Understanding the Risks: Are American VPN Users Facing 'Warrantless' Government Surveillance? [2025]
In the digital age, privacy is a commodity more valuable than ever, and a Virtual Private Network (VPN) is often touted as a shield against prying eyes. However, recent concerns have arisen regarding whether American VPN users are genuinely protected from 'warrantless' government surveillance. This comprehensive guide will explore the nuances of privacy laws, the technical underpinnings of VPNs, and the practical steps users can take to safeguard their online activities.
TL; DR
- Government Surveillance Concerns: American VPN users may not be as shielded from government surveillance as they believe, as discussed in a TechRadar article.
- Legal Frameworks: Current laws like the Patriot Act can enable 'warrantless' data collection, as outlined in a Congressional Research Service report.
- VPN Vulnerabilities: Technical limitations and provider policies can affect user privacy.
- Best Practices: Users should choose VPNs with strict no-log policies and robust encryption.
- Future Trends: Expect increased scrutiny on data privacy and potential changes in legislation.
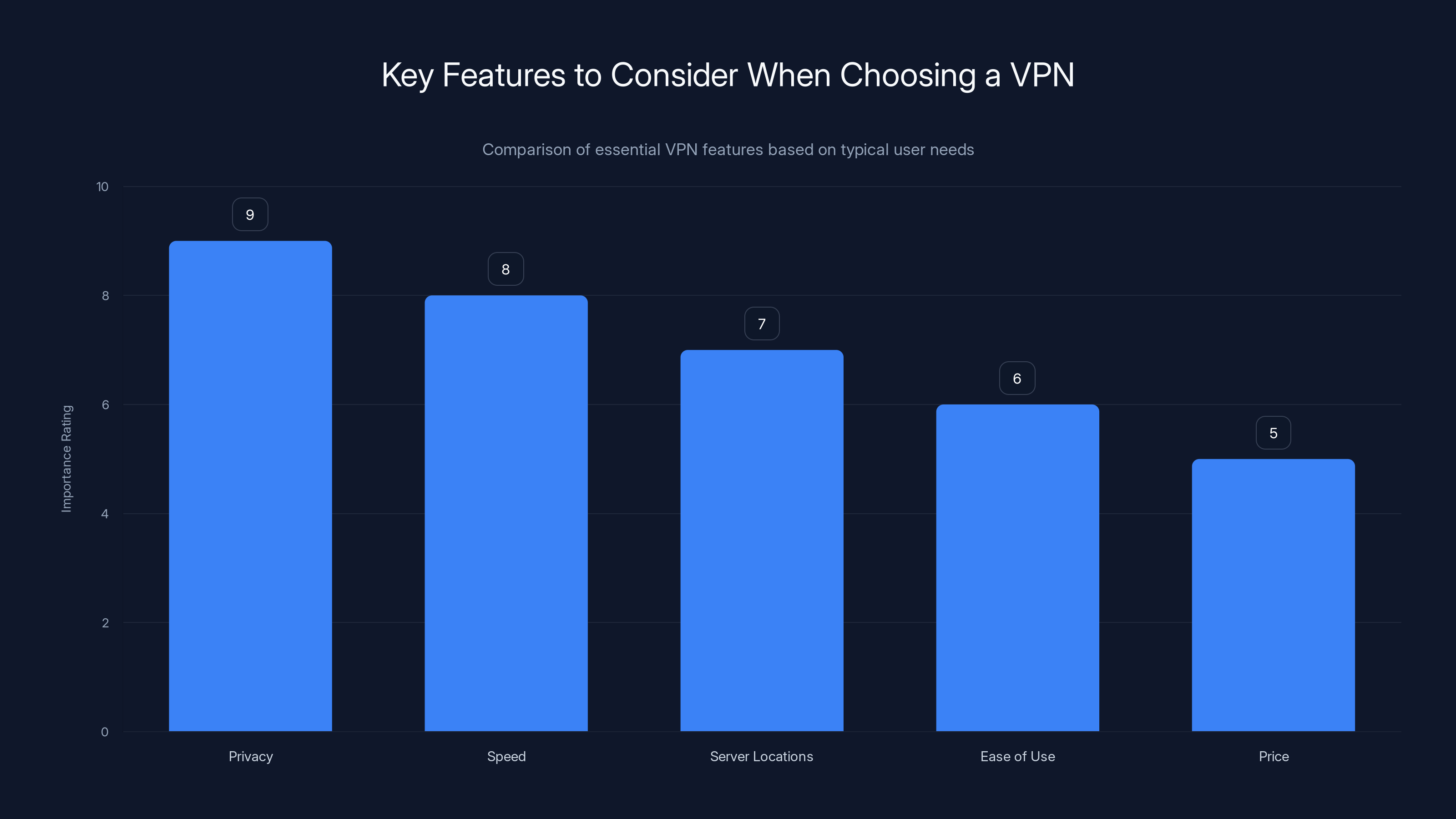
Privacy is the most crucial feature when selecting a VPN, followed by speed and server locations. Estimated data based on common user preferences.
