Microsoft's Warning: Security Flaw Puts 50 Million Android Users at Risk [2025]
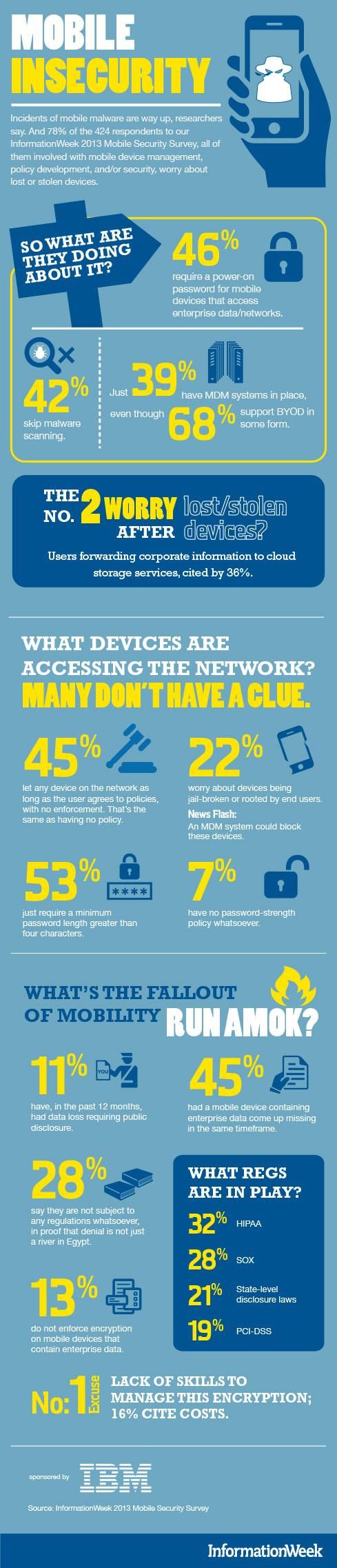
Last week, Microsoft announced a critical security vulnerability affecting over 50 million Android users worldwide. This flaw, rooted in an outdated software development kit (SDK), potentially exposed sensitive user credentials and financial data to malicious actors, as detailed in Microsoft's security blog.
TL; DR
- 50 million Android devices were affected by a critical security flaw.
- User credentials and financial data were at risk due to an outdated SDK.
- Sandbox bypass vulnerability allowed unauthorized access to sensitive data.
- Immediate updates and security patches are crucial for protection.
- Future trends include enhanced security measures and SDK auditing.
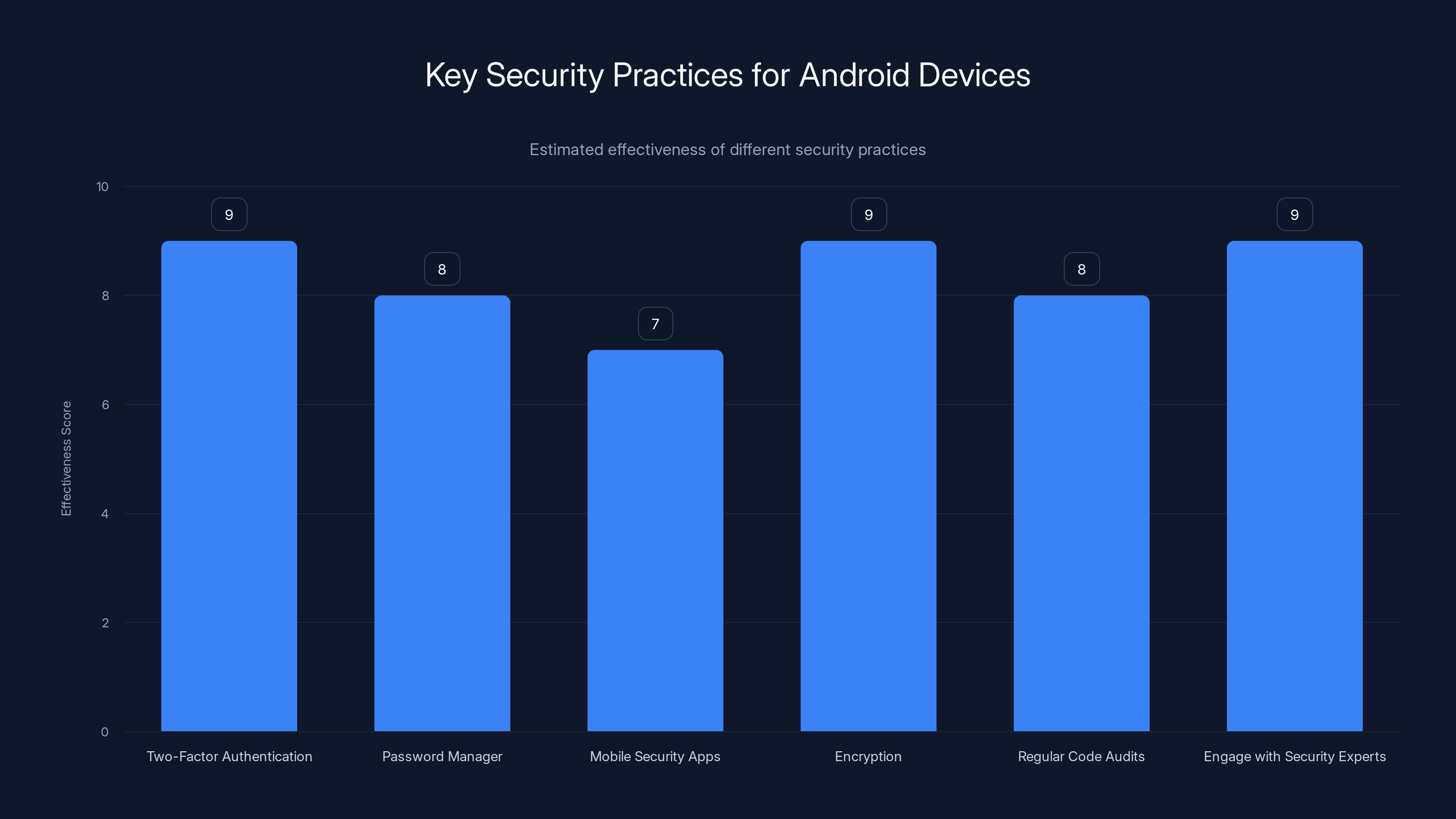
Two-Factor Authentication and Encryption are among the most effective security practices for enhancing Android device and app security. (Estimated data)
Understanding the Security Flaw
What Happened?
The vulnerability was traced to the Engage Lab SDK, which is commonly used by various applications to provide enhanced functionality such as analytics and user engagement features. However, an overlooked flaw in the SDK allowed applications to bypass Android's sandboxing mechanism, which is designed to isolate apps and protect user data, as reported by SecurityWeek.
How Serious Is This?
