Unveiling the Microsoft BitLocker USB Backdoor: Risks, Solutions, and Future Implications [2025]
When it comes to data encryption, BitLocker has long been a trusted ally for Windows users. But recent discoveries have shattered this confidence, revealing a potential backdoor that could grant unauthorized access to encrypted drives using nothing more than a USB stick. In this comprehensive guide, we'll delve into how this vulnerability works, explore the implications for users and organizations, and offer actionable advice to safeguard sensitive data.
TL; DR
- BitLocker Vulnerability: A newly discovered flaw allows access to encrypted drives with a USB stick, as detailed in Tom's Hardware.
- Critical Threat: This backdoor can compromise sensitive data without sophisticated tools, according to CyberNews.
- Immediate Action: Users must update their systems and review security protocols, as recommended by TechRadar.
- Long-term Strategy: Implement additional encryption layers and regular security audits, as advised by Wiz.io.
- Future Outlook: Expect advancements in encryption technology and increased scrutiny on data protection, as projected by Fortune Business Insights.

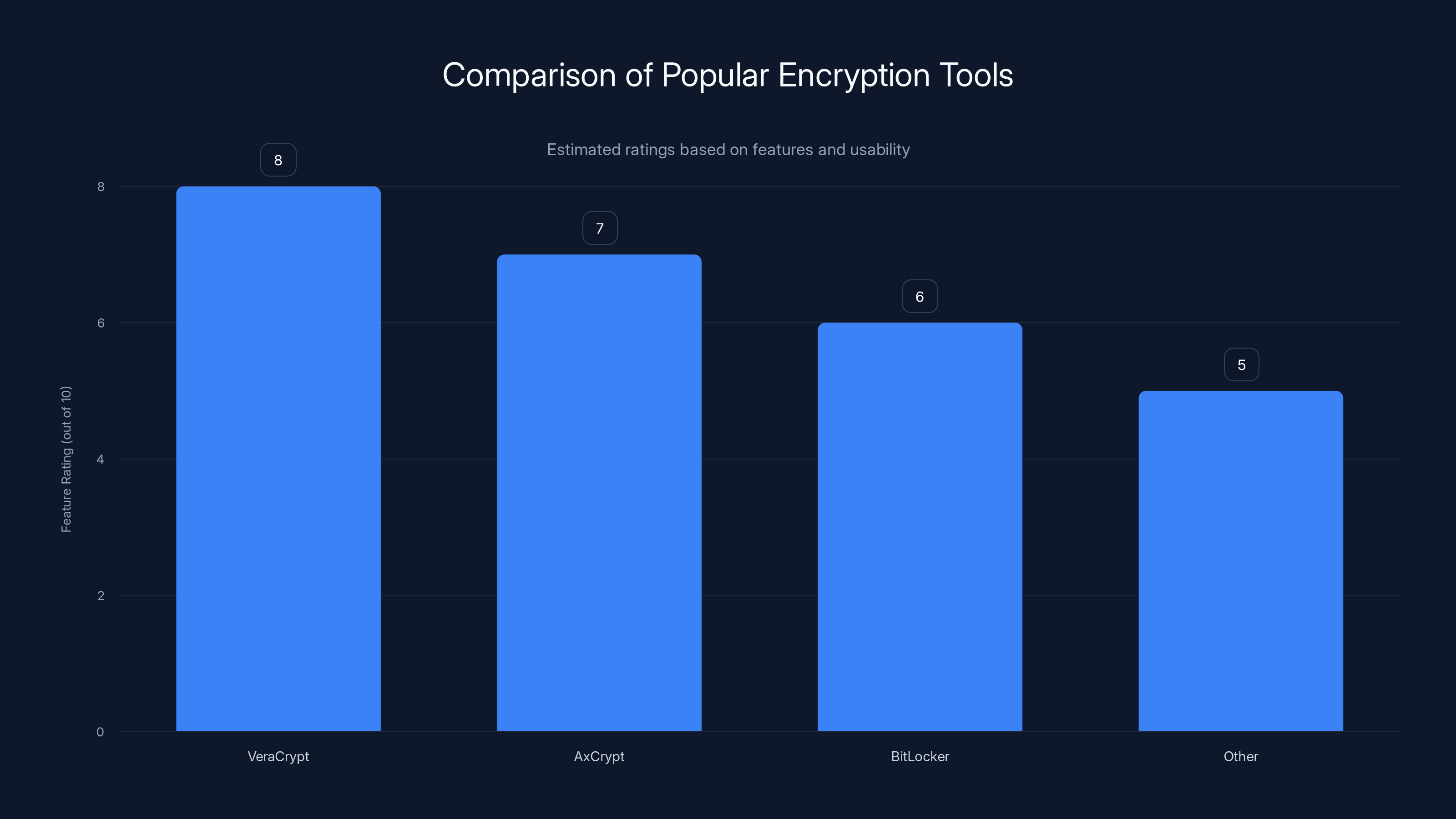
VeraCrypt and AxCrypt are rated higher than BitLocker for additional encryption features. Estimated data based on typical user reviews.
