European Commission Confirms Data Breach: Analysis and Implications [2025]
The recent announcement from the European Commission about a data breach on their cloud infrastructure has sent shockwaves across the cybersecurity community. With over 350GB of data reportedly compromised, this incident highlights the vulnerabilities inherent in cloud systems and the urgent need for robust security measures. In this article, we'll delve into the specifics of this breach, explore its implications, and discuss best practices for securing cloud environments.
TL; DR
- Data Breach Scope: Over 350GB of data was compromised from the European Commission's cloud infrastructure.
- Security Weakness: The breach exposes vulnerabilities in cloud systems, stressing the need for stronger security protocols.
- Regulatory Impact: This incident could lead to stricter data protection regulations and compliance requirements.
- Preventative Measures: Implementing multi-factor authentication, encryption, and regular audits is crucial.
- Future Trends: Expect a rise in AI-driven security solutions to combat sophisticated cyber threats.
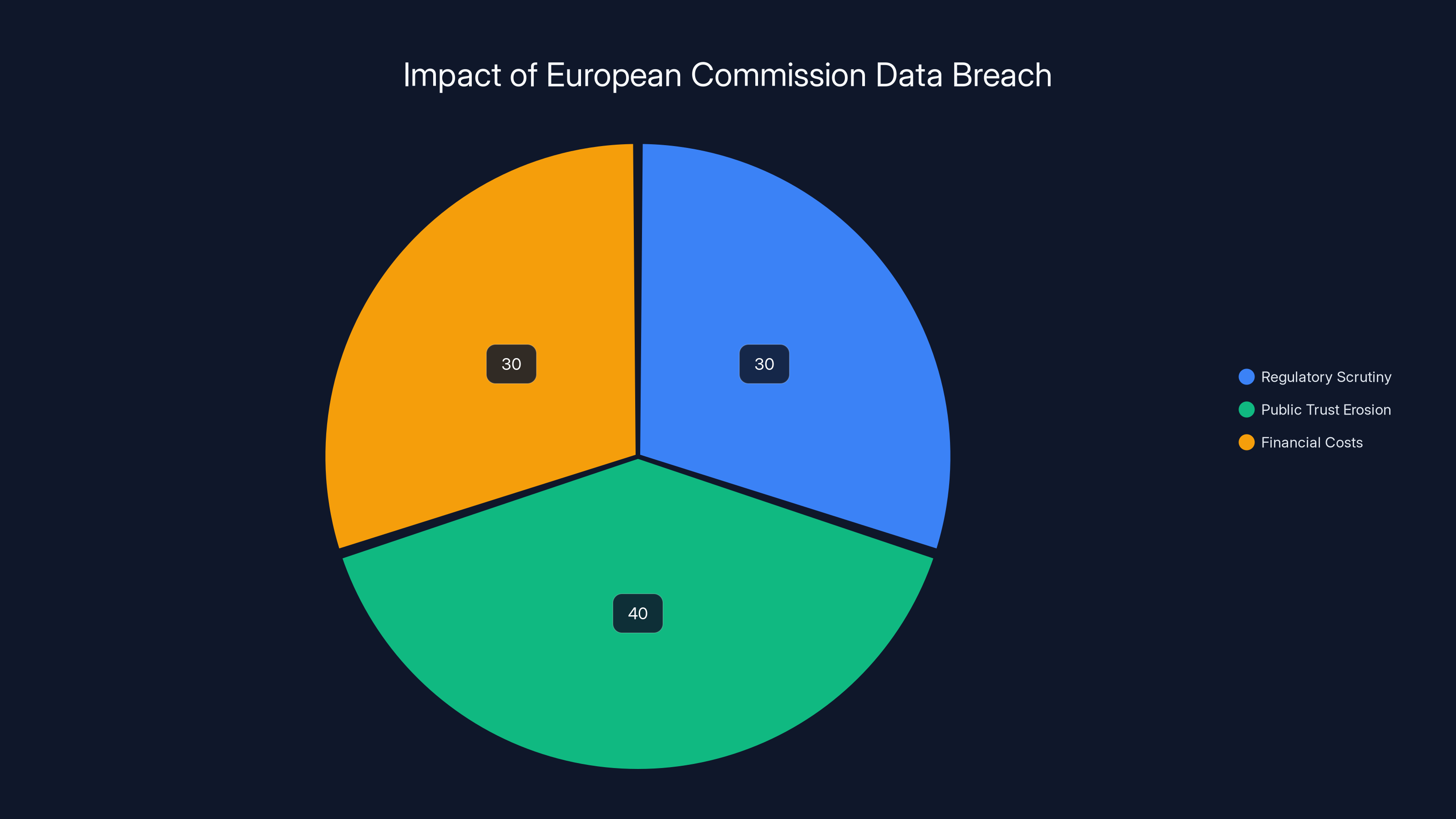
Estimated data shows that public trust erosion and regulatory scrutiny are major consequences of the breach, each accounting for around 30-40% of the impact.