The flaw's seriousness cannot be overstated. By bypassing the sandbox, malicious apps could potentially access and exfiltrate sensitive data stored within other apps, including login credentials and financial information.
Key Risks Involved:
- Unauthorized access to sensitive data
- Increased risk of phishing attacks
- Potential financial loss

Diving Deeper: How the Flaw Works
Sandboxing and Its Importance
Android's sandboxing feature is a fundamental security measure that ensures each app operates in its own isolated environment. This prevents apps from accessing data stored by others without explicit permission.
However, the Engage Lab SDK introduced a flaw that allowed malicious apps to bypass these restrictions. The SDK failed to implement proper security checks, which could be exploited to gain unauthorized access, as noted in Microsoft's detailed report.
Technical Breakdown
When an app using the vulnerable SDK is installed, it inadvertently grants the malicious app access to sensitive data through weak permission checks. This is akin to leaving a backdoor open for intruders.
Here's a simplified code snippet illustrating the oversight:
java// Flawed permission check
if (user Has Granted Permission()) {
// Proceed to access sensitive data
access Sensitive Data();
}
// Missing proper validation
Real-World Example
Consider a popular banking app that uses the Engage Lab SDK for analytics. A malicious app installed on the same device could exploit the vulnerability to access the banking app's stored credentials, leading to unauthorized transactions, as explained in USA Today's report on mobile security trends.
