Unmasking SVG Steganography: How Hackers Use Tiny Images to Hide Credit Card Skimmers [2025]
Last month, a security researcher discovered a new trick in the hacker playbook—using 1x 1 pixel SVG images to hide credit card skimmers. This revelation sent waves across the cybersecurity community, highlighting how even the smallest details can harbor significant threats.
TL; DR
- Tiny SVG images: Hackers hide malicious code in 1x 1 pixel SVG images, as detailed in a report by BleepingComputer.
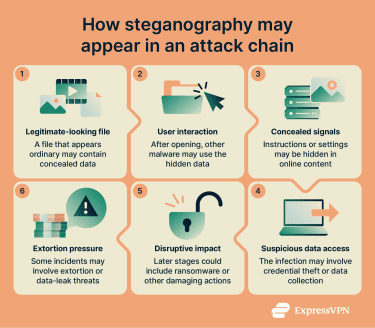
- Steganography: This technique is known as steganography, where data is concealed within other data.
- Magento vulnerability: The skimmers often exploit known vulnerabilities, like Magento Poly Shell.
- Detection challenges: Small image size makes detection difficult.
- Future predictions: Expect more sophisticated steganography techniques in cybercrime.
- Protection measures: Regular security audits and monitoring for unusual activity are crucial.
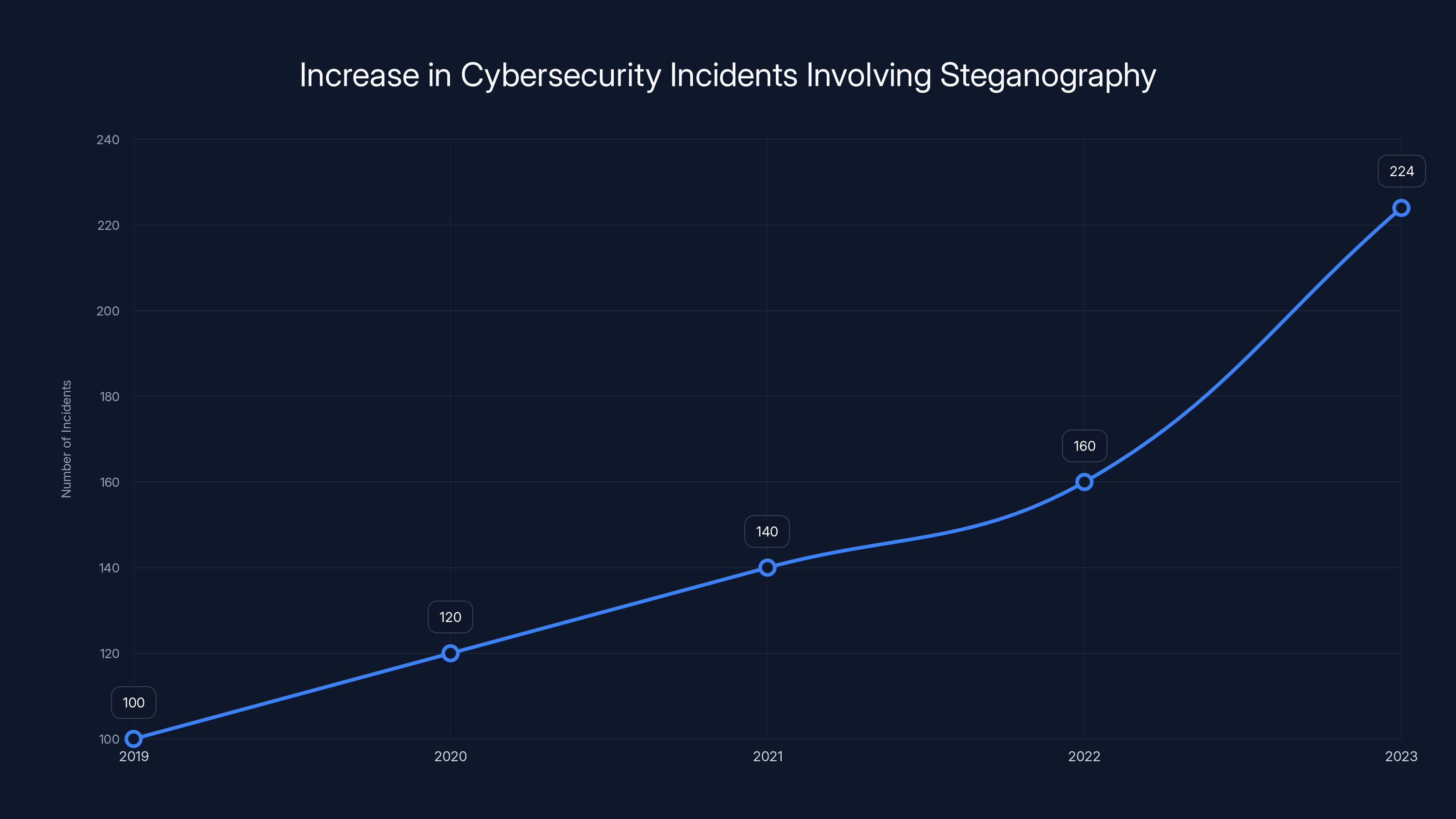
