Understanding the Basic-Fit Data Breach: A Comprehensive Guide to Data Security [2025]
Introduction
In the digital age, data breaches are becoming increasingly common, with organizations of all sizes falling victim to cyber attacks. Recently, Basic-Fit, a popular gym chain, experienced a significant data breach that exposed the personal details of over a million of its members across six countries. This breach included sensitive information like names, contact details, dates of birth, and bank information, although passwords reportedly remained secure. This incident highlights critical vulnerabilities in data security practices and raises important questions about how organizations can protect sensitive information.
In this comprehensive guide, we'll delve deep into the Basic-Fit data breach, examining what happened, the aftermath, and the broader lessons in data security. We'll explore best practices, common pitfalls, and future trends in cybersecurity, providing a resource for both individuals and organizations to enhance their data protection strategies.
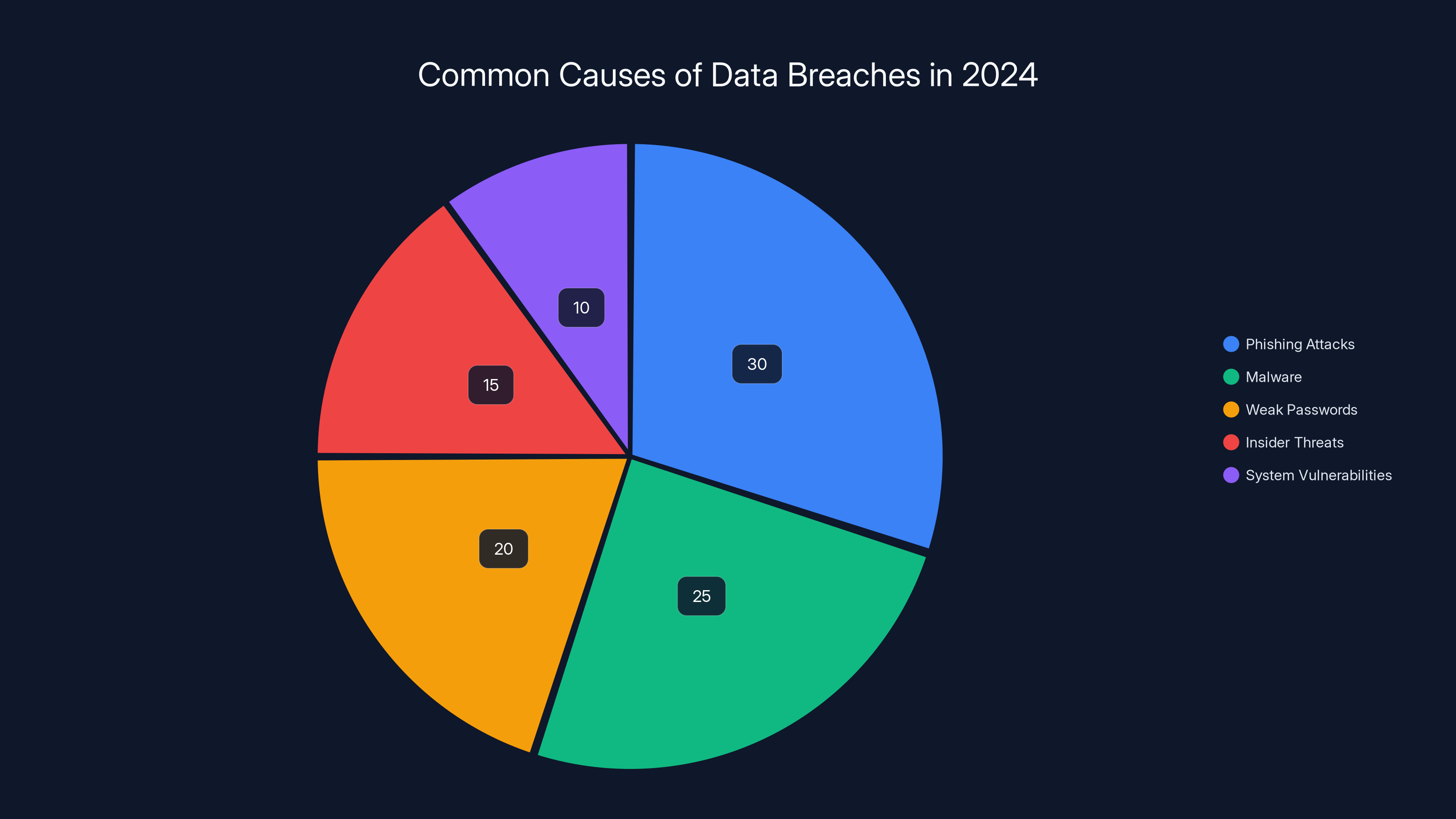
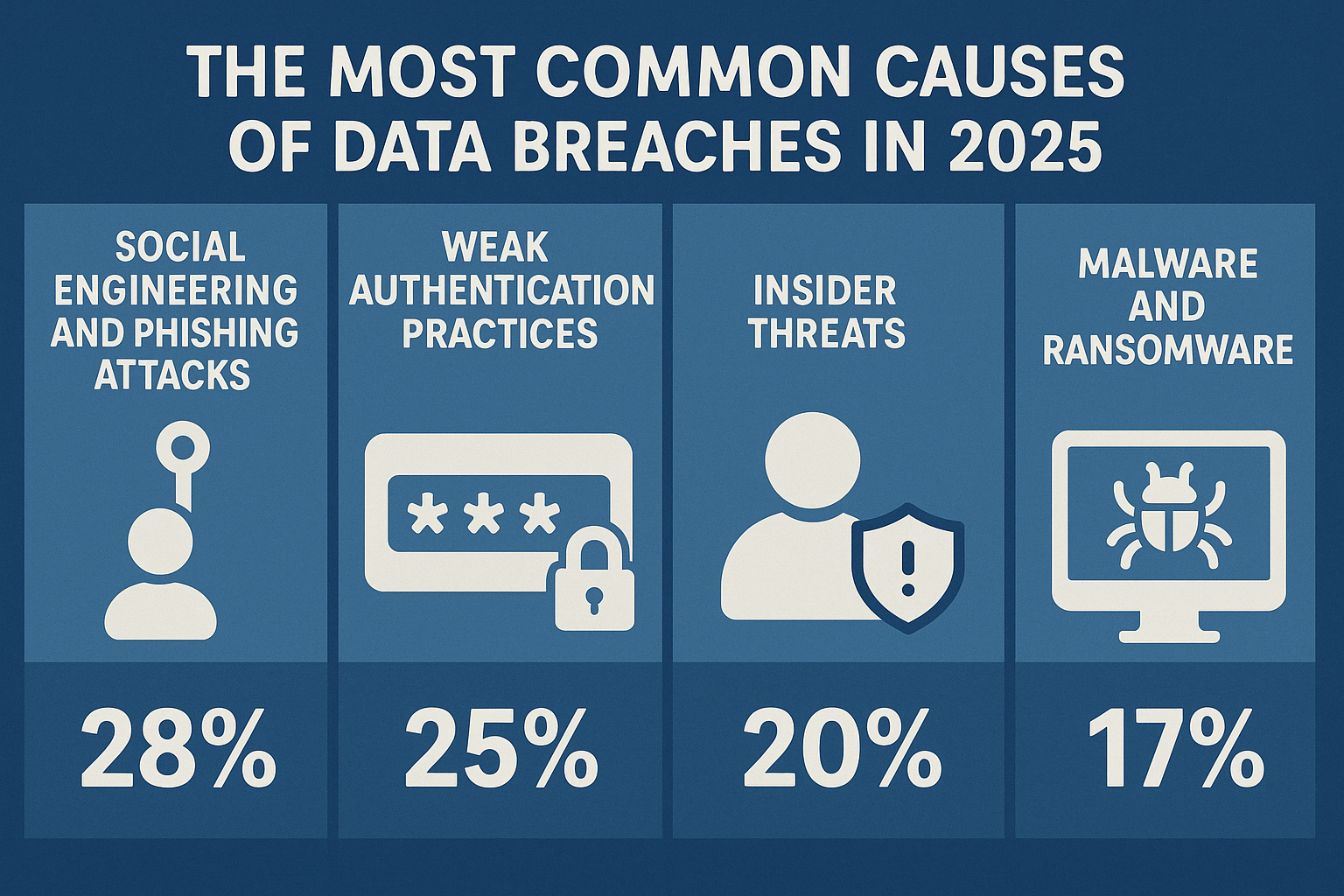
Phishing attacks are estimated to be the leading cause of data breaches in 2024, accounting for 30% of incidents, followed by malware at 25%. (Estimated data)
TL; DR
- Breach Impact: Over 1 million members across six countries were affected, as reported by CyberPress.
- Sensitive Data Exposed: Included names, contact details, DOB, and bank info, according to Athletech News.
- Cybersecurity Gaps: The breach highlights vulnerabilities in data protection.
