Booking.com Data Breach: What Customers Need to Know [2025]
Last week, a significant data breach at Booking.com sent ripples through the digital community. Customers are understandably concerned about their personal information's security. This article will delve into the details of the breach, the potential risks involved, and how you can protect yourself moving forward.
TL; DR
- Data Breach Details: Booking.com confirmed a breach impacting reservation details, including names, emails, and phone numbers.
- Potential Risks: Exposed data increases the risk of phishing and identity theft.
- Immediate Actions: Customers should update passwords and be vigilant about suspicious emails.
- Future Implications: Companies may need to enhance security protocols to prevent such breaches.
- Bottom Line: Staying informed and proactive is key to safeguarding your personal information.
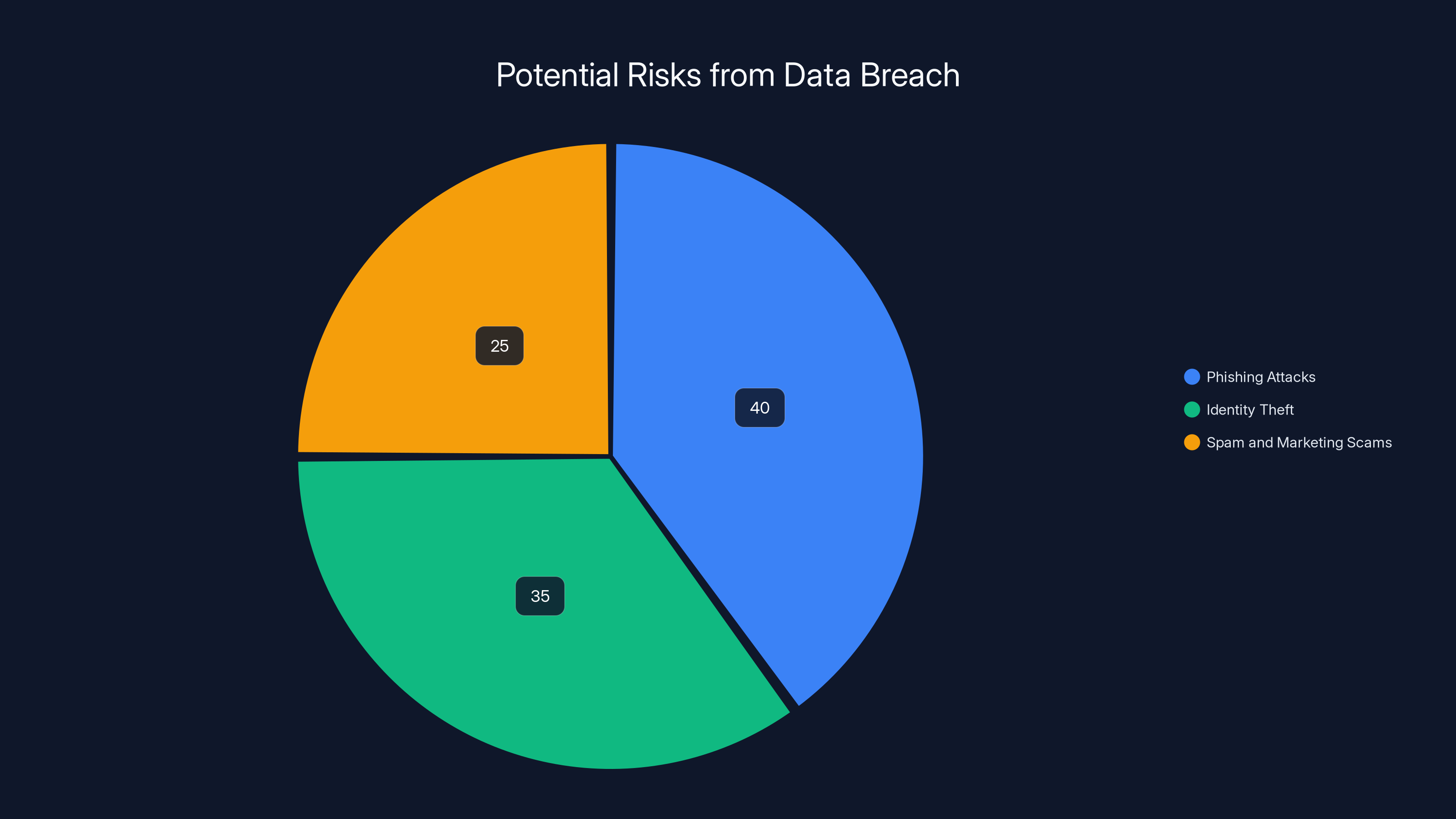
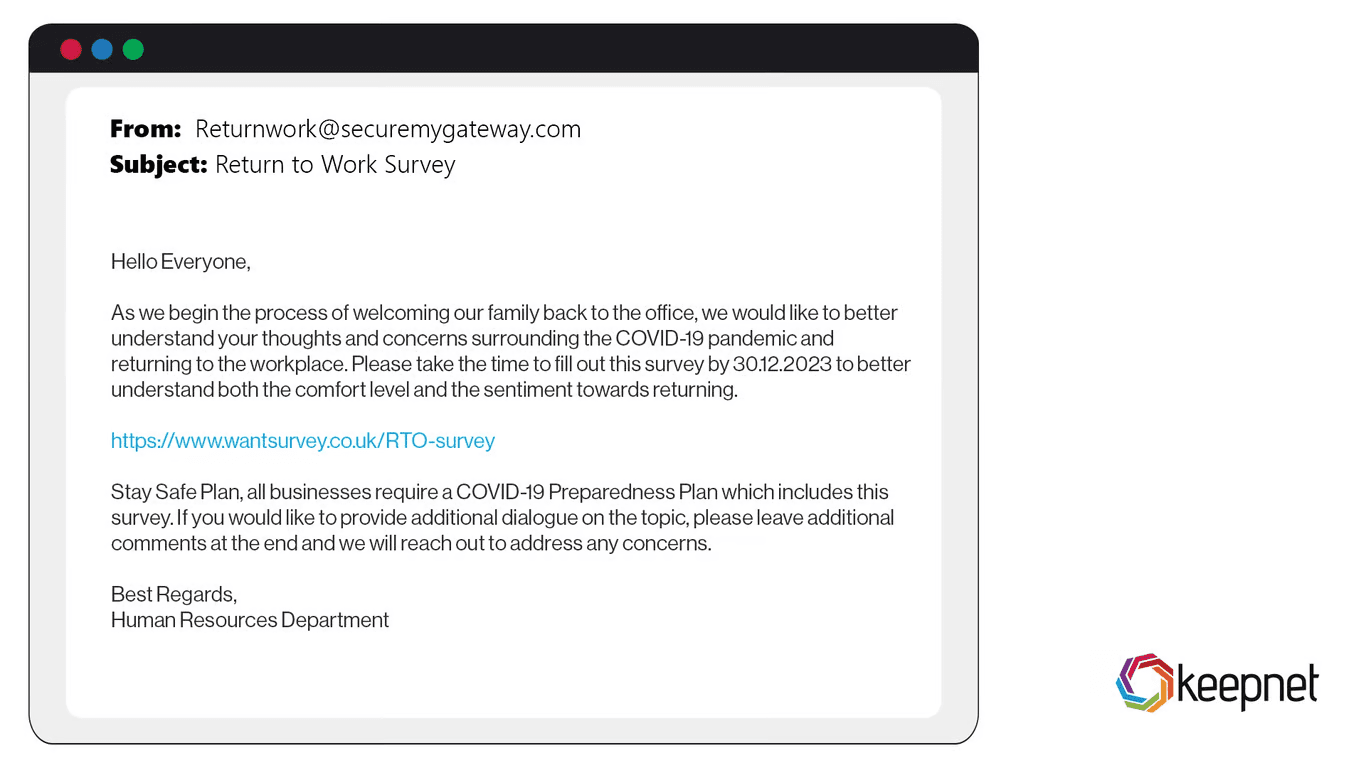
Estimated data shows phishing attacks as the most significant risk, followed by identity theft and spam. Estimated data.
The Breach: What Happened?
