Understanding Zero-Day Exploits: The Case of Yellow Key and Windows 11 Bit Locker [2025]
Last week, the cybersecurity community was rocked by the revelation of a zero-day exploit called Yellow Key that can bypass the default Bit Locker protections on Windows 11. This exploit, disclosed by a researcher known as Nightmare-Eclipse, highlights significant vulnerabilities in encryption systems many rely on for data security, as detailed by Tom's Hardware.
TL; DR
- Yellow Key exploit allows bypassing of Windows 11 Bit Locker encryption, granting unauthorized drive access, as reported by Gigazine.
- Physical access is required, emphasizing the need for stringent physical security measures.
- Bit Locker relies on TPM for encryption, which Yellow Key circumvents by manipulating disk volumes, according to Computer Weekly.
- Immediate patches and updates are crucial to mitigate risks associated with zero-day exploits.
- Future security: Enhanced encryption protocols and user awareness are vital.
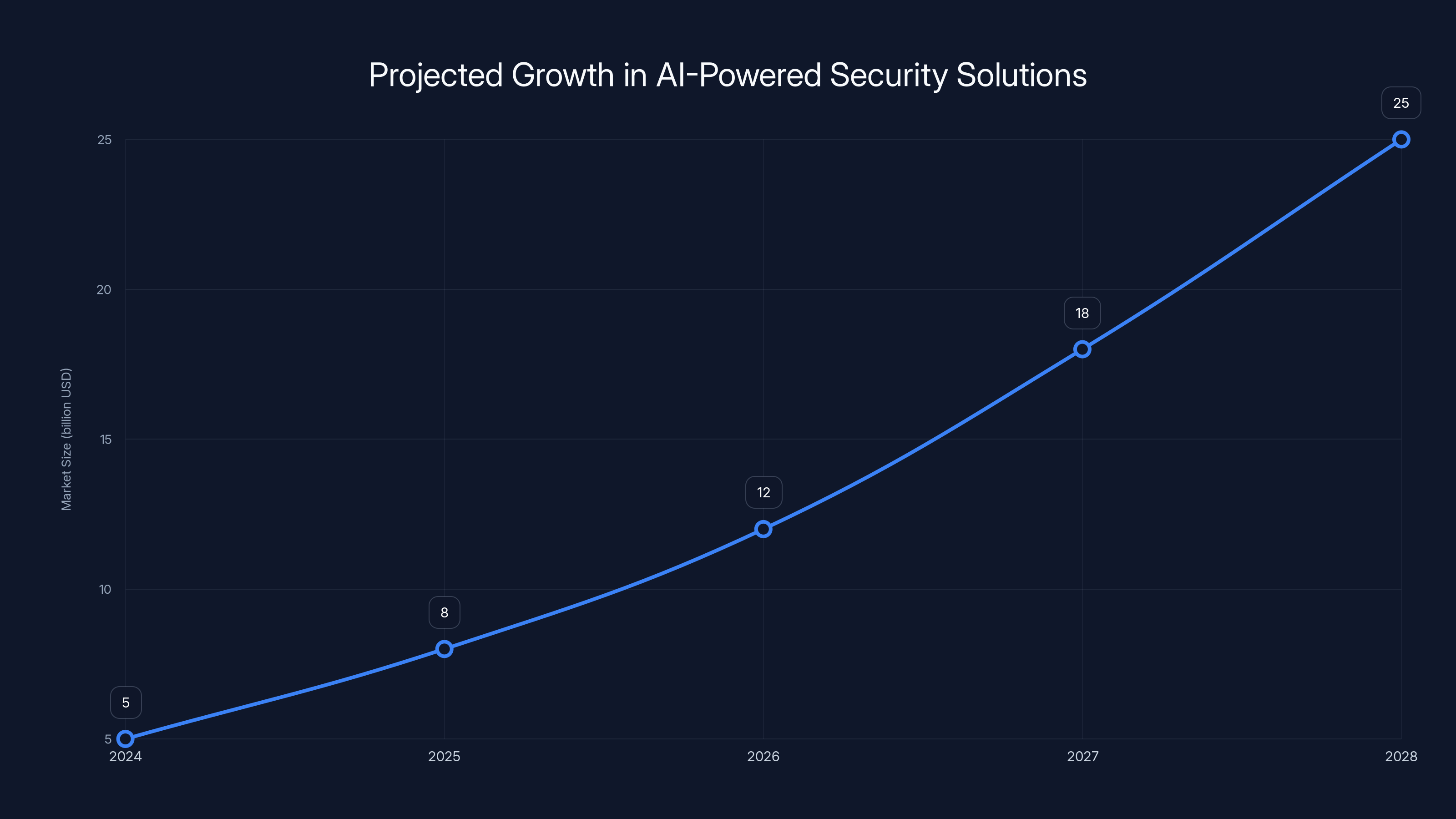
AI-powered security solutions are projected to grow significantly, reaching an estimated market size of 25 billion USD by 2028, as noted by Fortune Business Insights.