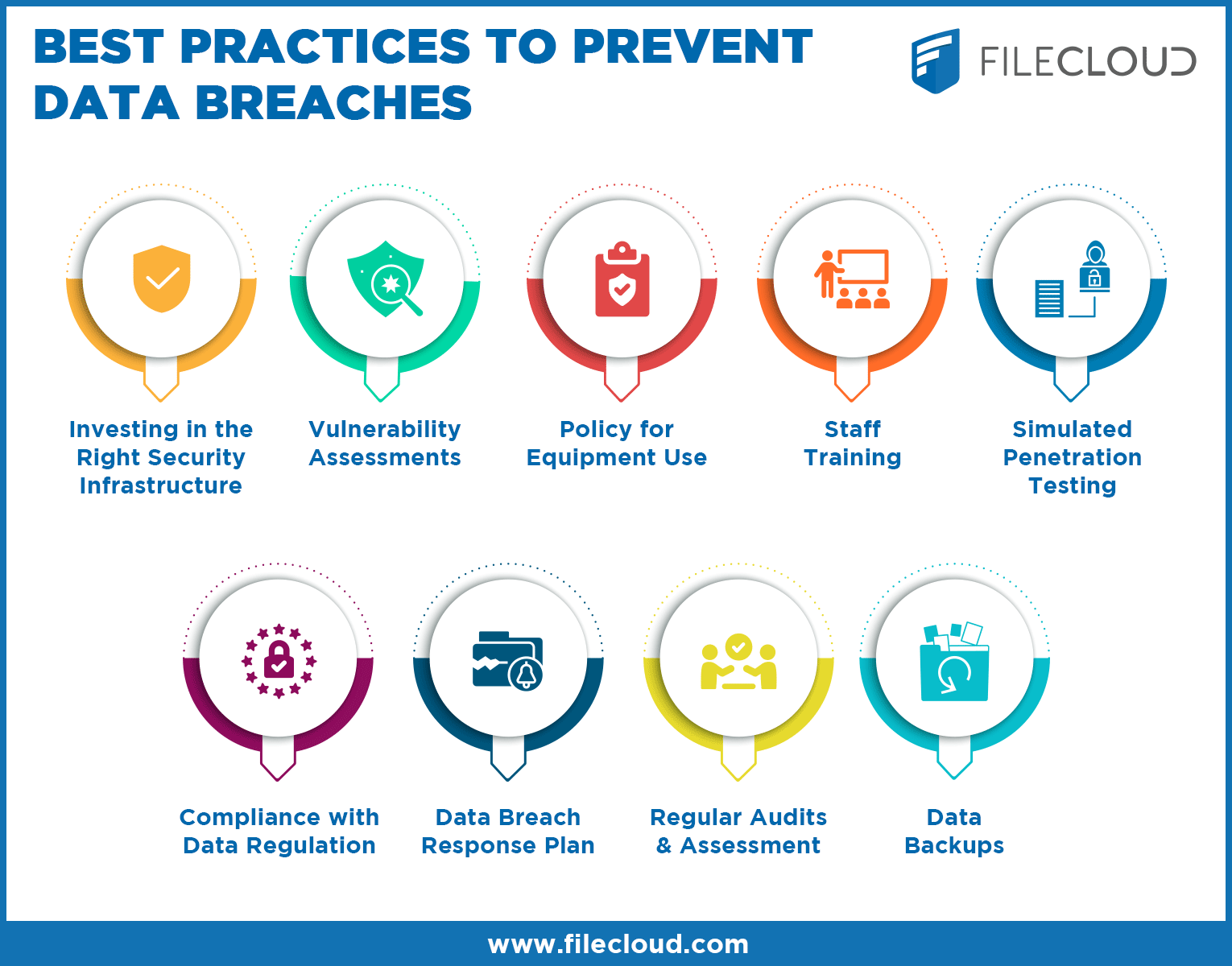
- Best Practices: Regular security audits and employee training are crucial.
- Future Trends: AI and automation in threat detection are on the rise.
