National Security at Risk: The Fallout of Over 3,500 US Legislators' Emails Exposed on the Dark Web [2025]
The digital landscape is fraught with perils, and nowhere is this more apparent than in the realm of cybersecurity. A recent study by Proton reveals a staggering number of over 3,500 US legislators' official emails have been leaked and are circulating on the dark web. This revelation raises profound questions about national security, data privacy, and the integrity of governmental communications.
TL; DR
- Over 3,500 US legislators' emails have been leaked, posing a significant threat.
- National security risks are heightened due to potential cyber espionage and misinformation.
- Dark web dynamics make tracking and retrieval of leaked data challenging.
- Enhanced cybersecurity measures are urgently needed to safeguard sensitive data.
- Future trends include increased reliance on AI-driven security solutions and blockchain technology.
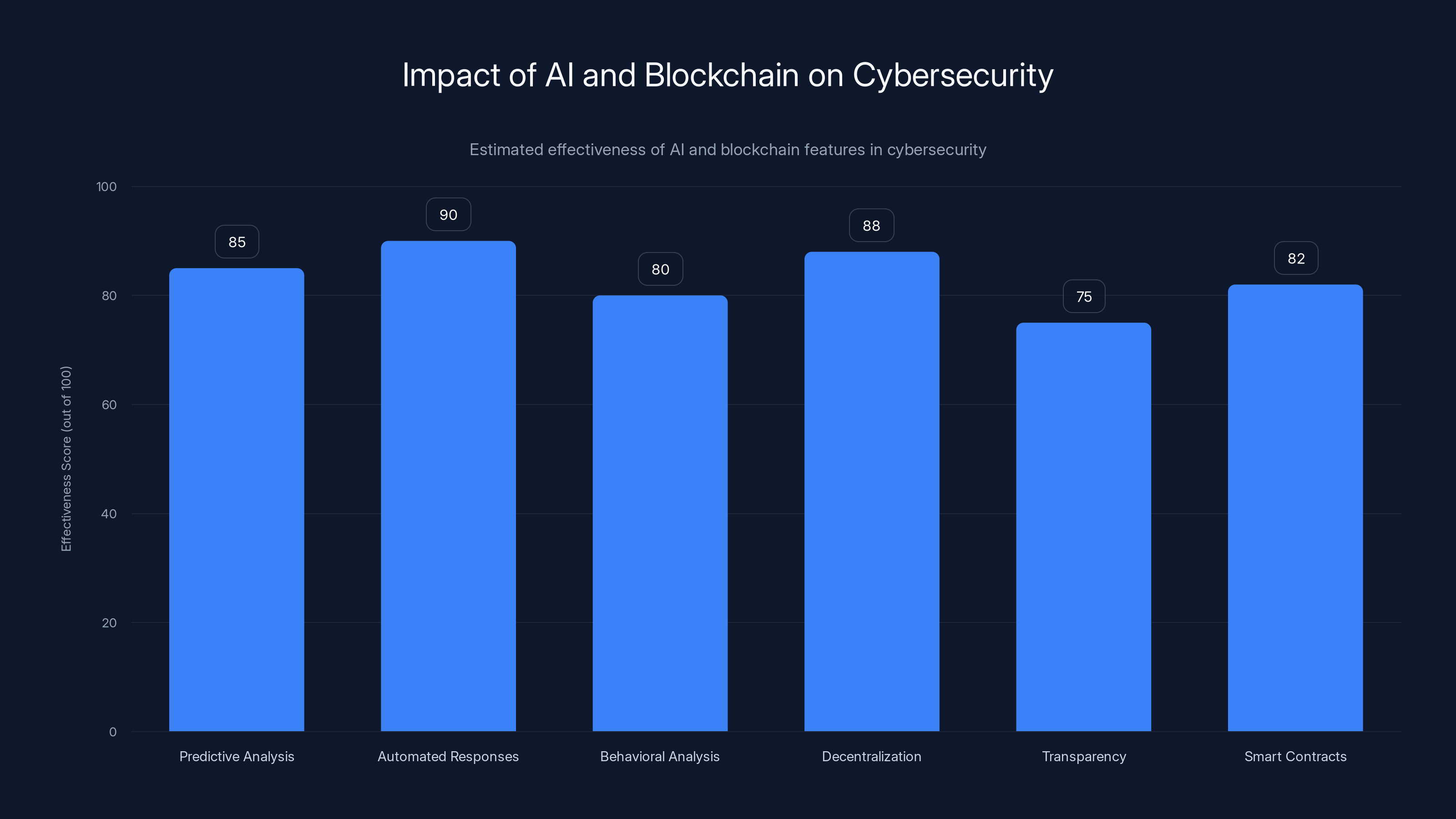
AI-driven solutions and blockchain technology are projected to significantly enhance cybersecurity, with automated responses and decentralization leading in effectiveness. Estimated data.