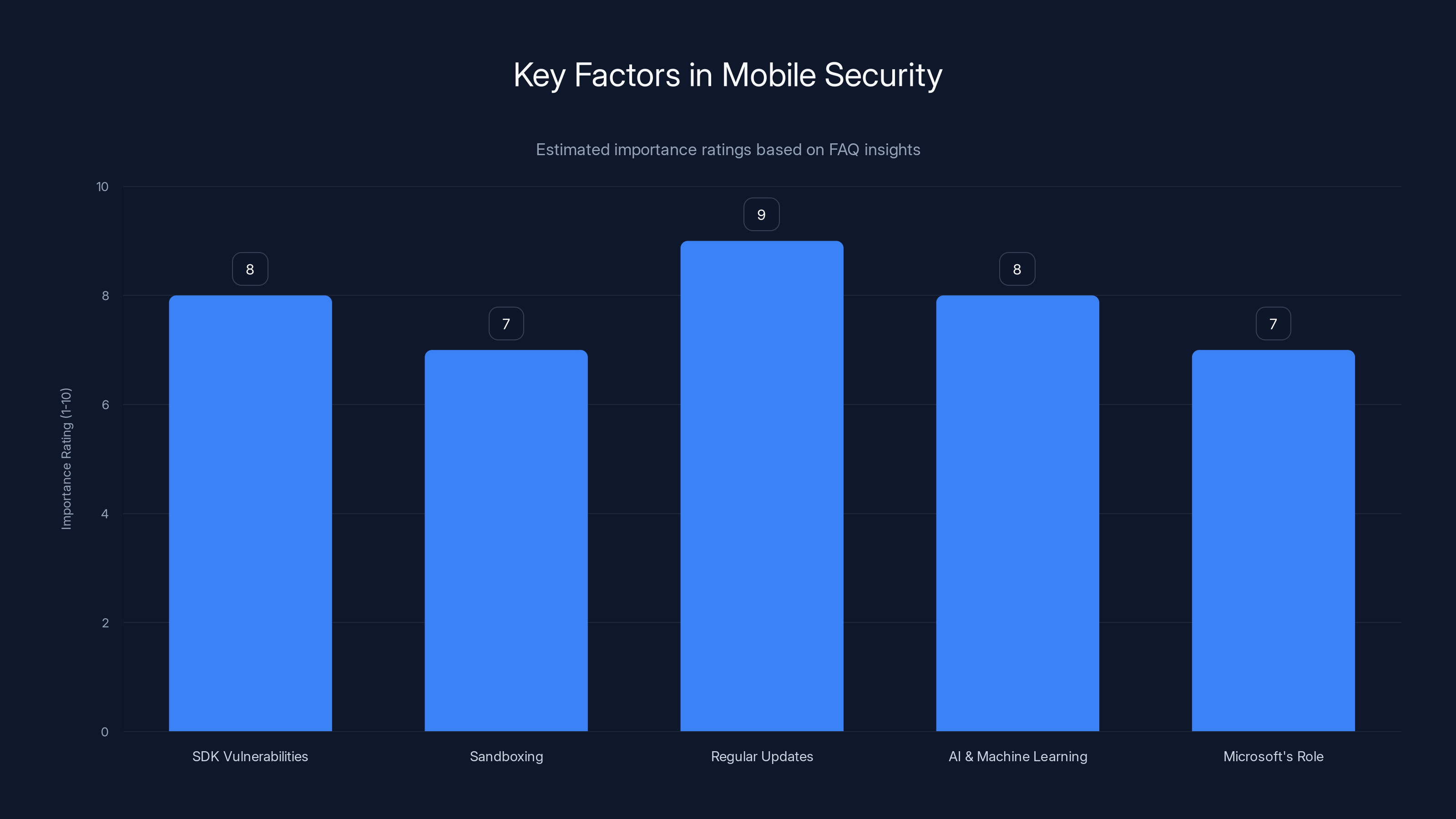
Regular updates are rated as the most important factor in mobile security, closely followed by AI and machine learning. (Estimated data)
Best Practices for Users
Protecting Your Data
- Update Regularly: Ensure all apps and the Android OS are updated to the latest versions, as updates often include security patches.
- Review Permissions: Regularly check app permissions and revoke any that seem unnecessary.
- Install Trusted Apps: Only download apps from reputable sources such as the Google Play Store, as recommended by TechLapse.
What Developers Can Do
- Audit SDKs: Developers should routinely audit third-party SDKs for vulnerabilities before integration.
- Implement Robust Security Checks: Always validate permissions and ensure data access is appropriately restricted.
- Monitor for Updates: Stay informed about SDK updates and security advisories from providers.

The Role of Microsoft and Security Vendors
How Microsoft Identified the Flaw
Microsoft's security research team used advanced scanning tools to identify anomalies in app behavior that indicated a potential security breach. Their proactive approach highlights the importance of continuous monitoring in the cybersecurity landscape, as discussed in Microsoft's security blog.
Steps Taken Post-Discovery
Upon discovering the flaw, Microsoft promptly notified Google and affected developers, leading to a coordinated effort to patch the vulnerability.

Future Trends in Mobile Security
Enhanced Security Measures
As mobile security threats evolve, so too must the defenses. We can expect to see:
- Advanced AI-powered monitoring to detect and prevent anomalies in real-time.