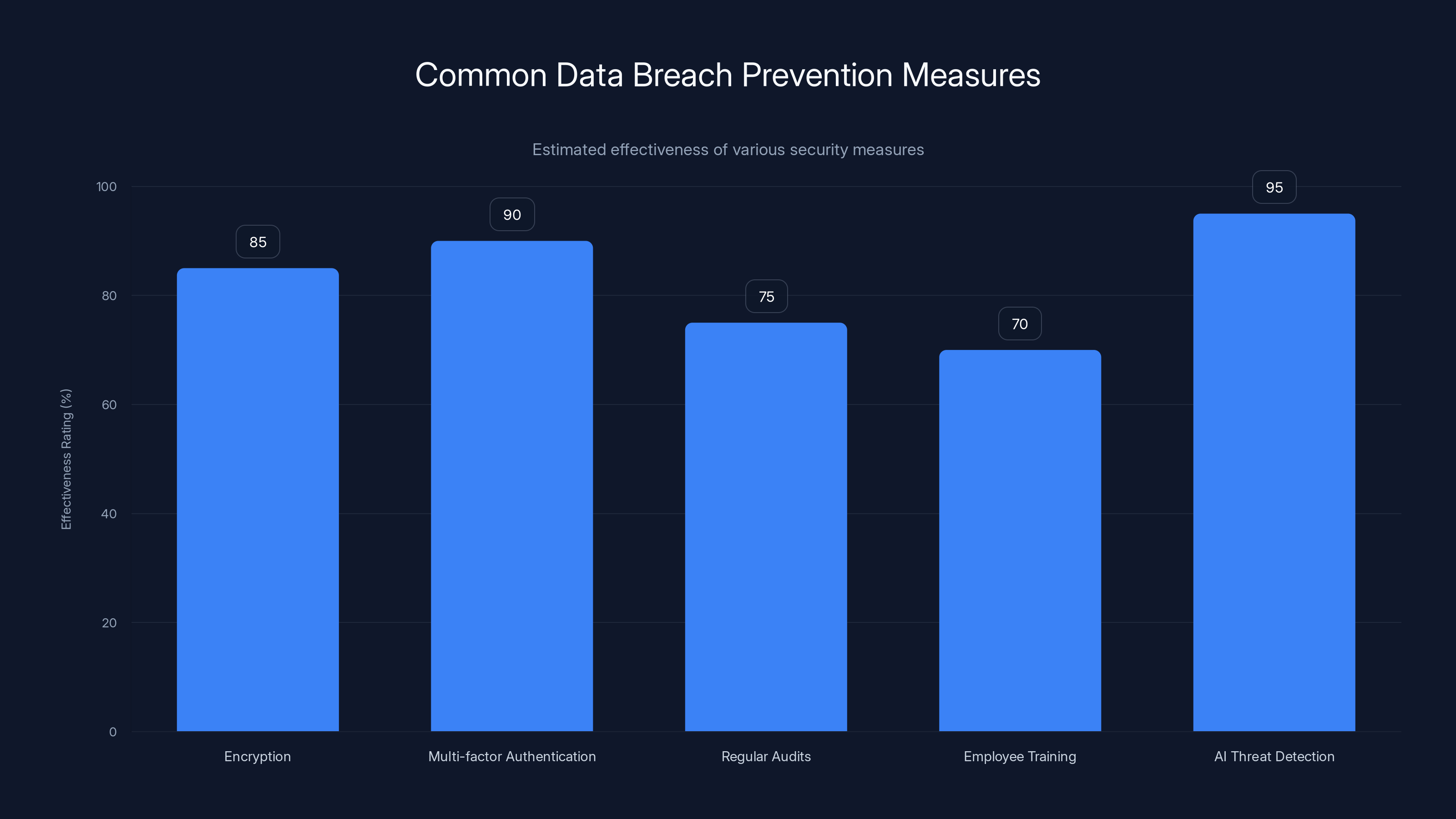
AI threat detection and multi-factor authentication are among the most effective measures for preventing data breaches. (Estimated data)
The Basic-Fit Data Breach: What Happened?
