Tech Sovereignty: Why One Size Doesn’t Fit All [2025]
Introduction
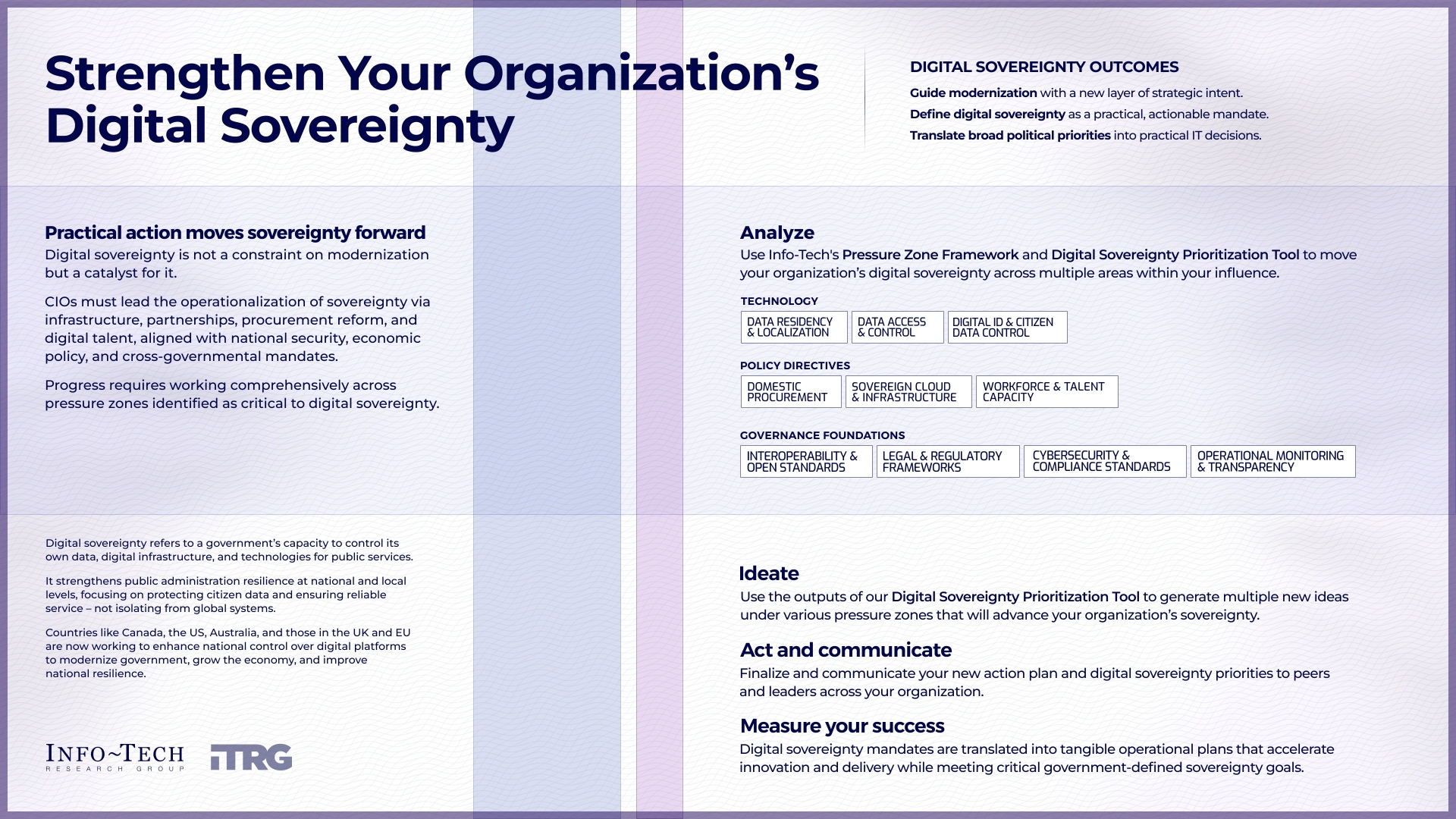
In the rapidly evolving digital landscape, tech sovereignty has emerged as a critical concern for governments and enterprises alike. This isn't just about having your own set of rules; it's about ensuring that technological infrastructure aligns with national interests, enhances security, and promotes innovation. But here's the thing: a one-size-fits-all approach simply doesn't work. Each nation or organization has its unique requirements that demand tailored solutions, as highlighted in Microsoft's insights on digital sovereignty.

