Infrastructure-Level Analysis in Cybersecurity: Lessons from Lazarus and Kimsuky [2025]
Cybersecurity is a constantly evolving field, and in recent years, the complexity and scale of cyber threats have increased significantly. Two groups that have consistently been at the forefront of these threats are the Lazarus Group and Kimsuky. These North Korean cyberwarfare units have demonstrated time and again why infrastructure-level analysis is not just beneficial, but crucial for effective cybersecurity.
TL; DR
- Infrastructure-level analysis is essential to identify threats like Lazarus and Kimsuky.
- Advanced persistent threats (APTs) exploit infrastructure vulnerabilities.
- Real-world case studies illustrate the effectiveness of infrastructure analysis.
- Future cybersecurity will heavily rely on infrastructure monitoring.
- Actionable steps include adopting infrastructure analysis tools and practices.

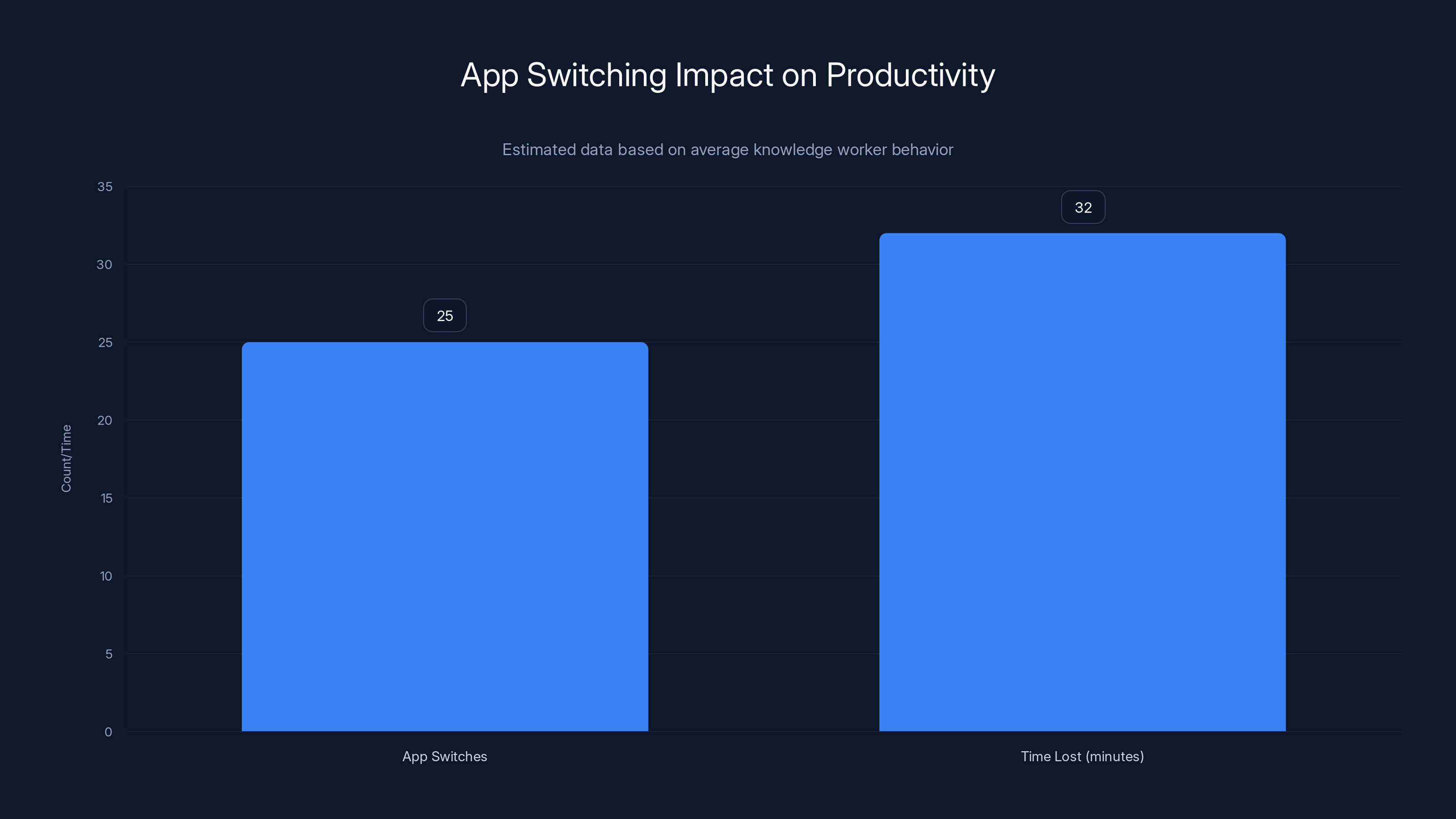
Knowledge workers switch apps 25 times daily, losing 32 minutes to context switching. Estimated data.