- Stronger sandboxing techniques to ensure even more secure app isolation.
- Increased focus on SDK security audits before integration, as highlighted in Anthropic's Glasswing project.
Regulatory Impacts
Governments and regulatory bodies may implement stricter data protection regulations, requiring developers to adhere to higher security standards.

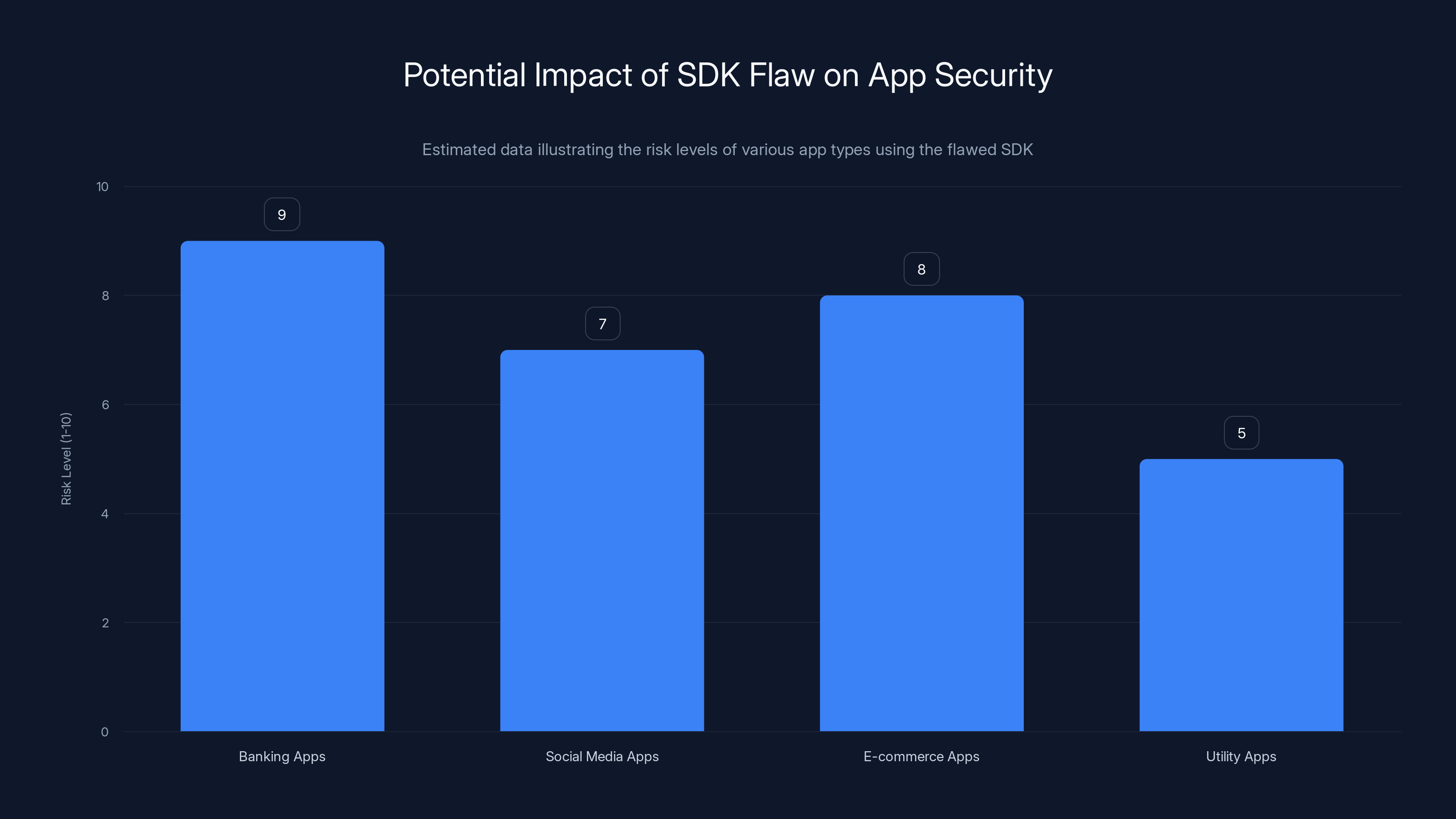
Banking apps face the highest risk from the SDK flaw due to sensitive data exposure. Estimated data highlights potential security concerns.
Practical Implementation Guides
Securing Your Android Device
- Enable Two-Factor Authentication (2FA): Adds an extra layer of security by requiring a second form of verification.
