Understanding Cybersecurity in the EU: Lessons from the European Commission Cyberattack [2025]
The recent cyberattack on the European Commission has highlighted vulnerabilities in even the most robust systems. As the EU's executive body works to mitigate the breach's effects, it provides a crucial opportunity to explore cybersecurity best practices, the evolving threat landscape, and future trends.
TL; DR
- Data Breach Impact: The cyberattack affected the European Commission's cloud services, underscoring vulnerabilities in cloud security.
- Mitigation Measures: Immediate containment and risk mitigation steps were implemented to prevent further damage.
- Internal Systems Safe: The Commission confirmed that internal systems remained unaffected, highlighting the importance of compartmentalization.
- Ongoing Investigation: The investigation continues, aiming to understand the breach's full scope and prevent future attacks.
- Future Recommendations: Emphasis on enhanced cloud security, regular audits, and staff training to bolster cybersecurity.

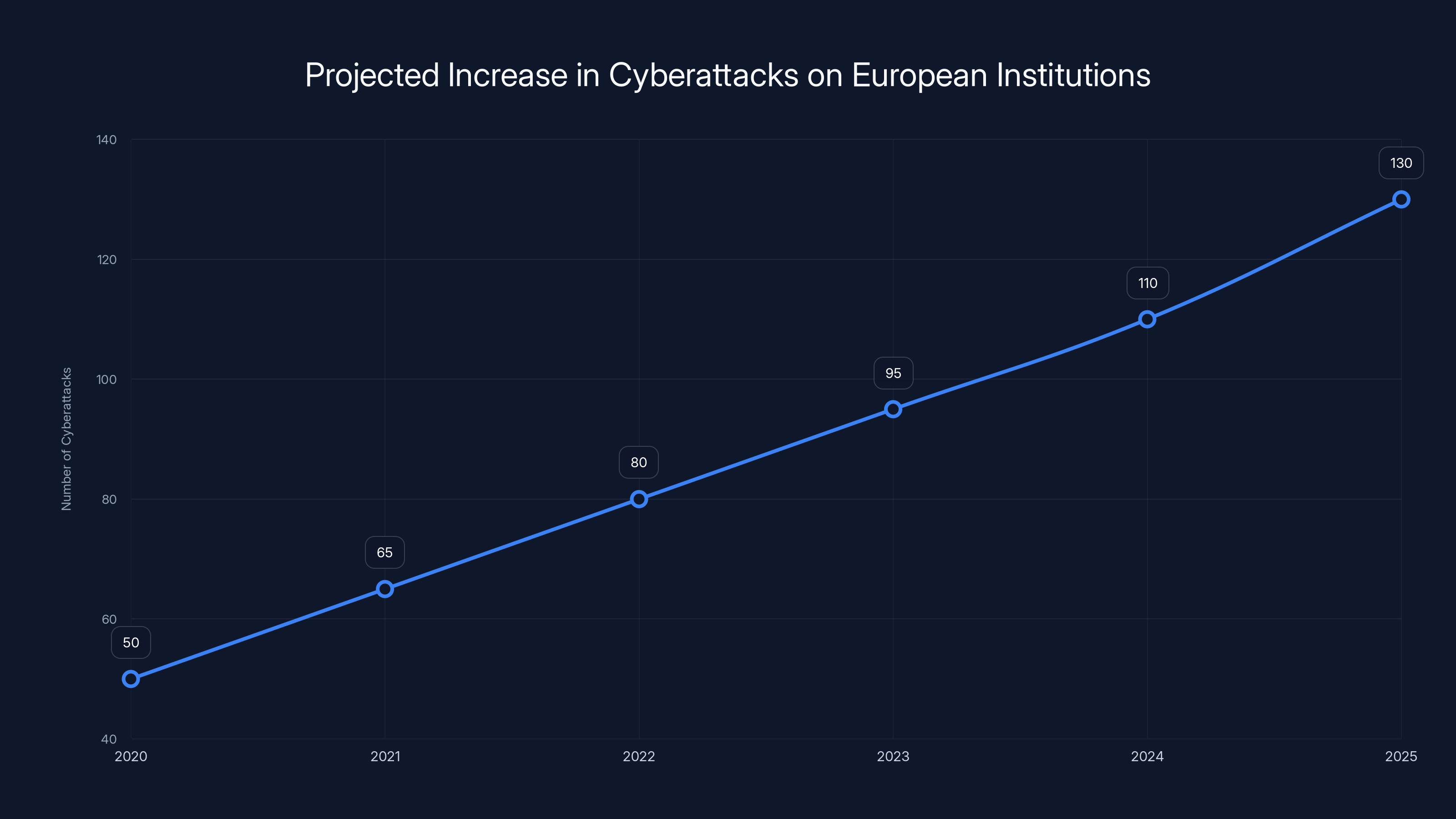
The number of cyberattacks on European institutions is projected to increase significantly by 2025, highlighting the growing threat landscape. (Estimated data)
The Cyberattack Overview
In March 2025, the European Commission confirmed a cyberattack targeting its cloud infrastructure. Hackers reportedly accessed and exfiltrated a significant amount of data from the Commission’s cloud storage, specifically affecting the platform hosting the Commission's web presence on Europa.eu.