Cybersecurity incidents involving steganography have increased by 40% in the past year, highlighting the growing threat of hidden malicious code. Estimated data.
The Rise of SVG Steganography
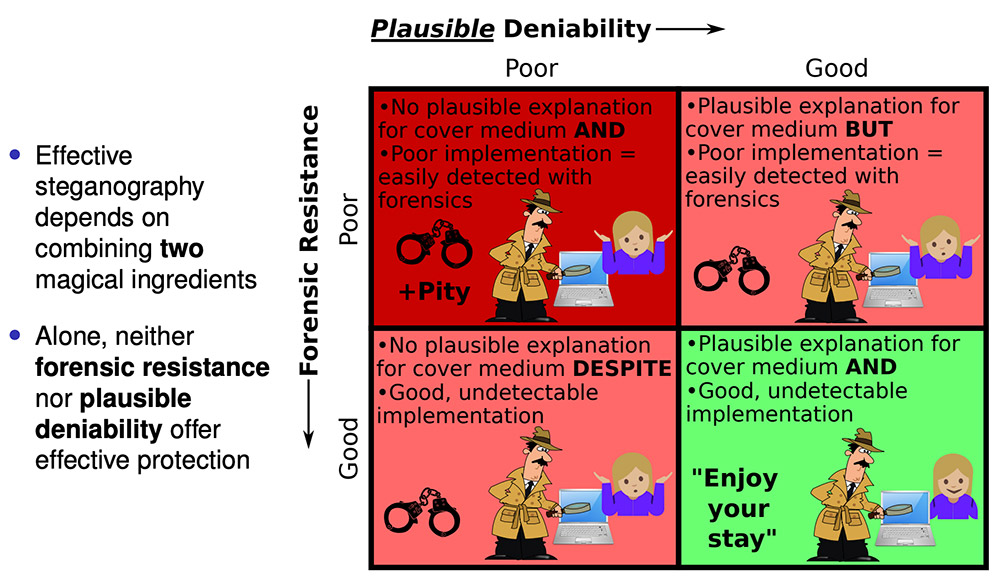
Steganography, the art of hiding messages in plain sight, is not new. But using SVG (Scalable Vector Graphics) images for this purpose is a novel twist. SVG images are text-based and can include scripts, making them ideal for embedding malicious code without raising suspicion.
What Makes SVGs Ideal for Steganography?
SVGs are versatile. They are XML-based and can be manipulated with CSS and JavaScript. This flexibility allows hackers to insert malicious scripts that activate when the image is processed by a browser.
Key Features of SVGs:
- Scalability: SVGs can be scaled without losing quality, making them useful across different platforms.
- Text-based: Being XML-based allows easy manipulation of SVG content.
- Scriptability: Supports the inclusion of JavaScript, enabling dynamic content.
