Accidental Hacks: Lessons from the 6,700 Robot Vacuum Incident [2025]
Last month, a seemingly innocuous discovery by an area man spiraled into a security nightmare involving 6,700 camera-enabled robot vacuums. This incident underscores the urgent need for robust cybersecurity measures in the rapidly expanding world of Internet of Things (IoT) devices. Let's dive deep into this situation to understand what happened, why it matters, and what can be done to prevent future lapses.
TL; DR
- Massive Breach: 6,700 robot vacuums were inadvertently hacked due to insecure network configurations.
- IoT Vulnerabilities: Many smart devices lack basic security features, making them prime targets.
- User Awareness: Users need to be educated about securing their home networks and devices.
- Security Best Practices: Implementing multi-factor authentication and regular firmware updates can mitigate risks.
- Future Trends: IoT security is expected to evolve with AI-driven threat detection.

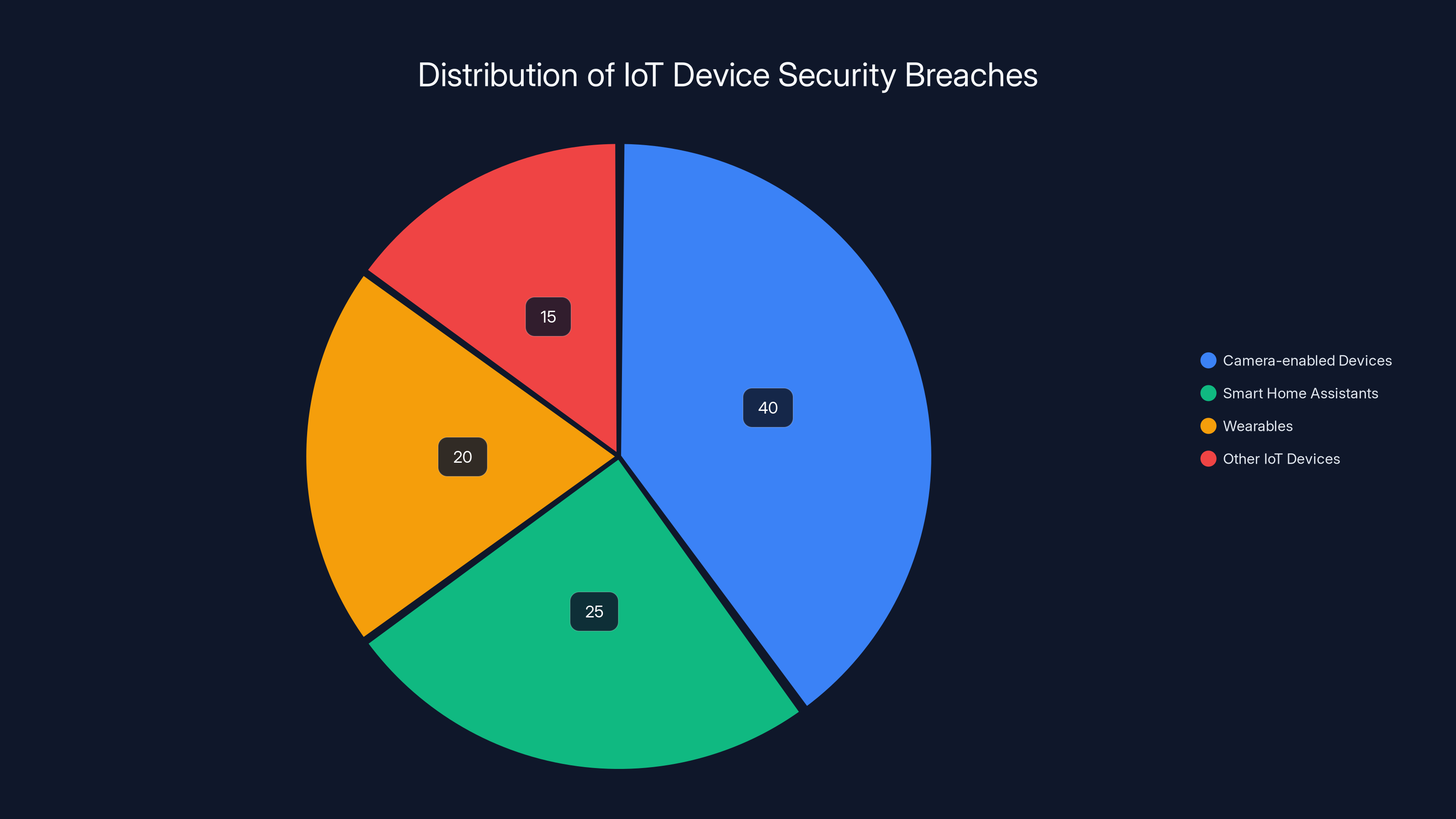
Camera-enabled devices, like robot vacuums, account for 40% of IoT security breaches, highlighting their vulnerability. Estimated data.
