How Cell Phones Lead to Self-Incrimination: A Deep Dive [2025]
Cell phones have become an integral part of our daily lives. From scheduling meetings to capturing memories, these devices are indispensable. However, their pervasive use also leads to unintentional self-incrimination, as they silently record our activities, communications, and locations.
TL; DR
- Digital Footprints: Every action on a phone leaves a trail that can be traced back to the user.
- Location Tracking: Cell tower pings and GPS data can pinpoint your whereabouts accurately.
- Data Recovery: Deleted messages are often recoverable, posing privacy risks.
- Legal Implications: Digital data is increasingly used as evidence in courts.
- Protective Measures: Encrypt sensitive data and regularly clear your digital history.

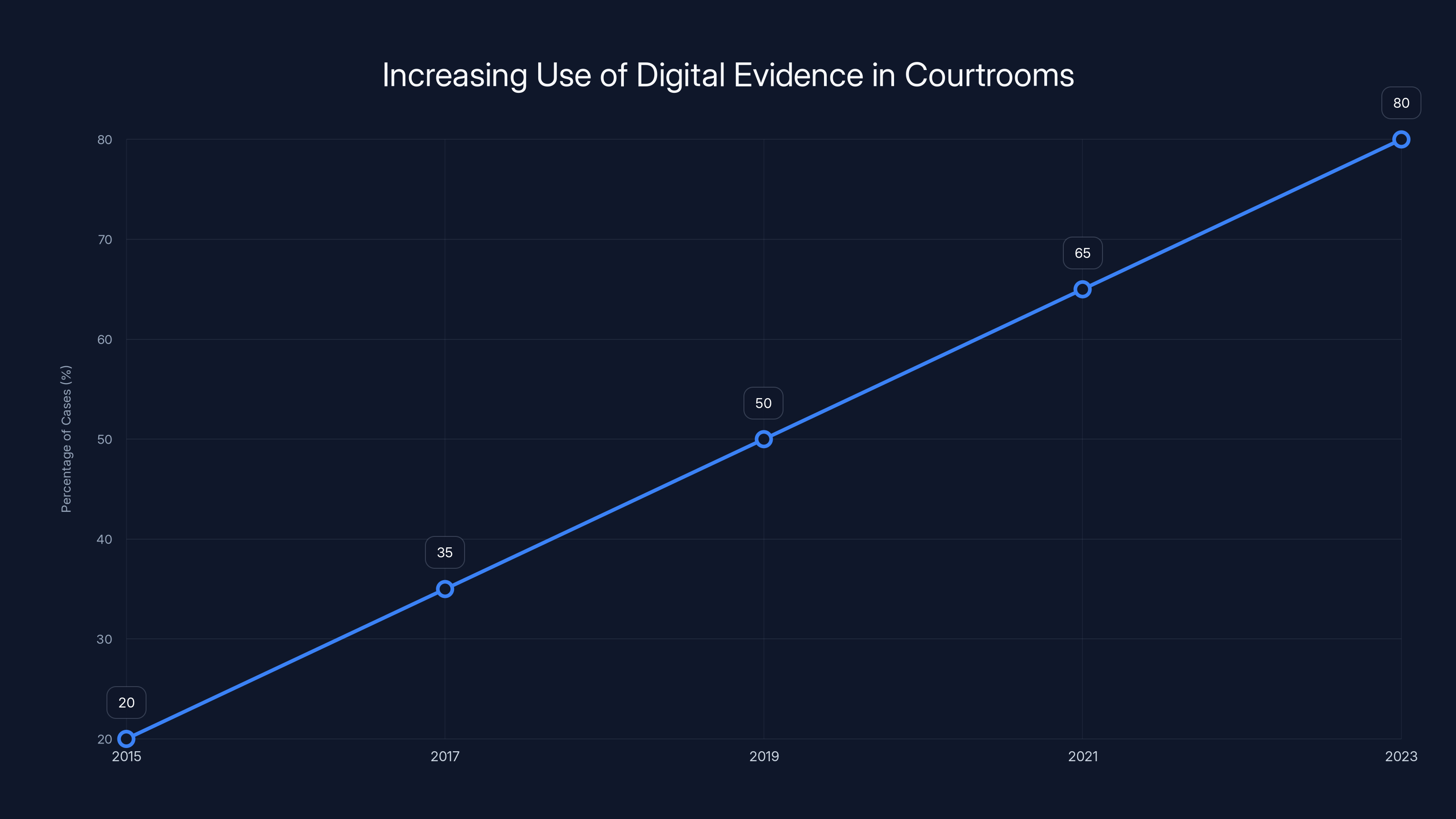
The use of digital evidence from cell phones in courtrooms has seen a significant increase, with an estimated 80% of cases incorporating such evidence by 2023. Estimated data.