- Use a Password Manager: Helps generate and store strong, unique passwords.
- Install Mobile Security Apps: Consider apps that offer real-time scanning and threat detection.
plaintextExample of 2FA: 1. Enter your password. 2. Receive a one-time code via SMS. 3. Input the code to gain access.
For Developers: Strengthening App Security
- Implement Encryption: Encrypt sensitive data both in transit and at rest.
- Regular Code Audits: Conduct regular audits to identify and fix vulnerabilities.
- Engage with Security Experts: Collaborate with cybersecurity professionals for comprehensive security assessments.

Common Pitfalls and Solutions
Overlooking SDK Updates
Problem: Developers often integrate SDKs and forget to update them as new versions are released.
Solution: Set up automated notifications for SDK updates and prioritize their integration.
Inadequate Permission Management
Problem: Apps request excessive permissions that users blindly accept.
Solution: Implement a permission review process to ensure only necessary permissions are requested.
Case Study: Successful Mitigation
Company X's Response to the Vulnerability
Company X, a leading financial app developer, swiftly responded to the Microsoft alert by:
- Conducting an immediate security audit of their app and associated SDKs.
- Releasing a patch within 48 hours to address the vulnerability.
- Communicating transparently with users about the potential risk and steps taken.
Outcome:
- No reported data breaches.
- Increased user trust and engagement.

Predictions and Recommendations
The Future of SDK Security
- Automated Security Scanning: Expect to see more tools that automatically scan SDKs for vulnerabilities during the integration process.
- Security Certifications for SDKs: As with software, SDKs may soon require security certifications to assure developers of their safety.
Recommendations for Stakeholders
- For Users: Stay informed about app updates and security news.
- For Developers: Prioritize security in the development lifecycle from design to deployment.
- For Vendors: Offer comprehensive support and timely updates for their SDKs.
Conclusion
The recent security flaw exposed by Microsoft underscores the ever-present risks in our digital lives. By understanding the nature of these vulnerabilities and implementing best practices, both users and developers can better protect themselves against potential threats. As technology continues to evolve, so too must our approach to security.

FAQ
What is an SDK vulnerability?
An SDK vulnerability refers to a flaw within a software development kit that can be exploited by malicious actors to bypass security measures and access sensitive data.
How does sandboxing protect Android devices?
Sandboxing isolates apps in separate environments, preventing them from accessing each other's data without explicit permission, thereby enhancing device security.
What should users do if their device is affected?
Users should immediately update all apps and the Android operating system, review app permissions, and consider installing a mobile security app.
How can developers prevent future vulnerabilities?
Developers should regularly audit SDKs for vulnerabilities, implement robust security checks, and stay informed about the latest security advisories and updates.
Why is regular app updating important?
Regular updates ensure that apps have the latest security patches, protecting users from known vulnerabilities and potential exploits.
What role do AI and machine learning play in mobile security?
AI and machine learning enhance security by detecting anomalies and potential threats in real-time, allowing for faster response and mitigation.
How does Microsoft contribute to mobile security?
Microsoft conducts security research and identifies vulnerabilities, working with developers and vendors to patch them and protect users.
What trends can we expect in mobile security?
Expect more advanced security measures, regulatory impacts, and a focus on SDK security, driven by AI and machine learning advancements.
Key Takeaways
- Over 50 million Android users affected by a critical security flaw.
- Vulnerability allowed apps to bypass sandbox protections.
- User credentials and financial data were at risk of exposure.
- Microsoft led the discovery and notification of the flaw.
- Regular updates and permission reviews are essential for security.
- Future trends include AI-driven security enhancements and SDK audits.
- Developers must prioritize security in the app development lifecycle.
- Regulatory bodies may impose stricter data protection standards.
Related Articles
- Mastering iPhone Privacy: Essential Settings for Ultimate Security [2025]
- The Autonomous Frontier: Rethinking Security with Mythos [2025]
- Project Glasswing: AI Cybersecurity's New Vanguard [2025]
- Safeguarding Older Apple Devices from DarkSword Attacks: A Comprehensive Guide [2025]
- CareCloud Data Breach: Details, Solutions, and Future Safeguards [2025]
- How to Stay Safe with Apple’s Critical iOS Software Alerts [2025]
![Microsoft's Warning: Security Flaw Puts 50 Million Android Users at Risk [2025]](https://tryrunable.com/blog/microsoft-s-warning-security-flaw-puts-50-million-android-us/image-1-1775837084698.jpg)



