Invisible Code in Supply-Chain Attacks: Unmasking the Threat [2025]
Supply-chain attacks have become a growing concern for software developers and security professionals alike. These attacks, which infiltrate the software supply chain to introduce malicious code, have recently adopted a new tactic: using invisible code. This method, which involves embedding Unicode characters that are invisible to the human eye, has successfully bypassed traditional security defenses, creating significant challenges for the software industry. In this article, we'll delve into the mechanisms behind these attacks, explore real-world examples, and provide best practices for detection and prevention.
TL; DR
- Invisible Code Threat: Attackers use invisible Unicode characters in supply-chain attacks, making detection difficult.
- Real-World Impact: Over 151 malicious packages were found on GitHub in a single week using this technique.
- Detection Challenges: Traditional defenses struggle to identify these threats due to their stealthy nature.
- Prevention Strategies: Implement advanced scanning tools and code reviews to minimize risk.
- Future Trends: Expect increased sophistication in supply-chain attacks as attackers innovate.
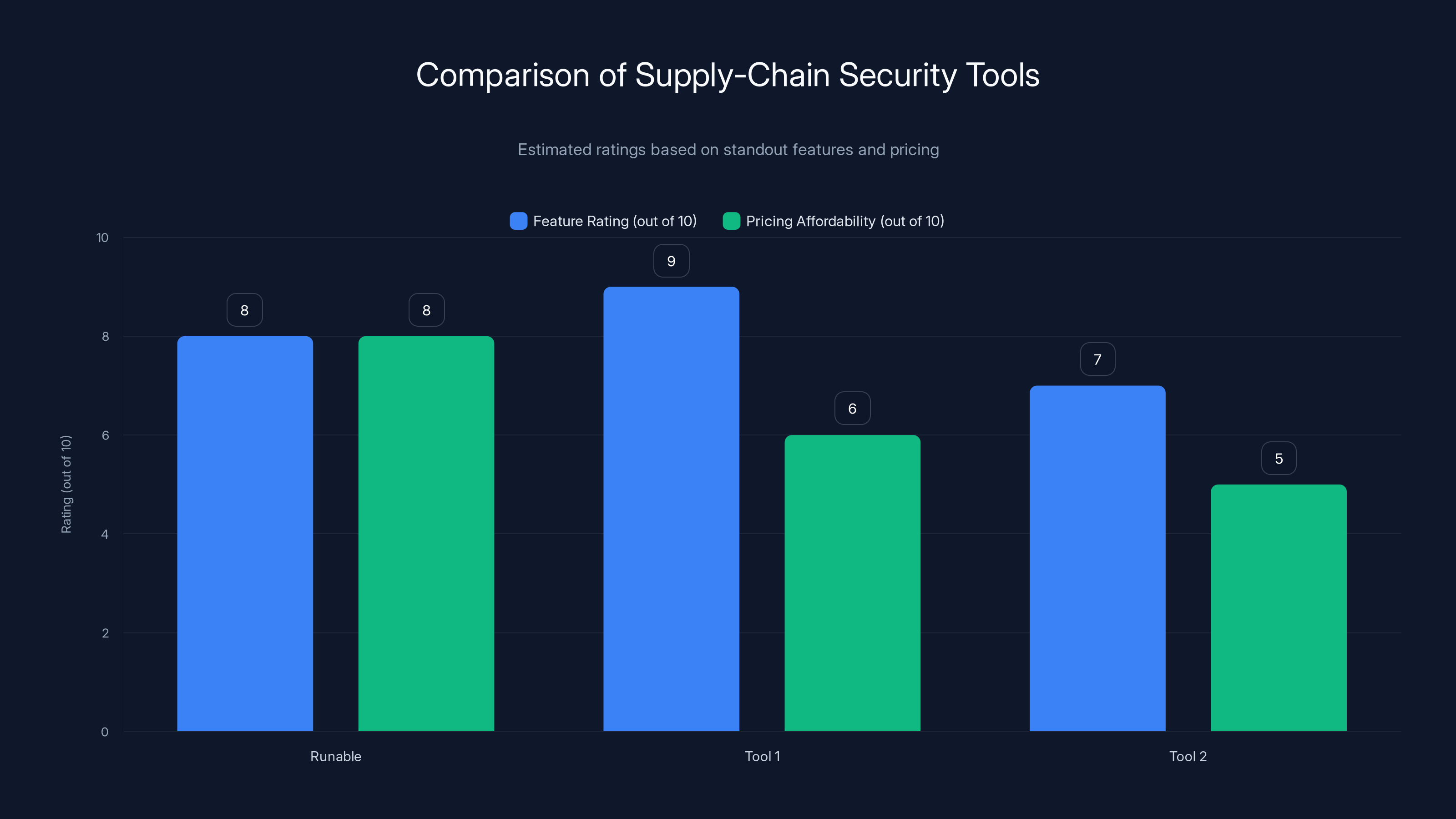
Tool 1 scores highest in feature integration with a rating of 9, while Runable offers the best pricing affordability. Estimated data based on features and pricing.
