Laughing RAT: The New Malware Threat in 2025
In a world where cybersecurity threats are constantly evolving, there’s a new player on the stage: the Laughing RAT. This malware isn’t just another run-of-the-mill threat. It's cunning, malicious, and has an ironic twist—it mocks its victims as it invades their systems. But here’s what makes it particularly menacing: it integrates prankware features that can make a mockery of your defenses while stealing sensitive information.
TL; DR
- Laughing RAT is a malware that combines data theft with prankware elements.
- It is primarily distributed via platforms like Telegram and YouTube.
- Remote Access Trojans (RATs) like Laughing RAT allow attackers full control over infected systems.
- Vigilance and robust security practices are crucial in defending against such threats.
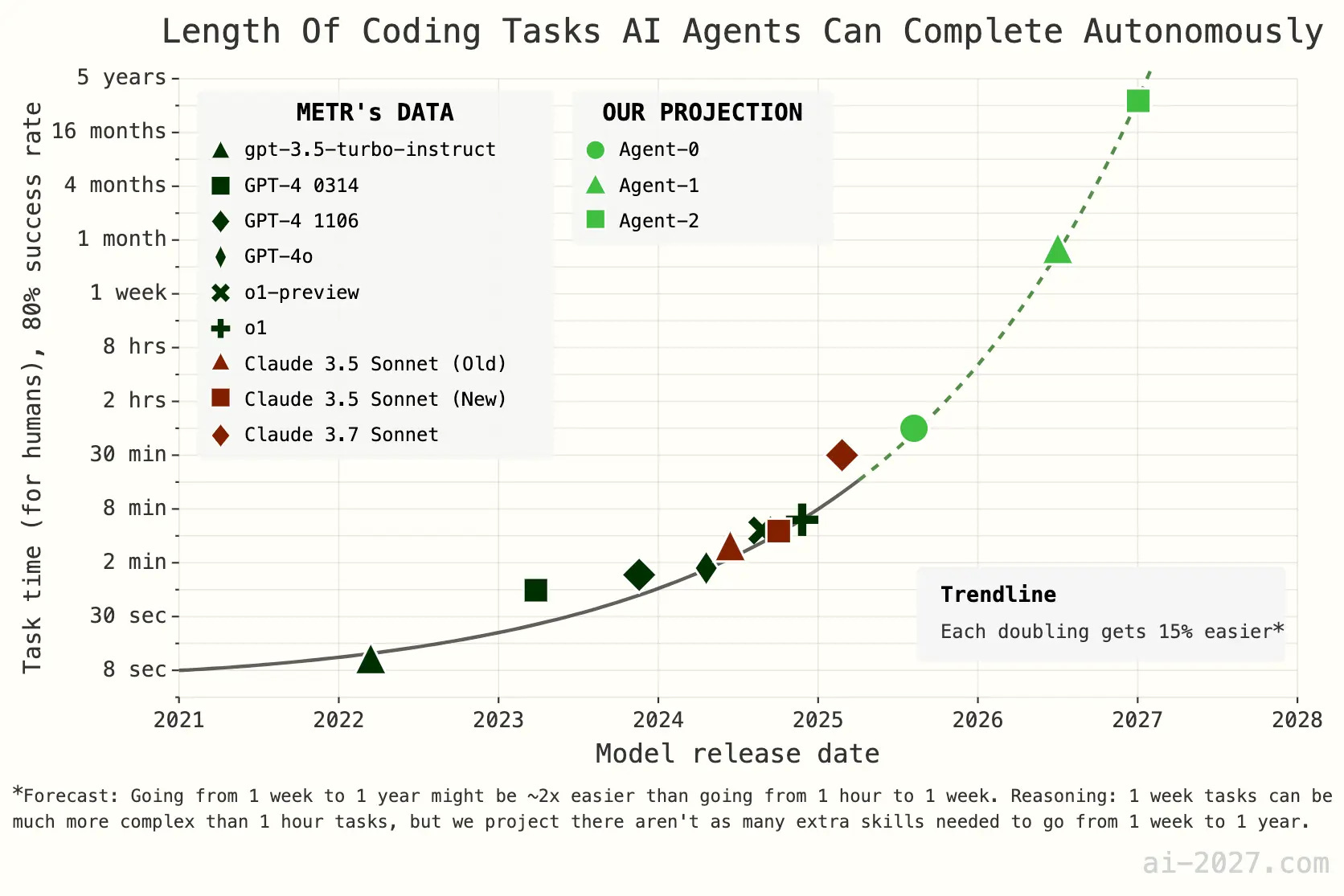
- Expect increased sophistication in malware as attackers leverage more advanced technologies.

