Understanding Telehealth Security: Lessons from the Hims & Hers Data Breach [2025]
Telehealth has revolutionized healthcare delivery, providing unprecedented convenience and accessibility. However, the recent data breach at Hims & Hers is a stark reminder of the vulnerabilities within digital health platforms. This article delves into the intricacies of telehealth security, using Hims & Hers as a case study, and explores how companies can fortify their defenses against similar threats.
TL; DR
- Data Breach Overview: Hims & Hers experienced a data breach affecting customer support systems, exposing personal information but not medical records, as reported by TechCrunch.
- Social Engineering Risks: Hackers exploited social engineering tactics, highlighting the need for robust employee training, as detailed in TechSpective.
- Data Protection Strategies: Encryption, access controls, and regular audits are critical for safeguarding sensitive information.
- Future Trends: AI and machine learning will play a significant role in enhancing telehealth security, according to Wiz.io.
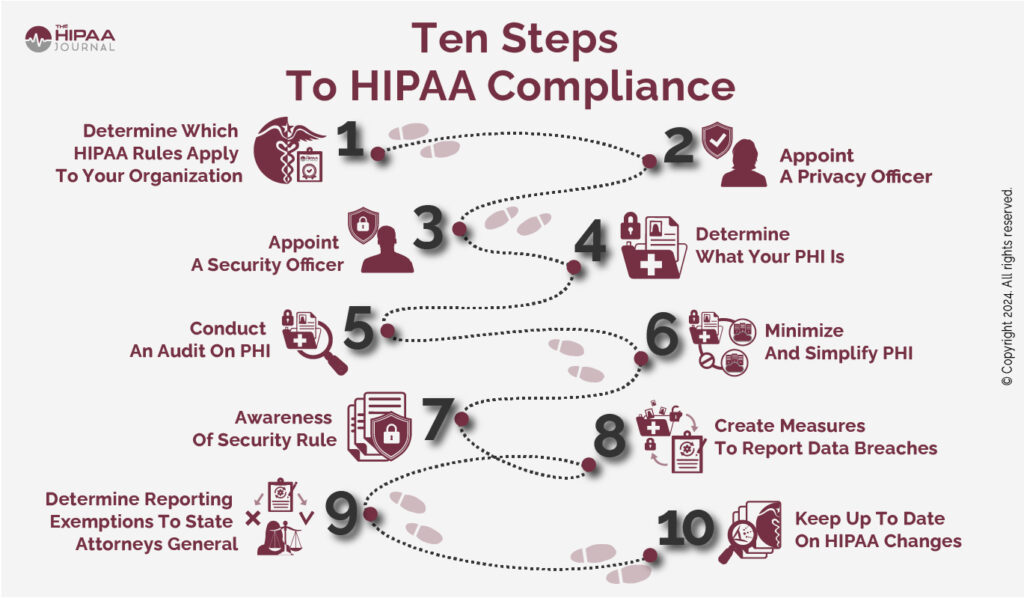
- Regulatory Compliance: Adherence to HIPAA and other regulations is essential for maintaining trust and avoiding legal repercussions, as outlined by the International Association of Privacy Professionals.