The Legal Landscape: Privacy Laws and Government Surveillance
Key Legislation Impacting Privacy
Understanding the legal landscape is crucial for assessing the privacy risks associated with VPN usage in the U.S. The Patriot Act, enacted after the September 11 attacks, significantly expanded the scope of government surveillance capabilities. It allows authorities to use broad warrants to access various forms of communication, including online activities, as detailed in the Congressional Research Service report.
Another important piece of legislation is the Foreign Intelligence Surveillance Act (FISA), which permits secretive court orders to collect data on foreign intelligence targets, sometimes sweeping up the communications of U.S. citizens in the process, as noted by the ACLU.
'Warrantless' Surveillance: Myth or Reality?
While the term 'warrantless' might imply an absence of oversight, the reality is more nuanced. These laws often involve secretive courts and broad interpretations, leading to what privacy advocates argue amounts to 'warrantless' surveillance. For example, a FISA warrant can be issued without the traditional checks and balances associated with regular warrants, as discussed in the Congressional Research Service report.
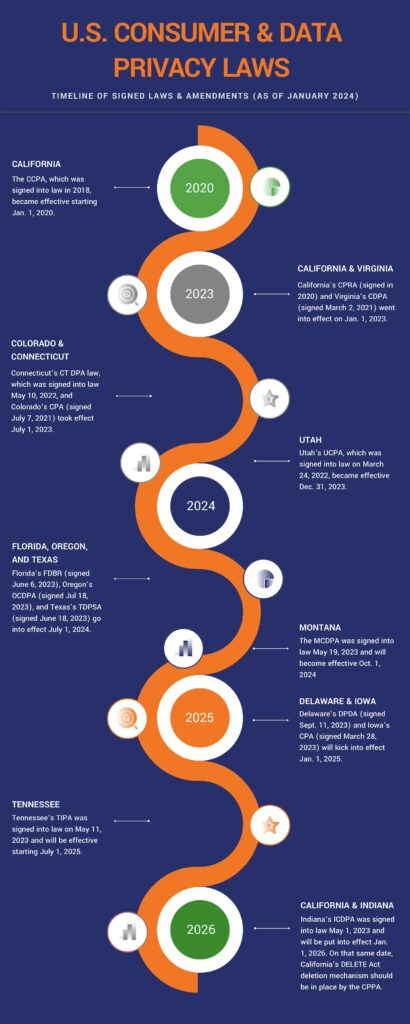
Recent Legislative Developments
In recent years, there has been a push for reform. The USA Freedom Act aimed to curtail some of the more controversial aspects of the Patriot Act, but privacy advocates argue it's not enough. As technology evolves, so too does the capacity for surveillance, necessitating ongoing legislative scrutiny and reform, as highlighted by FTI Consulting.
