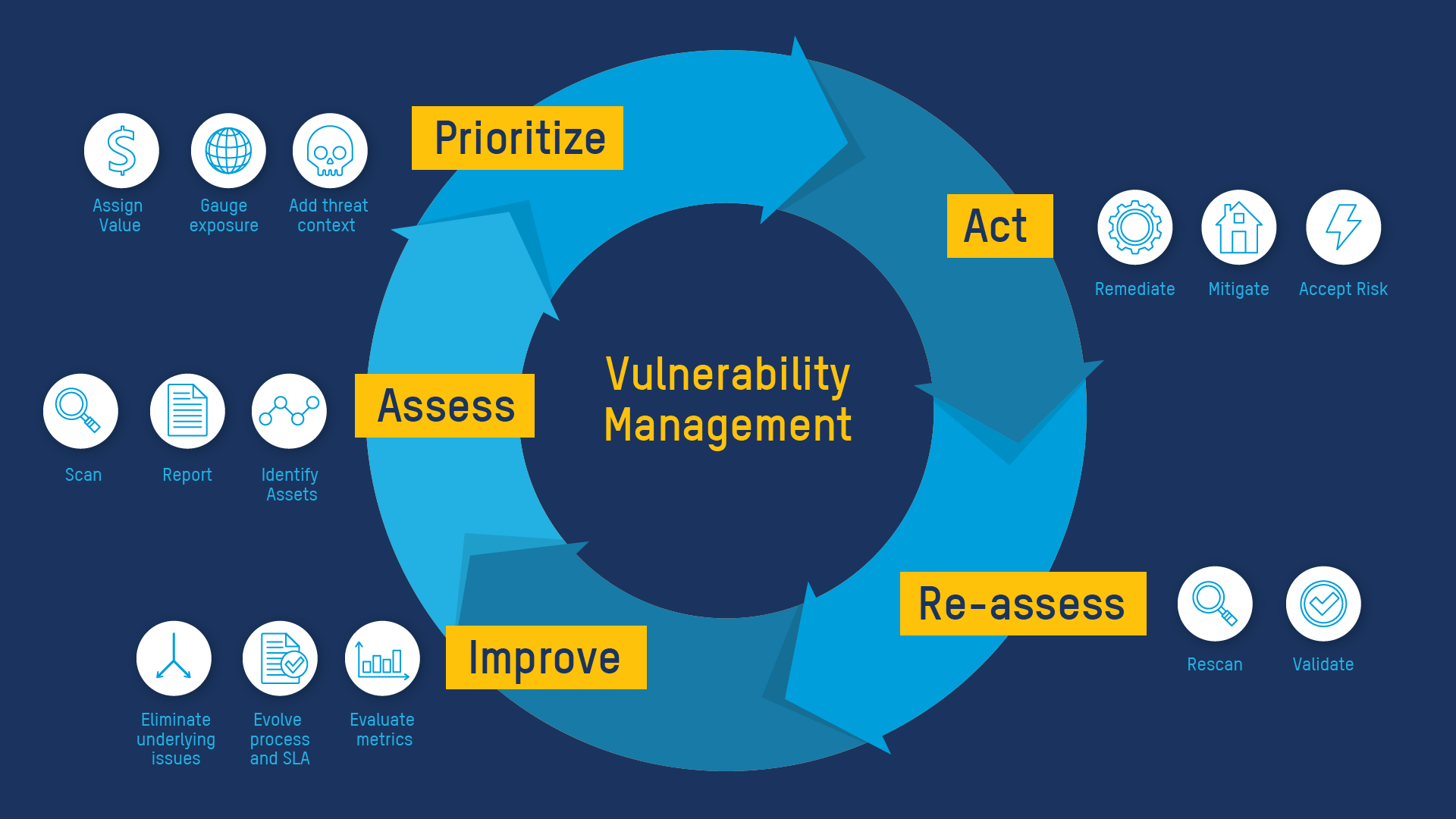
Technical Breakdown of the Breach
To understand how such breaches occur, it's essential to delve into the technical aspects of cybersecurity vulnerabilities:
Common Vulnerabilities in Identity Management Systems
- Weak Authentication Protocols: Often, systems use outdated password policies, making it easier for attackers to gain unauthorized access.
