Understanding Cybersecurity Breaches: Lessons from the Seiko USA Incident [2025]
Cybersecurity breaches have become a regular headline, underscoring the frailty of digital defenses in the face of sophisticated cyber threats. The recent incident involving the defacement and alleged data theft at Seiko USA is a stark reminder of the vulnerabilities that businesses face. While Seiko has yet to confirm the breach, the claims made by hackers highlight critical areas of concern for businesses relying on digital platforms.
TL; DR
- Data Breach Severity: Hackers claim to have accessed Seiko's entire customer database, with potential ramifications for customer privacy.
- Security Gaps Identified: Exploitation of vulnerabilities in Shopify's backend poses questions about third-party platform security.
- Ransom Demands: Hackers have demanded a ransom, pressuring businesses to reassess their response strategies.
- Proactive Measures: Enhancing cybersecurity protocols can mitigate risks of similar incidents.
- Future Outlook: As cyber threats evolve, continuous adaptation in security practices is crucial.


Phishing simulations and incident response training are highly effective in enhancing cybersecurity awareness among employees. (Estimated data)
The Anatomy of a Cybersecurity Breach
Understanding a cybersecurity breach involves dissecting the methods attackers use to penetrate systems. In the Seiko USA case, hackers claimed to exploit vulnerabilities in Shopify's backend. This highlights a common entry point for cybercriminals: third-party platforms.
Third-Party Platform Vulnerabilities
Third-party platforms provide essential services but can also introduce risks. Companies often integrate these platforms for e-commerce, customer relationship management, and more. However, each integration can serve as a potential vulnerability if not properly secured.
Common Vulnerabilities
- Outdated Software: Many platforms fail to update their software regularly, leaving security gaps.
- Weak Authentication: Insufficient authentication protocols make unauthorized access easier.
- Inadequate Monitoring: Without real-time monitoring, breaches can go undetected until it's too late.
To protect against these vulnerabilities, businesses should conduct regular audits and ensure all third-party integrations adhere to strict security standards.

Implementing Multi-Factor Authentication is estimated to reduce breach incidents by 70%, making it the most effective measure among those listed. Estimated data.
Best Practices in Cybersecurity
To prevent incidents like the Seiko USA breach, businesses should adopt comprehensive cybersecurity measures. Here's a guide to fortifying your digital defenses.
Implement Multi-Factor Authentication (MFA)
What It Is: Requiring multiple forms of verification before granting access.
Why It Matters: MFA significantly reduces the risk of unauthorized access by adding layers of security.
How to Implement:
- Step 1: Choose an MFA provider that supports your tech stack.
- Step 2: Configure MFA settings to include a combination of passwords, biometrics, and OTPs (one-time passwords).
- Step 3: Train employees on the importance and usage of MFA.
Regular Security Audits
Conducting frequent security audits helps identify and rectify vulnerabilities before they can be exploited.
Audit Checklist:
- Review access controls and permissions.
- Verify the security of third-party integrations.
- Test for vulnerabilities using penetration testing.
By proactively identifying weaknesses, organizations can address them before they become entry points for attackers.
Data Encryption
What It Is: Converting data into a code to prevent unauthorized access.
Why It Matters: Encrypting sensitive information ensures that even if data is intercepted, it remains unreadable without the decryption key.
How to Implement:
- Use industry-standard encryption algorithms.
- Regularly update encryption protocols.
- Educate employees on the importance of encryption.
The Role of Employee Training
Employees are often the first line of defense against cyber threats. Training them to recognize and respond to suspicious activities can prevent breaches.
Training Program Essentials:
- Phishing Simulation: Conduct regular phishing exercises to educate employees on recognizing fraudulent emails.
- Cyber Hygiene: Teach best practices, such as password management and secure browsing habits.
- Incident Response: Ensure employees know the protocol for reporting potential security breaches.