Understanding the Breach
The European Commission has confirmed a data breach that significantly impacted its cloud infrastructure, affecting the Europa.eu platform. The breach, reportedly orchestrated by a sophisticated threat actor, resulted in the extraction of over 350GB of sensitive data. This incident underscores the vulnerabilities in cloud-based systems and the critical importance of maintaining robust security practices.
What Happened?
The breach was detected when unusual activities were noticed on the European Commission's cloud infrastructure. Investigations revealed that a threat actor had accessed data stored on the platform, exploiting vulnerabilities that had not been adequately secured. The exact vectors used by the attackers are still under investigation, but initial reports suggest a combination of phishing attacks and weak endpoint security.
Implications of the Breach
This breach has significant implications for both the European Commission and organizations worldwide. It raises critical questions about data security, regulatory compliance, and the adequacy of current cybersecurity measures. The breach not only affects the reputation of the European Commission but also prompts a reevaluation of data protection strategies across sectors.
Key Consequences Include:
- Regulatory Scrutiny: Heightened regulatory scrutiny and potential sanctions.
- Public Trust: Erosion of public trust in government-managed data security.
- Financial Costs: Possible financial penalties and the cost of remediation efforts.

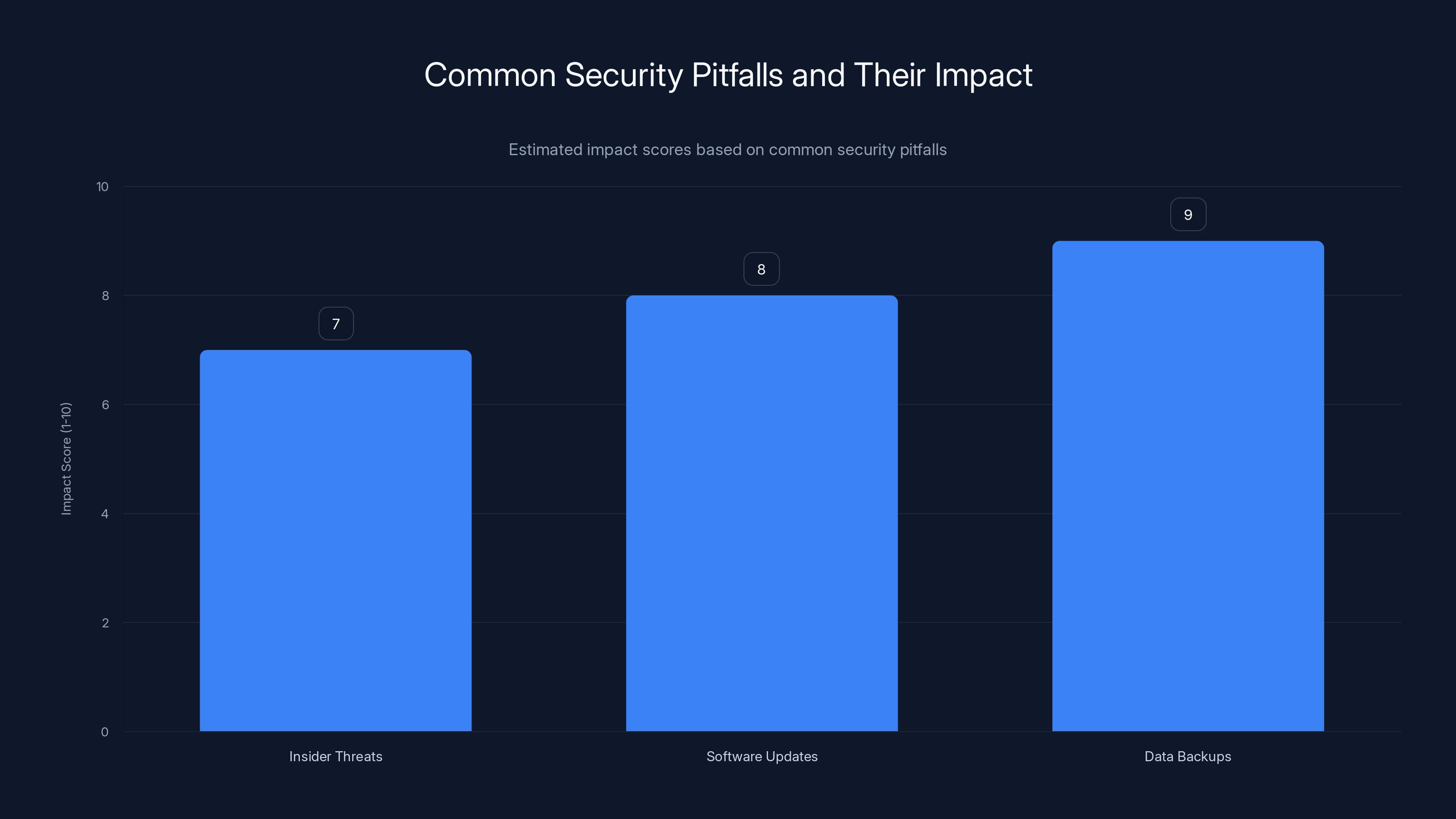
The chart estimates the impact scores of common security pitfalls, with inadequate data backups having the highest potential impact. Estimated data.
Technical Details and Breach Analysis
The Attack Vector
While the investigation is ongoing, early findings suggest that the attackers used a blend of social engineering tactics and technical exploits to gain access. Phishing emails targeting employees provided a foothold into the system, allowing the attackers to bypass initial security layers.
Cloud Infrastructure Vulnerabilities
The breach points to several weaknesses in the Commission's cloud infrastructure:
- Inadequate Access Controls: Insufficient controls allowed unauthorized access.
- Lack of Encryption: Data was not encrypted end-to-end, making it vulnerable.
- Poor Incident Response: Delays in detecting and responding to the breach.
Best Practices for Cloud Security
Organizations can mitigate similar risks by implementing comprehensive security measures:
- Multi-Factor Authentication (MFA): Enforce MFA for all users to add an extra layer of security.
- Encryption: Ensure that all data, both in transit and at rest, is encrypted to protect against unauthorized access.
- Regular Security Audits: Conduct audits to identify and rectify vulnerabilities promptly.
- Employee Training: Train employees to recognize phishing attempts and practice good cyber hygiene.