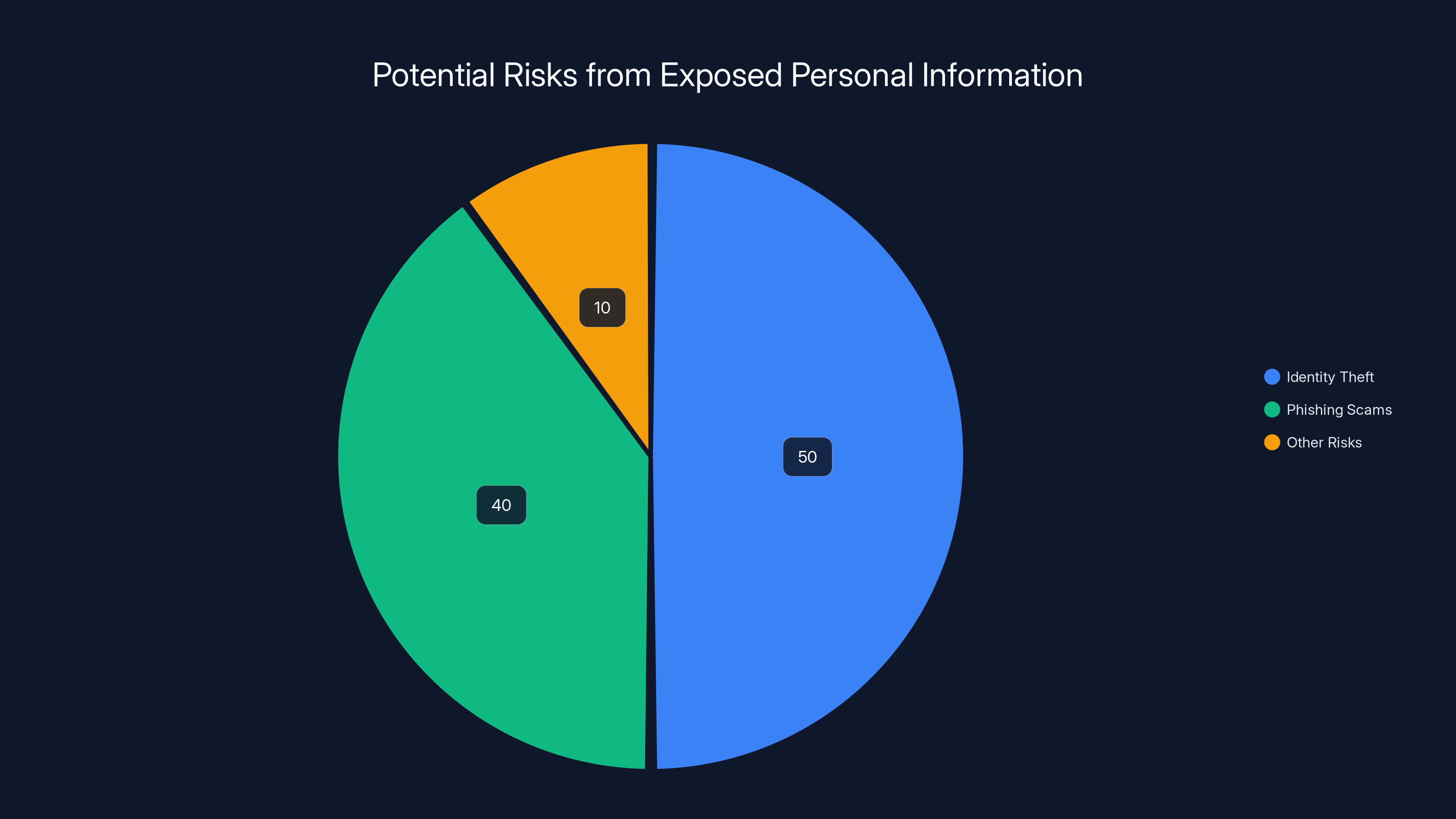
Identity theft and phishing scams are the primary risks from exposed personal information, with identity theft being slightly more prevalent. Estimated data.
The Hims & Hers Data Breach: What Happened?
Hims & Hers, a prominent telehealth company, recently disclosed a data breach involving its third-party customer support system. Hackers accessed customer names, contact information, and potentially other personal details. While the company assured that medical records remained secure, the breach underscores the importance of protecting all facets of customer data, as highlighted by HIPAA Journal.
