Understanding the French Government Data Breach: Implications, Mitigation, and Future Steps [2025]
Introduction
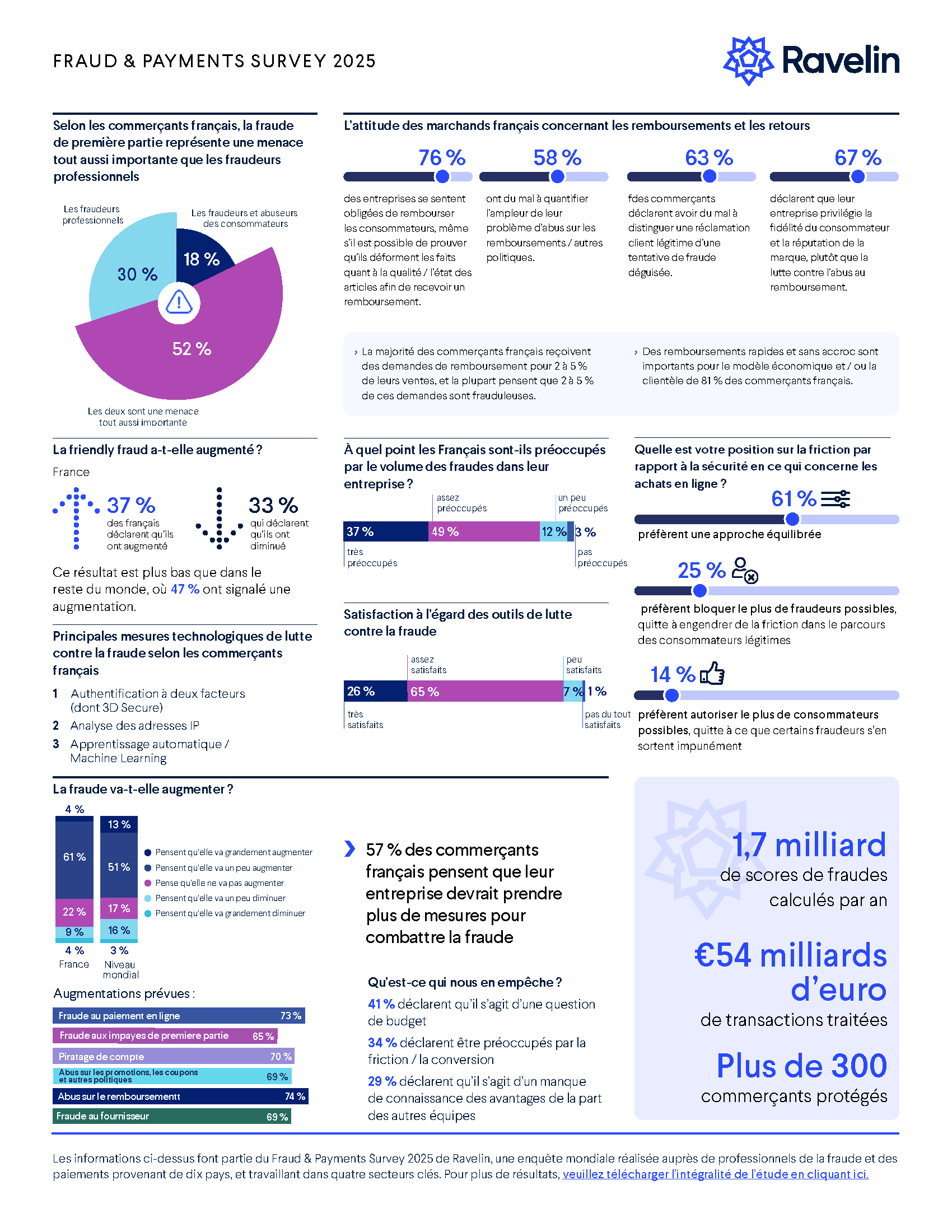
In a digital age where data is the new oil, the recent breach involving the French government agency ANTS (Agence Nationale des Titres Sécurisés) serves as a stark reminder of the vulnerabilities inherent in large-scale data management. A hacker's claim of accessing and selling up to 19 million sensitive records has sent ripples through the cybersecurity community and beyond. This incident underscores an urgent need for robust data protection strategies and highlights potential gaps in current systems, as detailed in TechRadar's report.

Outdated software poses the highest risk, followed by lack of encryption and inadequate access controls. Estimated data.
TL; DR
- 19 million records from the French government were allegedly stolen, raising security alarms, as reported by CyberNews.