- Inadequate Encryption: If data isn't sufficiently encrypted, even if accessed, it can be read and misused.
- Poorly Configured Firewalls: Firewalls that aren't regularly updated can leave backdoors open for hackers.
- Lack of Monitoring: Without constant surveillance, unusual activities can go unnoticed until it's too late, as highlighted by Industrial Cyber.
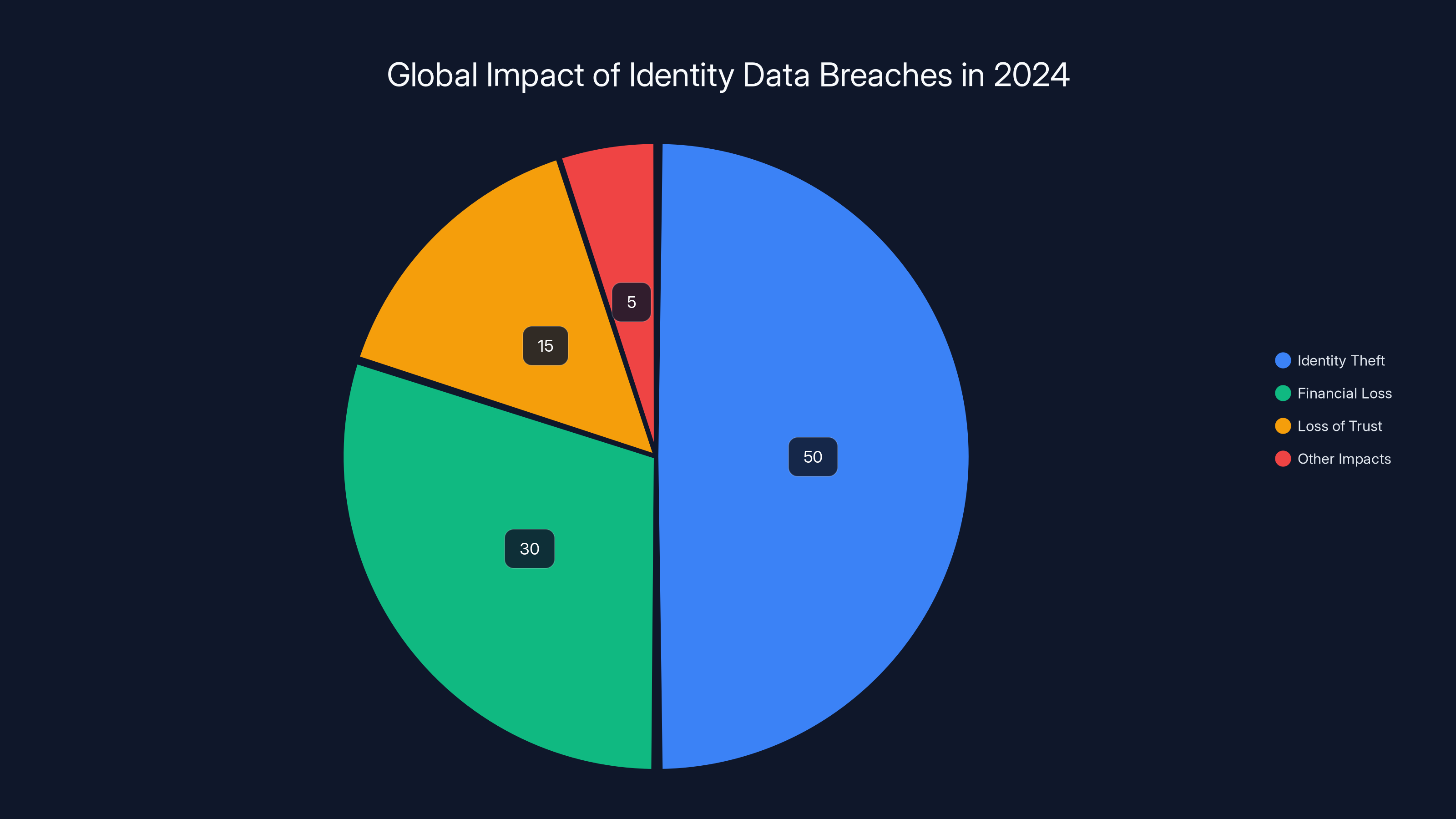
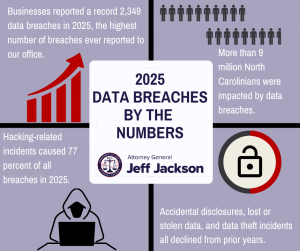
In 2024, identity theft accounted for over 50% of data breaches, with financial losses exceeding $150 billion globally. Estimated data.