In the face of increasing cyber threats, the Basic-Fit breach stands out due to its scale and impact. The attackers infiltrated the gym's systems, gaining unauthorized access to the personal data of more than a million members. The stolen data primarily included personally identifiable information (PII) such as names, contact details, dates of birth, and bank information. Fortunately, passwords were not compromised, which is a small consolation for those affected.
Anatomy of the Breach
The breach occurred due to inadequate security measures that left Basic-Fit's systems vulnerable to attack. It's believed that the attackers exploited vulnerabilities in the company's network, potentially through phishing or social engineering tactics. Once inside, they were able to extract vast amounts of sensitive data, as detailed by The Next Web.
Immediate Response
Upon discovering the breach, Basic-Fit took immediate action to contain the attack. They worked closely with cybersecurity experts to secure their systems and began an internal investigation to understand the full scope of the breach. The company also notified affected members and relevant authorities, as required by data protection laws, according to Reuters.
Understanding Data Breaches
What is a Data Breach?
A data breach occurs when unauthorized individuals gain access to confidential data, often with malicious intent. This can lead to the exposure, theft, or misuse of sensitive information. Data breaches can have severe consequences for both individuals and organizations, including financial loss, reputational damage, and legal repercussions.
Common Causes of Data Breaches
- Phishing Attacks: Deceptive emails or messages trick users into providing sensitive information.
- Malware: Malicious software infiltrates systems, allowing attackers to extract data.
- Weak Passwords: Easily guessable or reused passwords can be exploited by attackers.
- Insider Threats: Employees with access to sensitive data may intentionally or unintentionally cause breaches.
- System Vulnerabilities: Outdated software and unpatched systems are prime targets for attackers.
The Implications of Data Breaches
Data breaches can have far-reaching implications beyond immediate financial losses. They can erode customer trust, lead to regulatory fines, and necessitate costly remediation efforts. Moreover, the exposure of sensitive data can result in identity theft, fraud, and other criminal activities.
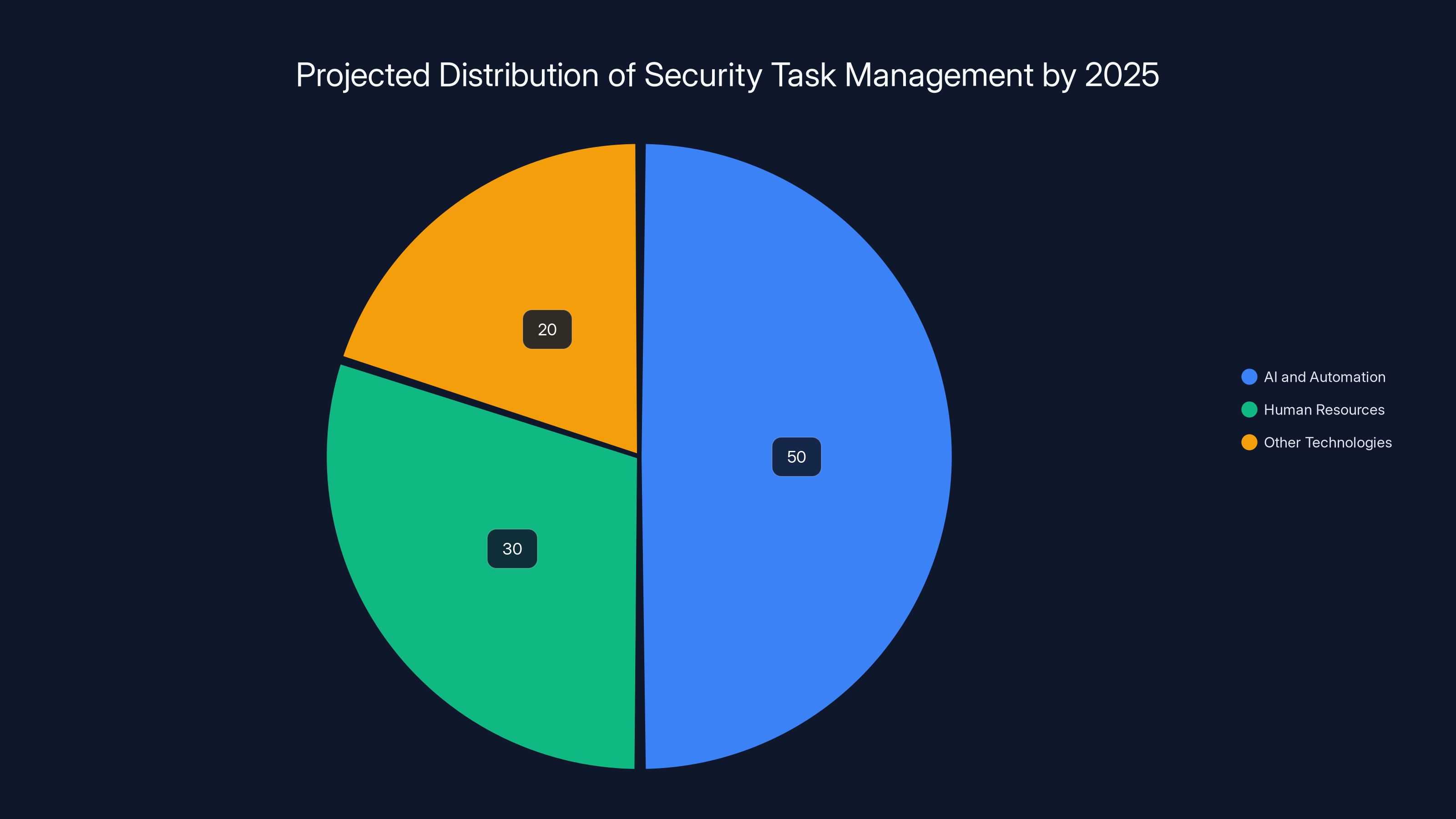