The Incident: What Went Wrong?
Here's the thing: a local tech enthusiast accidentally stumbled upon a significant vulnerability in a popular brand of robot vacuums. The root of the issue was a default configuration that left these devices exposed to remote access without authentication. This oversight allowed anyone with basic networking skills to access the cameras embedded within the vacuum cleaners.
How It Happened
The breach was not the result of a sophisticated hacking attempt but rather a consequence of weak security protocols. The vacuums were shipped with a factory setting that enabled remote access capabilities by default. Unfortunately, these settings were not secured with passwords, and the ports remained open to the internet.
Key Points:
- Default settings: Many IoT devices are shipped with default configurations that are insecure.
- Lack of authentication: The absence of password protection enabled unauthorized access.
- Open ports: Ports that were left open allowed external connections without restrictions.
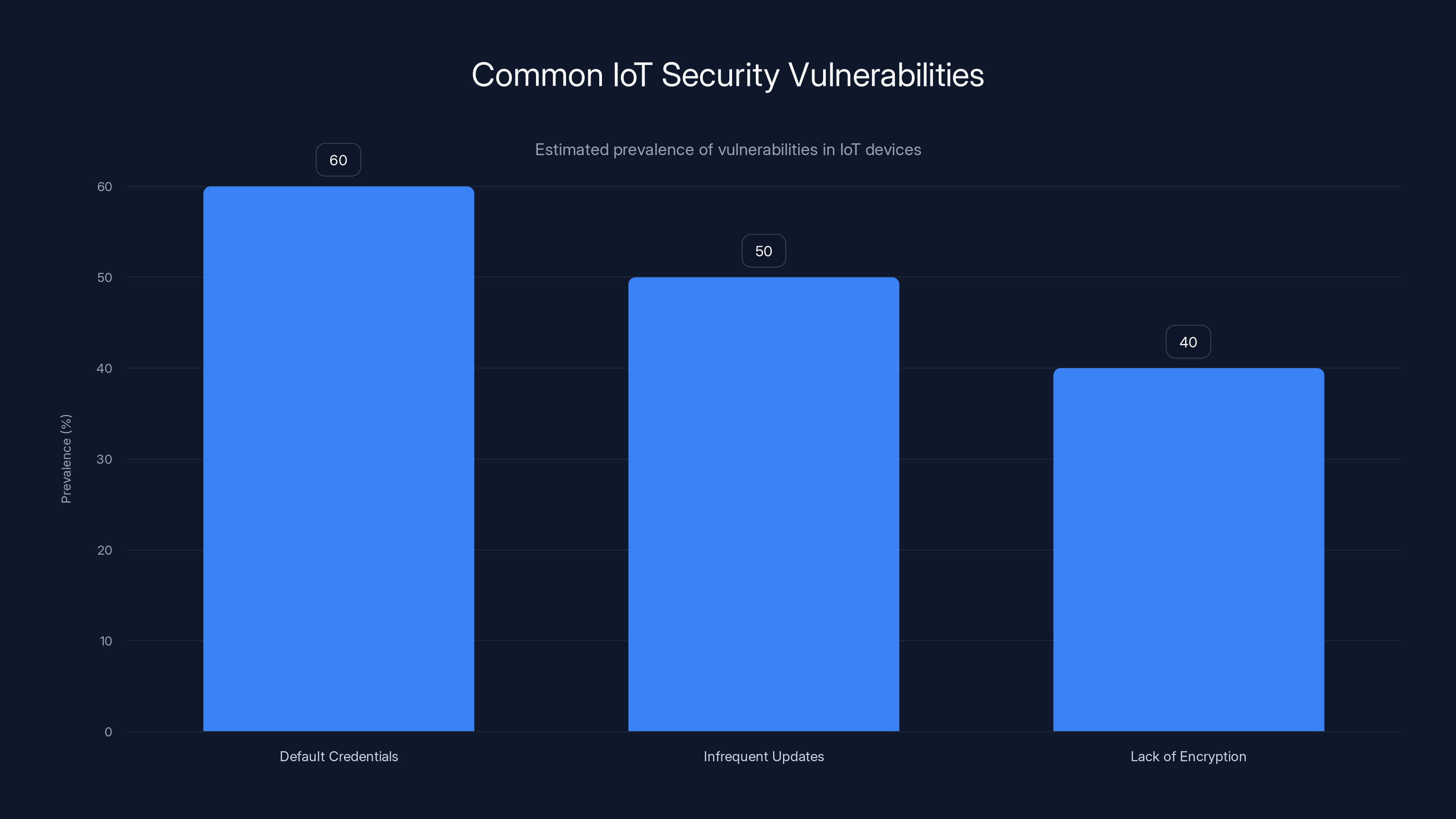
Default credentials are the most common IoT security vulnerability, affecting an estimated 60% of devices. Estimated data.