The Scale of the Leak
The Proton study has brought to light a critical issue: the exposure of thousands of official government email addresses on the dark web. But this is just the tip of the iceberg. The repercussions of such data exposure are far-reaching, affecting not just the individuals involved but potentially the entire nation.
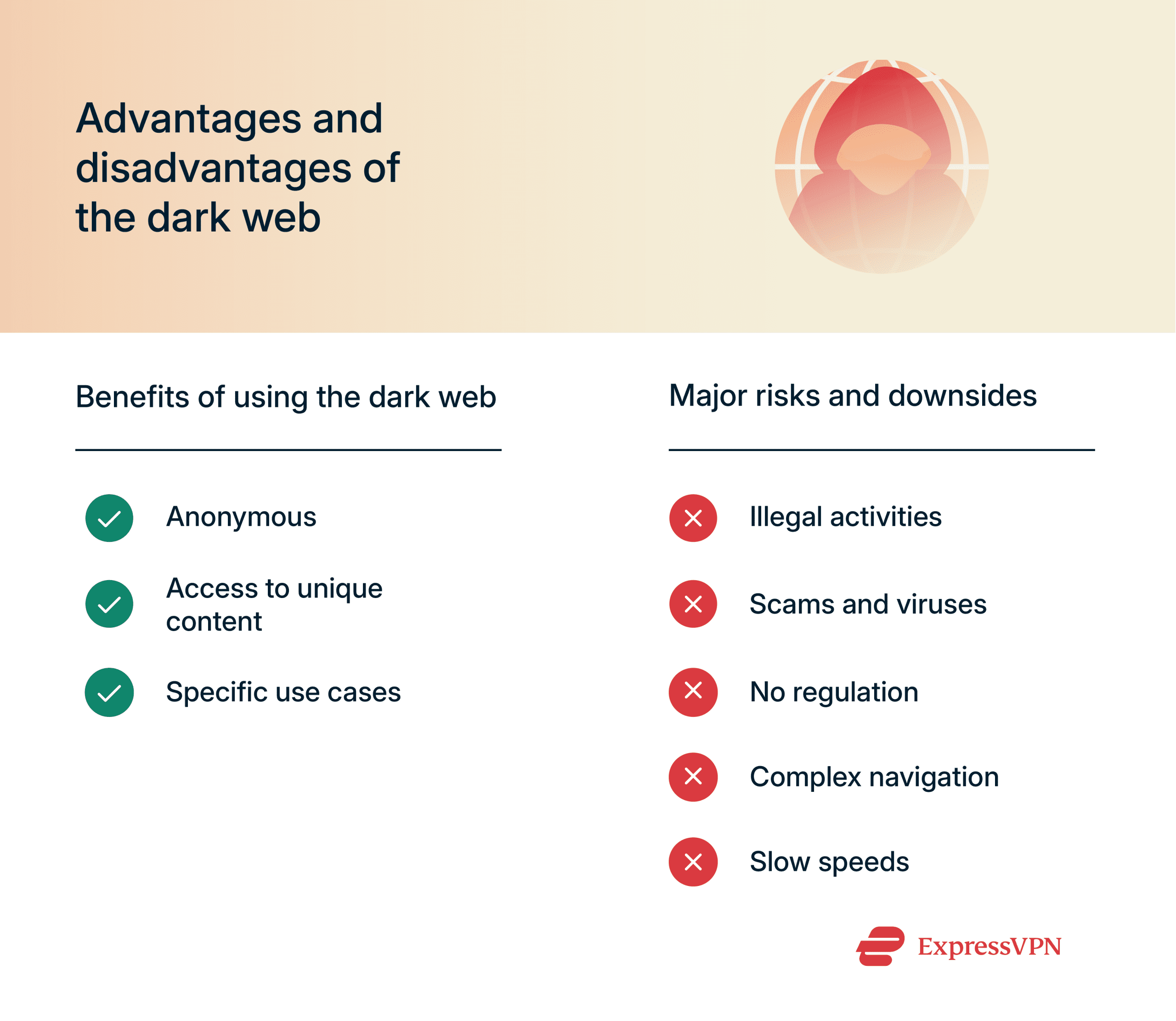
Understanding the Dark Web
The dark web is often misunderstood. It's a part of the internet that isn't indexed by traditional search engines and requires specific software, like Tor, to access. While it serves legitimate purposes, such as ensuring privacy in oppressive regimes, it also hosts illicit activities, including the trade of stolen data.
The dark web's anonymity is a double-edged sword. On one hand, it provides privacy and security for those in need. On the other, it facilitates criminal activities, making it an ideal marketplace for stolen data, including the leaked emails of US legislators.
The Immediate Threats
The exposure of these emails presents several immediate threats:
- Cyber Espionage: Malicious actors could use these emails to gain unauthorized access to sensitive information or as entry points for phishing attacks.
- Misinformation Campaigns: Leaked emails can be manipulated to spread false information, affecting public opinion and political stability.
- Identity Theft: Personal and professional details can be exploited for identity theft, leading to financial and reputational damage.
Case Study: The DNC Email Leak
A historical precedent can be found in the 2016 Democratic National Committee (DNC) email leak, which had significant political repercussions. The emails were used to influence public perception and had lasting impacts on the political landscape.