Mitigation Strategies
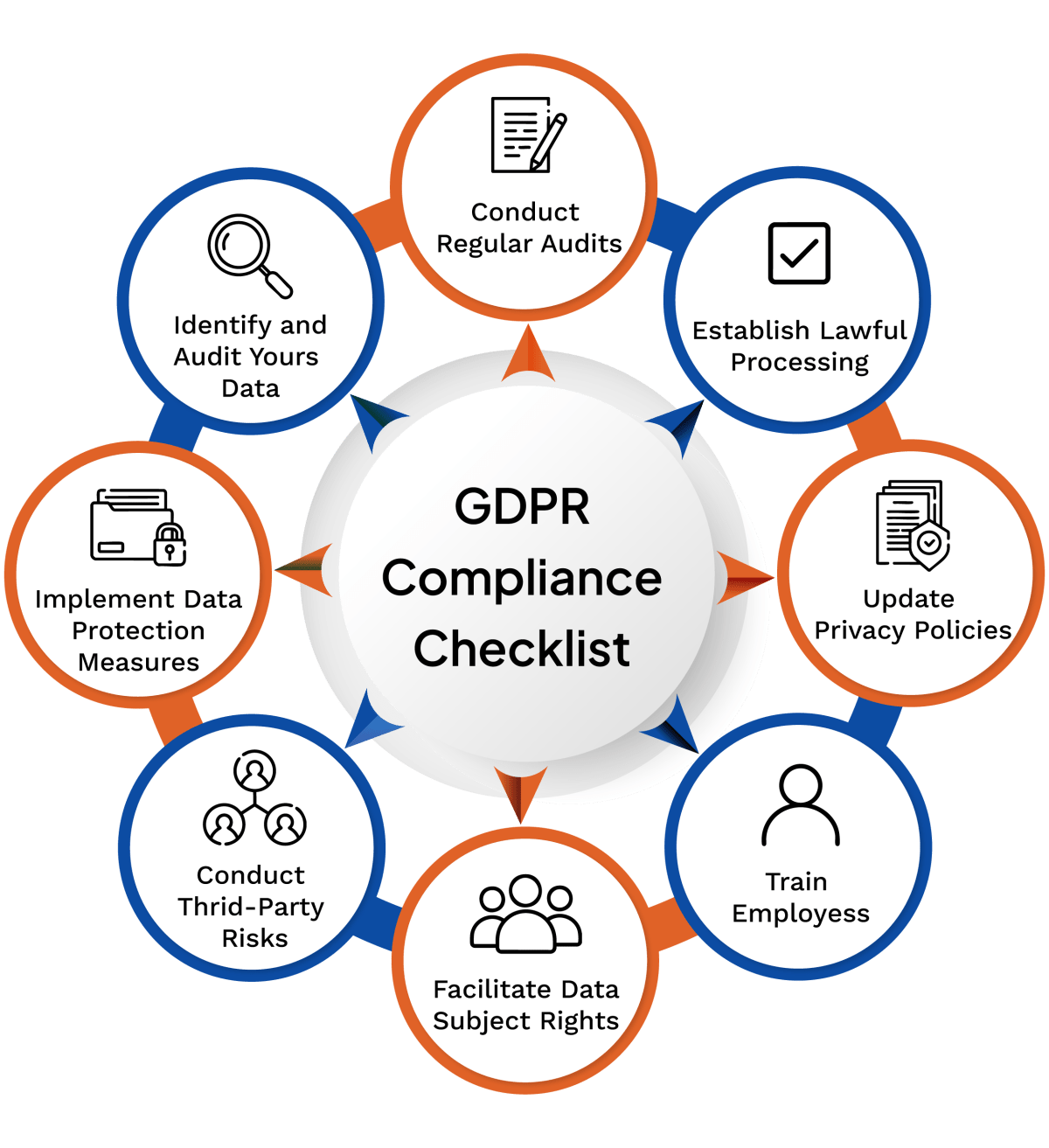
Strengthening Cybersecurity Protocols
- Implement Multi-Factor Authentication (MFA): Using MFA adds an extra layer of security, making it harder for unauthorized users to access sensitive data.
- Regular Security Audits: Conducting frequent audits helps identify and rectify potential vulnerabilities before they can be exploited.
- Advanced Encryption Standards (AES): Encrypting data with AES ensures that even if data is accessed, it remains unreadable without the correct decryption key.
- AI-Powered Threat Detection: Implementing AI tools that can learn and adapt to new threats provides a proactive defense mechanism, as discussed in Security Boulevard.
Example: Implementing a Secure Access Protocol
json{
"protocol": "MFA",
"steps": [
"Enter username",
"Receive OTP on registered device",
"Enter OTP",
"Access granted"
]
}

