Inside the Kraken Extortion Attack: How Crypto Giants Defend Against Cyber Threats [2025]
Last week, the cryptocurrency exchange giant Kraken announced that it was the target of an extortion attack. Early reports suggest that attackers obtained sensitive internal videos from Kraken's support systems. This breach, while not compromising any funds, exposed around 2,000 client accounts to potential privacy risks. Kraken has refused to meet the attackers' demands, instead opting to bolster their security measures and cooperate with authorities.
TL; DR
- Kraken faced an extortion attack: Internal videos were leaked, exposing client data.
- No funds were compromised: However, around 2,000 accounts were at privacy risk.
- Kraken refused to pay ransom: Opted for security enhancements and legal action.
- Cryptocurrency platforms remain vulnerable: Due to decentralized and anonymous nature.
- Future trends suggest more sophisticated attacks: Preparing robust defenses is crucial.

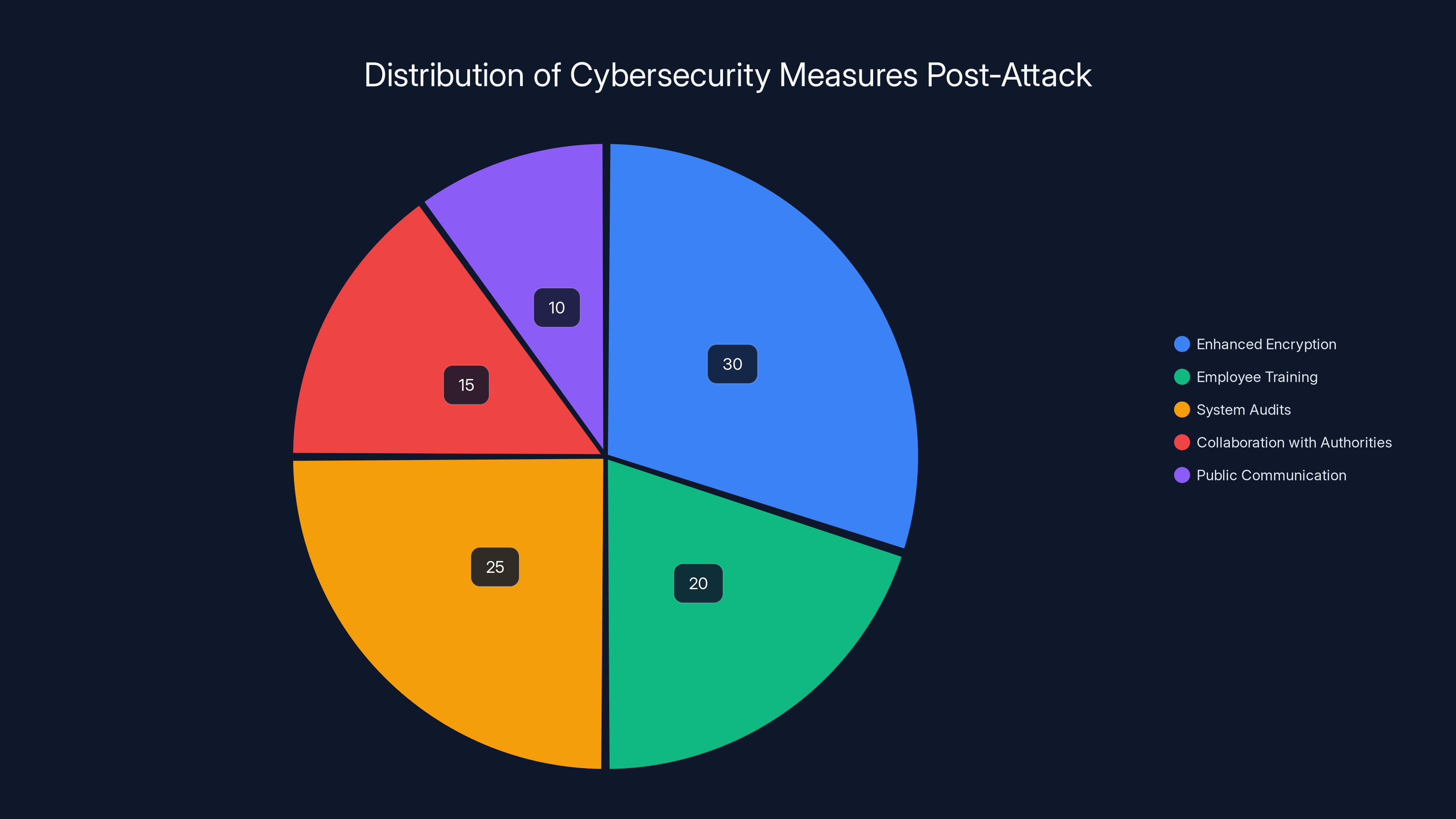
Estimated data shows Kraken's focus on enhancing encryption and conducting system audits as primary responses to the extortion attack.