The BitLocker Backdoor: An Overview
Microsoft's BitLocker has been a cornerstone of Windows security, providing full-disk encryption to protect data from unauthorized access. However, a newly uncovered vulnerability, often referred to as Yellow Key, has raised significant concerns. This flaw leverages a USB stick to bypass BitLocker’s encryption, effectively acting as a backdoor into what was presumed to be a secure fortress, as reported by TechPowerUp.
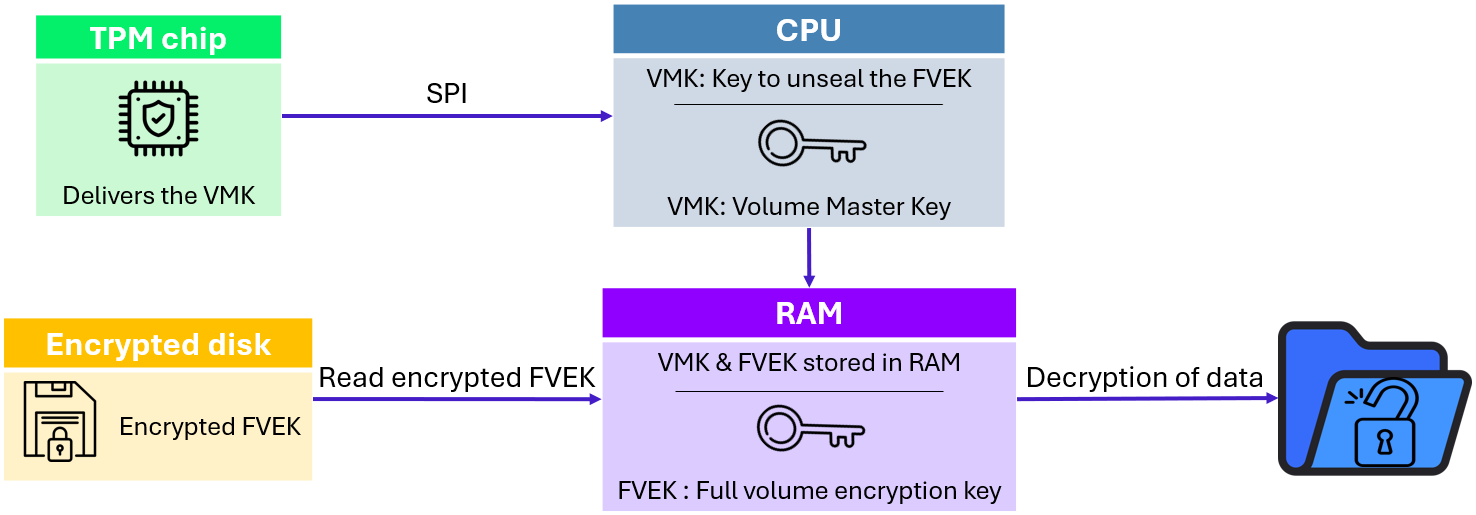
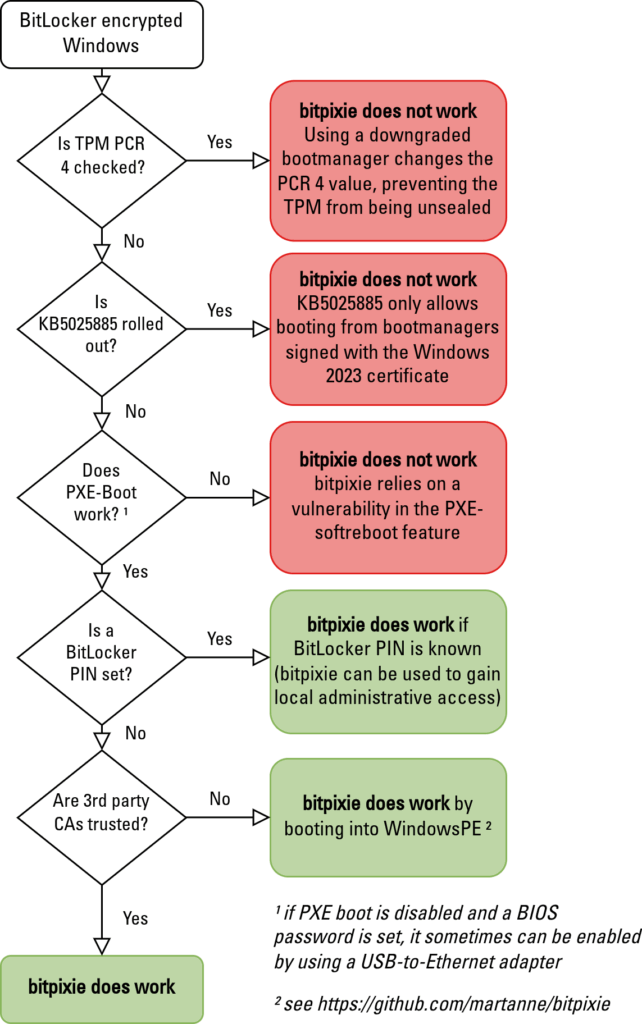
How the BitLocker Vulnerability Works
At the heart of this vulnerability is the ability to manipulate the BitLocker boot process. When a USB stick with specific malicious code is inserted during start-up, it can exploit the pre-boot authentication phase, where BitLocker is most vulnerable. By intercepting this phase, the USB stick can gain unauthorized access to the encrypted data, as explained by MakeUseOf.
Key Points:
- The attack requires physical access to the target machine.
- It exploits the pre-boot environment, bypassing standard encryption checks.
- The vulnerability is potentially exploitable on systems with outdated security patches, as noted by Qualys.