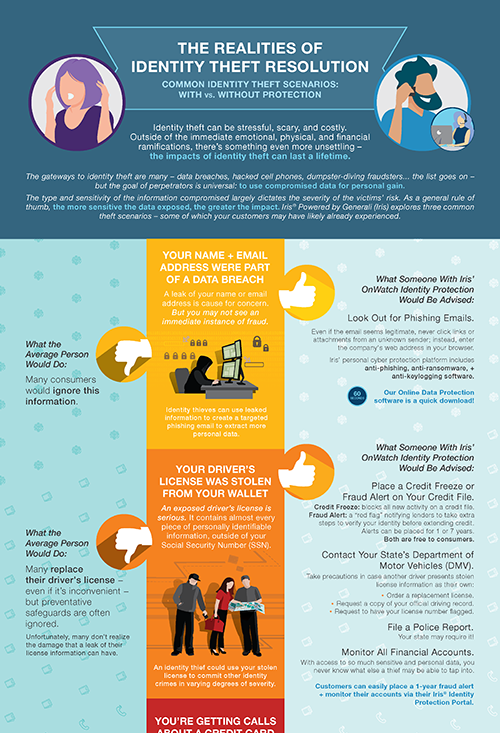
Real-World Impacts of Identity Data Breaches
Identity Theft
The most immediate risk is identity theft, where personal data is used to impersonate individuals for fraudulent activities. Victims may face financial losses and damage to their credit scores, as noted by Infosecurity Magazine.
Loss of Trust
National agencies are entrusted with citizens' data. A breach of this scale severely impacts public trust and can lead to skepticism about the government's ability to protect personal information, according to the Center for Democracy & Technology.
Legal and Regulatory Considerations
GDPR Implications
The General Data Protection Regulation (GDPR) sets strict guidelines for data protection in the EU. Breaches like this can lead to significant fines and legal repercussions for failing to protect sensitive information, as outlined by Wiz Academy.