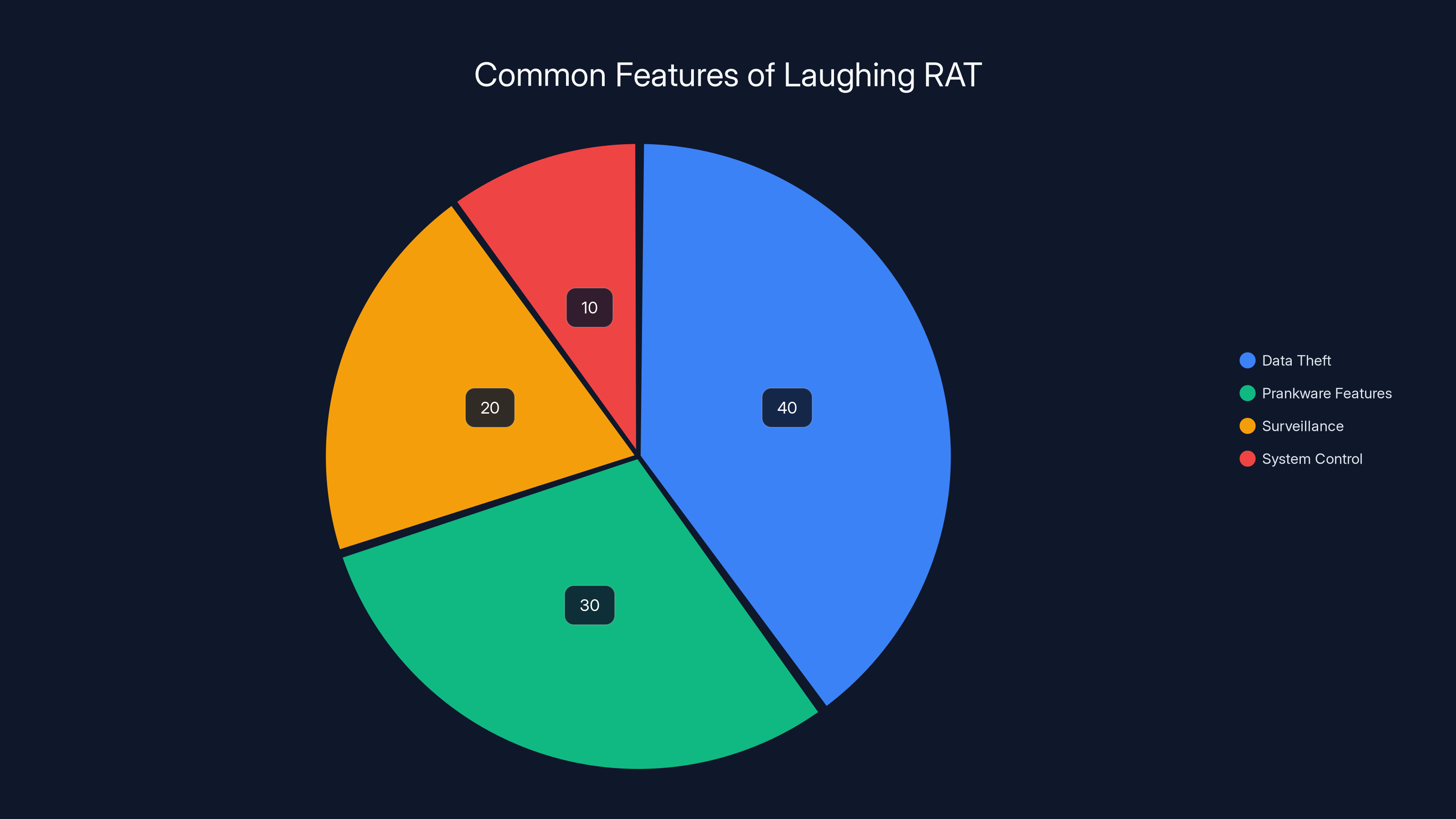
Laughing RAT primarily focuses on data theft (40%) and prankware features (30%), with additional capabilities in surveillance and system control. Estimated data.
What is Laughing RAT?
