Hasbro Cyberattack: Lessons and Strategies for Cyber Resilience [2025]
In recent years, cyberattacks have become increasingly sophisticated, targeting businesses across all sectors. Hasbro, one of the world's leading toymakers, recently became the latest victim of such an attack. While the specifics of the breach are still under investigation, the incident highlights the urgent need for comprehensive cybersecurity strategies.
TL; DR
- Hasbro's cyberattack: Affected website functionality, forcing an IT shutdown.
- Immediate response: Highlighted the importance of quick containment and recovery measures.
- Potential data theft: Underlines the necessity of robust data protection mechanisms.
- Future preparedness: Emphasizes ongoing cybersecurity training and system upgrades.
- Bottom Line: Cyber resilience is crucial for minimizing the impact of attacks.

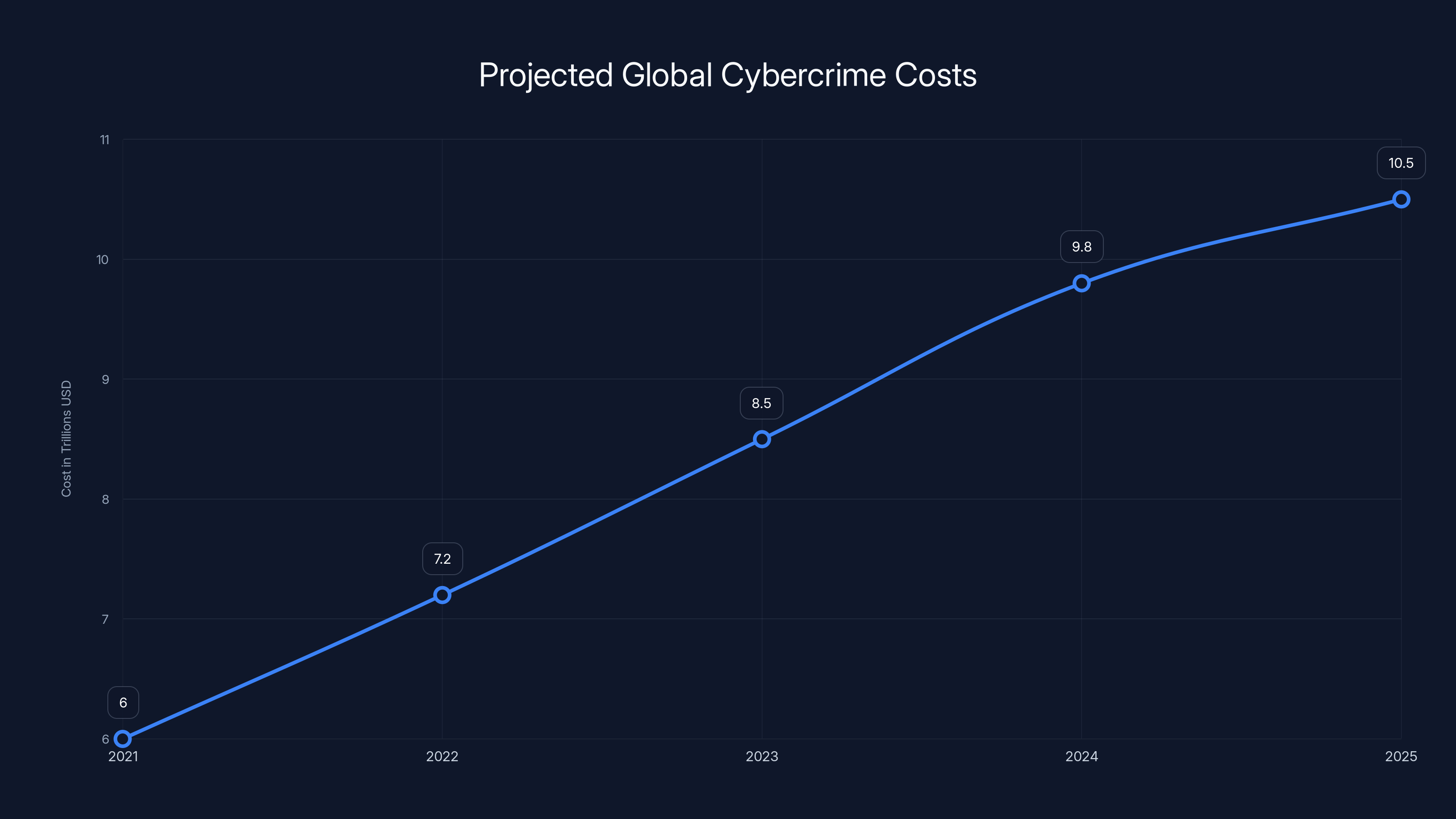
Global cybercrime costs are projected to increase significantly, reaching $10.5 trillion by 2025. Estimated data based on industry reports.
Understanding the Cyberattack Landscape
The digital transformation of businesses has led to increased vulnerability to cyber threats. Organizations, regardless of size, are now prime targets for cybercriminals seeking to exploit weaknesses. According to a recent report by Cybersecurity Ventures, global cybercrime costs are expected to reach $10.5 trillion annually by 2025.