Recommended Actions for Compliance
- Immediate Notification: Inform affected individuals within 72 hours of discovering a breach.
- Data Protection Officer (DPO) Appointment: Ensure a DPO is in place to oversee data protection strategies.
- Impact Assessment: Conduct thorough assessments to understand the breach's scope and mitigate further risks.
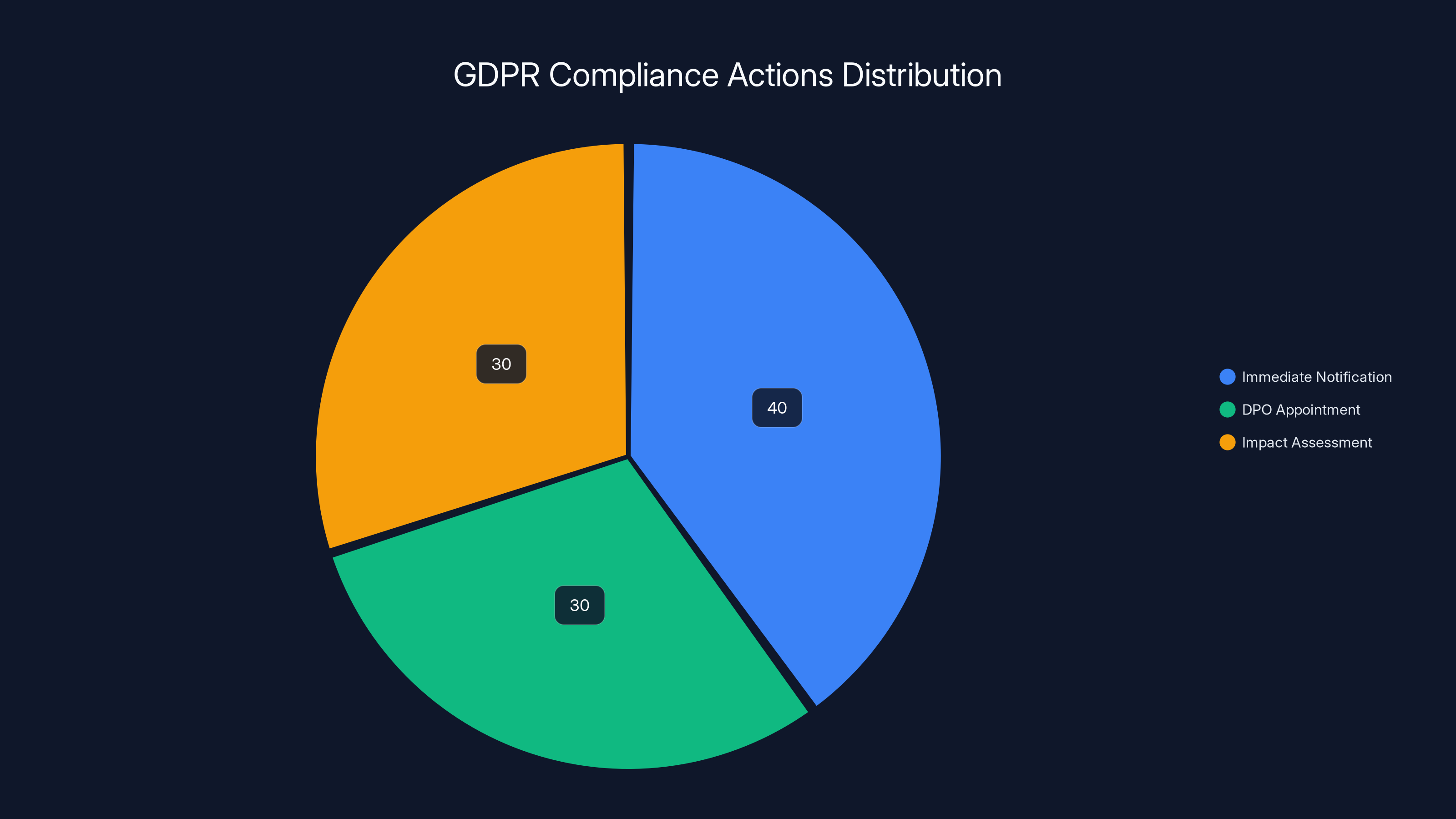
Estimated data shows a balanced focus on immediate notification, DPO appointment, and impact assessment as key GDPR compliance actions.