The Anatomy of the Attack
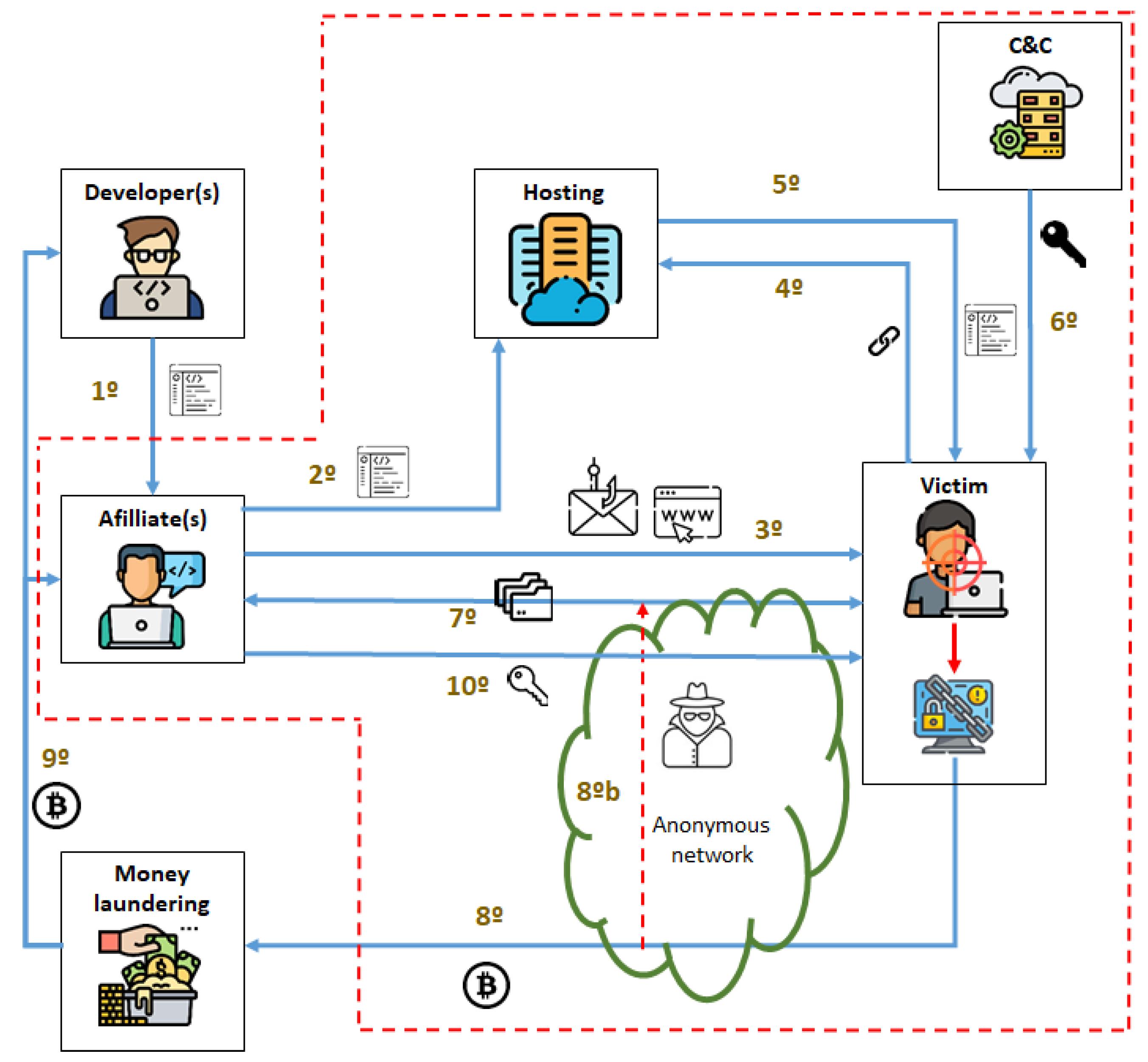
The attack on Kraken underscores the evolving nature of cyber threats faced by crypto exchanges. Extortion attacks typically involve threatening to release sensitive data unless a ransom is paid. In Kraken’s case, the attackers managed to leak videos from their support system, which could potentially include customer interactions and sensitive account information.
How Did the Attack Happen?
While specifics are still under investigation, initial findings suggest that the breach might have involved insider threats or compromised credentials. Insider threats often pose significant risks as they have legitimate access to sensitive systems. This incident highlights the importance of comprehensive insider threat programs.
Common methodologies for such breaches include:
- Phishing attacks: Tricking employees into divulging credentials.
- Credential stuffing: Using leaked credentials from other breaches.
- Exploiting software vulnerabilities: Taking advantage of unpatched systems or applications.
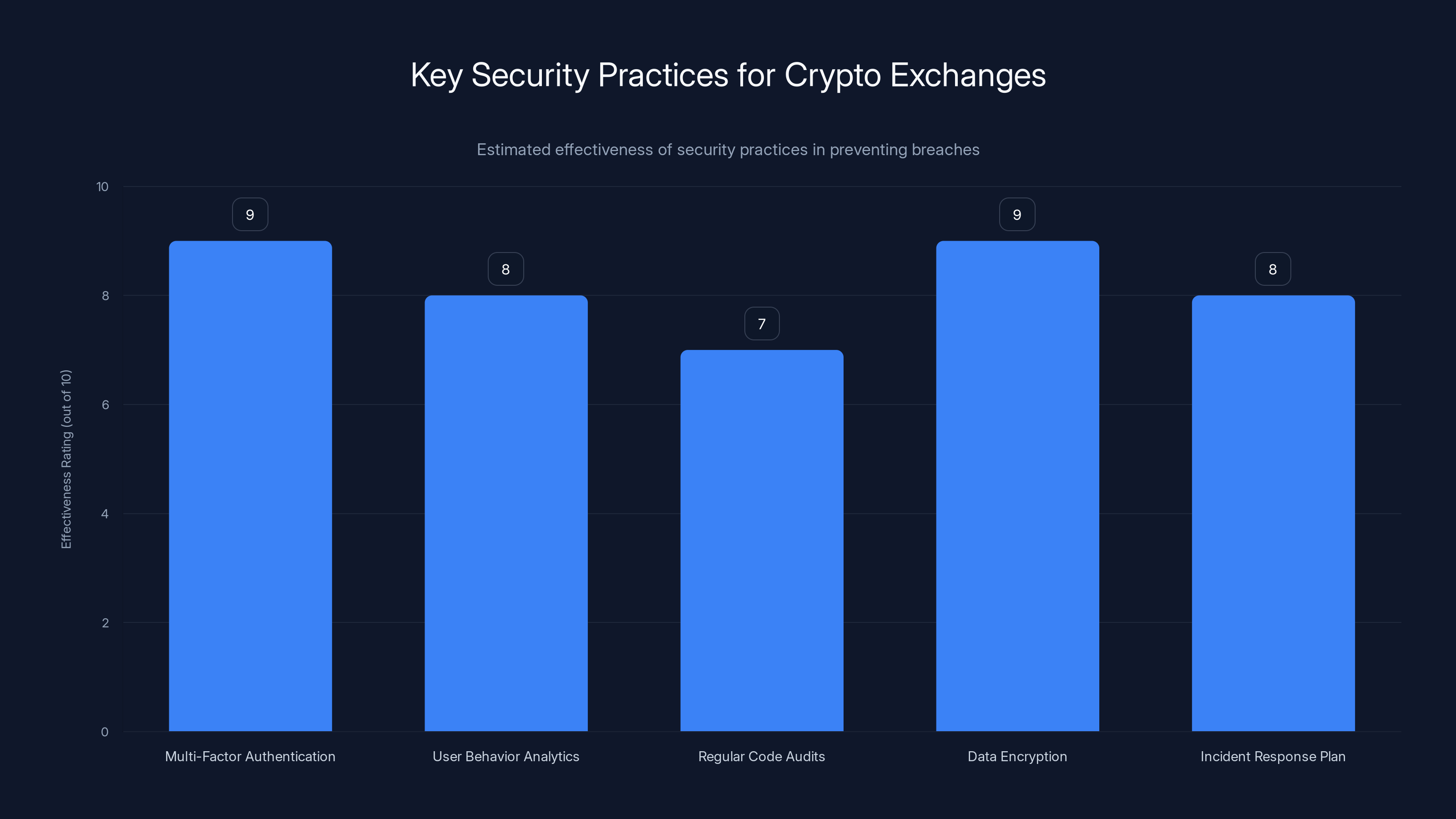
Multi-Factor Authentication and Data Encryption are rated highest in effectiveness for securing crypto exchanges. Estimated data.
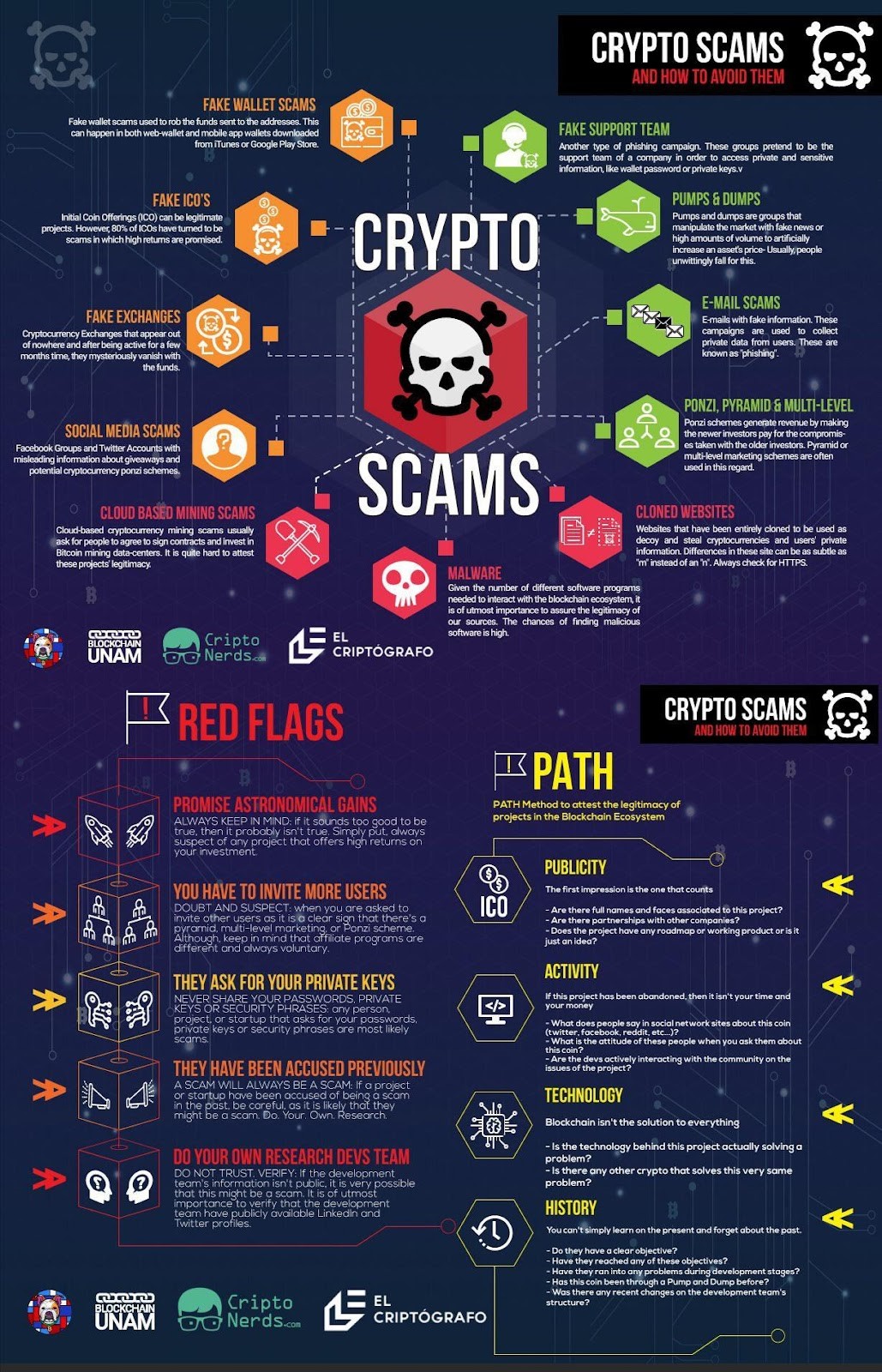
Crypto Exchange Vulnerabilities
Cryptocurrency exchanges like Kraken are prime targets for cybercriminals due to the high value of digital assets and the often anonymous nature of blockchain transactions. Here are some common vulnerabilities:
- Hot Wallets: While convenient for quick transactions, they are more susceptible to hacking.