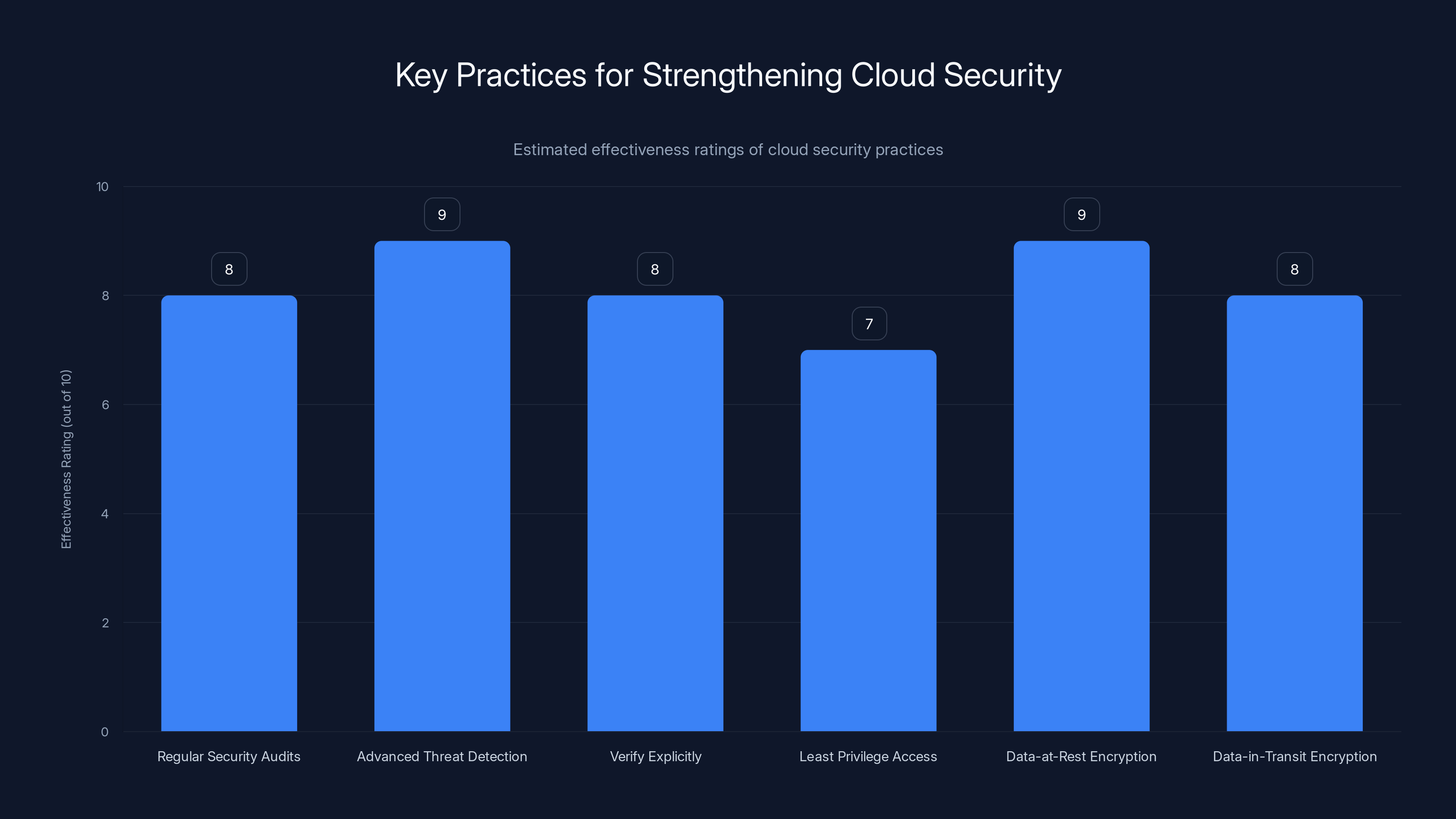
Advanced Threat Detection and Data Encryption are rated highly effective in strengthening cloud security. Estimated data based on typical industry assessments.
