FBI Takedown of W3LL: A Cybercrime Platform Exposed [2025]
In the latest twist of the cat-and-mouse game that is cybersecurity, the FBI has dismantled a notorious cybercrime operation known as W3LL. This was not your run-of-the-mill phishing scam; it was a full-fledged cybercrime platform targeting thousands worldwide. Let's unpack what made W3LL a significant threat and how its dismantling impacts the broader cybersecurity landscape.
TL; DR
- W3LL was more than a phishing operation; it offered full-service cybercrime tools.
- The operation targeted thousands of victims globally, affecting both individuals and businesses.
- The FBI's takedown involved international cooperation, highlighting the need for global cybersecurity strategies.
- Future cybersecurity measures must focus on collaboration and advanced threat detection.
- Awareness and training are crucial for individuals and organizations to prevent similar threats.
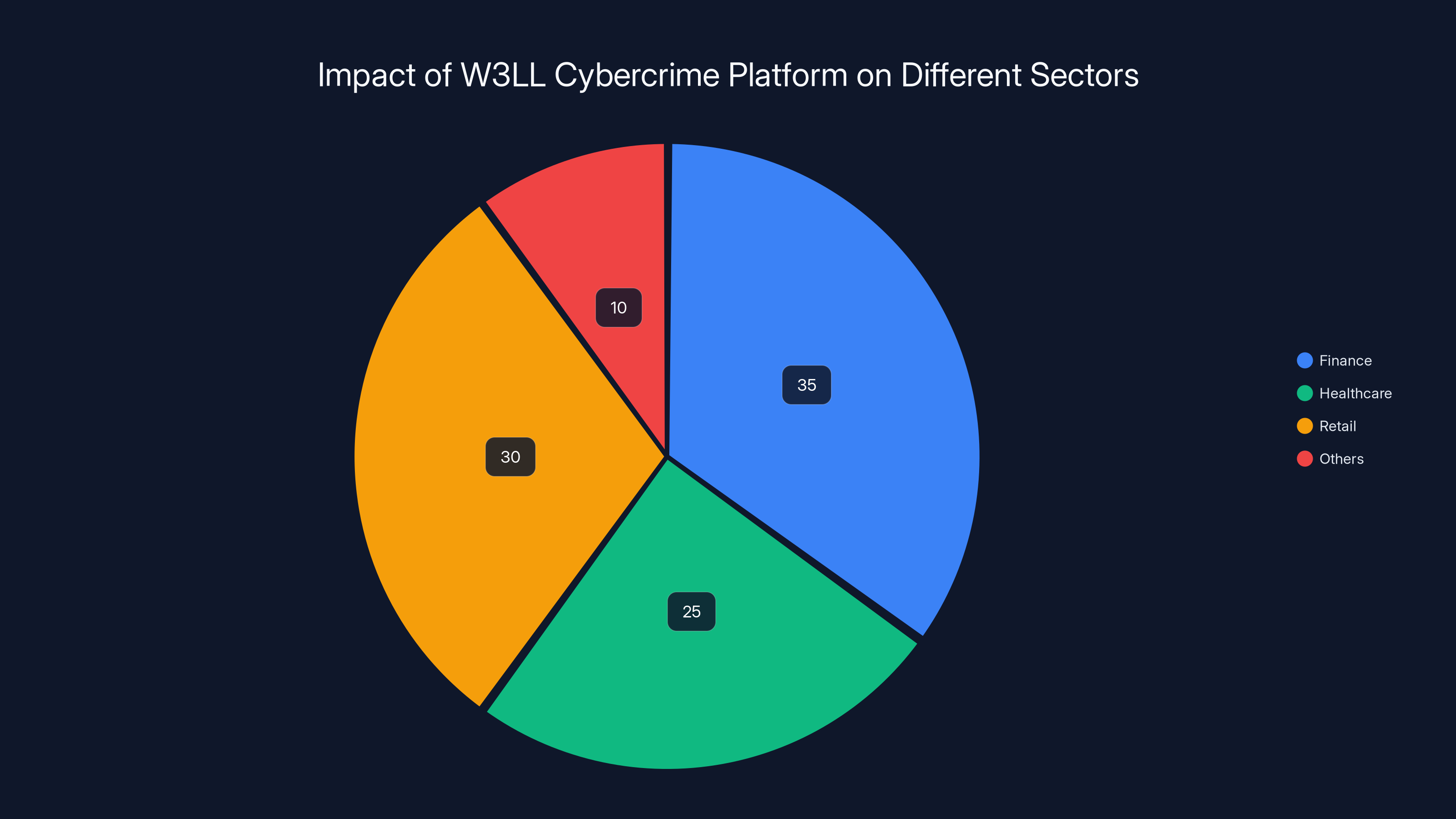
The W3LL platform had the most significant impact on the finance sector (35%), followed by retail (30%) and healthcare (25%). Estimated data.