By 2025, AI and automation are expected to manage over 50% of routine security tasks, significantly reducing the burden on human resources. (Estimated data)
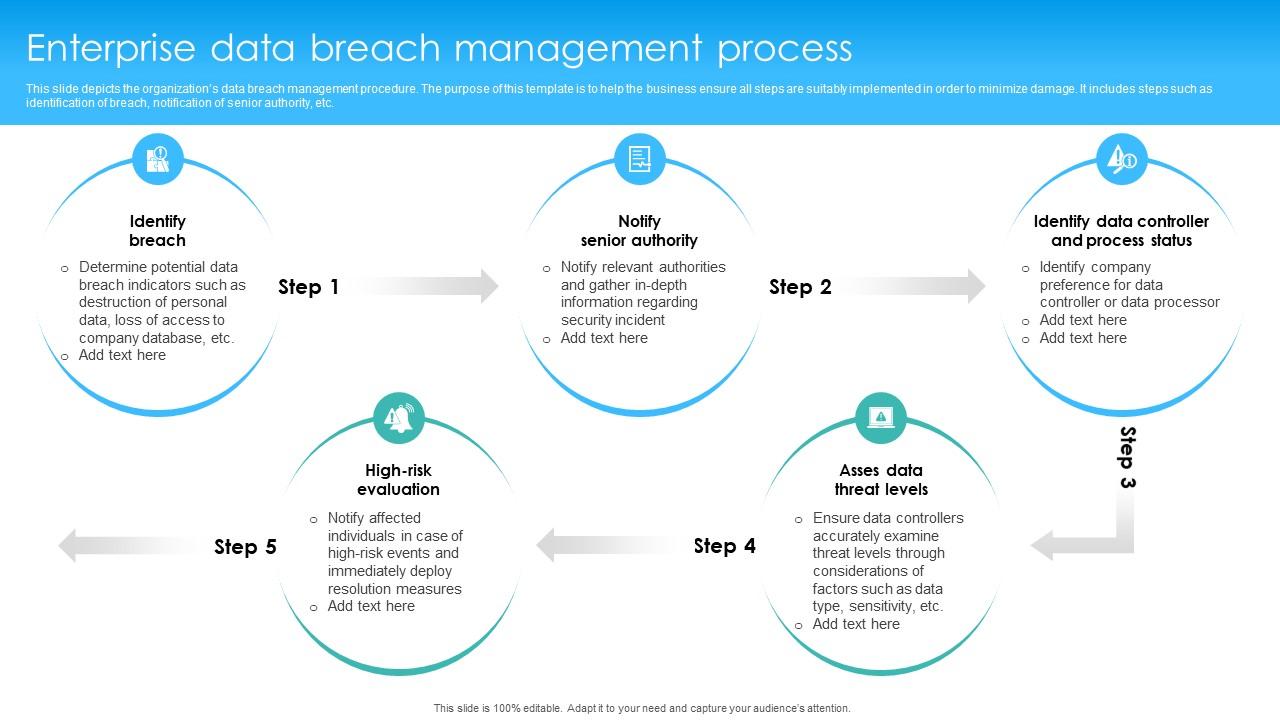
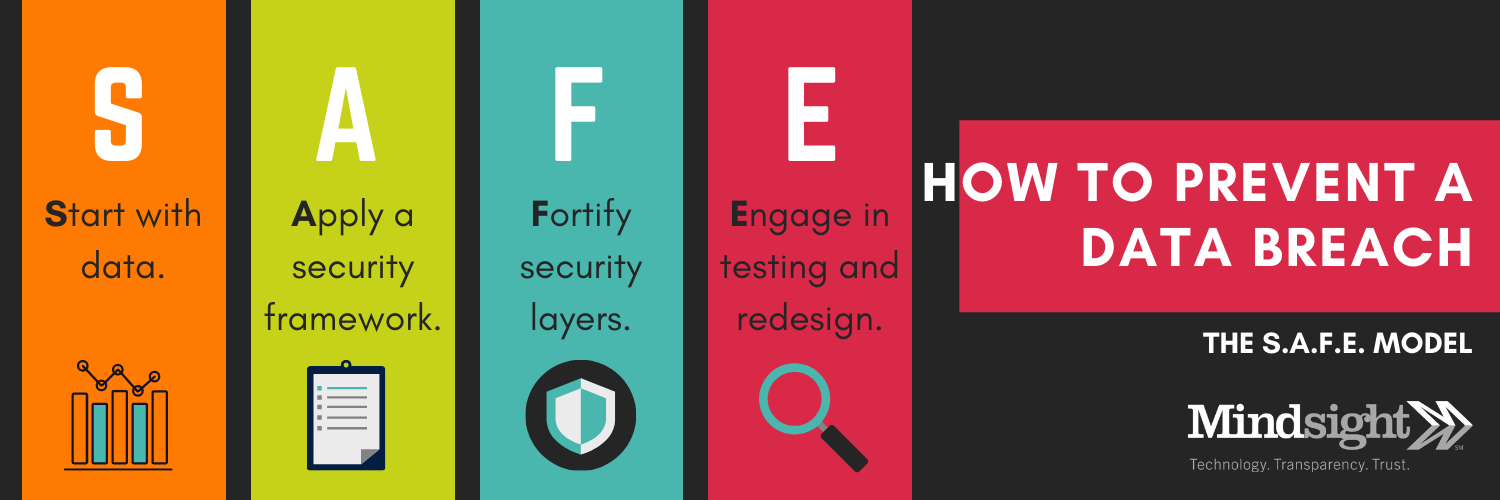
Responding to a Data Breach: Best Practices
1. Swift Identification and Containment
The first step in responding to a data breach is to identify and contain the incident as quickly as possible. This involves isolating affected systems to prevent further unauthorized access and starting an investigation to determine the breach's origin and scope.
2. Notification and Communication
Affected individuals and relevant authorities must be notified promptly, as dictated by data protection regulations like the GDPR in Europe. Transparent communication helps maintain trust and allows individuals to take protective measures.
3. Incident Analysis and Remediation
Conducting a thorough analysis of the breach helps organizations understand how it occurred and what measures can prevent future incidents. Remediation efforts may include patching vulnerabilities, enhancing security protocols, and updating software.
4. Ongoing Monitoring and Prevention
Implementing ongoing monitoring solutions and regular security audits can help detect potential threats before they escalate. Employee training and awareness programs are also vital to prevent common threats like phishing.
Implementing Robust Security Measures
Encryption
Encryption is a fundamental security measure that protects data by converting it into a code that can only be deciphered with a specific key. Encrypting sensitive data, both in transit and at rest, ensures that even if data is intercepted or accessed without authorization, it cannot be read or misused.
Multi-Factor Authentication (MFA)
MFA adds an extra layer of security by requiring users to provide two or more verification factors to gain access to a system. This could include something they know (a password), something they have (a smartphone), or something they are (a fingerprint).
Regular Security Audits
Conducting regular security audits allows organizations to identify and address vulnerabilities before they can be exploited. These audits should include penetration testing, vulnerability assessments, and reviews of security policies and procedures.
Employee Training and Awareness
Human error is a leading cause of data breaches. Regular training programs can help employees recognize phishing attempts, handle sensitive data securely, and adhere to company security policies.