- Decentralized Systems: The lack of a single point of control can lead to inconsistent security practices.
- Third-party Integrations: APIs and other integrations can introduce vulnerabilities if not properly secured.
Best Practices for Securing Crypto Exchanges
To combat these threats, crypto exchanges must implement multi-layered security strategies. Here’s a detailed guide to fortifying defenses:
1. Implement Strong Authentication
- Multi-Factor Authentication (MFA): Use MFA across all access points to add an extra layer of security.
- Biometric Verification: Leverage fingerprint or facial recognition for user authentication.
2. Monitor and Audit Access
Regularly audit who has access to sensitive data and systems:
- Access Logs: Keep detailed logs of access to critical systems.
- User Behavior Analytics (UBA): Use AI to detect anomalies in user behavior that might indicate a breach.
3. Secure Software Development Lifecycle (SDLC)
Ensure that software is developed with security in mind:
- Regular Code Audits: Conduct thorough security reviews of code and architecture.
- Penetration Testing: Simulate attacks to find and fix vulnerabilities.
4. Encrypt Sensitive Data
Encryption is vital for protecting customer data:
- Data at Rest: Use strong encryption protocols for stored data.
- Data in Transit: Ensure all data transmitted over networks is encrypted using SSL/TLS.
5. Develop a Robust Incident Response Plan
Prepare for potential breaches with a clear action plan:
- Incident Response Team: Establish a dedicated team to handle security incidents.
- Regular Drills: Conduct simulated attack scenarios to keep the team prepared.