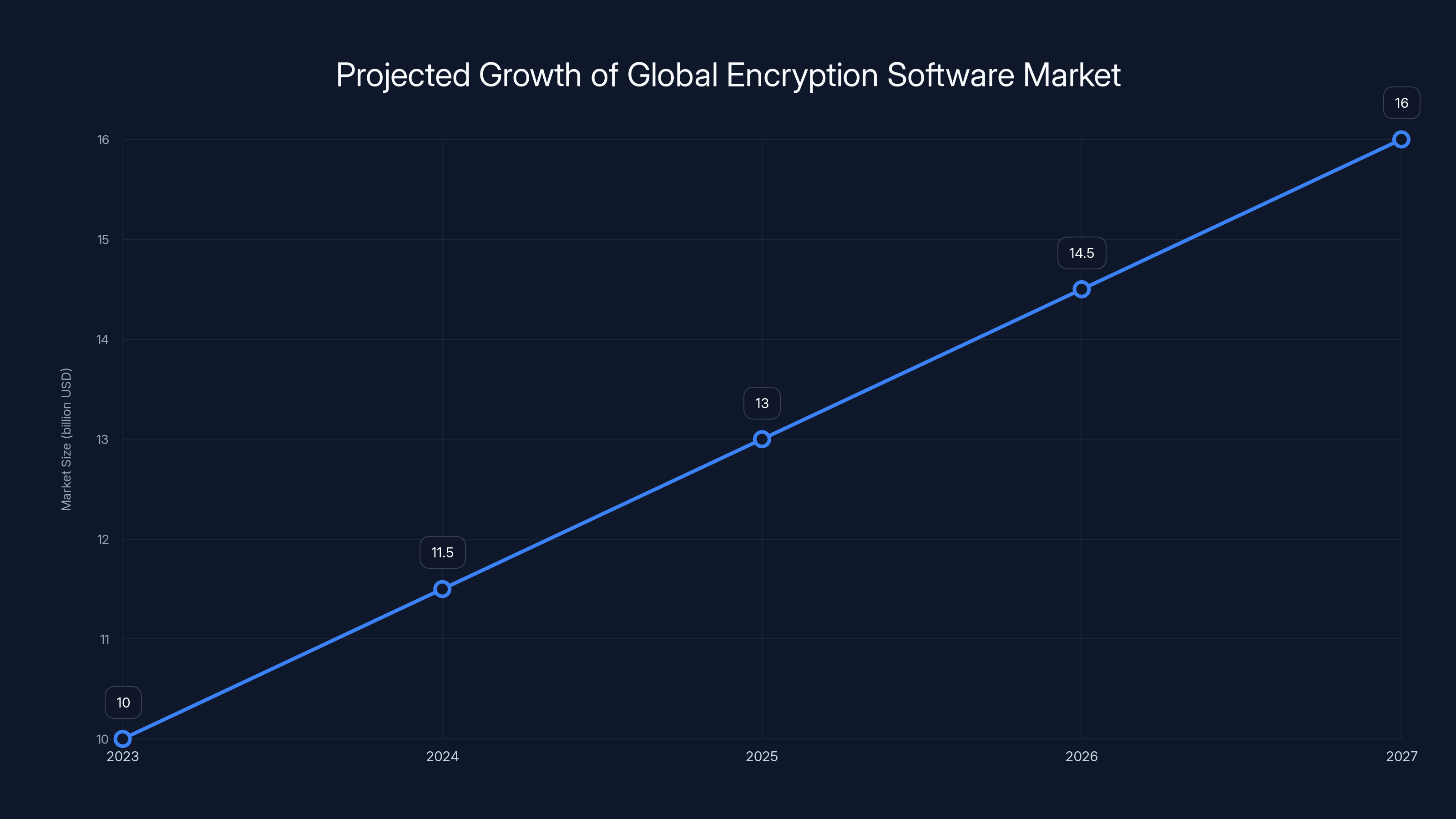
The global encryption software market is projected to grow from
Understanding the Implications
Personal Data at Risk
For individual users, the implications are clear: personal data stored on encrypted drives is no longer as secure as once believed. Sensitive information such as financial records, personal documents, and private communications could be exposed if a malicious actor gains physical access to your computer, as highlighted by BleepingComputer.