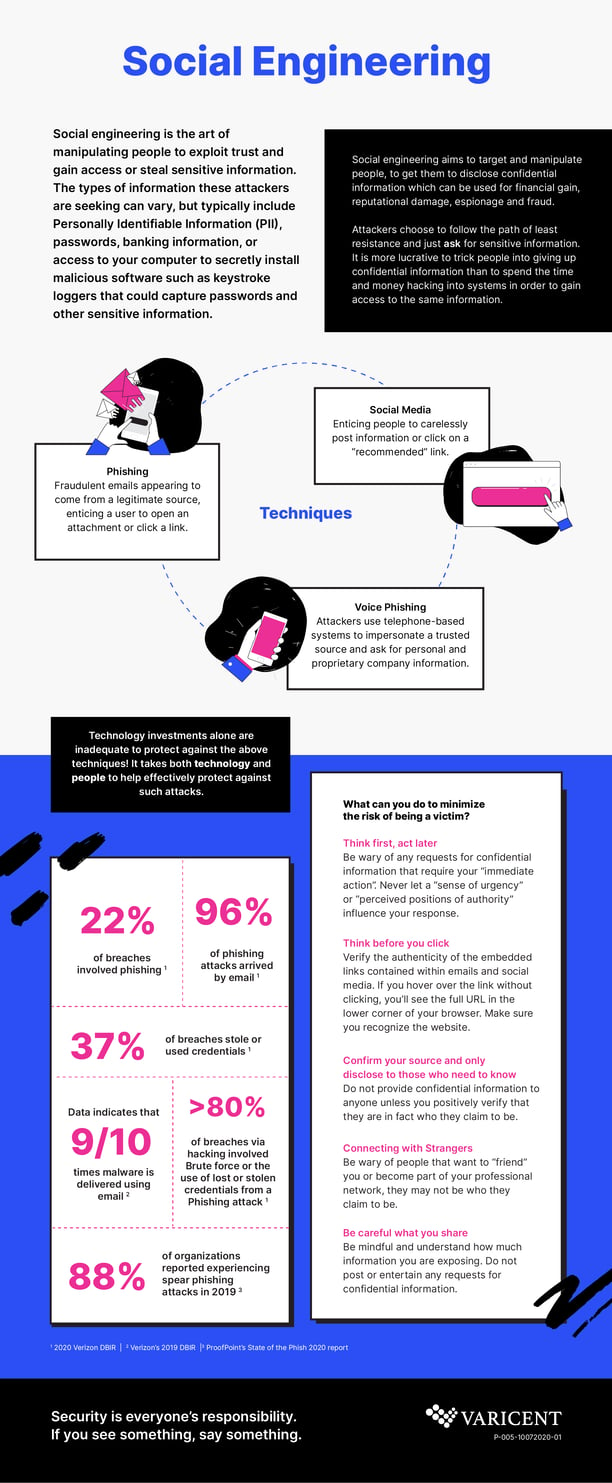
Social Engineering: The Weak Link
The breach at Hims & Hers was facilitated by a social engineering attack. This method relies on manipulating individuals into divulging confidential information. In this case, hackers tricked employees into granting access to sensitive systems.
What You Need to Know:
- Human Vulnerability: Social engineering exploits human psychology rather than technical vulnerabilities.
- Common Tactics: Phishing emails, pretexting (impersonating authority figures), and baiting (offering false promises), as discussed in KnowBe4.
Prevention Tips:
- Employee Training: Conduct regular security awareness sessions.
- Simulated Attacks: Test employees with mock phishing attempts.
- Clear Protocols: Establish protocols for verifying identities before granting access.
Data at Risk: Beyond Medical Records
While Hims & Hers confirmed that medical records were untouched, the compromised personal information could still pose significant risks:
- Identity Theft: With names and contact details, hackers can attempt identity theft or fraudulent activities, as noted by the National Council on Aging.
- Phishing Scams: Personal information can be used to craft convincing phishing emails targeting affected customers.