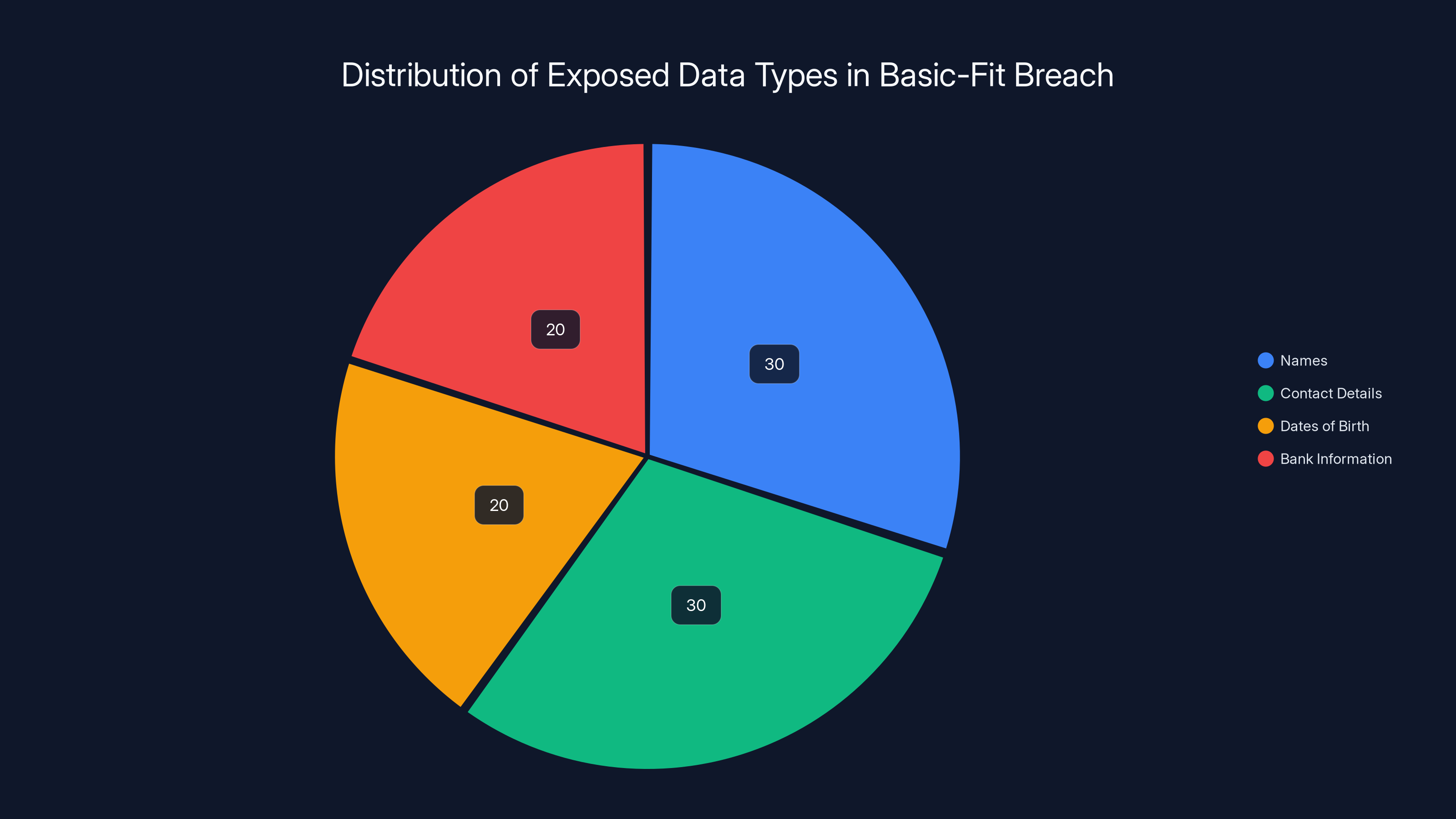
An estimated distribution of the types of data exposed in the Basic-Fit breach, highlighting the variety of personal information compromised. Estimated data.
Case Study: A Successful Breach Response
In 2022, a major retail company experienced a data breach that exposed the personal information of millions of customers. The company's swift and effective response serves as a model for others.
What They Did Right
- Immediate Containment: The company quickly isolated affected systems and began an investigation.
- Transparent Communication: Customers were notified within 48 hours, and regular updates were provided.
- Comprehensive Remediation: Vulnerabilities were patched, and security measures were enhanced.
- Long-Term Monitoring: Continuous monitoring was implemented to detect future threats.
This proactive approach minimized damage and helped restore customer trust.
The Role of Technology in Data Security
Advancements in technology are playing a crucial role in enhancing data security. From AI-powered threat detection to blockchain-based solutions, new tools are helping organizations stay ahead of cyber threats.
AI and Machine Learning
AI and machine learning are revolutionizing threat detection and response. These technologies can analyze vast amounts of data to identify patterns and anomalies, enabling faster and more accurate detection of potential threats, as discussed in Microsoft's security blog.
Blockchain for Data Security
Blockchain technology offers a decentralized and tamper-proof way to store and manage data. Its transparency and immutability make it an attractive option for organizations looking to enhance data security.
Automating Security Processes
Automation is streamlining security processes, reducing the risk of human error, and allowing security teams to focus on more strategic tasks. Automated solutions can handle tasks such as patch management, threat detection, and incident response.
Common Pitfalls in Data Security
Despite the availability of advanced security technologies, many organizations still fall victim to common pitfalls that can compromise their data security efforts.
Overlooking Insider Threats
Insider threats, whether malicious or accidental, are often overlooked. Organizations need to implement monitoring and access controls to mitigate these risks.
Inadequate Patch Management
Failing to regularly update and patch software leaves systems vulnerable to known exploits. Organizations should implement automated patch management solutions to ensure timely updates.
Lack of Employee Training
Without proper training, employees may fall victim to phishing attacks or inadvertently expose sensitive data. Continuous education and awareness programs are essential.
Underestimating the Importance of Backups
Regular data backups are crucial for recovery in the event of a breach. Organizations should implement a comprehensive backup strategy that includes both on-site and off-site storage.
Future Trends in Data Security
As cyber threats continue to evolve, so too must the strategies and technologies used to combat them. Here are some key trends shaping the future of data security.