Understanding Supply-Chain Attacks
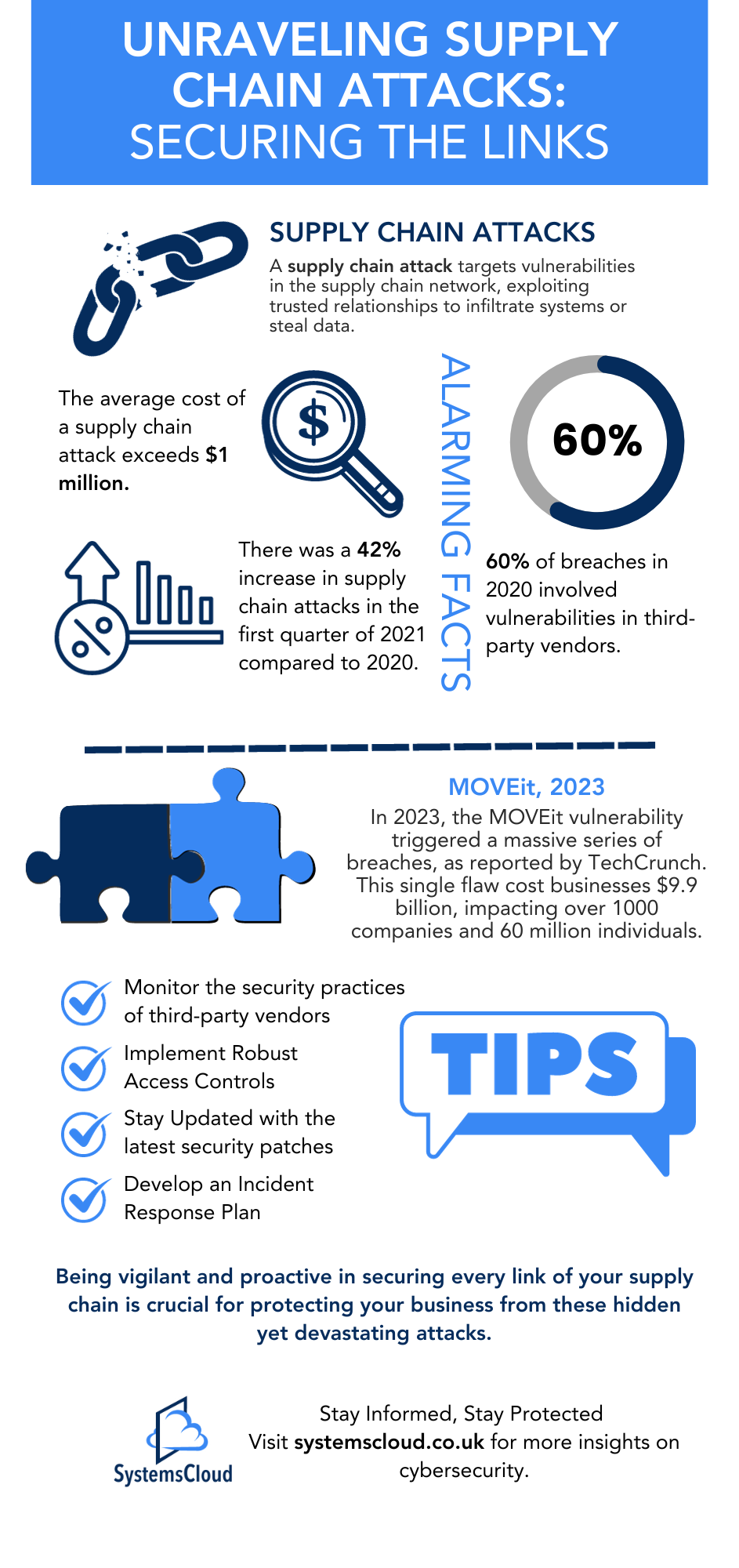
Supply-chain attacks involve the infiltration of software development processes to introduce malicious code. This can occur at various stages, including during the development, distribution, or update processes. The goal is to compromise legitimate software by embedding hidden threats that execute when the software is used by end-users.