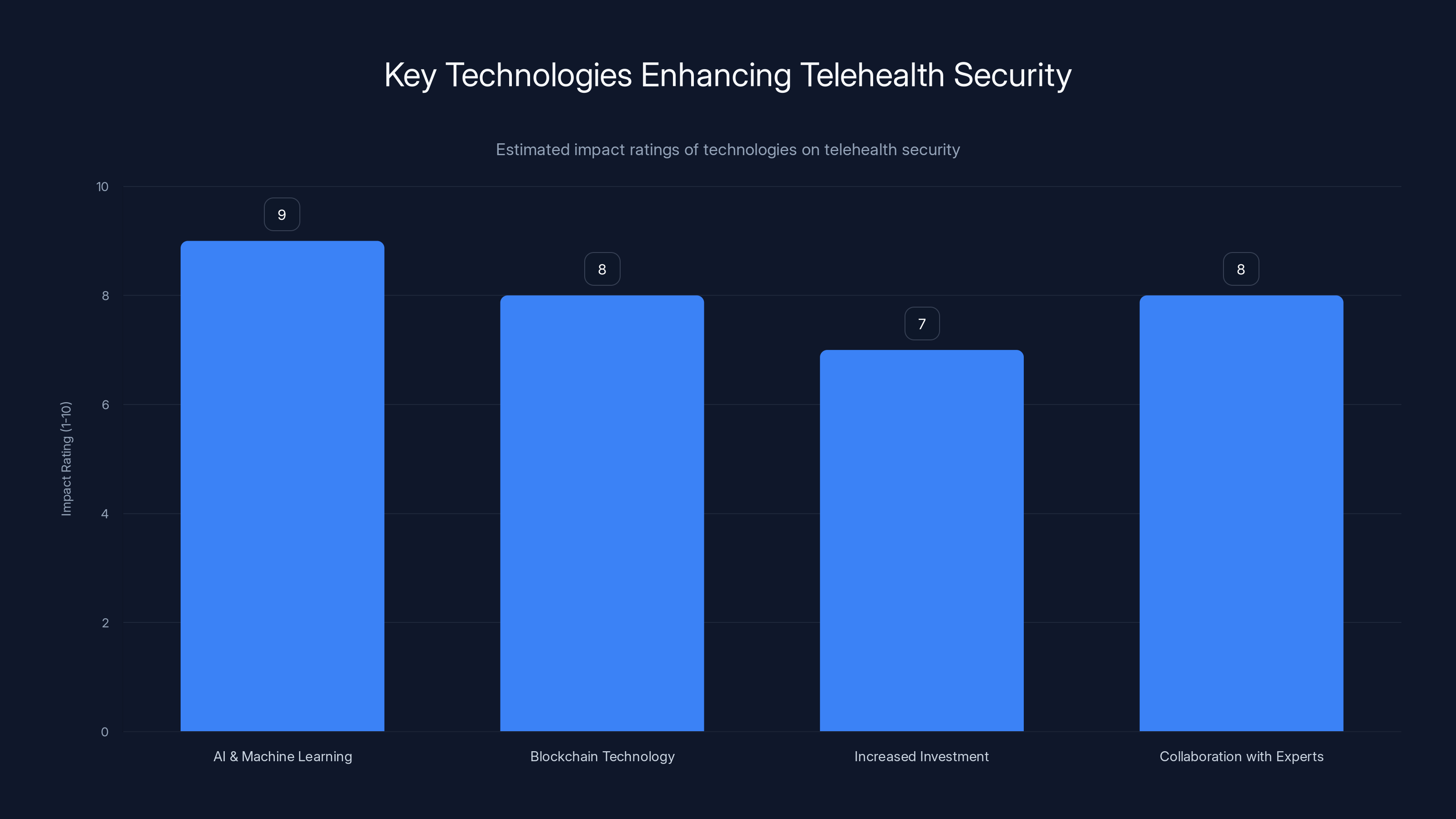
AI and Machine Learning are projected to have the highest impact on enhancing telehealth security, followed closely by Blockchain Technology. (Estimated data)
Key Security Practices for Telehealth Platforms
Ensuring the security of telehealth platforms requires a multi-layered approach. Here are some best practices to consider:
1. Encryption
Data encryption is a cornerstone of digital security. It involves encoding data so that only authorized parties can decipher it.
- In Transit: Use HTTPS and VPNs to secure data moving between servers and clients.
- At Rest: Encrypt stored data with strong algorithms like AES-256, as recommended by Palo Alto Networks' Unit 42.
2. Access Controls
Restricting who can access sensitive information is crucial. Implement role-based access controls (RBAC) to limit data access based on job roles.
- Least Privilege Principle: Users should only have access to the data necessary for their tasks.
- Multi-Factor Authentication (MFA): Adds an extra layer of security, requiring more than just a password.
3. Regular Security Audits
Conduct periodic audits to identify vulnerabilities and ensure compliance with security policies.
- Vulnerability Scanning: Use automated tools to detect potential security gaps.
- Penetration Testing: Simulate cyberattacks to evaluate the effectiveness of security measures, as suggested by AWS.