Understanding the Threat Landscape
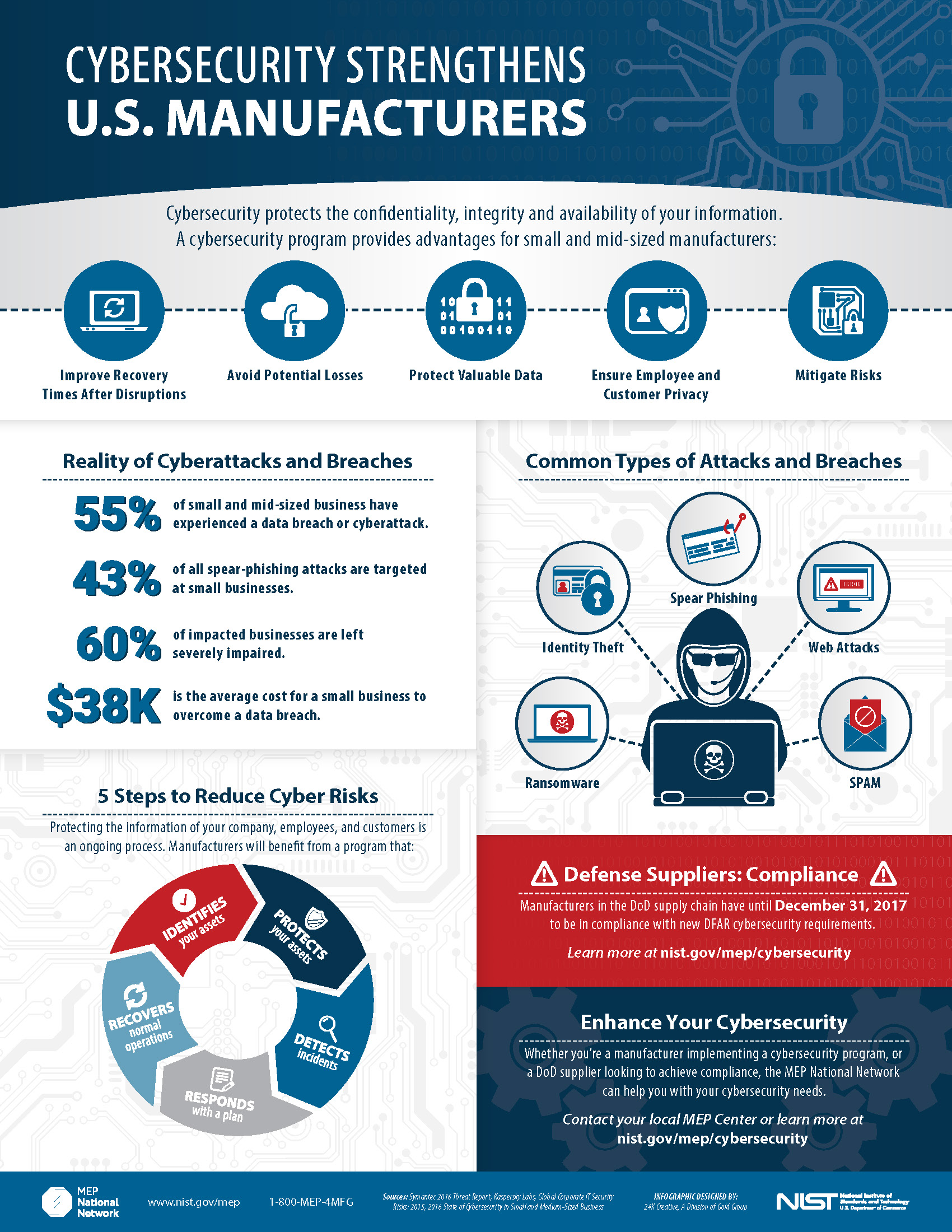
Cybercriminal groups like Lazarus and Kimsuky have been operating for years, often with the backing of state actors. These groups specialize in advanced persistent threats (APTs), which are prolonged and targeted cyberattacks aimed at stealing data or disrupting operations.
The Lazarus Group
The Lazarus Group is known for its sophisticated attacks on financial institutions and has been linked to major incidents like the Sony Pictures hack and the Wanna Cry ransomware attack. Their operations often involve exploiting infrastructure vulnerabilities to infiltrate networks and exfiltrate sensitive data.