- Sensitive data from both individual and professional accounts have been exposed.
- Immediate response includes beefing up security protocols and public alerts.
- Future strategies involve enhancing encryption standards and real-time monitoring.
- Data breaches can have far-reaching impacts on trust and operational integrity.

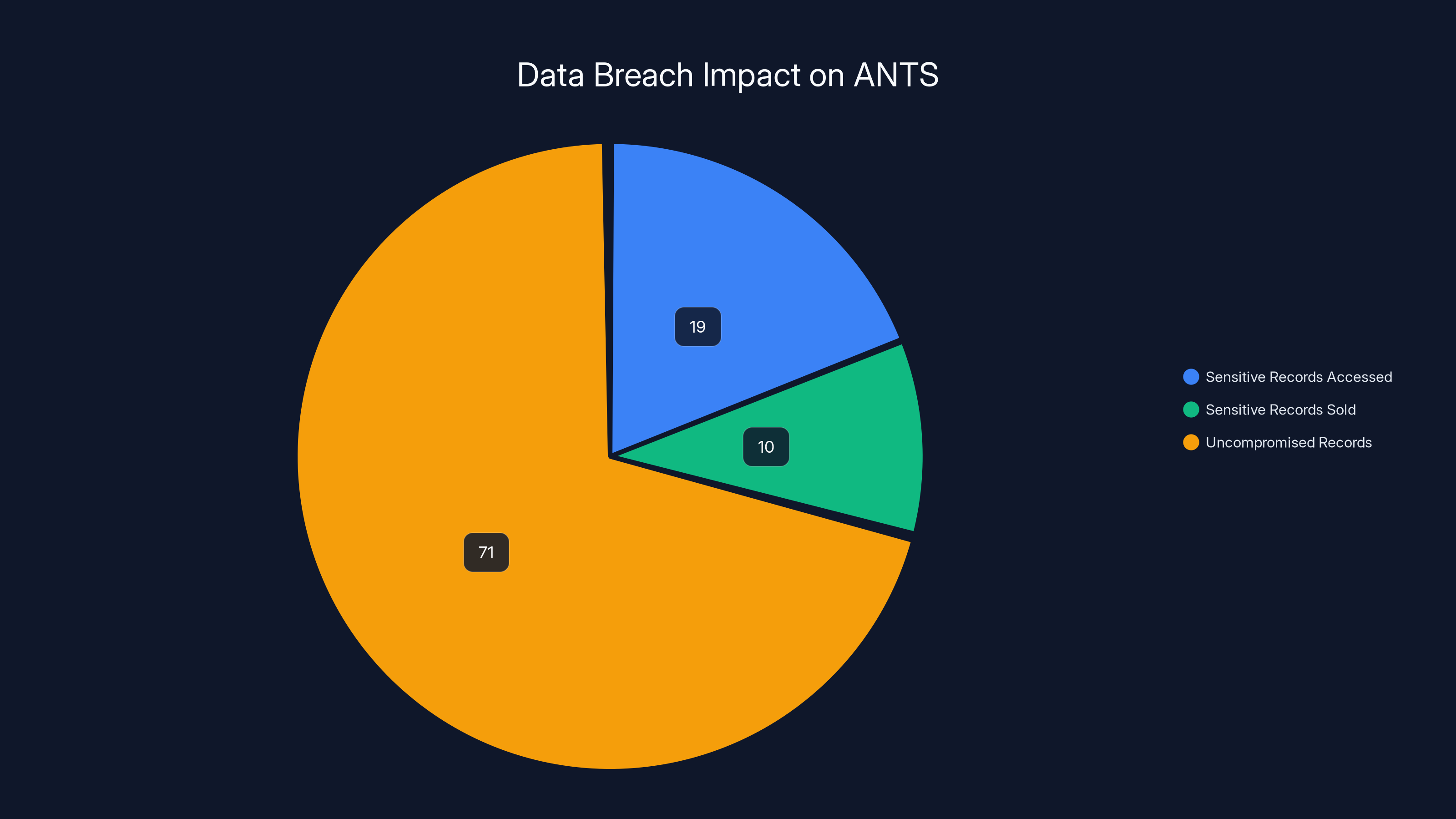
Estimated data shows that 19% of ANTS records were accessed, with 10% sold, highlighting significant security gaps. Estimated data.
The Breach Unveiled
What Happened?
