How to Secure Cryptocurrency Holdings: Lessons from the South Korean Crypto Incident [2025]
Last month, a security mishap shook the cryptocurrency world when South Korean police inadvertently leaked a wallet password, resulting in the loss of $5 million in seized assets. This incident serves as a stark reminder of the vulnerabilities in handling digital currencies, even by official entities. As crypto continues to grow, understanding how to secure these assets is more crucial than ever.
TL; DR
- Incident Overview: South Korean police accidentally exposed a wallet password, leading to a $5 million loss as reported by Ars Technica.
- Security Best Practices: Use cold wallets, enable two-factor authentication, and employ multi-signature wallets.
- Common Mistakes: Avoid sharing private keys and recovery phrases publicly or in unsecured environments.
- Emerging Trends: AI-driven security solutions and quantum-resistant cryptography are on the rise.
- Actionable Steps: Implement layered security measures to protect digital assets.
- Bottom Line: Proactive security strategies are essential to safeguard cryptocurrency investments.
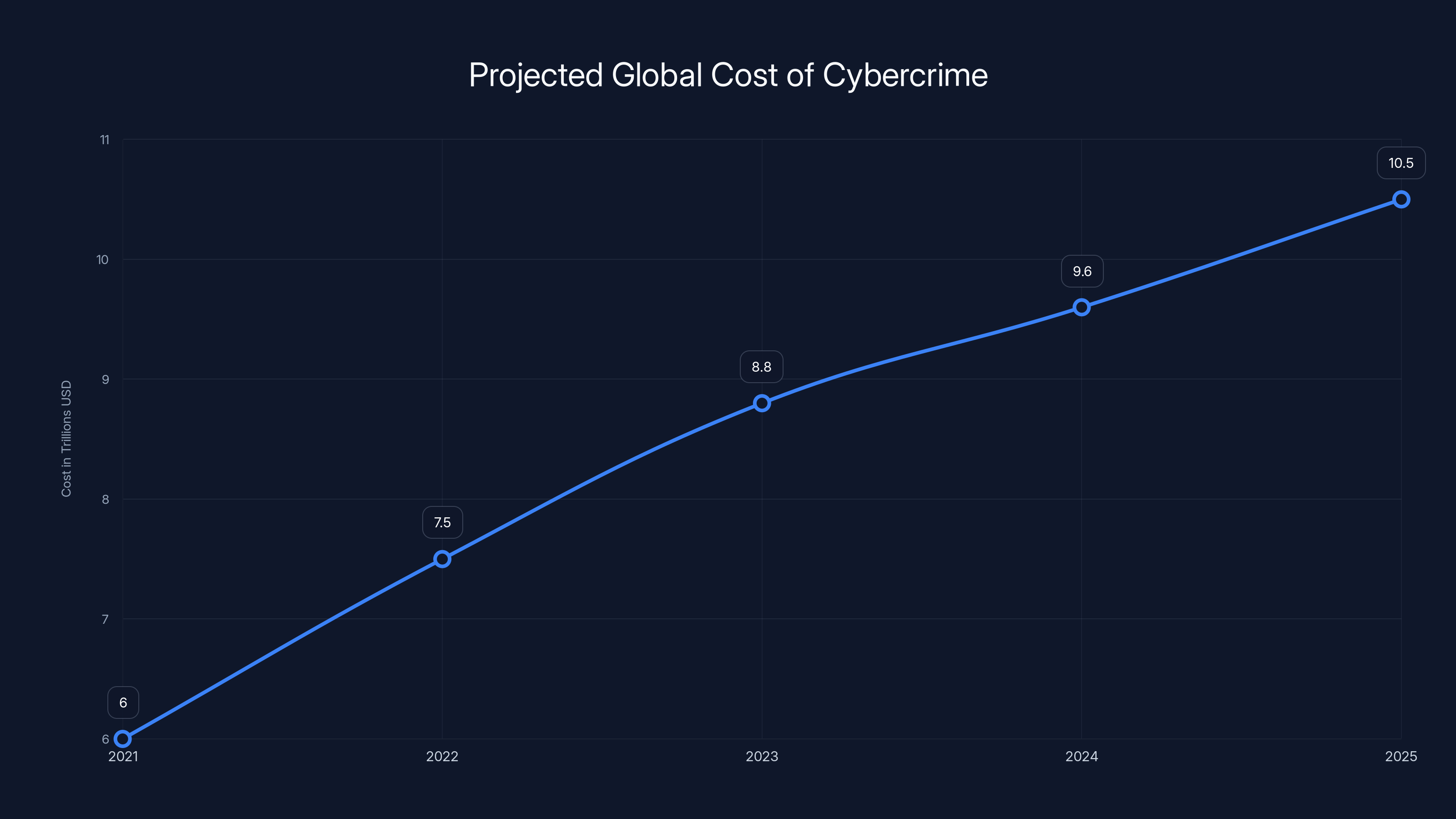
Cybercrime costs are projected to rise significantly, reaching $10.5 trillion by 2025. Estimated data highlights the growing importance of cybersecurity according to Cybersecurity Ventures.