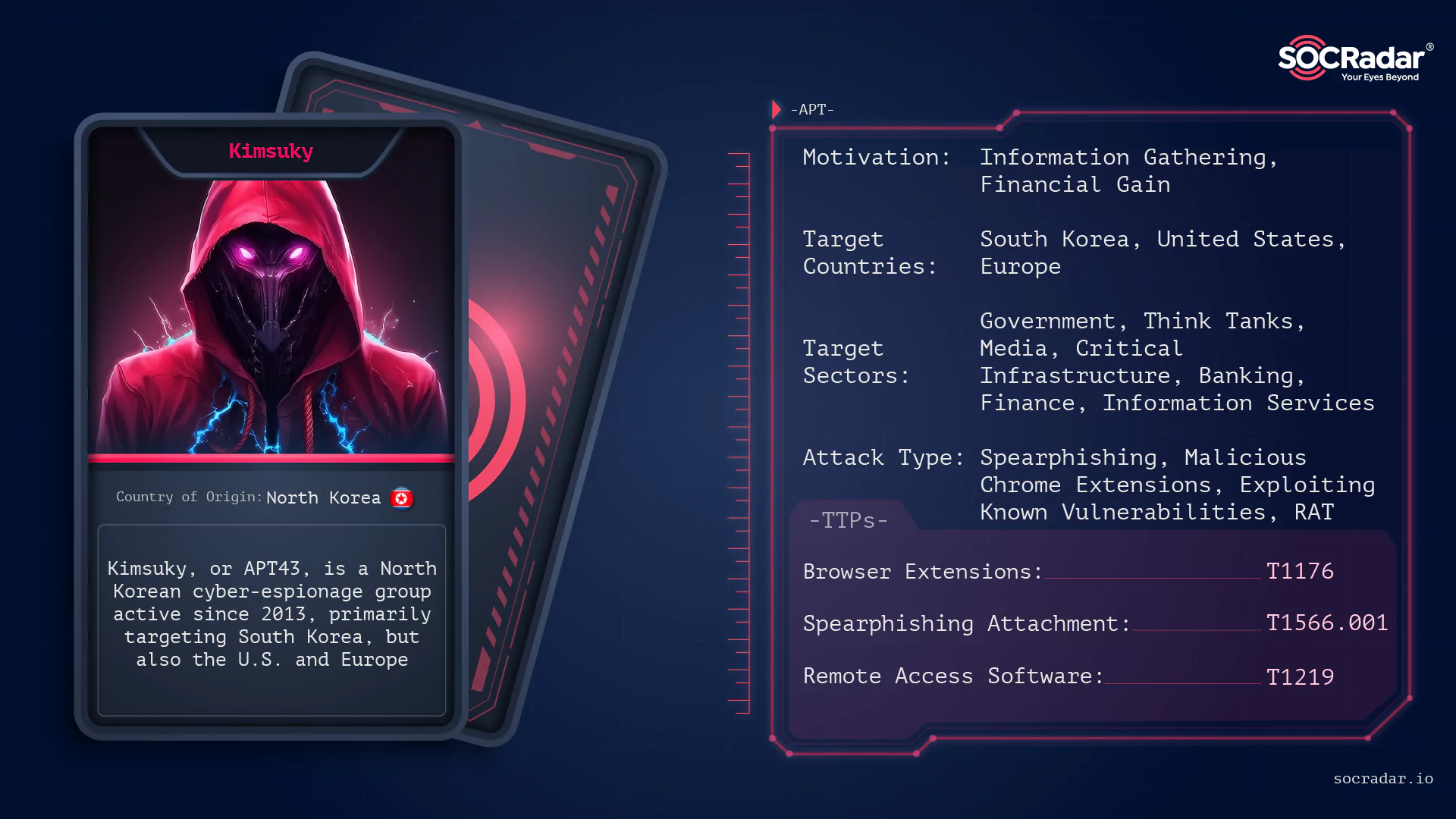
Kimsuky
Kimsuky, on the other hand, focuses on espionage activities, targeting government entities and think tanks. Their modus operandi involves phishing campaigns and malware distribution, often exploiting infrastructure weaknesses to gain a foothold in their targets' networks.