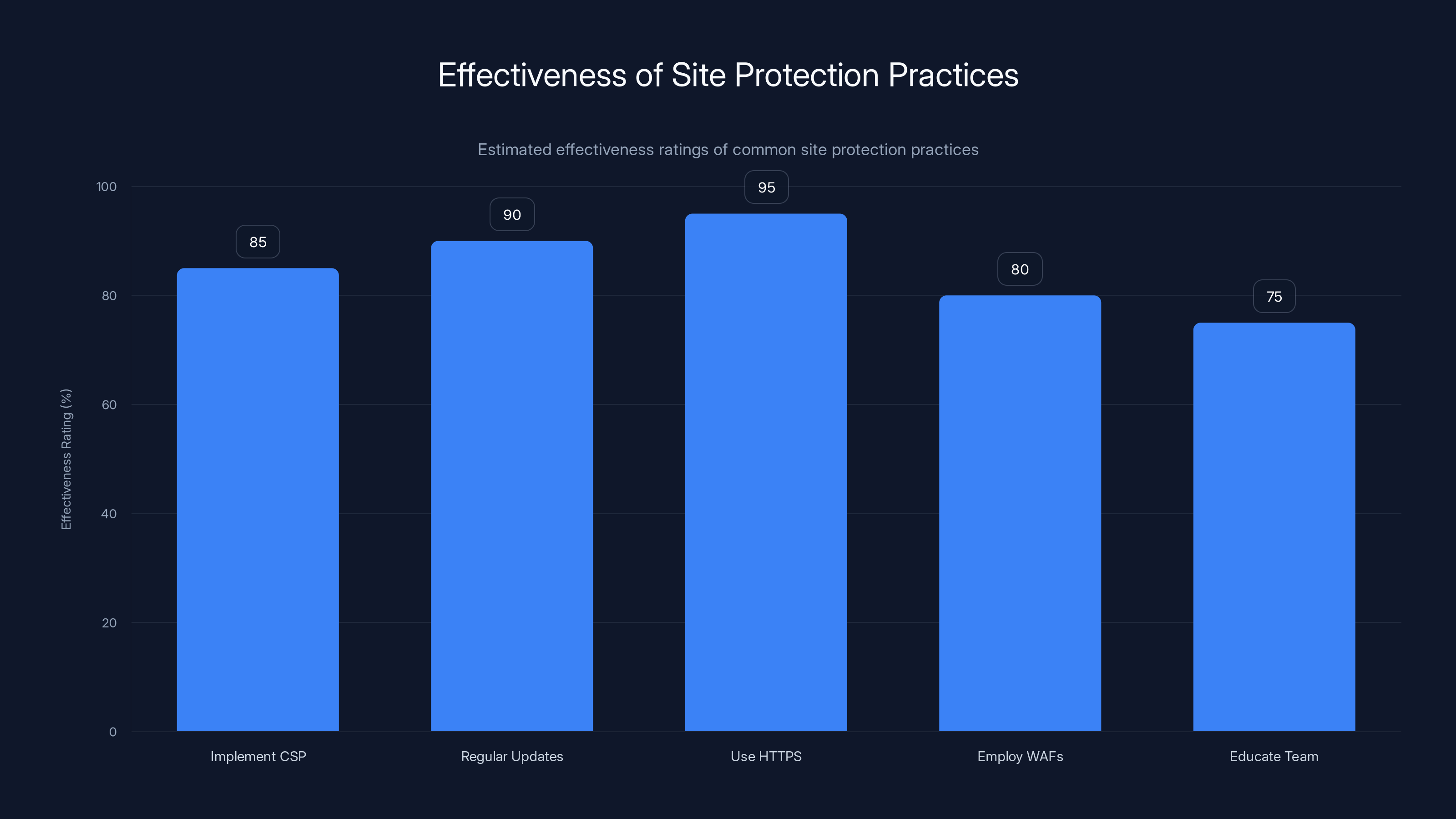
Regular updates and using HTTPS are estimated to be the most effective practices, with ratings of 90% and 95% respectively. (Estimated data)
How Hackers Exploit SVGs
The 1x 1 Pixel Trick
By creating a 1x 1 pixel SVG image, hackers can embed scripts that execute malicious tasks, such as stealing credit card information during an online transaction. The image is so small it is invisible to the naked eye, making it an effective tool for covert operations.