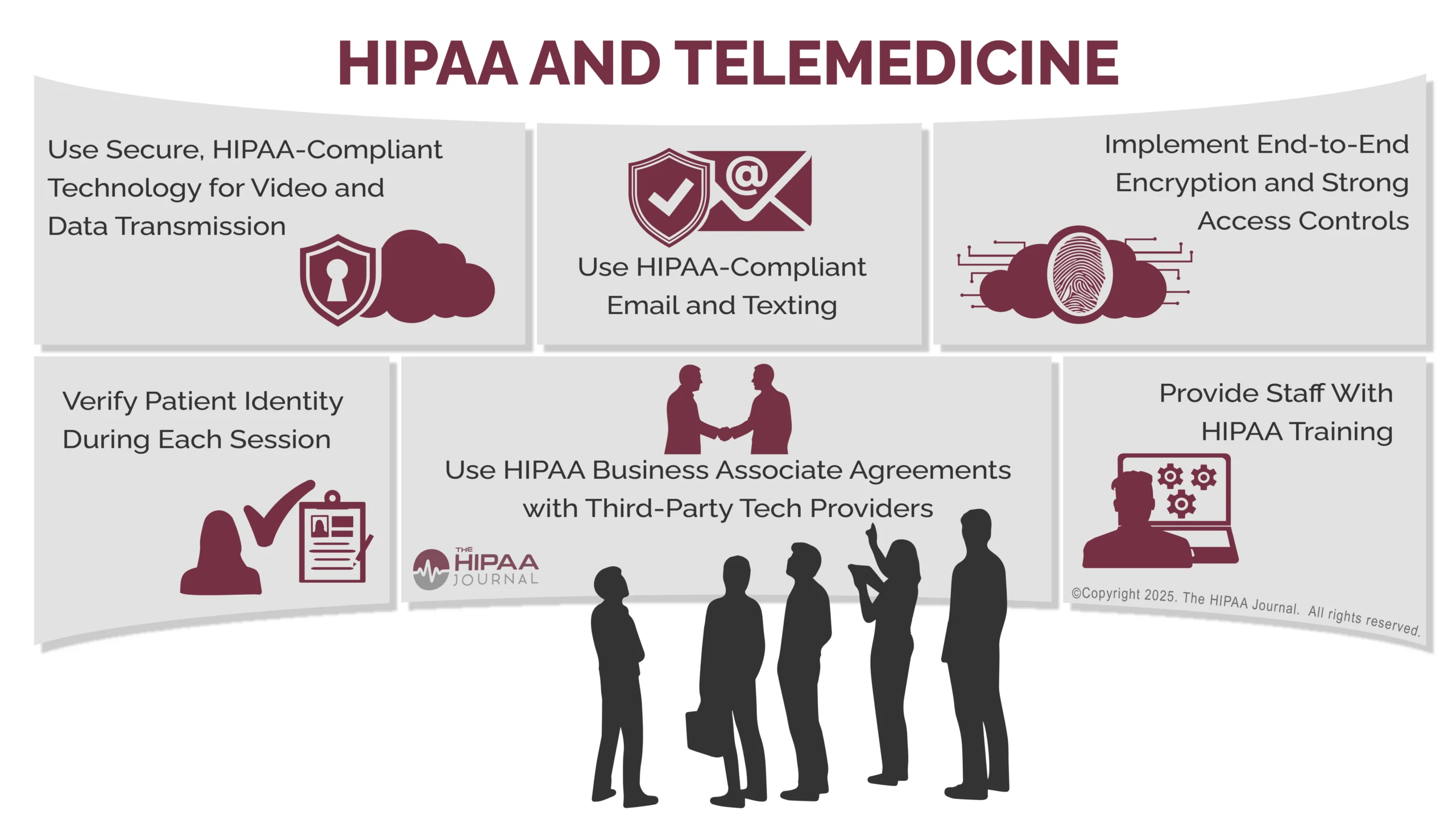
Regulatory Compliance: A Non-Negotiable Aspect
Telehealth companies must adhere to various regulations to protect patient data and maintain trust. In the United States, the Health Insurance Portability and Accountability Act (HIPAA) sets the standard for sensitive patient data protection.