Key Components of the Attack
Attack Vector Identification
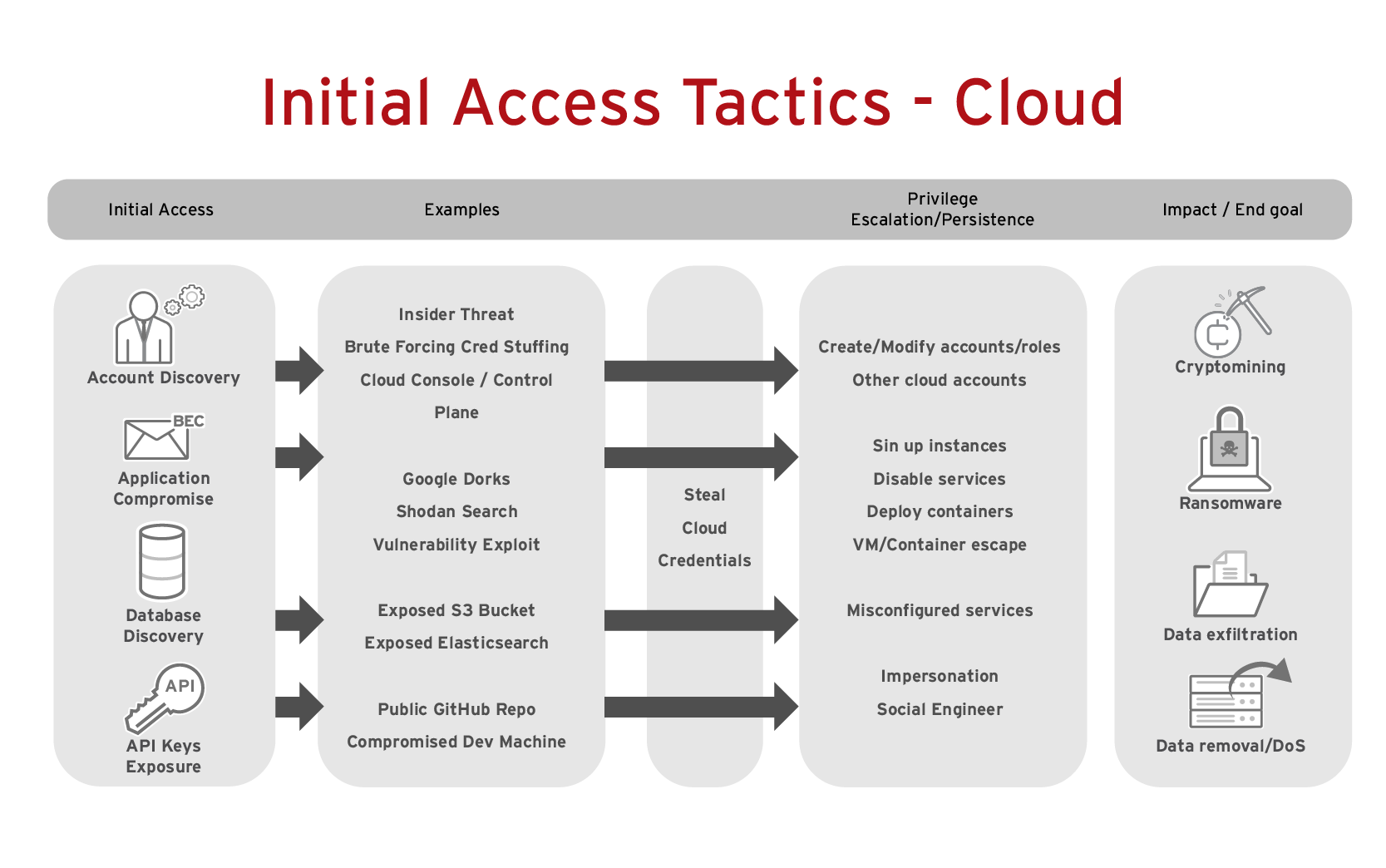
The cyberattack leveraged vulnerabilities within the cloud infrastructure. Such vectors often include:
- Phishing Campaigns: Emails crafted to deceive users into revealing sensitive information or downloading malicious software.