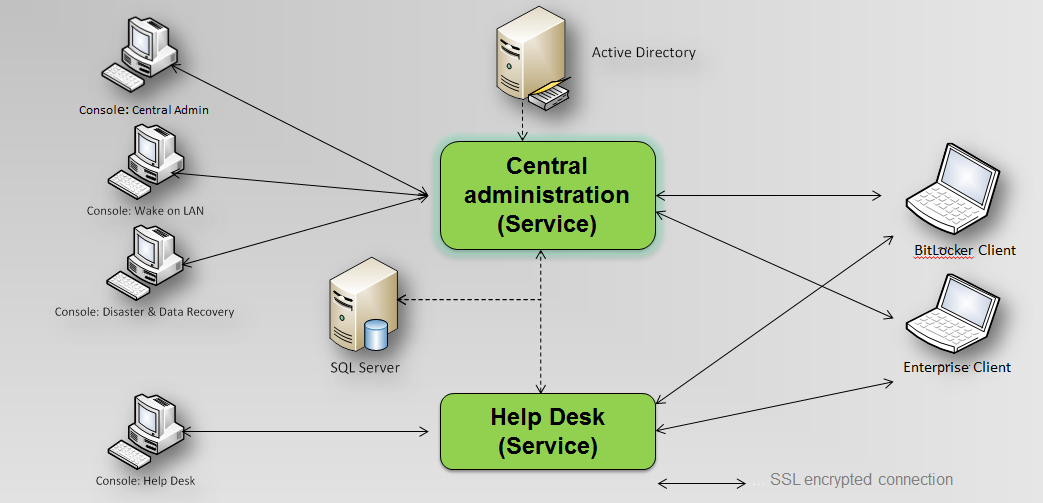
Organizational Threats
For organizations, the stakes are even higher. Corporate data breaches can lead to severe financial penalties, loss of customer trust, and legal repercussions. The ability for an attacker to unlock encrypted drives with minimal effort poses a substantial risk to corporate security protocols, as discussed in Trend Micro.
Example Scenario: Consider a scenario where an employee's laptop is stolen. With the BitLocker backdoor, any sensitive company data on that drive could be at immediate risk of exposure.
Best Practices for Mitigating Risk
Regular System Updates
The first line of defense against any security vulnerability is to ensure that all systems are up-to-date with the latest patches and updates. Microsoft routinely releases security updates that address identified vulnerabilities, including those that may affect BitLocker, as noted by TechRadar.
Quick Tip: Enable automatic updates on Windows systems to ensure you don't miss critical security patches.
Implementing Additional Encryption Layers
Relying solely on BitLocker for encryption may no longer be sufficient. Consider implementing additional encryption layers using third-party software solutions that can protect data at rest, in transit, and during access, as recommended by Wiz.io.
Popular Tools:
- VeraCrypt: Offers container-based encryption.
- AxCrypt: Provides easy-to-use file encryption for individual files.
Physical Security Measures
Since the vulnerability requires physical access, enhancing physical security can significantly reduce risk. Employ measures such as security cables for laptops, secure storage for devices, and access control systems in sensitive areas.