The Rise of Zero-Day Exploits
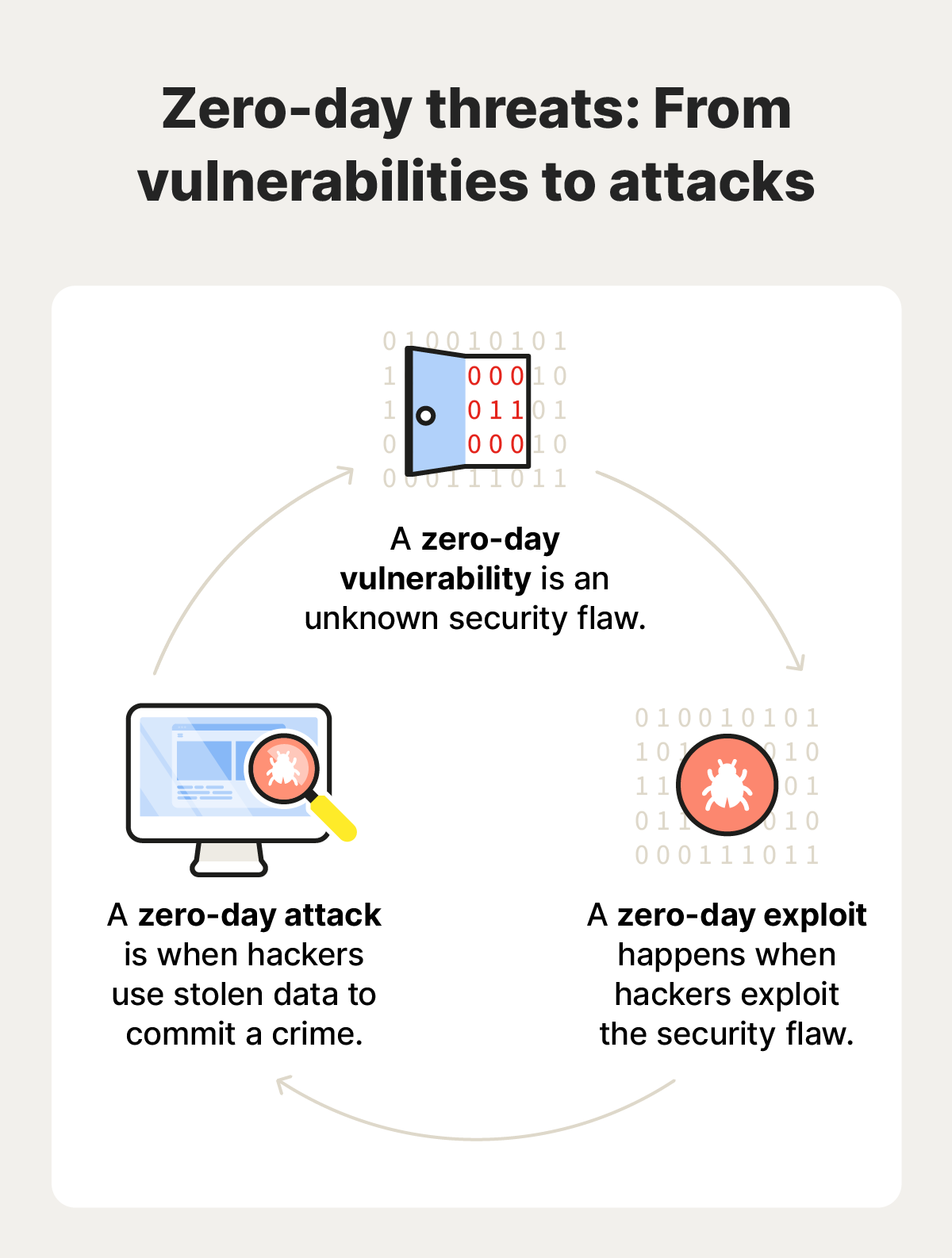
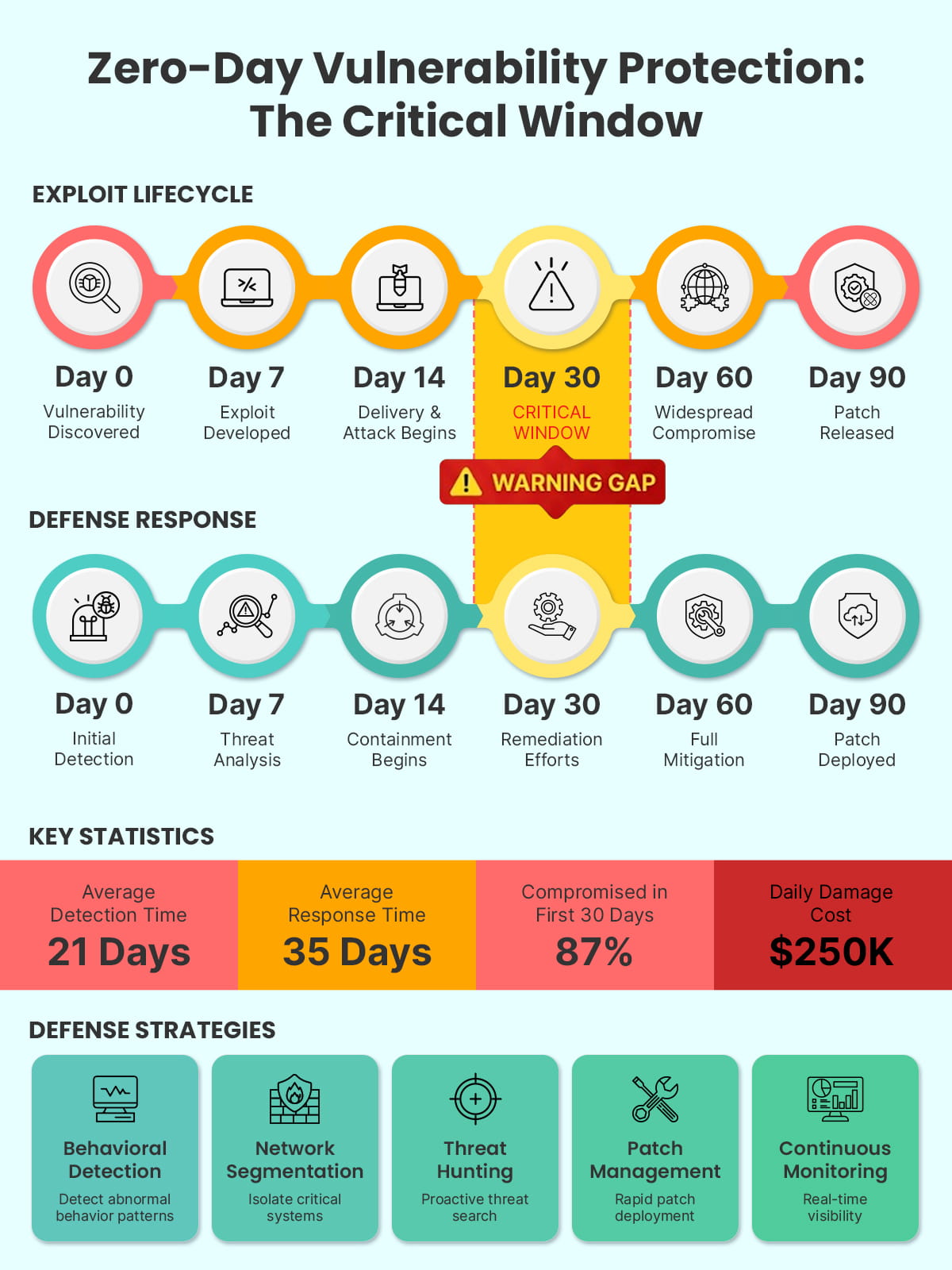
Zero-day exploits are vulnerabilities discovered by attackers before the software vendor is aware of them. These exploits are particularly dangerous because they can be used to compromise systems without any available fixes or patches, as highlighted by Bleeping Computer.