Example of a 1x 1 SVG Image Code:
xml<svg width="1" height="1" xmlns="http://www.w3.org/2000/svg">
<script type="text/javascript">
// Malicious code here
</script>
</svg>
Real-World Use Case: The Magento Poly Shell Vulnerability
Hackers often exploit existing vulnerabilities in platforms like Magento. The Poly Shell vulnerability, for instance, allows attackers to insert malicious scripts into the checkout pages of e-commerce sites, capturing credit card details as they are entered by customers.

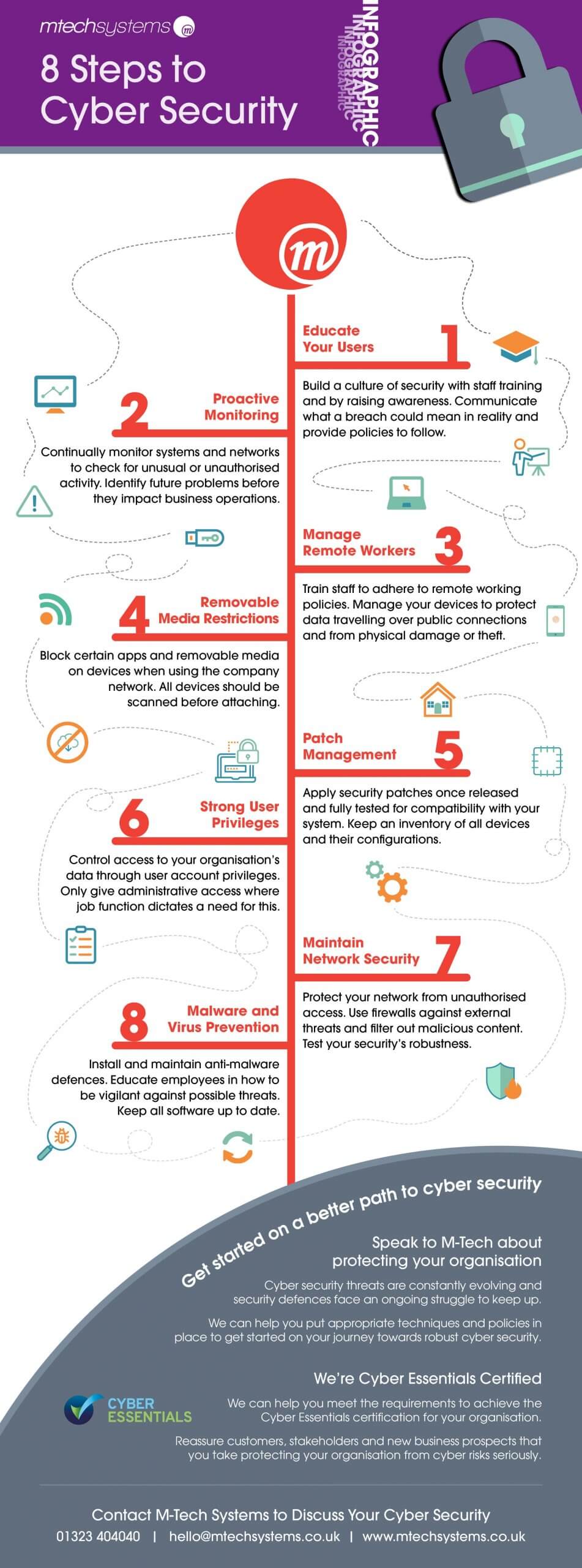
Detection and Prevention
Why Detection is Challenging
The small size of the SVG image, combined with the complexity of modern web pages, makes detection difficult. Traditional security tools may overlook these tiny images, allowing the malware to go unnoticed.