Fun Fact: Did you know that physical theft accounts for 50% of data breaches according to a recent cybersecurity report?
Regular Security Audits
Conducting regular security audits can help identify potential weaknesses in your security framework. These audits should include penetration testing, vulnerability assessments, and reviews of access controls, as advised by Wiz.io.
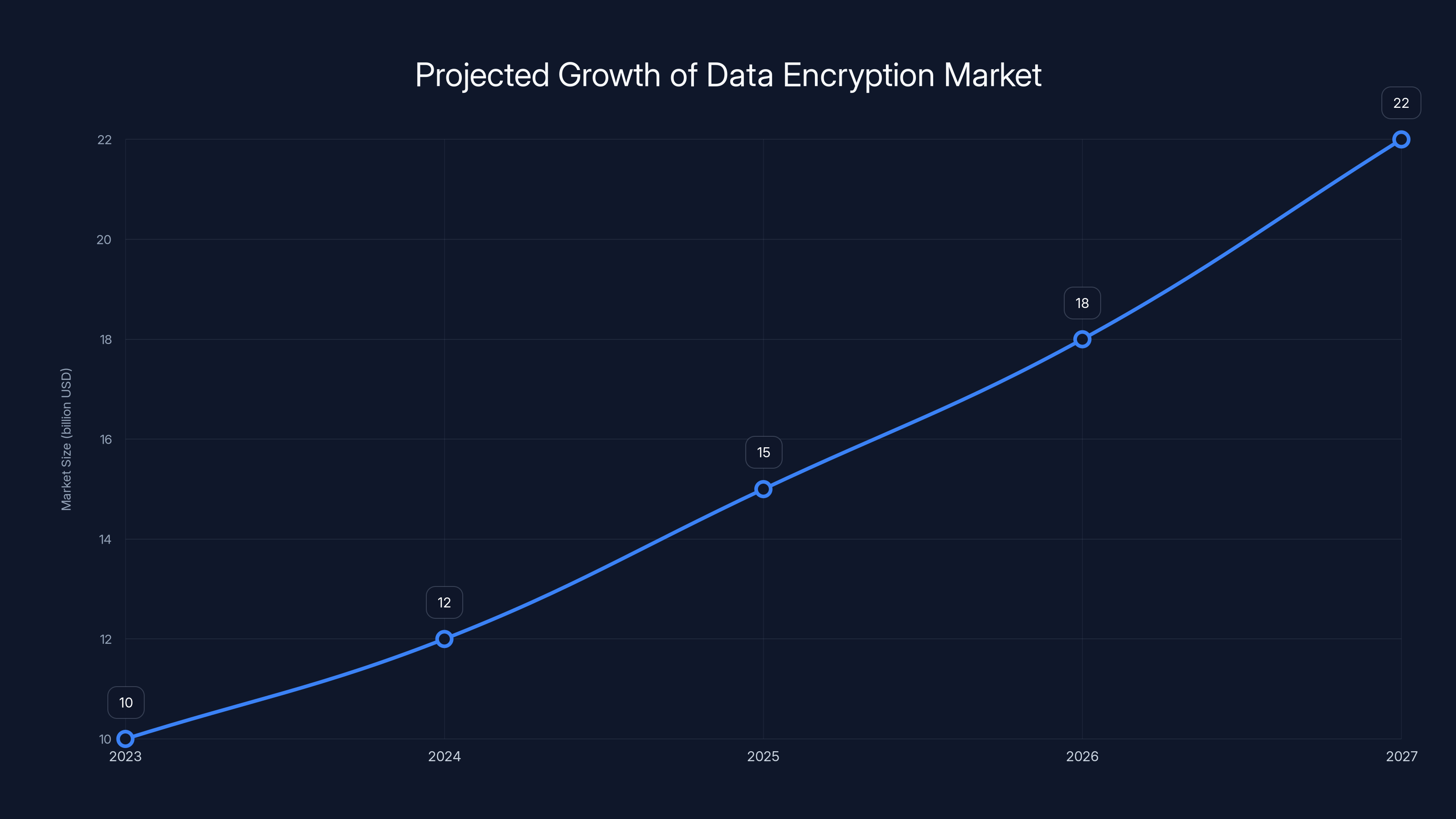
The data encryption market is projected to grow significantly, reaching an estimated $22 billion by 2027, driven by the need for secure data solutions and compliance. Estimated data.
Implementation Guide: Securing Your BitLocker Deployment
Step-by-Step BitLocker Security Enhancement
- Enable TPM (Trusted Platform Module): Ensure that BitLocker uses TPM to enhance security.
- Set a Strong Recovery Password: Create a complex, unique recovery password for BitLocker.
- Use Multifactor Authentication: Combine BitLocker with multifactor authentication for an extra layer of security.
- Encrypt Individual Files: Use additional software to encrypt critical files beyond BitLocker.
- Monitor Access Logs: Regularly review BitLocker access logs for unusual activity.
Common Pitfalls and Solutions
Pitfall: Neglecting Physical Security
Solution: Implement strict access controls and physical security measures to prevent unauthorized access to devices.
Pitfall: Failing to Update Regularly
Solution: Automate system updates and conduct regular checks to ensure all updates are applied promptly.
Pitfall: Overreliance on BitLocker
Solution: Diversify encryption strategies by using multiple layers of encryption and security measures.