The Laughing RAT is a type of Remote Access Trojan (RAT) that allows attackers to gain unauthorized access to a victim's computer. Once it infiltrates a system, the malware can perform a range of malicious activities, including stealing data, logging keystrokes, and taking control of the system remotely.
Key Features
- Data Theft: Laughing RAT is engineered to extract sensitive information such as passwords, banking details, and personal data.
- Prankware Integration: It includes features that play pranks on the user, such as random mouse movements or unexpected sounds.
- Remote Control: Attackers can control the victim's device, turning it into a puppet.
- Persistence: The malware employs techniques to remain undetected and persistent within the system.

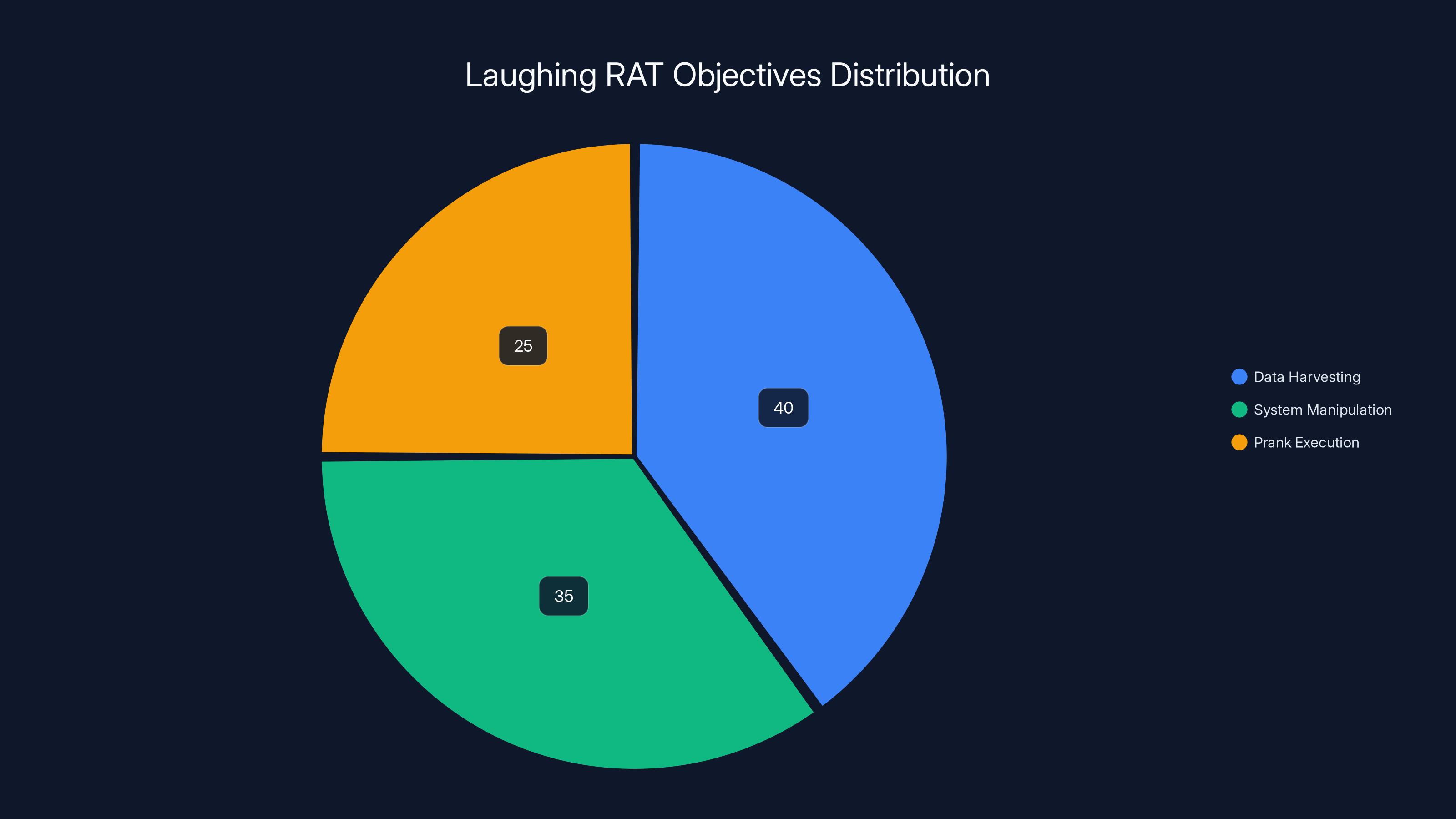
Estimated data shows that data harvesting is the primary objective of Laughing RAT, followed by system manipulation and prank execution.