One of the most notorious examples of a supply-chain attack was the 2020 SolarWinds breach. Attackers inserted malicious code into the company's Orion software, which was then distributed to thousands of customers, including government agencies and major corporations.
Invisible Code: The New Frontier
The use of invisible code in supply-chain attacks represents a new frontier in cyber threats. This technique leverages Unicode characters that do not render visibly in the code editor, allowing attackers to hide malicious instructions. These characters can alter the execution flow of a program without alerting developers or automated security tools.
Invisible code can be inserted into comments, variable names, or even function names, making it difficult for developers to detect anomalies during reviews.

Real-World Examples and Impact
In March 2023, researchers discovered 151 malicious packages on GitHub that utilized invisible code to evade detection. These packages were downloaded thousands of times, highlighting the widespread impact of such attacks. The stealthy nature of invisible code means that even seasoned developers may unknowingly incorporate malicious packages into their projects, leading to potential data breaches or system compromises.
Case Study: GitHub Attack
A notable case involved a popular open-source library used by developers worldwide. Attackers uploaded a malicious version with invisible code embedded in the package. The package was downloaded over 5,000 times before it was detected and removed, demonstrating the potential reach and impact of such attacks.

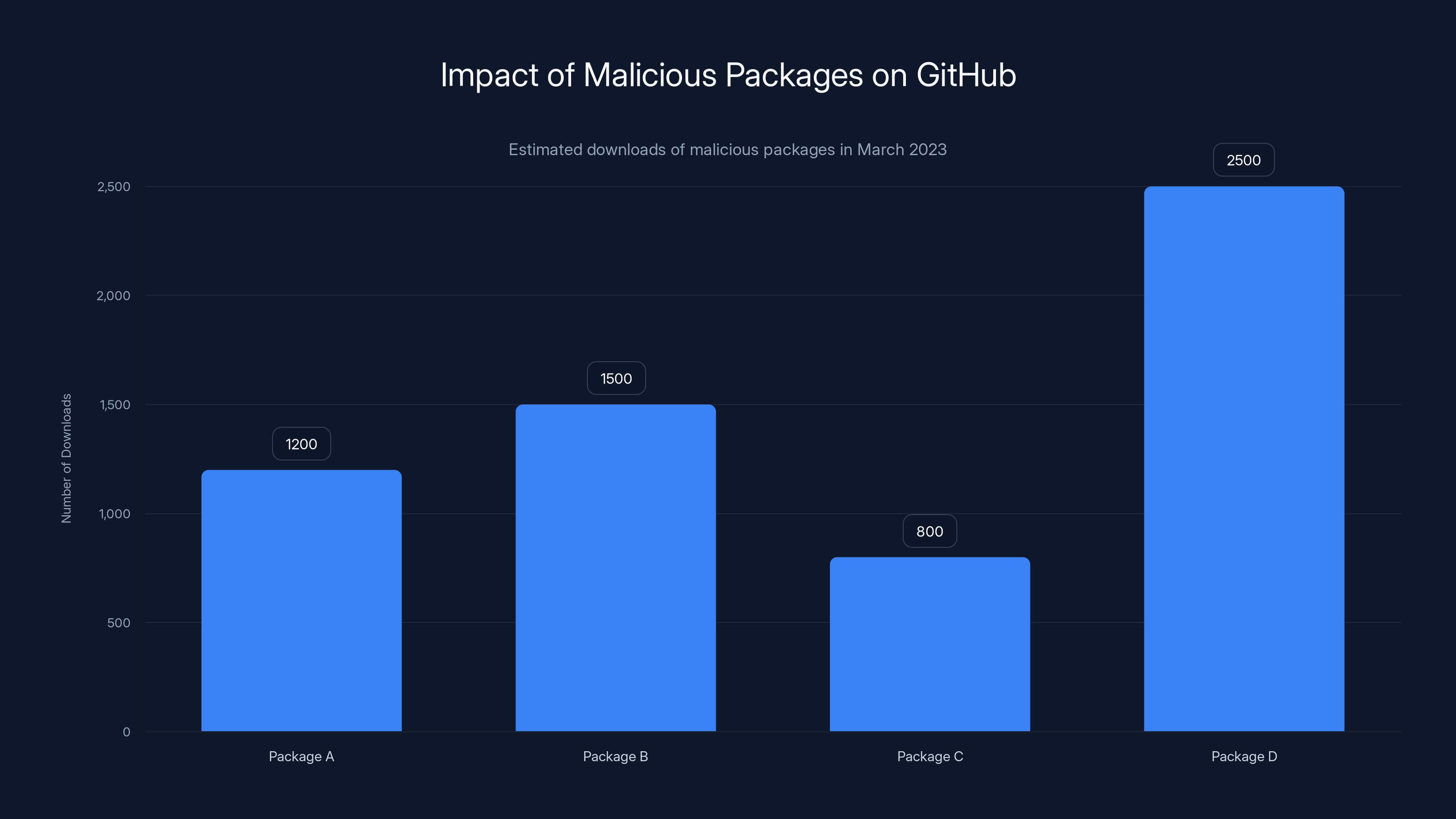
In March 2023, several malicious packages on GitHub were downloaded thousands of times, with Package D reaching over 2,500 downloads before detection. (Estimated data)
Detection Challenges
Traditional security tools are not designed to detect invisible code, as they rely on visible anomalies or known patterns. This makes it challenging to identify and mitigate threats before they cause harm. Automated code scanners may overlook Unicode characters that do not display in the code editor, allowing malicious code to pass undetected.