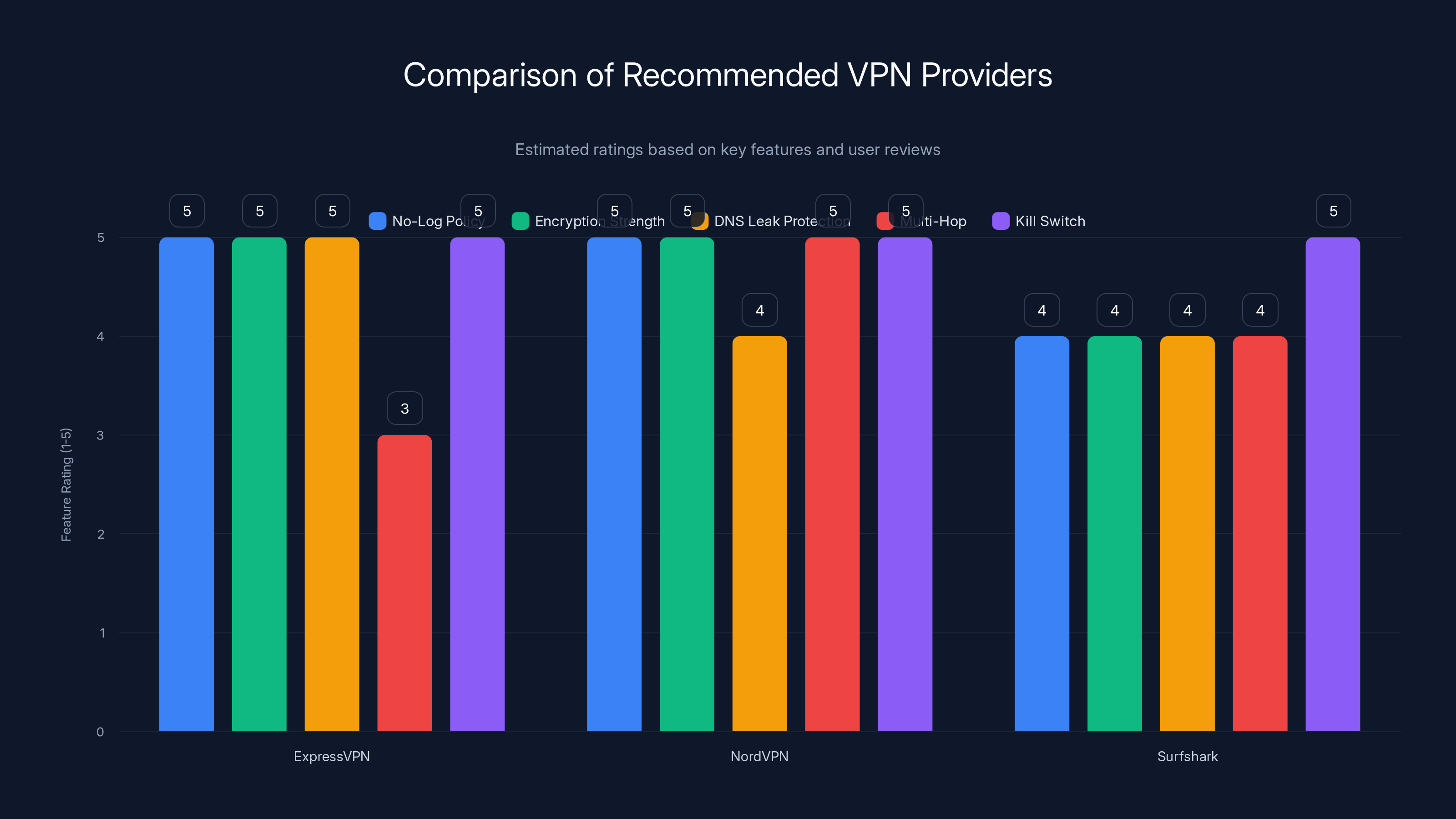
ExpressVPN and NordVPN excel in encryption and no-log policies, while Surfshark offers affordability with strong privacy protections. (Estimated data based on features)
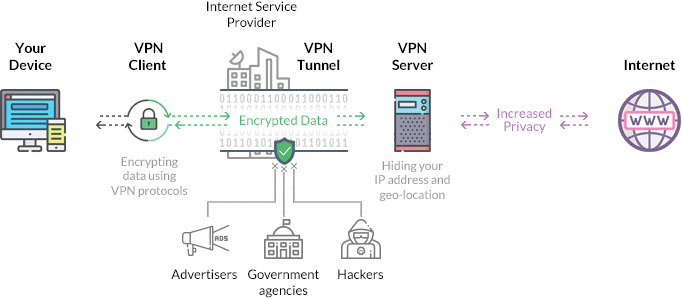
Technical Aspects of VPNs: How They Work
What is a VPN?