HIPAA Compliance
- Privacy Rule: Protects the privacy of individually identifiable health information.
- Security Rule: Sets standards for the security of electronic protected health information (ePHI).
- Breach Notification Rule: Requires covered entities to notify affected individuals and the government of data breaches, as outlined by IAPP.
Global Regulations
- GDPR (Europe): Governs data protection and privacy in the European Union.
- PIPEDA (Canada): Regulates how private sector organizations collect, use, and disclose personal information.
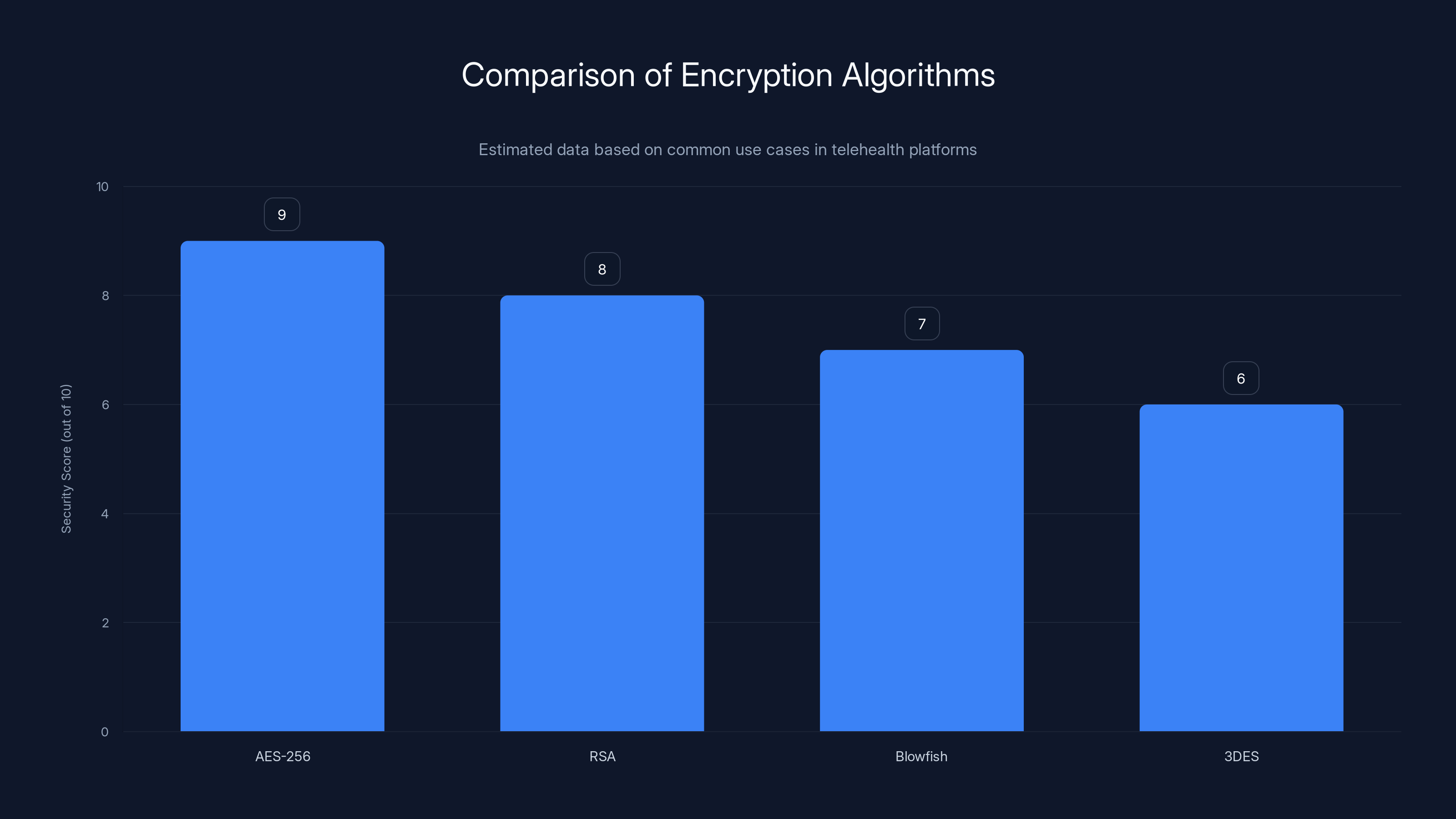
AES-256 is considered the most secure encryption algorithm for telehealth platforms, with a high security score of 9 out of 10. Estimated data based on typical use cases.