Detection Tips:
- Regular Audits: Conduct frequent audits of your website's codebase.
- Monitor Script Activity: Use tools to monitor for unusual script activity on your site.
- Whitelist SVG Usage: Restrict SVG use to trusted sources.
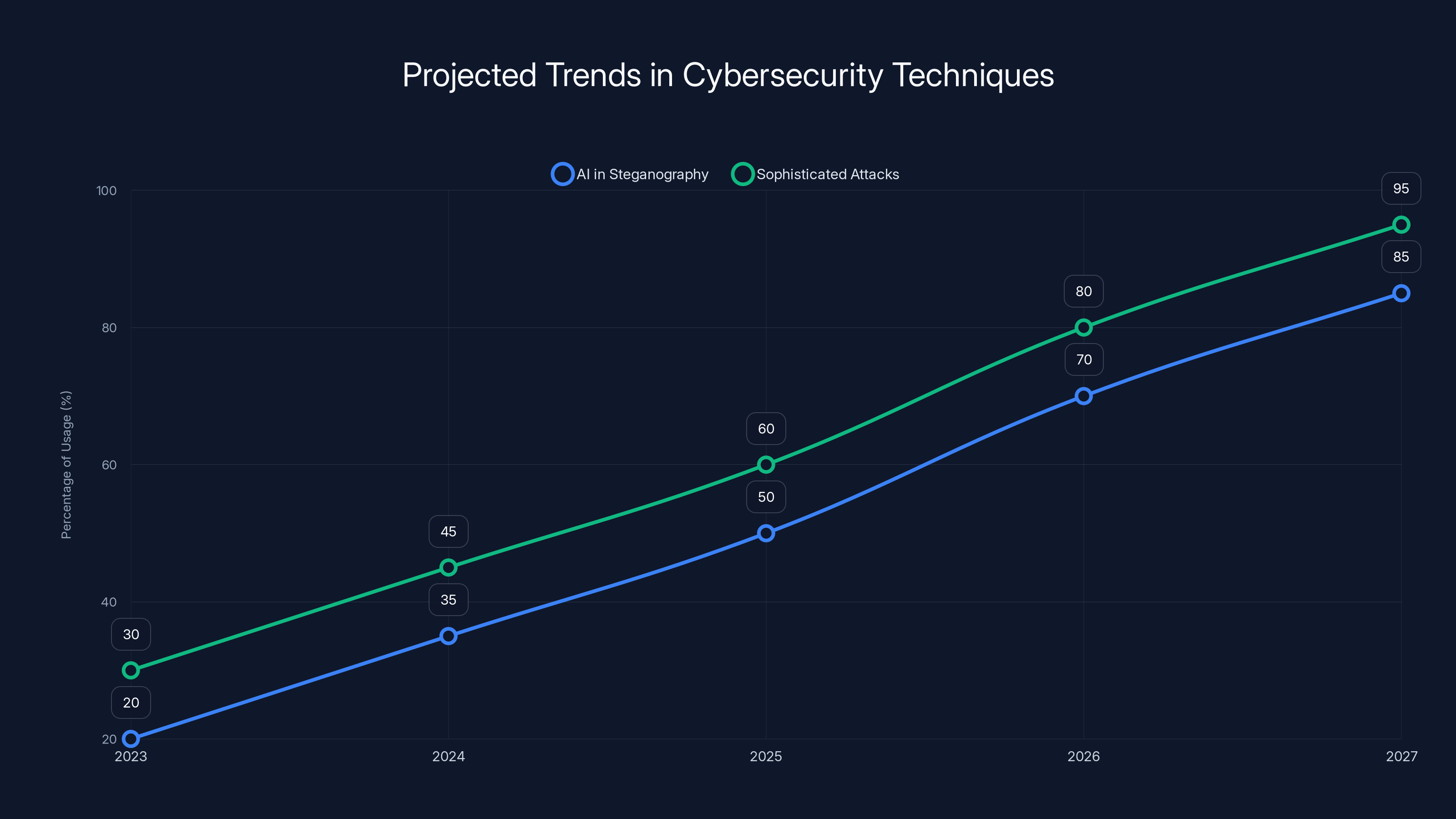
The use of AI in steganography and the sophistication of cyberattacks are expected to increase significantly by 2027. (Estimated data)
Best Practices for Protecting Your Site
-
Implement CSP (Content Security Policy): This helps control the resources that a webpage can load, mitigating the risk of malicious scripts.