How Laughing RAT Works
Step 1: Initial Infection
The journey begins with an unsuspecting user downloading a seemingly harmless file. This could be anything from a software update to a free game or tool. The malware is often embedded in legitimate-looking downloads.
Step 2: Establishing Control
Once inside, the malware establishes a connection with its command and control (C2) server. This connection allows the attacker to issue commands and extract data.
Step 3: Data Extraction and Control
With the connection established, the RAT can begin its main objectives:
- Data harvesting: Collecting information from the system.
- System manipulation: Executing commands that can alter system settings or disable security features.
Step 4: Prank Execution
What sets Laughing RAT apart is its prankware features. These are designed not only to amuse the attacker but also to confuse and frustrate the victim. Examples include:
- Sudden screen flips
- Random audio playback
- Automatic shutdowns or restarts
Why is Laughing RAT a Threat?
The combination of data theft and prankware makes Laughing RAT particularly dangerous. It preys on the psychological aspects of cybersecurity, creating not just a technical threat but also a mental strain on the victim.
Psychological Impact
The prank features can make victims feel powerless and paranoid, unsure whether their system is malfunctioning or being controlled by an external force.
Technical Impact
Beyond psychological impacts, Laughing RAT can lead to severe technical issues:
- Data Breaches: Compromised sensitive information can lead to identity theft and financial loss.
- System Downtime: Persistent disruptions can result in significant productivity loss.
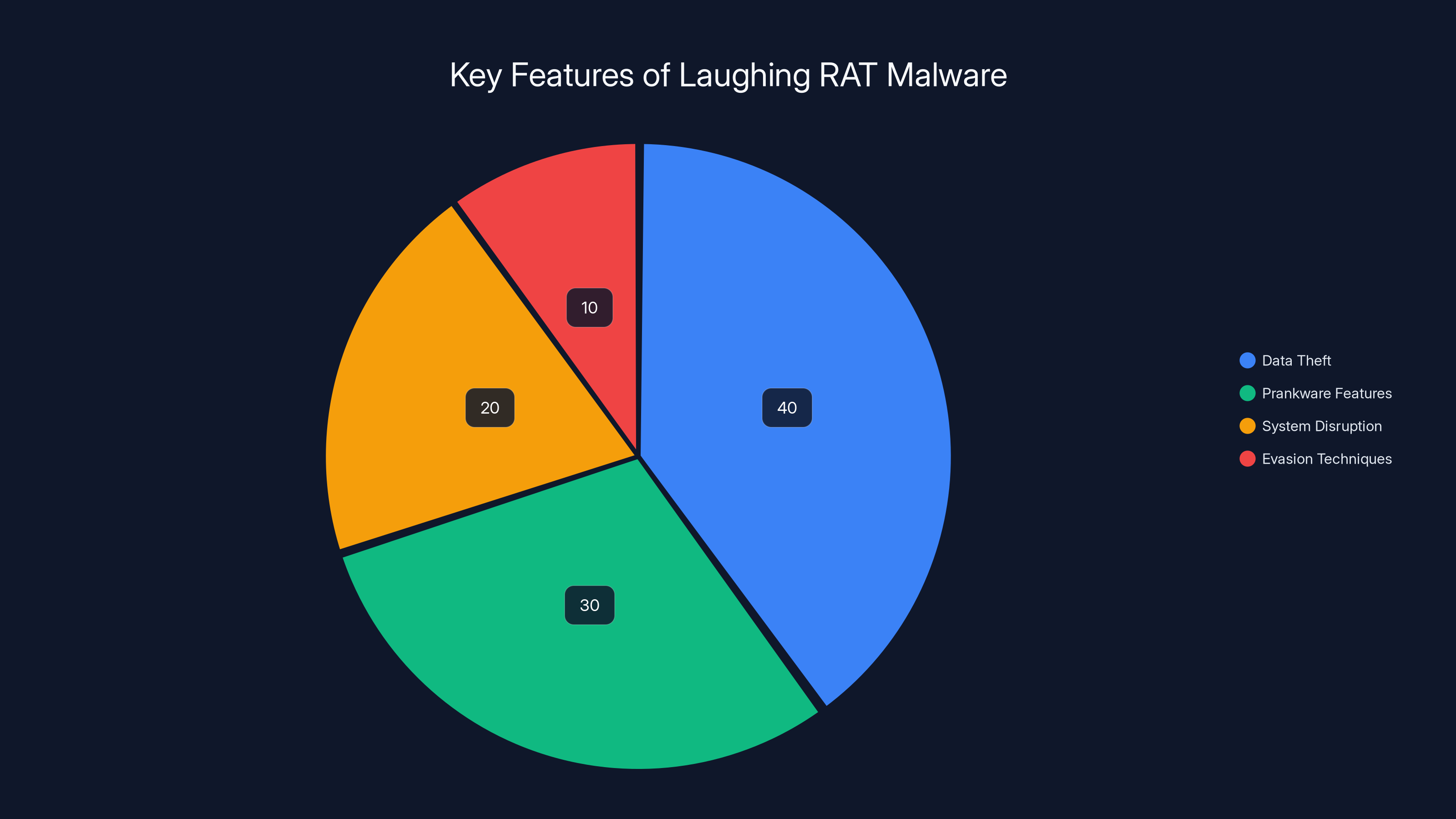
Laughing RAT's primary function is data theft (40%), but it also includes prankware features (30%) and system disruption (20%). Estimated data.