The French government's ANTS was reportedly targeted by a cyberattack, resulting in the theft of up to 19 million records. These records, containing both individual and professional data, highlight the vulnerability of centralized data systems. The breach was disclosed following a hacker's claims of offering the data for sale on the dark web, as covered by The Record.
Potential Impact
The breach's impact goes beyond just the loss of data. It potentially affects national security, individual privacy, and the operational integrity of governmental functions. The scale of compromise suggests that both personal and professional data could be exploited for fraudulent activities, as noted in The Whistler.
Immediate Response
In response, French authorities have initiated a comprehensive investigation, focusing on identifying the breach's scope and securing the compromised systems. Public advisories have been issued to warn individuals and organizations about potential phishing attacks leveraging the stolen data, as reported by CyberNews.
Technical Breakdown
How Did It Happen?
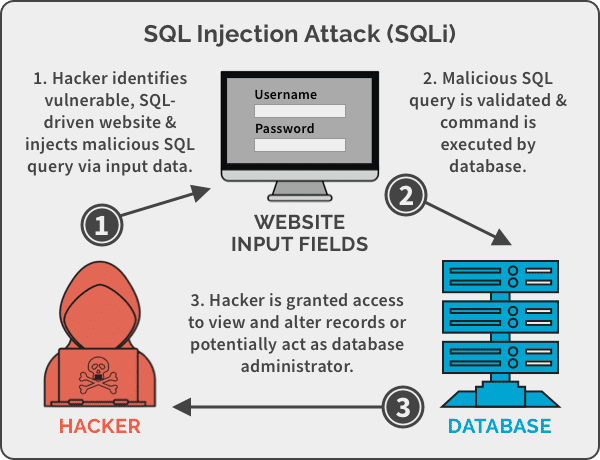
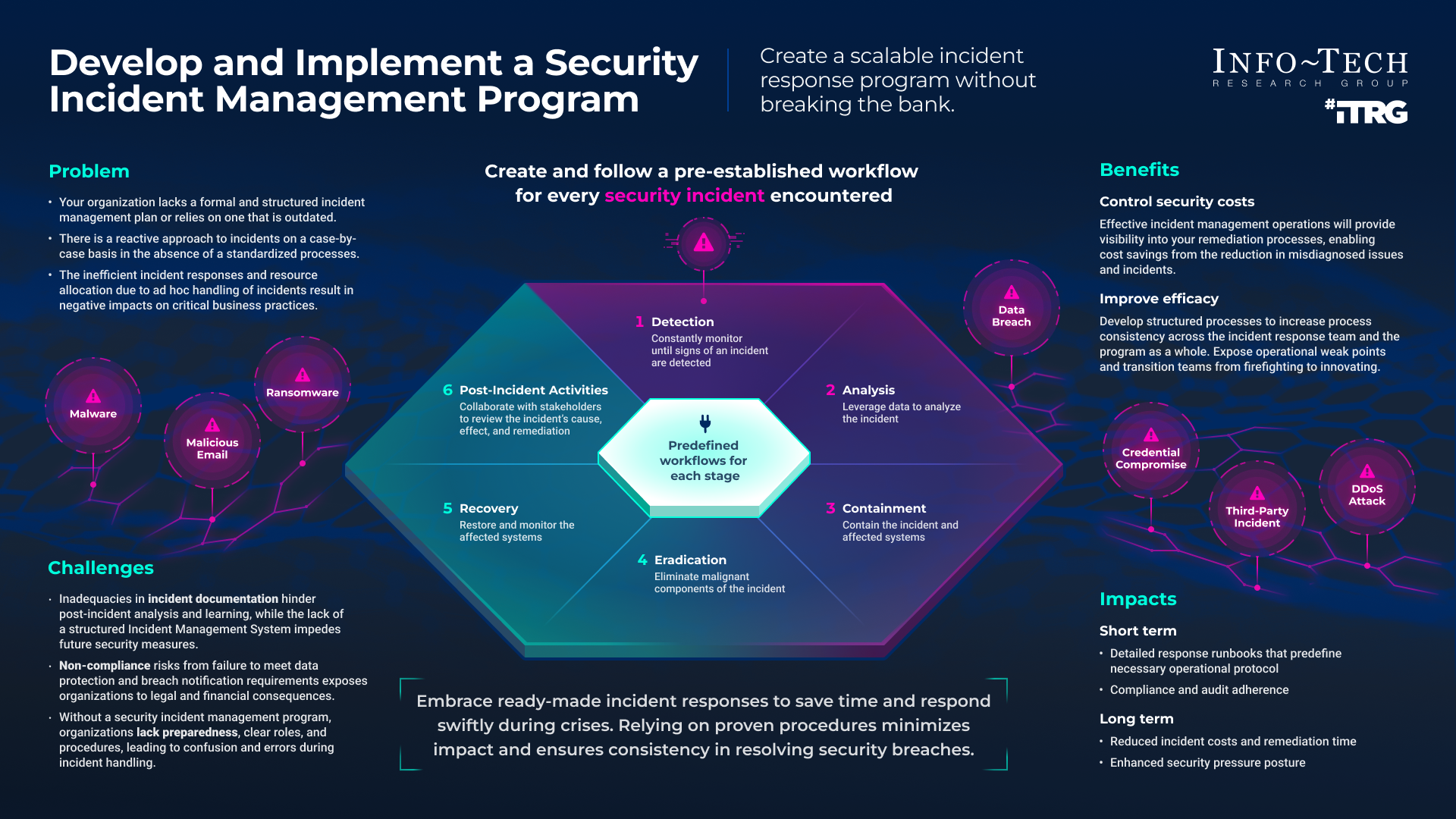
The breach likely involved sophisticated techniques such as SQL injection, phishing, or exploiting zero-day vulnerabilities. These methods target weak points in a system's architecture to gain unauthorized access, as explained by SecurityWeek.