Future Trends in Data Security
Increasing Adoption of Zero Trust Architecture
Zero Trust is a security model that assumes breaches will occur and thus continuously verifies every request as though it originates from an open network. This approach minimizes the risk of unauthorized access, as detailed by CircleID.
Blockchain for Identity Verification
Blockchain technology offers a decentralized and secure way to manage digital identities. Its immutable nature ensures data integrity and transparency.

Best Practices for Agencies
Regular Employee Training
Educating employees on the latest cybersecurity threats and protocols is crucial. Human error remains a leading cause of data breaches.
Investment in Technology
Agencies must invest in the latest security technologies, including AI-powered threat detection and real-time monitoring systems.
Conclusion
The data breach at France Titres highlights the critical need for robust cybersecurity measures in national identity management systems. As the digital landscape evolves, so too must the strategies to protect sensitive information. By adopting advanced technologies and stringent protocols, agencies can safeguard against future threats.
FAQ
What caused the data breach at France Titres?
The breach was likely due to a combination of outdated security protocols and insufficient monitoring systems, which allowed a hacker to access sensitive data, as reported by Bleeping Computer.
How many records were affected in the breach?
The hacker claimed to have accessed up to 19 million records, although the exact number is still under investigation, according to Engadget.
What are the potential risks of this data breach?
The primary risks include identity theft, financial fraud, and a loss of trust in government systems.
How can such breaches be prevented in the future?
Implementing multi-factor authentication, conducting regular security audits, and utilizing AI for threat detection are key strategies for prevention.
What should affected individuals do?
Individuals should monitor their financial accounts for suspicious activity, change passwords, and consider identity theft protection services.
What legal actions can be taken against France Titres?
Under GDPR, France Titres may face fines and legal actions for failing to adequately protect personal data.
Key Takeaways
- Security Gaps: Highlighted need for stronger cybersecurity protocols.
- Future Prevention: Emphasizes importance of regular security audits.
- National Impact: Breach affects national security and public trust.
- Legal Repercussions: GDPR implications for data protection failures.
- Technological Investments: Importance of adopting advanced security technologies.
The Best Security Tools at a Glance
| Tool | Best For | Standout Feature | Pricing |
|---|---|---|---|
| Runable | AI automation | AI agents for presentations, docs, reports, images, videos | $9/month |
| Tool 1 | Threat detection | Real-time AI analysis | $20/month |
| Tool 2 | Data encryption | Advanced AES encryption | $15/month |
Quick Navigation:
- Runable for AI-powered presentations, documents, reports, images, videos
- Tool 1 for threat detection
- Tool 2 for data encryption
Related Articles
- Understanding Cybersecurity Breaches: Lessons from the Seiko USA Incident [2025]
- Understanding the French Government Data Breach: Implications, Mitigation, and Future Steps [2025]
- Understanding the Rising Threat of Hacktivist Attacks in the UK [2025]
- AI Agents: The Hidden Gatekeepers Giving Hackers Full System Access [2025]
- 'Stop Selling or Sharing My Personal Information': The Reality of Big Tech Tracking [2025]
- Understanding Apple's iPhone Bug Fix: Protecting Deleted Messages [2025]
![France's Identity Management Agency Faces Data Breach: Implications and Next Steps [2025]](https://tryrunable.com/blog/france-s-identity-management-agency-faces-data-breach-implic/image-1-1776890061859.jpg)