How to Protect Your Systems
Use Comprehensive Security Solutions
Employing a robust antivirus and anti-malware solution is critical. These tools should include real-time scanning and heuristic analysis to detect suspicious behavior.
Regular Software Updates
Keeping all software up-to-date ensures that vulnerabilities are patched as soon as they become known.
User Education
Educating users about the dangers of downloading unknown files and clicking on suspicious links is one of the best defenses against RATs.
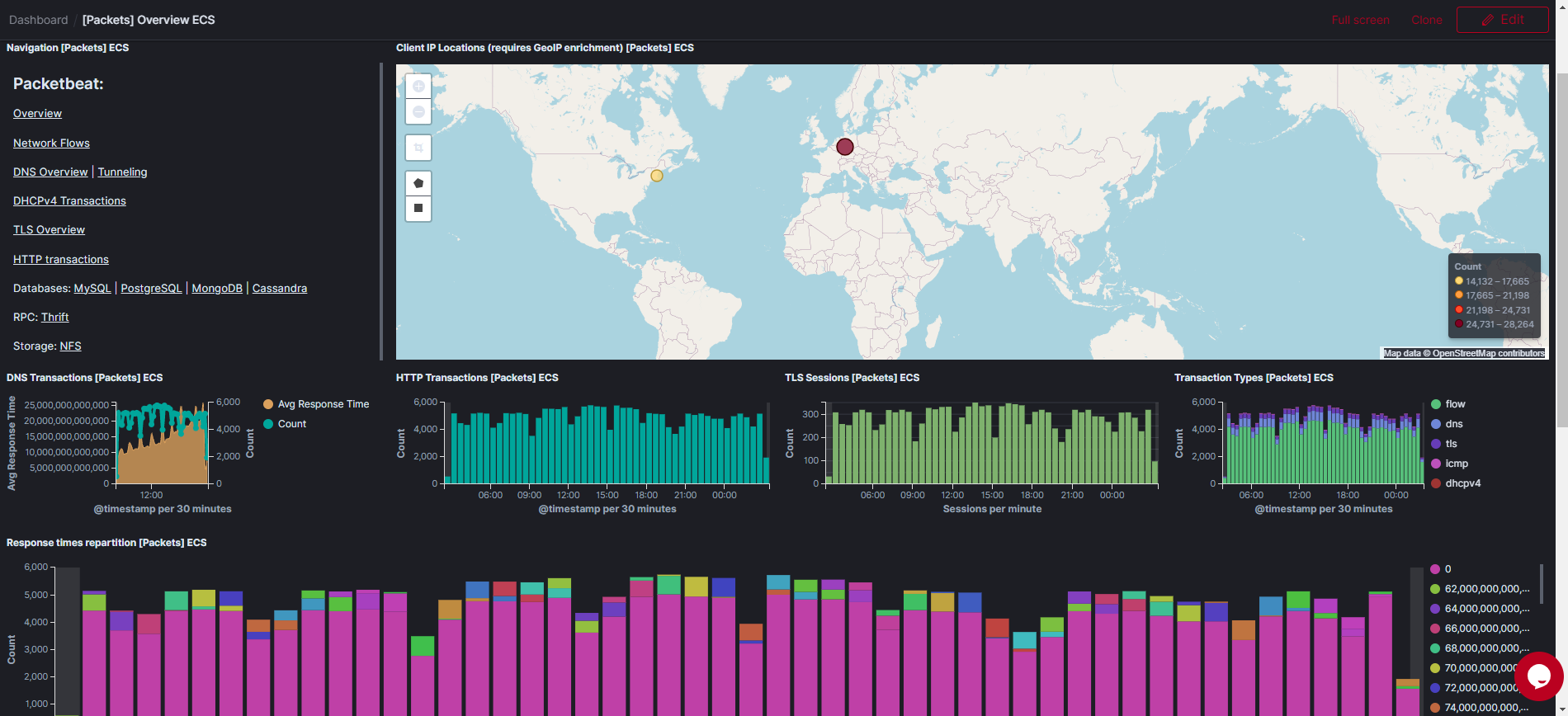
Network Monitoring
Implementing network monitoring tools can help detect unauthorized access attempts and unusual data transfers.