Two-factor authentication is estimated to be the most effective practice, blocking up to 99.9% of automated attacks. Estimated data based on typical effectiveness.
The Role of Cybersecurity in Government
In light of these threats, the role of cybersecurity in government cannot be overstated. Effective cybersecurity measures can prevent unauthorized access, protect sensitive data, and ensure the integrity of governmental communications.
Best Practices for Government Cybersecurity
- Regular Security Audits: Conduct frequent security audits to identify and address vulnerabilities.
- Two-Factor Authentication (2FA): Implement 2FA to add an extra layer of security to email accounts.
- Encryption: Use encryption to protect sensitive data both at rest and in transit.
- Cybersecurity Training: Provide comprehensive cybersecurity training for all government employees to recognize and mitigate threats.
Common Pitfalls and Solutions
Pitfall: Neglecting Regular Updates
Solution: Ensure all software and systems are up to date with the latest security patches to protect against known vulnerabilities.
Pitfall: Lack of Employee Training
Solution: Conduct regular training sessions to educate employees on recognizing phishing attempts and other cyber threats.

The Dark Web: A Double-Edged Sword
While the dark web poses significant challenges, it also offers insights into cybercriminal activities. Law enforcement agencies can monitor dark web activities to identify and mitigate threats before they escalate.
Navigating the Dark Web Safely
- Use of Tor Browser: Access the dark web anonymously and securely using the Tor browser.
- Legal Monitoring: Authorities should leverage legal means to monitor dark web activities for potential threats.
- Collaboration with Cybersecurity Firms: Partner with cybersecurity firms specializing in dark web monitoring to identify and address threats.
