Understanding Oblivion Malware: A New Threat to Android Security [2025]
Last week, cybersecurity researchers uncovered a new player in the Android malware arena: Oblivion. This Remote Access Trojan (RAT) is not just another name in the long list of mobile threats. It leverages Android's Accessibility Service to bypass security measures that even seasoned tech enthusiasts rely on. In this comprehensive guide, we'll break down how Oblivion works, its implications, and the best practices to safeguard your device against such threats.
TL; DR
- Oblivion targets Android devices using the Accessibility Service, granting attackers full control. According to TechRadar, this malware exploits permissions to gain unauthorized access.
- The malware can intercept SMS, notifications, and authentication codes without alerting users. CyberPress reports that Oblivion can manipulate notifications stealthily.
- It uses remote control for concealed access, often employing fake overlays to trick users. This technique is detailed in Rescana's analysis.
- Oblivion operates on a subscription basis, making it accessible to a wider audience of cybercriminals. The subscription model is highlighted in CyberPress.
- Staying updated on security patches and understanding app permissions are crucial defense strategies. PCMag emphasizes the importance of regular updates for security.

What is Oblivion Malware?
Oblivion is an advanced Android malware that functions as a Remote Access Trojan (RAT). Unlike typical malware, which might require user interaction to activate, Oblivion exploits Android's Accessibility Service to gain control over devices without user consent. TechRadar provides a detailed overview of its capabilities.
How It Works
The malware capitalizes on the Accessibility Service, a feature designed to help users with disabilities interact with their devices. It manipulates this service to bypass security measures, granting attackers access to perform any action a legitimate user could do. This includes intercepting SMS, manipulating notifications, and capturing two-factor authentication (2FA) codes as noted by CyberPress.
Key Features
- Remote Device Control: Oblivion can remotely control an infected device, enabling attackers to execute commands, access personal data, and manipulate settings.
- Silent Operations: The malware operates stealthily, using fake overlays to mask its activities and trick users into believing everything is normal.
- Subscription Model: Sold on a subscription basis starting at $300, Oblivion is accessible to a broad range of cybercriminals, lowering the barrier to entry for malicious activities. This pricing model is discussed in CyberPress.
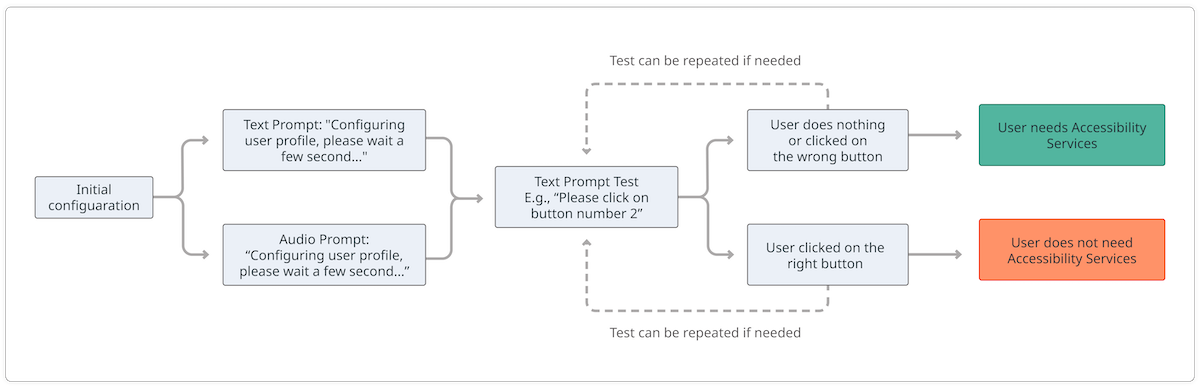
Technical Breakdown: Exploiting the Accessibility Service
The Accessibility Service is a double-edged sword in Android devices. While it enhances usability for individuals with disabilities, it also opens doors for potential exploitation.
Attack Vector
Oblivion malware exploits permissions granted to the Accessibility Service, allowing it to:
- Read and interact with UI elements: This enables the malware to intercept sensitive information displayed on the screen.
- Perform gestures: Attackers can simulate taps and swipes, effectively controlling the device.
- Capture sensitive data: With access to the screen and input, the malware can capture passwords and authentication codes. These capabilities are explored in TechRadar.
Code Example
javaAccessibility Service Info info = new Accessibility Service Info();
info.event Types = Accessibility Event. TYPES_ALL_MASK;
info.feedback Type = Accessibility Service Info. FEEDBACK_SPOKEN;
info.flags = Accessibility Service Info. FLAG_REPORT_VIEW_IDS;
info.notification Timeout = 100;
this.set Service Info(info);
This code snippet represents the setup of an Accessibility Service in Android, which can be manipulated by malware for unauthorized access.