Understanding the Incident
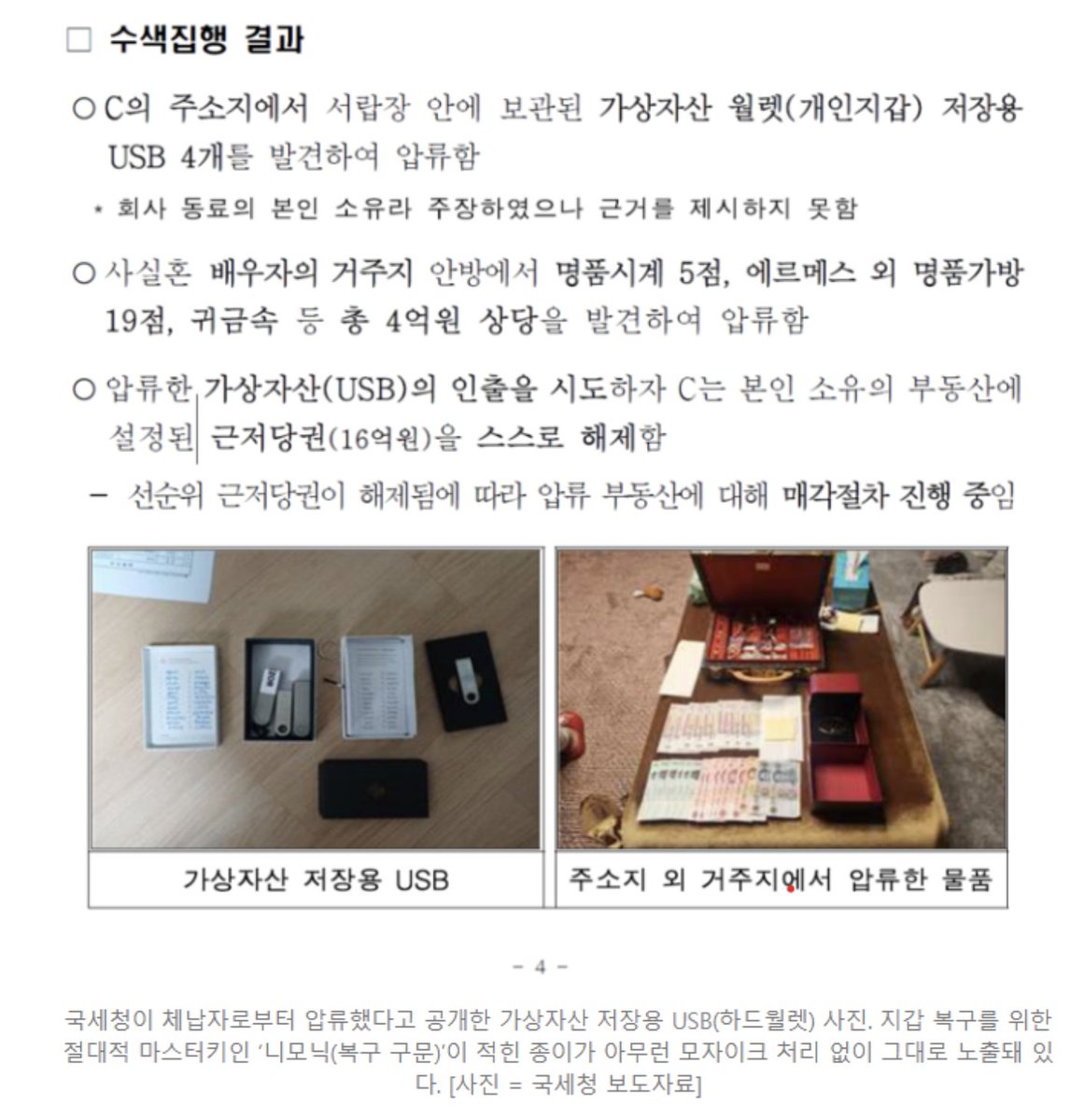
In a surprising turn of events, South Korean authorities lost control of a substantial amount of seized cryptocurrency. The mistake occurred when police unintentionally published images containing sensitive information, including a mnemonic recovery phrase, which allowed unauthorized access to the cold wallet storing the assets as detailed by The Block.