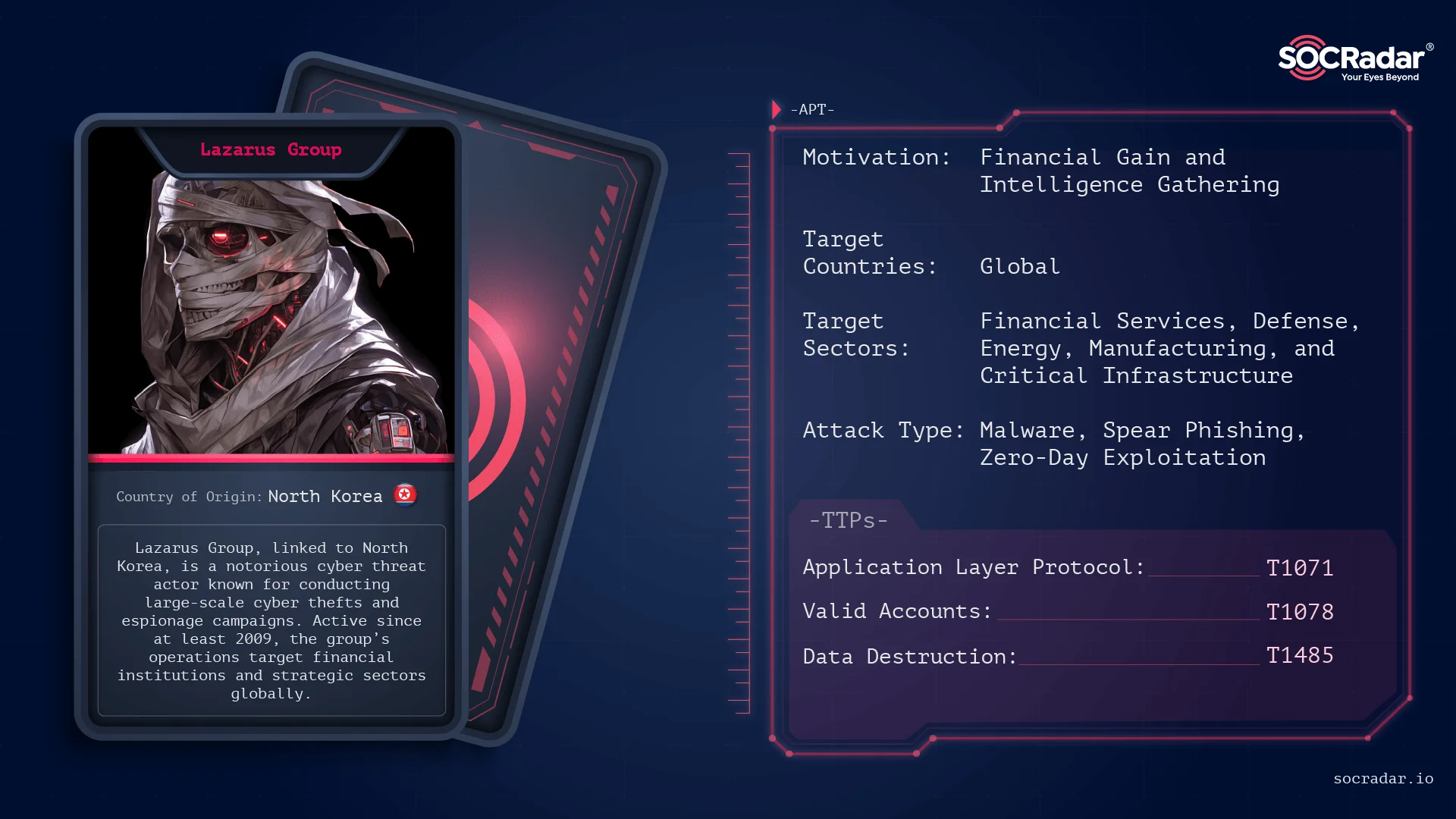

Lazarus and Kimsuky are leading in cyber threat activities, emphasizing the need for infrastructure-level analysis. Estimated data.