What Makes Zero-Day Exploits Dangerous?
Zero-day exploits are named for the lack of time developers have had to address the vulnerability—literally zero days. This means that once the exploit is discovered and used maliciously, users and organizations are at risk until a patch is released. These exploits can lead to unauthorized data access, system control, and potentially catastrophic data breaches.
Common Targets
Zero-day exploits often target:
- Operating Systems: Windows, Linux, and mac OS are frequent targets due to their widespread use.
- Browsers: Chrome, Firefox, and Edge are targeted for their extensive reach and potential to access sensitive information.
- Applications: Software with large user bases like Adobe Reader and Microsoft Office.

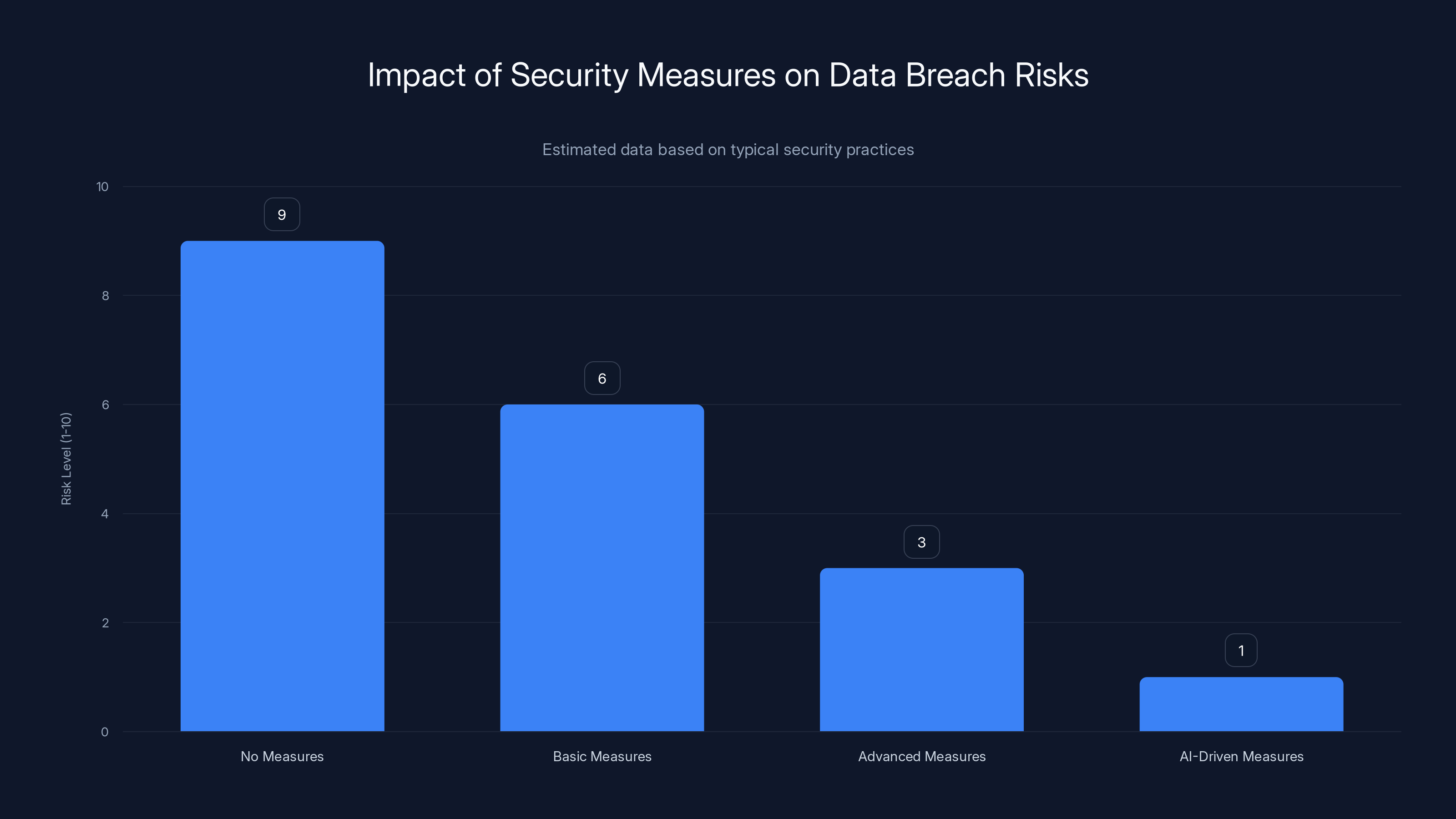
Implementing advanced and AI-driven security measures significantly reduces the risk level of data breaches, according to CyberScoop.