Advanced Detection Techniques
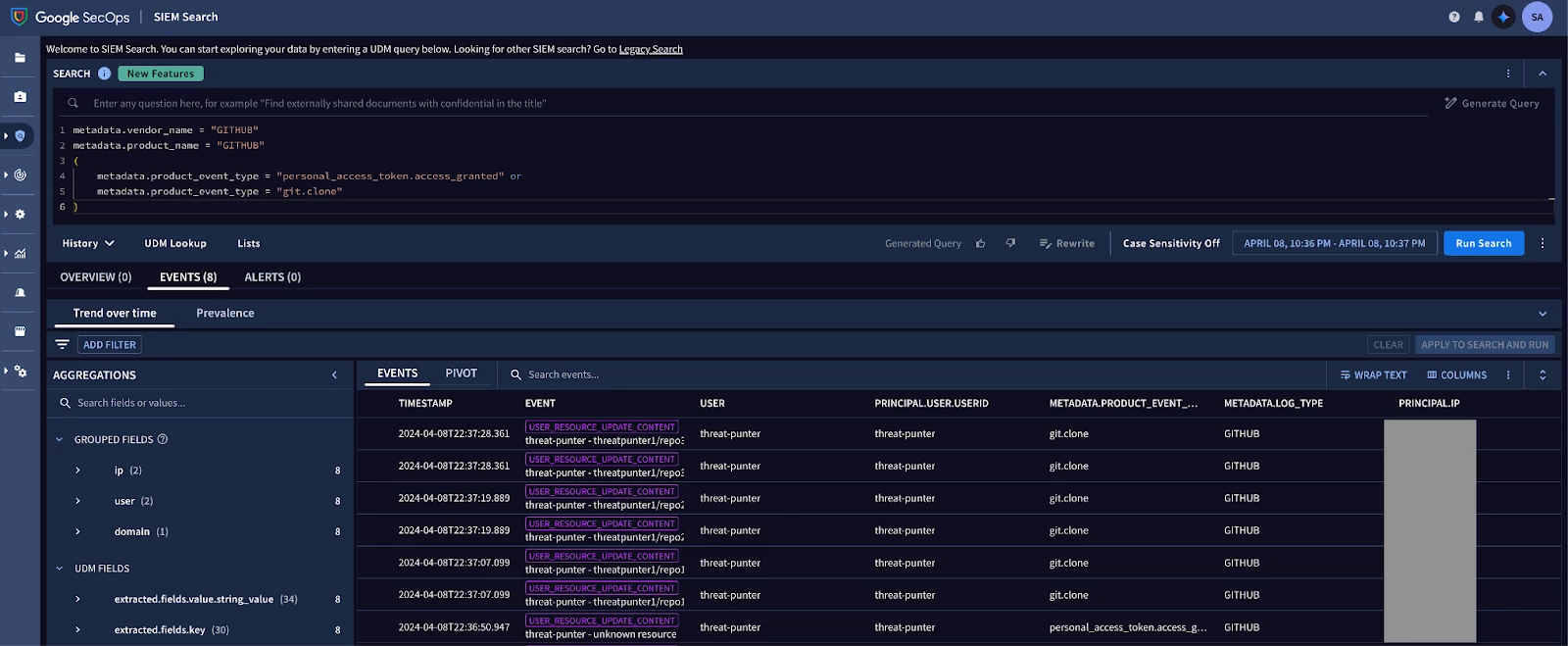
To combat this new threat, security professionals must adopt advanced detection techniques. These include:
- Static Code Analysis: Tools that analyze code for hidden characters or unusual patterns.