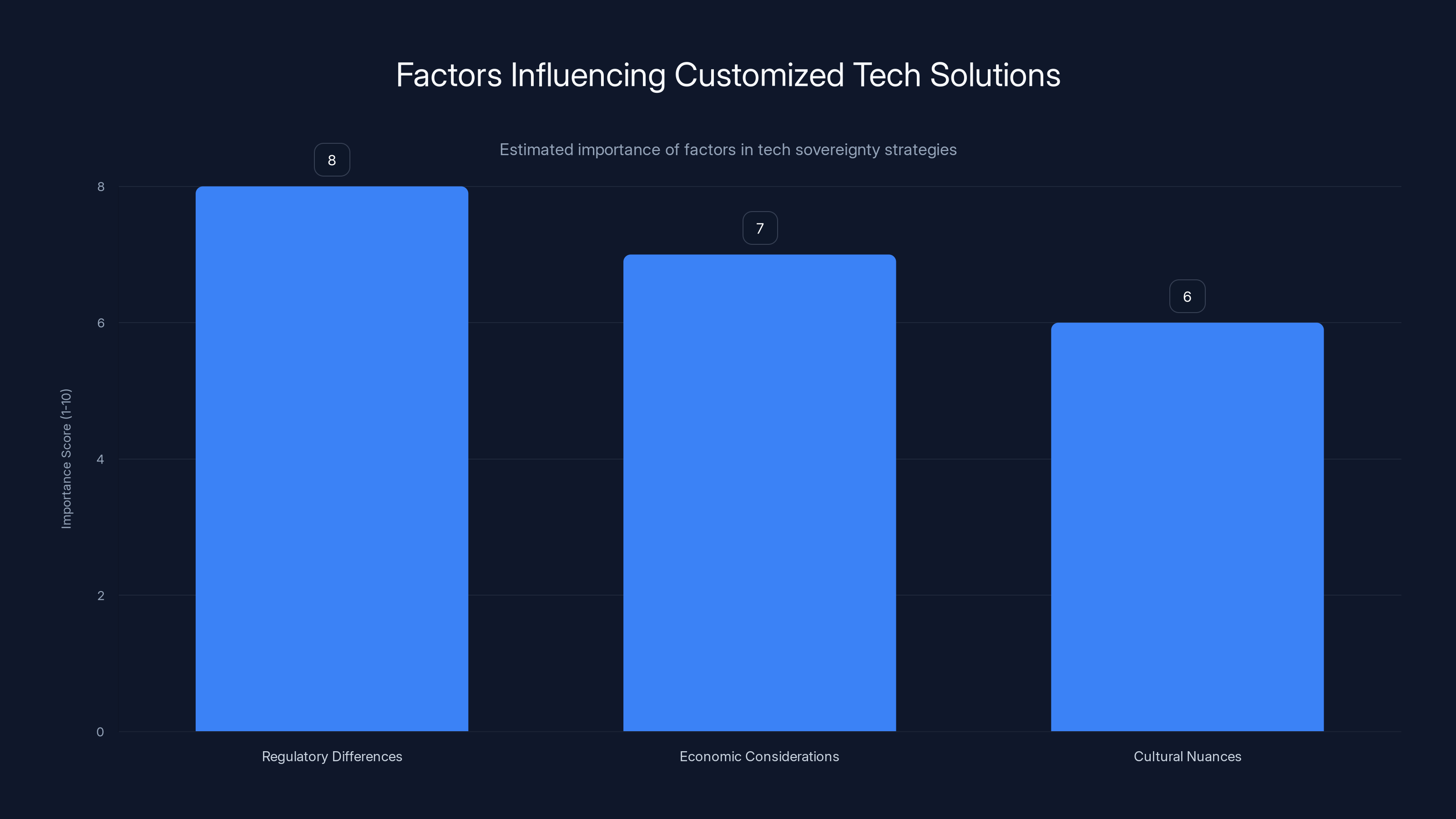
Regulatory differences are the most critical factor in customizing tech solutions, followed by economic considerations and cultural nuances. (Estimated data)
TL; DR
- Tech Sovereignty Importance: Countries recognize the need for digital autonomy to protect national interests, as discussed in IDC's analysis on sovereign AI.