What Happened?
The incident began with a routine press release celebrating the seizure of $5.6 million in cryptocurrency from tax evaders. Unfortunately, the images accompanying the release included a handwritten note displaying the recovery phrase for a Ledger device – a type of cold wallet used to securely store cryptocurrencies offline. This phrase acts as a master key, enabling anyone with access to it to transfer funds from the wallet. The press release was quickly picked up by local media, allowing a thief to act swiftly before the error was corrected as reported by Gizmodo.
Lessons Learned
This debacle highlights the importance of stringent security protocols when handling digital assets. Here are several key takeaways:
- Confidentiality: Sensitive information, like recovery phrases, should never be exposed, even inadvertently.
- Cold Storage Security: While cold wallets offer enhanced security by being offline, they are not immune to human error as noted by CryptoNews.
- Media Scrutiny: Any public disclosure involving digital assets must be meticulously vetted to avoid accidental leaks.

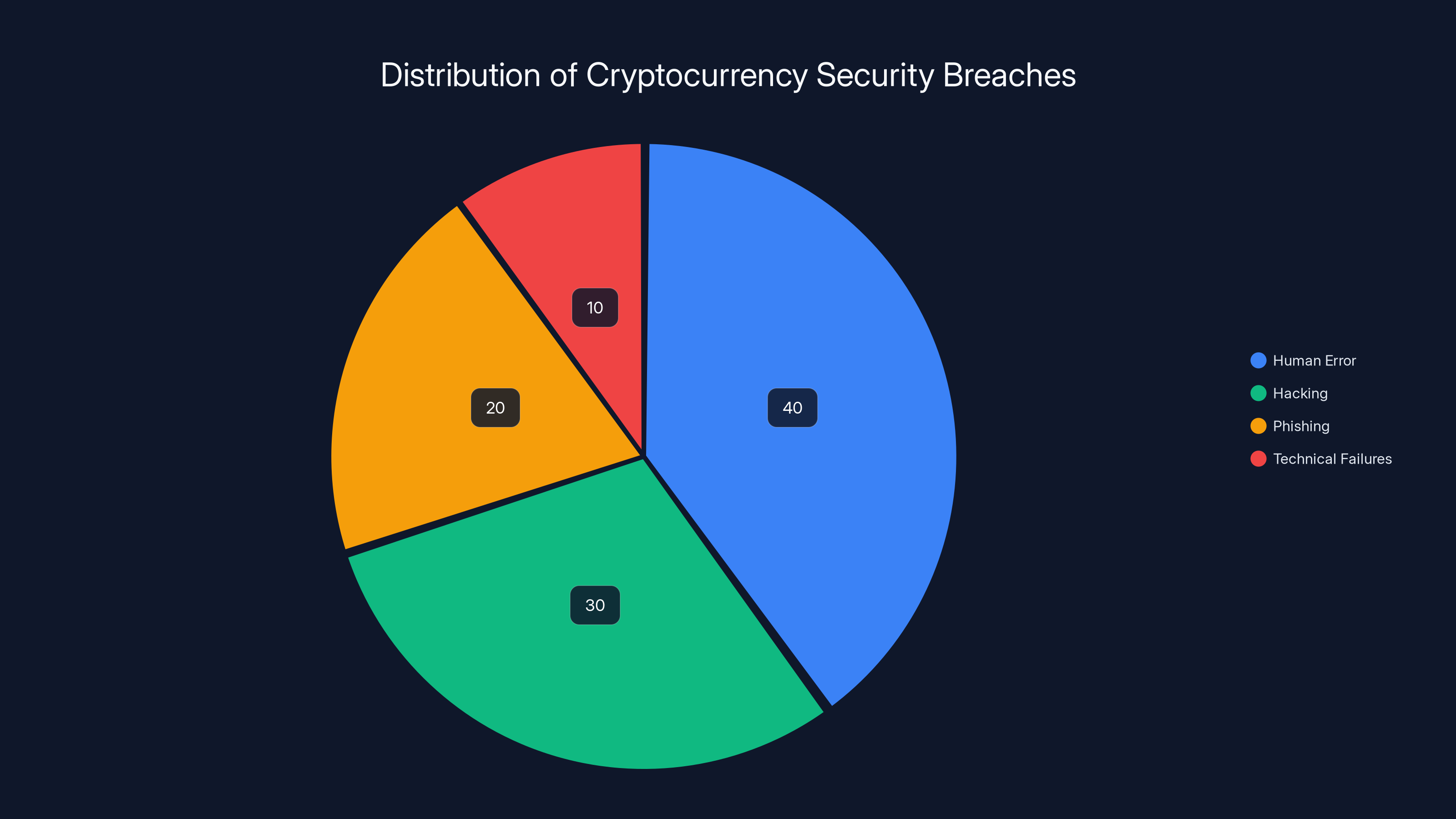
Human error accounts for an estimated 40% of cryptocurrency security breaches, highlighting the need for better training and protocols according to HIPAA Journal.