Introduction
Last month, a high-profile case involving a Utah real estate agent highlighted how cell phone data can play a pivotal role in legal proceedings. The agent's search history and text messages were instrumental in securing a conviction for a serious crime. This case underscores a growing trend: our cell phones know more about us than we realize, and they can betray us in a court of law.
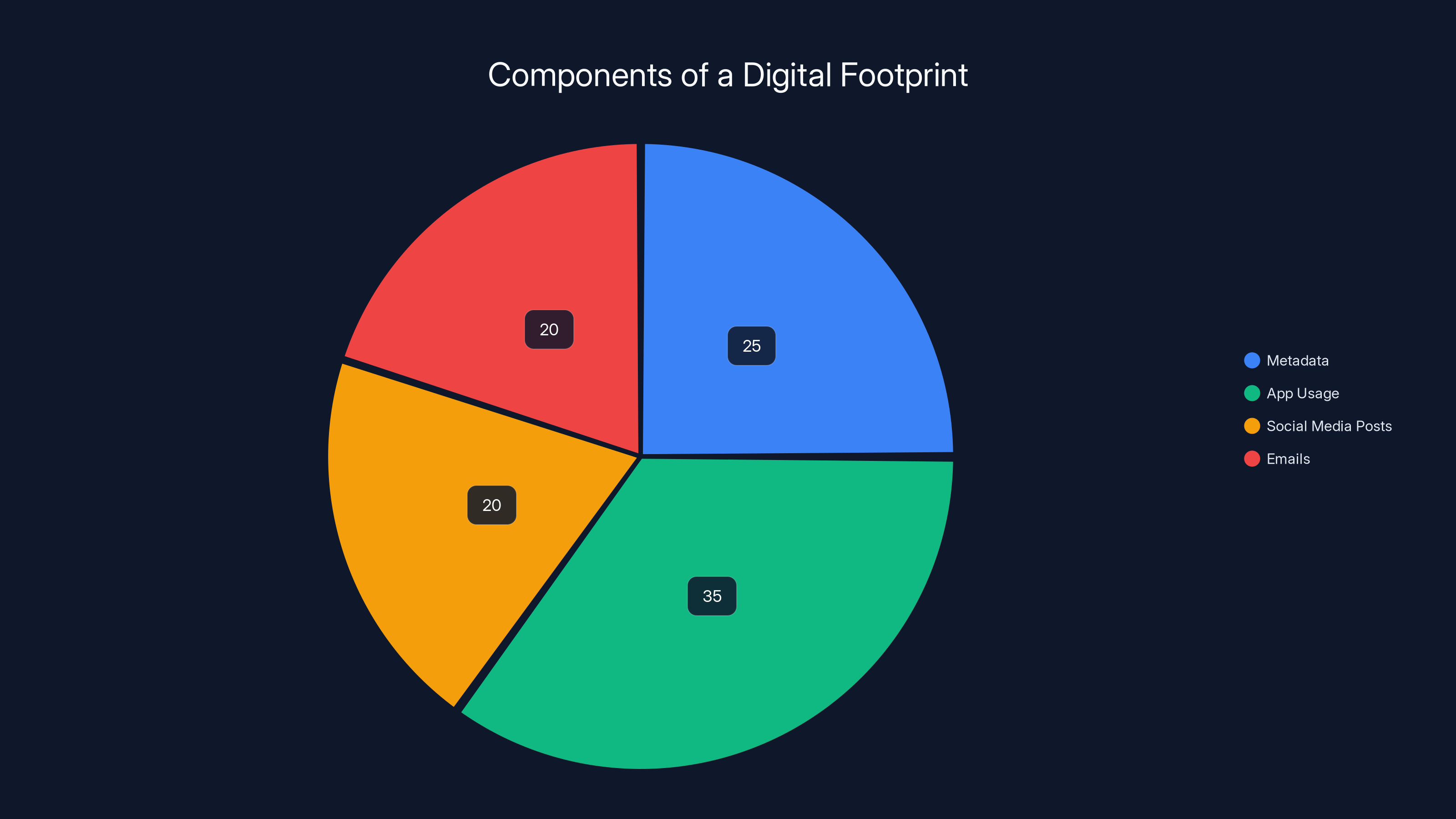
This pie chart illustrates the estimated distribution of components that make up a typical digital footprint, highlighting the significant role of app usage and metadata. Estimated data.