Common Pitfalls and Solutions
Overreliance on Default Security Settings
Many users rely solely on default security settings, which may not be sufficient to protect against sophisticated threats.
Solution: Customize security settings to fit the specific needs of your environment, enabling advanced features where available.
Ignoring Software Updates
Delaying updates can leave systems vulnerable to known exploits.
Solution: Automate updates where possible and schedule regular manual checks.
Weak Password Practices
Using weak or common passwords makes it easier for attackers to gain access.
Solution: Implement strong password policies that require complex and unique passwords.
The Future of Malware Threats
The evolution of malware is an ongoing battle between attackers and defenders. As security measures improve, so do the tactics of cybercriminals.
Increased Use of AI
Expect malware to integrate AI to improve its ability to evade detection and adapt to security environments.
More Sophisticated Social Engineering
Social engineering tactics will become more advanced, making it harder for users to distinguish between legitimate and malicious communications.
Best Practices for Organizations
Develop an Incident Response Plan
Having a clear and practiced incident response plan can minimize damage and recovery time in the event of an attack.
Regular Security Audits
Conduct audits to identify and mitigate vulnerabilities before they can be exploited.
Backup Critical Data
Regularly backing up data ensures that information can be restored in the event of a compromise.
Conclusion
The Laughing RAT represents a new wave of malware that combines traditional data theft with psychological manipulation through prankware. By staying informed and proactive, individuals and organizations can protect themselves against this and future threats. Implementing comprehensive security measures, educating users, and staying vigilant are key steps to securing digital environments.
Use Case: Quickly detect and respond to malware threats with AI-powered automation for enhanced security.
Try Runable For FreeFAQ
What is a Remote Access Trojan (RAT)?
A RAT is a type of malware that allows unauthorized users to control a computer remotely. It is often used for data theft and surveillance.
How does Laughing RAT differ from other malware?
Laughing RAT combines traditional data theft capabilities with prankware features that can confuse and frustrate users.
Can antivirus software protect against Laughing RAT?
Yes, a robust antivirus solution with real-time protection can help detect and prevent Laughing RAT infections.
What should I do if I suspect an infection?
Immediately disconnect from the internet, run a full system scan with updated antivirus software, and consult a cybersecurity professional if needed.
How can organizations prepare for malware attacks?
Organizations should develop incident response plans, conduct regular security audits, and educate employees about cybersecurity best practices.
Is Laughing RAT targeting specific industries?
Currently, Laughing RAT is not known to target specific industries but rather takes advantage of widespread vulnerabilities in unprotected systems.
Key Takeaways
- Laughing RAT integrates prankware with traditional malware functions.
- Distributed via platforms like Telegram, posing a broad threat.
- Emphasizes the need for comprehensive cybersecurity measures.
- AI is expected to play a role in future malware developments.
- Organizations must prioritize education and incident response planning.
Related Articles
- Hasbro Cyberattack: Lessons and Strategies for Cyber Resilience [2025]
- The Role of Spyware in Modern Law Enforcement: A Deep Dive into ICE's Use of Paragon's Tools [2025]
- Protect Your Privacy: Secure Your Granola Notes Now [2025]
- Understanding Telehealth Security: Lessons from the Hims & Hers Data Breach [2025]
- Maintaining Cyber Control When AI Acts Autonomously [2025]
- Understanding the Suspension of California's VC Diversity Reporting Law [2025]