Common Pitfalls and Solutions
Pitfalls
- Ignoring App Permissions: Many users grant app permissions without understanding the potential risks, enabling malware like Oblivion to exploit these permissions.
- Delayed Security Updates: Users often postpone installing security updates, leaving their devices vulnerable to known exploits.
- Unverified App Sources: Downloading apps from unofficial sources increases the risk of installing malicious software. CyberPress highlights the dangers of unverified sources.
Solutions
- Review App Permissions: Regularly check the permissions granted to apps and revoke any unnecessary access.
- Install Updates Promptly: Keep your device updated with the latest security patches.
- Use Official App Stores: Only download apps from trusted sources like the Google Play Store, as recommended by PCMag.
Real-World Use Cases
Case Study: A Corporate Espionage Scenario
Imagine a corporate executive installs an app from an unverified source. Unknown to them, the app is infected with Oblivion. The attacker gains access to sensitive company emails, financial data, and strategic plans. The damage? Irreparable.
Personal Device Hijacking
A user downloads a seemingly innocuous game from a third-party website. Oblivion silently installs, and the attacker gains access to personal photos, messages, and banking apps. The user notices nothing amiss until it's too late.

Best Practices for Protection
Device Settings
- Disable Unnecessary Services: Limit the use of Accessibility Service to apps that genuinely need it.
- Enable Two-Factor Authentication: Use 2FA for sensitive accounts to add an extra layer of security.
Behavioral Changes
- Be Cautious with Links: Avoid clicking on suspicious links in emails or messages.
- Educate Yourself: Stay informed about the latest cybersecurity threats and how to counter them.

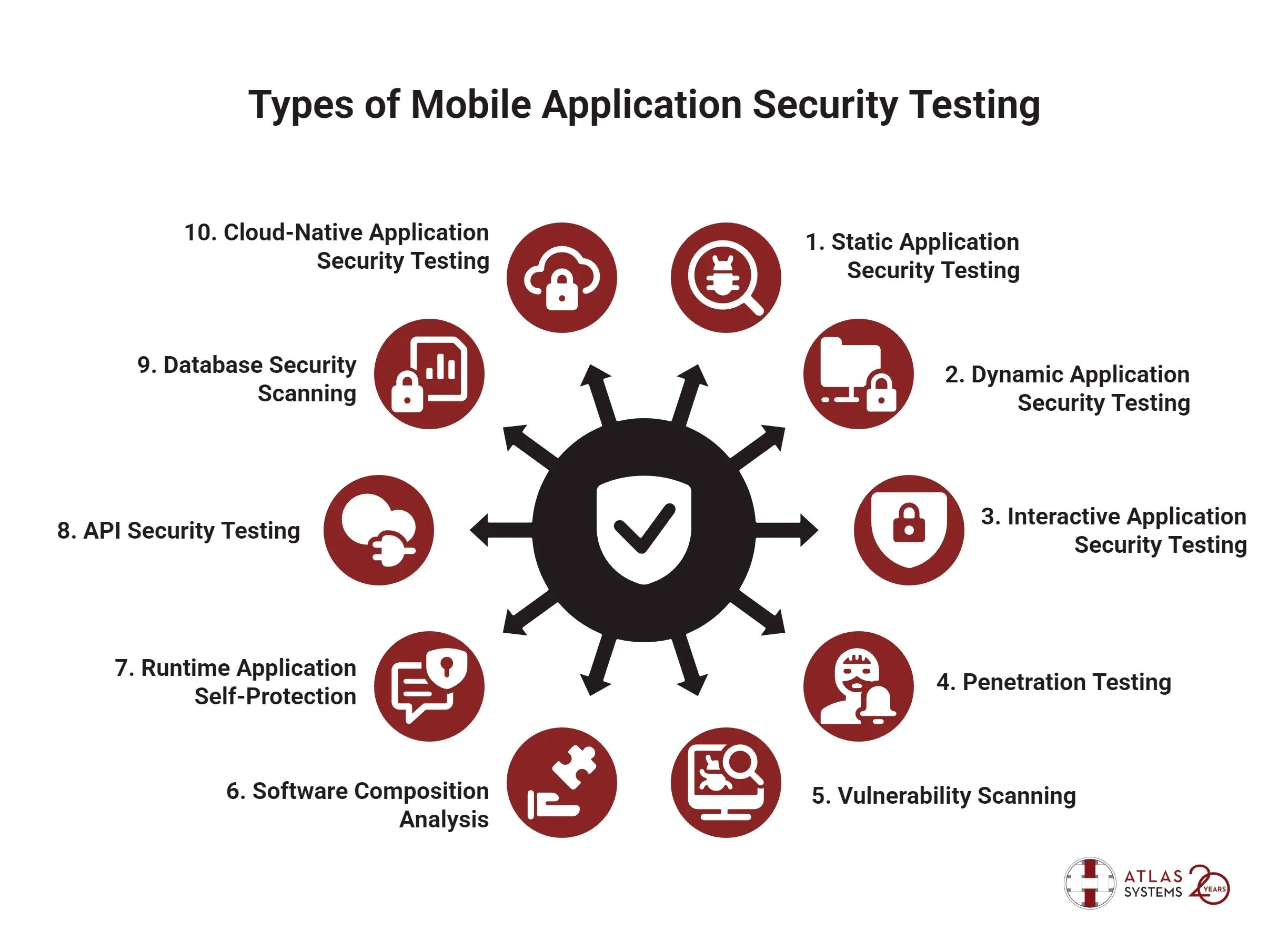
The Future of Android Security
As Android continues to evolve, so do the threats against it. Malware developers are becoming increasingly sophisticated, creating tools like Oblivion that exploit system features designed for accessibility and convenience.