Regulatory and Compliance Considerations
GDPR Implications
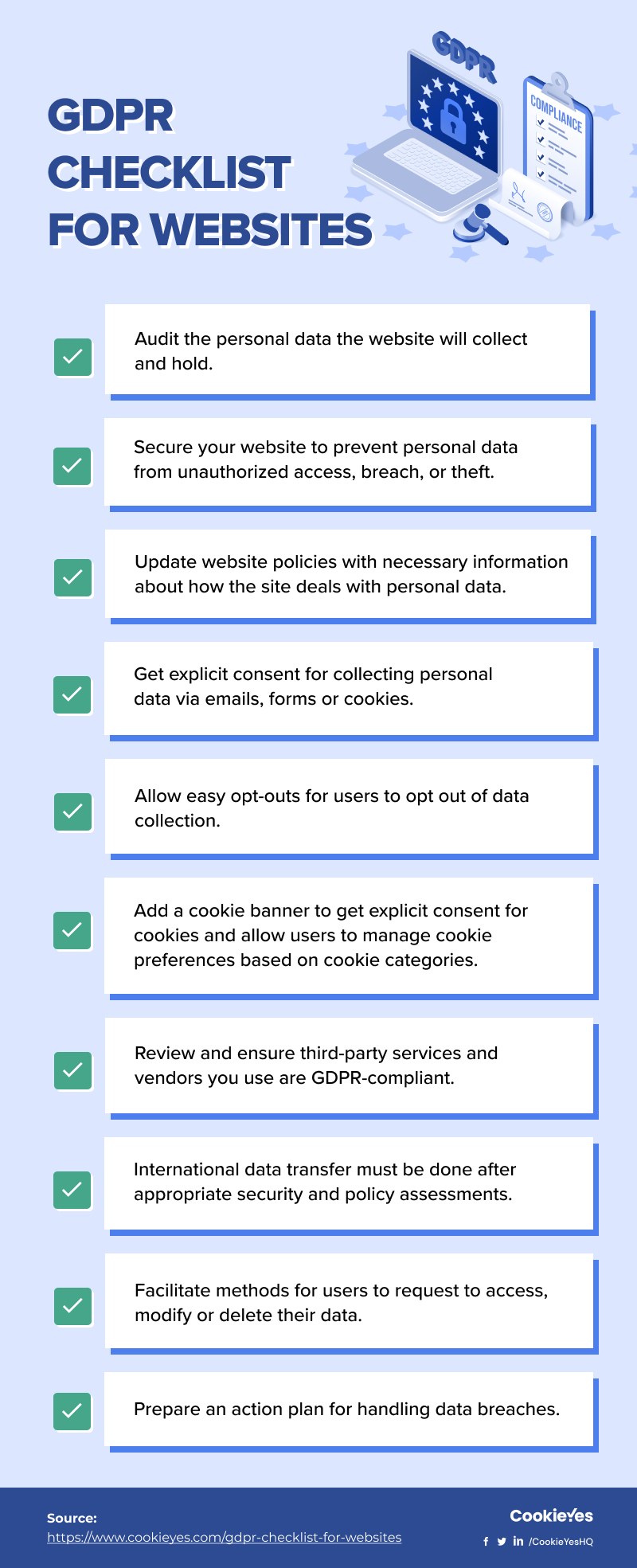
The General Data Protection Regulation (GDPR) requires organizations to protect personal data and ensure privacy. The European Commission's breach could lead to significant penalties under GDPR guidelines, emphasizing the importance of compliance.
GDPR Key Requirements Include:
- Data Protection by Design: Incorporate data protection measures from the outset.