Example:
SQL injection can occur when user inputs are not properly sanitized, allowing attackers to manipulate database queries and access or modify data.
Common Pitfalls in Data Security
- Lack of Encryption: Data not properly encrypted at rest and in transit can be easily intercepted.
- Inadequate Access Controls: Insufficient user authentication and authorization mechanisms can lead to unauthorized data access.
- Outdated Software: Using outdated or unpatched software increases vulnerability to attacks, as highlighted by Industrial Cyber.
Best Practices for Protection
- Implement Strong Encryption: Use advanced encryption standards (AES-256) to secure data both at rest and in transit.
- Regular System Updates: Ensure all systems and software are regularly updated to patch known vulnerabilities.
- Access Control Management: Employ multi-factor authentication and least privilege access principles.
- Real-Time Monitoring: Deploy security information and event management (SIEM) systems to detect and respond to threats in real-time, as recommended by ReversingLabs.
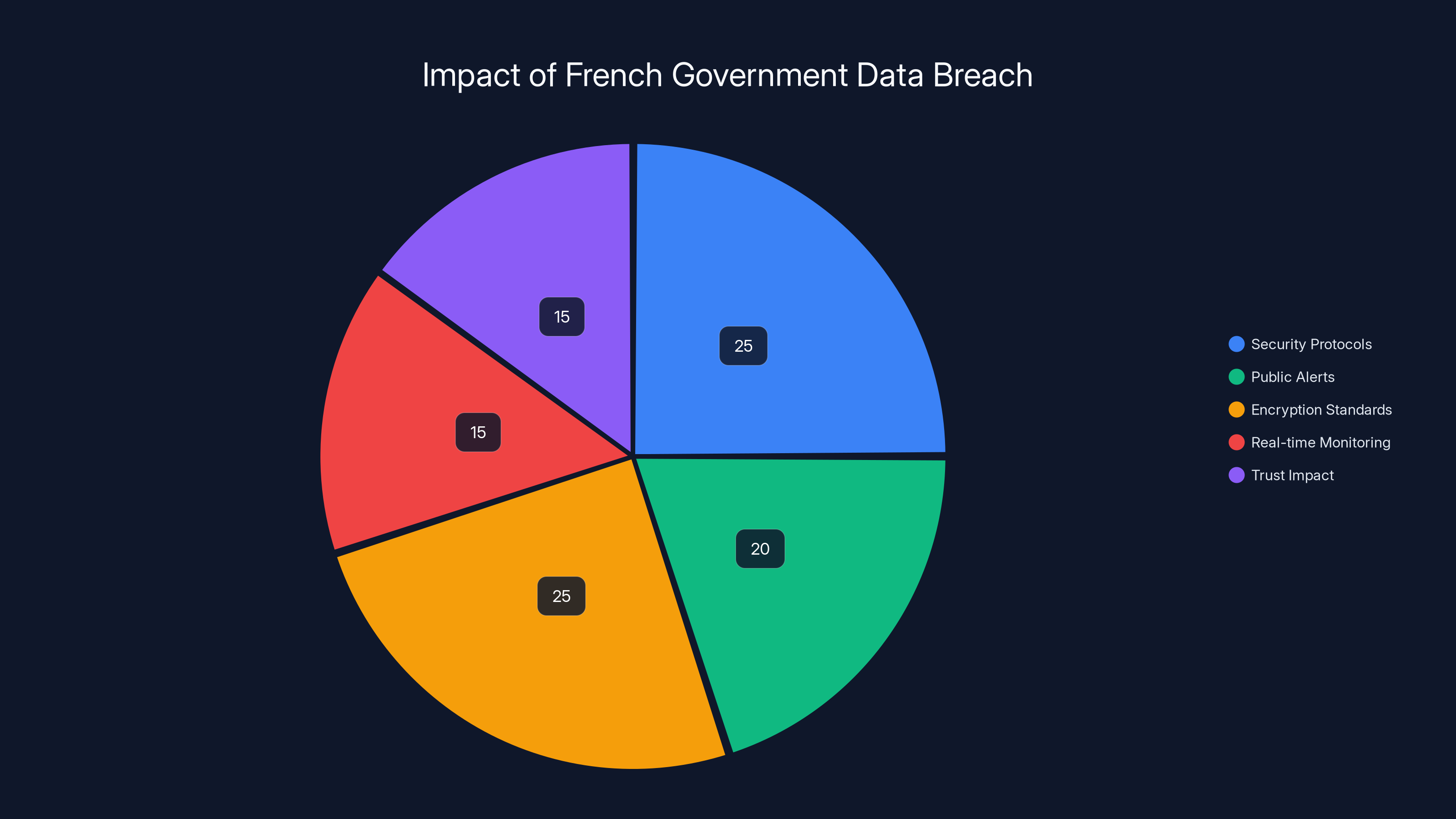
Estimated data shows a balanced focus on security protocols and encryption standards as key responses to the breach, alongside public alerts and trust impact considerations.
Future Trends and Recommendations
Enhancing Cybersecurity Resilience
The future of cybersecurity in government agencies lies in adopting a proactive rather than reactive stance. This includes integrating artificial intelligence and machine learning to predict and mitigate potential threats, as discussed by Industrial Cyber.
Example:
AI-driven systems can analyze network traffic patterns to detect anomalies that might indicate a breach attempt, allowing for preemptive action.