-
Regular Software Updates: Keep all software, especially CMS and plugins, updated to patch known vulnerabilities.
-
Use HTTPS: Ensure all data transfers are encrypted.
-
Employ Web Application Firewalls (WAFs): These can block malicious requests before they hit your server.
-
Educate Your Team: Train your staff on the latest cybersecurity threats.

Pitfalls and Solutions
Common Pitfalls
- Over-reliance on Automated Tools: Automated security tools may miss subtle threats like SVG-based attacks.
- Ignoring Security Patches: Failure to apply patches in a timely manner can leave your site vulnerable.
- Lack of Monitoring: Without continuous monitoring, attacks can go undetected for long periods.
Solutions
- Adopt a Layered Security Approach: Combine multiple security methods for comprehensive protection.
- Engage in Threat Hunting: Proactively search for signs of threats instead of waiting for alerts.
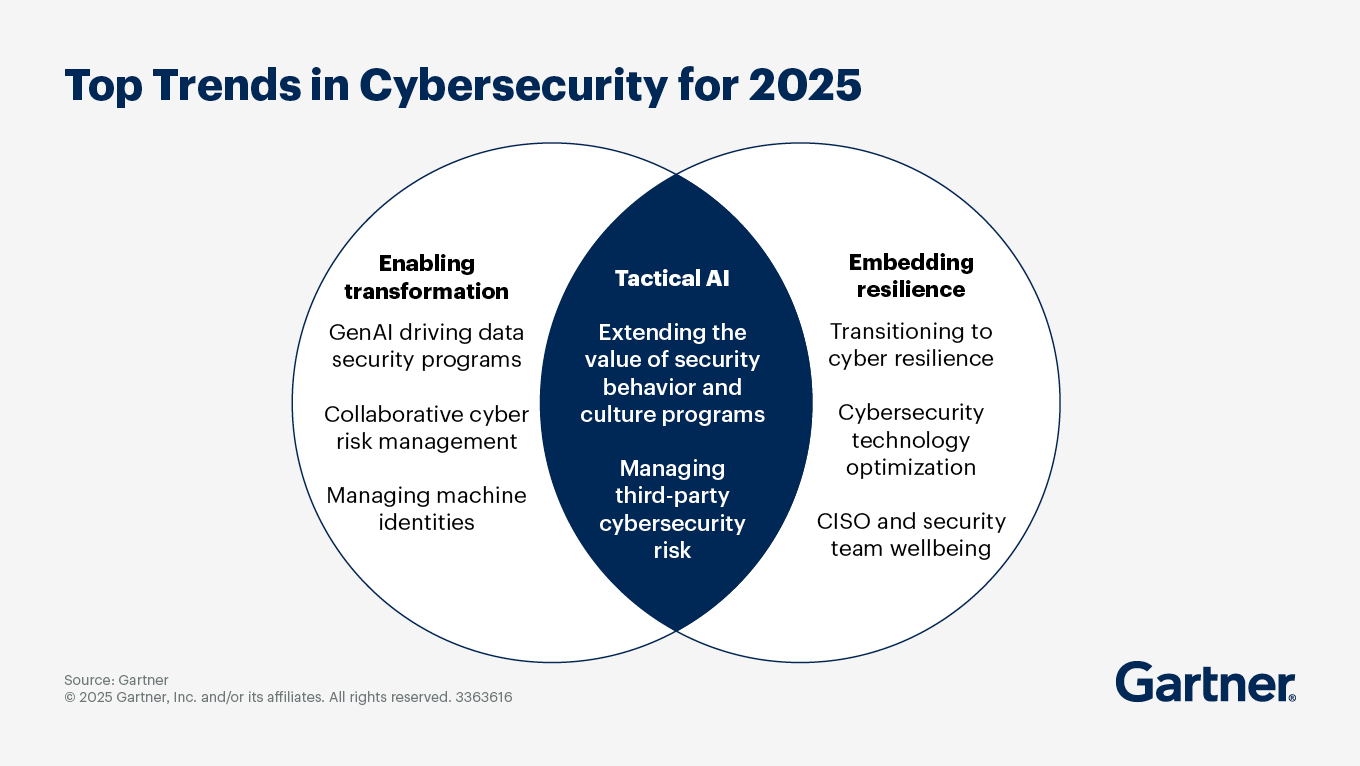
Future Trends in Cybersecurity
The Evolution of Steganography
As cybersecurity measures become more sophisticated, so do the methods employed by cybercriminals. Steganography is expected to evolve, with more complex techniques being used to embed malicious code in less obvious ways.