Emerging Trends
- AI-Powered Security: Future security solutions will likely incorporate artificial intelligence to detect and respond to threats in real-time.
- User Education: As threats evolve, so must user awareness and education efforts.
Recommendations
- Invest in Reliable Security Software: Use reputable antivirus and anti-malware solutions to protect your device.
- Participate in Security Forums: Engage with online communities to stay updated on the latest threats and defenses.
Conclusion
Oblivion represents a significant threat to Android security, but understanding how it operates and implementing best practices can mitigate its risks. Staying informed and proactive in your device security efforts is key to protecting your personal and professional data.
FAQ
What is Oblivion malware?
Oblivion is a sophisticated Android Remote Access Trojan (RAT) that exploits the Accessibility Service to gain unauthorized control over devices, allowing attackers to intercept data and manipulate settings.
How does Oblivion malware work?
The malware uses the permissions granted to the Accessibility Service to perform actions on behalf of the user, such as intercepting SMS and manipulating notifications without alerting the user.
What are the benefits of understanding malware threats?
Understanding malware threats like Oblivion helps users implement preventive measures, ensuring their devices and data remain secure from unauthorized access and exploitation.
How can I protect my Android device from malware?
Regularly update your device's software, review app permissions, and only download apps from official sources to reduce the risk of malware infections.
What should I do if I suspect my device is infected?
If you suspect your device is infected, run a full scan using a reputable antivirus app, review recent app installations, and consider resetting your device to factory settings if necessary.
Are all Android devices vulnerable to Oblivion?
Oblivion targets devices running Android versions 8 through 16, which includes a wide range of popular devices. Staying updated on security patches can help protect against such threats.
Key Takeaways
- Oblivion malware exploits Android's Accessibility Service to gain full device control.
- It operates silently, intercepting SMS, notifications, and 2FA codes.
- The malware's subscription model makes it accessible to many cybercriminals.
- Regular software updates and cautious app permissions are vital defenses.
- User education and AI-powered security solutions are crucial for future protection.
The Best Security Practices at a Glance
| Practice | Description | Importance |
|---|---|---|
| Software Updates | Regularly update device software | Essential for patching vulnerabilities |
| App Permissions | Review and limit app permissions | Prevents unauthorized access |
| Use Official Stores | Download apps from trusted sources | Reduces risk of malware installation |
| Antivirus Software | Use reputable security software | Detects and removes threats |
Quick Navigation:
- Understanding Oblivion Malware
- Technical Breakdown
- Common Pitfalls and Solutions
- Real-World Use Cases
- Best Practices for Protection
- The Future of Android Security
- FAQ
By staying informed and implementing these strategies, you can effectively protect your Android device from the emerging threat of Oblivion malware and similar threats in the future.
Related Articles
- Hacked Prayer App Sends ‘Surrender’ Messages to Iranians Amid Israeli and US Strikes | WIRED
- Accidental Hacks: Lessons from the 6,700 Robot Vacuum Incident [2025]
- The Week in Tech: Seven Game-Changing Stories You Need to Know [2025]
- Quantum-Proofing the Web: Google's Mathematical Approach to Securing HTTPS [2025]
- Beware of Google Tasks Scams: Protect Your Workplace from Phishing Attacks [2025]
- AI vs. the Pentagon: Killer Robots, Mass Surveillance, and Red Lines [2025]
![Understanding Oblivion Malware: A New Threat to Android Security [2025]](https://tryrunable.com/blog/understanding-oblivion-malware-a-new-threat-to-android-secur/image-1-1772309050054.jpg)