The Role of Cybersecurity Frameworks
Adopting comprehensive frameworks such as NIST or ISO 27001 can provide a structured approach to managing and mitigating cybersecurity risks, as noted by The Quantum Insider.
Educating the Workforce
Human error remains a significant vulnerability in cybersecurity. Regular training and awareness programs can equip employees with the necessary skills to recognize and respond to potential threats, as emphasized by Fortune.

Case Study: The Aftermath of a Breach
Following a data breach, a multinational corporation implemented a rigorous cybersecurity overhaul. This included enhanced data encryption, updated access controls, and an employee training program, resulting in a significant reduction in security incidents, as reported by Fintech Weekly.
Conclusion
The French government data breach serves as a reminder of the ever-present risks in our digital world. By learning from this incident and implementing robust security measures, organizations can better protect sensitive data and maintain public trust, as highlighted by Palo Alto Networks' Unit 42.
FAQ
What is a data breach?
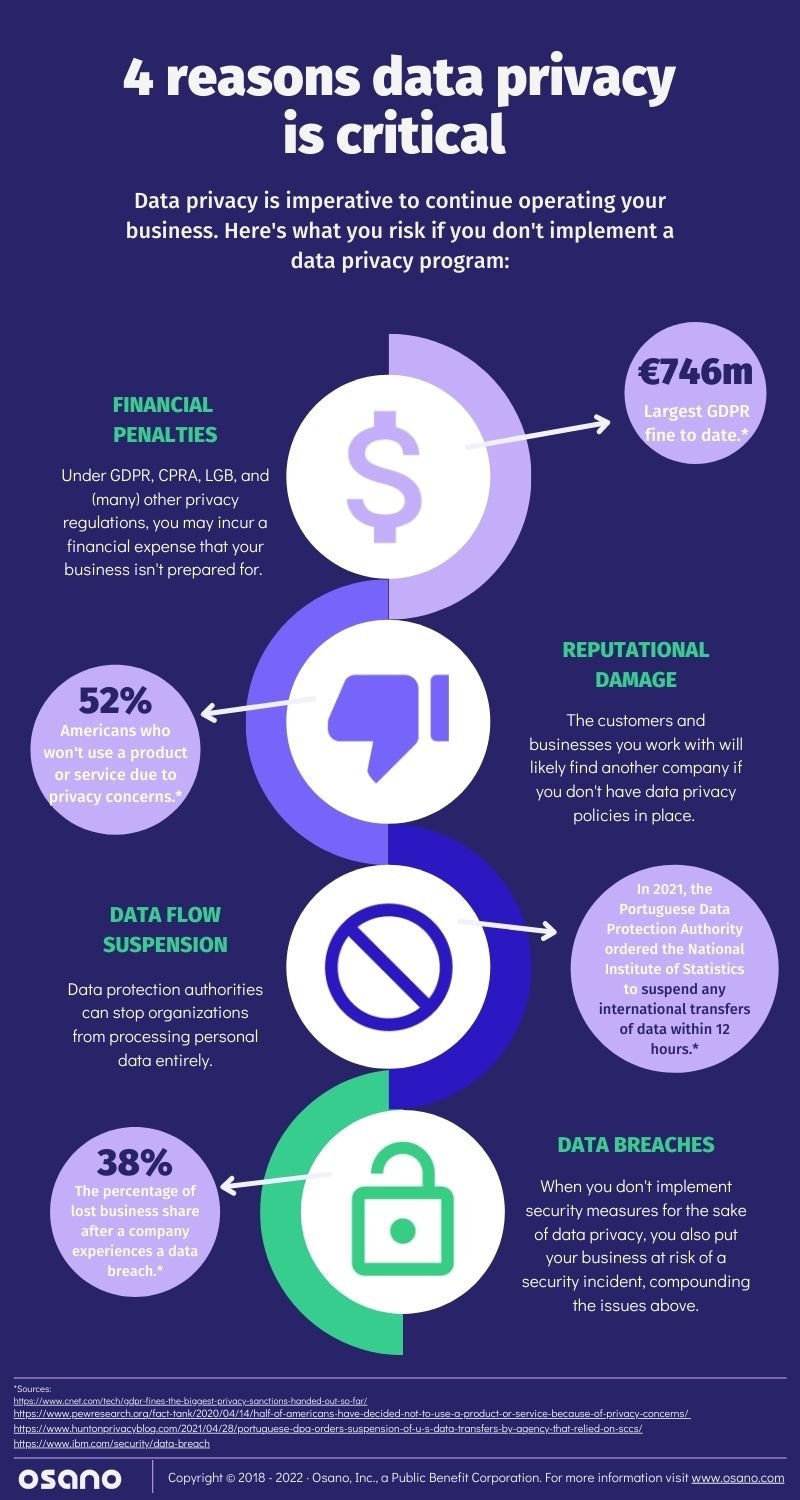
A data breach occurs when unauthorized individuals access sensitive information, potentially leading to identity theft, fraud, and other malicious activities.
How can data breaches be prevented?
Preventive measures include strong encryption, regular software updates, access controls, and employee training to recognize phishing and other threats.
What are the consequences of a data breach?
Consequences can include financial loss, reputational damage, legal penalties, and compromised personal and professional data.