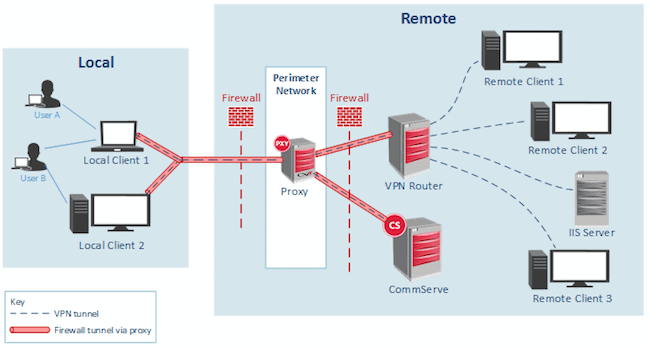
A Virtual Private Network (VPN) creates a secure tunnel between your device and the internet. By routing your connection through an encrypted server, it masks your IP address and encrypts your data, ostensibly protecting you from surveillance, as explained by PCMag.
How VPNs Protect You
- IP Masking: By hiding your real IP address, VPNs obfuscate your location and make it harder to track your online activities.
- Data Encryption: VPNs encrypt your data, making it unreadable to anyone who intercepts it.
- Secure Protocols: Protocols like Open VPN and Wire Guard are designed to provide robust security.
Common VPN Vulnerabilities
However, VPNs are not infallible. DNS leaks can expose your browsing habits by revealing DNS requests outside the VPN tunnel. Additionally, some VPN providers keep logs, which could potentially be accessed by government agencies, as noted in a TechRadar article.
Choosing the Right VPN: Best Practices
Key Features to Look For
When selecting a VPN, prioritize the following features:
- No-Log Policy: Ensure the provider does not keep logs of your activity.
- Strong Encryption: Look for at least AES-256 encryption.