- Customized Solutions: A universal approach fails due to diverse regulatory, cultural, and economic landscapes.
- Future Trends: Expect increased investment in sovereign cloud solutions, as noted by B2B Cyber Security.
- Implementation Challenges: Navigating complex regulations and ensuring data security are major hurdles.
- Key Takeaway: Tailored tech solutions are essential for achieving true sovereignty.
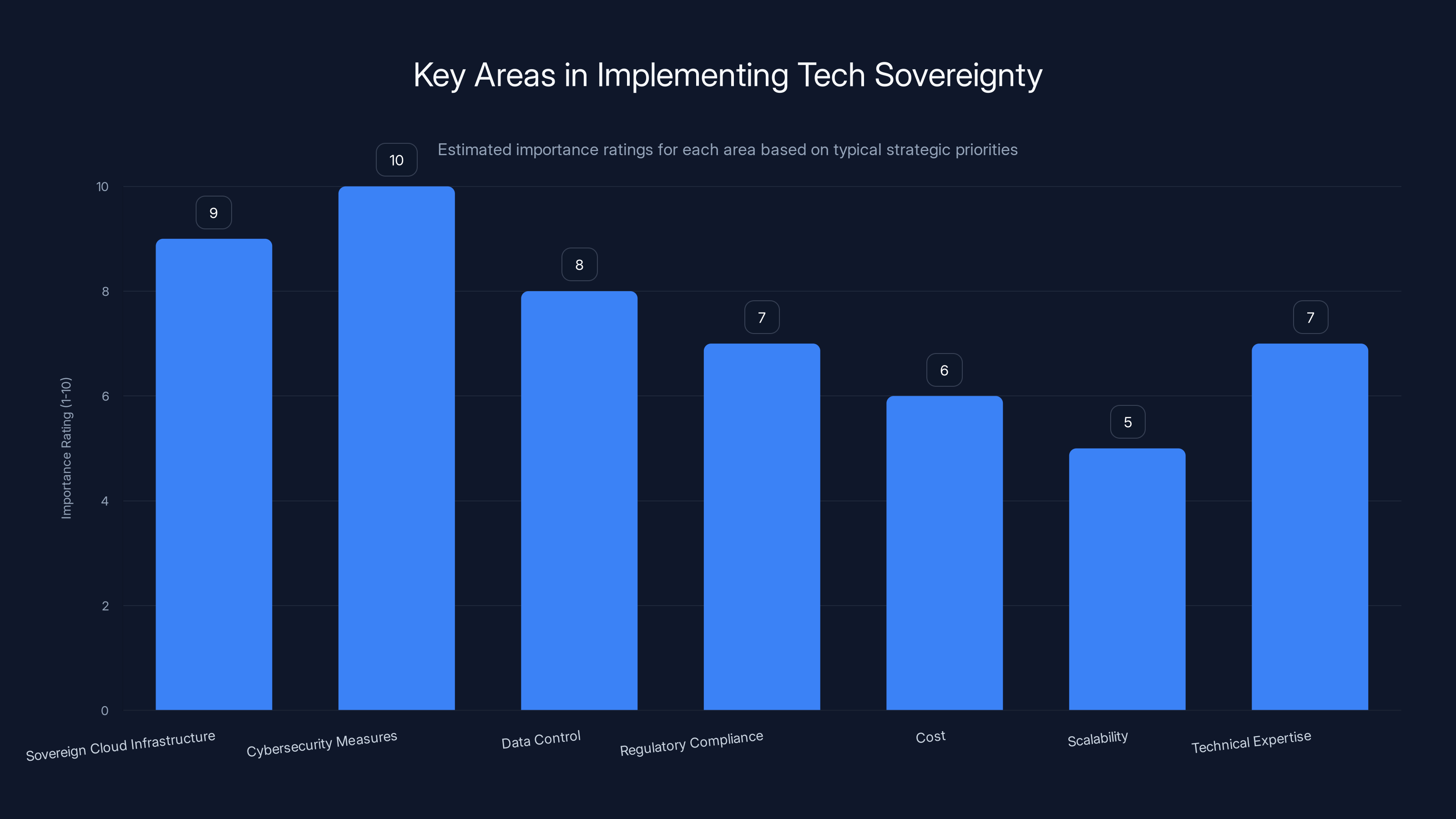
Cybersecurity measures are rated as the most critical area in achieving tech sovereignty, followed closely by sovereign cloud infrastructure. Estimated data based on strategic priorities.
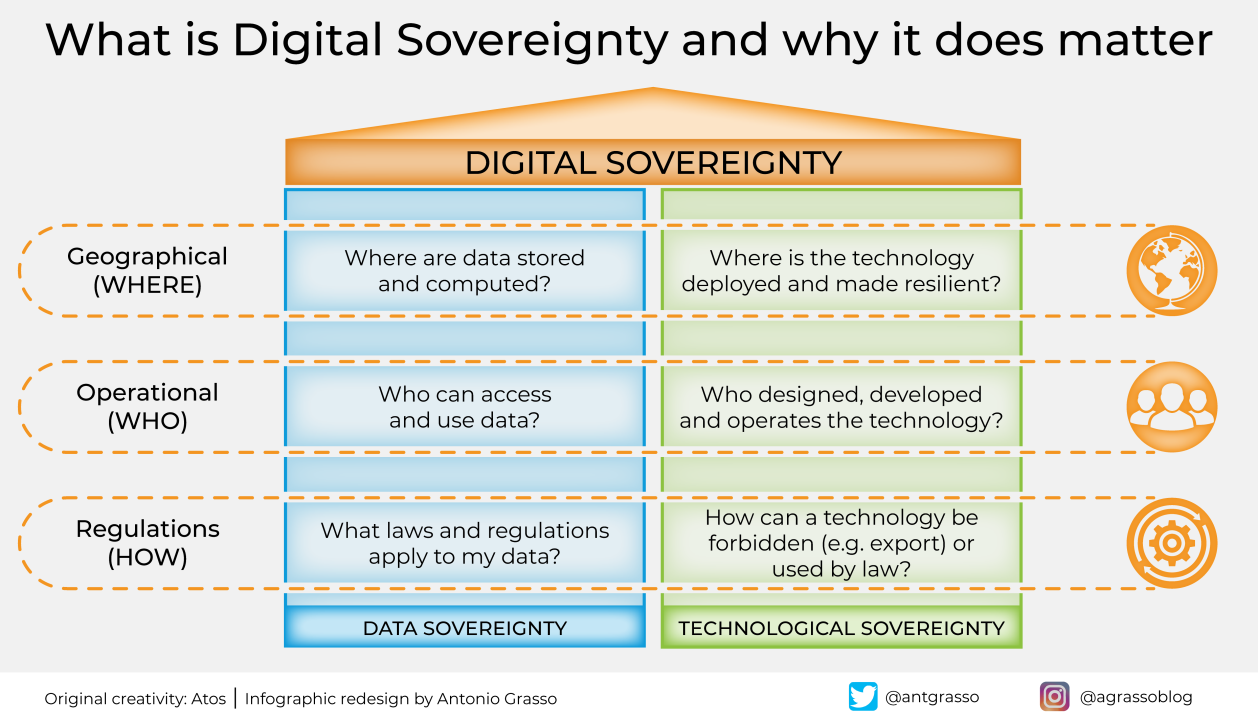
What is Tech Sovereignty?