Understanding the W3LL Cybercrime Platform
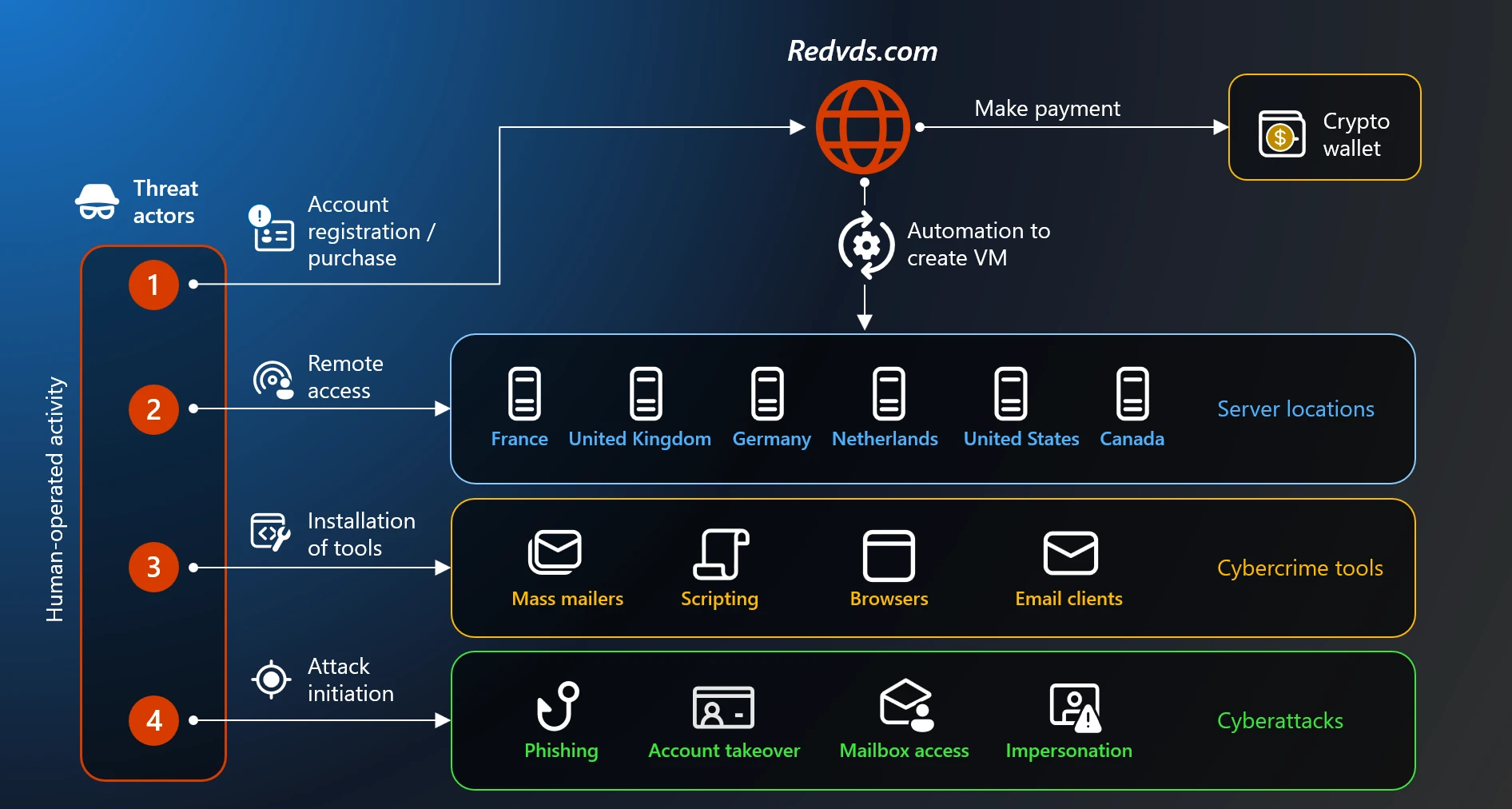
The W3LL operation was a sophisticated cybercrime platform that provided tools and services for executing phishing attacks. Unlike typical phishing operations that merely aim to steal credentials, W3LL offered a comprehensive suite of tools that facilitated everything from crafting phishing emails to managing stolen data.