Understanding IoT Security Risks
The proliferation of IoT devices has led to increased convenience in our daily lives, but it has also introduced new security challenges. These devices often operate on the fringes of our networks and, if not properly secured, can become gateways for cybercriminals.
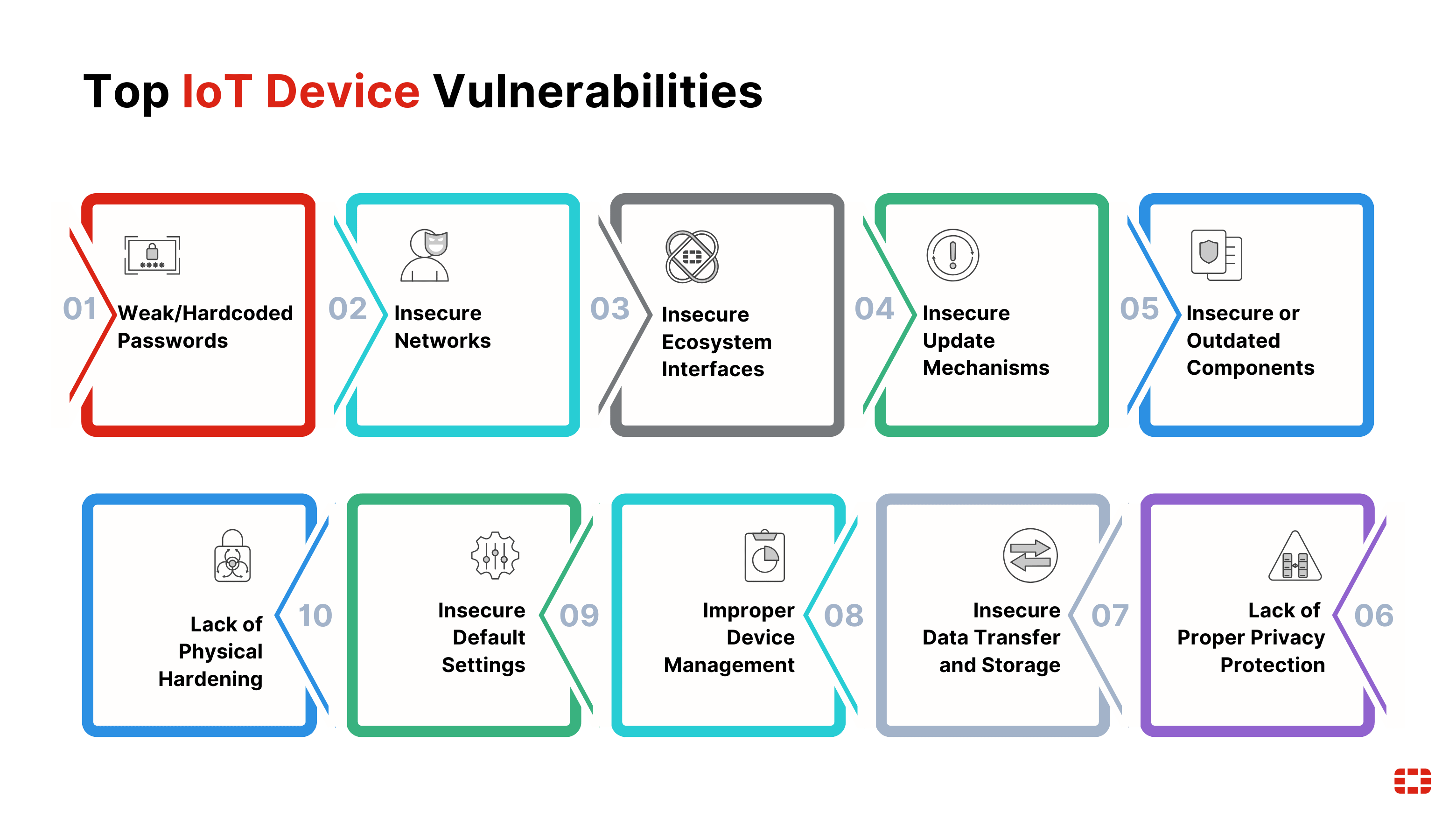
Common Vulnerabilities
- Default Credentials: Many devices come with default usernames and passwords, which are often not changed by users.