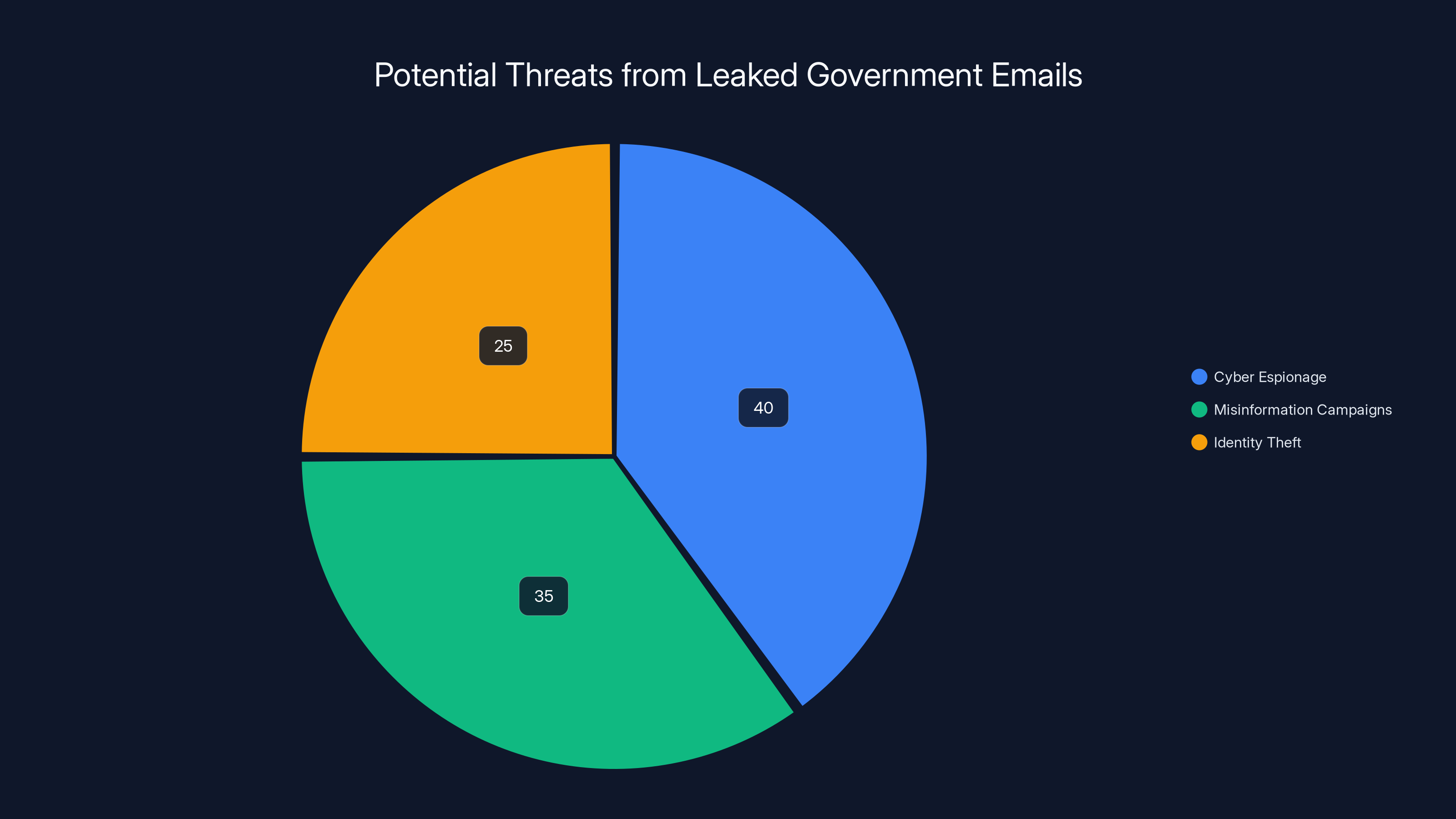
Cyber espionage poses the largest threat at 40%, followed by misinformation campaigns at 35%, and identity theft at 25%. Estimated data based on potential risks.
The Future of Cybersecurity
As technology evolves, so too must cybersecurity measures. The future of cybersecurity will likely see increased reliance on AI-driven solutions and blockchain technology to secure communications and protect sensitive data.