Bit Locker and Its Role in Data Security
Bit Locker is Microsoft's disk encryption program, designed to protect data by providing encryption for entire volumes. It is commonly used in enterprise environments to secure data on Windows devices, as explained in eSecurity Planet.
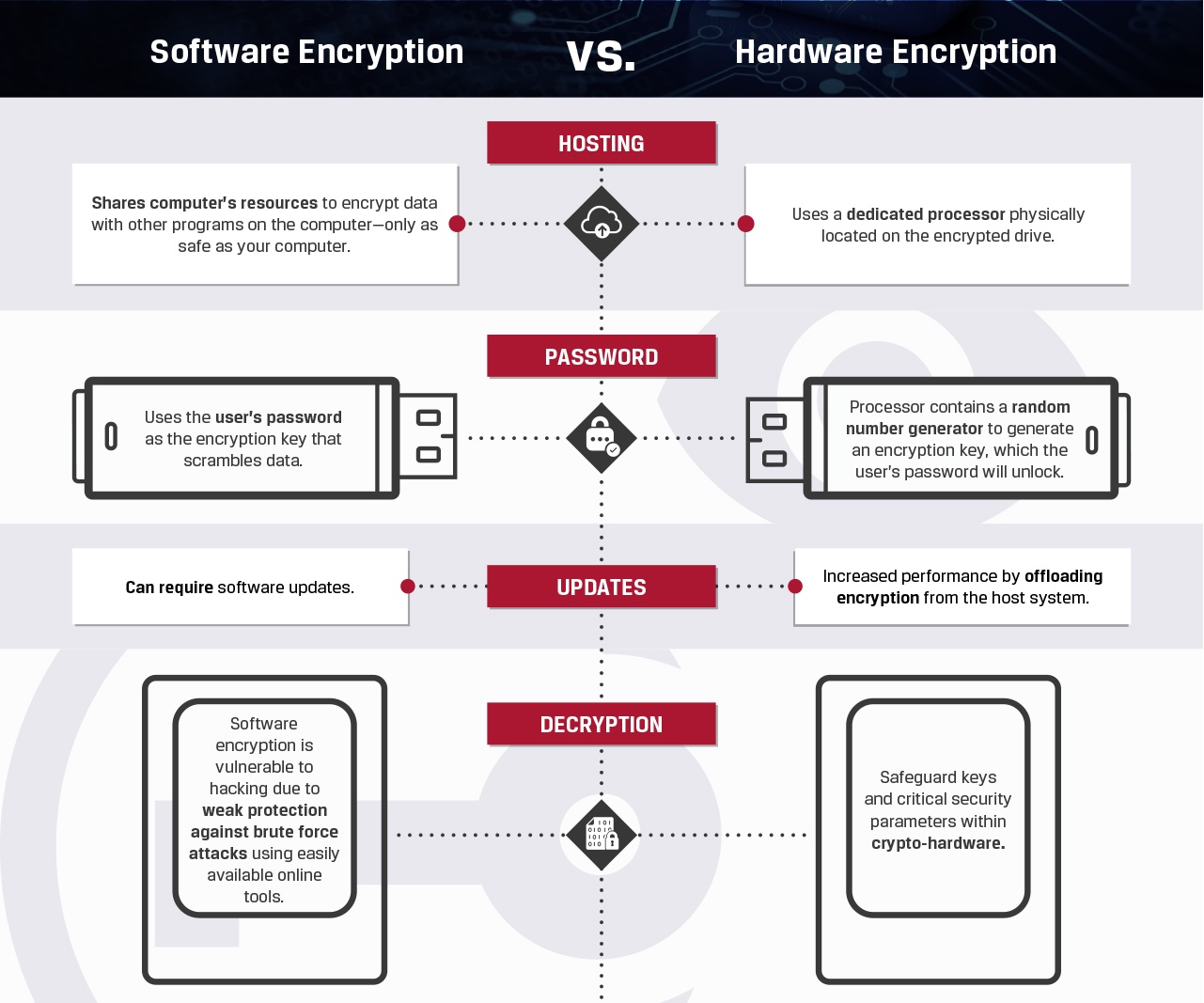
How Bit Locker Works
Bit Locker uses the Trusted Platform Module (TPM) to store encryption keys securely. The TPM is a hardware component that provides secure cryptographic functions. When Bit Locker is enabled, it encrypts the entire drive, making data inaccessible without the correct decryption key.