Zero Trust Architecture
Zero Trust is a security framework that requires all users, inside or outside the organization's network, to be authenticated and authorized before accessing resources. This approach minimizes the risk of unauthorized access and lateral movement within the network.
Quantum-Resistant Cryptography
With the advent of quantum computing, traditional cryptographic algorithms may become vulnerable. Quantum-resistant cryptography aims to develop algorithms that can withstand quantum attacks.
Data Privacy Regulations
Data privacy regulations are becoming more stringent, with new laws being introduced worldwide. Organizations must stay informed and compliant to avoid legal repercussions and protect customer data.
Conclusion
The Basic-Fit data breach serves as a stark reminder of the importance of robust data security practices. As cyber threats continue to grow in sophistication and frequency, organizations must prioritize data protection and stay informed of emerging trends and technologies. By implementing best practices, conducting regular security audits, and leveraging advanced technologies, businesses can protect their sensitive information and maintain customer trust.
FAQ
What is a data breach?
A data breach occurs when unauthorized individuals gain access to confidential data, often with malicious intent. This can lead to the exposure, theft, or misuse of sensitive information.
How can organizations prevent data breaches?
Organizations can prevent data breaches by implementing robust security measures such as encryption, multi-factor authentication, regular security audits, and employee training.
What should individuals do if their data is compromised?
If your data is compromised, monitor your accounts for suspicious activity, change passwords, and consider placing a fraud alert on your credit report.
What role does AI play in data security?
AI can enhance data security by automating threat detection and response, analyzing patterns and anomalies, and reducing the risk of human error.
What is Zero Trust architecture?
Zero Trust is a security framework that requires all users to be authenticated and authorized before accessing resources, minimizing the risk of unauthorized access.
How can organizations stay compliant with data privacy regulations?
Organizations can stay compliant by regularly reviewing and updating their data privacy policies, conducting audits, and ensuring employees are trained on compliance requirements.
What are the benefits of encryption?
Encryption protects data by converting it into a code that can only be deciphered with a specific key, ensuring that even if data is intercepted, it cannot be read or misused.
How can individuals protect their personal information online?
Individuals can protect their personal information online by using strong, unique passwords, enabling multi-factor authentication, and being cautious of phishing attempts.
Use Case: Automate your security audits and vulnerability assessments with AI-powered tools
Try Runable For Free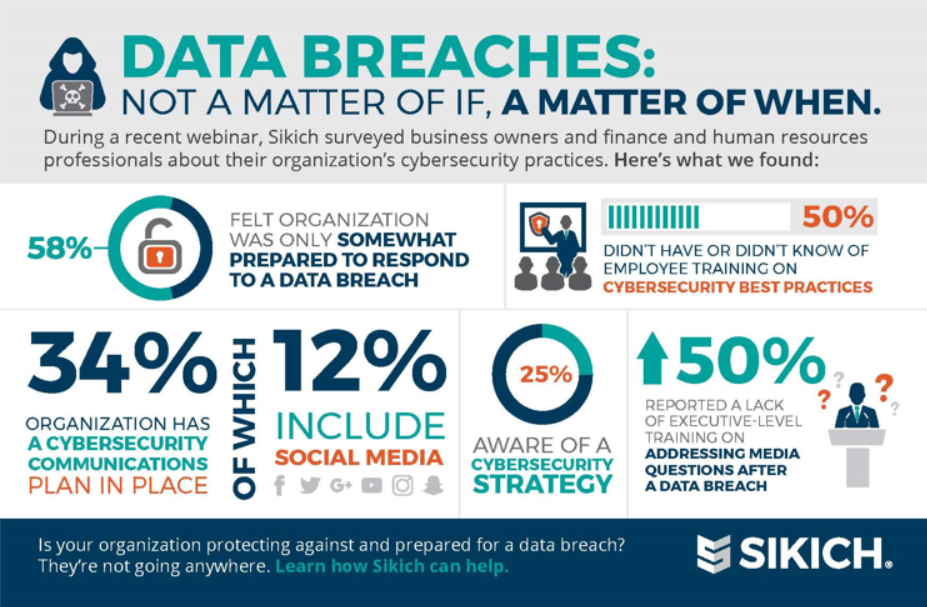
Key Takeaways
- Over 1 million Basic-Fit members' data exposed
- Critical need for robust data security measures
- AI and automation enhance threat detection
- Zero Trust architecture minimizes unauthorized access
- Regular updates and employee training are vital
- Quantum-resistant cryptography is the future
- Data privacy regulations are becoming stricter
- Backup strategies are essential for data recovery
Related Articles
- The Complex World of Data Breaches: Lessons from the Rockstar Games Leak [2025]
- Booking.com Data Breach: What Customers Need to Know [2025]
- Agility is the Key to Protecting Against Malware-as-a-Service [2025]
- Tech Support Scams and How to Combat Them [2025]
- Why Over 80% of Europeans Distrust US and Chinese Tech with Their Data [2025]
- Governing Generative AI Risks in the Enterprise [2025]
![Understanding the Basic-Fit Data Breach: A Comprehensive Guide to Data Security [2025]](https://tryrunable.com/blog/understanding-the-basic-fit-data-breach-a-comprehensive-guid/image-1-1776171863419.jpg)