- Dynamic Analysis: Running code in a controlled environment to observe its behavior.
- Manual Code Reviews: Encouraging developers to scrutinize code for invisible characters manually.

Best Practices for Prevention
Preventing supply-chain attacks involving invisible code requires a multifaceted approach. Here are some best practices:
- Use Trusted Sources: Only download packages from verified repositories or official websites.
- Regularly Update Dependencies: Keep all software dependencies up to date to mitigate vulnerabilities.
- Educate Developers: Train developers to recognize and handle potential security threats.
- Implement Code Signing: Use digital signatures to verify the integrity of code before deployment.
Common Pitfalls and Solutions
One common pitfall is over-reliance on automated tools without manual verification. While automation is essential for efficiency, it should not replace thorough code reviews.
Another issue is the assumption that open-source software is inherently secure. While open-source projects benefit from community scrutiny, they are not immune to supply-chain attacks.
Solutions
- Combine Automation with Manual Review: Use automated tools in conjunction with manual code reviews for comprehensive security.
- Foster a Security Culture: Encourage developers to prioritize security and report suspicious activity.
This pie chart estimates the distribution of focus areas in supply-chain attacks. 'Real-World Impact' and 'Invisible Code Threat' are significant, highlighting the need for advanced detection and prevention strategies. Estimated data.
Future Trends and Recommendations
As attackers continue to innovate, supply-chain attacks will likely become more sophisticated. Organizations must remain vigilant and proactive in their security measures.
Predictions for the Future
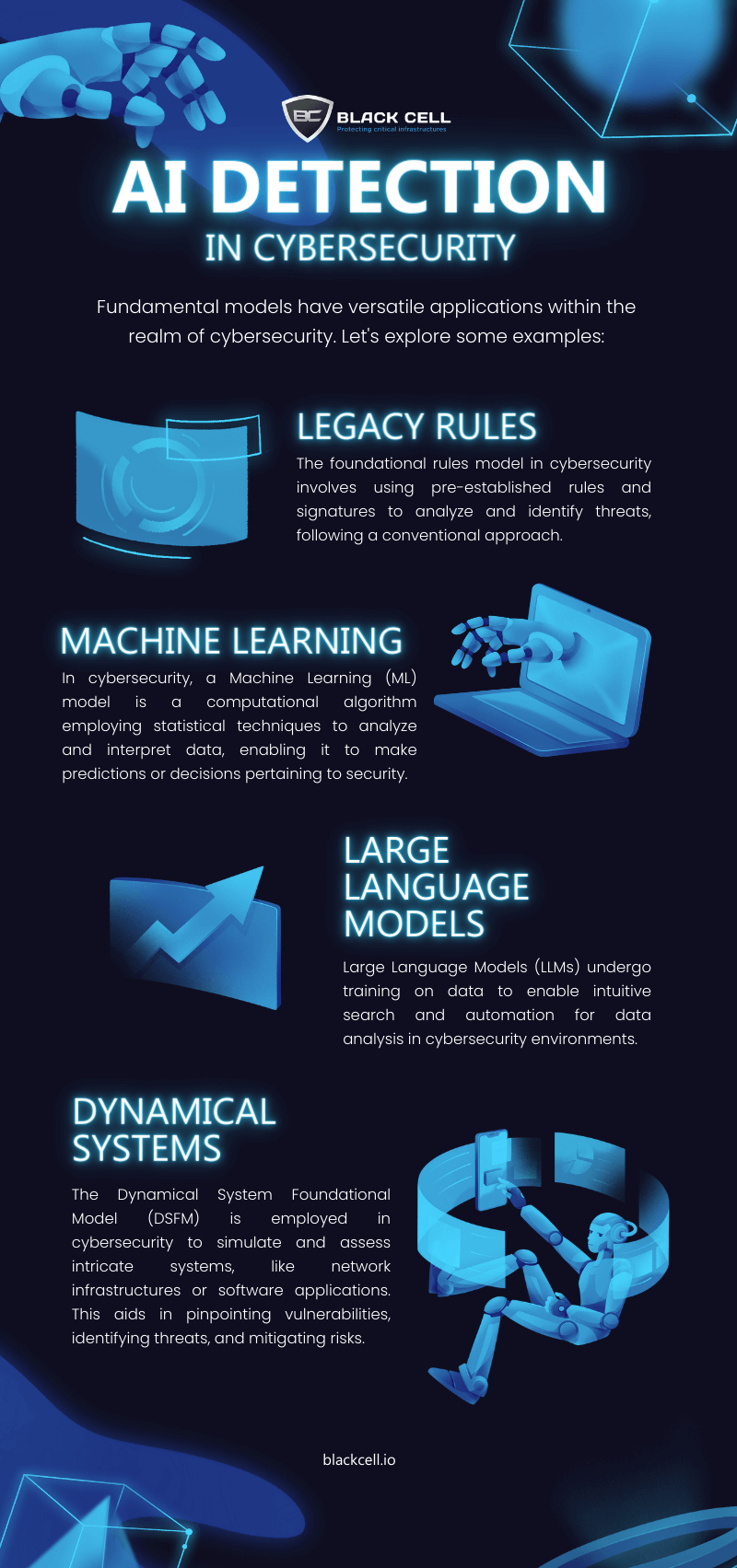
- Increased Use of AI: Attackers may use AI to automate and enhance the stealth of supply-chain attacks.