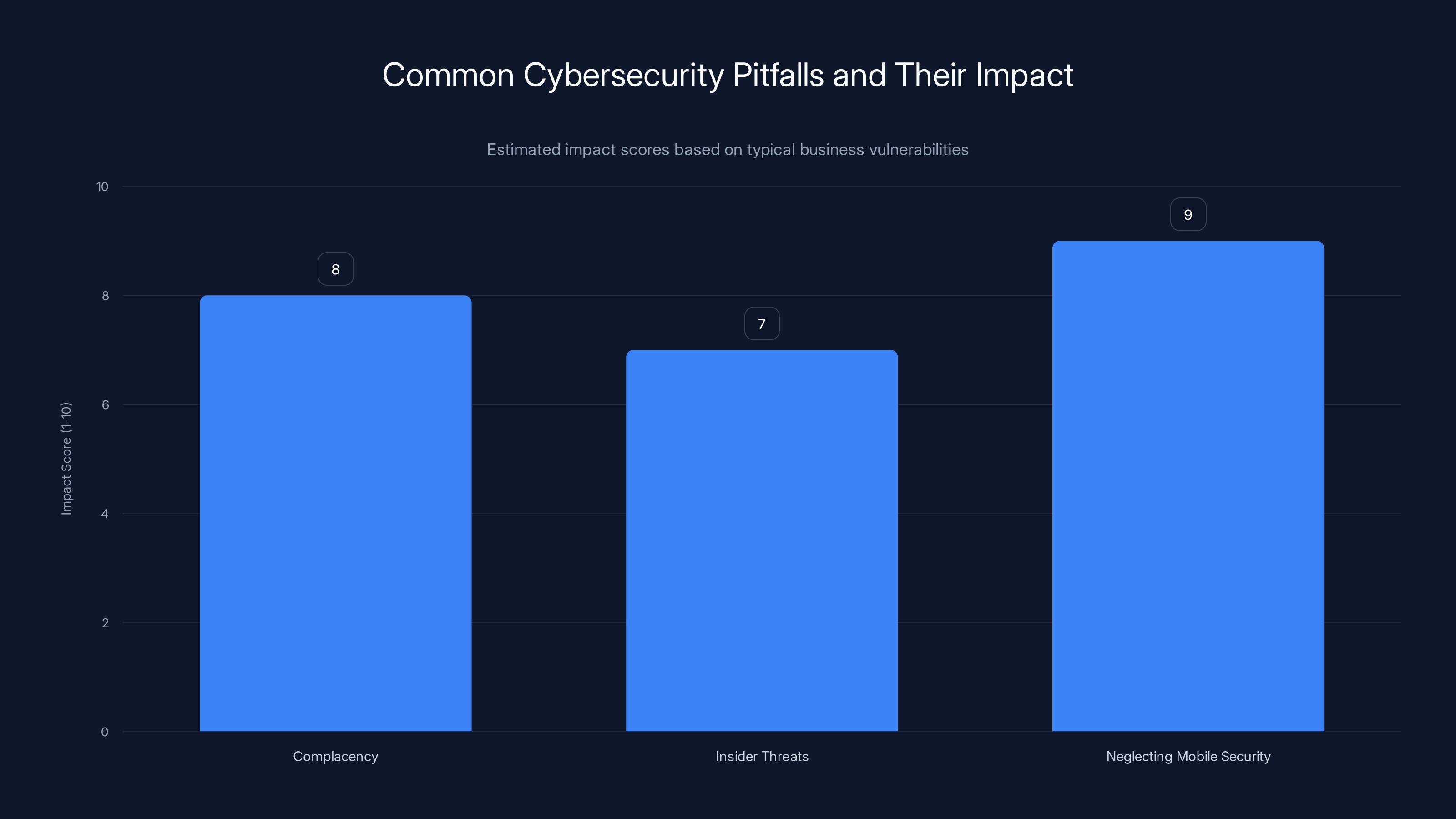
Complacency, insider threats, and neglecting mobile security are major pitfalls with high impact scores. Estimated data.
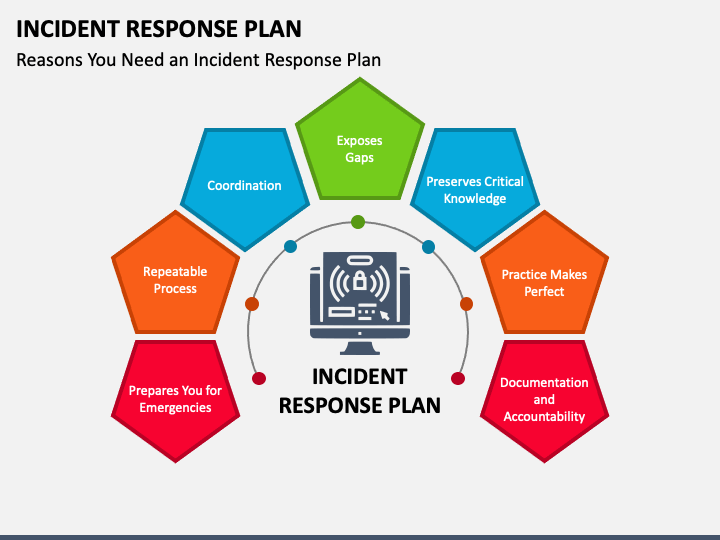
Incident Response Strategies
An effective incident response plan is crucial in mitigating damage during a cybersecurity breach. Here's a step-by-step guide to developing a robust response strategy.