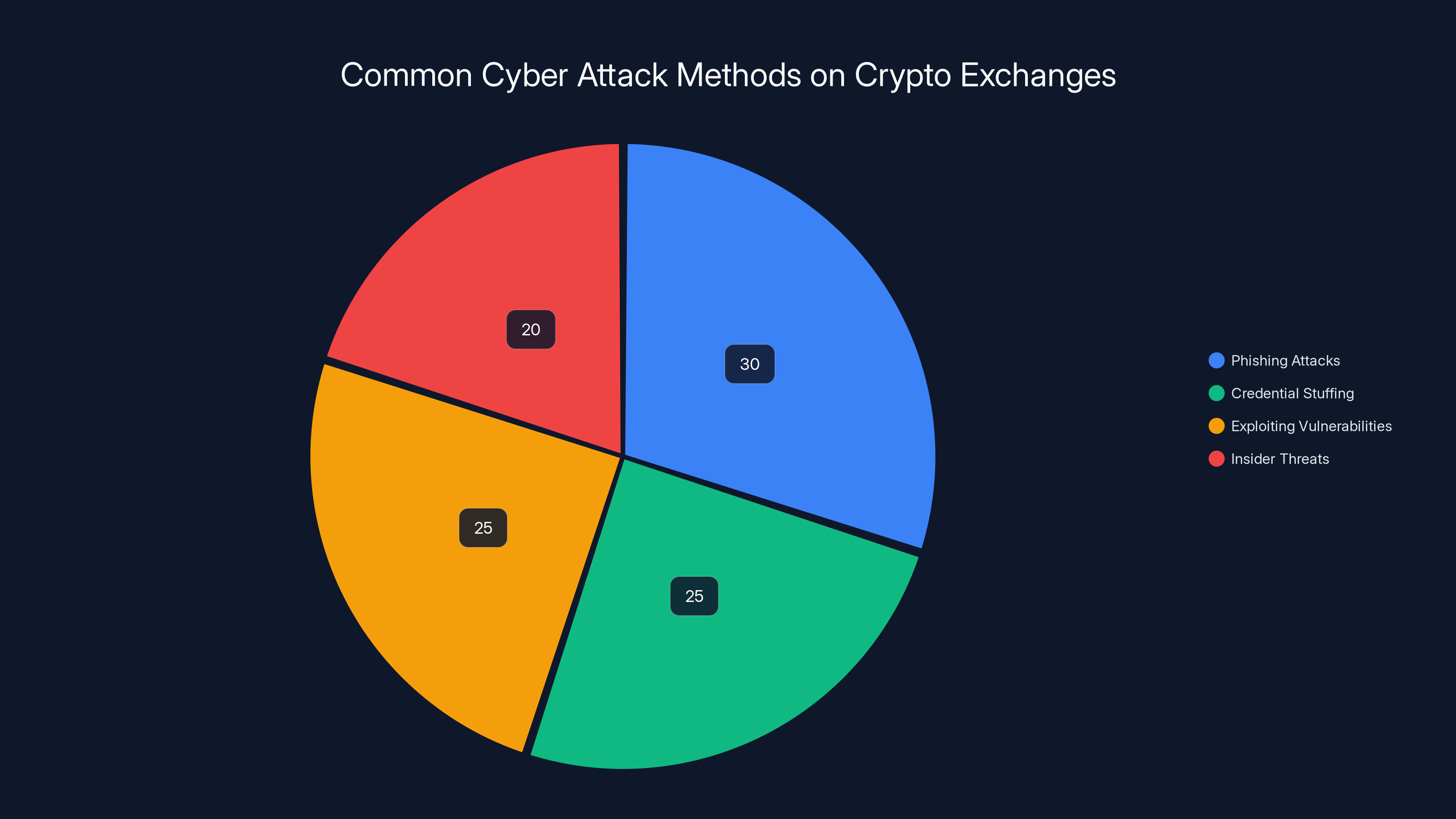
Phishing attacks are the most common method used against crypto exchanges, followed by credential stuffing and exploiting vulnerabilities. Estimated data.