Future Trends in Data Encryption
Advancements in Encryption Technologies
As vulnerabilities like the BitLocker backdoor are discovered, expect significant advancements in encryption technologies. This includes the development of quantum-resistant algorithms and more robust encryption frameworks, as anticipated by Fortune Business Insights.
Increased Regulatory Scrutiny
Governments and regulatory bodies are likely to impose stricter data protection standards. Organizations will need to comply with these regulations to avoid penalties and ensure data security, as noted by Wiz.io.
DID YOU KNOW: By 2027, the global encryption software market is expected to reach $16 billion, driven by increased demand for secure data solutions.

Recommendations for Organizations
- Invest in Employee Training: Educate employees about security best practices and how to recognize potential threats.
- Develop a Response Plan: Have a clear incident response plan in place to quickly address any breaches.
- Stay Informed: Keep abreast of the latest security threats and solutions through trusted cybersecurity sources.
- Evaluate Security Vendors: Regularly review and assess the security solutions and vendors you rely on.
Conclusion
The discovery of a backdoor in Microsoft's BitLocker is a wake-up call for anyone who relies on encryption for data protection. While the vulnerability poses significant risks, by understanding the threat and implementing robust security measures, individuals and organizations can protect themselves against unauthorized access. Stay vigilant, stay informed, and stay secure.
FAQ
What is the BitLocker backdoor vulnerability?
The BitLocker backdoor vulnerability refers to a flaw that allows unauthorized access to encrypted drives using a USB stick, as detailed by Tom's Hardware.
How can I protect my data from this vulnerability?
Protect your data by keeping your systems updated, using additional encryption layers, and enhancing physical security measures, as advised by TechRadar.
Why is physical security important for data protection?
Physical security prevents unauthorized access to devices, which is crucial since many vulnerabilities require physical access to exploit, as noted by CyberNews.
What should organizations do to mitigate risk?
Organizations should conduct regular security audits, train employees on security best practices, and implement comprehensive encryption strategies, as recommended by Wiz.io.
How will encryption technologies evolve in the future?
Expect advancements in quantum-resistant algorithms, more robust encryption frameworks, and increased regulatory scrutiny, as projected by Fortune Business Insights.
What is the future outlook for data encryption?
The future of data encryption will see significant growth in the market, driven by the need for secure data solutions and regulatory compliance, as noted by Fortune Business Insights.
How can I stay informed about the latest security threats?
Follow trusted cybersecurity sources, attend industry conferences, and participate in security forums to stay updated on emerging threats, as advised by Wiz.io.
What are the long-term impacts of the BitLocker vulnerability?
Long-term impacts include increased focus on encryption technologies, regulatory changes, and the adoption of more stringent security measures, as discussed by TechRadar.
Key Takeaways
- BitLocker vulnerability allows USB-based access to encrypted drives.
- Physical security is crucial for protecting data integrity.
- Regular updates and additional encryption layers are essential.
- Security audits help identify and mitigate potential threats.
- Future encryption technologies will focus on quantum resistance.
- Organizations must comply with evolving data protection regulations.
- Employee training is vital for recognizing and responding to threats.
- The encryption software market is poised for significant growth.
Related Articles
- Exposing Cyber Intruders: A Deep Dive into Russian Government Hackers Targeting Signal Accounts [2025]
- Microsoft's MDASH AI Security Platform: A Game Changer? [2025]
- Cisco's Record Revenue and Layoffs: Navigating Growth and Workforce Restructuring [2025]
- Understanding Supply Chain Attacks: Lessons from the OpenAI Data Breach [2025]
- Unveiling the Future: Microsoft's Innovative Xbox Cloud Gaming Controller [2025]
- Cisco's Strategic Shift: Embracing AI and Cybersecurity Amid Workforce Reductions [2025]
![Unveiling the Microsoft BitLocker USB Backdoor: Risks, Solutions, and Future Implications [2025]](https://tryrunable.com/blog/unveiling-the-microsoft-bitlocker-usb-backdoor-risks-solutio/image-1-1778778377730.jpg)