Securing Your Cryptocurrency: Best Practices
Protecting digital assets requires a multi-faceted approach. Here are some recommended practices to ensure your cryptocurrency holdings remain secure.
Use Cold Wallets
Cold wallets are devices or paper wallets that store cryptocurrencies offline, away from the reach of hackers. They are considered more secure than hot wallets, which are connected to the internet.
Key Features of Cold Wallets:
- Offline Storage: Keeps private keys away from internet-based threats.
- Enhanced Security: Requires physical access to the device for transactions.
- Long-Term Storage: Ideal for holding assets that you do not need to access frequently.
However, as seen in the South Korean incident, cold wallets are not foolproof. Physical security and careful handling of recovery phrases are equally important as explained by Ledger.
Enable Two-Factor Authentication (2FA)
Two-factor authentication adds an extra layer of security, requiring a second form of verification beyond just a password.
Implementation Tips:
- Use authenticator apps instead of SMS for added security.
- Regularly update your authentication methods to the latest standards.
Employ Multi-Signature Wallets
Multi-signature (multi-sig) wallets require multiple private keys to authorize a transaction, reducing the risk of a single point of failure.
Benefits of Multi-Sig Wallets:
- Shared Control: Ideal for organizations, requiring multiple approvals for fund transfers.
- Enhanced Security: Protects against unauthorized access through additional verification layers.

Common Mistakes and How to Avoid Them
Understanding common pitfalls in cryptocurrency management can help you avoid costly errors.
Sharing Private Keys and Recovery Phrases
Never share these sensitive details publicly or store them in easily accessible places. Keep them offline and in secure locations.
Alternative Storage Solutions:
- Use encrypted USB drives for digital storage.
- Consider hardware security modules (HSMs) for larger holdings.
Overreliance on Single Security Measures
Relying solely on one security method, such as passwords, can be risky. Implement multi-layered security measures to protect your assets.
Layered Security Approach:
- Combine cold storage with 2FA and encrypted backups.
- Regularly audit your security setup for potential vulnerabilities.
Ignoring Software Updates
Failing to update wallet software and security protocols can expose you to known vulnerabilities.
Best Practices for Updates:
- Enable automatic updates where possible.
- Follow trusted sources for security patches and updates.