What Made W3LL Different?
W3LL was not just about sending out deceptive emails. It was about creating an ecosystem where cybercriminals could operate with ease. Key features included:
- Spoofing Tools: Enabled attackers to create convincing replicas of legitimate websites.
- Credential Harvesters: Automated the collection of sensitive information from victims.
- Data Management Systems: Allowed criminals to organize and exploit stolen data efficiently.
Real-World Impact
The operation targeted sectors like finance, healthcare, and retail, affecting both individuals and organizations. For instance, a major retail chain reported a breach where customer data was accessed and misused, leading to significant financial losses and reputational damage.
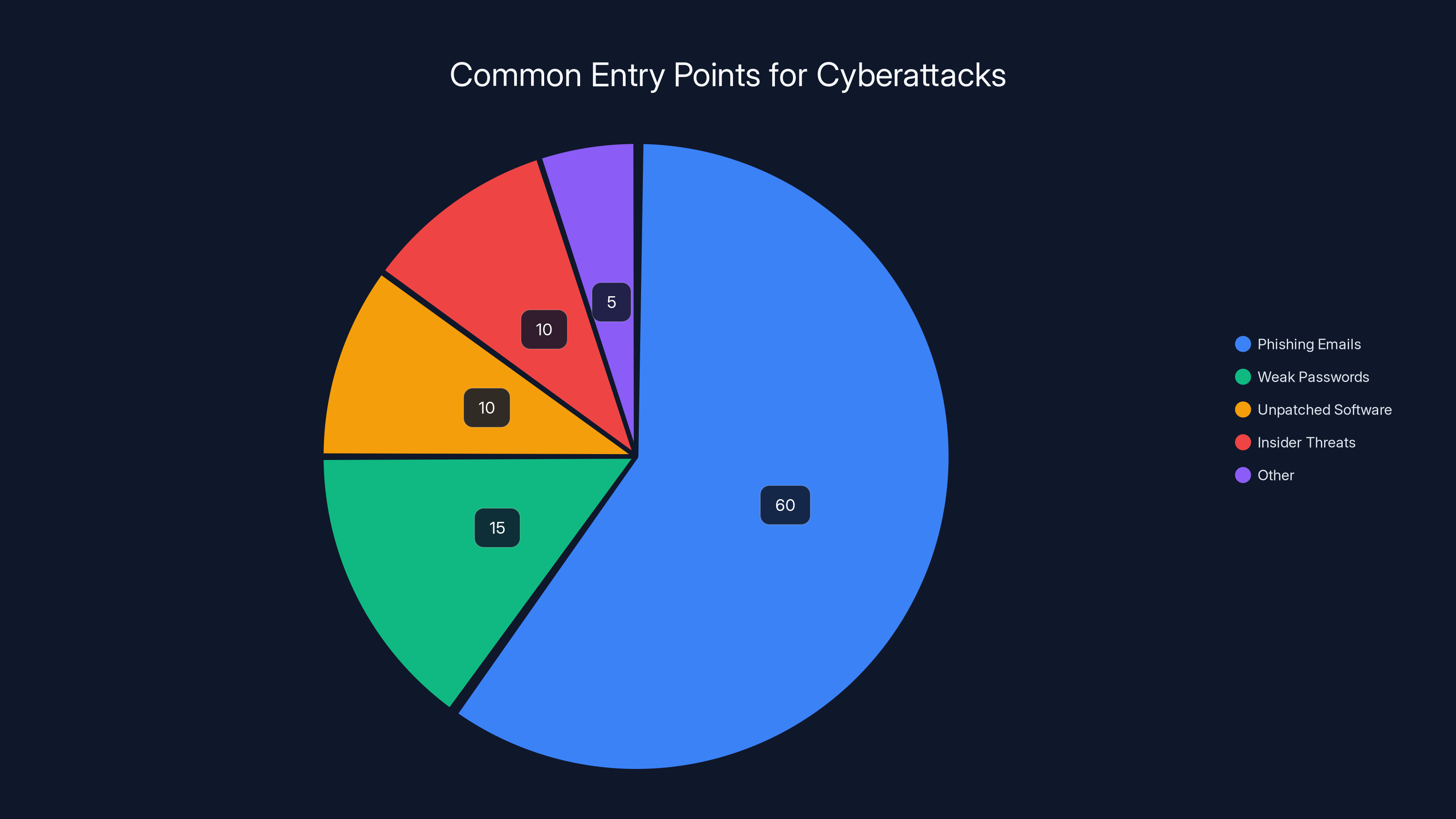
Phishing emails account for an estimated 60% of cyberattack entry points, highlighting the importance of email security and awareness. (Estimated data)
Anatomy of a Phishing Attack
To understand the threat posed by W3LL, it's essential to grasp how phishing attacks work. Typically, these attacks follow a structured approach to deceive victims into revealing sensitive information.
- Reconnaissance: Attackers gather information about potential targets.
- Crafting the Lure: Phishing emails or messages are designed to appear legitimate.
- Delivery: The lure is sent to the target via email, social media, or other channels.
- Exploitation: Victims interact with the lure, often leading to a fake website.
- Harvesting: Credentials and sensitive information are collected.
FBI's Takedown: A Collaborative Effort
The FBI's success in shutting down W3LL was not achieved in isolation. It required collaboration with international law enforcement agencies, showcasing a model for future cybercrime investigations. According to the FBI, this operation involved significant international cooperation.
Key Strategies Used
- Intelligence Sharing: Agencies across various countries shared data and insights, enabling a comprehensive understanding of W3LL's operations.