- Full-Disk Encryption: Encrypts all data on a drive, including user files and system files.
- Pre-Boot Authentication: Ensures that only authorized users can access the system.
Benefits of Bit Locker
- Data Protection: Even if a device is lost or stolen, the data remains protected.
- Compliance: Helps organizations meet regulatory requirements for data protection.
- Ease of Use: Integrated into Windows, making it simple for users to deploy.
The Yellow Key Exploit: Unveiling the Threat
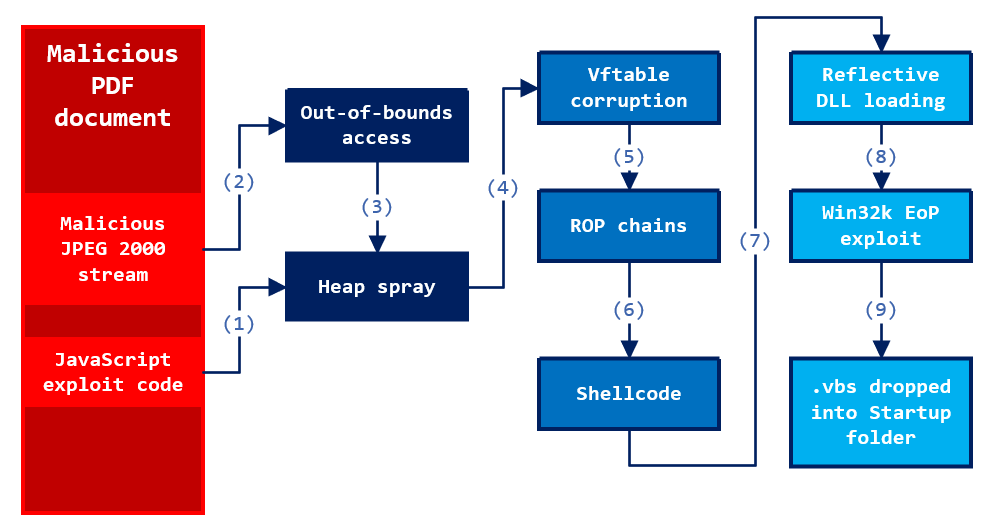
The Yellow Key exploit bypasses Bit Locker protections by exploiting a vulnerability in how Windows 11 handles disk volumes. The exploit requires physical access to the machine, making it a critical concern for devices that might be physically compromised, as detailed by Bitdefender.
How Yellow Key Works
The exploit involves creating a custom Fs Tx folder that manipulates disk volumes. This process circumvents the TPM, allowing access to encrypted data without the decryption key.
- Physical Access Required: Attackers need to have hands-on access to the device.
- Volume Manipulation: Alters the interaction between disk volumes to bypass encryption.
Implications of Yellow Key
- Data Breaches: Sensitive data can be accessed, leading to potential breaches and data leaks.
- Regulatory Risks: Organizations may face fines and penalties if they fail to protect data adequately.
- Trust Issues: Users and clients may lose trust in a company's ability to safeguard information.