Common Pitfalls and Solutions
Even with best practices, there are common pitfalls that crypto exchanges face:
- Overlooking Insider Threats: Regularly update access controls and monitor employee behavior.
- Neglecting Third-Party Risks: Ensure thorough vetting and continuous monitoring of third-party services.
- Inadequate Employee Training: Conduct regular security awareness training to prevent social engineering attacks.
Future Trends in Crypto Security
As the cryptocurrency industry evolves, so do the threats. Here are some trends to watch for:
Increased Use of AI in Cybersecurity
AI is becoming a powerful tool in detecting and mitigating cyber threats. It can analyze patterns and detect anomalies faster than human analysts.
Blockchain-Based Security Solutions
Blockchain technology itself offers unique security advantages. Decentralized Identity Management and Smart Contracts are being explored as methods to enhance security.
Regulatory Developments
With the rise in crypto adoption, regulatory bodies will likely impose stricter security and compliance requirements on exchanges.

Recommendations for Crypto Exchanges
To stay ahead of threats, exchanges should:
- Continuously Innovate: Leverage new technologies and strategies to enhance security.
- Collaborate with Industry Peers: Share threat intelligence and best practices to build a stronger defense community.
- Invest in Talent and Training: Develop internal expertise and keep staff updated on the latest security trends.

Conclusion
The extortion attack on Kraken is a stark reminder of the ever-present threats facing crypto exchanges. By adopting comprehensive security strategies and staying ahead of emerging threats, exchanges can protect their assets and maintain user trust.
FAQ
What is an extortion attack in the context of cryptocurrency?
An extortion attack involves cybercriminals threatening to release sensitive information unless a ransom is paid. In the case of Kraken, internal support system videos were leaked, though no funds were compromised.
How can cryptocurrency exchanges protect themselves from cyber threats?
Exchanges can protect themselves by implementing strong authentication measures, encrypting sensitive data, conducting regular security audits, and developing a robust incident response plan.
Why are crypto exchanges targeted by cybercriminals?
The high value of digital assets and the anonymity of blockchain transactions make crypto exchanges attractive targets. Cybercriminals exploit vulnerabilities to access these valuable resources.
What role does AI play in enhancing cryptocurrency security?
AI helps in detecting and mitigating threats by analyzing patterns and detecting anomalies more quickly than human analysts. It is being increasingly used to enhance the security of crypto exchanges.
What future trends are expected in the cybersecurity of crypto exchanges?
Future trends include increased use of AI, blockchain-based security solutions, and tighter regulatory requirements to ensure the security of cryptocurrency exchanges.
How important is employee training in maintaining the security of a crypto exchange?
Employee training is crucial as it helps prevent social engineering attacks and ensures that staff are aware of the latest security protocols and threats.
Key Takeaways
- Kraken's extortion attack highlights the vulnerability of crypto exchanges.
- No funds were compromised, but 2,000 accounts were exposed to privacy risks.
- Strong authentication and regular audits are crucial for security.
- Emerging technologies like AI and blockchain can enhance security measures.
- Future trends include increased regulatory requirements and advanced threat detection.
Related Articles
- Understanding the Basic-Fit Data Breach: A Comprehensive Guide to Data Security [2025]
- Unmasking the Hidden Dangers: Backdoors in WordPress Plug-ins [2025]
- How Hackers Hijack Your Inbox with Clever Tactics [2025]
- Booking.com Data Breach: What Customers Need to Know [2025]
- Europe's Quest for Tech Sovereignty: Realistic Dream or Political Mirage? [2025]
- Unpacking Surfshark's Post-Quantum 'Dausos' and Its Impact on Internet Speeds [2025]
![Inside the Kraken Extortion Attack: How Crypto Giants Defend Against Cyber Threats [2025]](https://tryrunable.com/blog/inside-the-kraken-extortion-attack-how-crypto-giants-defend-/image-1-1776269081928.jpg)