- Infrequent Updates: IoT devices may not receive regular security updates, leaving them vulnerable to known exploits.
- Lack of Encryption: Data transmitted by these devices is sometimes not encrypted, making it susceptible to interception.
Practical Implementation Guide for Securing IoT Devices
Securing IoT devices requires a multi-layered approach. Here are some practical steps you can take to enhance the security of your smart home ecosystem:
- Change Default Settings: Begin by updating default usernames and passwords to something unique and complex.
- Network Segmentation: Use a dedicated network for IoT devices separate from your primary network to contain potential breaches.
- Regular Firmware Updates: Ensure that all devices are running the latest firmware to protect against vulnerabilities.
- Enable Firewalls: Use firewalls to block unauthorized access to and from your IoT devices.
- Monitor Network Traffic: Keep an eye on the traffic to and from your devices to detect any unusual activity.

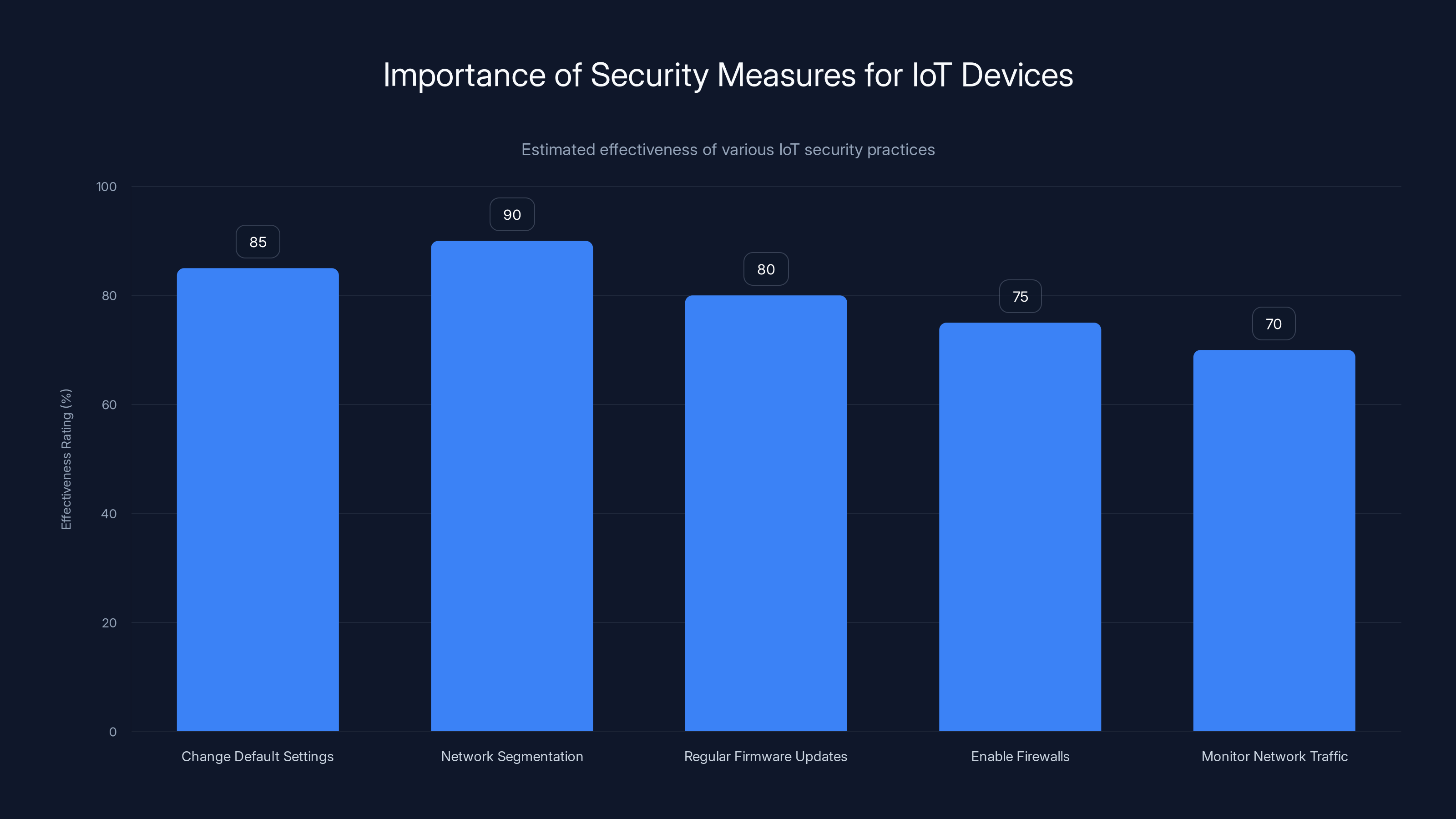
Network segmentation and changing default settings are highly effective in securing IoT devices. Estimated data based on typical security assessments.