Booking.com recently confirmed that its reservation data was compromised by hackers, potentially exposing sensitive customer information. This breach affects a wide range of data, including names, email addresses, physical addresses, and phone numbers. While financial information appears to be secure, the access to personal data has resulted in increased phishing risks.
How the Breach Occurred
The specifics of how hackers infiltrated Booking.com's systems remain undisclosed. However, data breaches of this nature typically involve exploiting vulnerabilities within the company's IT infrastructure. This could include unpatched software, inadequately configured firewalls, or even insider threats.
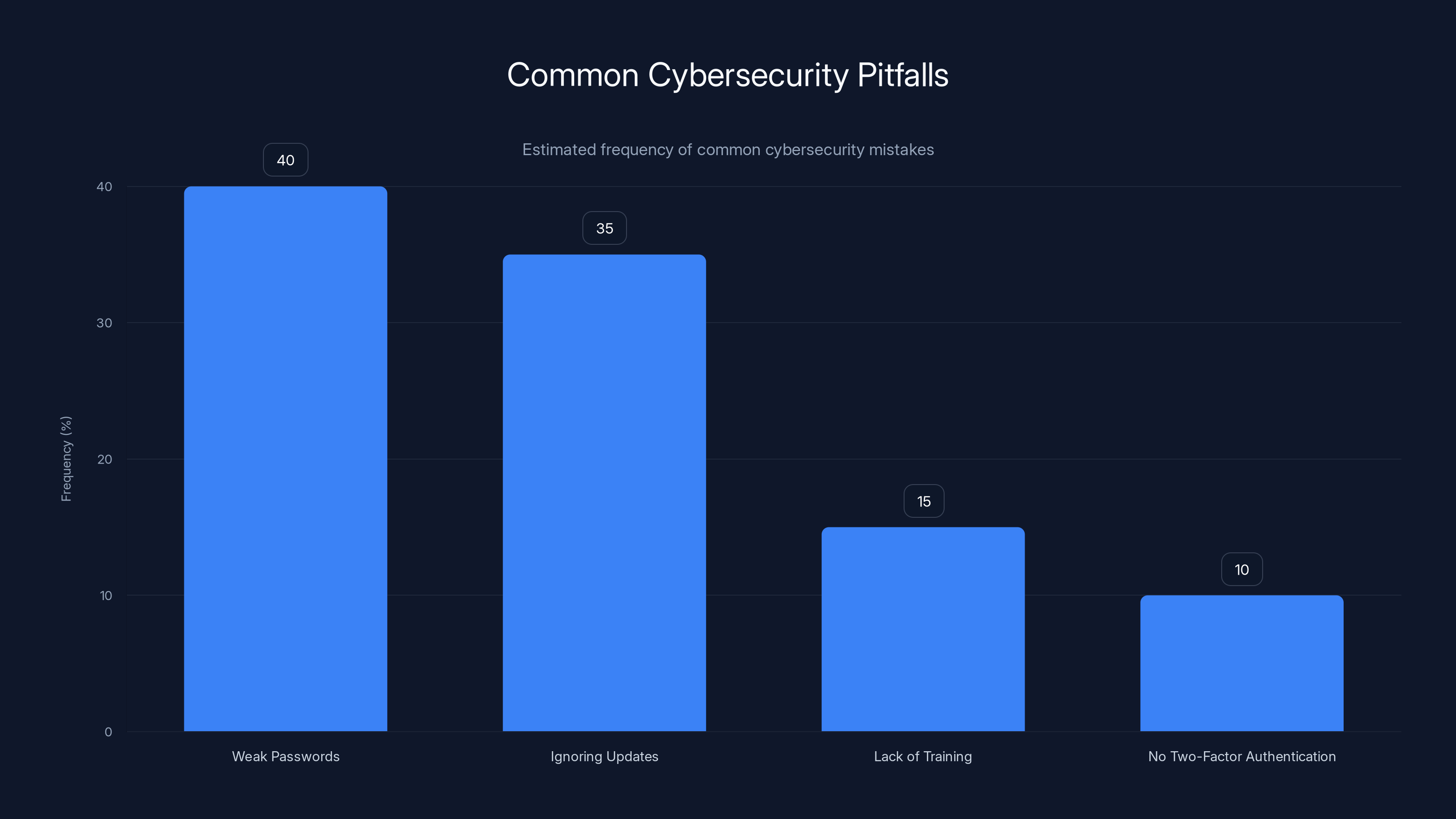
Weak passwords and ignoring software updates are the most common cybersecurity pitfalls, accounting for 75% of issues. (Estimated data)
Understanding the Impact
What Data Was Exposed?