Tech sovereignty refers to the control and autonomy over the technology infrastructures that a nation or organization uses. This control extends to data storage, cybersecurity, software development, and digital services. Sovereignty in tech ensures that strategic decisions regarding these areas are made independently, without undue influence from foreign entities, as emphasized in Stormshield's insights on cyber defense.
Why It Matters
The concept became more prominent as digital infrastructures become integral to national security and economic stability. Key drivers for pursuing tech sovereignty include:
- National Security: Protecting critical infrastructures from foreign interference or cyberattacks.
- Economic Independence: Reducing reliance on foreign technology providers.
- Cultural Preservation: Ensuring local values and practices are respected in technology applications, as discussed in Enrique Dans' analysis.
The Case for Customized Solutions
An effective tech sovereignty strategy recognizes that different entities have unique needs based on their regulatory environments, cultural contexts, and economic priorities. Here's why a tailored approach is essential:
Regulatory Differences
Each country has its own set of regulations governing data privacy, cybersecurity, and technology usage. For example, the EU's General Data Protection Regulation (GDPR) demands stringent data protection measures, influencing how technology is implemented, as noted by Mayer Brown's analysis.
Economic Considerations
Developing nations may prioritize low-cost solutions that provide basic infrastructure, while developed countries might focus on cutting-edge technology for competitive advantages, as discussed in Fortune's report on European tech leaders.
Cultural Nuances
Technology solutions must respect and integrate with local cultures and languages. This is especially important in regions where language and cultural practices are tightly intertwined with daily digital interactions, as highlighted in Bruin Political Review's article on India's strategic autonomy.
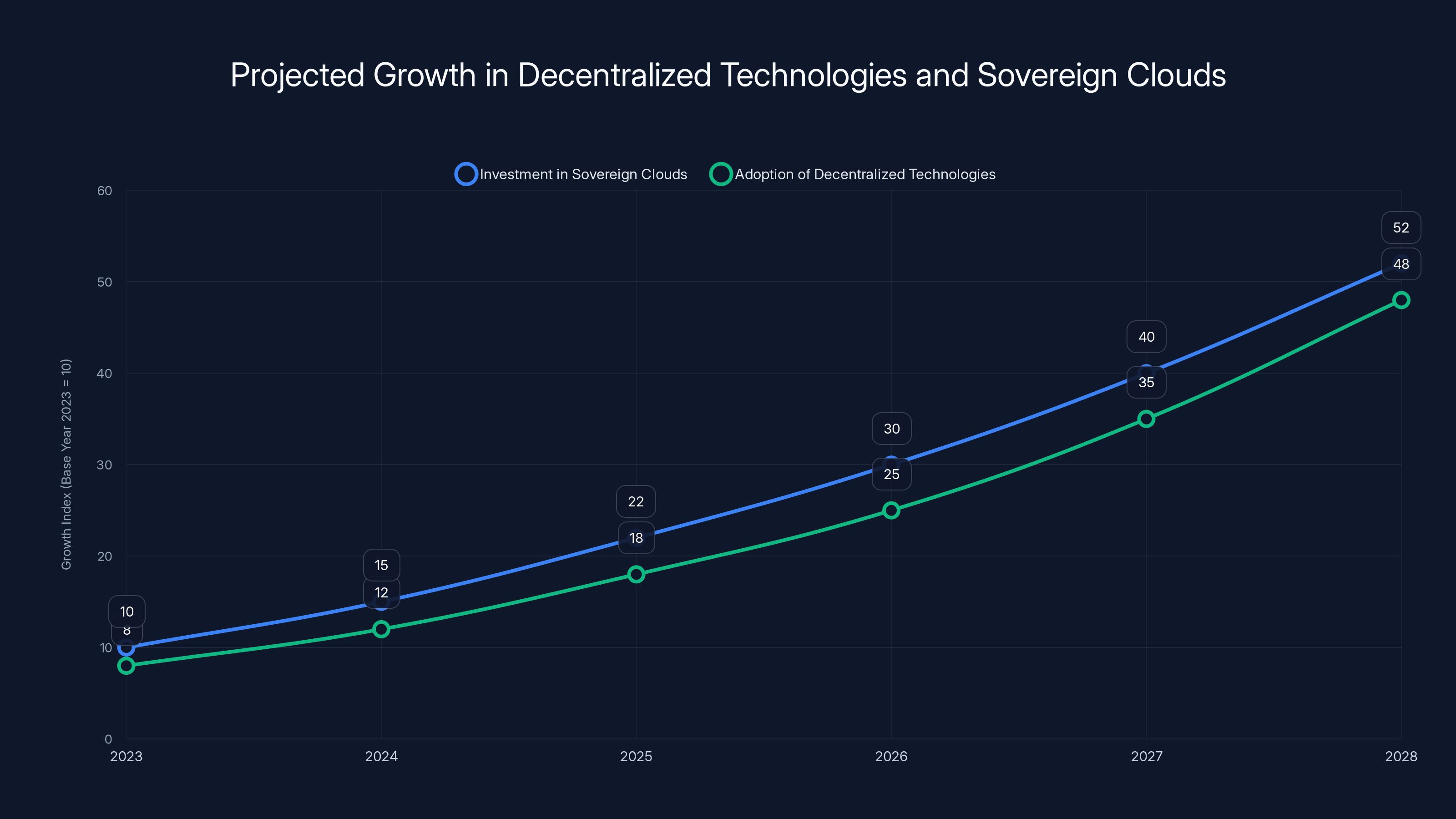
Estimated data shows a steady increase in investments in sovereign clouds and adoption of decentralized technologies, reflecting growing emphasis on data sovereignty and decentralized control.