- DNS Leak Protection: Protects against accidental exposure of your DNS requests.
- Multi-Hop: Routes your connection through multiple servers for added privacy.
- Kill Switch: Automatically disconnects your internet if the VPN connection is lost.
Recommended VPN Providers
- Express VPN: Known for its strong encryption and no-log policy, as reviewed by Salon.
- Nord VPN: Offers multi-hop connections and robust security features, highlighted in a Salon comparison.
- Surfshark: Affordable with excellent privacy protections, as noted in CNET's best VPN list.
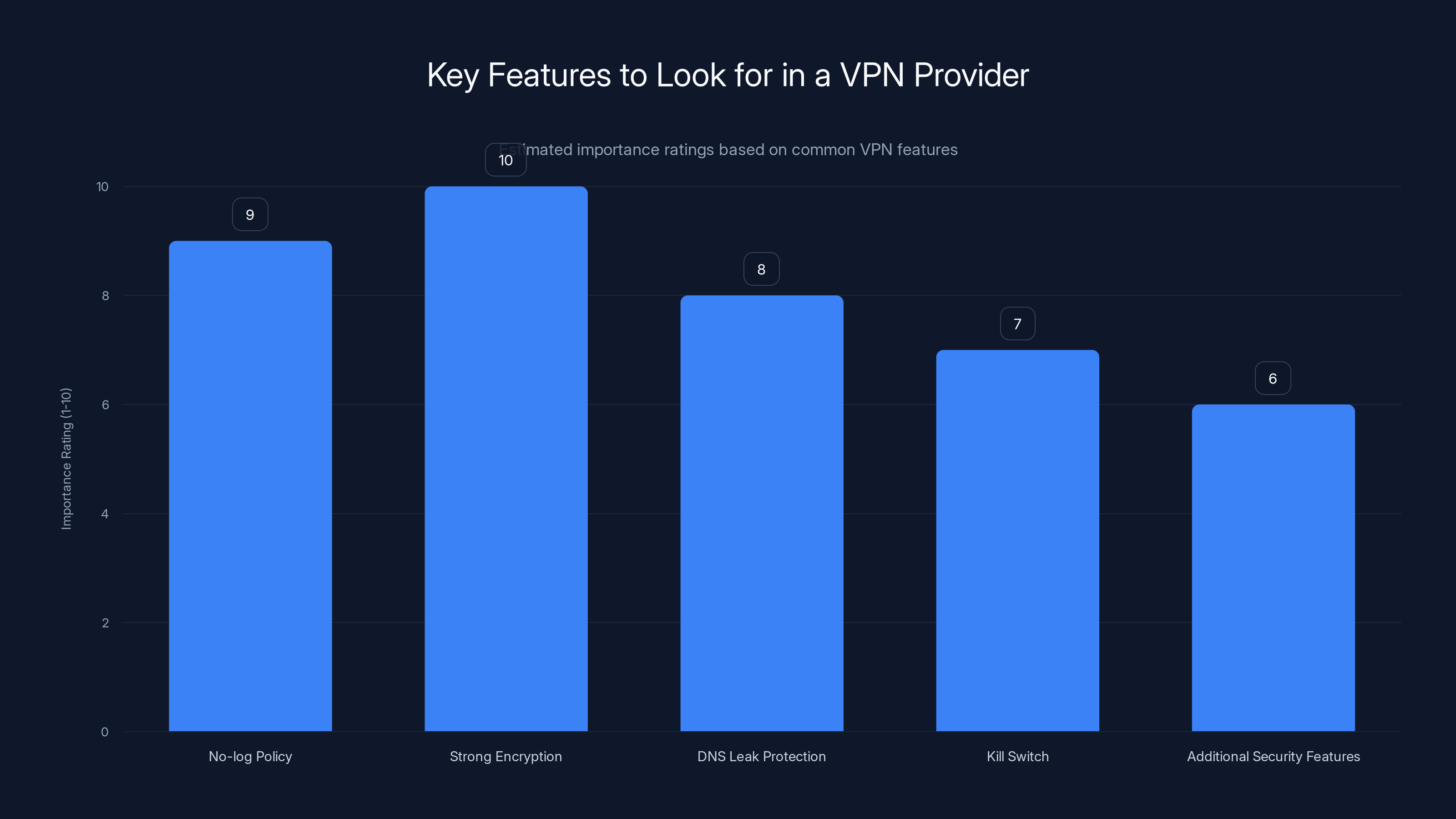
No-log policy and strong encryption are the most critical features when selecting a VPN provider. Estimated data based on common user priorities.
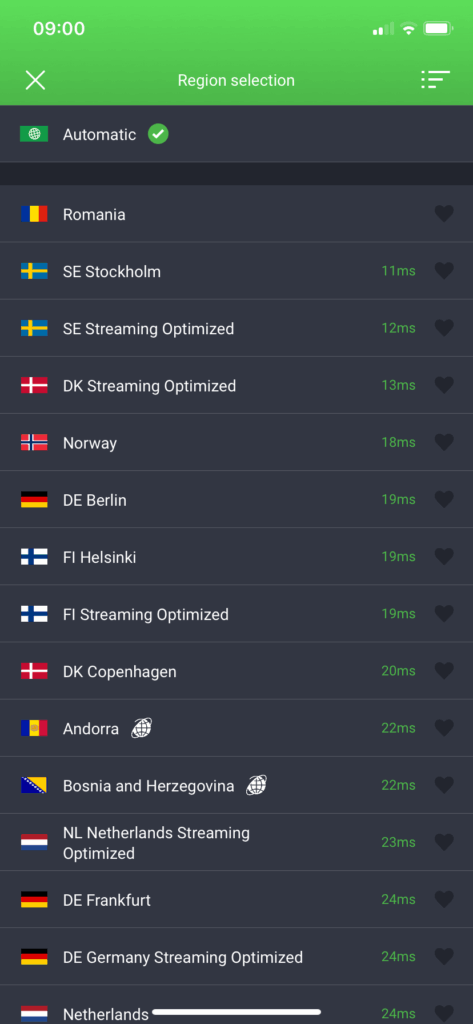
Implementation Guide: Setting Up Your VPN
Step-by-Step Setup
- Choose a VPN: Select a provider based on the features that best meet your privacy needs.
- Download and Install: Follow the provider’s instructions to download and install the VPN app on your devices.
- Configure Settings: Enable features like the kill switch and DNS leak protection.