- Exploiting Cloud Misconfigurations: Commonly overlooked security settings can provide attackers with entry points.
Immediate Response and Containment
Upon discovering the breach, the Commission acted swiftly to contain the attack. Key steps included:
- Isolation of Affected Systems: Segregating compromised systems to prevent lateral movement of the attack.
- Deployment of Incident Response Teams: Teams worked to assess the breach’s impact and begin remediation efforts.
Communication Strategy
The Commission communicated transparently about the breach, providing regular updates about the ongoing investigation and mitigation efforts.
Technical Details and Best Practices
Strengthening Cloud Security
Cloud security is paramount in protecting sensitive data. Some best practices include:
- Regular Security Audits: Frequent audits help identify vulnerabilities and compliance with security standards.
- Advanced Threat Detection: Implement AI-driven solutions for real-time threat detection and response.
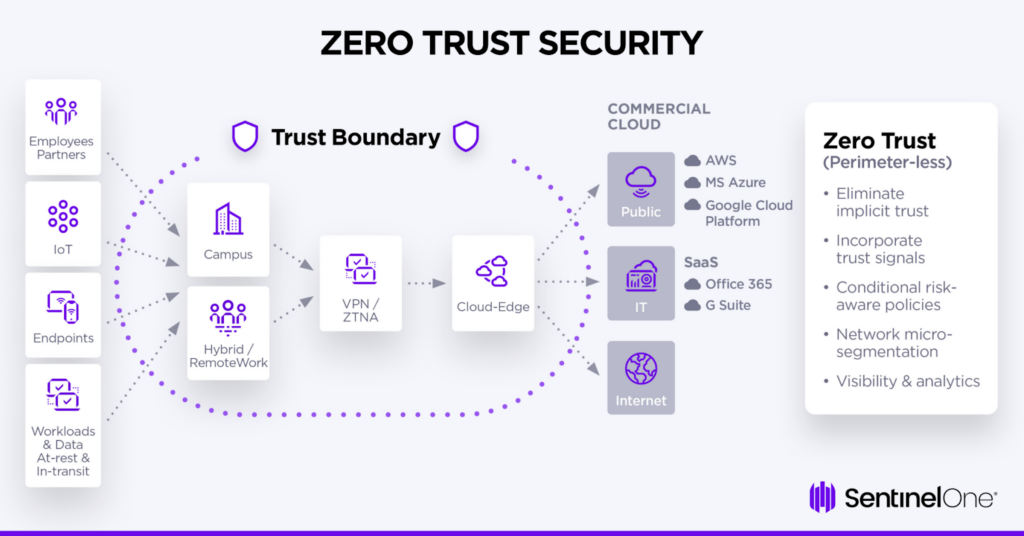
Implementing Zero Trust Architecture
Zero Trust is a cybersecurity model that assumes breaches are inevitable. Key principles include:
- Verify Explicitly: Authenticate and authorize based on all available data points, including user identity, location, device health, etc.
- Least Privilege Access: Limit user access rights to the bare minimum needed to perform their jobs.
Role of Encryption
Encryption is a critical tool in safeguarding data. It ensures that even if data is intercepted, it remains unreadable to unauthorized users.
- Data-at-Rest Encryption: Protect data stored on physical or virtual storage.
- Data-in-Transit Encryption: Secure data being transmitted across networks.