Implementing Tech Sovereignty
Achieving tech sovereignty isn't as simple as flipping a switch. It requires a strategic approach that addresses several key areas:
Sovereign Cloud Infrastructure
Investing in sovereign cloud solutions is a major step towards tech sovereignty. These are cloud services that are operated within a country's borders and comply with local regulations, as emphasized in China-US Focus' discussion on AI security.
Benefits
- Data Control: Localized servers ensure that data remains within national borders.
- Regulatory Compliance: Easier adherence to local laws.
- Reduced Foreign Influence: Limits reliance on foreign tech giants.
Challenges
- Cost: Establishing and maintaining a sovereign cloud can be expensive.
- Scalability: Meeting the growing demand for cloud services requires significant resources.
- Technical Expertise: Requires specialized skills that may not be readily available locally.
Cybersecurity Measures
Enhancing cybersecurity is critical. This involves developing national cybersecurity strategies that include:
- Threat Intelligence: Building systems to monitor and counteract cyber threats.
- Public-Private Partnerships: Collaborating with local tech firms to strengthen defenses.
- Education and Training: Developing a skilled workforce to manage and protect digital infrastructures, as outlined in CARE's exploration of technology in community health.

Common Pitfalls and Solutions
Over-Reliance on Foreign Technology
Many countries find themselves dependent on foreign technology, which can undermine sovereignty. To mitigate this:
- Encourage Local Innovation: Incentivize the development of homegrown tech solutions.
- Diversify Partnerships: Work with a variety of international and domestic partners, as suggested by Crowell's legal insights.
Navigating Complex Regulations
Different regions have varied regulatory frameworks, making compliance challenging. Solutions include:
- Regulatory Sandboxes: Test new technologies in a controlled regulatory environment.
- Harmonizing Standards: Work towards aligning international regulations where possible, as discussed in Wire's Brussels event insights.