The Hasbro Incident
Hasbro confirmed a cyberattack that led to significant disruptions across some parts of its websites. While operations continued, IT teams were forced to implement temporary shutdowns and containment measures. An ongoing investigation is assessing the scope of potential data theft, but no group has claimed responsibility yet.


Encryption is estimated to be the most effective strategy for mitigating data theft risks, followed by access controls and regular audits. (Estimated data)
Immediate Response and Containment
Immediate response to a cyberattack is critical. Hasbro's quick IT shutdown helped limit the attack's spread and potential damage. This step is a standard protocol in cybersecurity incident response plans.
Key Steps in Incident Response
- Detection: Early detection is crucial. Implementing real-time monitoring tools can help identify anomalies.
- Containment: Quick isolation of affected systems prevents further infiltration.
- Eradication: Removing malware or unauthorized access points.
- Recovery: Restoring normal operations while ensuring the threat has been neutralized.
- Lessons Learned: Post-incident analysis to improve future defenses.
QUICK TIP: Always conduct a thorough post-incident review to identify weaknesses and update your security protocols accordingly.

Potential Data Theft: Risks and Mitigation
Data theft is a major concern during cyberattacks. Organizations like Hasbro handle vast amounts of sensitive information, making them attractive targets.
Mitigating Data Theft Risks
- Encryption: Encrypt sensitive data both at rest and in transit.
- Access Controls: Implement strict access controls to limit data exposure.
- Regular Audits: Conduct regular security audits to identify and fix vulnerabilities.
DID YOU KNOW: According to IBM's Cost of a Data Breach Report, the average cost of a data breach in 2023 was $4.45 million.


AI-driven incident response is estimated to be the most effective strategy for minimizing downtime and protecting data integrity. Estimated data.
Cybersecurity Best Practices for Organizations
The Hasbro incident serves as a reminder of the importance of cybersecurity best practices. Organizations must adopt a proactive approach to protect themselves against potential threats.
Key Cybersecurity Strategies
- Employee Training: Regular training sessions on recognizing phishing attempts and other social engineering tactics.
- Multi-factor Authentication (MFA): Adding an extra layer of security to user accounts.
- Regular Software Updates: Keeping systems and applications up-to-date to patch vulnerabilities.
- Network Segmentation: Dividing a network into smaller, isolated segments to contain breaches.
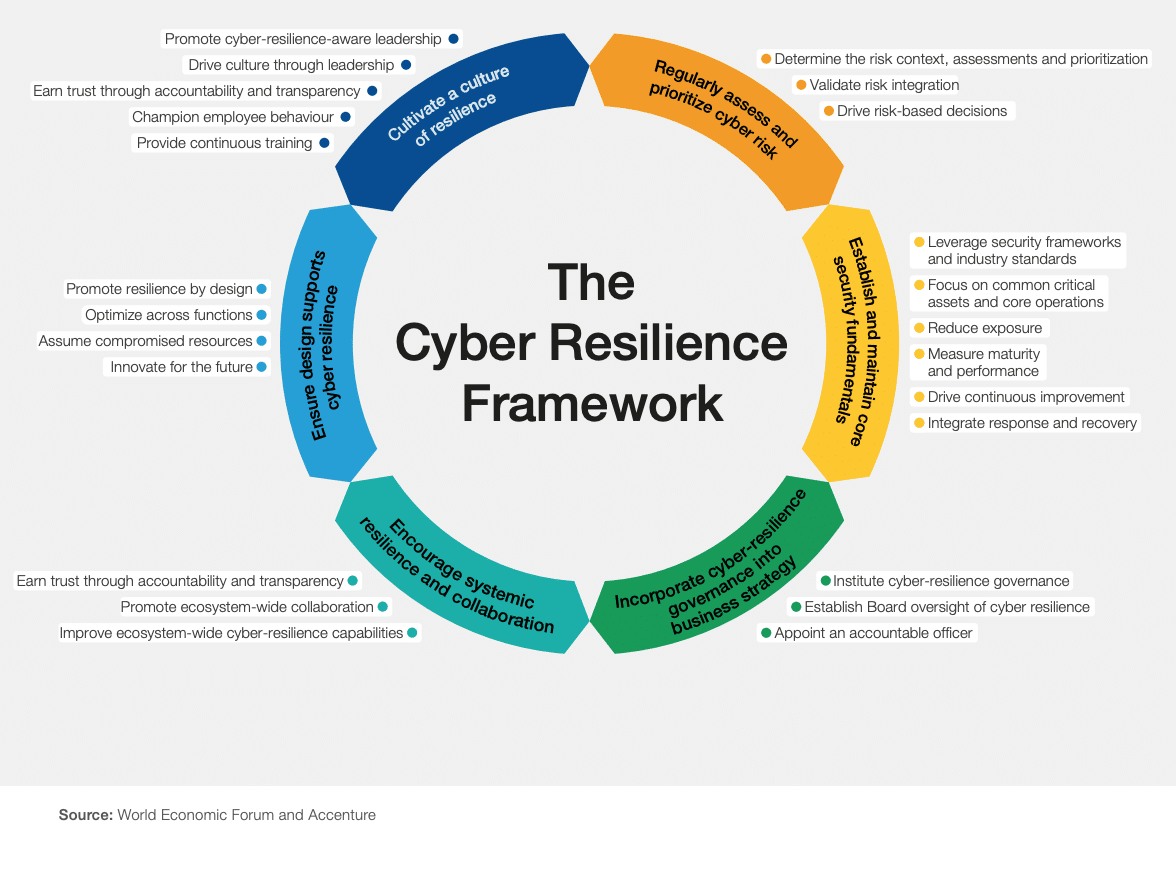
Implementing a Cyber Resilience Framework
Cyber resilience is about more than just preventing attacks; it's about ensuring business continuity in the face of adversity.