AI-Driven Security Solutions
AI can enhance cybersecurity by:
- Predictive Analysis: Identifying potential threats before they occur.
- Automated Responses: Quickly responding to threats in real-time.
- Behavioral Analysis: Detecting anomalies in user behavior to prevent unauthorized access.
Blockchain Technology
Blockchain offers a decentralized approach to data security, ensuring the integrity and authenticity of communications and transactions.
- Decentralization: Eliminates single points of failure, enhancing security.
- Transparency: Provides a transparent and immutable record of transactions.
- Smart Contracts: Automate processes and enforce security protocols without human intervention.
Recommendations for Government Agencies
- Invest in Advanced Cybersecurity Solutions: Allocate resources to adopt cutting-edge cybersecurity technologies like AI and blockchain.
- Foster Collaboration: Collaborate with private sector cybersecurity firms to leverage their expertise and resources.
- Develop a Cybersecurity Culture: Promote a culture of cybersecurity awareness and responsibility among employees.
- Regularly Review and Update Policies: Ensure cybersecurity policies are regularly reviewed and updated to address emerging threats.
Conclusion
The exposure of over 3,500 US legislators' emails on the dark web is a wake-up call for governments worldwide. It underscores the urgent need for robust cybersecurity measures to protect sensitive information and maintain national security. By embracing advanced technologies and fostering a culture of cybersecurity, governments can mitigate risks and safeguard their communications in an increasingly digital world.
FAQ
What is the dark web?
The dark web is a part of the internet that is not indexed by traditional search engines and requires special software, like Tor, to access. It is often associated with illegal activities but also serves legitimate purposes.
How can emails be leaked to the dark web?
Emails can be leaked to the dark web through data breaches, phishing attacks, or when individuals inadvertently share their credentials on insecure platforms.
What are the risks of having emails exposed on the dark web?
The risks include cyber espionage, misinformation campaigns, identity theft, and unauthorized access to sensitive information.
How can governments protect against email leaks?
Governments can protect against email leaks by implementing strong cybersecurity measures, such as two-factor authentication, encryption, and regular security audits.
What role does AI play in cybersecurity?
AI enhances cybersecurity by providing predictive analysis, automated threat responses, and behavioral analysis to detect anomalies and prevent unauthorized access.
How does blockchain improve cybersecurity?
Blockchain improves cybersecurity by providing a decentralized, transparent, and immutable record of transactions, eliminating single points of failure and enhancing data integrity.
Why is cybersecurity important for governments?
Cybersecurity is crucial for governments to protect sensitive information, maintain national security, and ensure the integrity of governmental communications.
What future trends can we expect in cybersecurity?
Future trends in cybersecurity include the increased use of AI-driven solutions, blockchain technology, and a greater emphasis on fostering a culture of cybersecurity awareness.
Key Takeaways
- Over 3,500 US legislators' emails leaked on dark web pose national security threat.
- Cyber espionage and misinformation campaigns are major risks of leaked emails.
- Dark web's anonymity complicates tracking and retrieval of leaked data.
- Governments must enhance cybersecurity measures to protect sensitive data.
- AI-driven security solutions and blockchain will play key roles in future cybersecurity.
Related Articles
- Understanding the LAPD Data Breach: Lessons and Future Safeguards [2025]
- Infrastructure-Level Analysis in Cybersecurity: Lessons from Lazarus and Kimsuky [2025]
- Unmasking SVG Steganography: How Hackers Use Tiny Images to Hide Credit Card Skimmers [2025]
- How Digital Devices Endanger Our Privacy Rights [2025]
- Reimagining FISA Section 702: Closing Surveillance Loopholes [2025]
- Unlock the Future of Tech: Last Chance to Save $500 on Your Disrupt 2026 Pass [2025]
![National Security at Risk: The Fallout of Over 3,500 US Legislators' Emails Exposed on the Dark Web [2025]](https://tryrunable.com/blog/national-security-at-risk-the-fallout-of-over-3-500-us-legis/image-1-1775838896296.jpg)