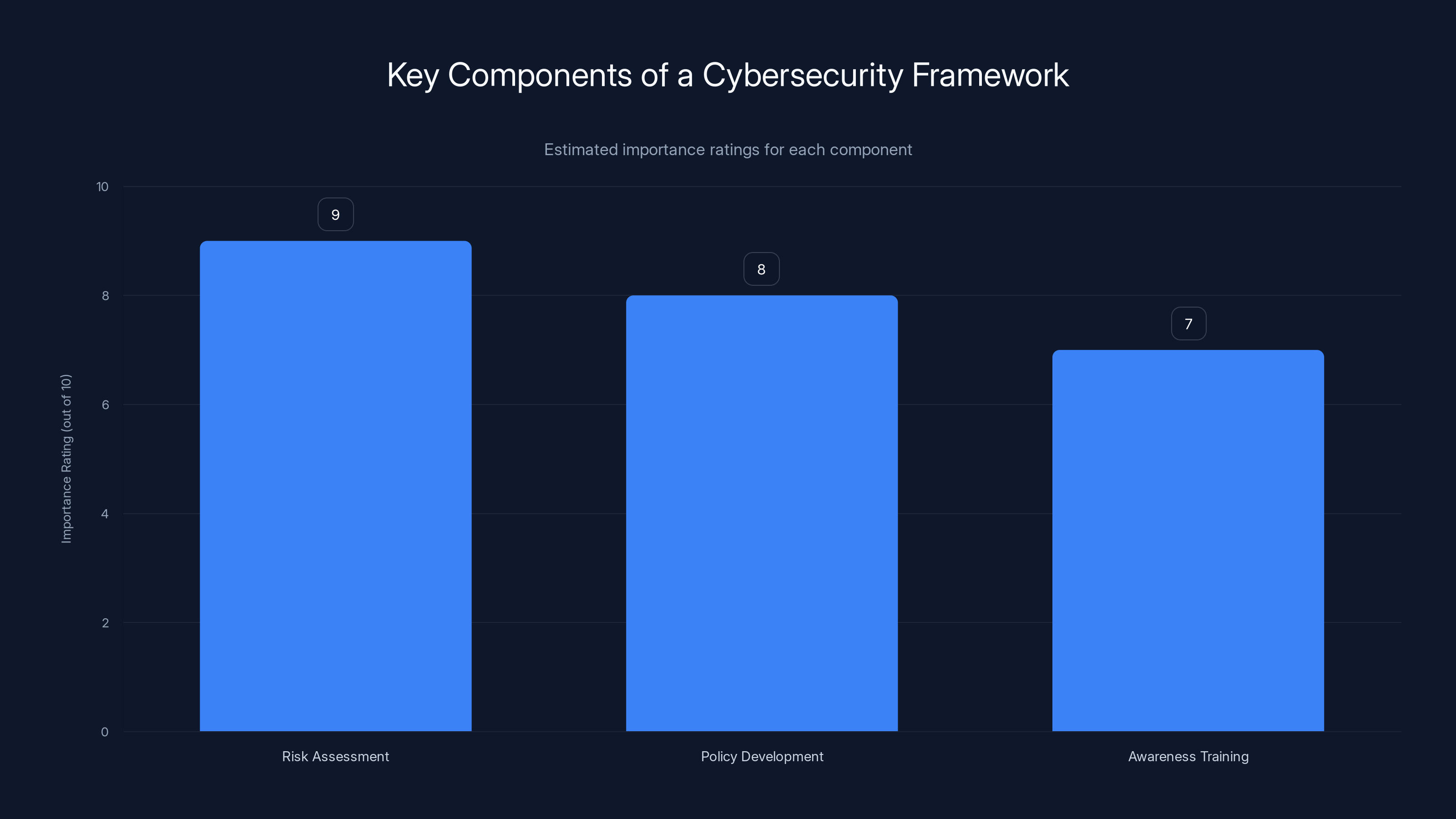
Risk assessment is rated highest in importance for establishing a cybersecurity framework, followed by policy development and awareness training. Estimated data.
Common Pitfalls and Solutions
Overreliance on Cloud Providers
Organizations often assume cloud providers fully manage security, leading to potential gaps. It's crucial to:
- Understand Shared Responsibility Models: Clarify which security aspects the provider covers and which are the customer's responsibility.
- Conduct Independent Security Evaluations: Regular assessments can uncover vulnerabilities overlooked by the provider.