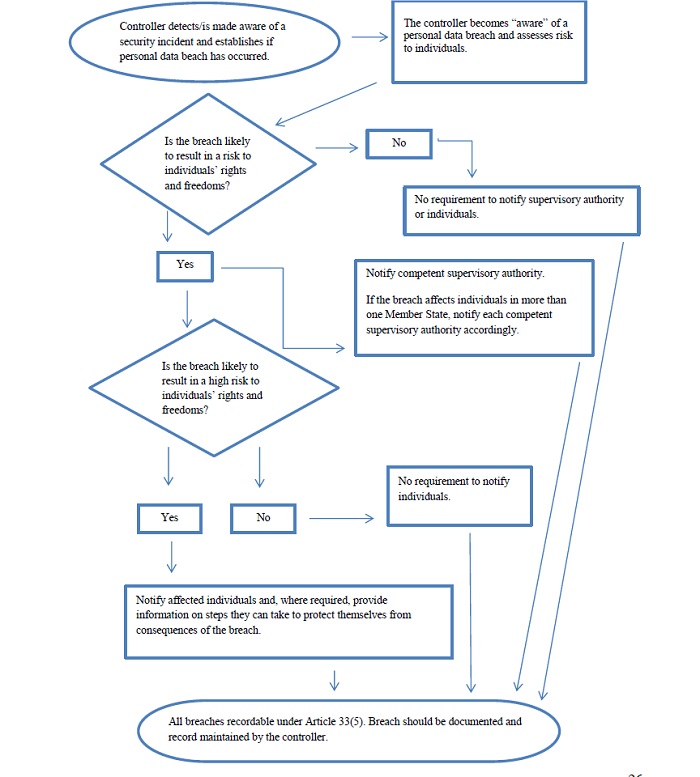
- Data Breach Notification: Mandatory reporting of breaches within 72 hours.
- Accountability and Governance: Establish clear data management policies.
Strengthening Compliance
To mitigate risks and ensure compliance, organizations should:
- Implement comprehensive data protection policies.
- Conduct regular compliance training and assessments.
- Engage with third-party experts for independent audits and recommendations.

Estimated data shows that implementing security measures takes the most time, followed by developing a security plan. Training employees is crucial but requires less time.
Future Trends in Cybersecurity
The breach at the European Commission highlights the evolving nature of cyber threats and the need for advanced security solutions. As technology advances, so do the tactics of cybercriminals. Here's what the future holds for cybersecurity:
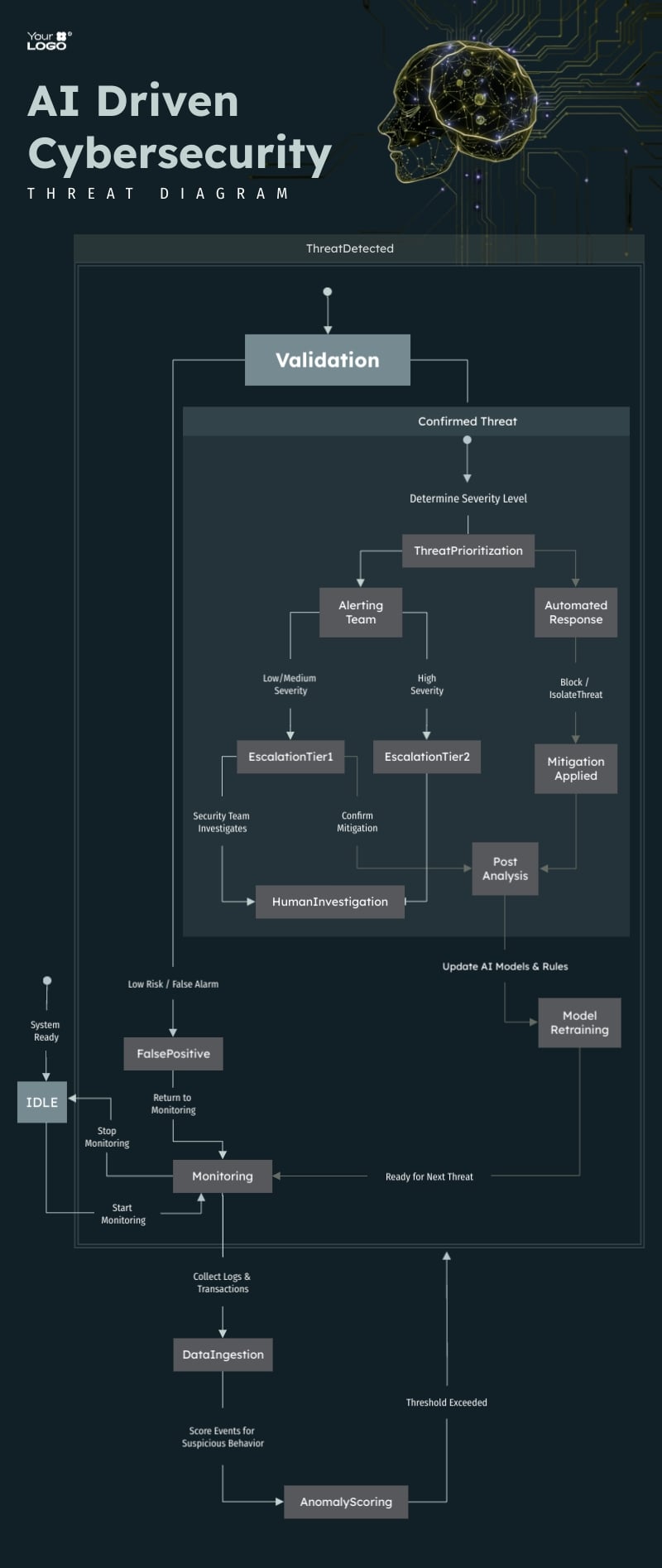
AI-Driven Security Solutions
AI and machine learning are becoming integral to cybersecurity strategies. These technologies can analyze vast amounts of data to detect anomalies and predict potential threats, significantly enhancing incident response capabilities.
Benefits of AI in Cybersecurity:
- Real-Time Threat Detection: Immediate identification of potential threats.
- Predictive Analytics: Anticipate and mitigate risks before they occur.
- Automated Responses: Reduce response times with automated security measures.
Increasing Role of Zero Trust Architecture
The Zero Trust model operates on the principle of "never trust, always verify," requiring strict identity verification for every person and device trying to access resources on a network.
Core Components of Zero Trust:
- Identity Verification: Continuous monitoring and verification of user identities.
- Least Privilege Access: Granting minimal access rights necessary for tasks.
- Micro-Segmentation: Dividing networks into smaller segments for better control.
Practical Implementation Guides
For organizations looking to bolster their cybersecurity posture, implementing new strategies can be daunting. Here's a step-by-step guide to help you navigate the process:
Step 1: Conduct a Security Audit
Begin with a thorough audit of your current security measures. Identify vulnerabilities, assess risks, and prioritize areas that need immediate attention.
- Inventory Assets: Catalog all devices, applications, and data assets.
- Assess Risk: Evaluate potential threats and their impact on your organization.
- Review Policies: Ensure existing policies align with industry standards.
Step 2: Develop a Comprehensive Security Plan
With insights from the audit, develop a security plan that addresses identified vulnerabilities and aligns with business objectives.
- Set Clear Objectives: Define what success looks like in terms of security.
- Allocate Resources: Determine budget, personnel, and technology needs.
- Establish Metrics: Identify key performance indicators to measure progress.
Step 3: Implement Security Measures
Deploy the necessary technologies and processes to enhance your security posture.
- Install Firewalls and IDS/IPS: Protect network perimeters and monitor for intrusions.
- Deploy Endpoint Protection: Secure all endpoints with antivirus and anti-malware solutions.
- Use Secure Configuration: Harden systems and applications to reduce vulnerabilities.
Step 4: Train Employees
Human error is a significant factor in security breaches. Regular training can help employees recognize threats and respond appropriately.
- Phishing Simulations: Conduct regular phishing tests to gauge employee awareness.
- Security Workshops: Offer hands-on training sessions to reinforce best practices.
- Policy Refreshers: Regularly update employees on policy changes and new threats.
Step 5: Monitor and Review
Security is not a one-time effort. Continuous monitoring and regular reviews are essential to maintaining a strong security posture.
- Use SIEM Tools: Implement Security Information and Event Management (SIEM) tools for real-time threat detection.
- Conduct Regular Reviews: Schedule periodic reviews of security policies and practices.
- Adapt to Changes: Stay informed about new threats and adjust your strategies accordingly.