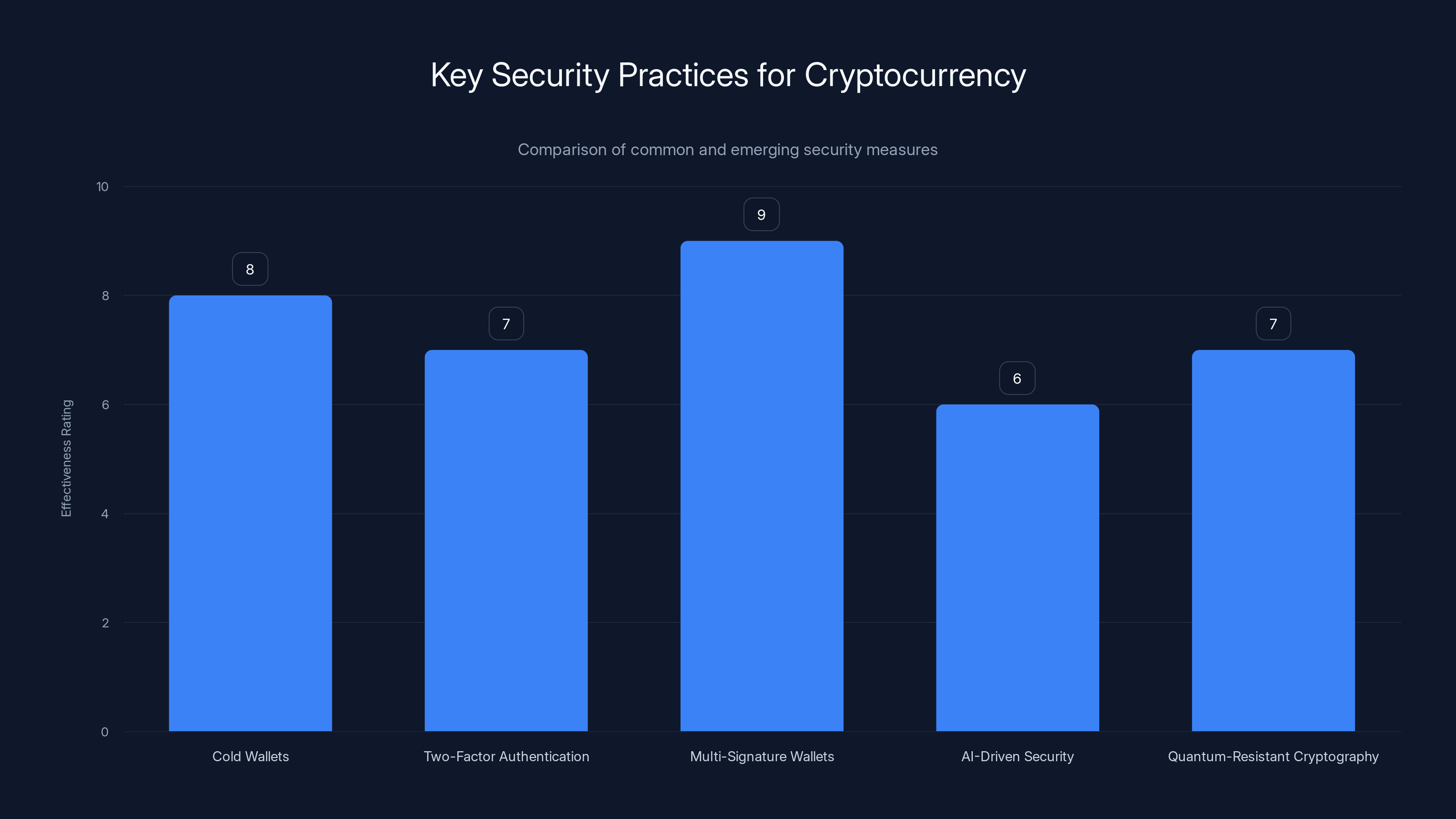
Cold wallets and multi-signature wallets are currently the most effective security measures, while AI-driven and quantum-resistant solutions are emerging trends as noted by Cointelegraph.
Future Trends in Cryptocurrency Security
The landscape of cryptocurrency security is evolving rapidly. Here are some trends to watch:
AI-Driven Security Solutions
Artificial intelligence is being leveraged to detect and prevent fraudulent activities in real-time.
AI Applications:
- Fraud Detection: Identifying unusual transaction patterns and potential threats.
- Automated Alerts: Notifying users of suspicious activities instantly.
Quantum-Resistant Cryptography
With the advent of quantum computing, traditional cryptographic methods could become vulnerable. Quantum-resistant algorithms are being developed to safeguard against potential quantum attacks as discussed by Quantum Zeitgeist.
Quantum Security Measures:
- Post-Quantum Cryptography: Development of algorithms resistant to quantum decryption.
- Hybrid Systems: Combining classical and quantum-resistant cryptographic methods.
Regulatory Developments
As the crypto ecosystem grows, regulatory frameworks are evolving to enhance security and compliance.
Regulatory Focus Areas:
- KYC and AML Compliance: Strengthening identity verification processes.
- Licensing Requirements: Ensuring service providers meet security standards.

Practical Implementation Guide
Securing cryptocurrency involves both technical and practical steps. Here’s a comprehensive guide to keep your digital assets safe.
Step 1: Choose the Right Wallet
Select a wallet that suits your needs, whether for day-to-day transactions or long-term storage.
Wallet Types:
- Hot Wallets: For frequent transactions, connected to the internet.