Components of a Cyber Resilience Framework
- Risk Assessment: Evaluating potential threats and their impact on the organization.
- Business Continuity Planning: Ensuring critical operations can continue during disruptions.
- Incident Response Plan: A documented strategy for responding to security breaches.
- Regular Testing: Conducting simulations and drills to test the effectiveness of response plans.
Common Pitfalls and How to Avoid Them
Even with the best intentions, organizations can fall into common cybersecurity pitfalls.
Avoiding Common Cybersecurity Mistakes
- Overconfidence: Believing that an attack won't happen to your organization.
- Neglecting Updates: Failing to update systems regularly can leave vulnerabilities open.
- Ignoring Insider Threats: Employees can unintentionally or maliciously cause security breaches.
QUICK TIP: Implement a zero-trust architecture where every access request is verified before being granted.
Future Trends in Cybersecurity
As technology evolves, so do cyber threats. Organizations need to stay ahead by adapting to new trends.
Emerging Cybersecurity Trends
- Artificial Intelligence (AI): AI is increasingly being used to predict and identify threats in real-time.
- Zero Trust Security: A security model that requires strict verification for every user and device.
- Quantum Computing: As this technology advances, it will pose new challenges and opportunities in cybersecurity.
Conclusion: Building a Cyber-Resilient Future
The cyberattack on Hasbro is a stark reminder of the ever-present threat of cybercrime. By implementing robust cybersecurity measures and fostering a culture of awareness and preparedness, organizations can build resilience against future attacks.
Use Case: Automating incident response procedures with AI to minimize downtime and protect data integrity.
Try Runable For FreeFAQ
What is a cyberattack?
A cyberattack is an attempt by cybercriminals to access, alter, or destroy a computer network or system. It can take many forms, including malware, phishing, or denial-of-service attacks.
How does a cyberattack affect businesses?
Cyberattacks can disrupt operations, lead to financial losses, damage reputations, and result in the theft of sensitive data. Businesses may face legal consequences and incur costs related to recovery and mitigation.
What are the benefits of cybersecurity measures?
Implementing strong cybersecurity measures helps protect sensitive data, ensure business continuity, and maintain customer trust. It reduces the risk of financial losses and regulatory penalties.
How can companies prepare for potential cyberattacks?
Companies can prepare by conducting regular risk assessments, developing incident response plans, training employees, and implementing robust security technologies.
What role does employee training play in cybersecurity?
Employee training is crucial in cybersecurity as it helps staff recognize and respond to threats such as phishing emails. It fosters a culture of security awareness and reduces the risk of human error.
What is the importance of encryption in cybersecurity?
Encryption is a critical component of cybersecurity, protecting sensitive data by converting it into a coded format that is unreadable to unauthorized users.
How do businesses recover from a cyberattack?
Recovery involves restoring systems and data, investigating the attack, and implementing measures to prevent future incidents. Communication with stakeholders and legal compliance are also important aspects of recovery.
What is cyber resilience?
Cyber resilience refers to an organization's ability to prepare for, respond to, and recover from cyberattacks while maintaining critical operations.
Key Takeaways
- Hasbro's cyberattack highlights the importance of quick containment measures.
- Potential data theft underscores the need for robust data protection mechanisms.
- Ongoing employee training is crucial for effective cybersecurity.
- Future cybersecurity trends include the adoption of AI and zero trust models.
- Building a cyber-resilient future involves comprehensive risk assessments and incident response plans.
Related Articles
- Safeguarding Older Apple Devices from DarkSword Attacks: A Comprehensive Guide [2025]
- The Hidden Risks of Exposed API Keys: How to Secure Your Cloud Systems [2025]
- The Hidden Dangers of AI: What If Your AI Agent Is Working Against You? [2025]
- Inside the Anthropic Leak: Unpacking the Claude Code Source Code Exposure [2025]
- Tech Sovereignty: Why One Size Doesn’t Fit All [2025]
- Unveiling OpenClaw Security Risks You Must Know About [2025]
![Hasbro Cyberattack: Lessons and Strategies for Cyber Resilience [2025]](https://tryrunable.com/blog/hasbro-cyberattack-lessons-and-strategies-for-cyber-resilien/image-1-1775129664461.jpg)