The breach primarily affected reservation details, which encompass:
- Customer Names
- Email Addresses
- Phone Numbers
- Physical Addresses
While no payment information was reported stolen, the exposure of personal data can lead to increased risks of phishing and identity theft.
The Risks Involved
Exposing personal information in this manner can have several repercussions:
- Phishing Attacks: Hackers may use the exposed data to craft convincing phishing emails, tricking users into revealing sensitive information.
- Identity Theft: Personal information like names and addresses can be used to commit identity theft.
- Spam and Marketing Scams: Users might see an increase in unsolicited marketing emails and calls.

Protecting Your Information: Immediate Steps
If you're a Booking.com customer, there are several steps you can take to mitigate potential risks:
Update Your Passwords
Change your Booking.com password immediately. Ensure your new password is strong, using a mix of letters, numbers, and symbols. Avoid reusing passwords across multiple sites.
Enable Two-Factor Authentication
Two-factor authentication (2FA) adds an extra layer of security. It requires not only a password and username but also something that only the user has on them, i.e., a piece of information only they should know or have immediately to hand—such as a physical token.
Be Vigilant for Phishing Attempts
Keep an eye out for emails asking for personal information. Booking.com will not ask for sensitive data via email. If in doubt, contact the company directly through their official website.
Monitor Your Accounts
Regularly check your financial accounts for any unauthorized transactions. Report any suspicious activity to your bank immediately.
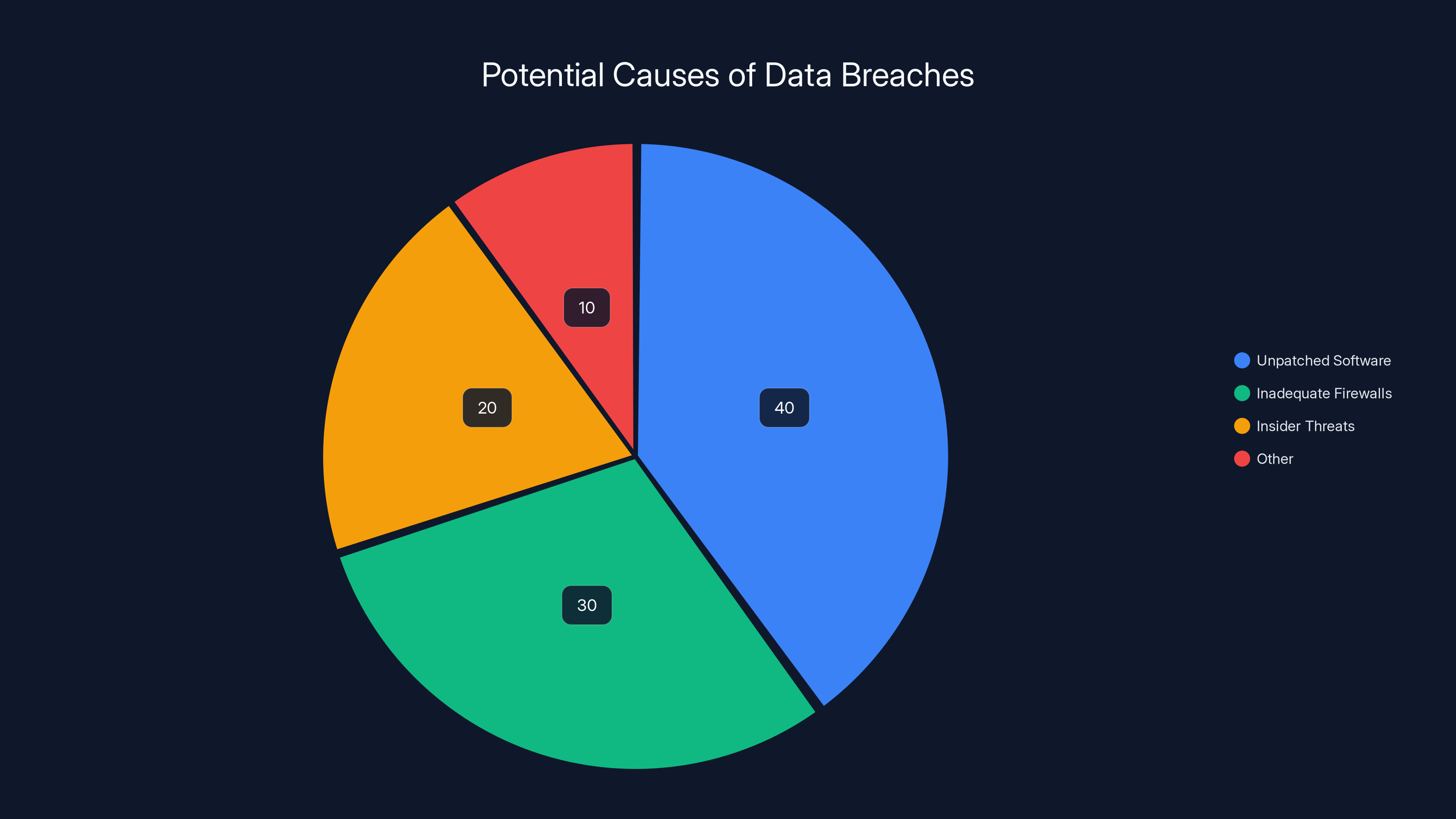
Estimated data suggests that unpatched software is the leading cause of data breaches, followed by inadequate firewalls and insider threats.
The Role of Companies in Data Protection
Enhancing Security Protocols
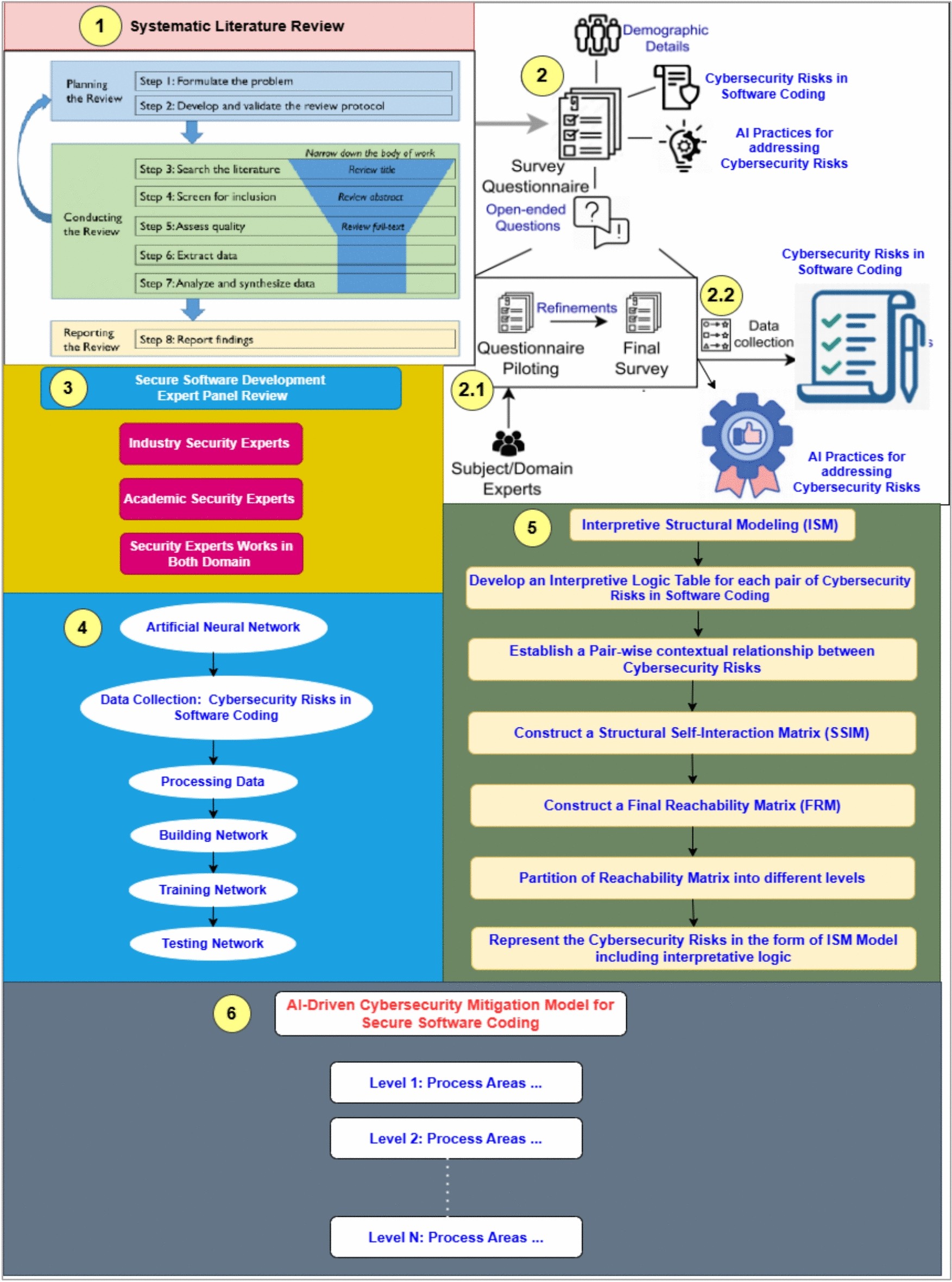