Step 1: Preparation
- Define Roles: Assign specific roles and responsibilities to team members.
- Establish Communication Protocols: Ensure clear lines of communication within the organization and with external partners.
Step 2: Detection and Analysis
- Deploy Monitoring Tools: Use tools to detect unusual activity or unauthorized access attempts.
- Conduct Forensic Analysis: Investigate to determine the nature and extent of the breach.
Step 3: Containment, Eradication, and Recovery
- Isolate Affected Systems: Prevent the spread of malware or unauthorized access.
- Eradicate Threats: Remove malware and close vulnerabilities.
- Restore Systems: Recover data and restore systems to normal operation.
Step 4: Post-Incident Review
- Analyze Response Effectiveness: Review the incident response to identify areas for improvement.
- Update Security Policies: Adjust policies and procedures based on lessons learned.
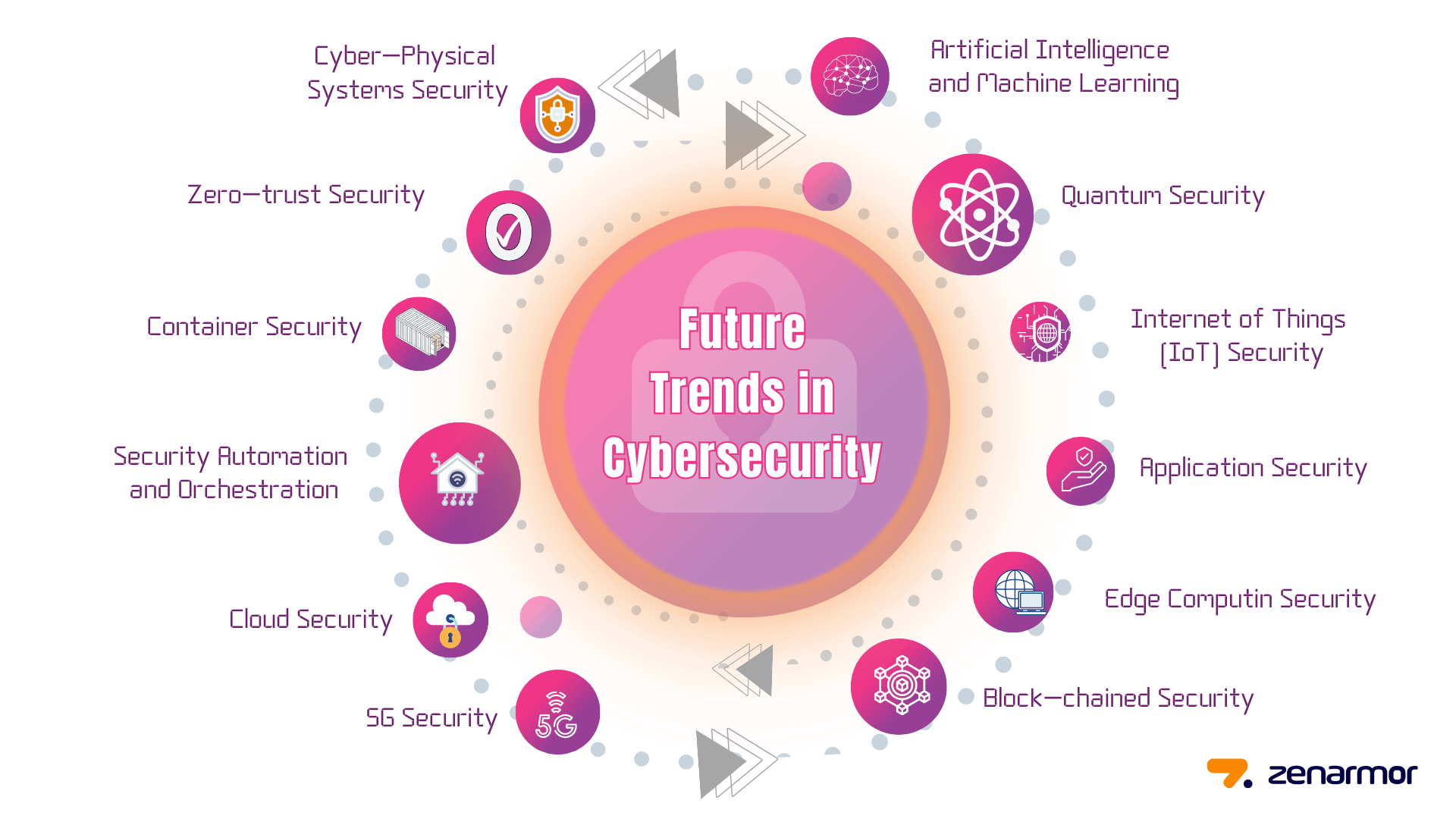
Future Trends in Cybersecurity
As technology advances, so do the methods employed by cybercriminals. Staying ahead requires anticipating future trends in cybersecurity.