The Future of Telehealth Security
As telehealth continues to grow, so too will the sophistication of cyber threats. However, advancements in technology offer promising solutions.
AI and Machine Learning
AI and machine learning can enhance security by identifying patterns and anomalies that may indicate a breach.
- Behavioral Analytics: AI can monitor user behavior to detect unusual activity.
- Automated Threat Detection: Machine learning models can predict and prevent attacks before they occur, as discussed in Telehealth.org.
Blockchain Technology
Blockchain offers a decentralized approach to data management and security, making unauthorized access more challenging.
- Immutable Records: Once data is recorded, it cannot be altered without consensus.
- Smart Contracts: Automate compliance and data sharing agreements.
The Role of Telehealth in Future Healthcare
Telehealth is poised to become an integral part of the healthcare landscape. To ensure its continued growth and acceptance, companies must prioritize security and privacy.
- Increased Investment: Companies are expected to invest more in cybersecurity to protect their platforms.
- Collaboration with Security Experts: Engaging with cybersecurity firms can provide specialized knowledge and tools.

Conclusion
The Hims & Hers data breach serves as a wake-up call for the telehealth industry. By adopting robust security measures and staying vigilant against emerging threats, telehealth providers can protect sensitive data, maintain patient trust, and continue to innovate in delivering healthcare solutions.
Telehealth security is not a one-time effort but an ongoing commitment to safeguarding the future of digital health.

FAQ
What is telehealth?
Telehealth refers to the use of digital technologies to deliver healthcare services remotely, allowing for increased accessibility and convenience.
How does social engineering work?
Social engineering exploits human psychology to manipulate individuals into revealing confidential information, often through deceptive tactics such as phishing or pretexting.
What are the benefits of encryption in telehealth?
Encryption protects sensitive data by encoding it, ensuring that only authorized parties can access and read the information, both in transit and at rest.
How can telehealth companies ensure compliance with regulations?
By adhering to laws such as HIPAA, GDPR, and PIPEDA, telehealth companies can ensure that they protect patient data and avoid legal repercussions.
What role does AI play in telehealth security?
AI enhances telehealth security by using machine learning algorithms to detect anomalies, predict threats, and automate responses to potential breaches.
How can blockchain technology improve telehealth security?
Blockchain provides a decentralized, immutable ledger for secure data management, reducing the risk of unauthorized access and tampering.
Key Takeaways
- Hims & Hers experienced a data breach through social engineering, highlighting vulnerabilities in customer support systems.
- Social engineering attacks exploit human psychology, underscoring the need for comprehensive employee training.
- Data protection strategies like encryption and access controls are crucial for securing telehealth platforms.
- Future trends in telehealth security include AI and blockchain technology, which offer enhanced protection against cyber threats.
- Regulatory compliance, such as adherence to HIPAA, is essential for maintaining trust and avoiding legal issues in telehealth.
Related Articles
- Hasbro Cyberattack: Lessons and Strategies for Cyber Resilience [2025]
- The Role of Spyware in Modern Law Enforcement: A Deep Dive into ICE's Use of Paragon's Tools [2025]
- The Hidden Risks of Exposed API Keys: How to Secure Your Cloud Systems [2025]
- Safeguarding Older Apple Devices from DarkSword Attacks: A Comprehensive Guide [2025]
- The Hidden Dangers of AI: What If Your AI Agent Is Working Against You? [2025]
- Maintaining Cyber Control When AI Acts Autonomously [2025]
![Understanding Telehealth Security: Lessons from the Hims & Hers Data Breach [2025]](https://tryrunable.com/blog/understanding-telehealth-security-lessons-from-the-hims-hers/image-1-1775165656987.jpg)