In light of this breach, companies must reassess their security protocols. This includes regular security audits, employee training on data protection, and implementing advanced security technologies like AI-driven threat detection.
Legal and Regulatory Implications
Data breaches often result in legal and regulatory scrutiny. Companies may face fines and be required to implement stricter data protection measures. This breach underscores the importance of compliance with regulations such as the General Data Protection Regulation (GDPR).

Common Pitfalls and Solutions
Pitfall 1: Weak Passwords
Many users still rely on weak passwords, making accounts vulnerable to breaches. Using simple or common passwords like "123456" or "password" are easy targets for attackers.
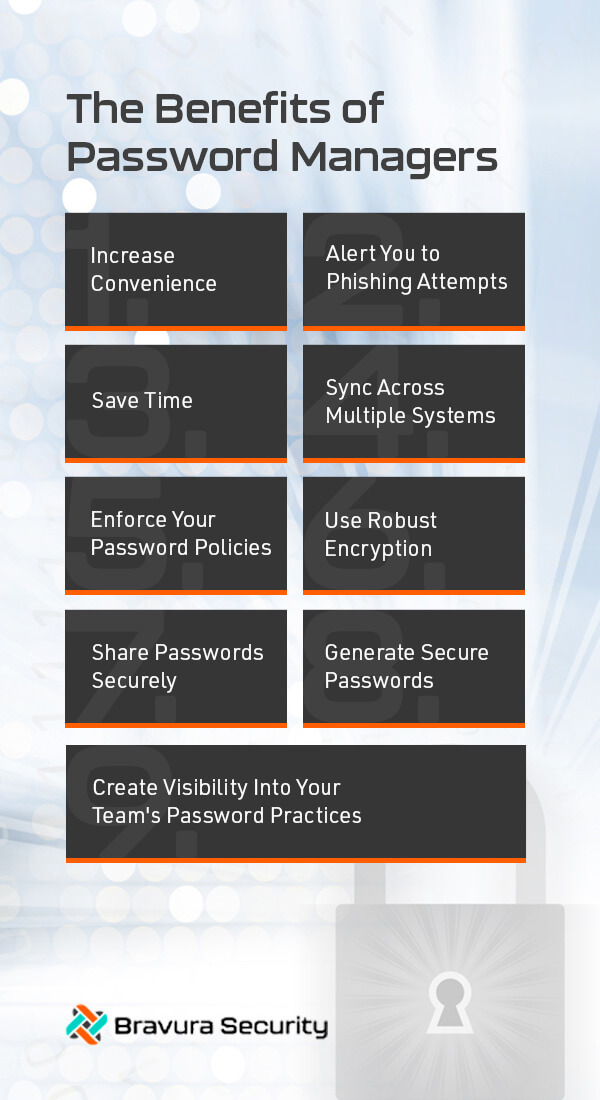
Solution: Use a Password Manager
A password manager can help create and store strong, unique passwords for each of your accounts. This reduces the likelihood of unauthorized access.