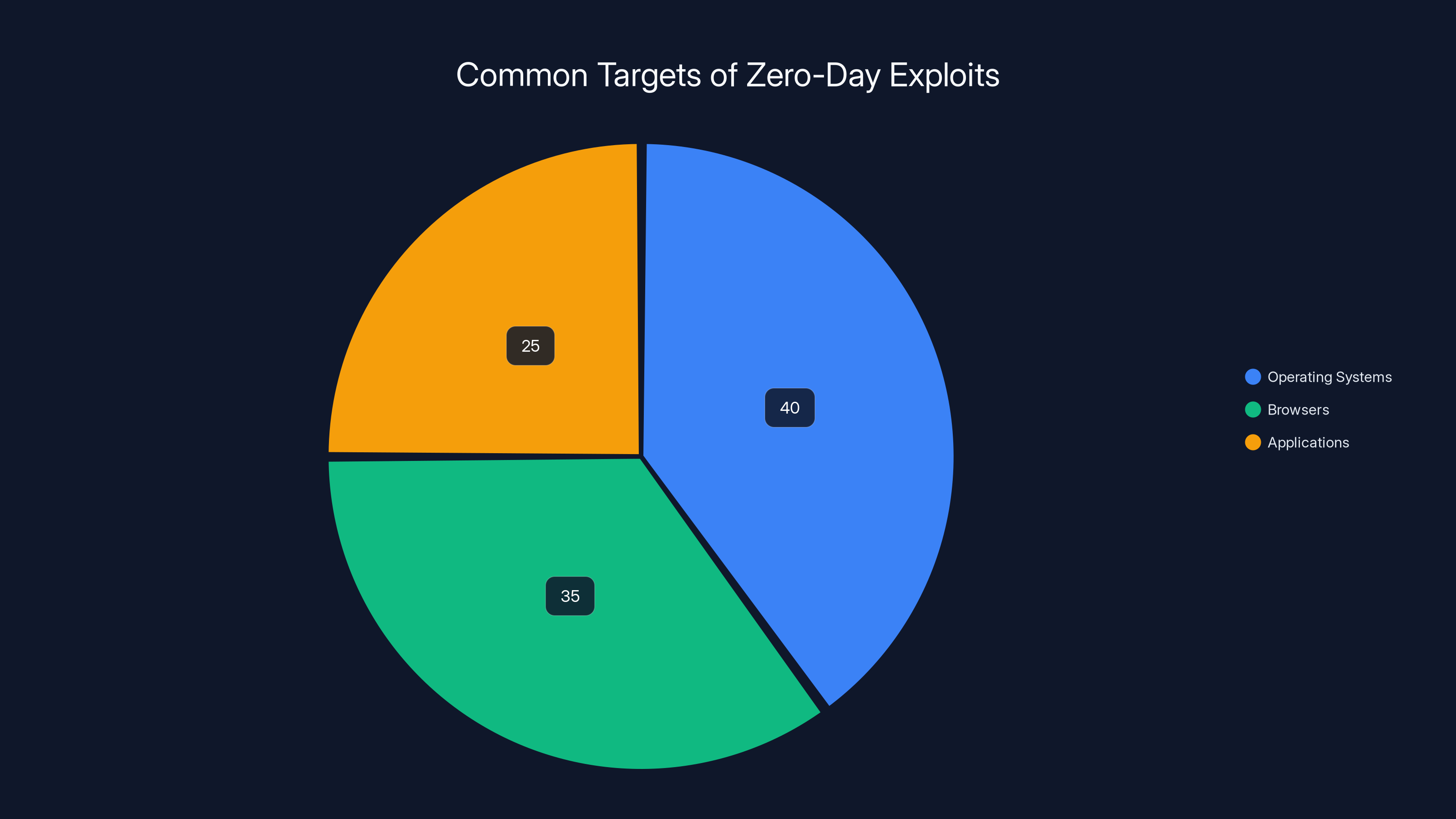
Operating systems are the most common targets for zero-day exploits, followed closely by browsers and applications, as noted by Mozilla.
How to Protect Against Zero-Day Exploits
Immediate Steps
- Apply Patches: As soon as Microsoft releases a patch, apply it to all affected systems, as advised by TechPowerUp.
- Restrict Physical Access: Limit who can physically access devices, especially in sensitive environments.
- Monitor Systems: Use intrusion detection systems to monitor for unusual activity.
Long-Term Strategies
- Regular Updates: Ensure all software and systems are regularly updated to protect against known vulnerabilities.
- User Education: Train users to recognize and avoid potential security threats.