Digital Footprints: A Double-Edged Sword
The Ubiquity of Digital Footprints
Every interaction with our cell phones leaves a digital footprint. Whether it's a simple text message, a social media post, or an email, these actions create data that can be stored, accessed, and analyzed by third parties.
What You Need to Know:
- Metadata: This includes details like the time a message was sent, the recipient, and the location from where it was sent.
- App Usage: Many apps track user behavior, including location and usage patterns.
Real-World Implications
Consider a scenario where someone is accused of being at a certain location at a specific time. Even if they claim otherwise, their phone's GPS data can provide contrary evidence.
Example: In one case, cell tower data was used to place a suspect at the scene of a crime, contradicting their alibi. The digital footprint left by their phone was a key piece of evidence.
Protective Measures
QUICK TIP: Regularly review app permissions to limit unnecessary data collection.
Location Tracking: The Invisible Witness
How Location Tracking Works
Cell phones can pinpoint a user's location using GPS, Wi-Fi, and cell tower triangulation. This data is often collected and stored by service providers and app developers.
Key Technologies:
- GPS: Provides precise location data using satellite signals.
- Cell Tower Triangulation: Estimates location based on signal strength from nearby towers.
- Wi-Fi Positioning: Uses nearby Wi-Fi networks to refine location data.
Legal and Ethical Considerations
While location tracking has legitimate uses, such as navigation and emergency services, it also raises privacy concerns.
Legal Perspective: Courts have increasingly accepted location data as reliable evidence. However, this practice has sparked debates on privacy rights and the need for warrants to access such data. As noted by SCOTUSblog, the U.S. Supreme Court has been involved in cases determining the legality of accessing location data without a warrant.
DID YOU KNOW: In 2018, the U.S. Supreme Court ruled that accessing cell tower location data requires a warrant, recognizing the privacy implications of such data.