Why Infrastructure-Level Analysis Matters
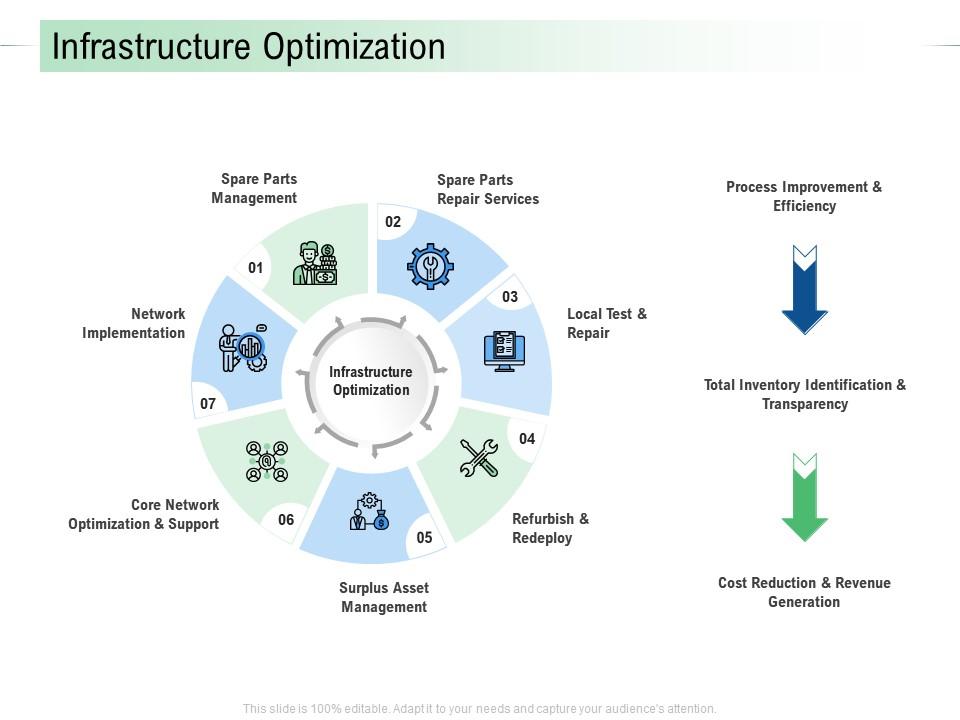
Infrastructure-level analysis refers to examining the foundational components of a network, such as servers, routers, firewalls, and other network devices. This approach helps identify vulnerabilities that could be exploited by attackers.
Key Benefits
- Comprehensive Visibility: Provides a holistic view of the network, identifying potential weak points before they are exploited.
- Proactive Defense: Enables the development of proactive defense strategies by understanding the attack vectors used by adversaries.
- Incident Response: Improves incident response capabilities by quickly isolating affected infrastructure components.
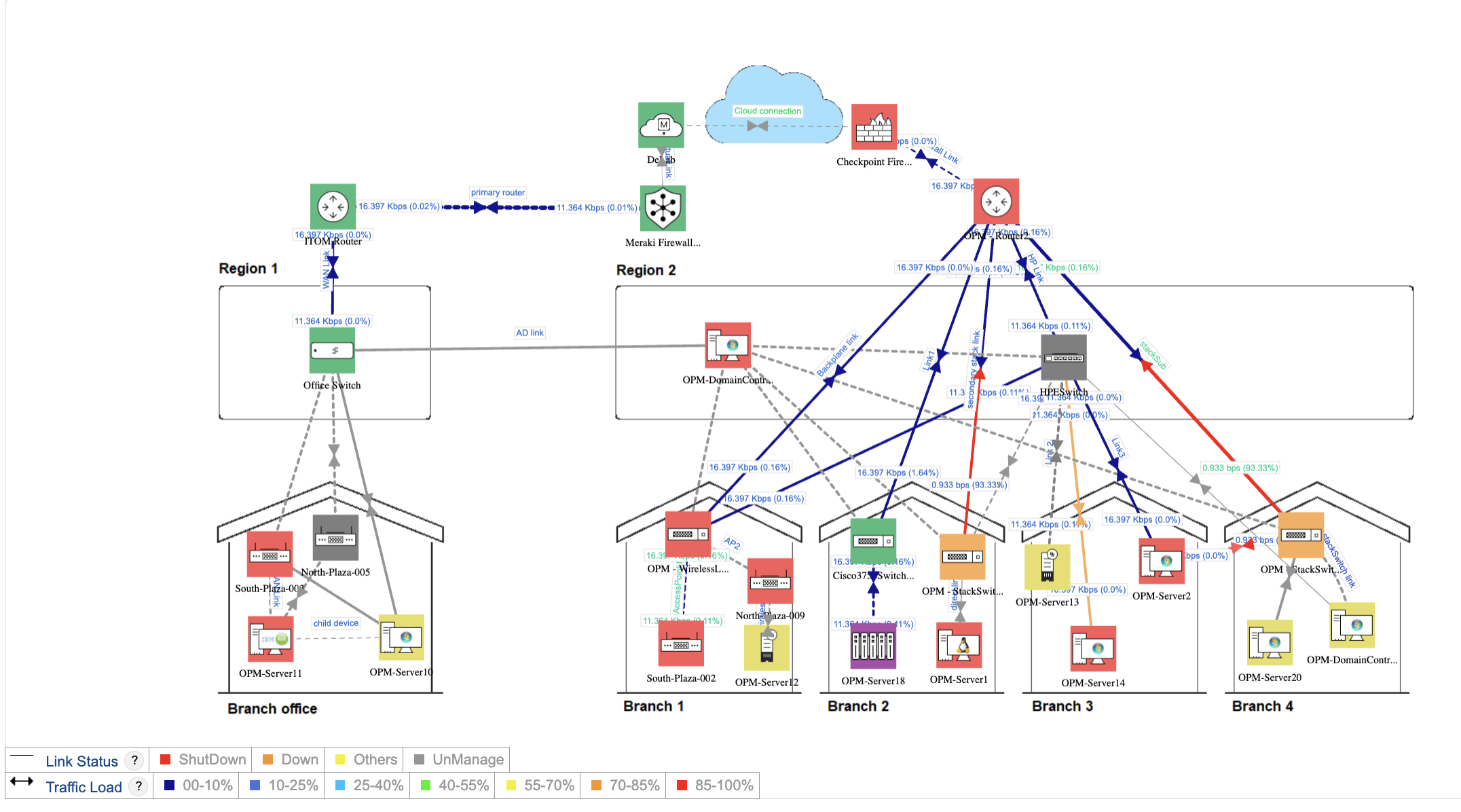
Practical Implementation of Infrastructure Analysis
Implementing infrastructure-level analysis requires a combination of tools, processes, and expertise. Here are some practical steps to get started:
- Network Mapping: Use tools like Nmap or Nessus to map the network and identify all connected devices.
- Vulnerability Scanning: Regularly scan the network for vulnerabilities using automated tools.
- Log Analysis: Implement log management solutions to analyze logs from various network devices and detect anomalies.
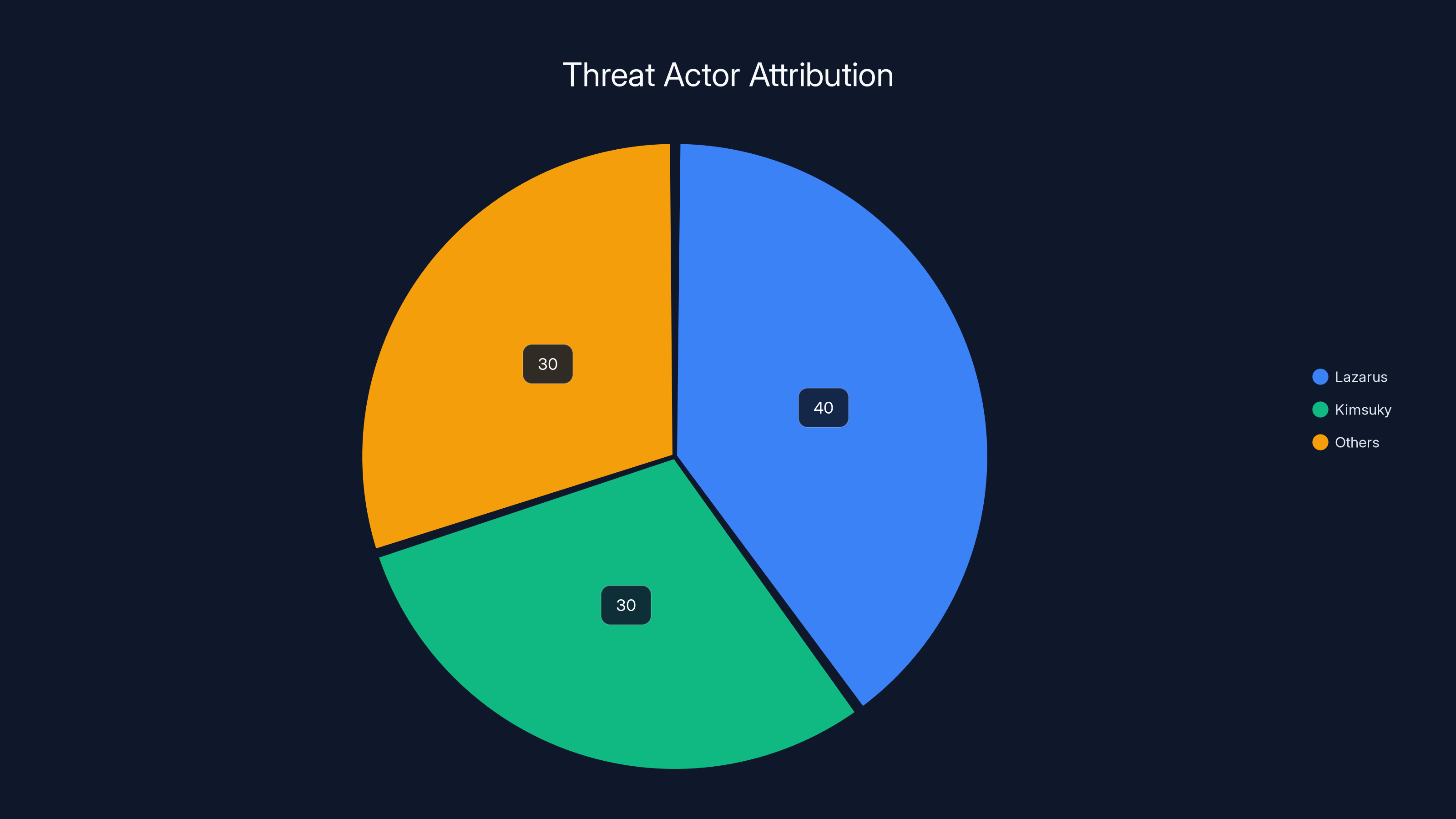
Lazarus and Kimsuky are responsible for a significant portion of cyberattacks, with each accounting for 30-40% of incidents. Estimated data.