- Advanced Security Tools: Employ tools that can detect and prevent zero-day exploits, such as endpoint protection platforms.
Implementing Stronger Encryption Practices
While Bit Locker is a robust security tool, its vulnerabilities highlight the need for a multi-layered approach to security.
Enhancing Encryption
- Multi-Factor Authentication (MFA): Add an extra layer of security by requiring multiple forms of verification.
- Enhanced TPM Configurations: Ensure TPM is configured to its highest security settings.
- Regular Security Audits: Conduct audits to identify and address potential vulnerabilities.
Common Pitfalls and Solutions
- Over-Reliance on Single Solutions: Relying solely on Bit Locker can be risky. Use additional security measures.
- Neglecting Physical Security: Implement robust physical security protocols to protect devices.
- Ignoring User Behavior: User negligence can lead to security breaches. Train staff regularly.
Future Trends in Encryption and Data Security
The Yellow Key exploit is a wake-up call for the cybersecurity community, highlighting the evolving nature of threats.
Predicted Developments
- AI-Powered Security: Artificial intelligence will play a larger role in detecting and preventing exploits, as suggested by IBM.
- Quantum Encryption: As quantum computing advances, new encryption methods will emerge to counteract its capabilities.
- Increased Regulation: Governments may impose stricter regulations to ensure data security.
Recommendations for Organizations
- Invest in Research: Stay informed about the latest security threats and advancements.
- Adopt a Proactive Approach: Regularly update security policies and practices.
- Collaborate with Experts: Engage with cybersecurity professionals to enhance defenses.

Conclusion
While the Yellow Key exploit poses significant challenges, it also underscores the importance of maintaining vigilant security practices. By understanding the nature of zero-day exploits and implementing robust security measures, organizations can better protect their data and maintain trust with their stakeholders.
Use Case: Automate encryption audits and enhance security protocols with AI-driven insights.
Try Runable For FreeKey Takeaways
- YellowKey exploit bypasses Windows 11's BitLocker, allowing unauthorized data access.
- Requires physical access, underscoring the need for robust physical security measures.
- Mitigation involves immediate software patches and restricting physical access.
- Future security enhancements will include AI-driven defenses and quantum encryption.
- User education and regular updates are critical in maintaining data security.
Related Articles
- Unveiling the Microsoft BitLocker USB Backdoor: Risks, Solutions, and Future Implications [2025]
- Microsoft's MDASH AI Security Platform: A Game Changer? [2025]
- Exposing Cyber Intruders: A Deep Dive into Russian Government Hackers Targeting Signal Accounts [2025]
- Windows Update's New Feature: Automatic Driver Rollback [2025]
- Microsoft Wants Your Help to Fix Windows 11 — Let’s Make It Count [2025]
- Understanding the Fragnesia Flaw: How It Threatens Linux Security [2025]
FAQ
What is Understanding Zero-Day Exploits: The Case of YellowKey and Windows 11 BitLocker [2025]?
Last week, the cybersecurity community was rocked by the revelation of a zero-day exploit called Yellow Key that can bypass the default Bit Locker protections on Windows 11
What does tl; dr mean?
This exploit, disclosed by a researcher known as Nightmare-Eclipse, highlights significant vulnerabilities in encryption systems many rely on for data security
Why is Understanding Zero-Day Exploits: The Case of YellowKey and Windows 11 BitLocker [2025] important in 2025?
- Yellow Key exploit allows bypassing of Windows 11 Bit Locker encryption, granting unauthorized drive access
How can I get started with Understanding Zero-Day Exploits: The Case of YellowKey and Windows 11 BitLocker [2025]?
- Physical access is required, emphasizing the need for stringent physical security measures
What are the key benefits of Understanding Zero-Day Exploits: The Case of YellowKey and Windows 11 BitLocker [2025]?
- Bit Locker relies on TPM for encryption, which Yellow Key circumvents by manipulating disk volumes
What challenges should I expect?
- Immediate patches and updates are crucial to mitigate risks associated with zero-day exploits
![Understanding Zero-Day Exploits: The Case of YellowKey and Windows 11 BitLocker [2025]](https://tryrunable.com/blog/understanding-zero-day-exploits-the-case-of-yellowkey-and-wi/image-1-1778785684011.jpg)