Insufficient Incident Response Planning
An inadequate incident response plan can exacerbate the impact of a cyberattack. Ensure your plan includes:
- Defined Roles and Responsibilities: Clearly outline who does what in the event of an incident.
- Regular Drills and Simulations: Test and refine your response plan periodically.

Practical Implementation Guides
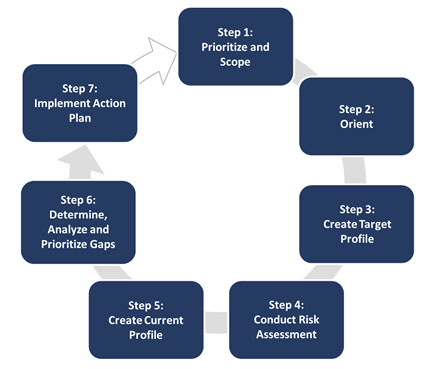
Establishing a Cybersecurity Framework
Creating a robust cybersecurity framework involves several steps:
- Risk Assessment: Identify and prioritize potential risks to your organization.
- Policy Development: Establish clear security policies and procedures.
- Awareness Training: Conduct regular training sessions for staff on security best practices.
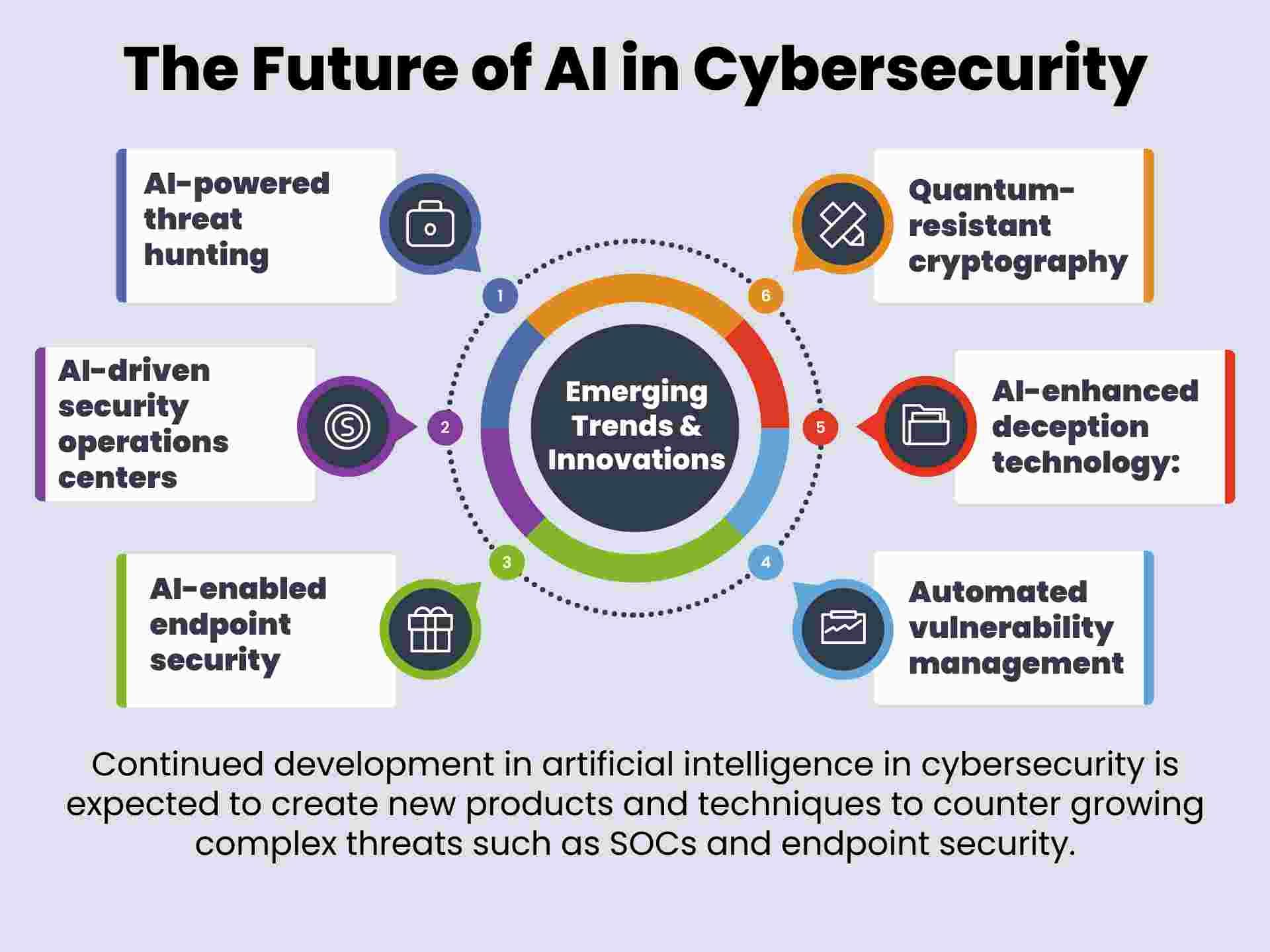
Utilizing AI for Cybersecurity
AI can enhance threat detection and response capabilities:
- Behavioral Analysis: AI can detect anomalies by analyzing user behavior patterns.