- Connect to a Server: Choose a server location that offers the best privacy and performance.
- Regularly Update: Keep the VPN app updated to protect against new vulnerabilities.
Common Pitfalls and Solutions
-
Pitfall: Selecting a free VPN with poor security standards.
-
Solution: Invest in a reputable paid VPN provider, as advised by BGR.
-
Pitfall: Ignoring VPN settings post-installation.
-
Solution: Regularly review and update your VPN settings to maintain optimal privacy.
Future Trends in VPN and Privacy
Increased Legislative Scrutiny
As digital privacy becomes a hotter topic, expect increased scrutiny of both VPN providers and government surveillance practices. Efforts to balance national security with individual privacy rights will likely intensify, as discussed in an NPR report.
Technological Advancements
Technological advancements such as quantum computing could potentially break current encryption methods, necessitating the development of new security protocols. VPN providers will need to adapt to these changes to maintain user privacy, as noted by FTI Consulting.
Recommendations for Users
- Stay Informed: Keep abreast of legislative changes and technological advancements.
- Evaluate Providers Regularly: Continuously assess your VPN provider to ensure they meet the latest privacy standards.
- Adopt Additional Privacy Tools: Use tools like Tor for added anonymity.

Conclusion
While VPNs offer a layer of privacy, they're not a panacea against government surveillance, especially under current U.S. laws. By understanding the legal and technical landscape, users can make informed decisions to protect their online privacy effectively. As technology and legislation evolve, staying informed and adaptable will be key to maintaining digital privacy.

FAQ
What is a VPN and how does it work?
A VPN, or Virtual Private Network, creates a secure connection to another network over the Internet. It masks your IP address and encrypts your data, enhancing privacy, as explained by PCMag.
Are VPNs completely foolproof against surveillance?
No, VPNs can reduce the risk of surveillance but are not completely foolproof. Factors like provider policies and technical vulnerabilities can affect their efficacy, as noted in a TechRadar article.
How can I ensure my VPN is protecting my privacy?
Choose a VPN with strong encryption, a strict no-log policy, and regularly test for DNS leaks to ensure your activities remain private.
Why should I care about government surveillance?
Privacy is a fundamental right, and unchecked surveillance can lead to abuses of power and invasion of personal freedoms, as discussed by the ACLU.
What should I look for in a VPN provider?
Look for providers with a no-log policy, strong encryption, DNS leak protection, and additional security features like a kill switch, as recommended by CNET.
How do privacy laws impact VPN usage?
Privacy laws can dictate what data VPN providers must share with the government. Understanding these laws helps in choosing a provider that best protects your privacy, as outlined in the Congressional Research Service report.
Will future technology affect VPN security?
Yes, advancements like quantum computing could potentially compromise current encryption methods, necessitating new security measures from VPN providers, as noted by FTI Consulting.

Key Takeaways
- VPNs offer privacy but aren't foolproof against government surveillance, as discussed in a TechRadar article.
- Current US laws like the Patriot Act allow broad data collection, as outlined in the Congressional Research Service report.
- Choose VPNs with a no-log policy and strong encryption for best protection, as recommended by CNET.
- Stay informed about legal changes and technological advancements in privacy, as noted by FTI Consulting.
- VPN users should regularly test for DNS leaks to ensure data privacy, as advised by PCMag.
- Future technologies like quantum computing could challenge current encryption, as discussed by FTI Consulting.
Related Articles
- Unveiling VPN Transparency: A Deep Dive Into User Data Privacy [2025]
- Maximize Your Cybersecurity: A 20% Off Acronis Cyber Protect Deal [2025]
- The Unveiling of Coruna and DarkSword: How These Leaked Hacking Tools Threaten Millions of iPhones [2025]
- Understanding the EU's Approach to Regulating AI and App Privacy [2025]
- LangChain Framework Faces Security Challenges: Key Vulnerabilities and Best Practices [2025]
- English Learning Apps: Critical Security Risks and Best Practices [2025]
![Understanding the Risks: Are American VPN Users Facing 'Warrantless' Government Surveillance? [2025]](https://tryrunable.com/blog/understanding-the-risks-are-american-vpn-users-facing-warran/image-1-1774633110058.jpg)