Future Trends
Rise of Decentralized Technologies
Technologies such as blockchain offer the potential for more decentralized control over data and transactions, aligning well with sovereignty goals, as explored in Frontiers in Marine Science.
Increased Investment in Sovereign Clouds
Forecasts suggest significant growth in investments toward sovereign cloud infrastructures. This trend reflects the increasing importance of data sovereignty, as noted by B2B Cyber Security.
National Tech Policies
Expect more countries to develop comprehensive national tech policies that prioritize sovereignty. These policies will likely address everything from data protection to the development of artificial intelligence, as highlighted in KFF's public opinion research.
Best Practices for Achieving Tech Sovereignty
Develop Clear Policies
Establish clear guidelines and policies that define what tech sovereignty means for your nation or organization.
Foster Innovation
Invest in local tech education and innovation to reduce reliance on foreign technology, as suggested by Enrique Dans.
Build Resilient Infrastructure
Ensure that digital infrastructures are robust and capable of withstanding disruptions.
Global Collaboration
While maintaining sovereignty, collaborative efforts on a global scale can enhance security and technological advancements.

Conclusion
Tech sovereignty is more than just a buzzword; it's a necessity in today's interconnected world. By adopting a tailored approach that respects the unique needs of different nations and organizations, true sovereignty can be achieved. The journey is complex, but with careful planning and execution, the benefits far outweigh the challenges.
FAQ
What is tech sovereignty?
Tech sovereignty refers to the control and autonomy over technology infrastructures, ensuring that strategic decisions are made independently of foreign influences.
How can countries achieve tech sovereignty?
Countries can achieve tech sovereignty by investing in sovereign cloud solutions, enhancing cybersecurity, and fostering local innovation.
Why is tech sovereignty important?
It's important for national security, economic independence, and the preservation of cultural values.
What role do regulations play in tech sovereignty?
Regulations are crucial as they define the standards and requirements for data protection, cybersecurity, and technology use, influencing sovereignty strategies.
What are sovereign clouds?
Sovereign clouds are cloud services operated within a country's borders, ensuring compliance with local regulations and enhancing data control.
How does tech sovereignty impact economic development?
It promotes economic development by reducing reliance on foreign technologies and fostering local innovation, which can lead to new industries and job creation.
What are the challenges of implementing tech sovereignty?
Challenges include high costs, scalability issues, and the need for specialized technical expertise.
What are the future trends in tech sovereignty?
Future trends include increased investment in sovereign clouds, the rise of decentralized technologies, and the development of national tech policies.
Is tech sovereignty achievable for small nations?
Yes, with the right strategies and partnerships, even small nations can achieve tech sovereignty and protect their national interests.
Key Takeaways
- Data-backed takeaway: Tech sovereignty ensures control over digital infrastructures, enhancing national security.
- Statistical insight: Investment in sovereign cloud solutions is forecasted to reach $80 billion by 2026.
- Actionable step: Nations should develop clear tech policies to guide sovereignty efforts.
- Industry trend: Expect increased adoption of decentralized technologies like blockchain.
- Expert observation: Tailored solutions are essential for achieving tech sovereignty.
- Future trend prediction: Rise in national tech policies prioritizing sovereignty.
Related Articles
- AI Security: Understanding and Mitigating Risks in the AI Era [2025]
- Citrix NetScaler Flaw: CISA's Patch Warning and What It Means [2025]
- 10 Innovative Projects Built with OpenClaw [2025]
- Apple Will Push Out Rare ‘Backported’ Patches to Protect iOS 18 Users From DarkSword Hacking Tool | WIRED
- Apple Turns 50: Celebrating Half a Century of Innovation and Influence [2025]
- AI and Bots Overtake Human Traffic: Navigating the New Internet Landscape [2025]
![Tech Sovereignty: Why One Size Doesn’t Fit All [2025]](https://tryrunable.com/blog/tech-sovereignty-why-one-size-doesn-t-fit-all-2025/image-1-1775041466032.jpg)