- Advanced Tracking: Cyber forensics played a crucial role in tracing the origins and networks involved.
- Legal Cooperation: International legal frameworks facilitated the apprehension and prosecution of suspects.


Organizations should focus on a balanced approach, with 'People' and 'Training' being slightly more critical due to the human factor in security breaches. Estimated data.
The Role of Technology in Modern Cybercrime
Cybercriminals are leveraging advanced technologies to enhance the efficacy of their operations. W3LL exemplifies how these technologies can be used maliciously. As noted by Wiz Academy, AI and automation play a crucial role in modern cybercrime.
AI and Automation
Artificial Intelligence (AI) and automation were integral to W3LL's operations, enabling:
- Automated Emails: AI-driven tools crafted and sent personalized phishing emails at scale.
- Data Analysis: Automation helped in analyzing and categorizing stolen data efficiently.
Cryptocurrency and Anonymity
Cryptocurrency facilitated anonymous transactions, making it challenging to trace financial trails back to the perpetrators. This anonymity is a double-edged sword in the digital economy.

Protecting Against Phishing and Cybercrime
Individuals and businesses can employ several strategies to guard against phishing and broader cybercriminal activities. According to Insurance Business Magazine, refining phishing tactics with AI is a growing concern.
Best Practices for Individuals
- Verify Links: Always check URLs before clicking. Look for subtle misspellings or unusual domain names.
- Use Multi-Factor Authentication (MFA): Adding an extra layer of security can prevent unauthorized access even if credentials are compromised.
- Educate Yourself: Stay informed about the latest phishing tactics and practice vigilance online.
Best Practices for Organizations
- Employee Training: Conduct regular cybersecurity training sessions to keep staff informed about potential threats.
- Implement Security Protocols: Deploy advanced security solutions such as firewalls, intrusion detection systems, and anti-phishing tools.