Common Pitfalls and Solutions
While infrastructure-level analysis is crucial, there are common pitfalls that organizations may encounter. Here are some examples and how to address them:
Pitfall 1: Lack of Skilled Personnel
Solution: Invest in training and hire cybersecurity professionals with experience in infrastructure analysis.
Pitfall 2: Overwhelming Data Volume
Solution: Implement automated tools that can filter and prioritize alerts based on severity.
Pitfall 3: Inadequate Tool Integration
Solution: Ensure that all cybersecurity tools are integrated into a central management system for streamlined analysis.

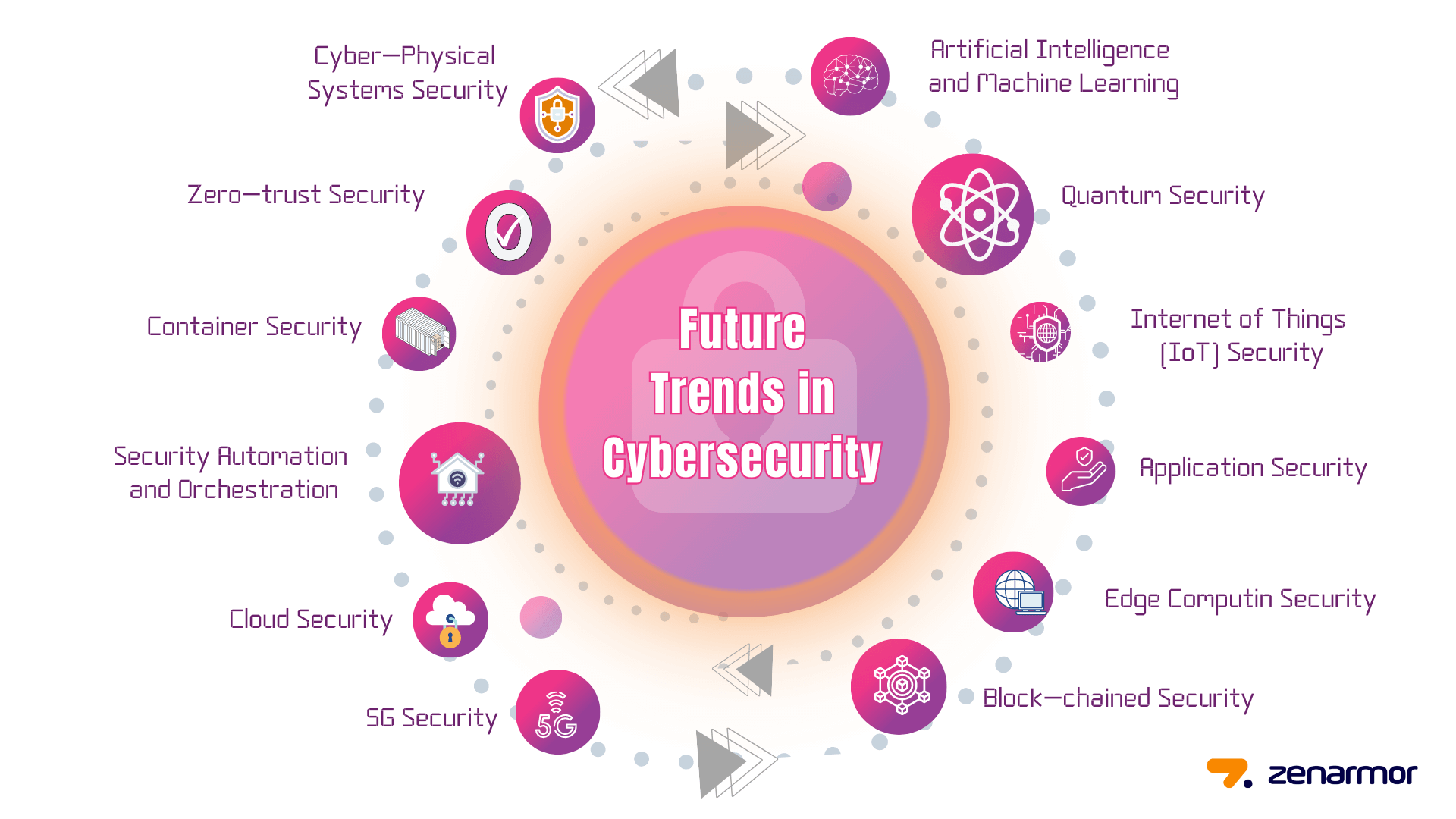
Future Trends in Infrastructure-Level Cybersecurity
As cyber threats continue to evolve, infrastructure-level analysis will become even more important. Here are some trends to watch:
- AI and Machine Learning: These technologies will enhance threat detection by identifying patterns and anomalies in network data.
- Cloud Security: As more organizations move to the cloud, securing cloud infrastructure will be a top priority.
- Io T Security: The increasing number of Io T devices will require robust infrastructure analysis to prevent breaches.
Recommendations for Organizations
To stay ahead of cyber threats, organizations should adopt the following best practices:
- Regular Audits: Conduct regular security audits to assess the health of your infrastructure.
- Adopt Zero Trust: Implement a Zero Trust architecture to minimize the risk of insider threats and lateral movement within the network.
- Continuous Monitoring: Utilize continuous monitoring solutions to detect and respond to threats in real-time.
Conclusion
Lazarus and Kimsuky have shown that infrastructure-level analysis is not just an option but a necessity in today's cybersecurity landscape. By focusing on the foundational components of networks, organizations can better protect themselves from sophisticated cyber threats.
FAQ
What is infrastructure-level analysis in cybersecurity?
Infrastructure-level analysis involves examining the foundational components of a network, such as servers, routers, and firewalls, to identify vulnerabilities and prevent cyberattacks.
How do Lazarus and Kimsuky use infrastructure to their advantage?
These groups exploit vulnerabilities in network infrastructure to infiltrate systems and exfiltrate sensitive data, often targeting financial institutions and government entities.
What tools are essential for infrastructure-level analysis?
Tools like Nmap for network mapping, Nessus for vulnerability scanning, and Splunk for log analysis are essential for comprehensive infrastructure-level analysis.
Why is AI important in future cybersecurity?
AI enhances threat detection by identifying patterns and anomalies in network data, enabling faster and more accurate responses to cyber threats.
How can organizations implement a Zero Trust architecture?
Organizations can implement Zero Trust by ensuring strict identity verification, micro-segmentation of networks, and continuous monitoring of user activities.
Key Takeaways
- Infrastructure-level analysis is crucial in cybersecurity.
- Lazarus and Kimsuky exploit infrastructure vulnerabilities.
- Proactive defense strategies are enabled by infrastructure analysis.
- AI and machine learning enhance threat detection.
- Zero Trust architecture minimizes insider threats.
Related Articles
- The Dark Side of Cybersecurity: NHS Scotland Domains and the Hidden Threats [2025]
- Unmasking SVG Steganography: How Hackers Use Tiny Images to Hide Credit Card Skimmers [2025]
- Understanding the LAPD Data Breach: Lessons and Future Safeguards [2025]
- How Emojis Are Reshaping Cybercrime Tactics: A Deep Dive [2025]
- Understanding the LAPD Data Breach: Lessons in Cybersecurity [2025]
- Samsung Galaxy S22 Ultra Factory Reset Hijack: Understanding the Issue and Solutions [2025]
![Infrastructure-Level Analysis in Cybersecurity: Lessons from Lazarus and Kimsuky [2025]](https://tryrunable.com/blog/infrastructure-level-analysis-in-cybersecurity-lessons-from-/image-1-1775819053818.jpg)