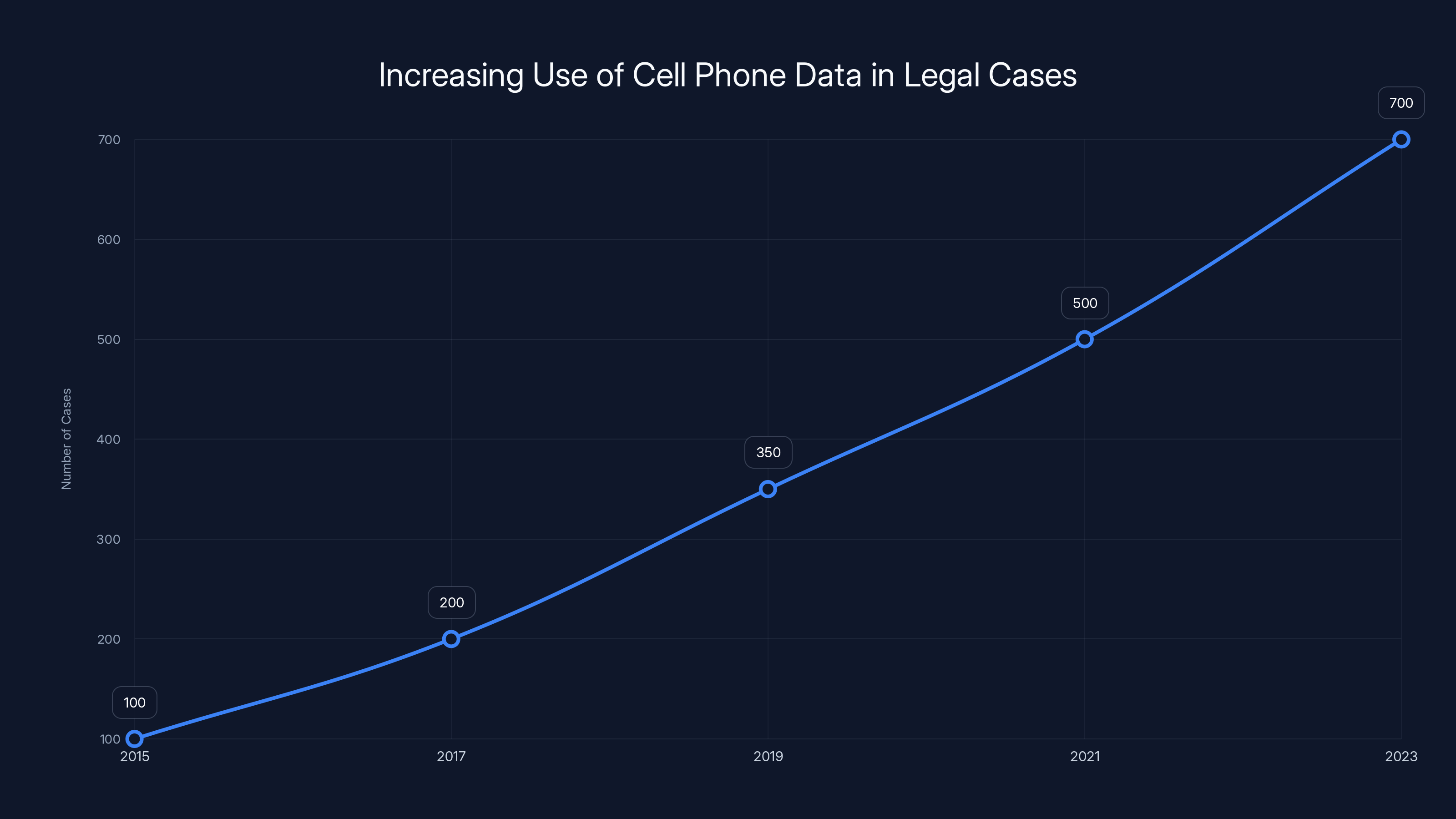
The use of cell phone data in legal cases has significantly increased over the past years, highlighting its growing importance in securing convictions. (Estimated data)
Data Recovery: The Illusion of Deletion
Why Deletion Isn't Always Permanent
Many users assume that deleting a message or photo from their phone removes it completely. However, this data often remains accessible through backups or forensic software.
Technical Insight:
- Data Persistence: Deleted files often remain in storage until overwritten.
- Cloud Backups: Many devices automatically back up data to the cloud, preserving information that users think they have deleted.
Practical Implications
In legal scenarios, recovered data can provide crucial evidence. For instance, Apple's recent patch addressed a flaw that allowed the recovery of deleted chats, highlighting the ongoing challenges in data deletion.
Case Study: A suspect attempted to delete incriminating messages. However, forensic experts were able to recover the data from the phone's internal storage, leading to a conviction.
Best Practices
QUICK TIP: Use secure file deletion tools that overwrite data, making recovery impossible.

Legal Implications: Cell Phones in the Courtroom
The Growing Role of Digital Evidence
Courts increasingly rely on digital evidence from cell phones to corroborate or contradict testimonies. This trend has transformed how cases are investigated and prosecuted.
Key Developments:
- Widespread Use: Mobile data is now a common element in criminal and civil cases.
- Expert Testimony: Digital forensics experts play a crucial role in interpreting phone data.
Example: In a recent case, text messages were used to establish intent, leading to a conviction for fraud.
Challenges and Considerations
While digital evidence is powerful, it also presents challenges:
- Chain of Custody: Ensuring data integrity from collection to presentation in court.
- Interpretation: Data can be misinterpreted without proper context or expertise.