Trend 1: AI-Driven Security
AI and machine learning are becoming integral to cybersecurity, providing advanced threat detection and response capabilities.
- Predictive Analysis: AI can predict potential threats by analyzing patterns and anomalies.
- Automated Response: AI-driven systems can respond to threats faster than human analysts.
Trend 2: Zero Trust Architecture
Zero Trust is a security framework that requires strict identity verification for every individual and device accessing the network.
- Continuous Monitoring: Regularly verify the identity and integrity of devices and users.
- Micro-Segmentation: Divide networks into smaller zones to contain breaches.
Common Pitfalls and Solutions
Despite the best intentions, businesses often fall into common cybersecurity pitfalls. Here’s how to avoid them.
Pitfall 1: Complacency
Assuming that current security measures are sufficient can lead to vulnerabilities.
Solution: Regularly update and review security protocols to adapt to new threats.
Pitfall 2: Overlooking Insider Threats
Insider threats can be as damaging as external attacks.
Solution: Implement monitoring systems to detect unusual behavior from employees.
Pitfall 3: Neglecting Mobile Security
With the increase in remote work, mobile devices have become a common target for attackers.
Solution: Secure mobile endpoints with encryption, MFA, and mobile device management (MDM) solutions.
Conclusion
The Seiko USA incident serves as a wake-up call for businesses to strengthen their cybersecurity defenses. By understanding the methods attackers use and implementing robust security protocols, companies can protect their data and maintain customer trust. As cyber threats continue to evolve, staying informed and proactive is key to safeguarding against potential breaches.

FAQ
What is a cybersecurity breach?
A cybersecurity breach is an unauthorized intrusion into a computer system or network, resulting in data theft, data loss, or disruption of services.
How does a cybersecurity breach occur?
Breaches occur through various methods, including malware, phishing attacks, exploitation of software vulnerabilities, and insider threats.
What are the benefits of a robust cybersecurity strategy?
Benefits include reduced risk of data breaches, improved customer trust, compliance with regulations, and protection of sensitive information, as supported by Harvard Business Review.
How can businesses protect against data breaches?
Implementing strong security measures such as multi-factor authentication, regular security audits, employee training, and incident response plans can mitigate the risk of data breaches.
What role does AI play in cybersecurity?
AI enhances cybersecurity by providing advanced threat detection through predictive analysis and enabling faster automated responses to threats, as noted by AI Multiple.
What is Zero Trust Architecture?
Zero Trust Architecture is a security framework that requires strict verification for every user and device accessing the network, reducing the risk of unauthorized access.
How often should security audits be conducted?
Security audits should be conducted regularly, ideally quarterly, to ensure that security measures are up-to-date and effective against current threats.
What are insider threats?
Insider threats involve individuals within the organization, such as employees or contractors, who intentionally or unintentionally compromise security.
Key Takeaways
- Hackers claim to have accessed Seiko's customer database, highlighting potential data privacy risks.
- Exploitation of Shopify's backend suggests vulnerabilities in third-party platforms.
- Ransom demands emphasize the need for robust incident response strategies.
- Implementing multi-factor authentication and regular security audits can mitigate breach risks.
- AI-driven security and Zero Trust Architecture are emerging trends in cybersecurity.
Related Articles
- Understanding and Mitigating Microsoft Teams Helpdesk Impersonation Attacks [2025]
- Inside the $290M Kelp DAO Heist: North Korea's Lazarus Group Strikes Again [2025]
- WordPress Vulnerability: How Hackers Exploit Simple Plugin Flaws [2025]
- Why AES 128 Remains Secure in a Post-Quantum World [2025]
- They Built a Legendary Privacy Tool. Now They’re Sworn Enemies | WIRED
- Spotting the Spyware: How Modern Spies Are Weaponizing Phishing [2025]
![Understanding Cybersecurity Breaches: Lessons from the Seiko USA Incident [2025]](https://tryrunable.com/blog/understanding-cybersecurity-breaches-lessons-from-the-seiko-/image-1-1776796836140.jpg)