How does encryption protect data?
Encryption transforms data into a coded format, making it unintelligible to unauthorized users and protecting it during storage and transmission.
What steps should be taken after a data breach?
Immediate steps include assessing the breach's scope, notifying affected parties, securing systems, and implementing measures to prevent future incidents.
Why is employee training important in cybersecurity?
Employees are often the first line of defense. Training them to recognize and respond to threats reduces the risk of human error leading to breaches.
Key Takeaways
- 19 million records allegedly stolen in French government breach
- Enhanced encryption standards are critical for data protection
- Human error remains a significant cybersecurity vulnerability
- AI and machine learning can predict and mitigate threats
- Comprehensive cybersecurity frameworks enhance resilience
- Proactive cybersecurity measures are essential for future protection
Related Articles
- Why AES 128 Remains Secure in a Post-Quantum World [2025]
- Understanding Cybersecurity Breaches: Lessons from the Seiko USA Incident [2025]
- Inside the $290M Kelp DAO Heist: North Korea's Lazarus Group Strikes Again [2025]
- Anthropic's Mythos Under Investigation for Unauthorized Access [2025]
- AI Agents: The Hidden Gatekeepers Giving Hackers Full System Access [2025]
- YouTube's AI Likeness Detection Technology: Expanding Safeguards for Celebrities in 2025
![Understanding the French Government Data Breach: Implications, Mitigation, and Future Steps [2025]](https://tryrunable.com/blog/understanding-the-french-government-data-breach-implications/image-1-1776857759745.jpg)