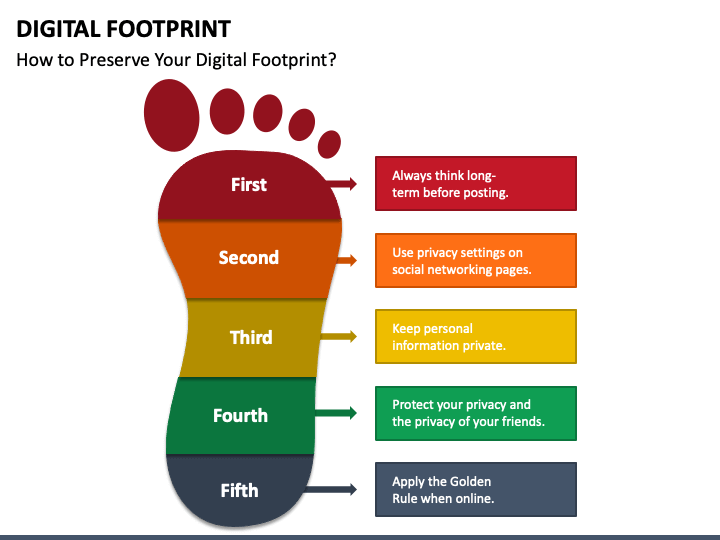
Protecting Your Privacy: Best Practices
Practical Steps to Safeguard Your Data
While it's difficult to completely eliminate digital footprints, there are steps users can take to minimize their exposure.
- Use Encryption: Encrypt sensitive data to prevent unauthorized access.
- Regularly Clear History: Periodically delete browsing history, call logs, and messages.
- Disable Location Services: Turn off location tracking when not needed to reduce data collection.
- Review App Permissions: Limit apps' access to unnecessary data.
Avoiding Common Pitfalls
QUICK TIP: Be cautious about sharing personal information on social media, as this data can be used against you.

Future Trends: The Evolution of Digital Privacy
Emerging Technologies and Their Impact
As technology evolves, so do the methods for collecting and analyzing digital data. Here are some trends to watch:
- AI and Machine Learning: These technologies can process vast amounts of data, identifying patterns that might be missed by human analysts.
- Blockchain for Privacy: Blockchain technology offers potential solutions for secure, transparent data management.
Recommendations for the Future
- Stay Informed: Keep up with changes in technology and privacy laws.
- Adopt New Tools: Use privacy-focused apps and services to protect your data.
- Advocate for Change: Support policies and legislation that prioritize digital privacy.

Conclusion
Cell phones are a double-edged sword. While they offer convenience and connectivity, they also pose significant risks to privacy and security. By understanding how digital data is collected and used, individuals can take proactive steps to protect themselves from self-incrimination.

FAQ
What is digital footprint?
A digital footprint is the trail of data you leave behind when using digital devices and services. It includes everything from your social media activity to your search history.
How does location tracking work on cell phones?
Location tracking uses GPS, Wi-Fi signals, and cell tower triangulation to determine a phone's position. This data is often used for navigation and location-based services.
What are the benefits of encrypting data?
Encryption protects your data from unauthorized access by converting it into a coded format. Only authorized users with the decryption key can access the original data.
How can I protect my privacy on my cell phone?
Use encryption, regularly clear your browsing history, disable unnecessary location services, and review app permissions to minimize data collection.
What should I do if my phone is lost or stolen?
Immediately report the loss to your service provider, remotely lock the device, and change passwords for any accounts accessed through the phone.

Key Takeaways
- Digital footprints can inadvertently lead to self-incrimination.
- Location tracking data is often used as evidence in legal cases.
- Deleted data is frequently recoverable, posing privacy risks.
- Legal systems increasingly rely on digital evidence from cell phones.
- Encrypting data and managing app permissions can protect privacy.
- Emerging technologies like AI may enhance both data collection and privacy protection.
- Understanding digital data collection is crucial for avoiding self-incrimination.
Related Articles
- Understanding Data Security in the Age of AI: Lessons from a US Bank Security Lapse [2025]
- Understanding Zero-Day Exploits: The Case of YellowKey and Windows 11 BitLocker [2025]
- Unveiling the Microsoft BitLocker USB Backdoor: Risks, Solutions, and Future Implications [2025]
- Motorola Razr 2025 Review: The Best-Value Flip Phone for Most People [2025]
- Google Chrome's Incognito Mode and Browsing Privacy [2025]
- Building Data Centers in Orbit: The Future of Cloud Infrastructure [2025]
![How Cell Phones Lead to Self-Incrimination: A Deep Dive [2025]](https://tryrunable.com/blog/how-cell-phones-lead-to-self-incrimination-a-deep-dive-2025/image-1-1778789300307.jpg)