- Cold Wallets: For long-term storage, kept offline.
Step 2: Backup and Encrypt
Regularly backup your wallet data and encrypt it to prevent unauthorized access.
Backup Strategies:
- Use secure cloud storage with encryption for digital backups.
- Maintain physical copies in secure locations for redundancy.
Step 3: Regular Security Audits
Conduct periodic reviews of your security setup to identify vulnerabilities.
Audit Checklist:
- Verify software updates and patch installations.
- Assess the effectiveness of current security measures.
- Test backup and recovery procedures.
Step 4: Educate and Train
Stay informed about the latest security threats and best practices.
Training Resources:
- Online courses on cybersecurity fundamentals.
- Webinars and workshops on cryptocurrency security.

Common Pitfalls and Solutions
Even seasoned investors can fall victim to security lapses. Here’s how to avoid some common pitfalls:
Pitfall: Phishing Attacks
Solution: Always verify the source of emails and messages before clicking on links or downloading attachments.
Pitfall: Weak Passwords
Solution: Use a password manager to generate and store complex passwords.
Pitfall: Complacency
Solution: Regularly review and update your security measures to adapt to new threats.

Future Predictions and Recommendations
Looking ahead, the future of cryptocurrency security will be shaped by technological advancements and regulatory changes.
Prediction 1: Increased Adoption of Decentralized Security
Decentralized security models will gain traction, reducing reliance on centralized entities.
Prediction 2: Rise of User-Centric Security Solutions
Personalized security solutions will emerge, allowing users to tailor protection to their needs.
Recommendation: Stay Proactive
Continuously monitor the crypto landscape and adapt your security measures to stay ahead of emerging threats.

Conclusion
The South Korean crypto incident underscores the critical importance of robust security practices in the management of digital assets. By implementing best practices, staying informed about emerging trends, and proactively addressing vulnerabilities, individuals and organizations can protect their investments and contribute to a more secure cryptocurrency ecosystem.

Key Takeaways
- Incident highlights critical need for secure handling of digital assets.
- Cold wallets are secure but require careful management of recovery details.
- Emerging trends like AI and quantum cryptography offer new security solutions.
- Regular security audits and multi-layered defenses are essential.
- Future regulatory frameworks will enhance compliance and security.
- Educating users on security best practices is crucial.
Related Articles
- Accidental Hacks: Lessons from the 6,700 Robot Vacuum Incident [2025]
- Sony's $2.7 Billion Antitrust Lawsuit in the UK: Implications and Future Outlook [2025]
- When AI Lies: Navigating the Complexities of Alignment Faking in Autonomous Systems [2025]
- Decoding the Streaming Piracy Dilemma and Its Global Implications [2025]
- Ensuring Secure AI Usage in the Workplace [2025]
- Understanding Oblivion Malware: A New Threat to Android Security [2025]
FAQ
What is How to Secure Cryptocurrency Holdings: Lessons from the South Korean Crypto Incident [2025]?
Last month, a security mishap shook the cryptocurrency world when South Korean police inadvertently leaked a wallet password, resulting in the loss of $5 million in seized assets as reported by Ars Technica.
What does tl; dr mean?
This incident serves as a stark reminder of the vulnerabilities in handling digital currencies, even by official entities as noted by Crowdfund Insider.
Why is How to Secure Cryptocurrency Holdings: Lessons from the South Korean Crypto Incident [2025] important in 2025?
As crypto continues to grow, understanding how to secure these assets is more crucial than ever according to Market.us.
How can I get started with How to Secure Cryptocurrency Holdings: Lessons from the South Korean Crypto Incident [2025]?
- Incident Overview: South Korean police accidentally exposed a wallet password, leading to a $5 million loss as detailed by Bleeping Computer.
What are the key benefits of How to Secure Cryptocurrency Holdings: Lessons from the South Korean Crypto Incident [2025]?
- Security Best Practices: Use cold wallets, enable two-factor authentication, and employ multi-signature wallets as explained by Britannica.
What challenges should I expect?
- Common Mistakes: Avoid sharing private keys and recovery phrases publicly or in unsecured environments as highlighted by Nature.
![How to Secure Cryptocurrency Holdings: Lessons from the South Korean Crypto Incident [2025]](https://tryrunable.com/blog/how-to-secure-cryptocurrency-holdings-lessons-from-the-south/image-1-1772490847012.jpg)