Pitfall 2: Ignoring Software Updates
Outdated software can contain vulnerabilities that hackers exploit. It's crucial to keep all systems and applications up to date with the latest patches.
Solution: Enable Automatic Updates
Most software can be set to update automatically, ensuring you always have the latest security patches.
Future Trends in Cybersecurity
Rise of AI in Cybersecurity
Artificial intelligence is increasingly being used to detect and prevent cyber threats. AI can analyze vast amounts of data in real-time, identifying suspicious activity that might go unnoticed by human analysts.
Importance of Zero Trust Architecture
Zero trust is a security framework requiring all users, whether inside or outside the organization, to be authenticated, authorized, and continuously validated for security configuration and posture before being granted access to applications and data.
Increased Focus on Data Encryption
Encrypting data both at rest and in transit is becoming a standard practice. This ensures that even if data is intercepted, it remains unreadable without the correct decryption key.
Recommendations for Companies
Regular Security Audits
Conducting regular security audits helps identify vulnerabilities before they can be exploited. This proactive approach can save companies from the reputational damage and financial losses associated with data breaches.
Employee Training
Employees are often the first line of defense against cyber threats. Regular training on recognizing phishing attempts and other common scams can significantly reduce the risk of a breach.
Investing in Advanced Security Solutions
Investing in advanced cybersecurity solutions, such as behavioral analytics and intrusion detection systems, can provide an additional layer of protection.
Conclusion
Data breaches like the one experienced by Booking.com highlight the importance of robust cybersecurity measures. While companies must enhance their security protocols, customers also have a role to play in protecting their personal information. By staying informed and taking proactive steps, you can minimize the risks and keep your data secure.
FAQ
What happened in the Booking.com data breach?
Booking.com experienced a data breach where hackers accessed reservation details, including customer names, emails, and phone numbers.
How can I protect my information after the breach?
Change your Booking.com password, enable two-factor authentication, and be vigilant for phishing attempts. Monitor your financial accounts for any suspicious activity.
What are the risks of exposed personal information?
Exposed information can lead to phishing attacks, identity theft, and an increase in unsolicited marketing emails and calls.
How can companies prevent data breaches?
Companies can prevent data breaches by conducting regular security audits, training employees, and investing in advanced cybersecurity technologies.
What is two-factor authentication?
Two-factor authentication is a security process in which users provide two different authentication factors to verify themselves. This adds an extra layer of security.
Why is data encryption important?
Data encryption ensures that even if data is intercepted, it remains unreadable without the correct decryption key, thus protecting sensitive information.
What is a zero trust architecture?
Zero trust is a security framework that requires all users to be authenticated and authorized before accessing applications and data, regardless of their location.
What are some common cybersecurity pitfalls?
Common pitfalls include using weak passwords and ignoring software updates, both of which can make systems vulnerable to attacks.
Key Takeaways
- Data breach at Booking.com exposed reservation details.
- Phishing and identity theft are increased risks.
- Customers should update passwords and enable 2FA.
- Companies need to enhance security protocols.
- AI and zero trust architecture are future trends.
Related Articles
- Rockstar Games and the Third-Party Data Breach: Understanding the Fallout [2025]
- The Complex World of Data Breaches: Lessons from the Rockstar Games Leak [2025]
- Understanding the Impact of Cybersecurity Breaches on Gaming Industry: A Deep Dive [2025]
- No, Elon Musk Doesn't Want to Give You a $5,000 Tax Refund — It's a Scam [2025]
- Agility is the Key to Protecting Against Malware-as-a-Service [2025]
- National Security at Risk: The Fallout of Over 3,500 US Legislators' Emails Exposed on the Dark Web [2025]
![Booking.com Data Breach: What Customers Need to Know [2025]](https://tryrunable.com/blog/booking-com-data-breach-what-customers-need-to-know-2025/image-1-1776166449803.jpg)