- Conduct Regular Audits: Frequent security audits can help identify vulnerabilities before they're exploited.

Cybersecurity Challenges and Solutions
Despite advancements in technology, cybersecurity remains a challenging field. The dynamic nature of cyber threats demands constant vigilance and adaptation.
Common Pitfalls
- Overconfidence in Technology: Relying solely on technology without human oversight can lead to blind spots.
- Ignoring Insider Threats: Employees can unintentionally or maliciously cause security breaches.
- Delayed Updates: Failing to update software and systems promptly can leave vulnerabilities open.
Solutions and Recommendations
- Adopt a Holistic Approach: Combine technology, processes, and people in your cybersecurity strategy.
- Leverage Threat Intelligence: Use threat intelligence platforms to stay ahead of emerging threats.
- Foster a Security Culture: Encourage a culture of security awareness within your organization.
Future Trends in Cybersecurity
As cyber threats continue to evolve, so too must our responses. The following trends are shaping the future of cybersecurity. According to Fortune, AI-driven security measures are becoming increasingly important.
Rise of AI-Driven Security
AI and machine learning are becoming pivotal in detecting and responding to threats in real-time. These technologies enable:
- Predictive Analysis: AI can identify patterns that precede an attack, providing early warnings.
- Automated Incident Response: Machine learning algorithms can autonomously respond to certain types of attacks, reducing response times.
Enhanced International Cooperation
Cybercrime knows no borders, and neither should cybersecurity efforts. Enhanced international cooperation will be crucial in tackling global threats.

Conclusion: The Battle Continues
The takedown of W3LL is a victory, but it's just one battle in the ongoing war against cybercrime. As technology advances, so do the methods of cybercriminals. By staying informed, adopting best practices, and fostering global cooperation, we can better protect against the threats of tomorrow.

FAQ
What was the W3LL operation?
The W3LL operation was a sophisticated cybercrime platform that offered tools for executing phishing attacks, targeting thousands of individuals and businesses worldwide.
How did the FBI dismantle W3LL?
The FBI's takedown involved international collaboration, intelligence sharing, and advanced cyber forensics to trace and dismantle the network.
How can individuals protect themselves from phishing?
Individuals can protect themselves by verifying URLs, using multi-factor authentication, and staying informed about the latest phishing tactics.
What role does AI play in modern cybercrime?
AI is used to automate and enhance phishing attacks, enabling cybercriminals to craft more convincing lures and analyze stolen data efficiently.
What are the future trends in cybersecurity?
Future trends include the rise of AI-driven security measures, enhanced international cooperation, and a focus on building a culture of security awareness.
Why is international cooperation important in cybersecurity?
Cybercrime often crosses national borders, making international cooperation essential for effective threat detection, response, and prosecution.
How can organizations build a robust cybersecurity strategy?
Organizations should adopt a holistic approach, combining technology, processes, and people, while conducting regular audits and fostering a security culture.
What is the importance of employee training in cybersecurity?
Employee training is crucial as it helps staff recognize phishing attempts and understand the importance of following security protocols.

Key Takeaways
- W3LL was a full-service cybercrime platform beyond typical phishing operations.
- The operation's global impact highlights the need for robust cybersecurity measures.
- FBI's successful takedown illustrates the importance of international cooperation.
- AI and machine learning are crucial in modern threat detection and response.
- Organizations must adopt holistic security strategies combining technology, processes, and people.
Related Articles
- Understanding the Basic-Fit Data Breach: A Comprehensive Guide to Data Security [2025]
- Booking.com Data Breach: What Customers Need to Know [2025]
- Understanding the Impact of Cybersecurity Breaches on Gaming Industry: A Deep Dive [2025]
- Your Push Notifications Aren’t Safe From the FBI | WIRED
- Secure Your Digital Life: Keeper Password Manager's Big Discounts [2026]
- Agility is the Key to Protecting Against Malware-as-a-Service [2025]
![FBI Takedown of W3LL: A Cybercrime Platform Exposed [2025]](https://tryrunable.com/blog/fbi-takedown-of-w3ll-a-cybercrime-platform-exposed-2025/image-1-1776179165819.jpg)