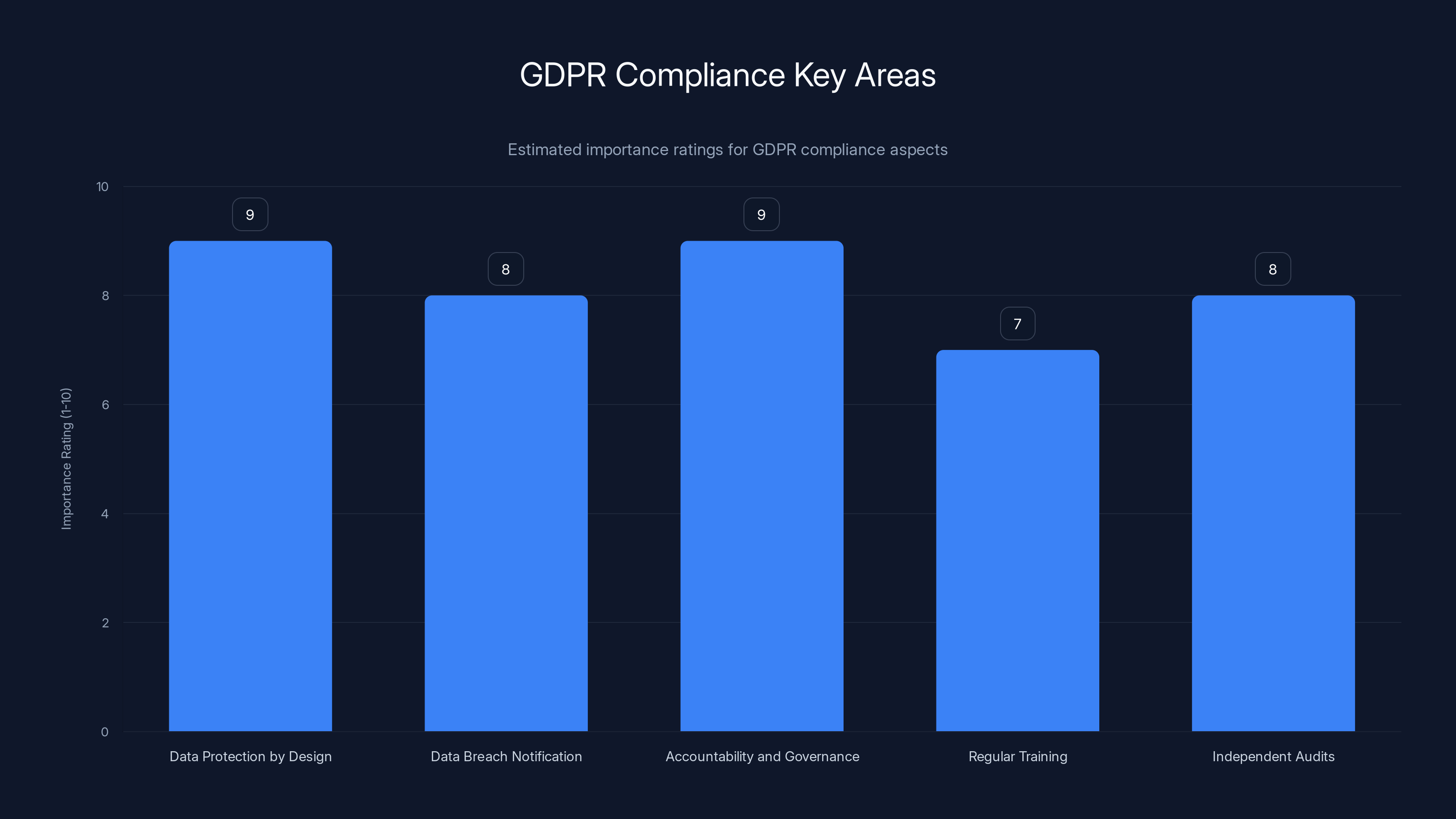
Data Protection by Design and Accountability are crucial for GDPR compliance, with high importance ratings. Estimated data.