Future Predictions:
- Increased Use of AI: Hackers may use AI to automate the creation of steganographic content.
- More Sophisticated Attacks: Expect attacks to be more targeted and personalized.
Recommendations for the Future
-
Invest in Advanced Threat Detection Systems: Use systems that leverage AI to identify patterns and anomalies indicative of steganography.
-
Collaboration with Security Experts: Work with cybersecurity experts to stay ahead of emerging threats.
-
Continuous Learning: Stay informed about the latest cybersecurity trends and technologies.
Conclusion
The use of miniature SVG images to hide malicious code represents a significant challenge in the realm of cybersecurity. By understanding how these threats operate and implementing robust security measures, organizations can better protect themselves against this and other emerging cyber threats.
FAQ
What is SVG steganography?
SVG steganography refers to the technique of hiding malicious code within SVG images, exploiting their text-based nature and ability to include scripts.
How do hackers use SVG images for cyberattacks?
Hackers embed malicious scripts within SVG images, often as small as 1x 1 pixels, to execute unauthorized actions like stealing credit card details.
What are the risks of not securing SVG usage?
Unsecured SVG usage can lead to data breaches, financial loss, and damage to your organization's reputation.
How can I protect my website from SVG-based attacks?
Implement a Content Security Policy, regularly update software, use HTTPS, and monitor for unusual activity to protect against SVG-based attacks.
Why are SVG images challenging to detect?
Their small size and integration within complex web pages make SVG images difficult for traditional security tools to detect.
What future trends should I watch for in cybersecurity?
Look out for more sophisticated steganography techniques, increased use of AI in attacks, and a greater emphasis on personalized cyber threats.
How important is continuous monitoring for cybersecurity?
Continuous monitoring is crucial for detecting and responding to threats in real-time, minimizing potential damage.
Key Takeaways
- Tiny SVG images can conceal powerful threats like credit card skimmers.
- Steganography exploits the text-based nature of SVGs to embed malicious scripts.
- Regular security audits and monitoring are essential to detect such hidden threats.
- Future trends point to more sophisticated steganography and AI-driven attacks.
- Implementing a Content Security Policy is a critical defense strategy.
Related Articles
- The Dark Side of Cybersecurity: NHS Scotland Domains and the Hidden Threats [2025]
- Understanding the LAPD Data Breach: Lessons in Cybersecurity [2025]
- The Alinto Data Breach: Lessons in Cybersecurity for Enterprises [2025]
- How Digital Devices Endanger Our Privacy Rights [2025]
- How Emojis Are Reshaping Cybercrime Tactics: A Deep Dive [2025]
- Politicians Are Spending More Money on Security as They Increasingly Become Targets | WIRED
![Unmasking SVG Steganography: How Hackers Use Tiny Images to Hide Credit Card Skimmers [2025]](https://tryrunable.com/blog/unmasking-svg-steganography-how-hackers-use-tiny-images-to-h/image-1-1775748894851.jpg)