- Automated Responses: Implement AI-driven systems to automatically quarantine threats upon detection.
Future Trends and Recommendations
The Rise of AI in Cybersecurity
AI is set to revolutionize cybersecurity with capabilities such as predictive analytics and automated threat mitigation.
- Predictive Threat Intelligence: AI can anticipate potential threats based on historical data and trends.
- Adaptive Security Models: AI-driven systems that adapt to evolving threats in real-time.
Importance of Cyber Hygiene
Cyber hygiene involves routine practices to ensure system health and security. Key practices include:
- Regular Software Updates: Keep all systems and applications up to date to protect against known vulnerabilities.
- Strong Password Policies: Encourage the use of complex passwords and regular changes.
Conclusion
The cyberattack on the European Commission serves as a stark reminder of the ever-evolving cybersecurity landscape. By learning from this incident, organizations can bolster their defenses, implement best practices, and stay ahead of emerging threats.
FAQ
What is a cyberattack?
A cyberattack is an offensive maneuver employed by individuals or organizations targeting computer systems, infrastructures, networks, or personal devices, often with the intent to steal, alter, or destroy data.
How does the European Commission handle cyberattacks?
The European Commission handles cyberattacks by implementing immediate containment measures, conducting thorough investigations, and enhancing security protocols to prevent future incidents.
What are the benefits of a Zero Trust architecture?
Zero Trust architecture enhances security by verifying every request as though it originates from an open network, reducing the risk of unauthorized access and data breaches.
How can organizations improve their cybersecurity posture?
Organizations can improve cybersecurity by conducting regular risk assessments, implementing comprehensive security frameworks, and leveraging AI for threat detection and response.
Why is encryption important in cybersecurity?
Encryption protects sensitive data by converting it into a coded form, making it unreadable to unauthorized users, thereby preventing data breaches.
What future trends are expected in cybersecurity?
Future trends in cybersecurity include increased adoption of AI-driven solutions, greater emphasis on cyber hygiene, and the development of adaptive security models that evolve with emerging threats.

Key Takeaways
- Data breaches highlight vulnerabilities in cloud security systems.
- Immediate response and containment are crucial in mitigating cyberattacks.
- Zero Trust architecture is essential for modern cybersecurity.
- AI offers advanced threat detection and response capabilities.
- Understanding shared responsibility models with cloud providers prevents security oversights.
- Regular training and drills enhance incident response effectiveness.
- Future trends include AI-driven adaptive security models and enhanced cyber hygiene.
Related Articles
- Understanding Banking App Glitches: Lessons from Lloyds and Beyond [2025]
- Understanding the Risks: Are American VPN Users Facing 'Warrantless' Government Surveillance? [2025]
- Maximize Your Cybersecurity: A 20% Off Acronis Cyber Protect Deal [2025]
- English Learning Apps: Critical Security Risks and Best Practices [2025]
- LangChain Framework Faces Security Challenges: Key Vulnerabilities and Best Practices [2025]
- Understanding the Impact of AI and Data Centers: A Deep Dive into the Sanders-AOC Bill [2025]
![Understanding Cybersecurity in the EU: Lessons from the European Commission Cyberattack [2025]](https://tryrunable.com/blog/understanding-cybersecurity-in-the-eu-lessons-from-the-europ/image-1-1774634678545.jpg)