Common Pitfalls and Solutions
Despite best efforts, organizations can fall into common traps when implementing security measures. Here are some pitfalls to watch out for and solutions to consider:
Pitfall 1: Overlooking Insider Threats
Solution: Implement strict access controls and monitor user activities to detect suspicious behavior early.
Pitfall 2: Neglecting Software Updates
Solution: Establish a patch management process to ensure all systems are up-to-date and secure.
Pitfall 3: Inadequate Data Backups
Solution: Implement a robust backup and recovery plan with regular testing to ensure data integrity.

Conclusion and Recommendations
The European Commission's data breach is a stark reminder of the evolving cyber threat landscape. As organizations increasingly rely on cloud infrastructure, they must prioritize security to protect sensitive data and maintain trust.
Key Recommendations
- Enhance Security Protocols: Implement comprehensive security measures tailored to your organization's needs.
- Adopt Advanced Technologies: Leverage AI and machine learning to bolster your cybersecurity defenses.
- Foster a Security-First Culture: Encourage a proactive approach to security across all levels of the organization.
- Stay Informed: Keep abreast of the latest cyber threats and trends to adapt strategies accordingly.
By taking these steps, organizations can better protect themselves against cyber threats and minimize the impact of potential breaches.
FAQ
What is a data breach?
A data breach occurs when unauthorized individuals gain access to sensitive, protected, or confidential data, often resulting in the exposure of personal or financial information.
How does a data breach impact an organization?
Data breaches can lead to financial loss, reputational damage, regulatory penalties, and loss of customer trust. They often require costly remediation efforts.
What are the benefits of multi-factor authentication?
Multi-factor authentication adds an extra layer of security by requiring users to verify their identity through multiple factors, reducing the risk of unauthorized access.
How can organizations prepare for a data breach?
Organizations can prepare for a data breach by implementing strong security measures, conducting regular audits, training employees, and developing an incident response plan.
What role does AI play in cybersecurity?
AI enhances cybersecurity by enabling real-time threat detection, predictive analytics, and automated responses, helping organizations respond to threats more effectively.
Why is regular employee training important?
Regular employee training is crucial because human error is a common cause of security breaches. Training helps employees recognize threats and respond appropriately.
How can Zero Trust architecture improve security?
Zero Trust architecture improves security by requiring strict identity verification for everyone trying to access resources, reducing the risk of unauthorized access.
What is the GDPR and how does it relate to data breaches?
The GDPR is a regulation that protects personal data within the European Union. It mandates organizations to implement strong data protection measures and report breaches within 72 hours.
Key Takeaways
- Over 350GB of data was compromised from the European Commission's cloud infrastructure.
- The breach exposes vulnerabilities in cloud systems, highlighting the need for stronger security protocols.
- Regulatory scrutiny will likely increase, potentially leading to stricter data protection regulations.
- Organizations should implement multi-factor authentication, encryption, and regular audits to enhance security.
- AI-driven security solutions are expected to become integral in combating sophisticated cyber threats.
Related Articles
- Understanding Cybersecurity in the EU: Lessons from the European Commission Cyberattack [2025]
- Maximize Your Cybersecurity: A 20% Off Acronis Cyber Protect Deal [2025]
- Understanding Banking App Glitches: Lessons from Lloyds and Beyond [2025]
- Mastering Data Protection: A Comprehensive Guide to Acronis True Image [2025]
- How Browser Hijacking Can Occur with Chrome Extensions: Insights from the Claude Extension Flaw [2025]
- Understanding the Risks: Are American VPN Users Facing 'Warrantless' Government Surveillance? [2025]
![European Commission Confirms Data Breach: Analysis and Implications [2025]](https://tryrunable.com/blog/european-commission-confirms-data-breach-analysis-and-implic/image-1-1774643683708.jpg)