Case Study: The Consequences of Neglect
Consider a smart home system where the owner failed to update the firmware on their smart thermostat. A known vulnerability allowed a hacker to gain access to the home network, eventually leading to a breach of the homeowner's personal data. This case highlights the importance of keeping all devices up-to-date.
Lessons Learned:
- Ignoring firmware updates can lead to severe consequences.
- Regular maintenance of IoT devices is critical to security.
Common Pitfalls and How to Avoid Them
Overlooking Firmware Updates
One of the most common mistakes users make is neglecting to update the firmware of their IoT devices. These updates often contain critical security patches that address vulnerabilities discovered after the device was released.
Solution: Set devices to auto-update or regularly check for updates manually.
Neglecting Network Security
Many users fail to secure their home networks adequately, leaving them open to attacks that target connected devices.
Solution: Use strong, unique passwords for your Wi-Fi network and enable WPA3 encryption if available.
Ignoring Security Features
Some IoT devices come with built-in security features that are disabled by default. Users may not be aware of these features or may not take the time to enable them.
Solution: Review the security settings of each device and enable features like two-factor authentication and network access controls.

Future Trends in IoT Security
As IoT devices become more prevalent, the need for enhanced security measures will grow. Here are some trends to watch:
- AI-Driven Security: Artificial intelligence will play a significant role in identifying and mitigating threats in real-time.
- Blockchain for IoT: Blockchain technology could be used to secure data transactions and ensure device integrity.
- Regulatory Changes: Governments may introduce more stringent regulations around IoT security standards.

Recommendations for Manufacturers
Manufacturers play a crucial role in ensuring the security of IoT devices. Here are some best practices they should adopt:
- Secure by Design: Develop devices with built-in security features that are enabled by default.
- User Education: Provide clear instructions and resources to help users secure their devices.
- Regular Security Audits: Conduct regular security assessments to identify and fix vulnerabilities.
Conclusion
The accidental hacking of 6,700 robot vacuums serves as a stark reminder of the importance of IoT security. By understanding the risks, implementing best practices, and staying informed about emerging trends, users and manufacturers alike can help prevent future incidents.
For those looking to enhance their smart home security, tools like Runable offer AI-powered automation solutions that can streamline the process of securing and managing IoT devices.
FAQ
What is IoT?
The Internet of Things (IoT) refers to the network of physical devices connected to the internet, capable of collecting and sharing data.
How can I secure my IoT devices?
Secure your devices by changing default passwords, enabling encryption, and segmenting your network.
Why are IoT devices vulnerable?
IoT devices are often vulnerable due to default credentials, infrequent updates, and lack of encryption.
What should manufacturers do to improve IoT security?
Manufacturers should design devices with security in mind, educate users, and conduct regular security audits.
What are future trends in IoT security?
Future trends include AI-driven threat detection, blockchain for device integrity, and increased regulatory oversight.

Key Takeaways
- IoT devices often ship with insecure default settings, posing security risks.
- Regular firmware updates are critical for maintaining device security.
- Network segmentation can limit the impact of potential security breaches.
- AI and blockchain are emerging as key technologies in IoT security.
- User education and awareness are vital for securing smart home devices.
Related Articles
- Understanding the Impact of Data Broker Breaches on Identity Theft [2025]
- How Secure Is Your Home Wi-Fi, Really? [2025]
- The Week in Tech: Seven Game-Changing Stories You Need to Know [2025]
- Quantum-Proofing the Web: Google's Mathematical Approach to Securing HTTPS [2025]
- 18 Best Wireless Chargers, All Tested and Reviewed [2026]
- Beware of Google Tasks Scams: Protect Your Workplace from Phishing Attacks [2025]
![Accidental Hacks: Lessons from the 6,700 Robot Vacuum Incident [2025]](https://tryrunable.com/blog/accidental-hacks-lessons-from-the-6-700-robot-vacuum-inciden/image-1-1772280227072.jpg)