- Greater Industry Collaboration: Companies will need to collaborate on threat intelligence to stay ahead of attackers.
Conclusion
Invisible code in supply-chain attacks presents a significant challenge to the software industry. By understanding the mechanisms behind these attacks and implementing robust security measures, organizations can better protect themselves from potential threats. Staying informed and vigilant will be key to mitigating the risks associated with this evolving threat landscape.
FAQ
What is a supply-chain attack?
A supply-chain attack occurs when attackers infiltrate the software development process to introduce malicious code into legitimate software, affecting end-users when the software is deployed.
How does invisible code work in these attacks?
Invisible code uses Unicode characters that do not render visibly in code editors, allowing attackers to embed malicious instructions without detection.
What are the benefits of using advanced detection techniques?
Advanced detection techniques, such as static and dynamic analysis, can identify hidden threats that traditional security tools might miss, improving overall security.
How can developers protect against supply-chain attacks?
Developers can protect against these attacks by using trusted sources, regularly updating dependencies, and implementing code signing and manual code reviews.
Why is it important to educate developers about security?
Educating developers about security helps them recognize and handle potential threats, reducing the risk of supply-chain attacks.
What future trends should we expect in supply-chain attacks?
Future trends may include increased use of AI by attackers, greater industry collaboration on threat intelligence, and more sophisticated attack vectors.
The Best Supply-Chain Security Tools at a Glance
| Tool | Best For | Standout Feature | Pricing |
|---|---|---|---|
| Runable | AI automation | AI agents for presentations, docs, reports, images, videos | $9/month |
| Tool 1 | AI orchestration | Integrates with 8,000+ apps | Free plan available; paid from $19.99/month |
| Tool 2 | Data quality | Automated data profiling | By request |
Quick Navigation:
- Runable for AI-powered presentations, documents, reports, images, videos
- Tool 1 for AI orchestration
- Tool 2 for data quality
Internal Links
- AI Automation Guide: Contextually relevant to workflow section
Pillar Suggestions
- Invisible Code Threats: Relevant due to the increasing complexity of supply-chain attacks
Key Takeaways
- Invisible Unicode characters pose a new threat in supply-chain attacks.
- Traditional security tools struggle to detect invisible code.
- Advanced detection techniques are essential for modern cybersecurity.
- Regular updates and trusted sources reduce attack risks.
- Future attacks may leverage AI for increased sophistication.
- Educating developers is critical to maintaining code security.
Related Articles
- SocksEscort Proxy Network Takedown: A Deep Dive [2025]
- FBI Investigation: Malware Hidden in Steam Games [2025]
- Telus Digital's Massive Data Breach: An In-Depth Look [2025]
- The Complex Cyberattack on Stryker's Windows Network: Unraveling the Who, What, and Why [2025]
- Google Chrome on Arm-powered Linux Devices: What You Need to Know [2025]
- Meta’s Massive Undersea Cable Project Faces Challenges Amid Regional Hostilities [2025]
![Invisible Code in Supply-Chain Attacks: Unmasking the Threat [2025]](https://tryrunable.com/blog/invisible-code-in-supply-chain-attacks-unmasking-the-threat-/image-1-1773434074363.jpg)



